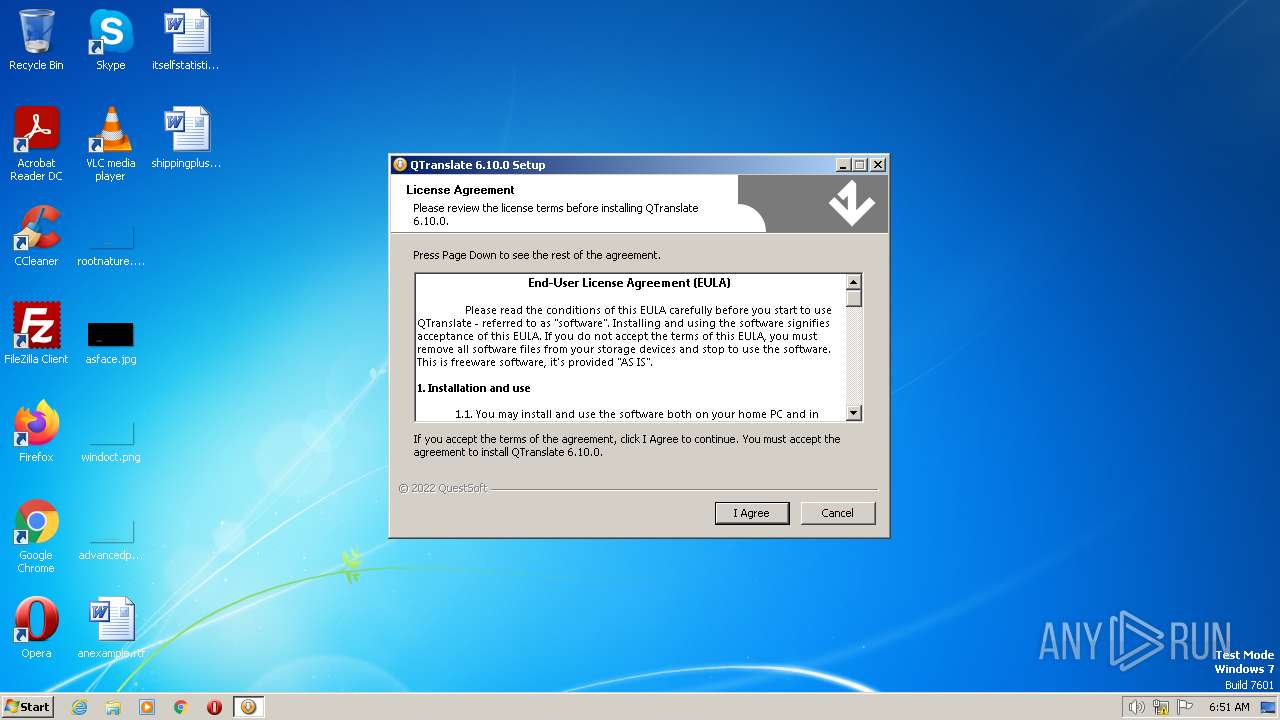
| File name: | Setup.exe |
| Full analysis: | https://app.any.run/tasks/2b9ddfda-6465-468a-800d-5bb67130b8b2 |
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2023, 05:51:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | E23FFECB44C814AAA4708D56AB5B144B |
| SHA1: | 202311D615685E7BAAA41DC149B5A76A69C05A0E |
| SHA256: | D395AF3C10E18C944CF8ADE76A650623DC23E050EAF652FF31056C84077A013C |
| SSDEEP: | 24576:GYnrVnqxCGl2NN5SSbyE3dJfz7oHf2qj2HHmR:bnRqMzlPNJfzfHg |
MALICIOUS
Loads dropped or rewritten executable
- Setup.exe (PID: 1348)
- QTranslate.exe (PID: 2708)
Application was dropped or rewritten from another process
- QTranslate.exe (PID: 2708)
SUSPICIOUS
Executable content was dropped or overwritten
- Setup.exe (PID: 1348)
Searches for installed software
- QTranslate.exe (PID: 2708)
