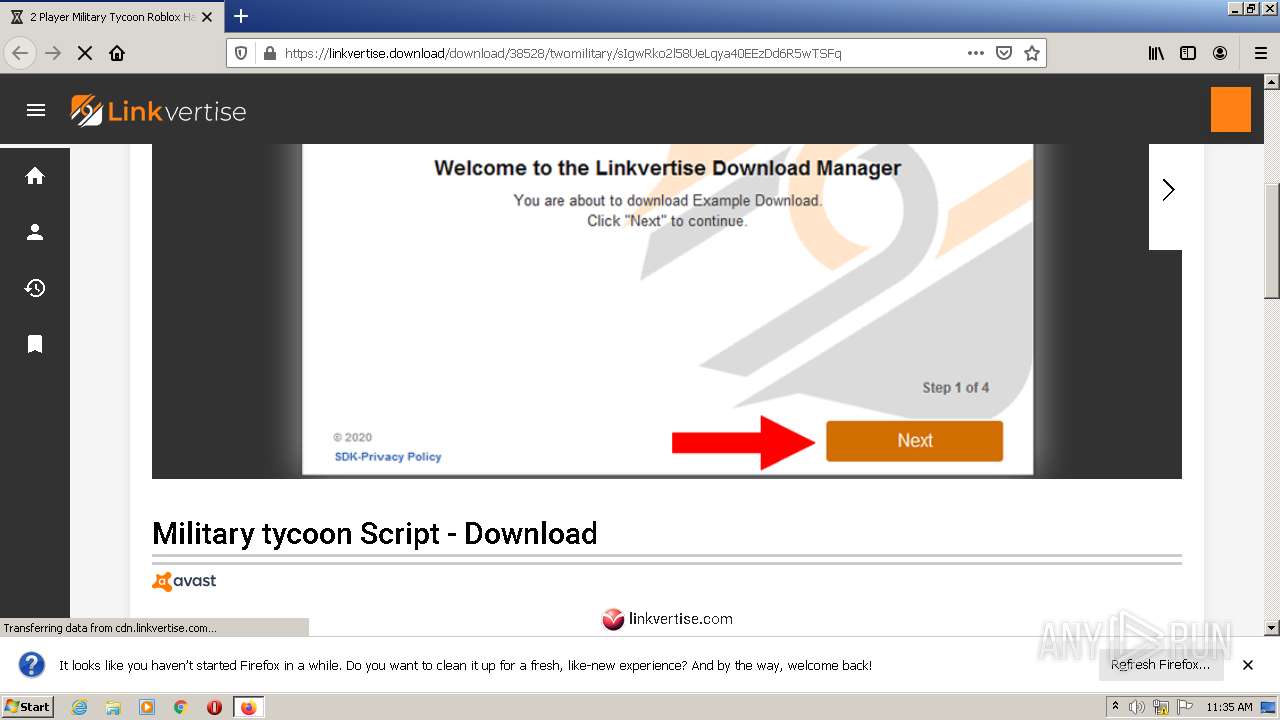
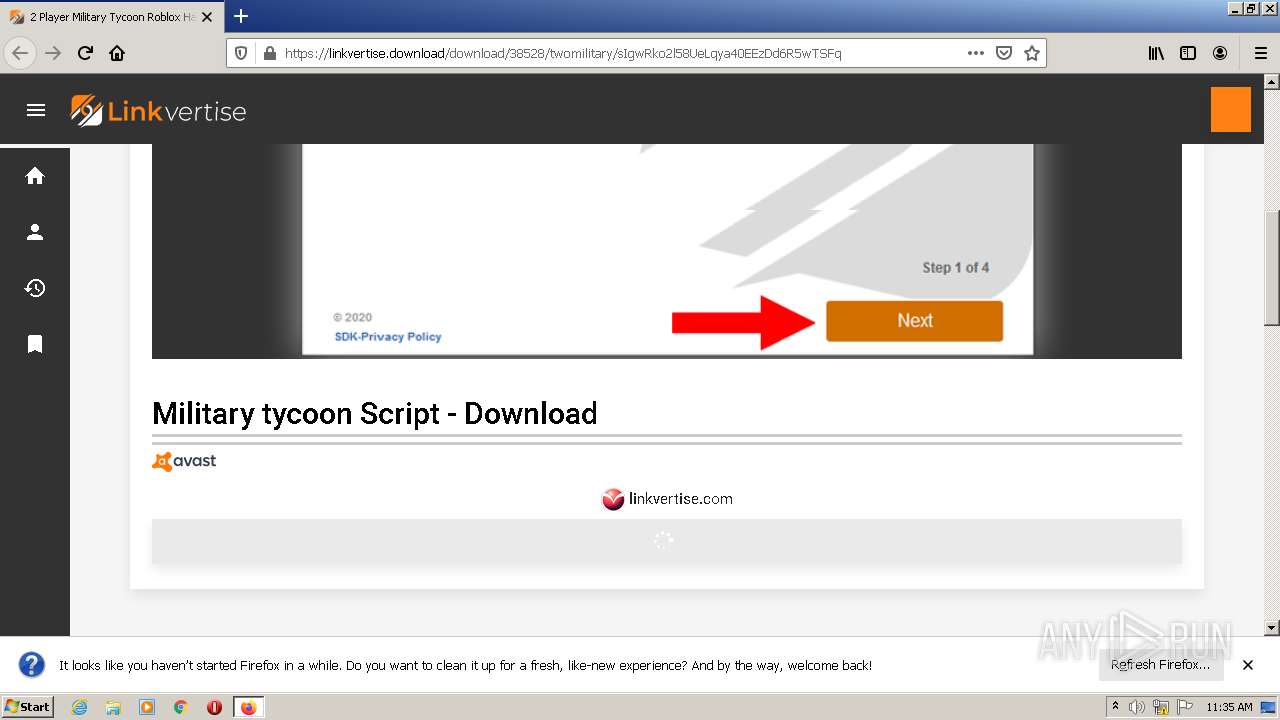
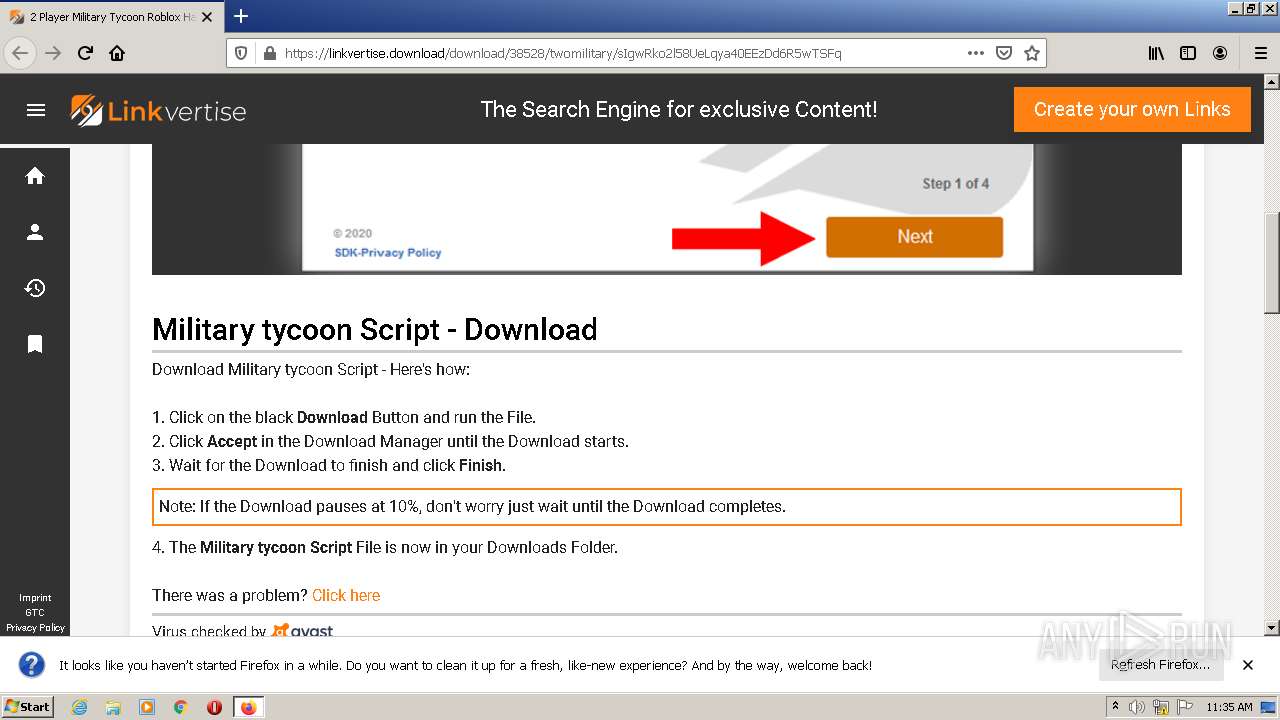
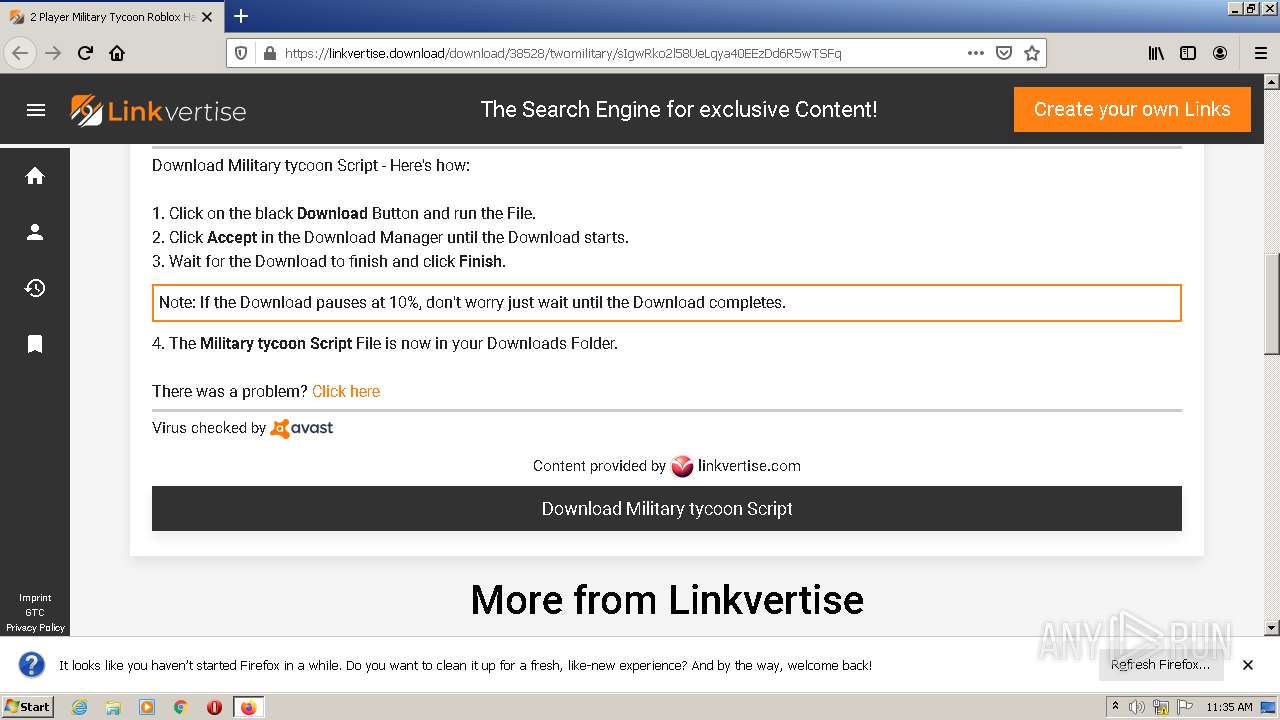
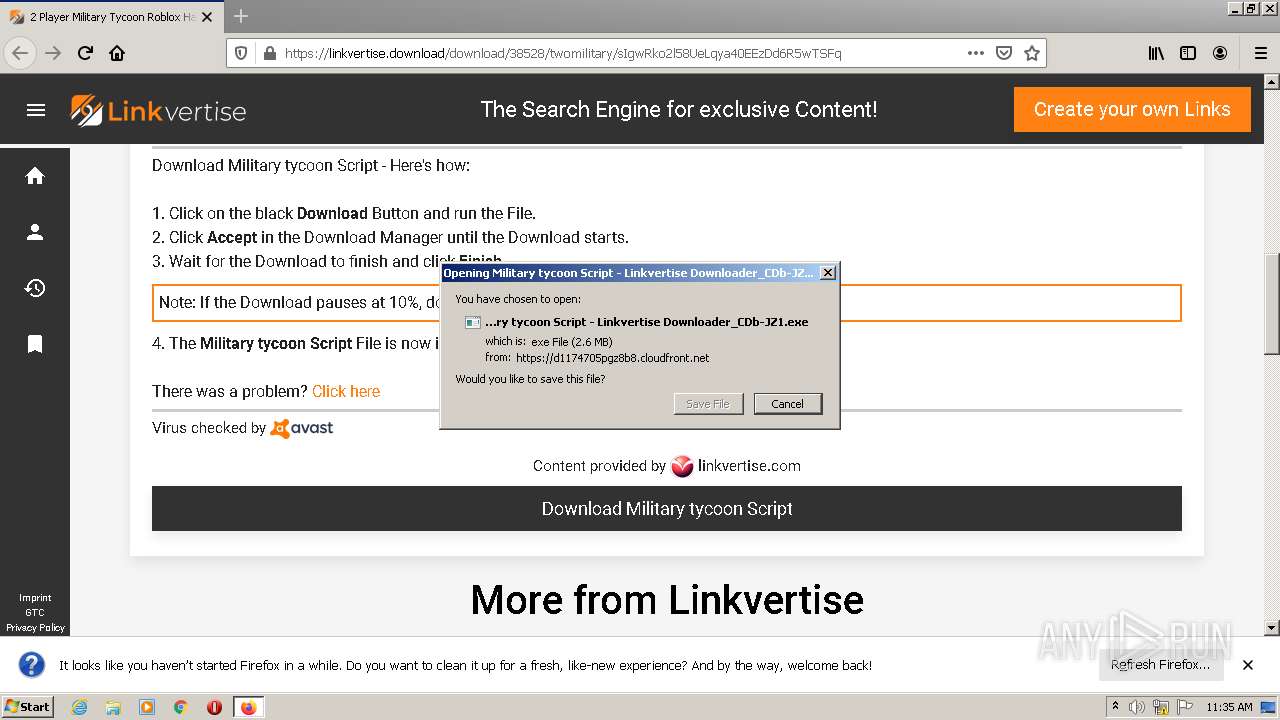
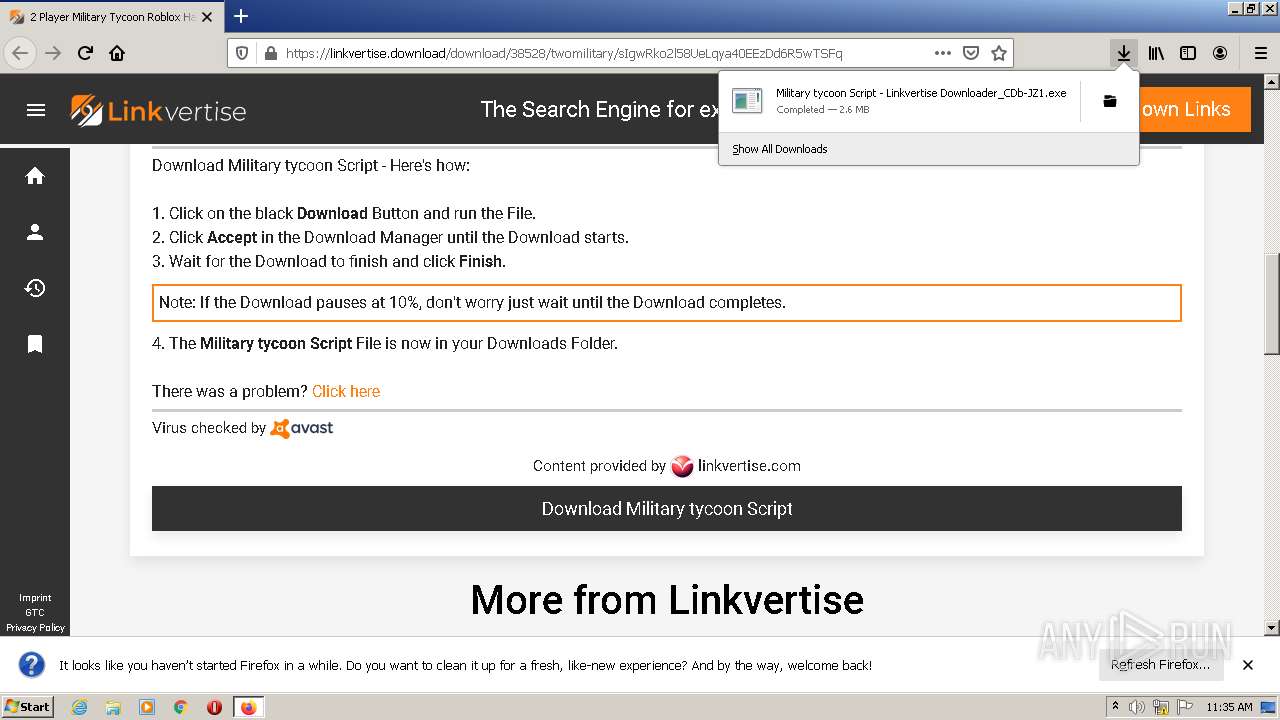
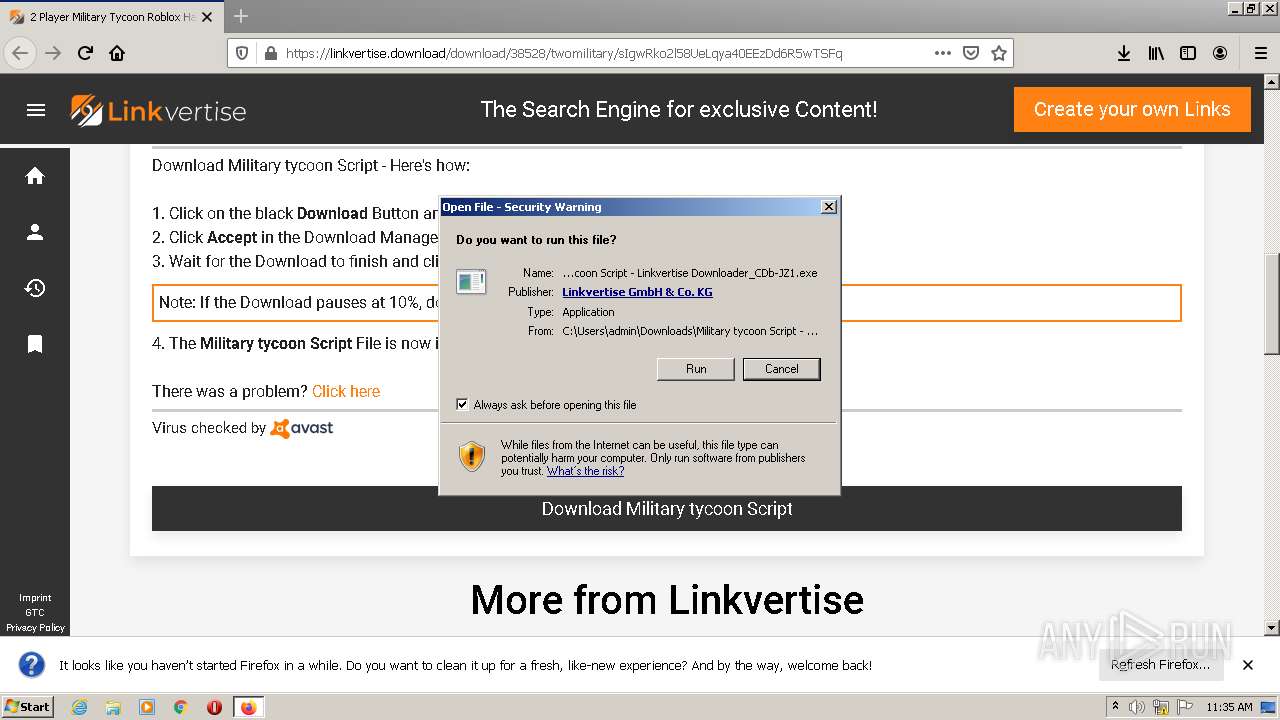
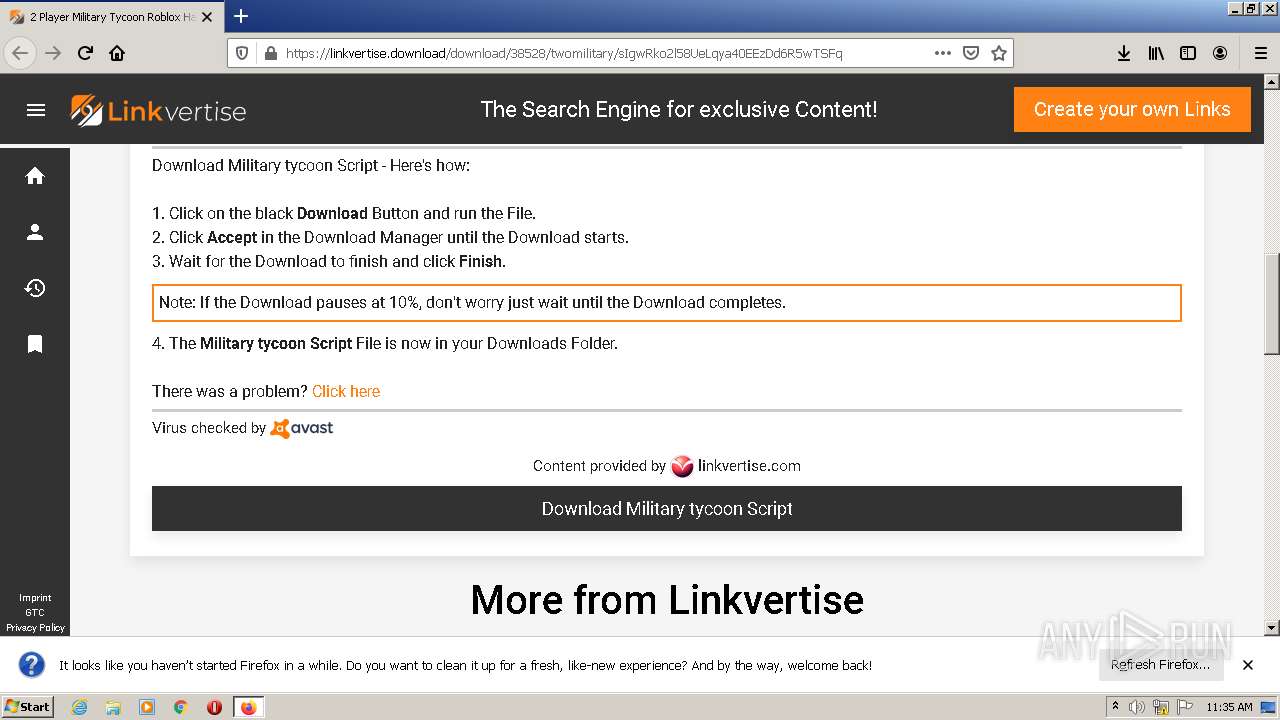
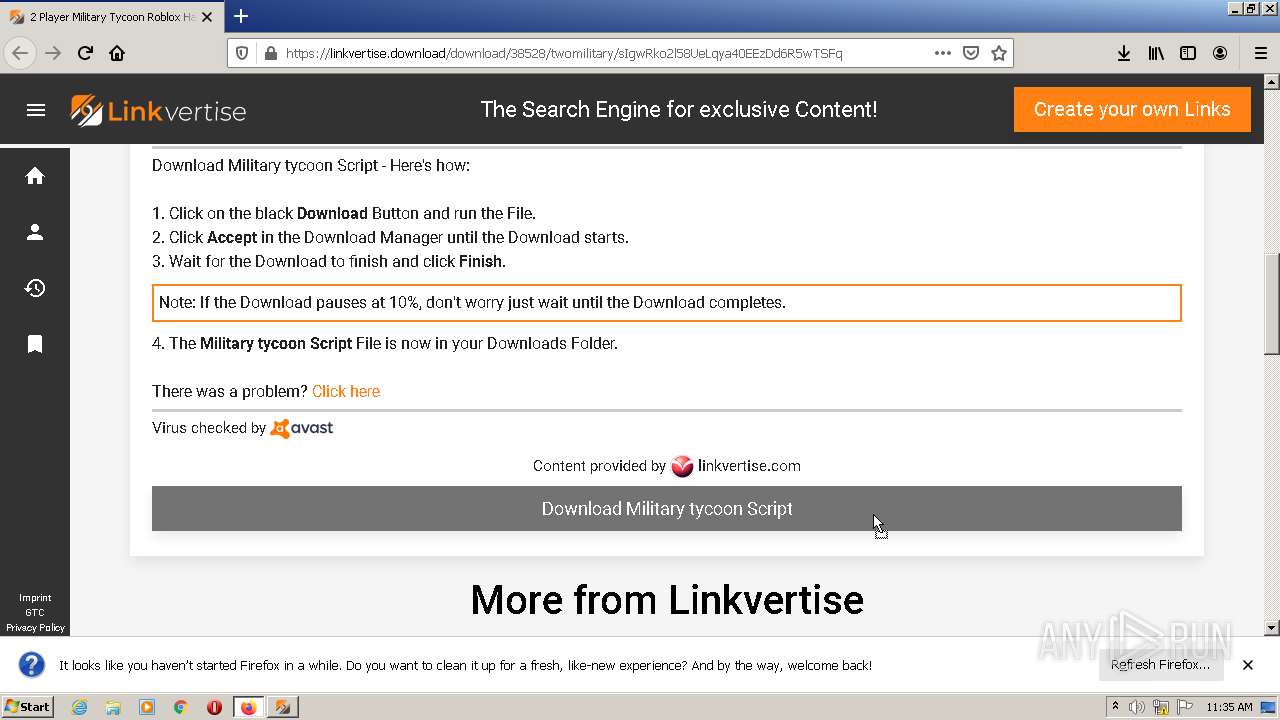
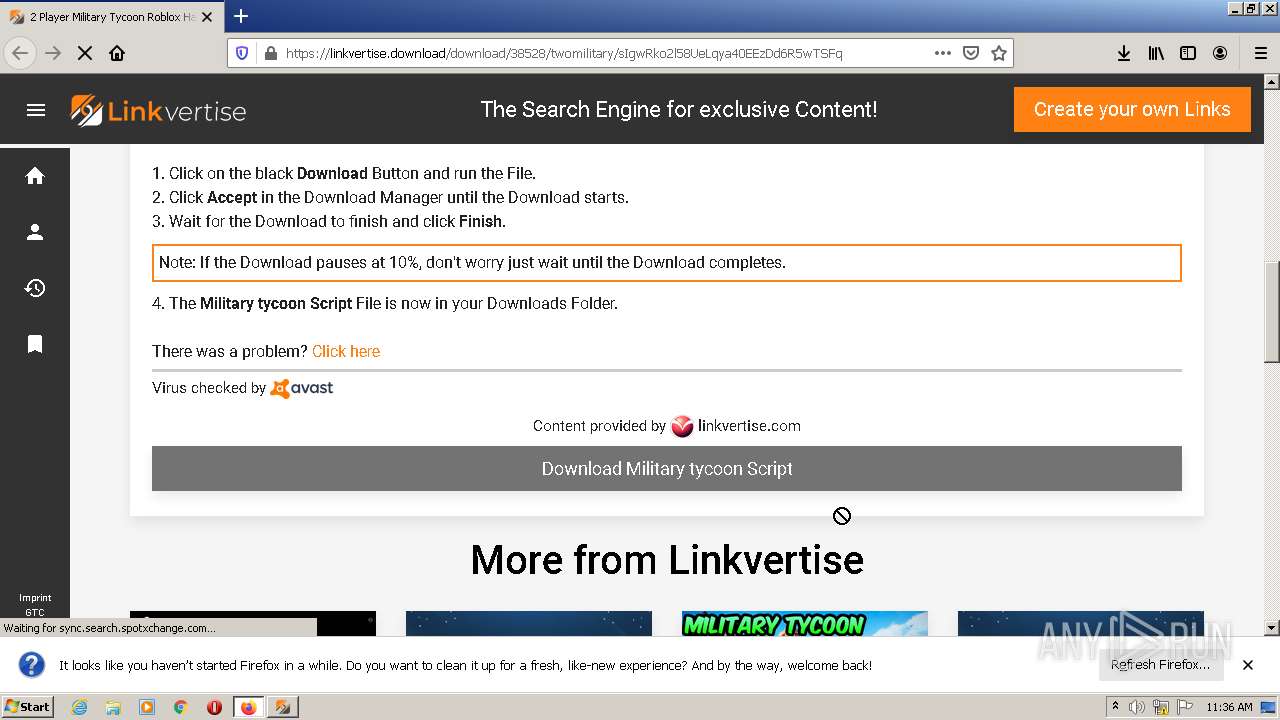
| URL: | https://linkvertise.download/download/38528/twomilitary/sIgwRko2l58UeLqya40EEzDd6R5wTSFq |
| Full analysis: | https://app.any.run/tasks/e2422ae9-6e0c-4961-9ea4-9a2f20c4160e |
| Verdict: | Malicious activity |
| Analysis date: | June 27, 2022, 10:35:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F6258B1C00E3B9D7A7DC1F83FC555402 |
| SHA1: | B6FE7CF593FC94114DC347E3E7F5AFC49AC6683E |
| SHA256: | D3B41EBF7060B1326468447F9F64097C955B1B0B19AB35B5814A313B29D61605 |
| SSDEEP: | 3:N8MLRBXA1zKXXJkWSXdKRejCepalJBU6:2MNi1zohSNKRejCepalJBU6 |
MALICIOUS
Application was dropped or rewritten from another process
- Military tycoon Script - Linkvertise Downloader_CDb-JZ1.exe (PID: 1644)
- Military tycoon Script - Linkvertise Downloader_CDb-JZ1.exe (PID: 1828)
Drops executable file immediately after starts
- Military tycoon Script - Linkvertise Downloader_CDb-JZ1.exe (PID: 1644)
- firefox.exe (PID: 4032)
- Military tycoon Script - Linkvertise Downloader_CDb-JZ1.exe (PID: 1828)
SUSPICIOUS
Drops a file with a compile date too recent
- firefox.exe (PID: 4032)
