| File name: | 快码专业短信平台_V2.3.3.exe |
| Full analysis: | https://app.any.run/tasks/1c20b5f4-0f9a-4481-b0d5-a6813bca926a |
| Verdict: | Malicious activity |
| Analysis date: | October 28, 2019, 12:42:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 9F6220D24A3DB7306599F538FA9B50D1 |
| SHA1: | A00F7BB46BE4D9F9EB79C775DADE4C98CB3B30FE |
| SHA256: | D3ADC2C6F44B38CAD77C164310DE367274081C2B1E8EE6A3E46DDF0EC3D95649 |
| SSDEEP: | 393216:Tmmt/x6eUnHO8N4Z2T8egT0NjfMkyHfIS:Lx6juN48rTcTHCIS |
MALICIOUS
Loads dropped or rewritten executable
- setup_wid_boss@foreign.exe (PID: 3784)
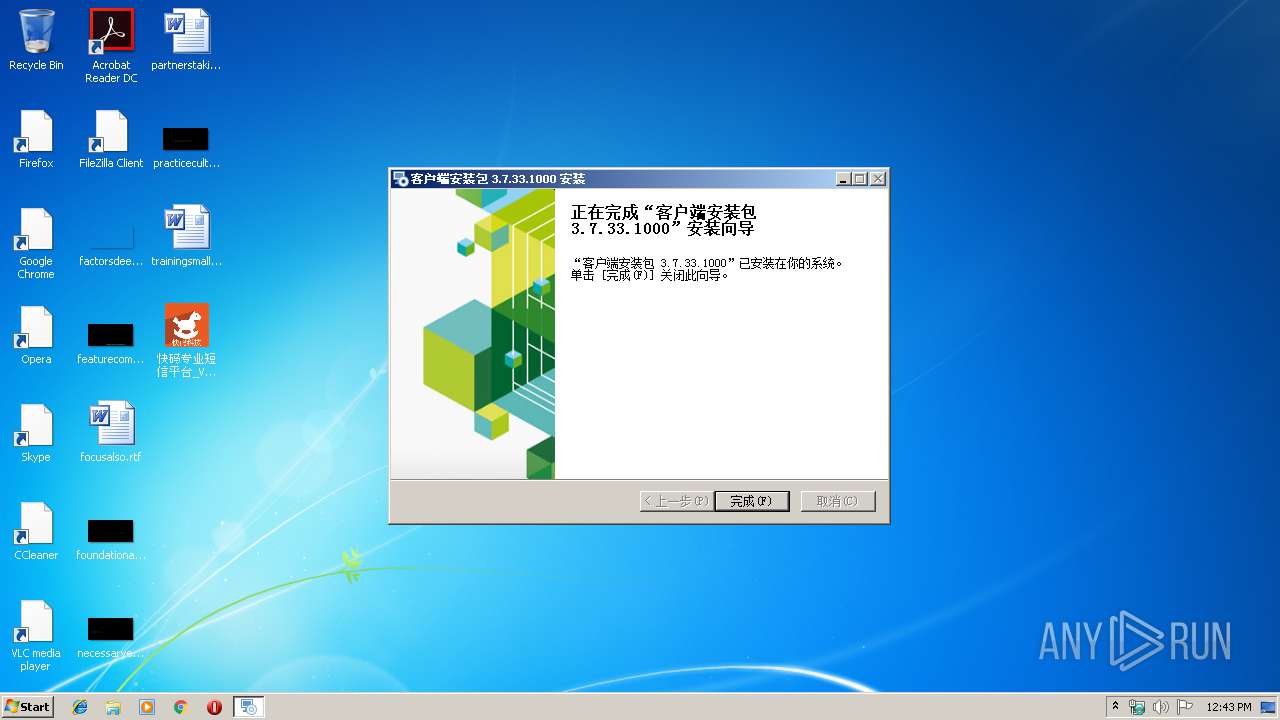
- NSecRTS.exe (PID: 3316)
- NSecRTS.exe (PID: 1584)
- explorer.exe (PID: 352)
- regsvr32.exe (PID: 3136)
- Fixit.exe (PID: 1784)
Application was dropped or rewritten from another process
- setup_wid_boss@foreign.exe (PID: 3784)
- NSecRTS.exe (PID: 1584)
- Fixit.exe (PID: 1784)
- NSecRTS.exe (PID: 3316)
- NSecRTS.exe (PID: 3832)
- NSec.exe (PID: 3788)
- instrap.exe (PID: 2644)
- nsF308.tmp (PID: 584)
Changes the autorun value in the registry
- rundll32.exe (PID: 4000)
Registers / Runs the DLL via REGSVR32.EXE
- NSecRTS.exe (PID: 3316)
SUSPICIOUS
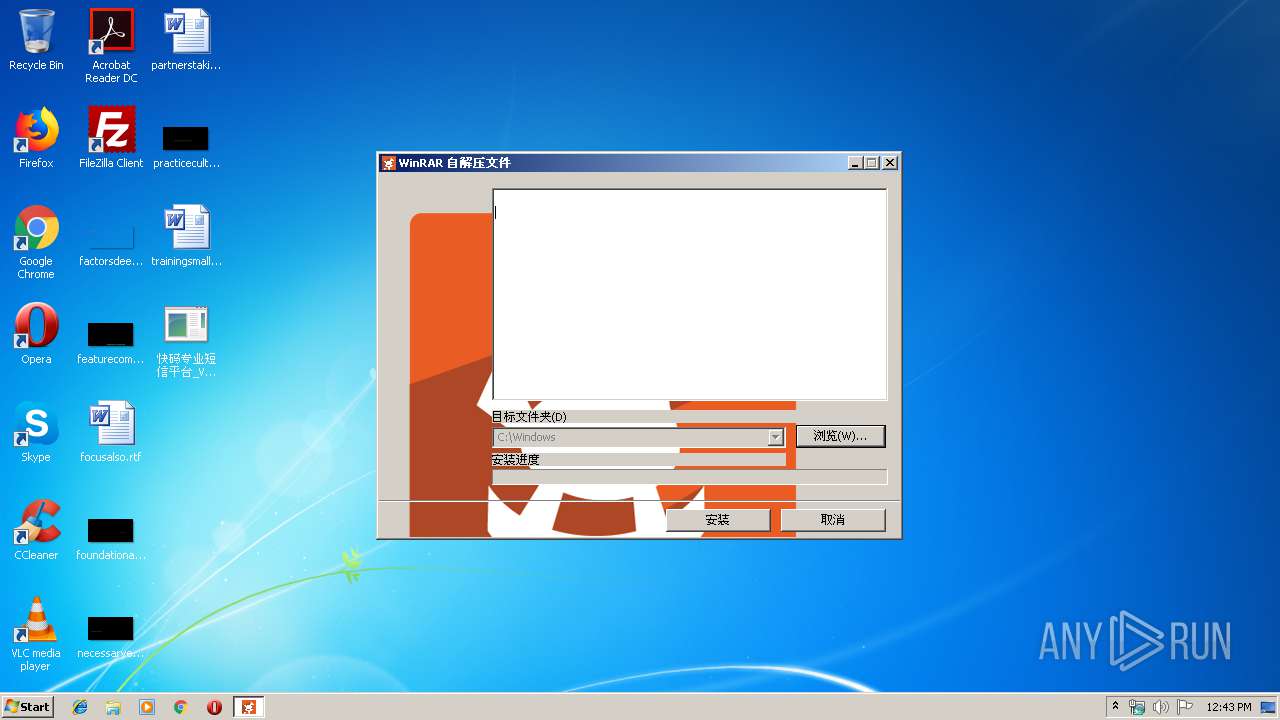
Creates files in the Windows directory
- 快码专业短信平台_V2.3.3.exe (PID: 3980)
- rundll32.exe (PID: 4000)
- NSecRTS.exe (PID: 3316)
Application launched itself
- 快码专业短信平台_V2.3.3.exe (PID: 1096)
Uses RUNDLL32.EXE to load library
- NSecRTS.exe (PID: 1584)
Executable content was dropped or overwritten
- 快码专业短信平台_V2.3.3.exe (PID: 3980)
- rundll32.exe (PID: 4000)
- NSecRTS.exe (PID: 1584)
- setup_wid_boss@foreign.exe (PID: 3784)
- NSecRTS.exe (PID: 3316)
Starts application with an unusual extension
- setup_wid_boss@foreign.exe (PID: 3784)
Executed as Windows Service
- NSecRTS.exe (PID: 3316)
Removes files from Windows directory
- rundll32.exe (PID: 4000)
Creates files in the driver directory
- rundll32.exe (PID: 4000)
- NSecRTS.exe (PID: 3316)
Creates or modifies windows services
- rundll32.exe (PID: 4000)
Creates files in the program directory
- NSecRTS.exe (PID: 3316)
- NSecRTS.exe (PID: 1584)
- setup_wid_boss@foreign.exe (PID: 3784)
Creates COM task schedule object
- regsvr32.exe (PID: 3136)