The process creates files with name similar to system file names
- Setup.exe (PID: 1348)
Reads the Internet Settings
- QTranslate.exe (PID: 2708)
INFO
Reads the computer name
- Setup.exe (PID: 1348)
- QTranslate.exe (PID: 2708)
Creates files or folders in the user directory
- Setup.exe (PID: 1348)
Checks supported languages
- Setup.exe (PID: 1348)
- QTranslate.exe (PID: 2708)
The process checks LSA protection
- Setup.exe (PID: 1348)
- QTranslate.exe (PID: 2708)
Create files in a temporary directory
- Setup.exe (PID: 1348)
Creates files in the program directory
- Setup.exe (PID: 1348)
Reads the machine GUID from the registry
- QTranslate.exe (PID: 2708)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 4 |
| EntryPoint: | 0x3640 |
| UninitializedDataSize: | 2048 |
| InitializedDataSize: | 141824 |
| CodeSize: | 26624 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| TimeStamp: | 2021:09:25 21:56:47+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Sep-2021 21:56:47 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 25-Sep-2021 21:56:47 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006676 | 0x00006800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.41746 |
.rdata | 0x00008000 | 0x0000139A | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.14107 |
.data | 0x0000A000 | 0x00020378 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.11058 |
.ndata | 0x0002B000 | 0x00025000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00050000 | 0x00006F50 | 0x00007000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.78261 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.29667 | 1066 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.61959 | 4264 | UNKNOWN | English - United States | RT_ICON |