- Military tycoon Script - Linkvertise Downloader_CDb-JZ1.exe (PID: 1644)
- Military tycoon Script - Linkvertise Downloader_CDb-JZ1.exe (PID: 1828)
Executable content was dropped or overwritten
- firefox.exe (PID: 4032)
- Military tycoon Script - Linkvertise Downloader_CDb-JZ1.exe (PID: 1828)
- Military tycoon Script - Linkvertise Downloader_CDb-JZ1.exe (PID: 1644)
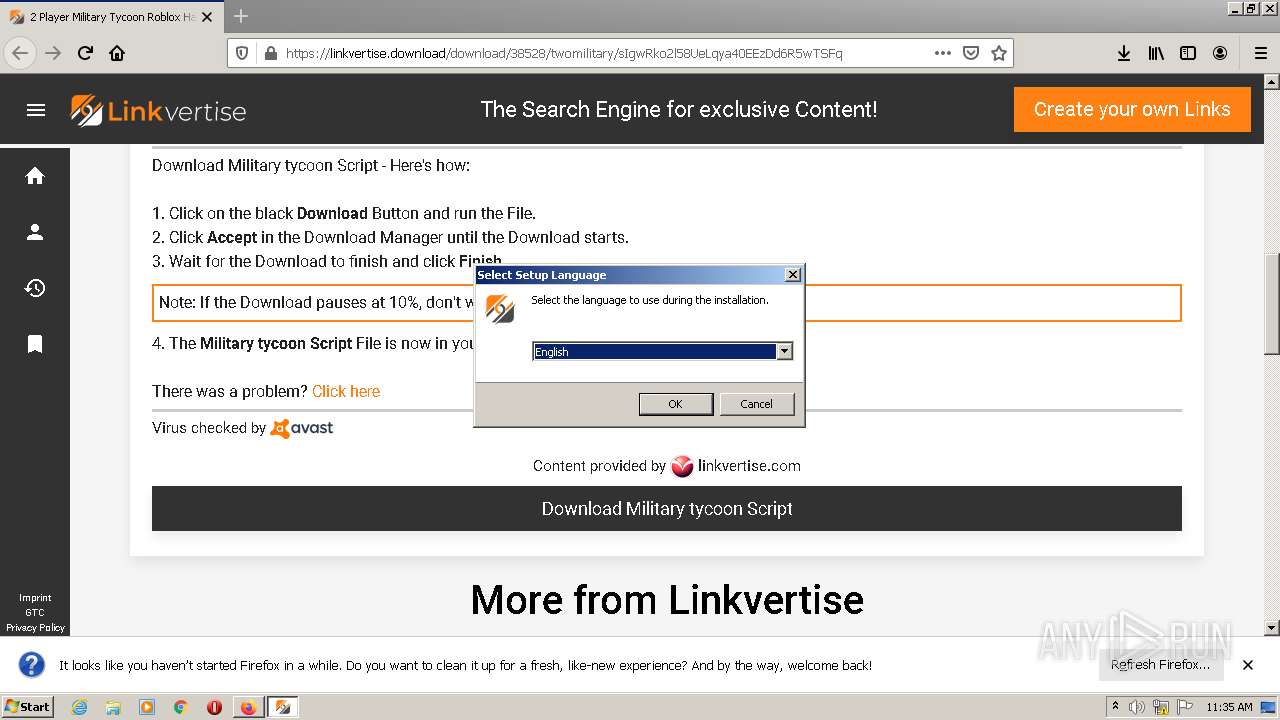
Checks supported languages
- Military tycoon Script - Linkvertise Downloader_CDb-JZ1.exe (PID: 1644)
- Military tycoon Script - Linkvertise Downloader_CDb-JZ1.tmp (PID: 2440)
- Military tycoon Script - Linkvertise Downloader_CDb-JZ1.exe (PID: 1828)
- Military tycoon Script - Linkvertise Downloader_CDb-JZ1.tmp (PID: 1844)
Reads the computer name
- Military tycoon Script - Linkvertise Downloader_CDb-JZ1.tmp (PID: 1844)
- Military tycoon Script - Linkvertise Downloader_CDb-JZ1.tmp (PID: 2440)
INFO
Checks supported languages
- firefox.exe (PID: 2948)
- firefox.exe (PID: 4032)
- firefox.exe (PID: 3392)
- firefox.exe (PID: 3964)
- firefox.exe (PID: 3532)
- firefox.exe (PID: 2332)
- firefox.exe (PID: 3296)
- firefox.exe (PID: 124)
Reads CPU info
- firefox.exe (PID: 4032)
Reads the computer name
- firefox.exe (PID: 4032)
- firefox.exe (PID: 3392)
- firefox.exe (PID: 3964)
- firefox.exe (PID: 3532)
- firefox.exe (PID: 2332)
- firefox.exe (PID: 3296)
- firefox.exe (PID: 124)
Application launched itself
- firefox.exe (PID: 2948)
- firefox.exe (PID: 4032)
Creates files in the program directory
- firefox.exe (PID: 4032)