INFO
Dropped object may contain Bitcoin addresses
- setup_wid_boss@foreign.exe (PID: 3784)
- NSecRTS.exe (PID: 1584)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:04:27 22:03:27+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 190976 |
| InitializedDataSize: | 1006080 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1d759 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-Apr-2019 20:03:27 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 27-Apr-2019 20:03:27 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002E854 | 0x0002EA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.69231 |
.rdata | 0x00030000 | 0x00009A9C | 0x00009C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.13286 |
.data | 0x0003A000 | 0x000213D0 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.25381 |
.gfids | 0x0005C000 | 0x000000E8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.11154 |
.rsrc | 0x0005D000 | 0x000E8E64 | 0x000E9000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.52396 |
.reloc | 0x00146000 | 0x00001FCC | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.64554 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25329 | 1875 | Latin 1 / Western European | Chinese - PRC | RT_MANIFEST |
7 | 5.24197 | 182 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
8 | 5.27357 | 214 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
9 | 5.38938 | 202 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
10 | 5.11103 | 116 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
11 | 5.36199 | 642 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
12 | 4.71863 | 148 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
13 | 4.78806 | 120 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
14 | 4.39475 | 124 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
15 | 4.33363 | 82 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
Imports
KERNEL32.dll |
USER32.dll (delay-loaded) |
gdiplus.dll |
Total processes
54
Monitored processes
15