3 | 4.84061 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 6.16608 | 2216 | UNKNOWN | English - United States | RT_ICON |
5 | 3.91942 | 1640 | UNKNOWN | English - United States | RT_ICON |
6 | 5.42186 | 1384 | UNKNOWN | English - United States | RT_ICON |
7 | 5.58096 | 1128 | UNKNOWN | English - United States | RT_ICON |
8 | 3.74963 | 744 | UNKNOWN | English - United States | RT_ICON |
9 | 3.01957 | 296 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
42
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1348 | "C:\Users\admin\AppData\Local\Temp\Setup.exe" | C:\Users\admin\AppData\Local\Temp\Setup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2524 | "C:\Users\admin\AppData\Local\Temp\Setup.exe" | C:\Users\admin\AppData\Local\Temp\Setup.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
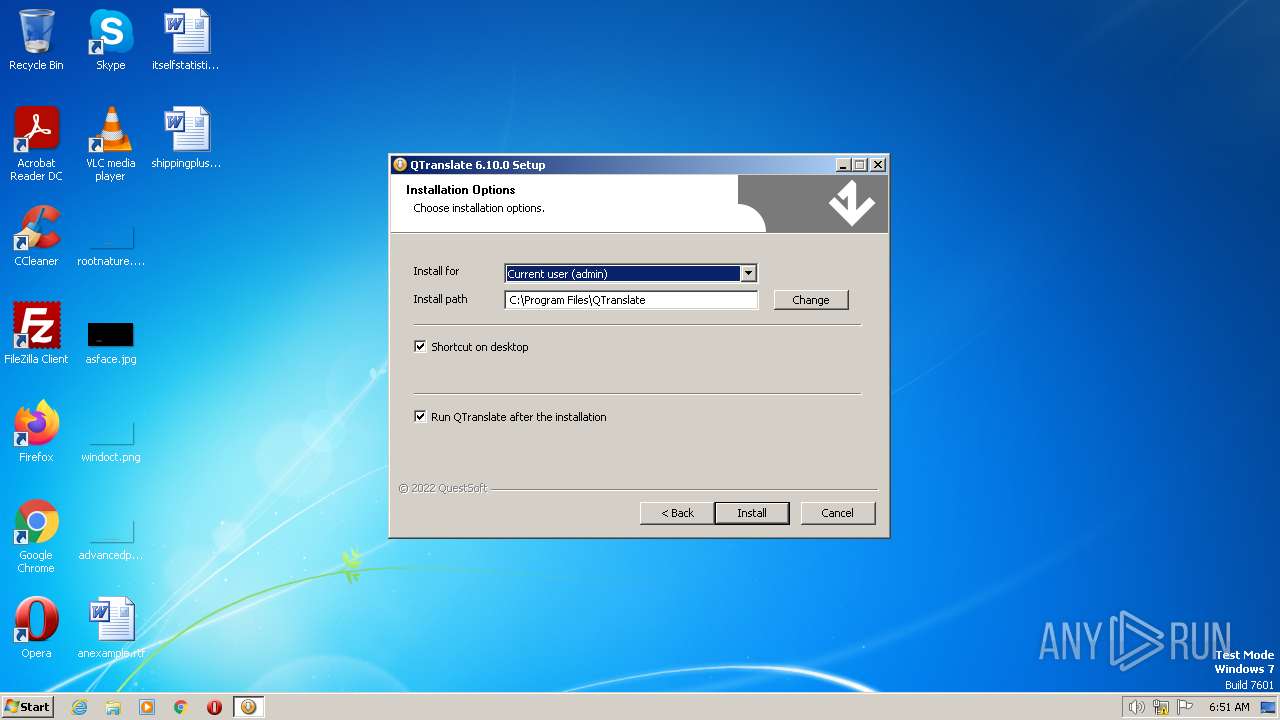
