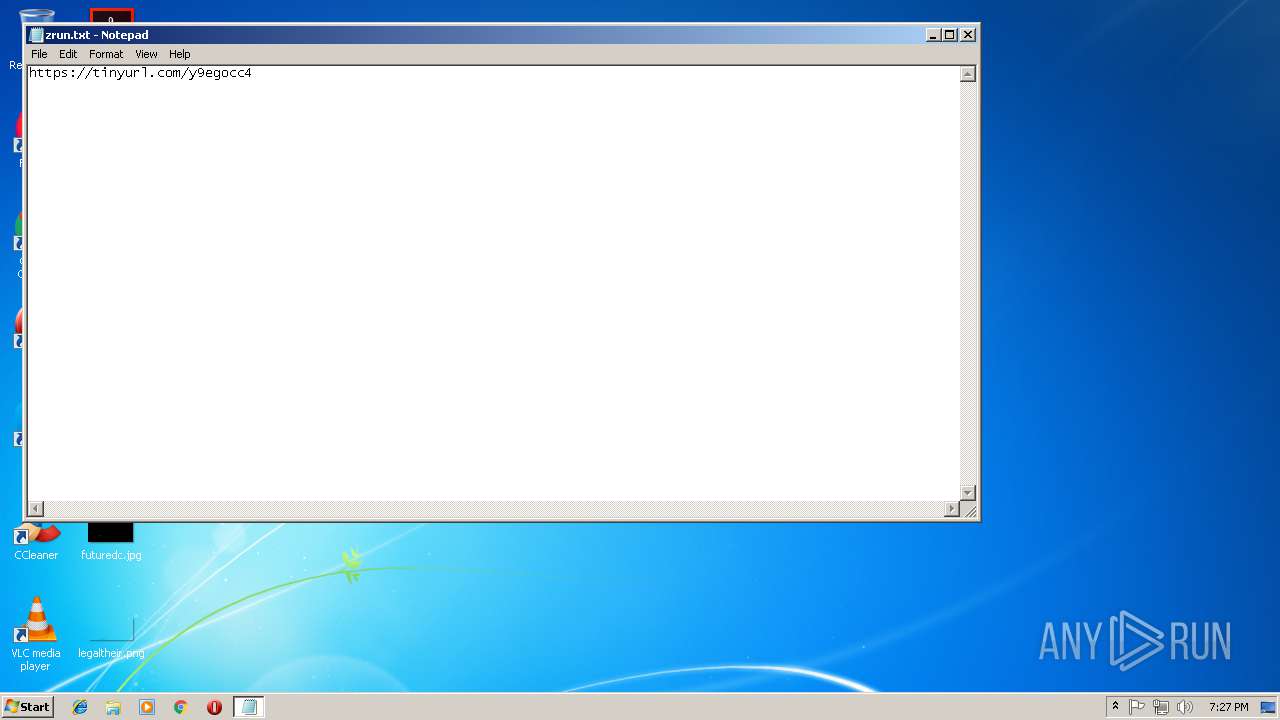
| File name: | zrun.txt |
| Full analysis: | https://app.any.run/tasks/eae2fef0-b5c6-44f3-b7f7-3bb47d23f6c8 |
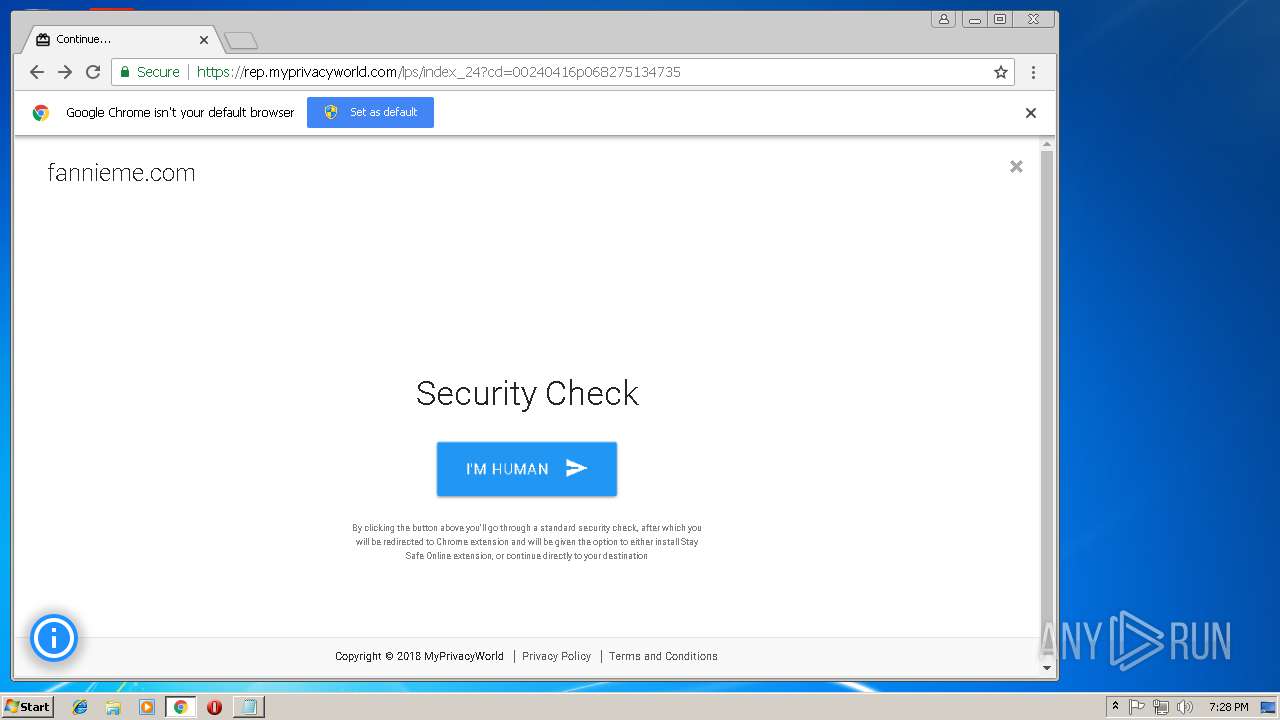
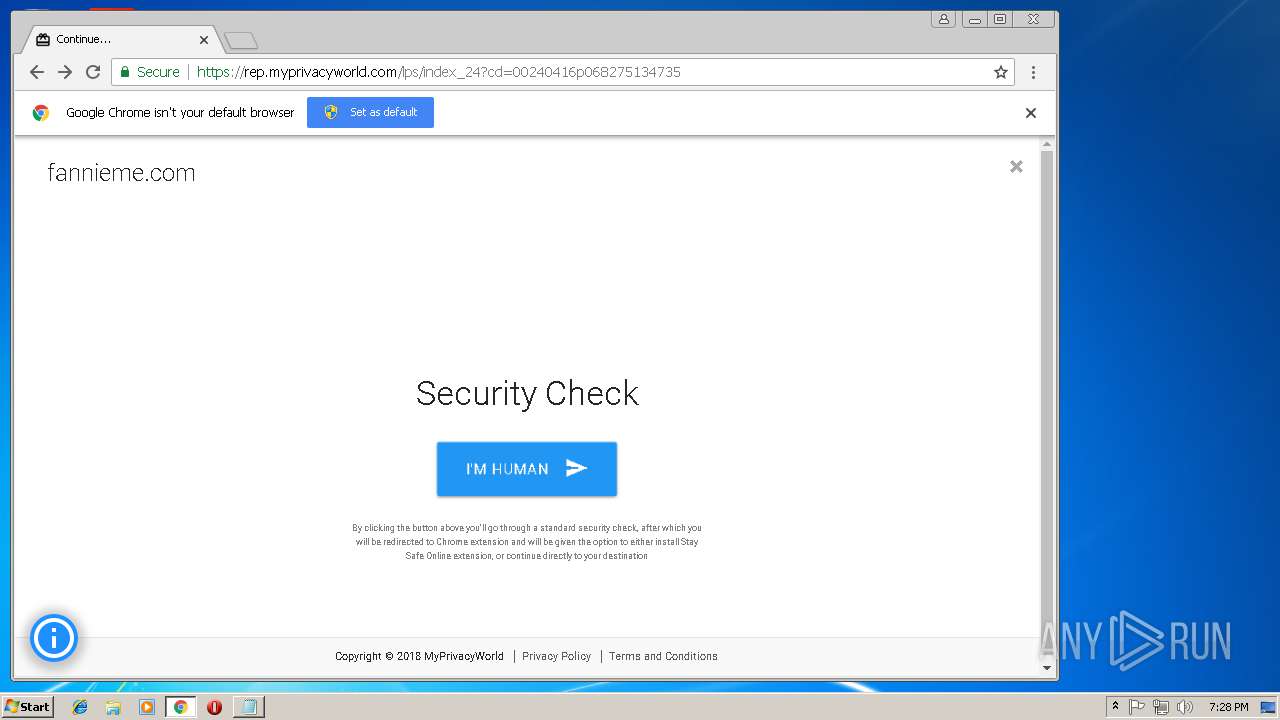
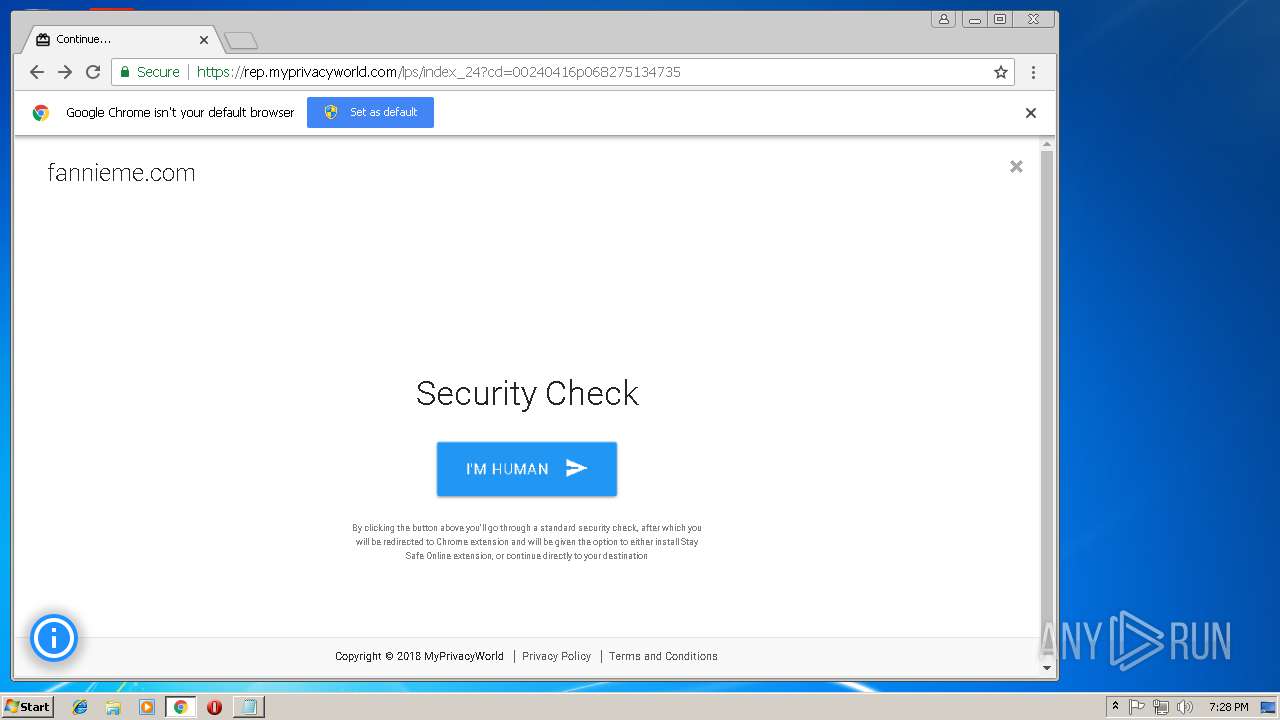
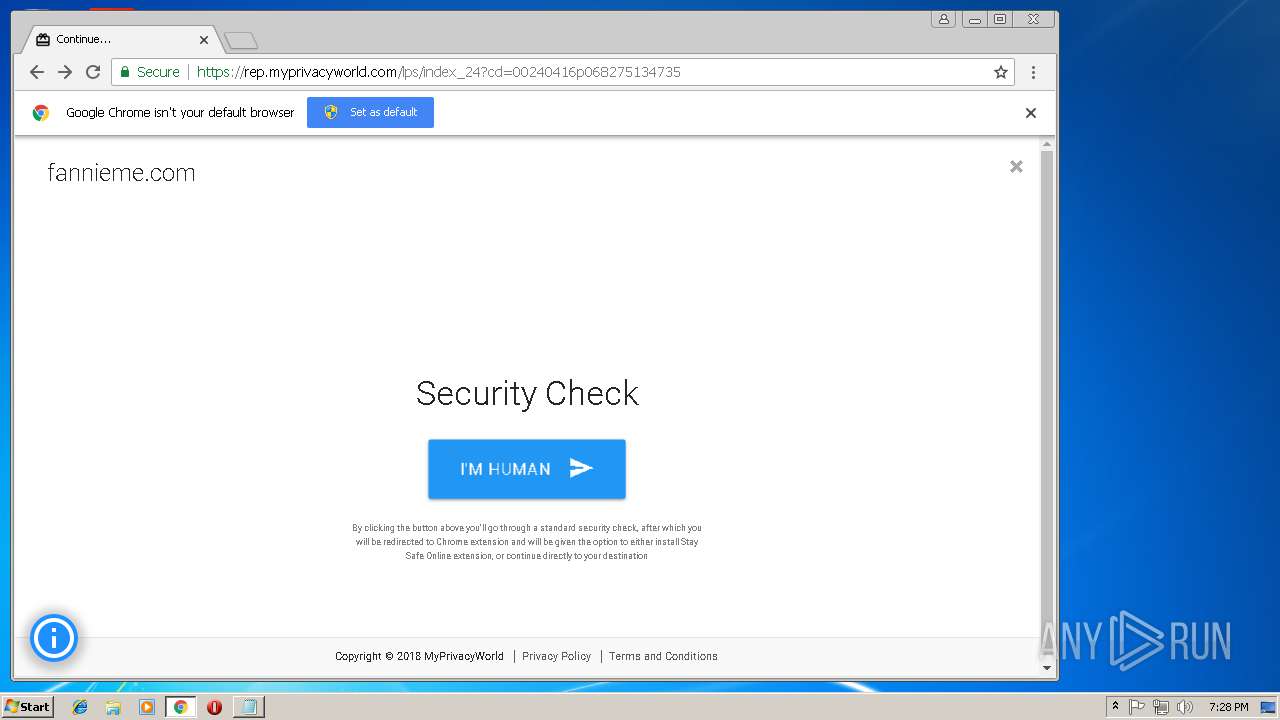
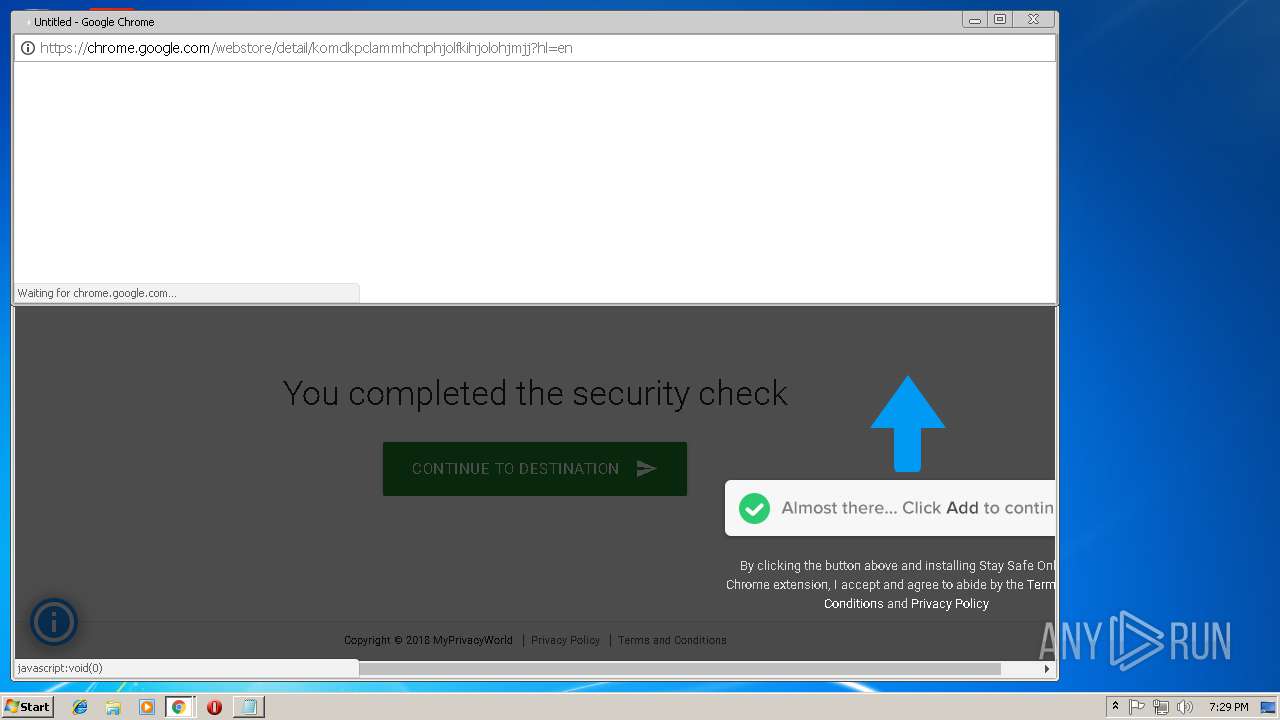
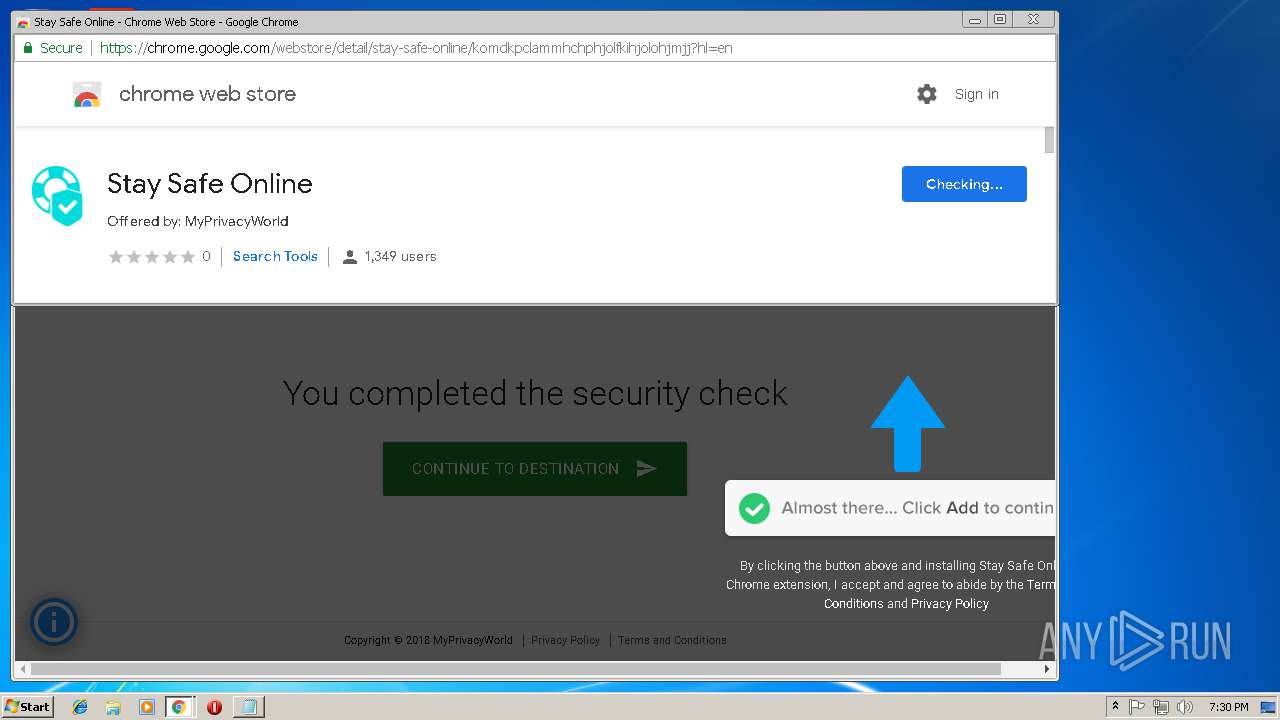
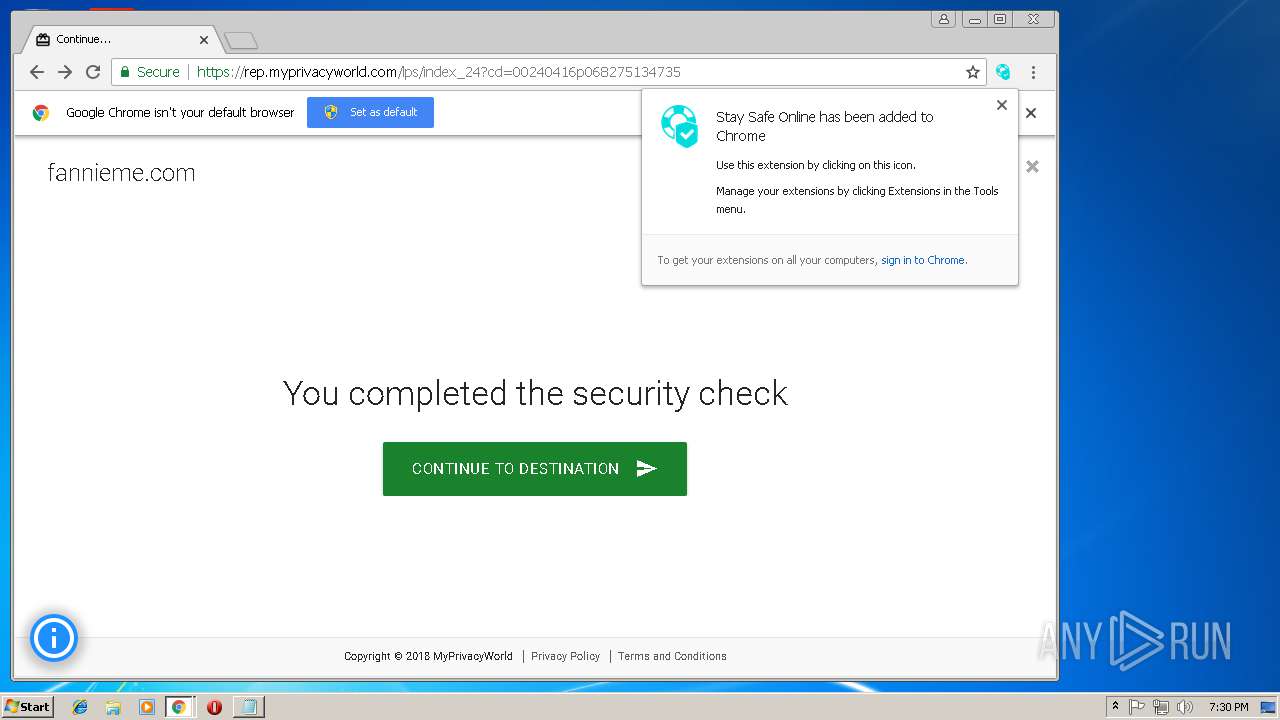
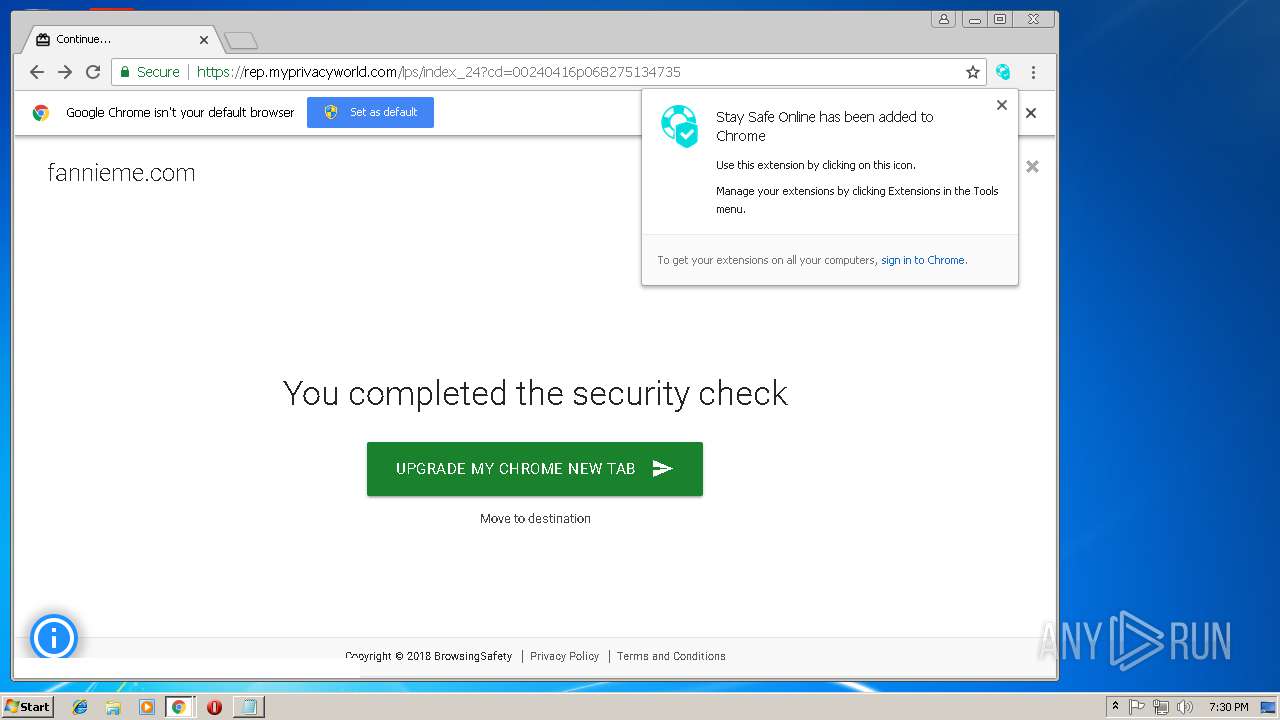
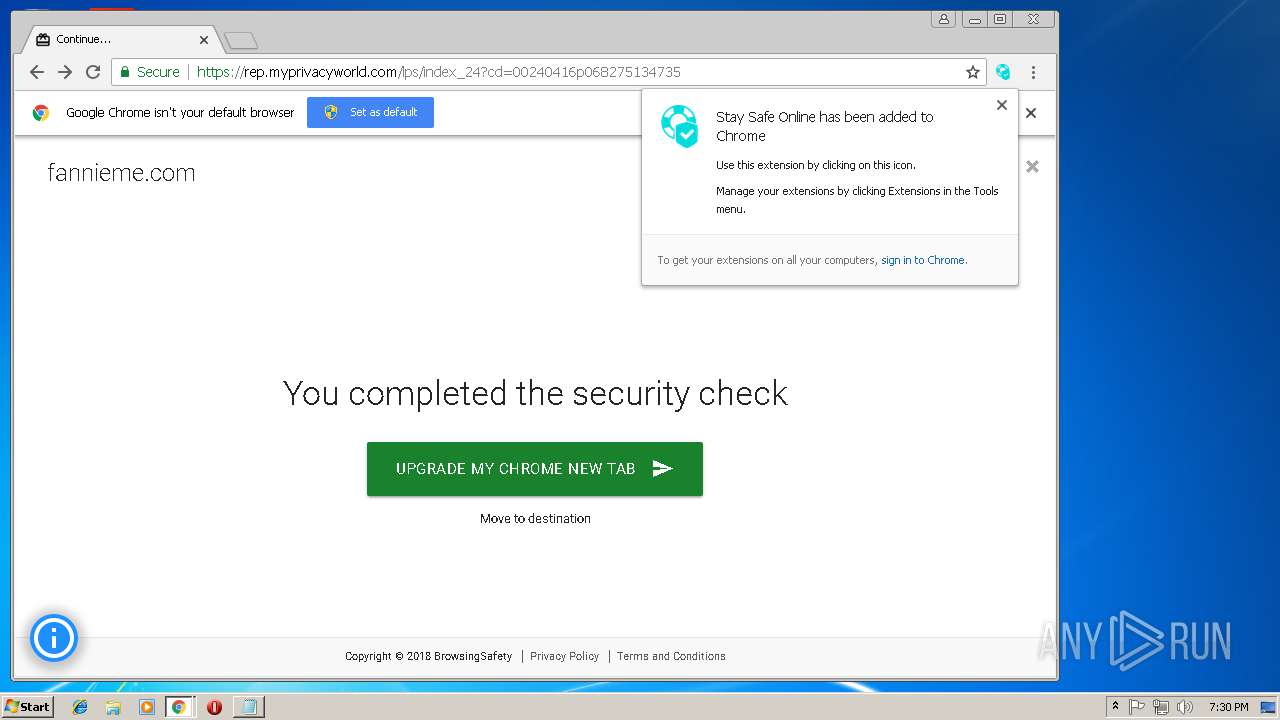
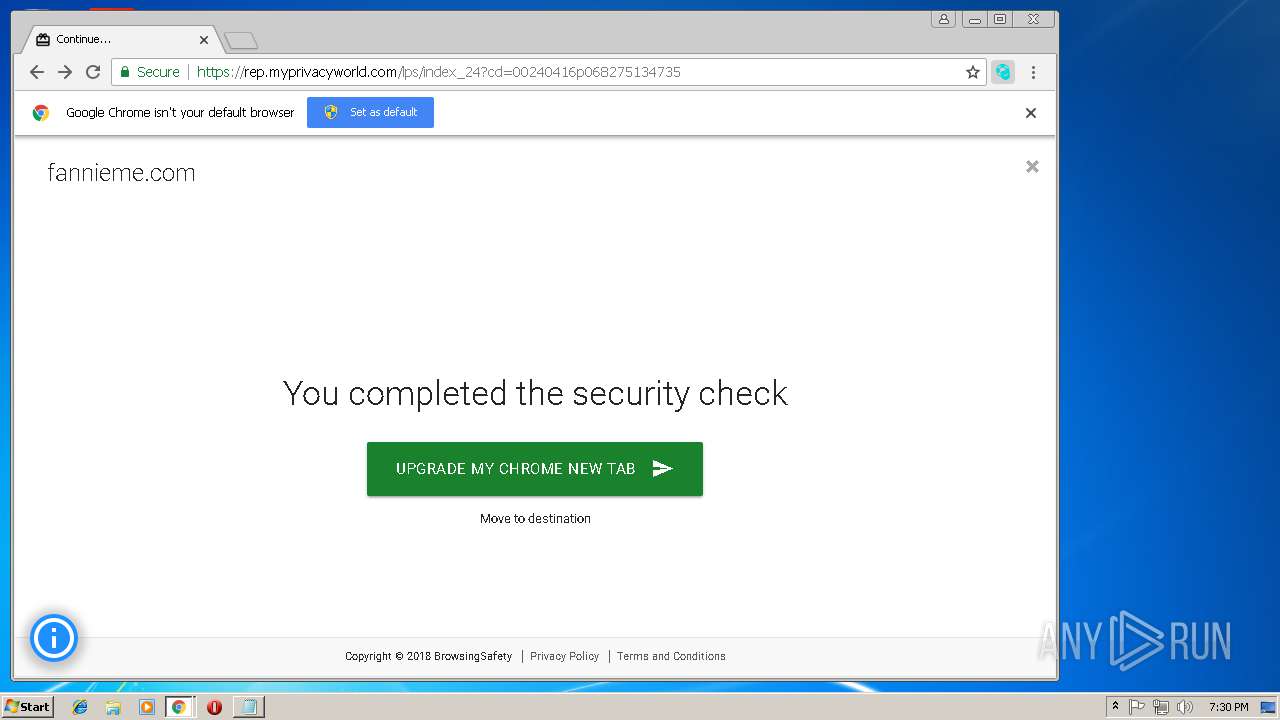
| Verdict: | Malicious activity |
| Analysis date: | November 15, 2018, 19:26:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with no line terminators |
| MD5: | 5B2CAEE7730EF905D42896BEB5EEA2CA |
| SHA1: | 108EC55612ADD8798F008F78C1239103CD0614C1 |
| SHA256: | D37D9AE7E0B452ED1976ED9FDE36CFB8244700502C393683CAC8B7B2DA296C2D |
| SSDEEP: | 3:N8EzLdIHEdG:2Endsj |
MALICIOUS
No malicious indicators.SUSPICIOUS
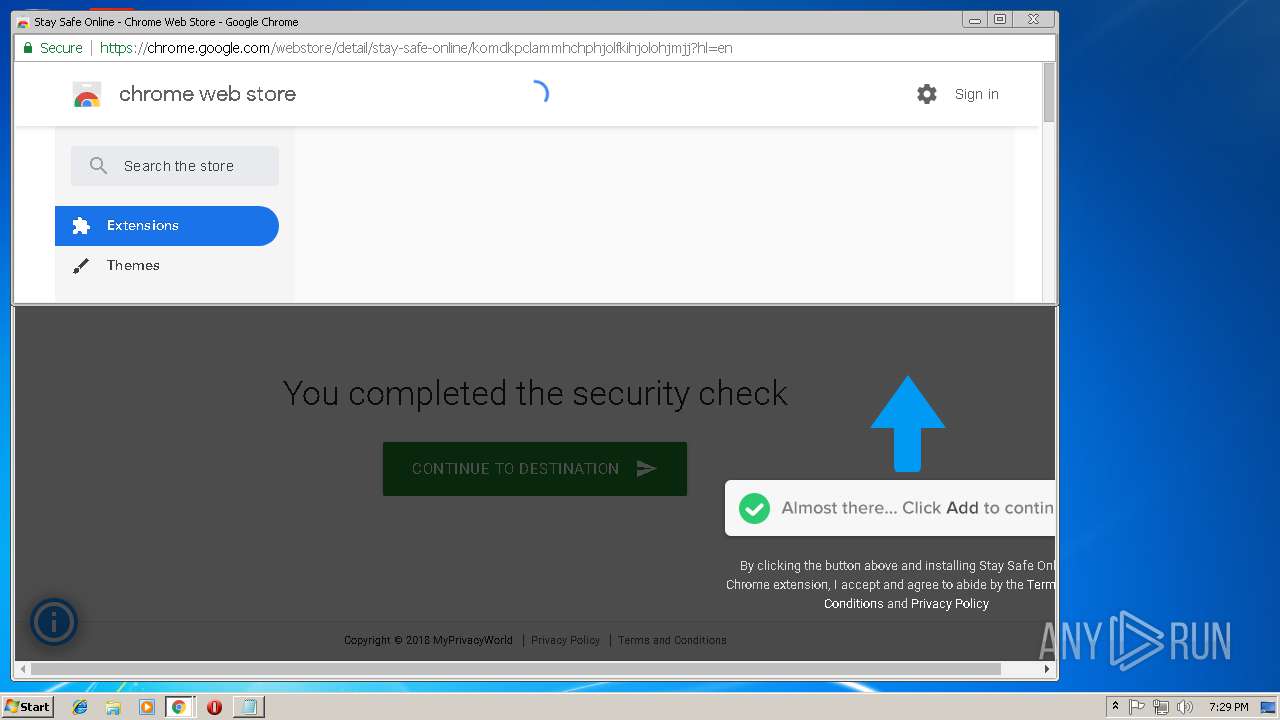
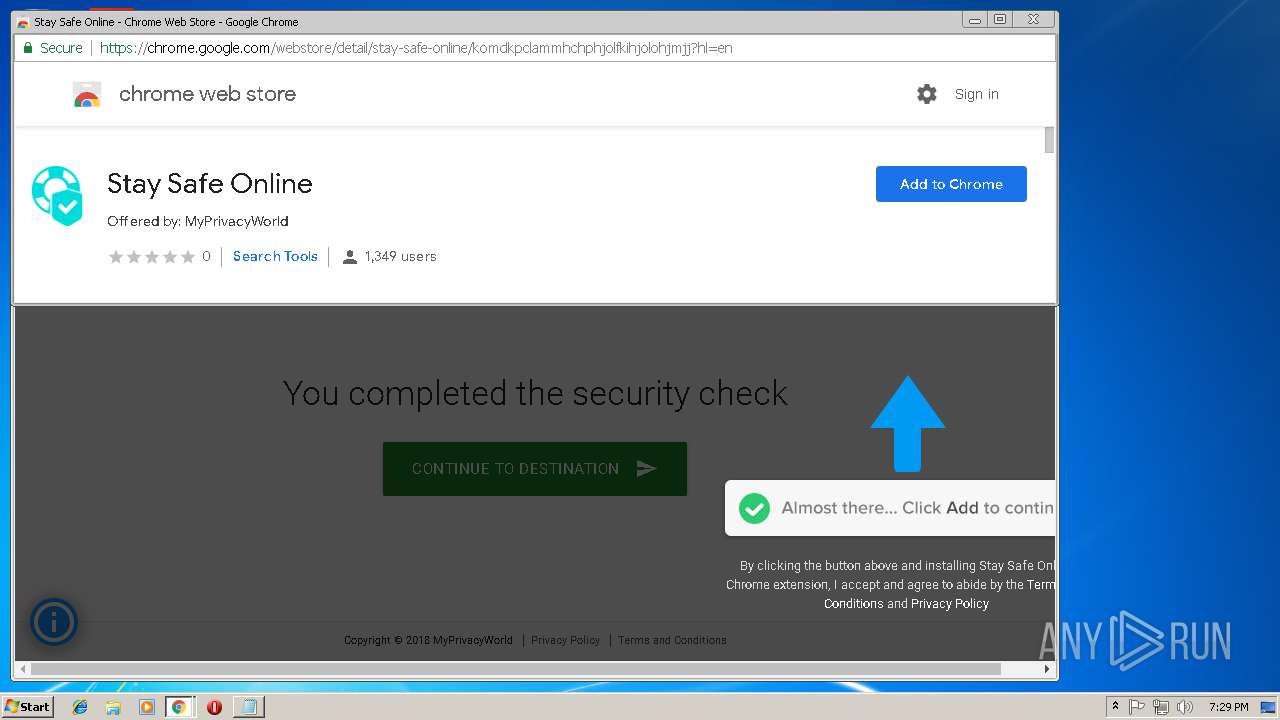
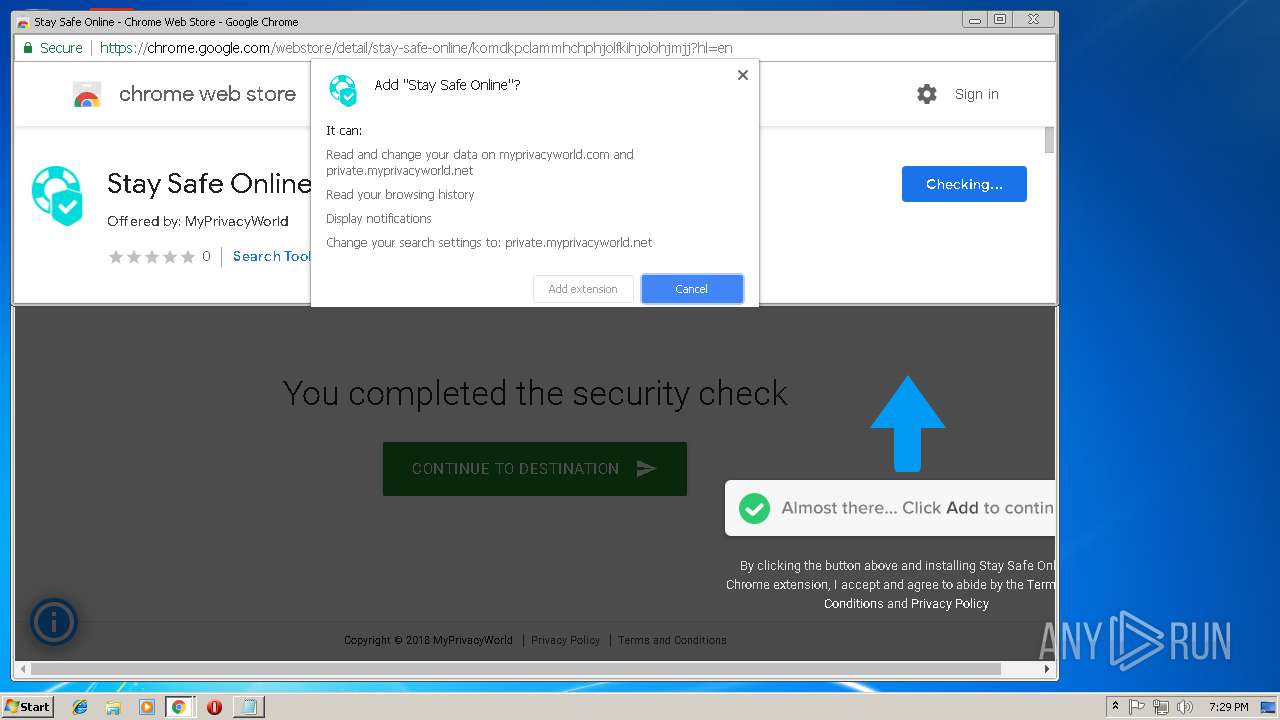
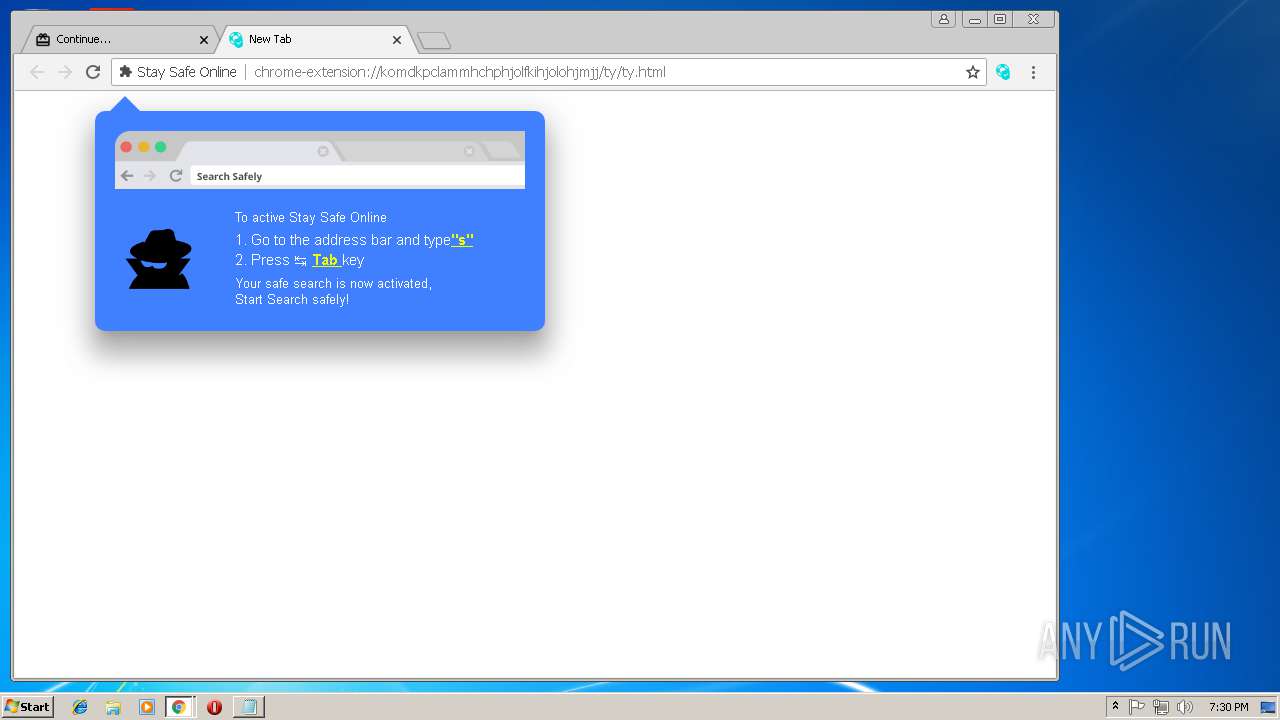
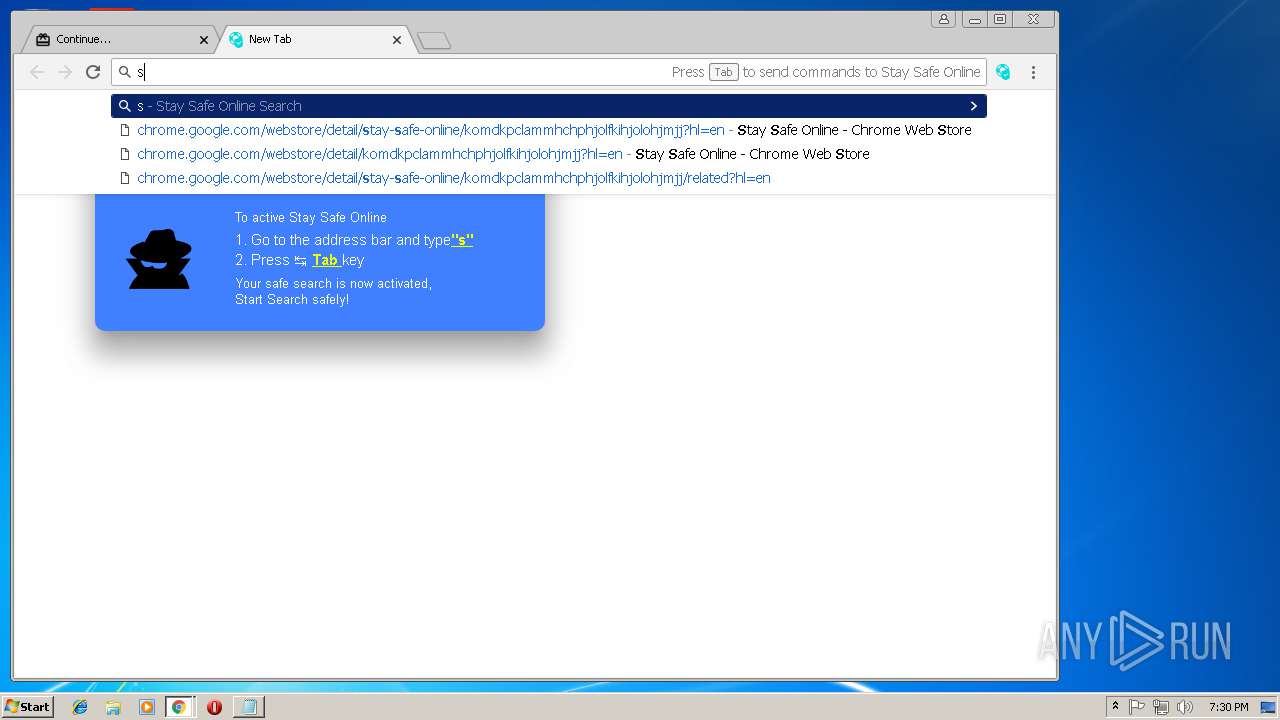
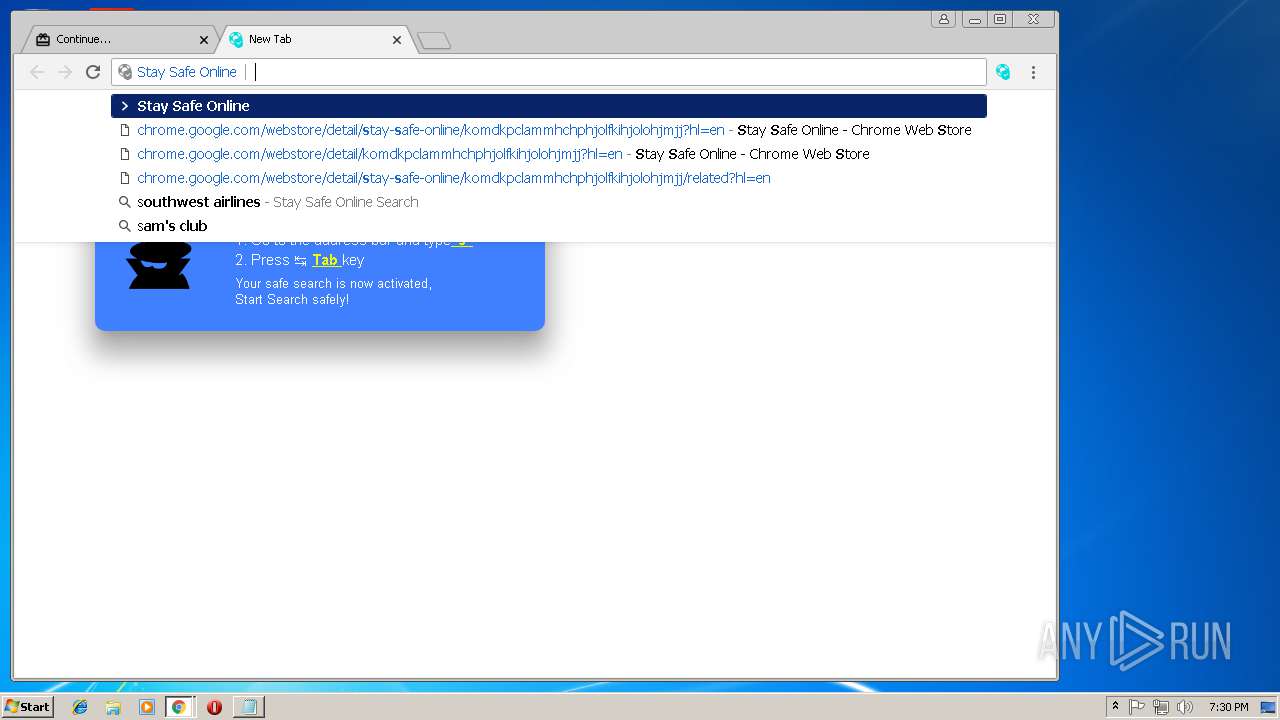
Modifies files in Chrome extension folder
- chrome.exe (PID: 2224)
INFO
Application launched itself
- chrome.exe (PID: 2224)
Reads Internet Cache Settings
- chrome.exe (PID: 2224)
Reads settings of System Certificates
- chrome.exe (PID: 2224)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
55
Monitored processes
25