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 584 | "C:\Users\admin\AppData\Local\Temp\nskD1C4.tmp\nsF308.tmp" "C:\Program Files\Common Files\NSEC\NSec.exe" -ip | C:\Users\admin\AppData\Local\Temp\nskD1C4.tmp\nsF308.tmp | — | setup_wid_boss@foreign.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1096 | "C:\Users\admin\Desktop\快码专业短信平台_V2.3.3.exe" | C:\Users\admin\Desktop\快码专业短信平台_V2.3.3.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
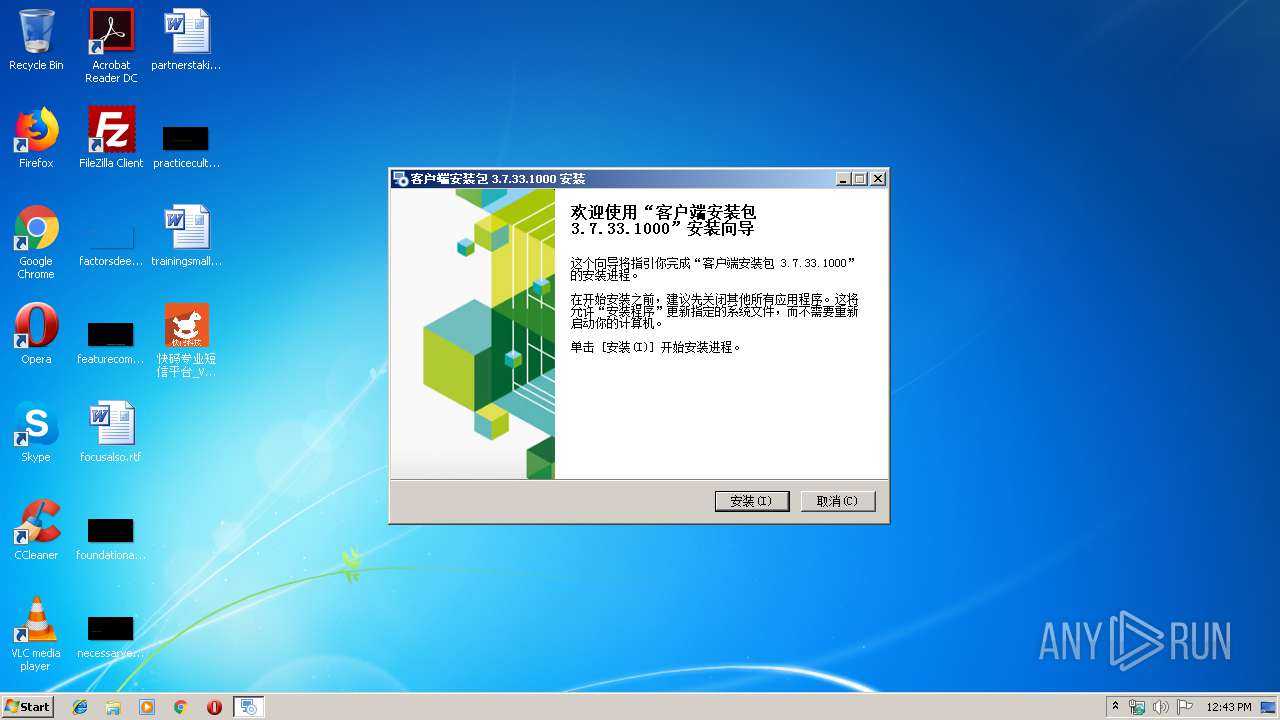
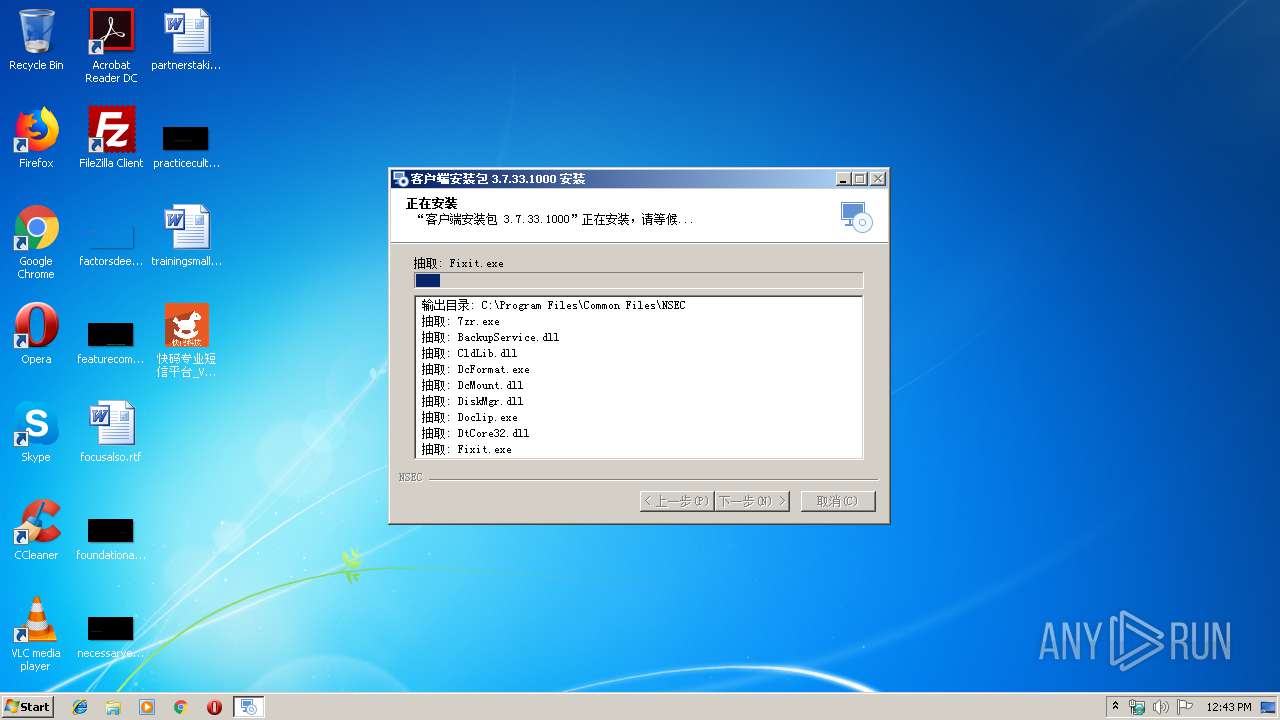
| 1584 | "C:\Program Files\Common Files\NSEC\NSecRTS.exe" | C:\Program Files\Common Files\NSEC\NSecRTS.exe | instrap.exe | ||||||||||||
User: admin Company: NSEC Co.,Ltd Integrity Level: HIGH Description: Endpoint Protection & DLP Real-time Service Exit code: 0 Version: 3.7.33.4256 Modules
| |||||||||||||||
| 1784 | "C:\Program Files\Common Files\NSEC\Fixit.exe" -df | C:\Program Files\Common Files\NSEC\Fixit.exe | — | NSecRTS.exe | |||||||||||
User: SYSTEM Company: NSEC Co.,Ltd Integrity Level: SYSTEM Description: Install Update Fix Exit code: 0 Version: 3.7.30.4180 Modules
| |||||||||||||||
| 2340 | "C:\Windows\system32\runonce.exe" -r | C:\Windows\system32\runonce.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Run Once Wrapper Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2416 | "C:\Windows\System32\grpconv.exe" -o | C:\Windows\System32\grpconv.exe | — | runonce.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Progman Group Converter Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2644 | "C:\Program Files\Common Files\NSEC\instrap.exe" | C:\Program Files\Common Files\NSEC\instrap.exe | — | setup_wid_boss@foreign.exe | |||||||||||
User: admin Company: NSEC Co.,Ltd Integrity Level: HIGH Description: Install Trap Exit code: 0 Version: 3.7.23.3484 Modules
| |||||||||||||||
| 3136 | C:\Windows\system32\regsvr32.exe /s "C:\Program Files\Microsoft Research\NSEC\NShellExt32.dll" | C:\Windows\system32\regsvr32.exe | — | NSecRTS.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3316 | "C:\Program Files\Common Files\NSEC\NSecRTS.exe" -r | C:\Program Files\Common Files\NSEC\NSecRTS.exe | services.exe | ||||||||||||
User: SYSTEM Company: NSEC Co.,Ltd Integrity Level: SYSTEM Description: Endpoint Protection & DLP Real-time Service Exit code: 0 Version: 3.7.33.4256 Modules
| |||||||||||||||
Total events
1 241
