| File name: | Windows.ps1 |
| Full analysis: | https://app.any.run/tasks/f6fc9855-72bc-47da-b216-900f7bd49e9d |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 08:27:39 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines (2316), with CRLF line terminators |
| MD5: | 4322A5D42EC411A3F17B0A9E864176E1 |
| SHA1: | 30711D2B29E29A7AD217CBE71D39435A61C01524 |
| SHA256: | D3B182F7E2ECBA645144AD324505C658DE2000320C434BBFE3E560741ECAECE1 |
| SSDEEP: | 96:U6EBrivyW6bCptuJs0QQgi4ati4Fi4ihFi4iwzIrT6MTrDXa:bUW6b3JszQzyuTr2 |
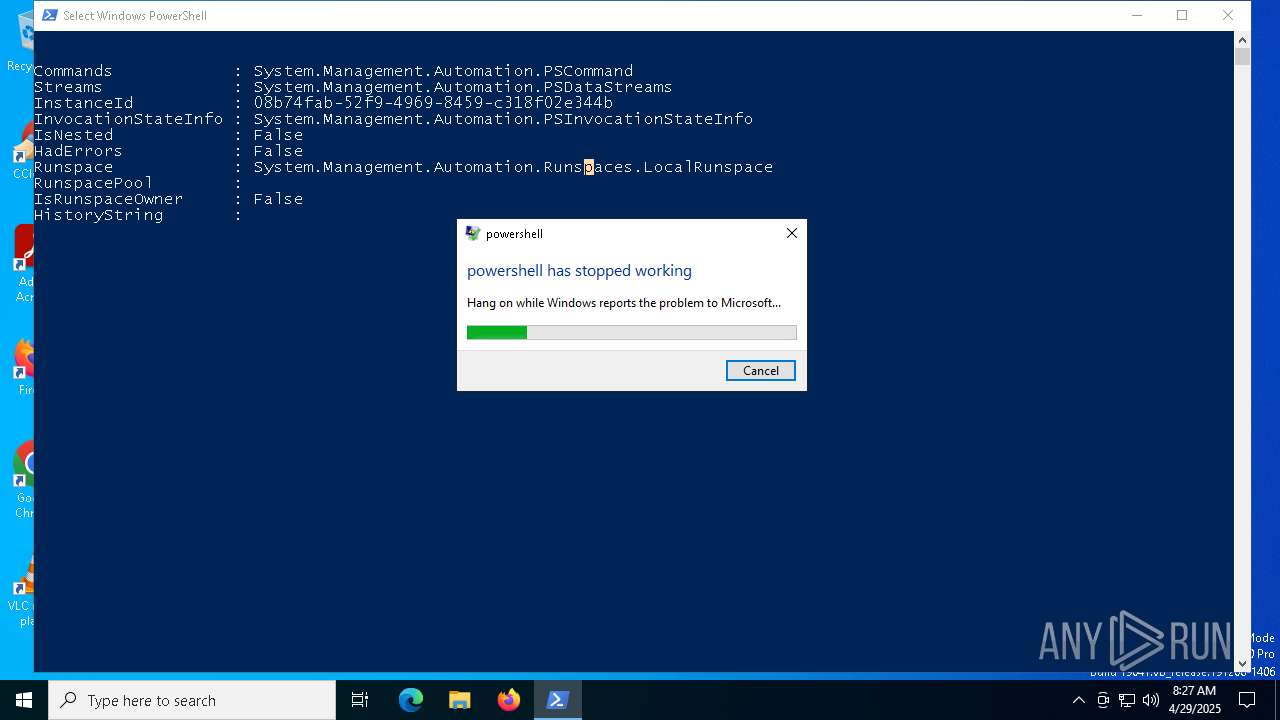
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 7540)
SUSPICIOUS
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7540)
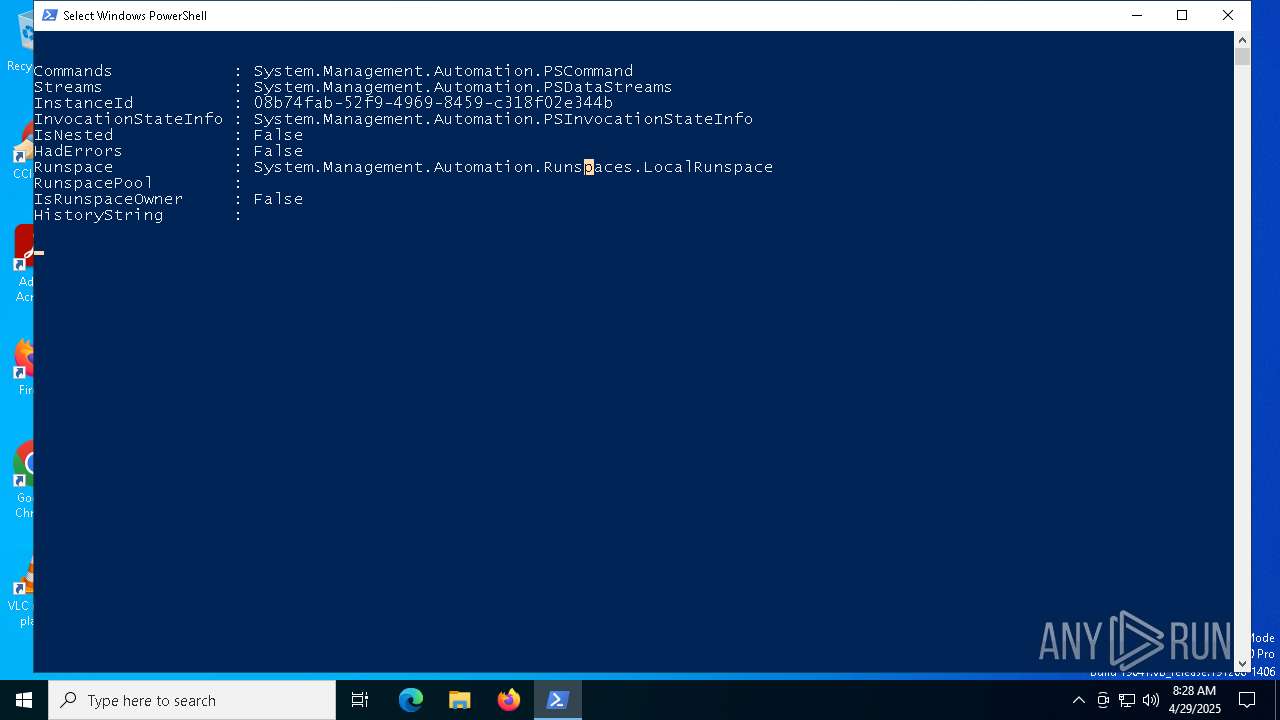
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 7540)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 7540)
Connects to the server without a host name
- powershell.exe (PID: 7540)
CSC.EXE is used to compile C# code
- csc.exe (PID: 8172)
Executable content was dropped or overwritten
- csc.exe (PID: 8172)
Reverses array data (POWERSHELL)
- powershell.exe (PID: 7540)
The process creates files with name similar to system file names
- wermgr.exe (PID: 7152)
INFO
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 7540)
Disables trace logs
- powershell.exe (PID: 7540)
Checks proxy server information
- powershell.exe (PID: 7540)
- wermgr.exe (PID: 7152)
Checks supported languages
- csc.exe (PID: 8172)
- cvtres.exe (PID: 5024)
Reads the machine GUID from the registry
- csc.exe (PID: 8172)
Create files in a temporary directory
- cvtres.exe (PID: 5024)
- csc.exe (PID: 8172)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 7540)
Potential library load (Base64 Encoded 'LoadLibrary')
- powershell.exe (PID: 7540)
Potential access to remote process (Base64 Encoded 'OpenProcess')
- powershell.exe (PID: 7540)
Potential dynamic function import (Base64 Encoded 'GetProcAddress')
- powershell.exe (PID: 7540)
Creates files in the program directory
- powershell.exe (PID: 7540)
Creates files or folders in the user directory
- wermgr.exe (PID: 7152)