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=920,18420738487058802020,6181842269892805032,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=BE4D4C57EF379280B7F9627A3747B47B --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=BE4D4C57EF379280B7F9627A3747B47B --renderer-client-id=6 --mojo-platform-channel-handle=3644 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=920,18420738487058802020,6181842269892805032,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=A1439E1A54A7210CE33D9737EF936BD0 --mojo-platform-channel-handle=4660 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=920,18420738487058802020,6181842269892805032,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=1C414D365FB735AA92DBDC657AE048B9 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1C414D365FB735AA92DBDC657AE048B9 --renderer-client-id=7 --mojo-platform-channel-handle=3904 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=920,18420738487058802020,6181842269892805032,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=A9EFB57318BA33B0B86B214535DAB2EF --mojo-platform-channel-handle=4464 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=920,18420738487058802020,6181842269892805032,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=30FD378F0E9CD870A7A75B1F7A38BA67 --mojo-platform-channel-handle=884 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2224 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=920,18420738487058802020,6181842269892805032,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=CBC96981CEAB6DE941D7E5B7FE09B7B7 --mojo-platform-channel-handle=624 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1552 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2424 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x701100b0,0x701100c0,0x701100cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=920,18420738487058802020,6181842269892805032,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1CAE4AD4351DA1C66E0364A27B6D61EE --mojo-platform-channel-handle=512 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
654
Read events
553
Write events
96
Delete events
5
Modification events
| (PID) Process: | (2224) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2224) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2224) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2224) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2224) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2224) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (2224) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2224-13186783671818750 |
Value: 259 | |||
| (PID) Process: | (2224) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2224) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2224) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
0
Suspicious files
70
Text files
143
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2224 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\eb9cbf69-6f86-42d4-a56b-8c598985d56a.tmp | — | |
MD5:— | SHA256:— | |||