Read events
1 100
Write events
140
Delete events
1
Modification events
| (PID) Process: | (1096) 快码专业短信平台_V2.3.3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1096) 快码专业短信平台_V2.3.3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | P:\Hfref\nqzva\Qrfxgbc\快码专业短信平台_I2.3.3.rkr |
Value: 000000000000000000000000E6060000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000003200000037000000FEDE1200090000000D000000CC19050033003000380030003400360042003000410046003400410033003900430042000000460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E006500780065000000740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C0049006E007400650072006E006500740020004500780070006C006F007200650072005C0051007500690063006B0020004C00610075006E00630068005C0055007300650072002000500069006E006E006500000000000034FF01F832FF01D4E3E1013DA94A7600000000FBFFFF7FF8E3E101987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000534275066D42750653427506000000000000000000000000080000002E006C00E72F0A77A48EF37600000000AC032E0000002E00E72F0A77B08EF37603005B019604010000002E005B148D23020000006CE4E101B07F0A7744E5E1010000000058005A0044E5E1010200000010E5E101F2700A7791830A771C8FF37611000000B8453100B045310078192F00F8FD580600E500008F148D23B0E4E10182914A7600E5E101B4E4E10127954A7600000000CC90FF01DCE4E101CD944A76CC90FF0188E5E101408CFF01E1944A7600000000408CFF0188E5E101E4E4E101090000000D000000CC19050033003000380030003400360042003000410046003400410033003900430042000000460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E006500780065000000740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C0049006E007400650072006E006500740020004500780070006C006F007200650072005C0051007500690063006B0020004C00610075006E00630068005C0055007300650072002000500069006E006E006500000000000034FF01F832FF01D4E3E1013DA94A7600000000FBFFFF7FF8E3E101987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000534275066D42750653427506000000000000000000000000080000002E006C00E72F0A77A48EF37600000000AC032E0000002E00E72F0A77B08EF37603005B019604010000002E005B148D23020000006CE4E101B07F0A7744E5E1010000000058005A0044E5E1010200000010E5E101F2700A7791830A771C8FF37611000000B8453100B045310078192F00F8FD580600E500008F148D23B0E4E10182914A7600E5E101