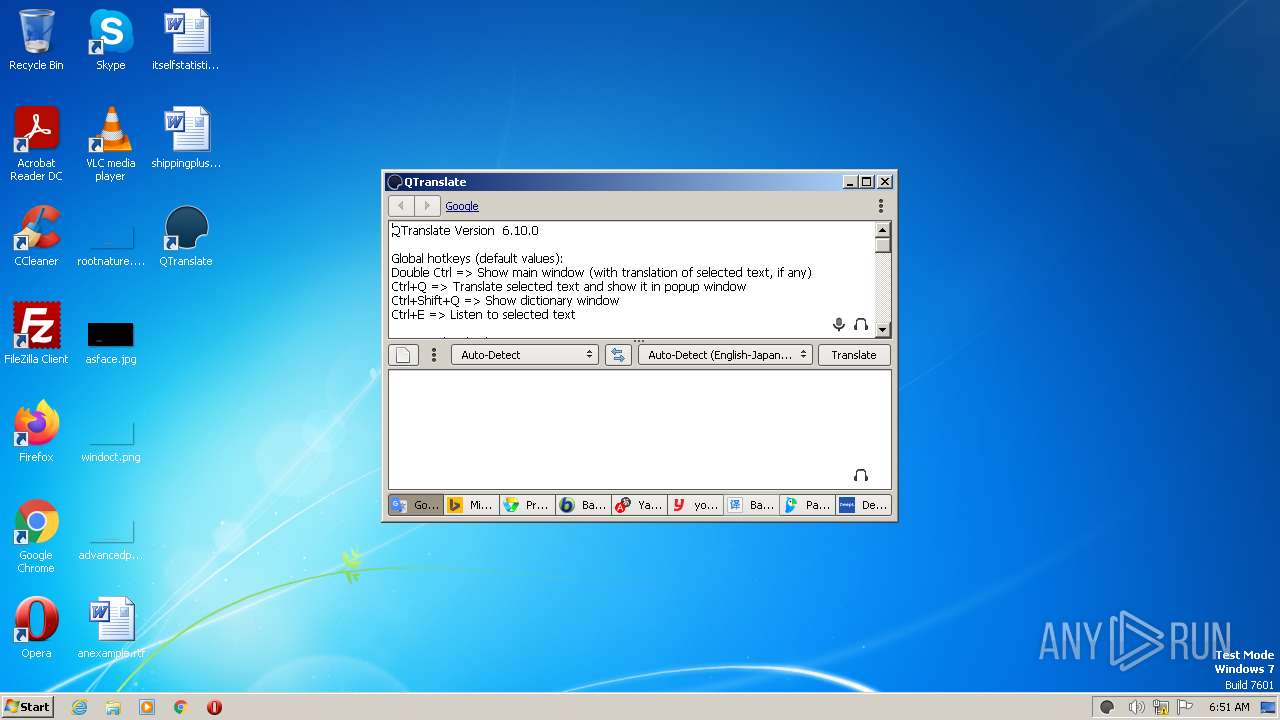
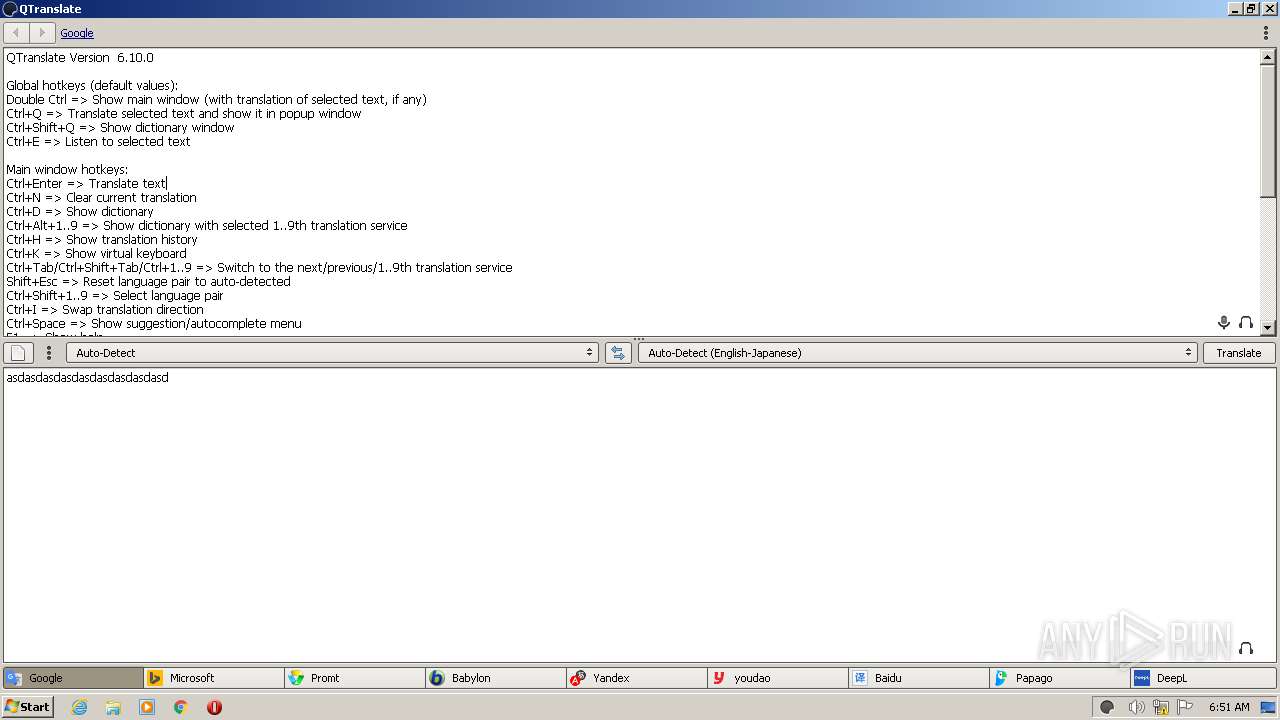
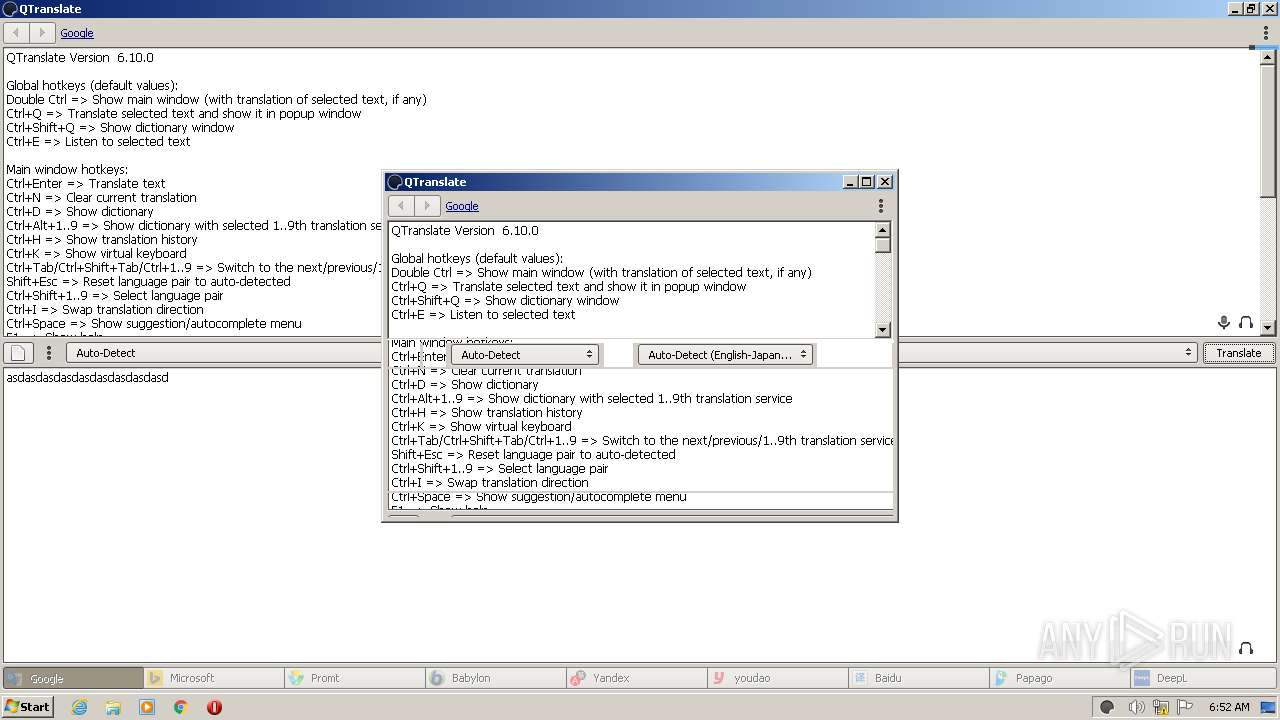
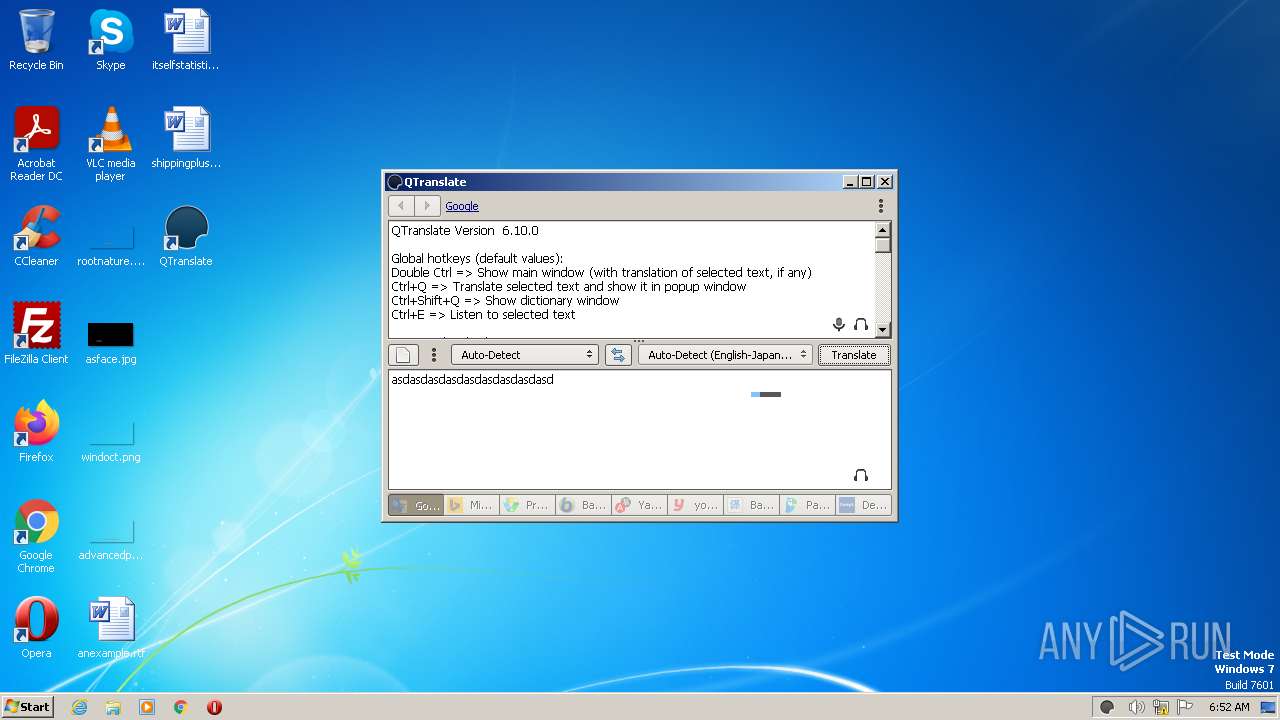
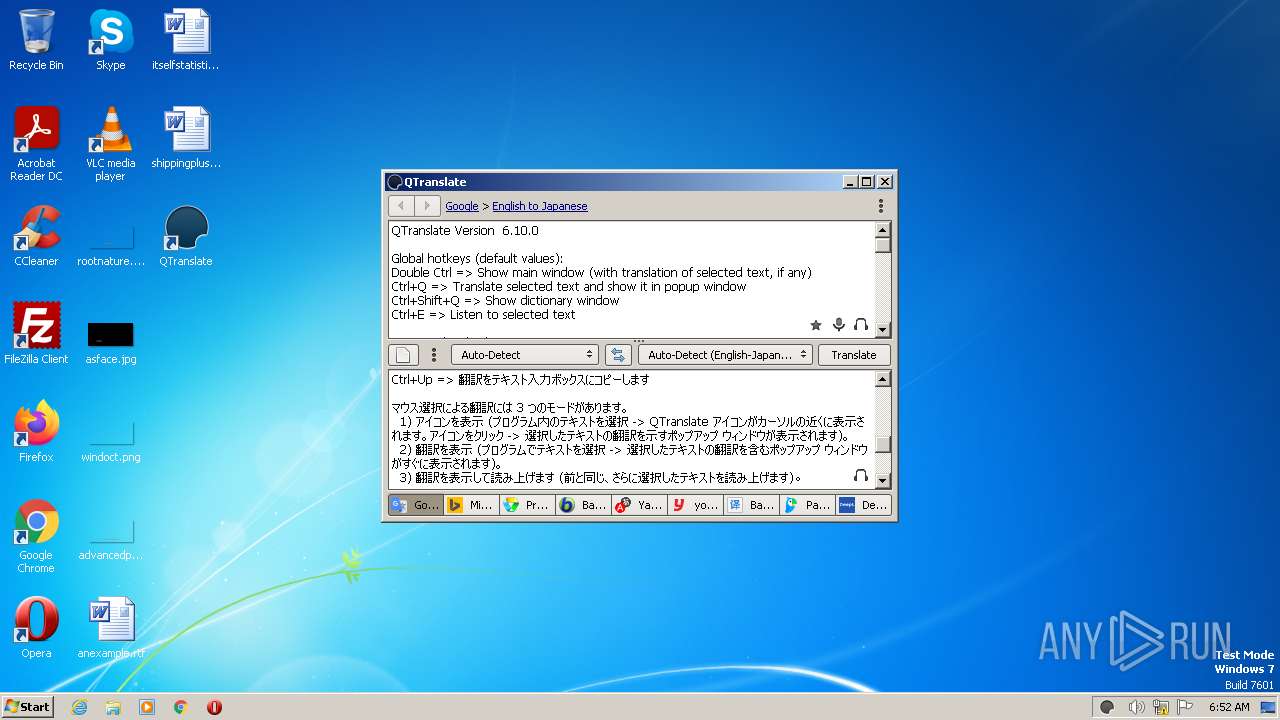
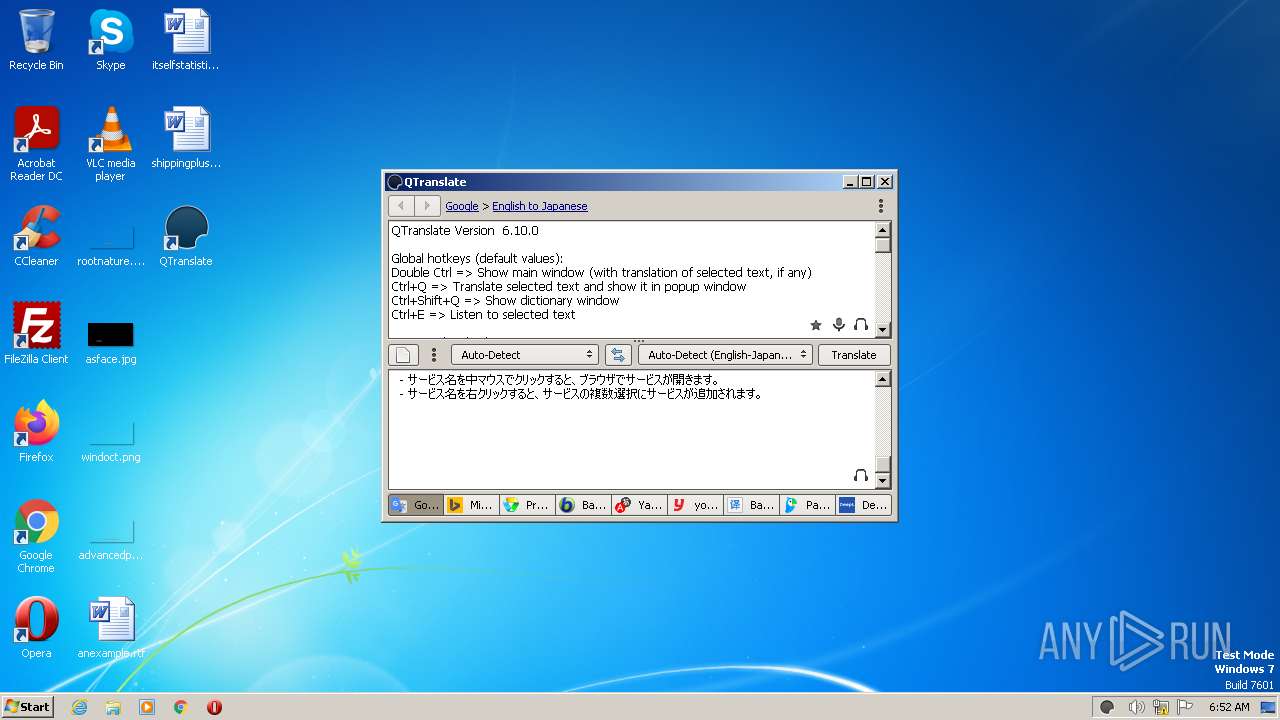
| 2708 | "C:\Program Files\QTranslate\QTranslate.exe" | C:\Program Files\QTranslate\QTranslate.exe | Setup.exe | ||||||||||||
User: admin Company: QuestSoft Integrity Level: HIGH Description: QTranslate Exit code: 0 Version: 6.10.0.0 Modules
| |||||||||||||||
Total events
1 194
Read events
1 194
Write events
0
Delete events
0
Modification events
Executable files
6
Suspicious files
8
Text files
119
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1348 | Setup.exe | C:\Program Files\QTranslate\Services\ABBYY Lingvo Live\Service.ico | image | |
MD5:199E649A59A9582A1EFE8D50DEF9CCB2 | SHA256:56D583D80ADAC1307B023E01E2B61FE06874511315E3618826DBC7694CD1A6AE | |||