Reads the software policy settings
- wermgr.exe (PID: 7152)
- slui.exe (PID: 7748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
137
Monitored processes
8
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1056 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5024 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESE8BC.tmp" "c:\Users\admin\AppData\Local\Temp\CSC5F55D4F95A984BE0BFA36B532F4DD11B.TMP" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.32.31326.0 Modules
| |||||||||||||||
| 7152 | "C:\WINDOWS\system32\wermgr.exe" "-outproc" "0" "7540" "3248" "3184" "3252" "0" "0" "3256" "0" "0" "0" "0" "0" | C:\Windows\System32\wermgr.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7540 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass C:\Users\admin\AppData\Local\Temp\Windows.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7548 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7704 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7748 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8172 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\jd52p1r4.cmdline" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
Total events
10 543
Read events
10 543
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
10
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7152 | wermgr.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\Critical_powershell.exe_d52d907383af593b633a47addd4b79917e9947_00000000_d971cb1b-ca72-48c9-8605-8b5e0400117a\Report.wer | — | |
MD5:— | SHA256:— | |||
| 7540 | powershell.exe | C:\Users\admin\AppData\Local\Temp\jd52p1r4.0.cs | text | |
MD5:16A930769B13E3C78E998BBCEEEBB869 | SHA256:E2A6D7843CDEAA984ED650C9E8F7698CA11D8C2C055A8D1B20F358ABB60D2ABA | |||
| 7540 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_koom02e4.03e.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7540 | powershell.exe | C:\Users\admin\AppData\Local\Temp\jd52p1r4.cmdline | text | |
MD5:C84477886EBAD16C24118C54BE56B96D | SHA256:6E32427C57E9E8430F9C3AD78937F08BE5B9C88EF6D0B2BDE69B215FDC0FDAE6 | |||
| 5024 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RESE8BC.tmp | binary | |