Dropped object may contain Bitcoin addresses
- firefox.exe (PID: 4032)
Creates files in the user directory
- firefox.exe (PID: 4032)
Checks Windows Trust Settings
- firefox.exe (PID: 4032)
Reads settings of System Certificates
- firefox.exe (PID: 4032)
Application was dropped or rewritten from another process
- Military tycoon Script - Linkvertise Downloader_CDb-JZ1.tmp (PID: 2440)
- Military tycoon Script - Linkvertise Downloader_CDb-JZ1.tmp (PID: 1844)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
50
Monitored processes
12
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="4032.28.214720823\1837763853" -childID 5 -isForBrowser -prefsHandle 7332 -prefMapHandle 7336 -prefsLen 8793 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 4032 "\\.\pipe\gecko-crash-server-pipe.4032" 7304 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 1644 | "C:\Users\admin\Downloads\Military tycoon Script - Linkvertise Downloader_CDb-JZ1.exe" | C:\Users\admin\Downloads\Military tycoon Script - Linkvertise Downloader_CDb-JZ1.exe | firefox.exe | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Linkvertise GmbH & Co. KG Exit code: 0 Version: 3.43.7745.13 Modules
| |||||||||||||||
| 1828 | "C:\Users\admin\Downloads\Military tycoon Script - Linkvertise Downloader_CDb-JZ1.exe" /SPAWNWND=$20176 /NOTIFYWND=$20160 | C:\Users\admin\Downloads\Military tycoon Script - Linkvertise Downloader_CDb-JZ1.exe | Military tycoon Script - Linkvertise Downloader_CDb-JZ1.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Linkvertise GmbH & Co. KG Exit code: 0 Version: 3.43.7745.13 Modules