| 1348 | Setup.exe | C:\Program Files\QTranslate\Services\Common.js | text | |
MD5:AC2A7401C01685C15B626963C7415687 | SHA256:A03D677A8B3788B5D97B31A33874D96719DC25E0F53087883964D20A878F8B93 | |||
| 1348 | Setup.exe | C:\Users\admin\AppData\Local\Temp\nsa75AC.tmp\nsDialogs.dll | executable | |
MD5:6C3F8C94D0727894D706940A8A980543 | SHA256:56B96ADD1978B1ABBA286F7F8982B0EFBE007D4A48B3DED6A4D408E01D753FE2 | |||
| 1348 | Setup.exe | C:\Users\admin\AppData\Local\Temp\nsa75AC.tmp\modern-header.bmp | image | |
MD5:FA91E636C40B029E183FD04932DCD35E | SHA256:7EC3906768AE3DEBB2FEB86F130AB78D0ED3BE1DD7A6DAD84362DF8C3ACF515C | |||
| 1348 | Setup.exe | C:\Users\admin\AppData\Local\Temp\nsa75AC.tmp\System.dll | executable | |
MD5:CFF85C549D536F651D4FB8387F1976F2 | SHA256:8DC562CDA7217A3A52DB898243DE3E2ED68B80E62DDCB8619545ED0B4E7F65A8 | |||