B4E4E10127954A7600000000CC90FF01DCE4E101CD944A76CC90FF0188E5E101408CFF01E1944A7600000000408CFF0188E5E101E4E4E101090000000D000000CC19050033003000380030003400360042003000410046003400410033003900430042000000460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E006500780065000000740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C0049006E007400650072006E006500740020004500780070006C006F007200650072005C0051007500690063006B0020004C00610075006E00630068005C0055007300650072002000500069006E006E006500000000000034FF01F832FF01D4E3E1013DA94A7600000000FBFFFF7FF8E3E101987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000534275066D42750653427506000000000000000000000000080000002E006C00E72F0A77A48EF37600000000AC032E0000002E00E72F0A77B08EF37603005B019604010000002E005B148D23020000006CE4E101B07F0A7744E5E1010000000058005A0044E5E1010200000010E5E101F2700A7791830A771C8FF37611000000B8453100B045310078192F00F8FD580600E500008F148D23B0E4E10182914A7600E5E101B4E4E10127954A7600000000CC90FF01DCE4E101CD944A76CC90FF0188E5E101408CFF01E1944A7600000000408CFF0188E5E101E4E4E101 | |||
| (PID) Process: | (3980) 快码专业短信平台_V2.3.3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3980) 快码专业短信平台_V2.3.3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | P:\Hfref\nqzva\Qrfxgbc\快码专业短信平台_I2.3.3.rkr |
Value: 00000000000000000000000028090000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 00000000320000003700000040E11200090000000D000000CC19050033003000380030003400360042003000410046003400410033003900430042000000460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E006500780065000000740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C0049006E007400650072006E006500740020004500780070006C006F007200650072005C0051007500690063006B0020004C00610075006E00630068005C0055007300650072002000500069006E006E006500000000000034FF01F832FF01D4E3E1013DA94A7600000000FBFFFF7FF8E3E101987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000534275066D42750653427506000000000000000000000000080000002E006C00E72F0A77A48EF37600000000AC032E0000002E00E72F0A77B08EF37603005B019604010000002E005B148D23020000006CE4E101B07F0A7744E5E1010000000058005A0044E5E1010200000010E5E101F2700A7791830A771C8FF37611000000B8453100B045310078