| |||||||||||||||
| 1844 | "C:\Users\admin\AppData\Local\Temp\is-6FVPN.tmp\Military tycoon Script - Linkvertise Downloader_CDb-JZ1.tmp" /SL5="$30174,1785071,899584,C:\Users\admin\Downloads\Military tycoon Script - Linkvertise Downloader_CDb-JZ1.exe" /SPAWNWND=$20176 /NOTIFYWND=$20160 | C:\Users\admin\AppData\Local\Temp\is-6FVPN.tmp\Military tycoon Script - Linkvertise Downloader_CDb-JZ1.tmp | — | Military tycoon Script - Linkvertise Downloader_CDb-JZ1.exe | |||||||||||
User: admin Company: Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2332 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="4032.20.2005580492\1618982160" -childID 3 -isForBrowser -prefsHandle 7696 -prefMapHandle 7700 -prefsLen 7378 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 4032 "\\.\pipe\gecko-crash-server-pipe.4032" 7684 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 2440 | "C:\Users\admin\AppData\Local\Temp\is-5T14H.tmp\Military tycoon Script - Linkvertise Downloader_CDb-JZ1.tmp" /SL5="$20160,1785071,899584,C:\Users\admin\Downloads\Military tycoon Script - Linkvertise Downloader_CDb-JZ1.exe" | C:\Users\admin\AppData\Local\Temp\is-5T14H.tmp\Military tycoon Script - Linkvertise Downloader_CDb-JZ1.tmp | — | Military tycoon Script - Linkvertise Downloader_CDb-JZ1.exe | |||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2948 | "C:\Program Files\Mozilla Firefox\firefox.exe" "https://linkvertise.download/download/38528/twomilitary/sIgwRko2l58UeLqya40EEzDd6R5wTSFq" | C:\Program Files\Mozilla Firefox\firefox.