| 1348 | Setup.exe | C:\Program Files\QTranslate\Services\Babylon\Service.ico | image | |
MD5:E3128633E94A0C352375D0FFFC497052 | SHA256:47068C0E950F0EE240E38F2F0C3DCF305633B423D4D81FC522F5F2AF8A6AC79B | |||
| 1348 | Setup.exe | C:\Program Files\QTranslate\Services\Babylon Dictionary\Service.ico | image | |
MD5:E3128633E94A0C352375D0FFFC497052 | SHA256:47068C0E950F0EE240E38F2F0C3DCF305633B423D4D81FC522F5F2AF8A6AC79B | |||
| 1348 | Setup.exe | C:\Program Files\QTranslate\Services\Babylon Dictionary\Service.js | text | |
MD5:474F5269EAFCEC35B00F232CFF92DACD | SHA256:F406C6FB359820DC24BA74C60CCBDA85F191211320C3A62D2460A18E8220B900 | |||
| 1348 | Setup.exe | C:\Program Files\QTranslate\Services\ABBYY Lingvo Live\Service.js | html | |
MD5:CAD24AB28FF0A3050DD1B2F664562C4F | SHA256:4C0EF8506FF322CE78A29488B90E04F3DD16E55A5BF93E5DDEE0282F637D04E0 | |||
| 1348 | Setup.exe | C:\Program Files\QTranslate\Services\Babylon\Service.js | text | |
MD5:8595F4DEF5FB61F7D36EAE11568DF1B4 | SHA256:C12E825D73CBF78CE3BE414A3BBBD2CDF7FF9BB4AE1FA2CDA33C1BBF4947C324 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
8
DNS requests
3
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
568 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2708 | QTranslate.exe | 172.217.18.14:443 | consent.google.com | GOOGLE | US | whitelisted |
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2708 | QTranslate.exe | 172.217.16.142:443 | translate.google.com | GOOGLE | US | whitelisted |
2708 | QTranslate.exe | 213.180.204.29:80 | speller.yandex.net | YANDEX LLC | RU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
speller.yandex.net |
| whitelisted |
translate.google.com |
| whitelisted |
consent.google.com |
| shared |