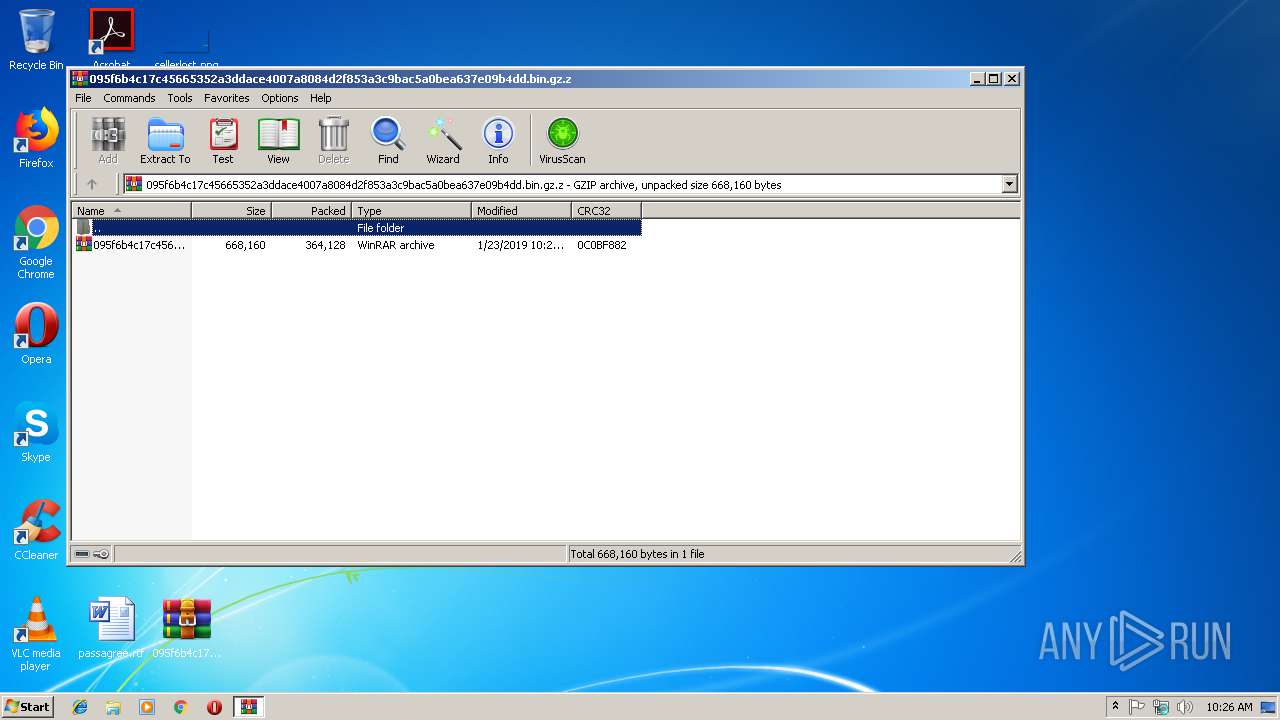
| File name: | 095f6b4c17c45665352a3ddace4007a8084d2f853a3c9bac5a0bea637e09b4dd.bin.gz |
| Full analysis: | https://app.any.run/tasks/da9f6474-9b9b-475a-aa29-f7ed2fc3ef29 |
| Verdict: | Malicious activity |
| Analysis date: | January 23, 2019, 10:25:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/gzip |
| File info: | gzip compressed data, max compression, from Unix |
| MD5: | 7685B3C15FEE72CDCB423507BADD3163 |
| SHA1: | 042396A21942F44FF8C753B7DD27FC4608199531 |