MD5:C401360C5400422584CBE172ACE12D7E | SHA256:5D74FA27B545D33BD9C32FE98A0AABEFD48FB88C4F584E0DE04D0362F7F8F9E7 | |||
| 7540 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\A2D9XYAW94GBVKEVNPZX.temp | binary | |
MD5:91C2239ED26C2052DDBAC3DCE1A75133 | SHA256:A791C19D2284E0D678F3877DA3F2BC26B0BA7822CA452ED041493AB06FA6E122 | |||
| 7540 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:91C2239ED26C2052DDBAC3DCE1A75133 | SHA256:A791C19D2284E0D678F3877DA3F2BC26B0BA7822CA452ED041493AB06FA6E122 | |||
| 7540 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF10b807.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 7152 | wermgr.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERED12.tmp.xml | xml | |
MD5:E804AC06AE81D7189B79276E7CA8AAD3 | SHA256:348496587B71AD283B36048BF1AB0C694235183E408CC5CAFFB504BCF13B07A4 | |||
| 7152 | wermgr.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\37C951188967C8EB88D99893D9D191FE | binary | |
MD5:3B5E0BD6640456A749D9155E6C135727 | SHA256:C362A3D2B661C6066A02FC169FAAA1976C2F6160DA5837C7E68B7E0F67B794ED | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
27
DNS requests
17
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.25:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7540 | powershell.exe | GET | 200 | 45.15.162.16:80 | http://45.15.162.16/System.txt | unknown | — | — | malicious |
7152 | wermgr.exe | GET | 200 | 23.216.77.25:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7152 | wermgr.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7296 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7296 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.25:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.32.72:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
2112 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
watson.events.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7540 | powershell.exe | A Network Trojan was detected | ET MALWARE Windows executable base64 encoded |
7540 | powershell.exe | Misc activity | ET HUNTING EXE Base64 Encoded potential malware |