| 2224 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2224 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2224 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\0b99b948-1d23-4e4e-a3a3-06e35f7f6853.tmp | — | |
MD5:— | SHA256:— | |||
| 2224 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 2224 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2224 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\CacheStorage\e6622492fa163609ddd4212f54512baa07929ed3\caecb3bd-7969-4305-84d6-3a376453ec73\index-dir\temp-index | — | |
MD5:— | SHA256:— | |||
| 2224 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2224 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF5e0a28.TMP | text | |
MD5:— | SHA256:— | |||
| 2224 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
49
DNS requests
33
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2224 | chrome.exe | GET | 302 | 173.192.101.27:80 | http://forwrdnow.com/aS/feedclick?s=u6geJV4sLGvIe8h9TRMbtI8uDhK_8R6jmUHXgwrpbaDwHKbB7fA1-qd73pnnDH6ohvzYfNFjJsIjeRAqbTvnpz6eRXw8SrHEg_8qf52JeBxwRzjJCykhw7FqdAuhxW3B1m0_7Kh50mbN-QiTSYr1vOyYfCkXAtBnsF4k2OZTBwu9C7YcJrvM2pYkqcmdX4HFupn17oLTfzQVTIVbhHWwXPa5SLNwpMBri7Gt6Dd79_69YNuQArQBWdvnhopHr4q90gFS9HoqXV8Fa7bEkpY8TbBEiYP6CbG7ZNigAavczMrjuJSJpJp8CSdJQrHthfIlDX1H6cfvA5Sa-4TMdvZRrTMwoCY_E1jXvFWEyY6DP57smIWd5dckuomIoHCEQEJnKwZVytqAJFMNSN3TjQiWtIGAXXBt339xhessaUIpWULqmZYkNFopnl9zOElbbZfpLrobj-5F_RANocn4M-50RhiVQCUFaOZFJ2iHsxD3wibbmZzUlGO3t76IshQ3gT-6Lg_aaxuxmheA3cQe0IkTxmVRoUZ9AVs8PmXJPK64qsy5wbLqT0IvA4gVaauWZrU2Ug56WURAGzRMe9_2aAuff6YQovSpdXwjZT4E6YXHoD5OvZN_nzl3wy-cr8RR1zQbFtF5Fq-PL7oBdojGUf6Iz3Cgunb5WtapincHP-7asgxUNDE6rWOov32Xq6JmmBxR5JKQ6ucNzm7r1zfSJ5Dp4LDFmaxIWROSREH0_C18Zxjxn-HHHnc6JmwPT8BLw5poo6dd8lKvfuhPpUrhTAn-F7Zxp1kA7GKyAduQ3aoG39BoTESsE0Ggq7D8FYMrpqNSGSunDWClUgnegVV5_pxB4X0QhkJzvUjSp2SpUaUSZbHTAtLsVgzdTWtnkAXmWKPan-oFOynKb1_9mUA7HW9EVqaMn6YcPtcLxmhKNBIaXp3-doRYK2bAydzmfWTNRRvs19dwKsWmZ9YxIqBrEeZASgRjJogyuSDASi8RnOH-tTEtx12e0ctlpdvWxUvIWQTsU37p7o_uXHX-u2ghGTWE8IQBfV7D0uzzF8BrvXkBkzX1-g1GXCRanPaZZYrluWbhOrMWw1gCkfL69DclL8ac_s7NkrJjwobCs8tqr5xBRMwJhtcGckeXjd3spmdttmGfu3yEnFY52n9E60pyAZWRjnQejEbMDUIVMiA3EkA7ryg1uE0DwIqYsseXKEjehLJ-gO5YpWYxvsWRcCBfdDBlKgxUiLFxqPm6YHXqPoq1ZW9zwO73keWPA9NEUwNpSWhdnjsGVxGo0hrcLAvg6yC2PLW9Z3WDAcAPi6HQacIPSBqIuhoivTAt9k9K9hAIsIGu4JIFx55CO0H5zpYR5gf0oeqtqT4ev7VoK-2iwNMlNEDzlKXY0a5HFqwMVTv0vOnikUze_KYCfGQUsdUK02fmCeeJEZ8D1Y_zHUbn3IrajgzDYY9WvbV5_WM9q4vVMj5C2t_7a48VUKCjXvz7JqLE5kEMeTe26ktRdco0hfuB8pAQegR4auF0PuyyXHt8z5otW5dlSEAyrOdo8IXmId7gtaj6U5npjKdCN4BImU4dMOG-A0D46LOFeRutkymGuOeN17HYlWIzs_Fc-D1MB76lciK_f-Pcbwowd9oHlo9WfDCLWnTIFxlY5UzrMwF_EZbA_z00oRiiNXHQZhFzOrFGCGPMAtvkAgOhogGUNV5EtmmKo5Et0XFXHTIgE5VJ-oU98S0hJfVRni6wgWgOA3-vjY9_4fYzeU428uoExAuuTYFb7-Q7G1Fr6R0JB8HppEYWWrCbZ-8AxSmyCq0lHJdYisFVRDB_Zwx6yJmV8HCwXzDAsRKLGNmQ6TSBd0HZJahat0DdwxcGrIHOWVm-GwGu7WawfwDZkHZEoLI9da1QtxZve21zvDXNNEGhfIhkyHFh_EQ6DfVpA-MqIWbQXdYUVbR1wTu5YHTF7y8-7bLLrRecu40pk_zOS-T6H9Yw3TXfL86EsQGNXIarefPN0LsCFnpDGOhk_xOrgmQ3YxyIe_5fjs9YaLgK5UQgN4YuYjzKa7XeeMxOS6SQG2p4vuaos_TpTjwdHJXJO_FKo6aFSL1C3x8-jzYcqfgl1FyDvVWGVLGAvJZToQaMGev4R0cBEXybN3WmbEs9HECIHt--Rx64uOUH0YypS0jk1pIklGf-oGe4sWlNrVMCMlAytHw3gvflt81KLkDKtuZjpqWR8JEbyASfTre