| SHA256: | D3A0250D58D22D78A2EA206F108AA3B515A865AEB81C4E85F5DADD282FD2DDB6 |
| SSDEEP: | 6144:Lw0k2zfcmfDeJOx4FYgTz5CPc3+OgAAUhD3R0dL1QetDNnI4Ya9n+vrWcP4REF:c0kM9fDAOgYgTtZ6UhD3RgLdI4zn+DtN |
MALICIOUS
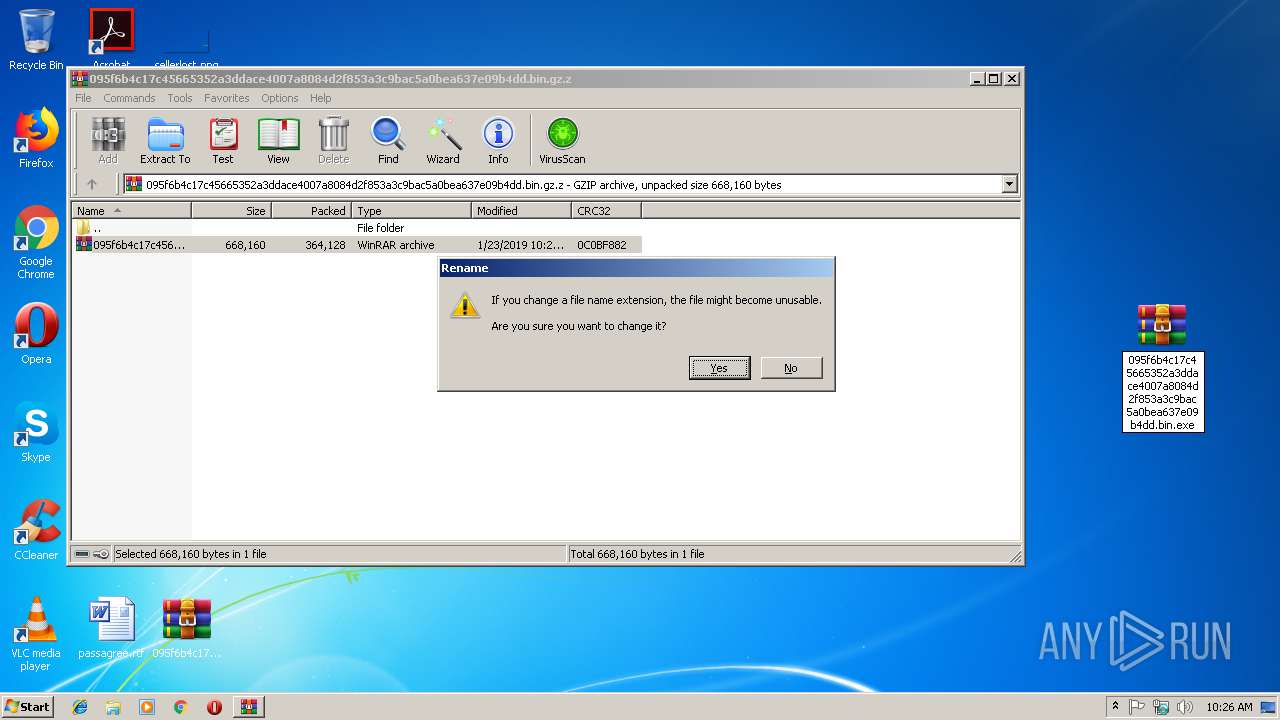
Application was dropped or rewritten from another process
- 095f6b4c17c45665352a3ddace4007a8084d2f853a3c9bac5a0bea637e09b4dd.bin.exe (PID: 3144)
- 095f6b4c17c45665352a3ddace4007a8084d2f853a3c9bac5a0bea637e09b4dd.bin.exe (PID: 3216)
SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .z/gz/gzip | | | GZipped data (100) |
|---|