192F00F8FD580600E500008F148D23B0E4E10182914A7600E5E101B4E4E10127954A7600000000CC90FF01DCE4E101CD944A76CC90FF0188E5E101408CFF01E1944A7600000000408CFF0188E5E101E4E4E101090000000D000000CC19050033003000380030003400360042003000410046003400410033003900430042000000460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E006500780065000000740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C0049006E007400650072006E006500740020004500780070006C006F007200650072005C0051007500690063006B0020004C00610075006E00630068005C0055007300650072002000500069006E006E006500000000000034FF01F832FF01D4E3E1013DA94A7600000000FBFFFF7FF8E3E101987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000534275066D42750653427506000000000000000000000000080000002E006C00E72F0A77A48EF37600000000AC032E0000002E00E72F0A77B08EF37603005B019604010000002E005B148D23020000006CE4E101B07F0A7744E5E1010000000058005A0044E5E1010200000010E5E101F2700A7791830A771C8FF37611000000B8453100B045310078192F00F8FD580600E500008F148D23B0E4E10182914A7600E5E101B4E4E10127954A7600000000CC90FF01DCE4E101CD944A76CC90FF0188E5E101408CFF01E1944A7600000000408CFF0188E5E101E4E4E101090000000D000000CC19050033003000380030003400360042003000410046003400410033003900430042000000460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E006500780065000000740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C0049006E007400650072006E006500740020004500780070006C006F007200650072005C0051007500690063006B0020004C00610075006E00630068005C0055007300650072002000500069006E006E006500000000000034FF01F832FF01D4E3E1013DA94A7600000000FBFFFF7FF8E3E101987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000534275066D42750653427506000000000000000000000000080000002E006C00E72F0A77A48EF37600000000AC032E0000002E00E72F0A77B08EF37603005B019604010000002E005B148D23020000006CE4E101B07F0A7744E5E1010000000058005A0044E5E1010200000010E5E101F2700A7791830A771C8FF37611000000B8453100B045310078192F00F8FD580600E500008F148D23B0E4E10182914A7600E5E101B4E4E10127954A7600000000CC90FF01DCE4E101CD944A76CC90FF0188E5E101408CFF01E1944A7600000000408CFF0188E5E101E4E4E101 | |||
| (PID) Process: | (2644) instrap.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\NSecsoft\NSEC |