1bo78neSBErOw1_1uVYdQUAU9CtelIQ2EA5BhFcKaCIwR0Hf0eZPOBXAj4QfeX3Gef3sHljpBYSUySzhyTNDfNWfsHU3vBWUmOZlqUO9m3OLdcEGi8_Ap75fv_be6YXibX4UDEy2xifFnPkMwkIWJJIkbO7pWllwGdVGZXxgmhR3INz-QU0tQexjS1sjTSDdvxg2Yaspthu2RDMWDEcIrEsluFClVyyFIA6tqCJWlIXuPiXimj-ytXsIJhccXI35do1o0ZQWr8yGfTnmBlX7ANpO2OXtO--JYKsn45T5k59QTC7uGTIWrDIE1sbWvDOf4m4V6OGeYVfXPUwdVBDShm3Kwl9dwrUQYd6OeQ94j1HPACFu1THW5bSC8nE6peK6wQbBxgAJh9c0SETOTQvbh3IoI94GpBibqsRx59KXv90PpYVbqAATGGCnYMcsJNuckVrcXZ5BfilH9m0I3BUT57NcsPsQcWLqpxgp5cwzQD-9cHSXT9o-30Kph1M-0gGJAYwnj4vY3tjHhzv4C6i6HR0lgXKKzJKVAZOBdXRwaVvI9_gVqXrVxwvwQDDrUJy5LERKAlP_JZXMP600Waop5_DvDp0Jzr9wwYNAB-qUtCP23X2mrgSrzMhmwN_jv-Shr19YpekO6WtQ3barODFuR7L-tRD7L5StnH5s9NqtxX6PR015dXGVf7gU | US | — | — | whitelisted |
2224 | chrome.exe | GET | 302 | 66.147.227.29:80 | http://7lyonline.com/app/feedclick?p=u6geJV4sLGvIe8h9TRMbtI8uDhK_8R6jv2if_q5RuUAGvLcNuFljMMsHVc3fmJ8sEBqlHeFe70XLFqxf4ky0E6Q9dhCjttud1qq1tisruCLEXpY0oHWiQTHLGt5AuemyqEmhqsNIl4hQT9ZwyKcFTMAynbggay7BgSiNqhZmjz2BY5Z6Fa5OqYVGeT03WhpiYsUgAk-UlB-wflf3-qO81Lg0RkymVKuPaI_eQxuXiyQqVS2NqhH6QNrxSg8i7hzee0b3xHlwK9wZK9q40obcIfc3zuh-yLRkCQkNklUferuLHUUEMeD1-g3j3NkGC2EKRGkxi2cUwBN0yapvYRrRvI5yZIYGiC0Nr0EAihA2wIwCEReHZKpLSFvoVavGDlfEPacWqcwxbcD0O7ccbxGWk2GYOadziPn6yRfP3k16E90yRbr9evEIXLsC2bykHICTpi_WIIf-JedY9Imb2IrV87go2E-HBITemZibvSU0cAYdT6HSUse69NczxVFRjg-aUwdVBDShm3JWAueooxKEDIqJ8GMJ6GyZAkWQs6ExYpMbNSoUBs93fH6UwTpNf2leufsZRntBDqVPNC_OJaKrruNNVC9UvhJwiRY2qP7MuLWnxlR0enNHmHDmApL_E0jfTs-ylLhx7khGz3q-Dq26s7F54JeKebuaylpqcAKMB5XXCJErnCubpFAtSDM7bP0EMR-kFASuBGGyeejFEOQSMkP5B8gI5mYZM2JLCDbjMLPs_X7FS3o7aPbY5JzIQab-1ao7TiYOKnScjfelOeHGwL0g3M6keRy12DHLCTbnJFa3F2eQX4pR_ZtCNwVE-ezXLD7EHFi6qcYKeXMM0A_vXB0l0_aPt9CqYdTPtIBiQGMJ4-L2N7Yx4c7-Auouh0dJYFyisySlQGTgXV0cGlbyPf4Fal61ccL8EAw61CcuSxESgJT_yWVzD-tNFmqKefw7w6dCc6_cMGDQAfqlLQj9t19pq4Eq8zIZsDf47_koa9fWKXpDulrUN22qzgxbkey_JvBYl9ZIc0mHTSfvOlmjjKhkxw0Zk5PGYnZvNf3s-VZbqPUtTsK_PSRq_lo6uma-25ib5Co8CNrInBm3-VFkYuTLzYYLDH0n-__ALWAYET2q9jGXRR52kzmf69Jk_AuDavN9GVzRVtrGhMYAHogEABlraAkNv954nkP74NiFVJDenN7M04CCSu2nSwnabEkGRsyyYlqeZN3buGCoWbWHR5C1Ly4o8GPor8B03O_VrMp4M80EuafXFSyyRkxSG5YnW8dRNyh2G3JTB1UENKGbcipbOu_-ZsTUJtJRNwX8T1G4EC17gwbEkrUI60rekRH5sMQslIbgJ7fK2UTPT7CZLPyXi-X7GbDThMmCZZH16KCV-F4QlcVXhTZ3wyQ9Adoks1tP2y9k4CoTQzuGOZN__Vok2Y9CnnpLwneGUwx_cCCtvi2L0afolUhPTkAXToIA1fj2MHx-TVk7WD6YQLKVl_CpfqEMSrarujqLnyC56uZgSiRhEsraPVh4oQFX05se-Kt9gkQ3q1xA7vYUpawyau4mAMWKeMbw5-AyGh2A3Ge38bjjAh_SQnjg7qh1r1ddOCD_P6d8kmzATYdesGwAA12JWLR-7y4O | US | — | — | whitelisted |
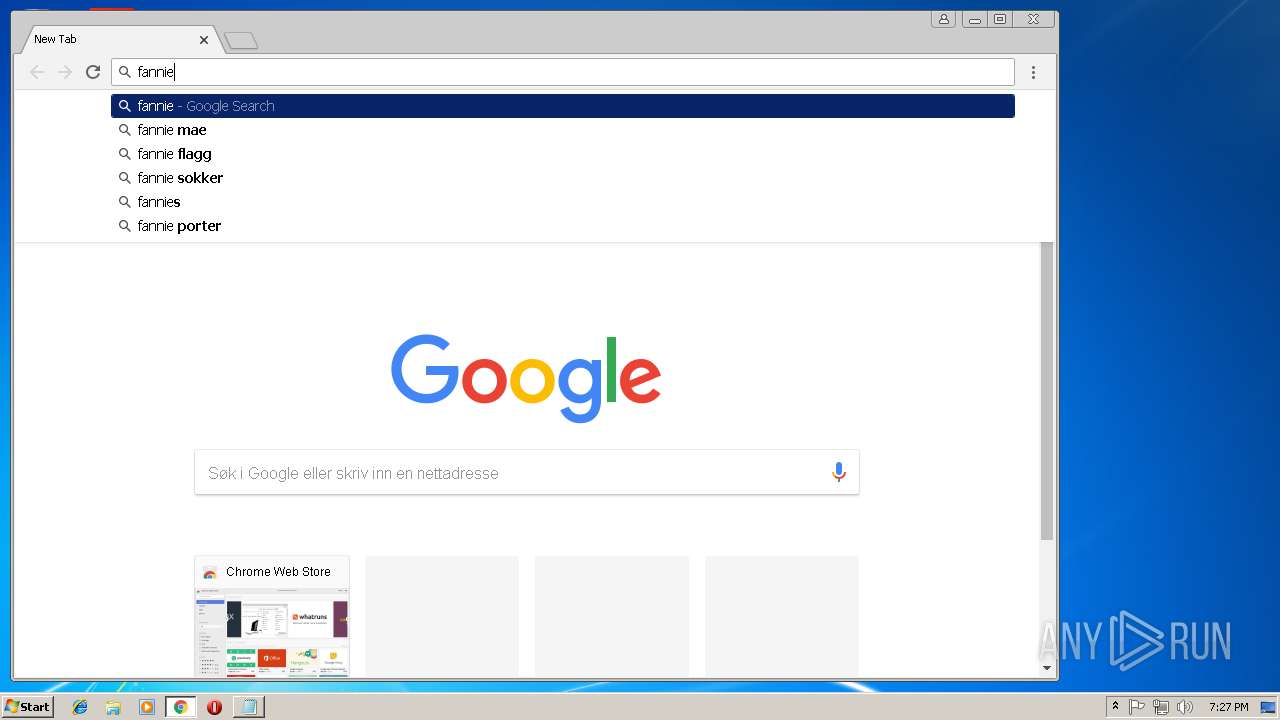
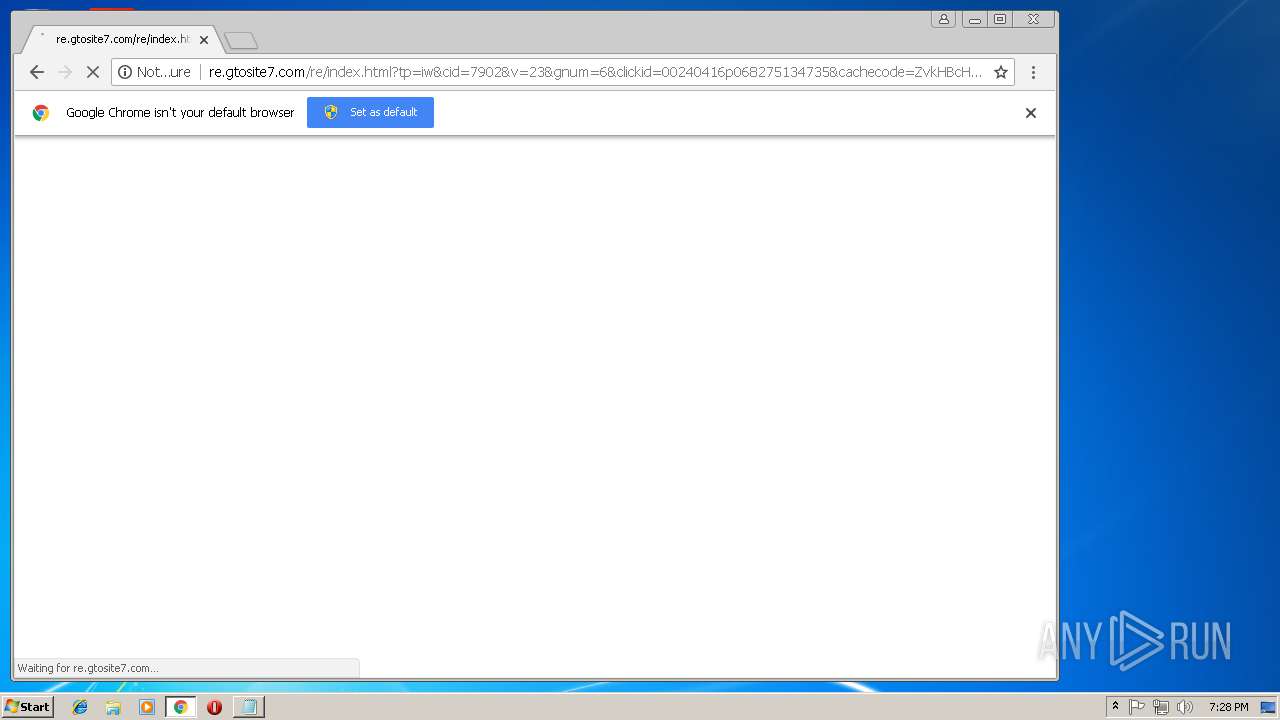
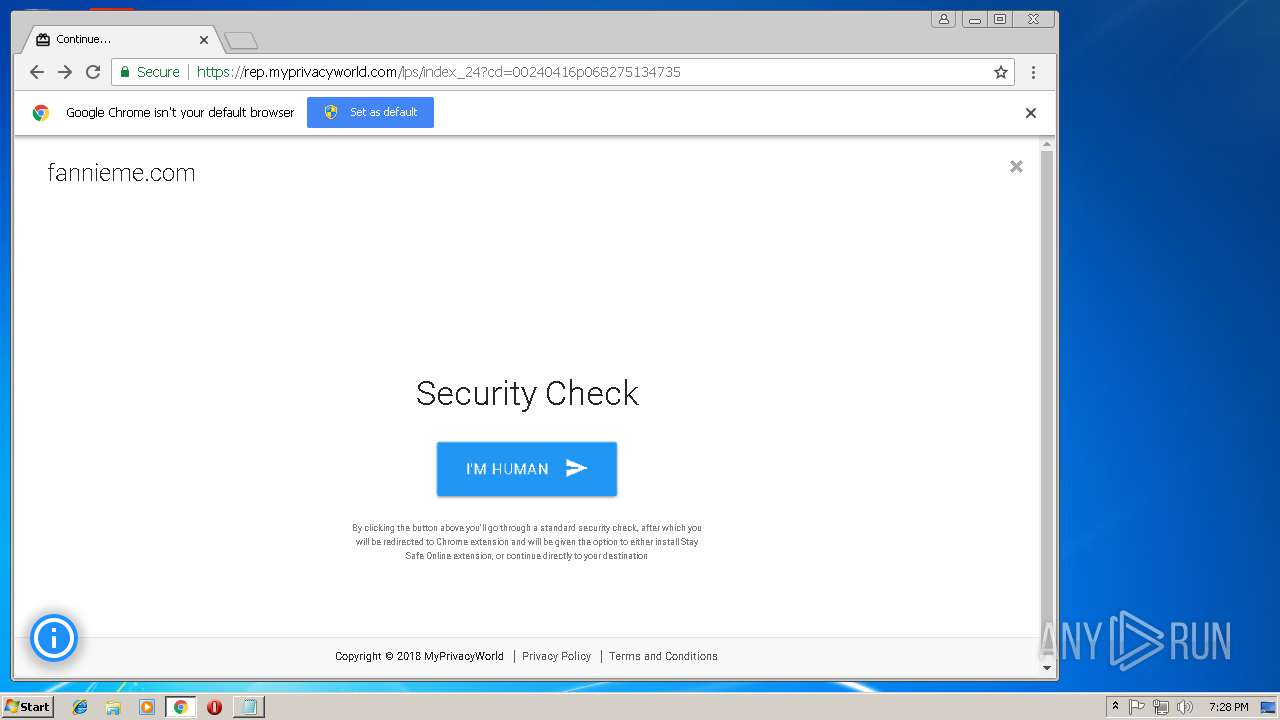
2224 | chrome.exe | GET | 200 | 172.217.168.19:80 | http://re.gtosite7.com/re/index.html?tp=iw&cid=7902&v=23&gnum=6&clickid=00240416p068275134735&cachecode=ZvkHBcHv4fEMuik4r0A8Pw&q=mortgage%20KW%20%20%20Foreclosed%20%20payday%20loans%20%20Bank%20%20Properties%20%20Lending%20Finance%20%20Owned%20%20quicken%20loans%20cash%20advance%20%20bad%20credit%20Credit%20Listings%20Real%20%20Estate%20fannieme.com%20fanniemae.com&dkw=fannieme.com&g=NO&cc2=kwX%2BNlCNTPJ7tI2XOEg%2BdA%3D%3D%3AZmVkY2JhOTg3NjU0MzIxMA%3D%3D | US | html | 1.84 Kb | malicious |