EXIF
ZIP
| Compression: | Deflated |
|---|---|
| Flags: | (none) |
| ModifyDate: | 0000:00:00 00:00:00 |
| ExtraFlags: | Maximum Compression |
| OperatingSystem: | Unix |
Total processes
35
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
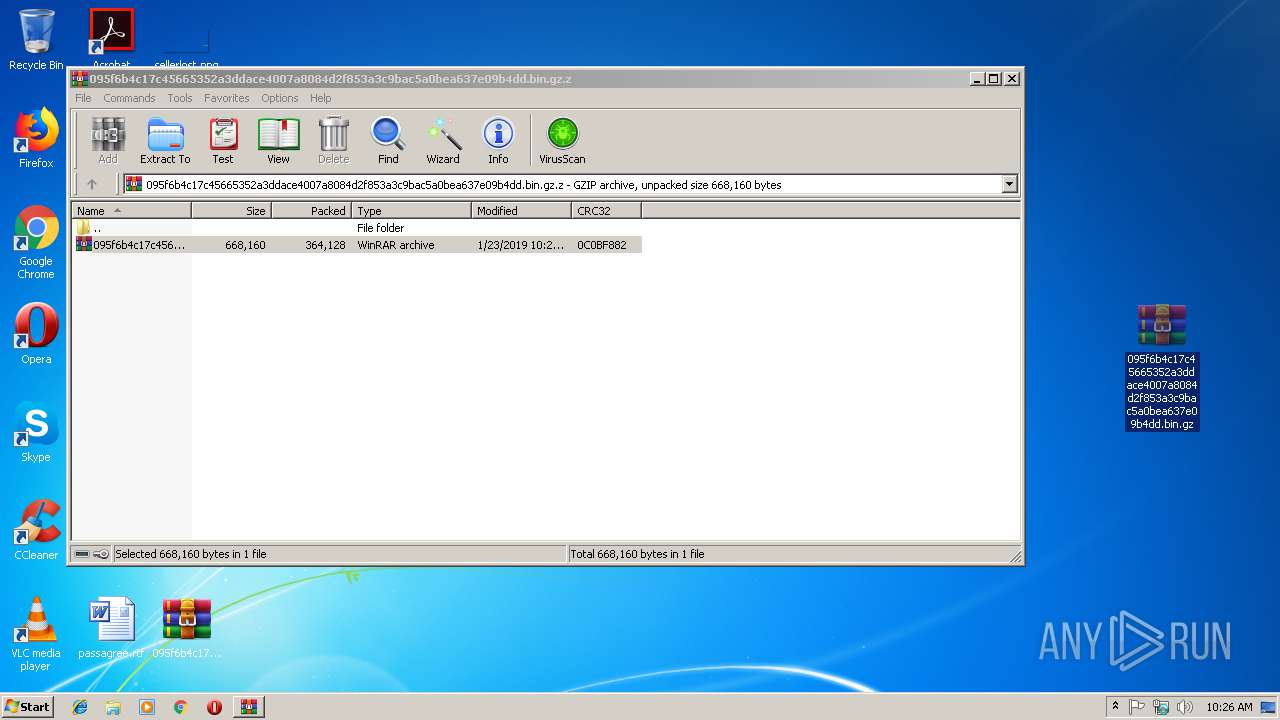
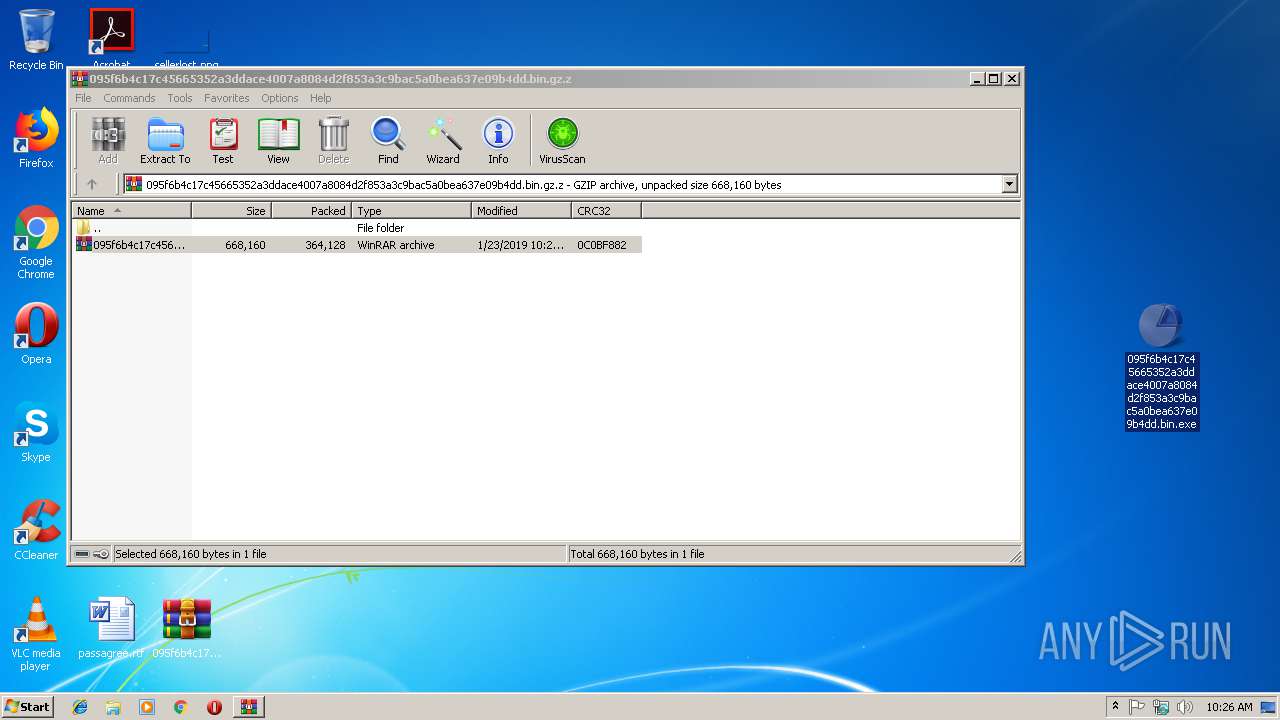
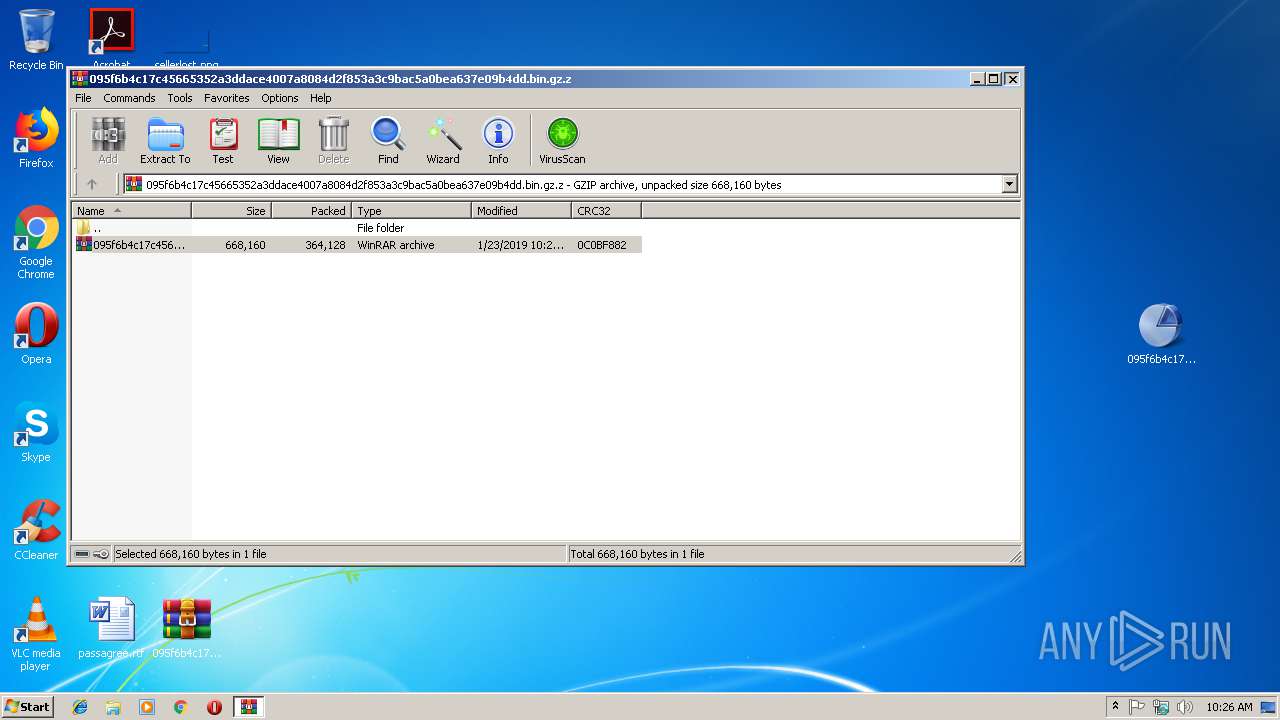
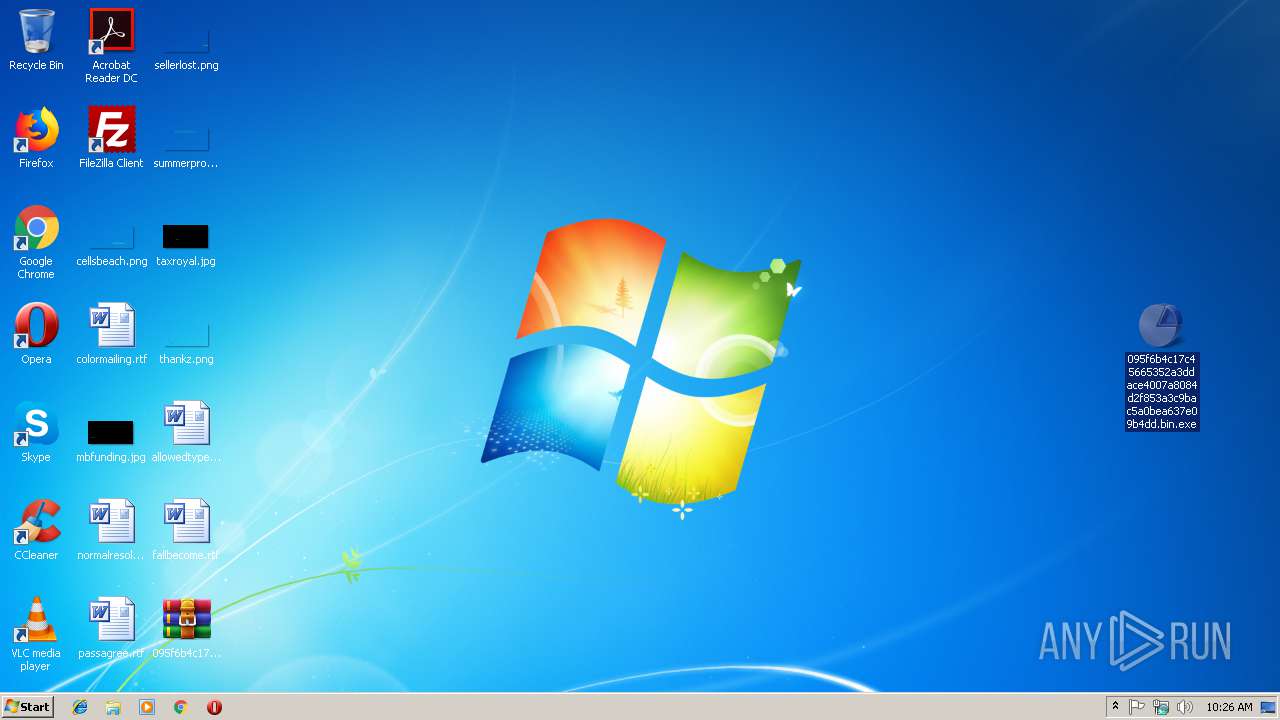
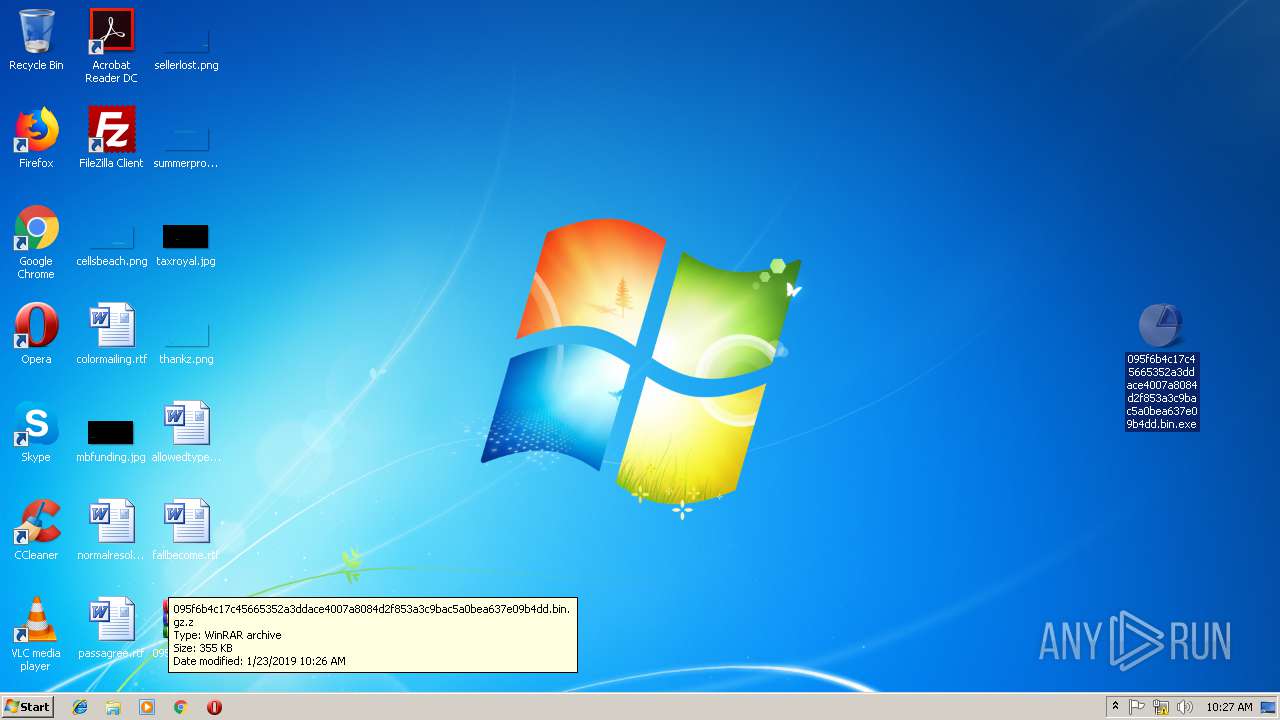
| 3056 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\095f6b4c17c45665352a3ddace4007a8084d2f853a3c9bac5a0bea637e09b4dd.bin.gz.z" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3144 | "C:\Users\admin\Desktop\095f6b4c17c45665352a3ddace4007a8084d2f853a3c9bac5a0bea637e09b4dd.bin.exe" | C:\Users\admin\Desktop\095f6b4c17c45665352a3ddace4007a8084d2f853a3c9bac5a0bea637e09b4dd.bin.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3216 | "C:\Users\admin\Desktop\095f6b4c17c45665352a3ddace4007a8084d2f853a3c9bac5a0bea637e09b4dd.bin.exe" | C:\Users\admin\Desktop\095f6b4c17c45665352a3ddace4007a8084d2f853a3c9bac5a0bea637e09b4dd.bin.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
323
Read events
304
Write events
19
Delete events
0
Modification events
| (PID) Process: | (3056) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3056) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3056) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3056) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\095f6b4c17c45665352a3ddace4007a8084d2f853a3c9bac5a0bea637e09b4dd.bin.gz.z | |||
| (PID) Process: | (3056) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3056) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3056) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3056) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3056) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (3056) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\Desktop | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3056 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3056.17734\095f6b4c17c45665352a3ddace4007a8084d2f853a3c9bac5a0bea637e09b4dd.bin.gz | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report