| Operation: | write | Name: | InstDir |
Value: C:\Program Files\Common Files\NSEC\ | |||
| (PID) Process: | (2644) instrap.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\NSecsoft\Debug |
| Operation: | write | Name: | LogUser |
Value: C:\NSEC\Debug\Log | |||
Executable files
152
Suspicious files
7
Text files
45
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3784 | setup_wid_boss@foreign.exe | C:\Users\admin\AppData\Local\Temp\nskD1C4.tmp\ioSpecial.ini | text | |
MD5:— | SHA256:— | |||
| 3784 | setup_wid_boss@foreign.exe | C:\Program Files\Common Files\NSEC\NSecRTS.exe | executable | |
MD5:— | SHA256:— | |||
| 3980 | 快码专业短信平台_V2.3.3.exe | C:\Windows\setup_wid_boss@foreign.exe | executable | |
MD5:— | SHA256:— | |||
| 3784 | setup_wid_boss@foreign.exe | C:\Program Files\Common Files\NSEC\DcMount.dll | executable | |
MD5:— | SHA256:— | |||
| 3784 | setup_wid_boss@foreign.exe | C:\Program Files\Common Files\NSEC\BackupService.dll | executable | |
MD5:— | SHA256:— | |||
| 3784 | setup_wid_boss@foreign.exe | C:\Program Files\Common Files\NSEC\CldLib.dll | executable | |
MD5:— | SHA256:— | |||
| 3784 | setup_wid_boss@foreign.exe | C:\Program Files\Common Files\NSEC\Doclip.exe | executable | |
MD5:— | SHA256:— | |||
| 3784 | setup_wid_boss@foreign.exe | C:\Program Files\Common Files\NSEC\NSec.exe | executable | |
MD5:— | SHA256:— | |||
| 3784 | setup_wid_boss@foreign.exe | C:\Program Files\Common Files\NSEC\DiskMgr.dll | executable | |
MD5:— | SHA256:— | |||
| 3784 | setup_wid_boss@foreign.exe | C:\Program Files\Common Files\NSEC\DtCore32.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3316 | NSecRTS.exe | GET | 200 | 182.254.157.201:8987 | http://cloud.nsecsoft.com:8987/ndns/boss@foreign | CN | text | 69 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3316 | NSecRTS.exe | 103.235.46.39:80 | www.baidu.com | Beijing Baidu Netcom Science and Technology Co., Ltd. | HK | unknown |
3316 | NSecRTS.exe | 182.254.157.201:8987 | cloud.nsecsoft.com | Shenzhen Tencent Computer Systems Company Limited | CN | unknown |
3316 | NSecRTS.exe | 47.56.9.126:28987 | — | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.baidu.com |
| whitelisted |
cloud.nsecsoft.com |
| unknown |