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 3296 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="4032.27.113584253\495690542" -childID 4 -isForBrowser -prefsHandle 7348 -prefMapHandle 7352 -prefsLen 8793 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 4032 "\\.\pipe\gecko-crash-server-pipe.4032" 7324 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 3392 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="4032.0.1353316160\1790885595" -parentBuildID 20201112153044 -prefsHandle 1108 -prefMapHandle 832 -prefsLen 1 -prefMapSize 238726 -appdir "C:\Program Files\Mozilla Firefox\browser" - 4032 "\\.\pipe\gecko-crash-server-pipe.4032" 1208 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 3532 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="4032.13.118156640\1024247033" -childID 2 -isForBrowser -prefsHandle 1992 -prefMapHandle 1988 -prefsLen 6644 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 4032 "\\.\pipe\gecko-crash-server-pipe.4032" 1976 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
Total events
15 378
Read events
15 339
Write events
39
Delete events
0
Modification events
| (PID) Process: | (2948) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 38C15CEF9E000000 | |||
| (PID) Process: | (4032) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: DEC95CEF9E000000 | |||
| (PID) Process: | (4032) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 0 | |||
| (PID) Process: | (4032) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (4032) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableTelemetry |
Value: 1 | |||
| (PID) Process: | (4032) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableDefaultBrowserAgent |
Value: 0 | |||
| (PID) Process: | (4032) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|ServicesSettingsServer |
Value: https://firefox.settings.services.mozilla.com/v1 | |||
| (PID) Process: | (4032) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|SecurityContentSignatureRootHash |
Value: 97:E8:BA:9C:F1:2F:B3:DE:53:CC:42:A4:E6:57:7E:D6:4D:F4:93:C2:47:B4:14:FE:A0:36:81:8D:38:23:56:0E | |||
| (PID) Process: | (4032) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (4032) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
4
Suspicious files
91
Text files
34
Unknown types
25
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4032 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 4032 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 4032 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | text | |
MD5:299A2B747C11E4BDA194E563FEA4A699 | SHA256:94EE461F62E8B4A0A65471A41E10C8C56722B73C0A019D76ACA7F5BAF109813E | |||
| 4032 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 4032 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\places.sqlite-wal | sqlite-wal | |
MD5:— | SHA256:— | |||
| 4032 | firefox.exe | C:\Users\admin\AppData\Local\Temp\mz_etilqs_sMuwggNPtKW0zgG | binary | |
MD5:— | SHA256:— | |||