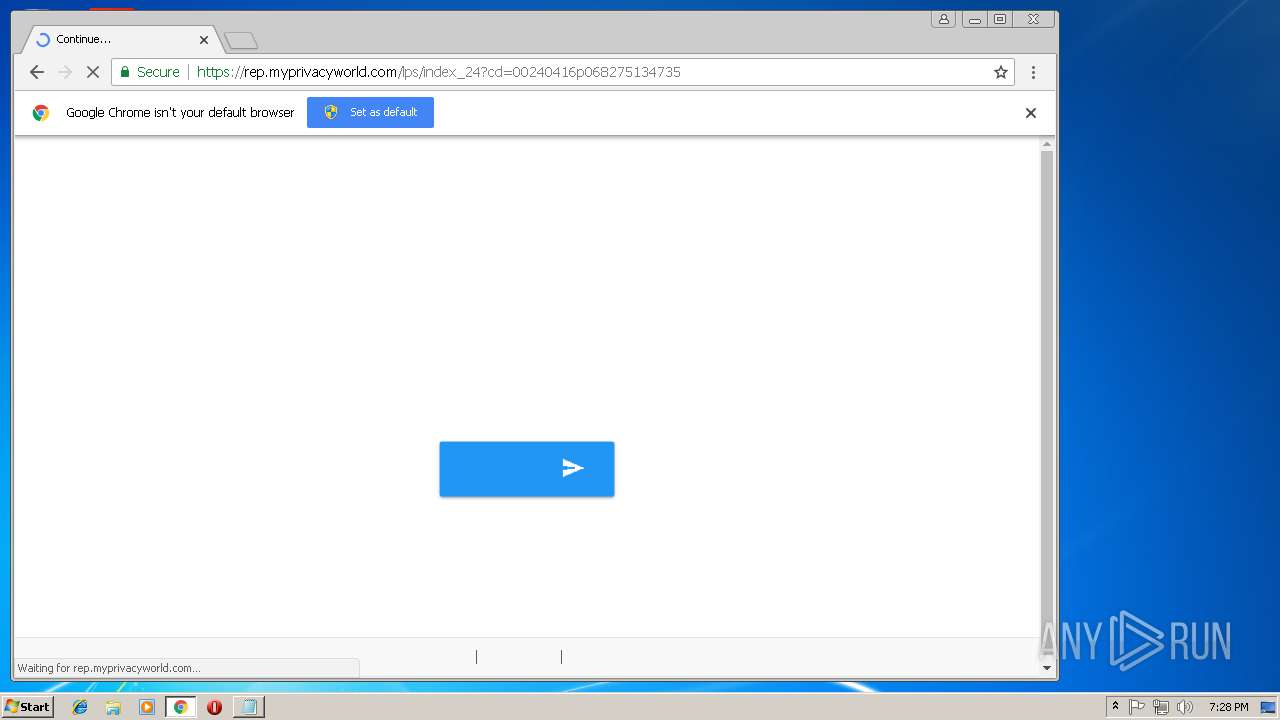
2224 | chrome.exe | GET | 200 | 151.139.237.32:80 | http://sug.myprivacyworld.net/search/index_sg.php?q=s | US | text | 71 b | malicious |
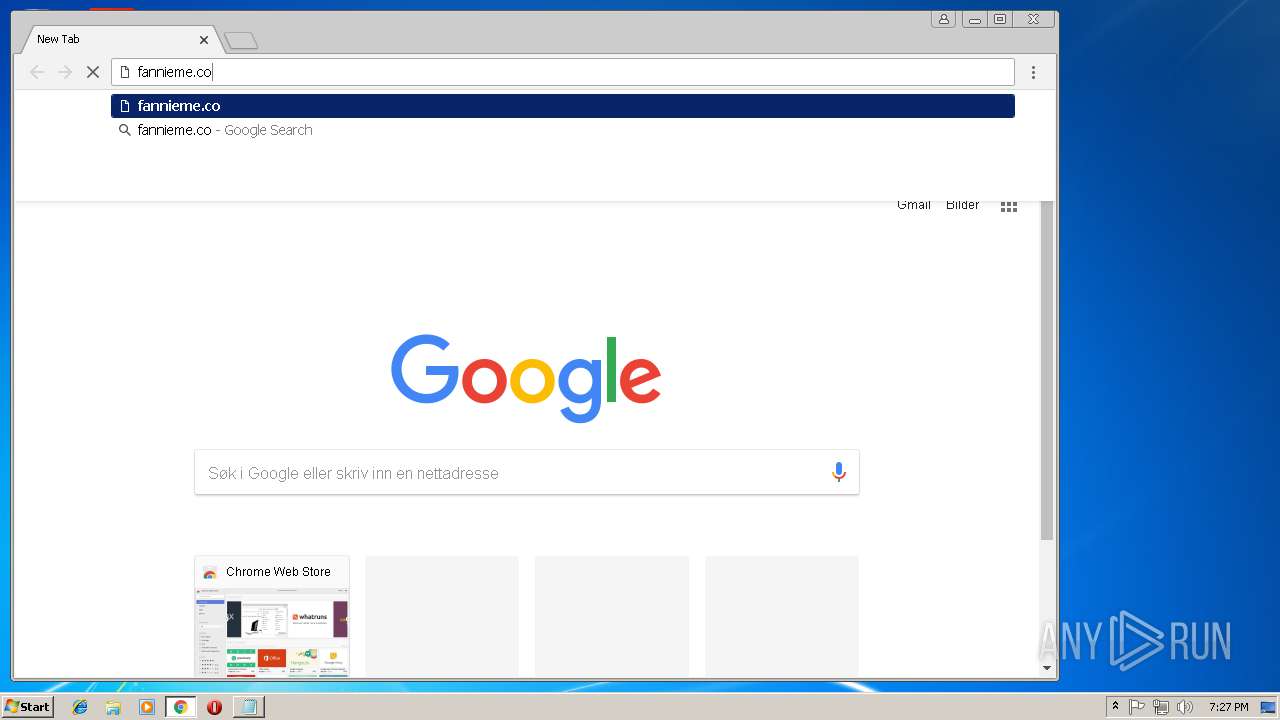
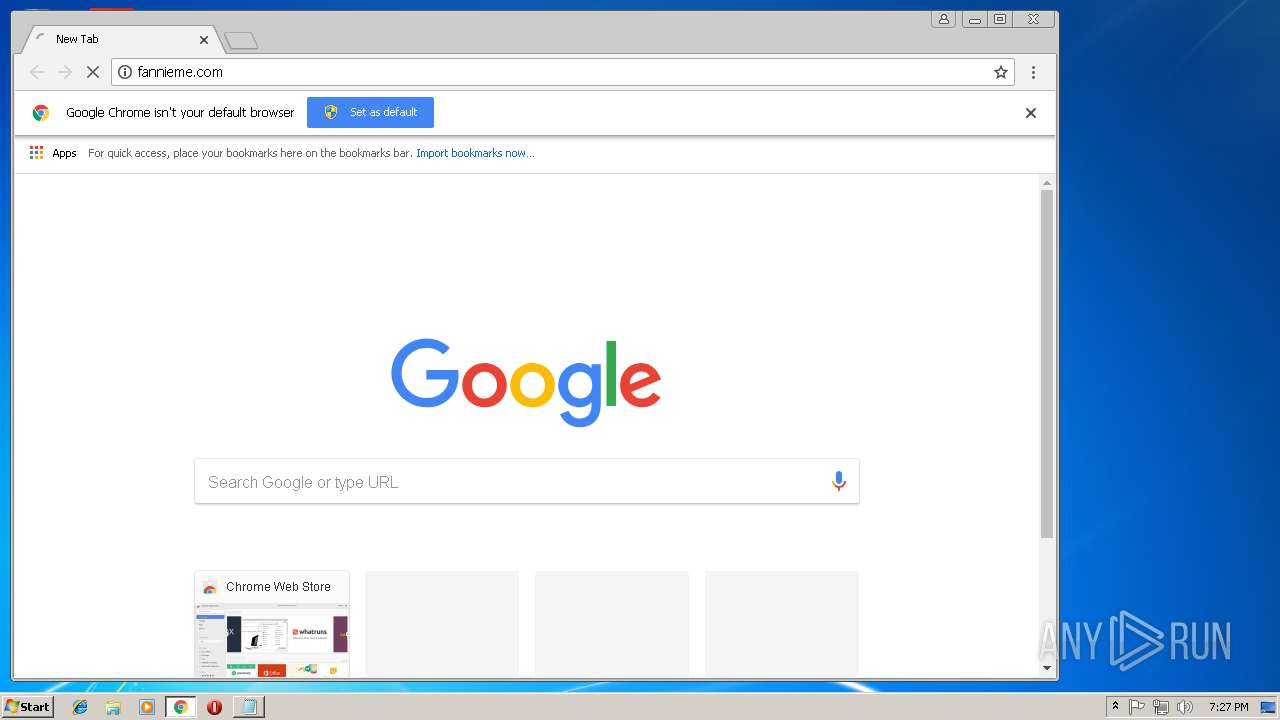
2224 | chrome.exe | GET | 302 | 207.244.67.139:80 | http://fannieme.com/ | US | text | 11 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2224 | chrome.exe | 173.192.101.27:80 | forwrdnow.com | SoftLayer Technologies Inc. | US | unknown |
2224 | chrome.exe | 207.244.67.139:80 | fannieme.com | Leaseweb USA, Inc. | US | malicious |
2224 | chrome.exe | 172.217.168.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2224 | chrome.exe | 66.147.227.29:80 | 7lyonline.com | HostRocket.com, Inc. | US | unknown |
2224 | chrome.exe | 172.217.168.19:80 | re.gtosite7.com | Google Inc. | US | whitelisted |
2224 | chrome.exe | 172.217.168.19:443 | re.gtosite7.com | Google Inc. | US | whitelisted |
2224 | chrome.exe | 216.58.215.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2224 | chrome.exe | 216.58.215.234:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2224 | chrome.exe | 172.217.168.3:443 | www.google.de | Google Inc. | US | whitelisted |
2224 | chrome.exe | 216.58.215.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.de |
| whitelisted |
www.gstatic.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
clients4.google.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.com |
| malicious |
www.google.no |
| whitelisted |