| 4032 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 4032 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 4032 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-wal | binary | |
MD5:— | SHA256:— | |||
| 4032 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
150
DNS requests
228
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4032 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
4032 | firefox.exe | POST | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gts1c3 | US | der | 471 b | whitelisted |
4032 | firefox.exe | POST | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gts1c3 | US | der | 472 b | whitelisted |
4032 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
4032 | firefox.exe | POST | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gts1c3 | US | der | 472 b | whitelisted |
4032 | firefox.exe | POST | 200 | 143.204.101.74:80 | http://ocsp.sca1b.amazontrust.com/ | US | der | 471 b | whitelisted |
4032 | firefox.exe | POST | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/s/gts1d4/4ZbXmmEOtpo | US | der | 472 b | whitelisted |
4032 | firefox.exe | POST | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gts1c3 | US | der | 471 b | whitelisted |
4032 | firefox.exe | POST | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gts1c3 | US | der | 471 b | whitelisted |
4032 | firefox.exe | POST | 200 | 172.64.155.188:80 | http://ocsp.sectigo.com/ | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4032 | firefox.exe | 184.24.77.146:443 | p.typekit.net | Time Warner Cable Internet LLC | US | suspicious |
4032 | firefox.exe | 142.250.185.72:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
4032 | firefox.exe | 143.204.89.115:443 | snippets.cdn.mozilla.net | — | US | unknown |
4032 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | — | US | whitelisted |
4032 | firefox.exe | 104.21.68.126:443 | linkvertise.download | Cloudflare Inc | US | unknown |
4032 | firefox.exe | 143.204.89.103:443 | firefox.settings.services.mozilla.com | — | US | unknown |
4032 | firefox.exe | 142.250.185.67:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
4032 | firefox.exe | 104.17.25.14:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | suspicious |
4032 | firefox.exe | 52.36.164.126:443 | location.services.mozilla.com | Amazon.com, Inc. | US | unknown |
4032 | firefox.exe | 23.35.228.23:443 | contextual.media.net | Zayo Bandwidth Inc | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
linkvertise.download |
| suspicious |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
firefox.settings.services.mozilla.com |
| whitelisted |
location.services.mozilla.com |
| whitelisted |
locprod2-elb-us-west-2.prod.mozaws.net |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cs9.wac.phicdn.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4032 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
4032 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
4032 | firefox.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |