| File name: | 01798128_2 |
| Full analysis: | https://app.any.run/tasks/21491b68-7079-40f6-afd2-ea144fb2d7c1 |
| Verdict: | Malicious activity |
| Analysis date: | January 30, 2020, 02:00:02 |
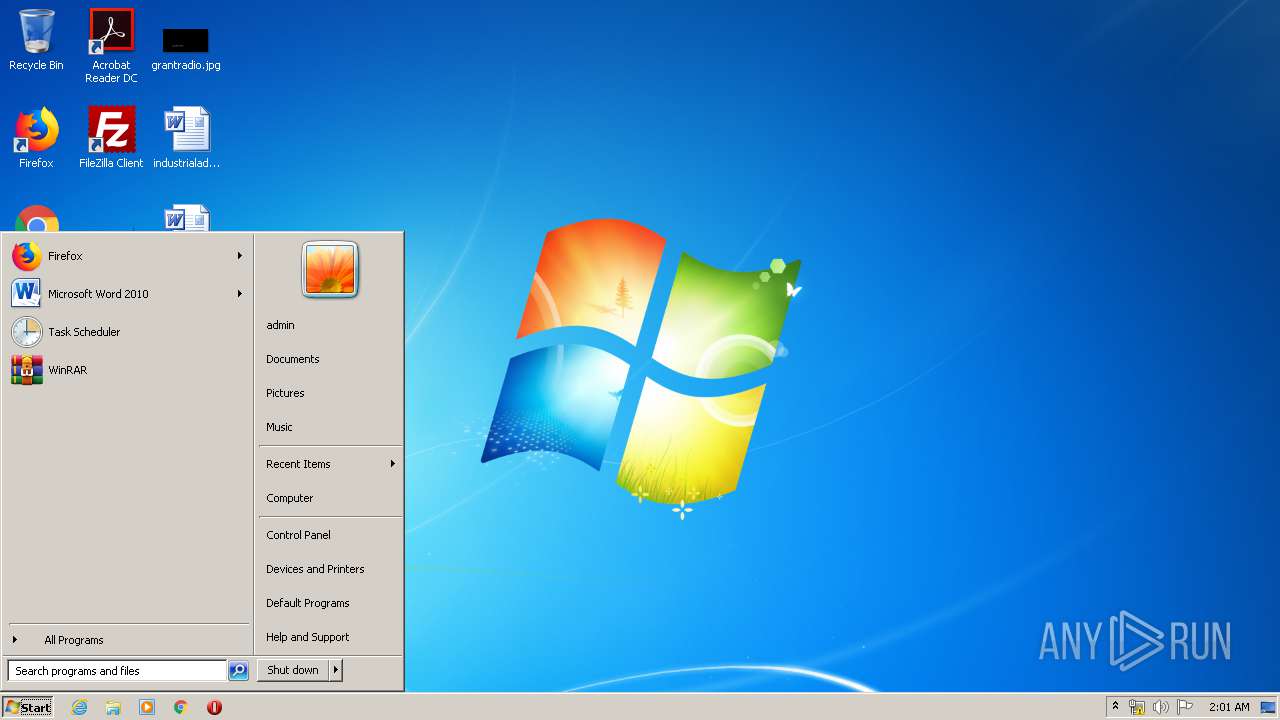
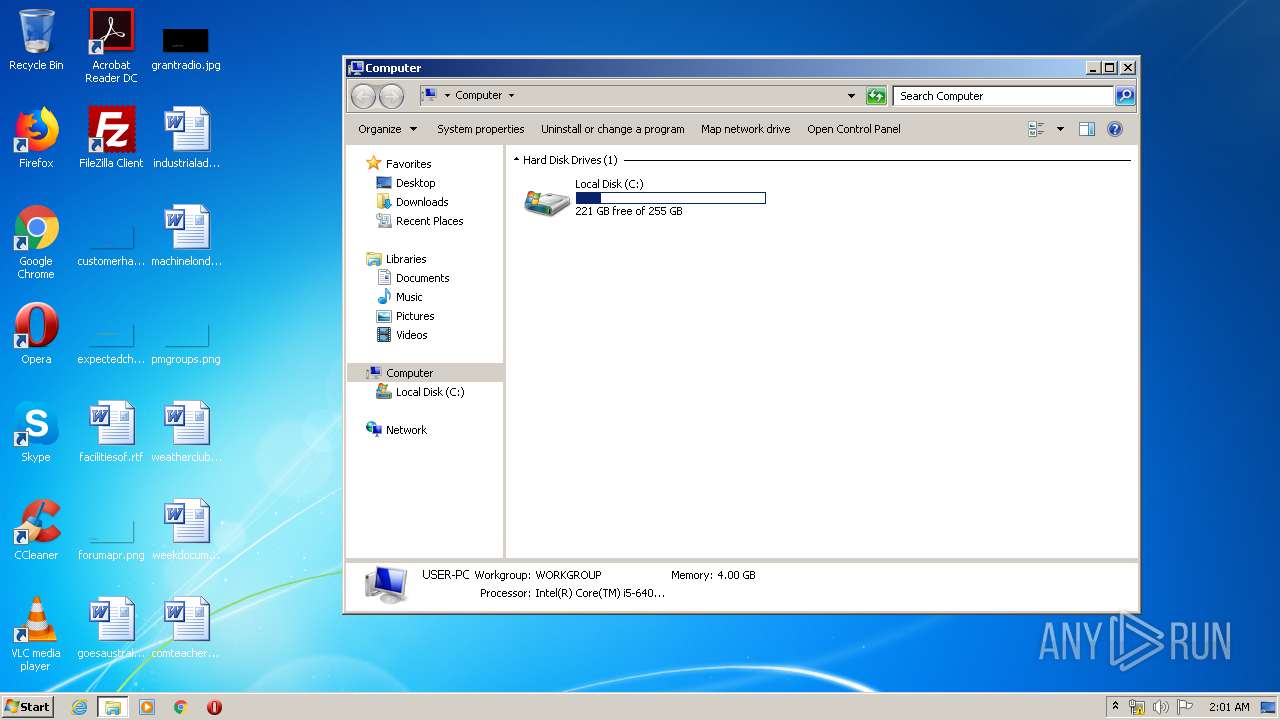
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
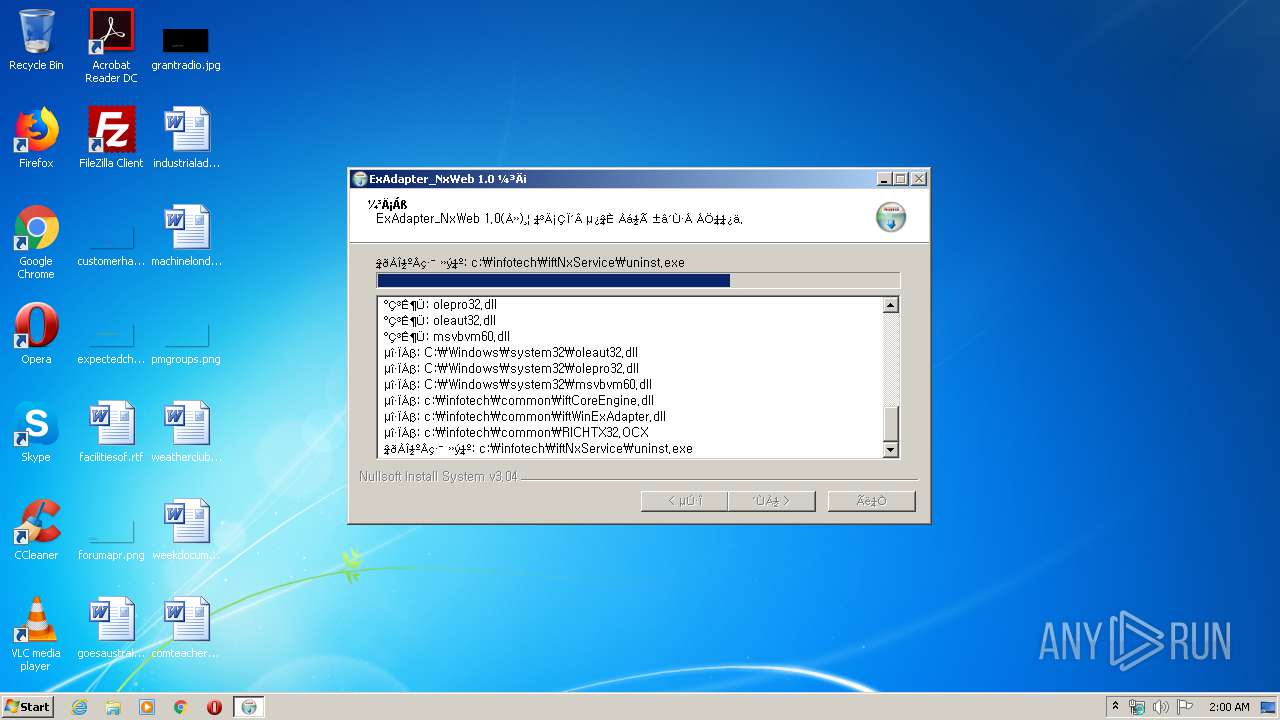
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 1A63A80612782EF8DE77E6CE94406743 |
| SHA1: | C989EC15F1561AA315E69A462592F3C53D0E2C06 |
| SHA256: | D37A65A1D1B22EB544F9A09A43A43814325E931BDA2ECCD2630011C8C63A97B3 |
| SSDEEP: | 196608:SieTNW1O8FxQs4fN1MxsQwvQJFtqLuOn8xNd+oAJizfYNKRx:NeJWo8Fxc3MwAeuOnUNkoA9NK |
MALICIOUS
Loads dropped or rewritten executable
- 01798128_2.exe (PID: 2184)
Changes settings of System certificates
- 01798128_2.exe (PID: 2184)
- certutil.exe (PID: 3284)
Application was dropped or rewritten from another process
- nsFB23.tmp (PID: 2908)
- iftExWeb.exe (PID: 916)
- iftExWeb.exe (PID: 3964)
SUSPICIOUS
Creates files in the Windows directory
- 01798128_2.exe (PID: 2184)
- certutil.exe (PID: 3284)
Creates COM task schedule object
- 01798128_2.exe (PID: 2184)
Modifies the open verb of a shell class
- 01798128_2.exe (PID: 2184)
Creates a software uninstall entry
- 01798128_2.exe (PID: 2184)
Removes files from Windows directory
- certutil.exe (PID: 3284)
Starts application with an unusual extension
- 01798128_2.exe (PID: 2184)
Creates files in the program directory
- certutil.exe (PID: 3284)
Executed as Windows Service
- iftExWeb.exe (PID: 916)
Creates files in the user directory
- certutil.exe (PID: 780)
Executable content was dropped or overwritten
- 01798128_2.exe (PID: 2184)
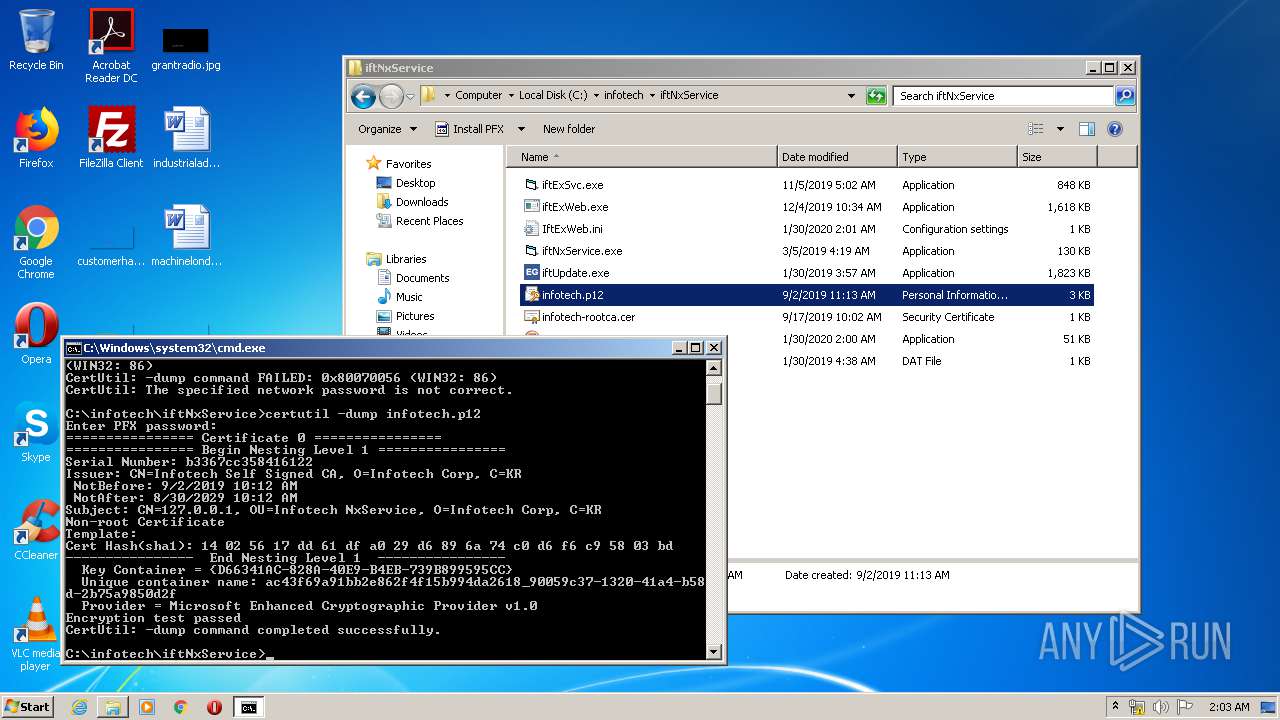
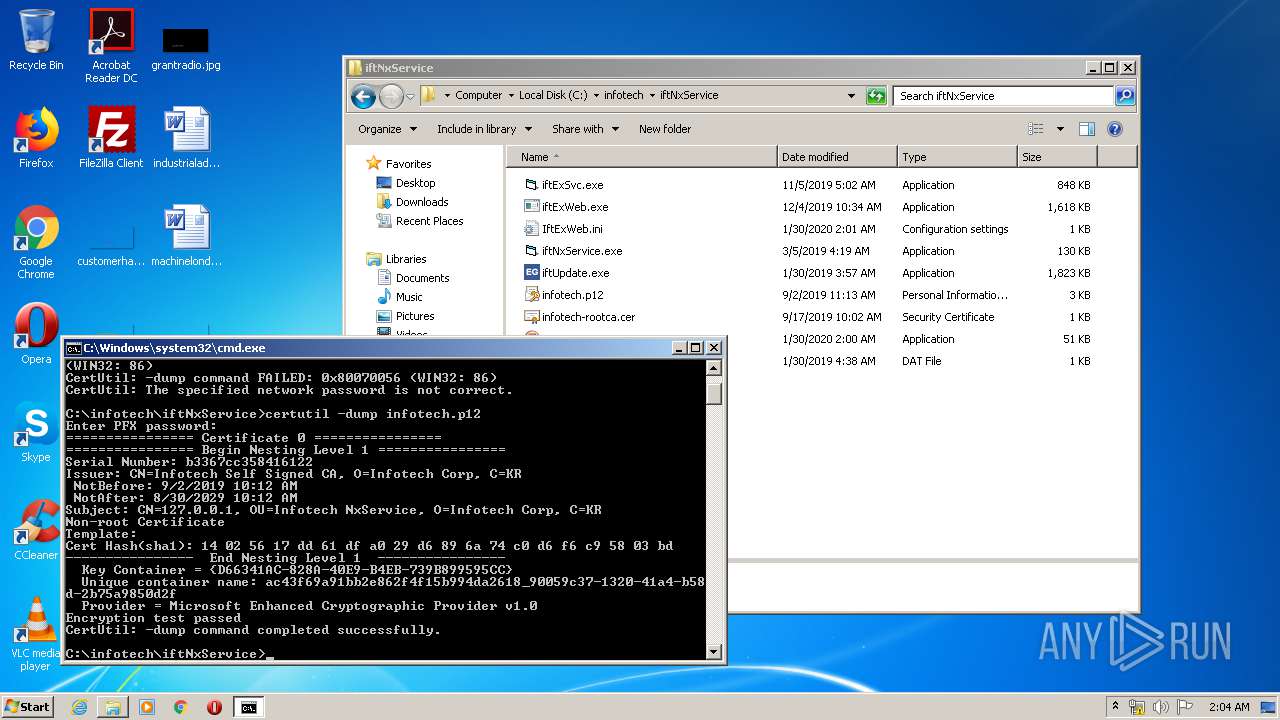
Adds / modifies Windows certificates
- certutil.exe (PID: 3284)
INFO
Reads settings of System Certificates
- certutil.exe (PID: 3284)
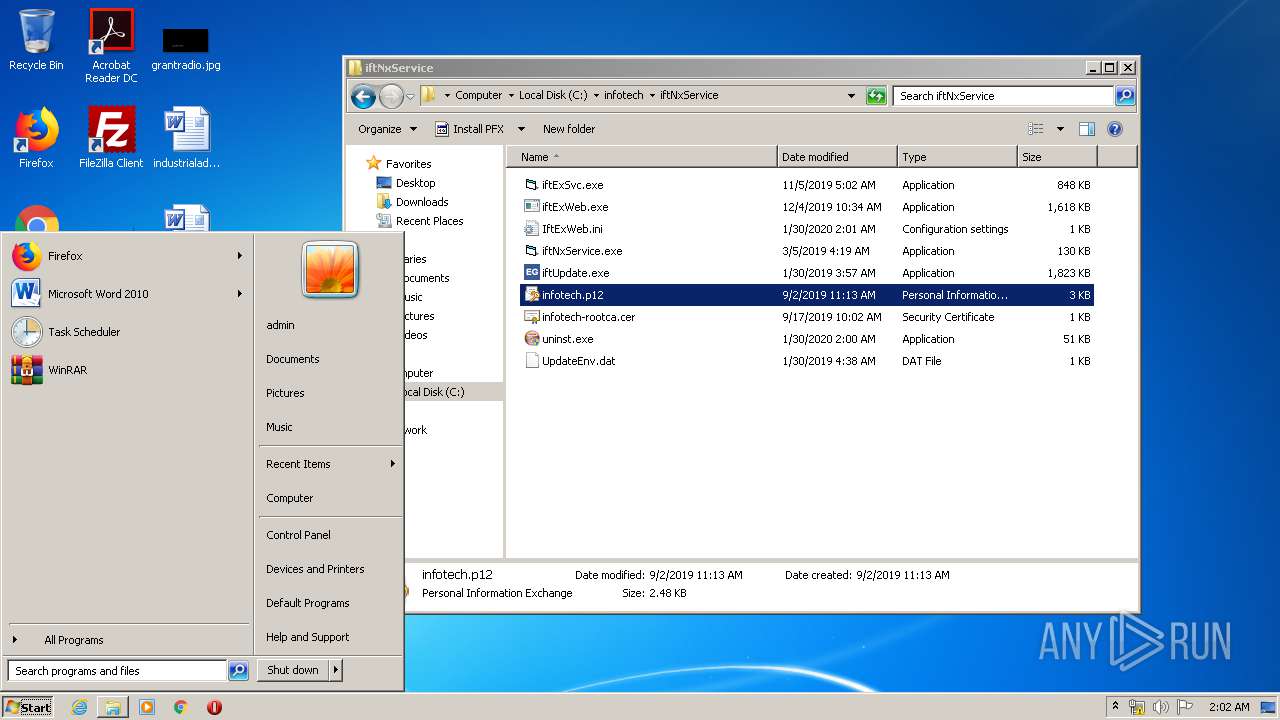
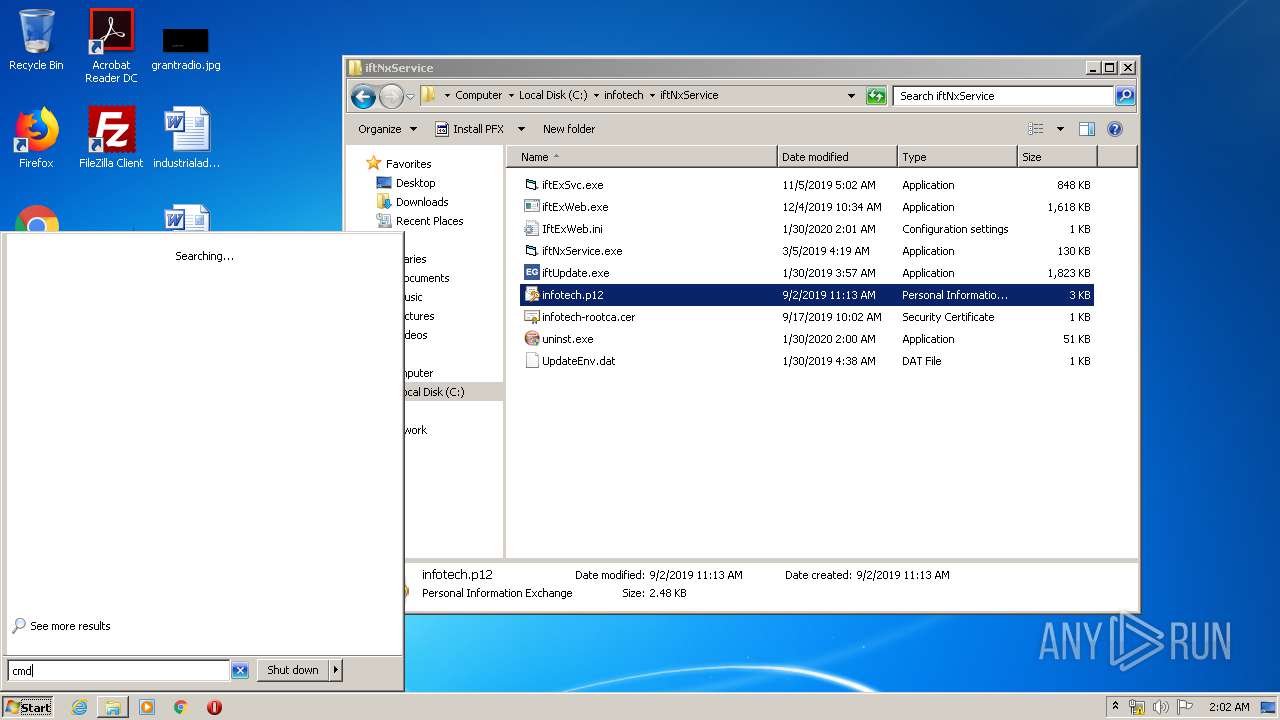
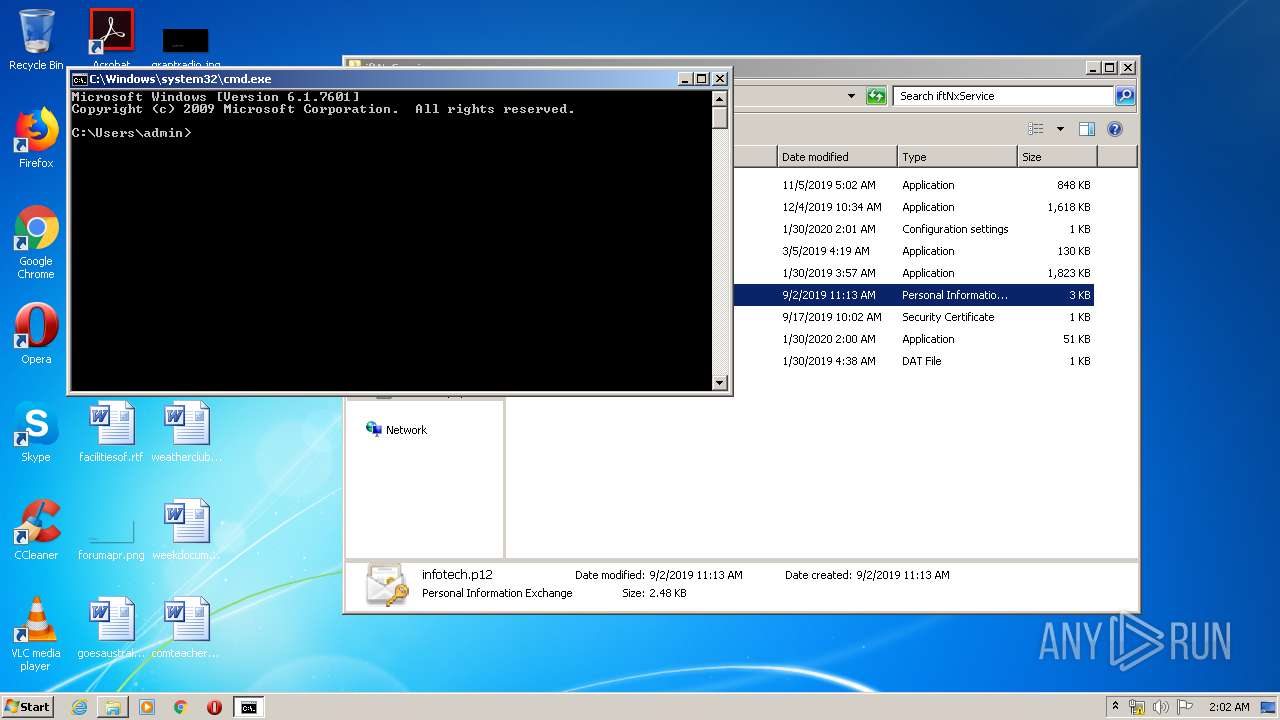
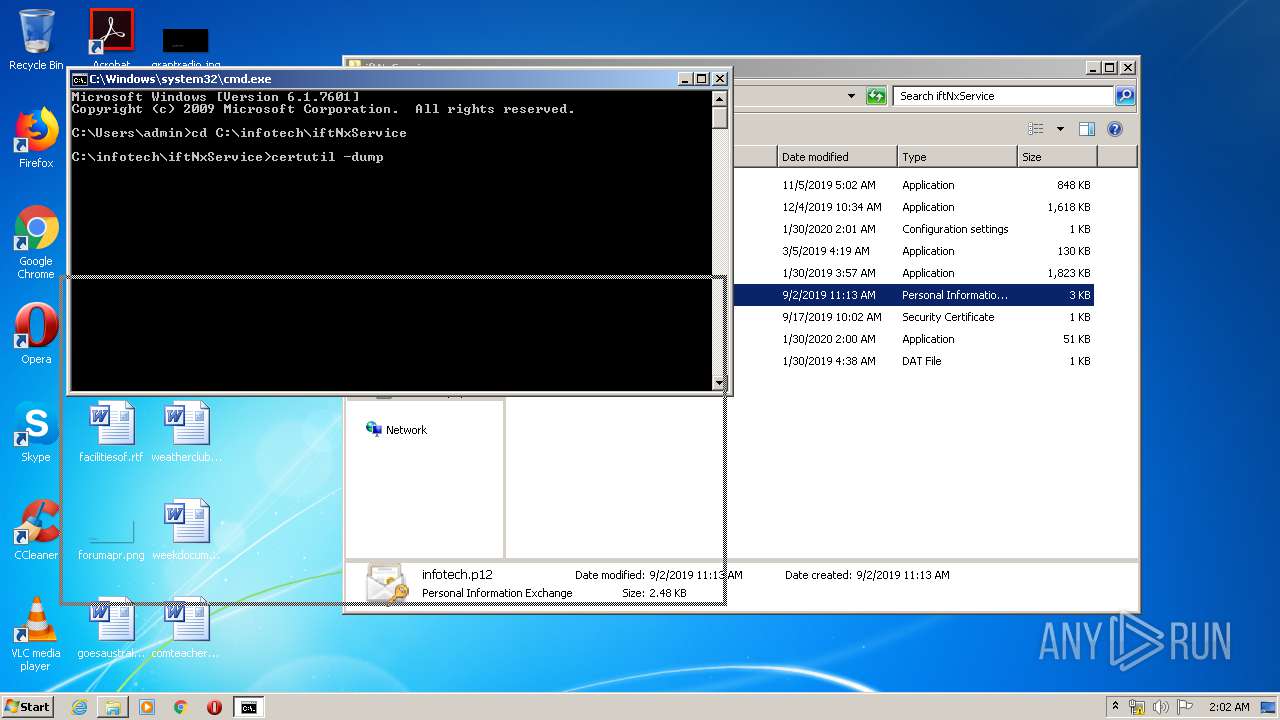
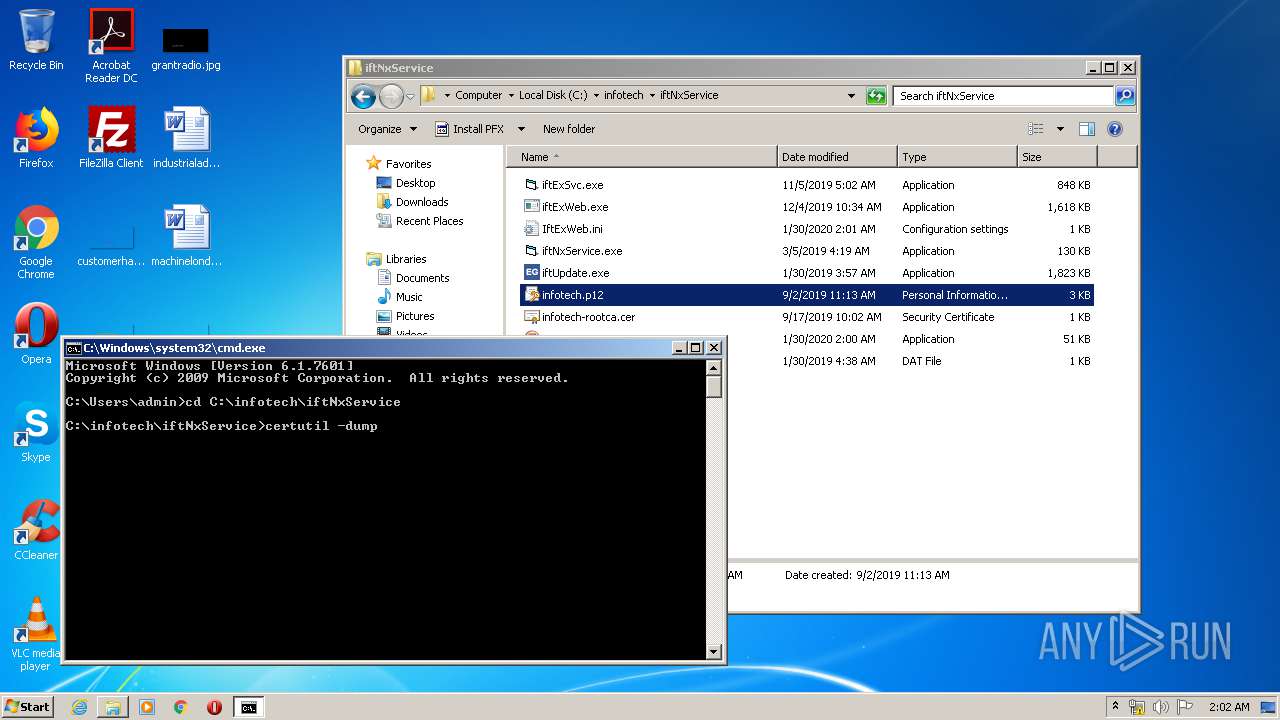
Manual execution by user
- cmd.exe (PID: 2808)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:12:15 23:24:41+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25600 |
| InitializedDataSize: | 162816 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x320c |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Dec-2018 22:24:41 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 15-Dec-2018 22:24:41 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000628F | 0x00006400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.44221 |
.rdata | 0x00008000 | 0x0000135C | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.24004 |
.data | 0x0000A000 | 0x00025518 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.04938 |
.ndata | 0x00030000 | 0x00009000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00039000 | 0x000040D8 | 0x00004200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.99951 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28794 | 1070 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.9993 | 3752 | UNKNOWN | English - United States | RT_ICON |
3 | 6.24459 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 5.01502 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 6.16057 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 3.34146 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 3.04232 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 2.6691 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.68176 | 494 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.86295 | 228 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
51
Monitored processes
9
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
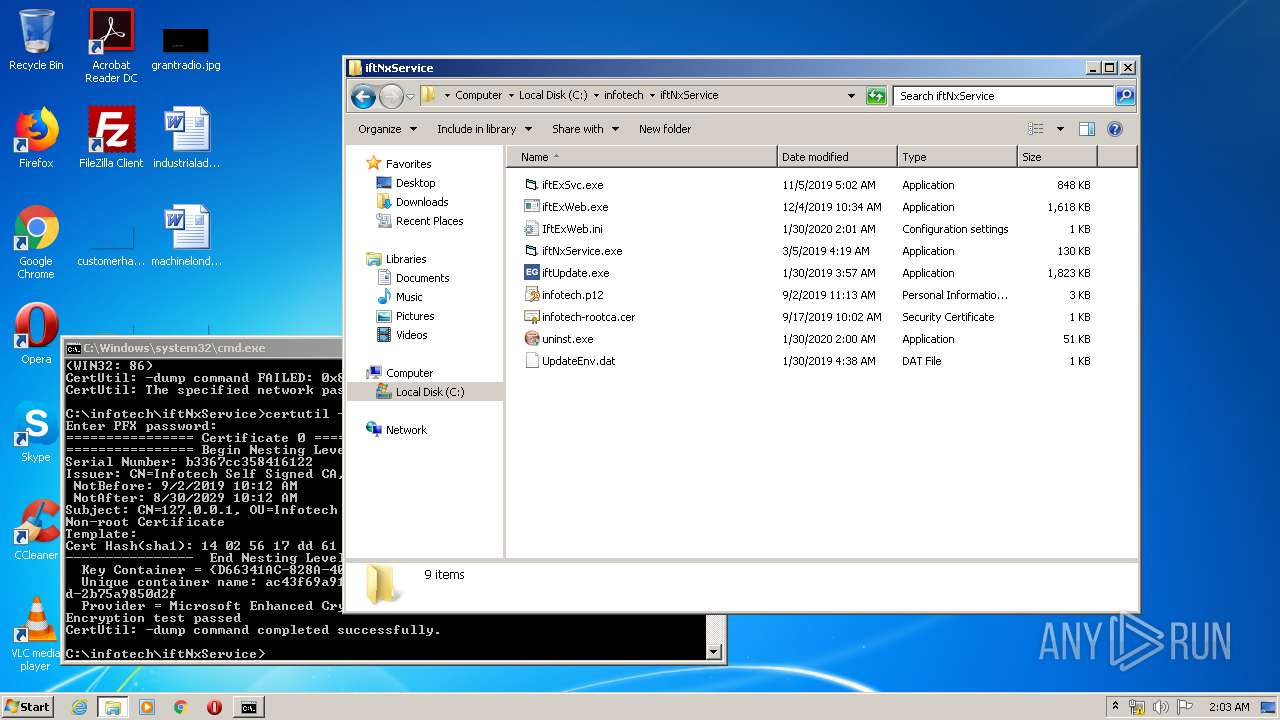
| 780 | certutil -dump infotech.p12 | C:\Windows\system32\certutil.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CertUtil.exe Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
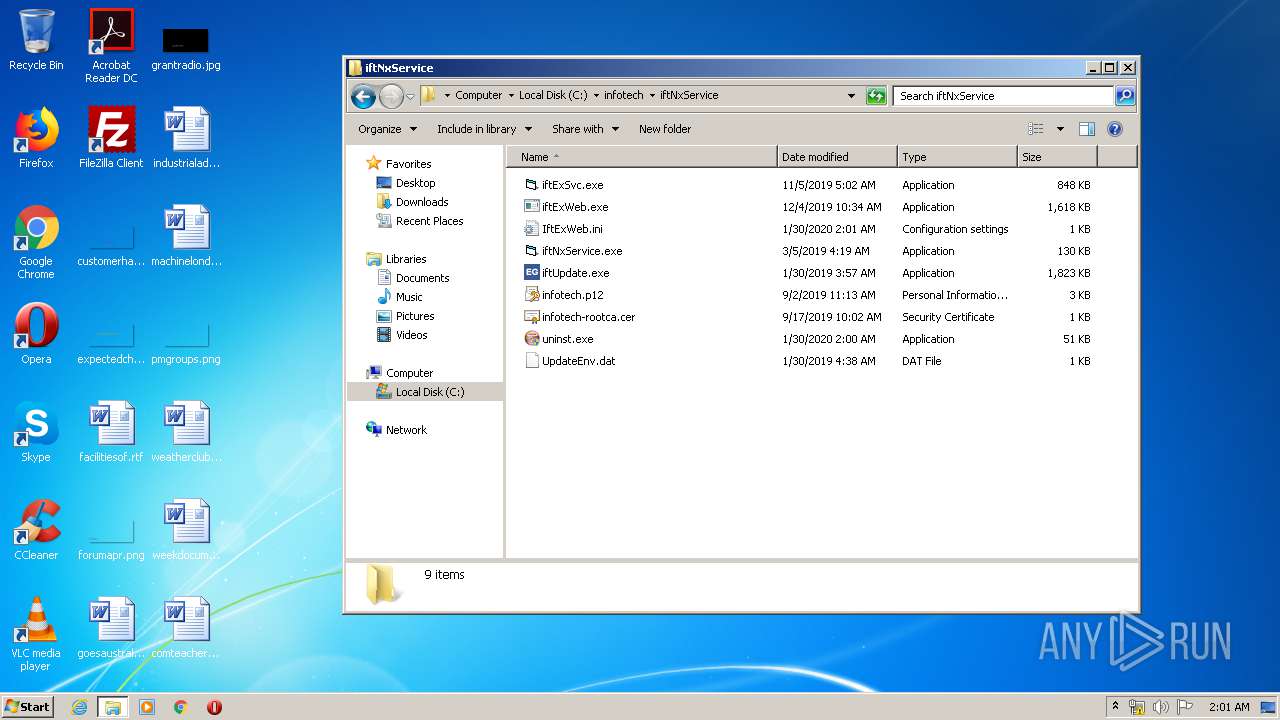
| 916 | c:\infotech\iftNxService\iftExWeb.exe | c:\infotech\iftNxService\iftExWeb.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 1352 | "C:\Users\admin\AppData\Local\Temp\01798128_2.exe" | C:\Users\admin\AppData\Local\Temp\01798128_2.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2184 | "C:\Users\admin\AppData\Local\Temp\01798128_2.exe" | C:\Users\admin\AppData\Local\Temp\01798128_2.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2352 | certutil -dump infotech.p12 | C:\Windows\system32\certutil.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CertUtil.exe Exit code: 2147942486 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2808 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2908 | "C:\Users\admin\AppData\Local\Temp\nsq7BC1.tmp\nsFB23.tmp" "certutil.exe" -f -p infotech@30 -importpfx c:\infotech\iftNxService\infotech.p12 | C:\Users\admin\AppData\Local\Temp\nsq7BC1.tmp\nsFB23.tmp | — | 01798128_2.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3284 | "certutil.exe" -f -p infotech@30 -importpfx c:\infotech\iftNxService\infotech.p12 | C:\Windows\system32\certutil.exe | — | nsFB23.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: CertUtil.exe Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3964 | c:\infotech\iftNxService\iftExWeb.exe -i | c:\infotech\iftNxService\iftExWeb.exe | — | 01798128_2.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
Total events
1 638
Read events
432
Write events
1 202
Delete events
4
Modification events
| (PID) Process: | (2184) 01798128_2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{D5DE8D20-5BB8-11D1-A1E3-00A0C90F2731} |
| Operation: | write | Name: | |
Value: VBPropertyBag | |||
| (PID) Process: | (2184) 01798128_2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{D5DE8D20-5BB8-11D1-A1E3-00A0C90F2731}\InProcServer32 |
| Operation: | write | Name: | |
Value: C:\Windows\system32\msvbvm60.dll | |||
| (PID) Process: | (2184) 01798128_2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{D5DE8D20-5BB8-11D1-A1E3-00A0C90F2731}\InProcServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Apartment | |||
| (PID) Process: | (2184) 01798128_2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{A4C466B8-499F-101B-BB78-00AA00383CBB}\TypeLib |
| Operation: | write | Name: | Version |
Value: 6.0 | |||
| (PID) Process: | (2184) 01798128_2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{A4C46780-499F-101B-BB78-00AA00383CBB}\TypeLib |
| Operation: | write | Name: | Version |
Value: 6.0 | |||
| (PID) Process: | (2184) 01798128_2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\AppID\{3CBCBD39-EB47-4388-972D-80D72AC9D535} |
| Operation: | write | Name: | |
Value: iftCoreEngine | |||
| (PID) Process: | (2184) 01798128_2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\AppID\iftCoreEngine.DLL |
| Operation: | write | Name: | AppID |
Value: {3CBCBD39-EB47-4388-972D-80D72AC9D535} | |||
| (PID) Process: | (2184) 01798128_2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\iftCoreEngine.iftGate.1 |
| Operation: | write | Name: | |
Value: iftGate Class | |||
| (PID) Process: | (2184) 01798128_2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\iftCoreEngine.iftGate.1\CLSID |
| Operation: | write | Name: | |
Value: {88F635D0-C128-4850-BCBE-1AF6AD372A31} | |||
| (PID) Process: | (2184) 01798128_2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\iftCoreEngine.iftGate |
| Operation: | write | Name: | |
Value: iftGate Class | |||
Executable files
25
Suspicious files
4
Text files
29
Unknown types
2
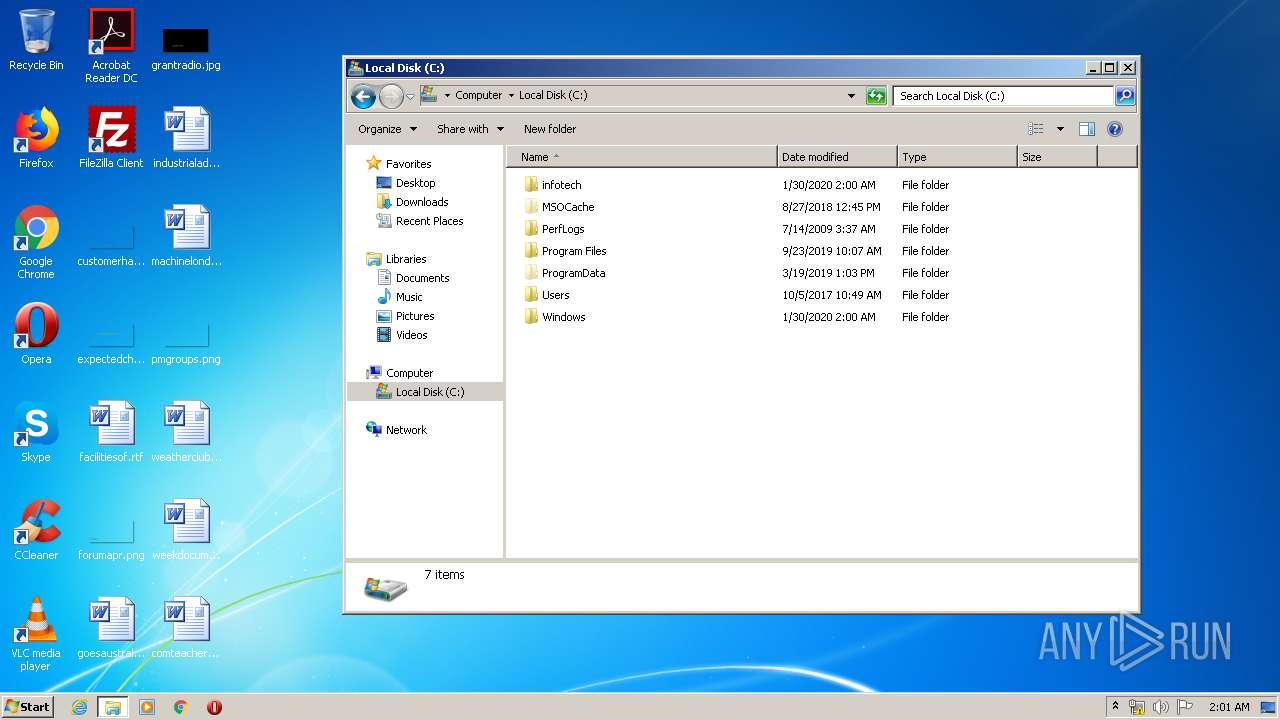
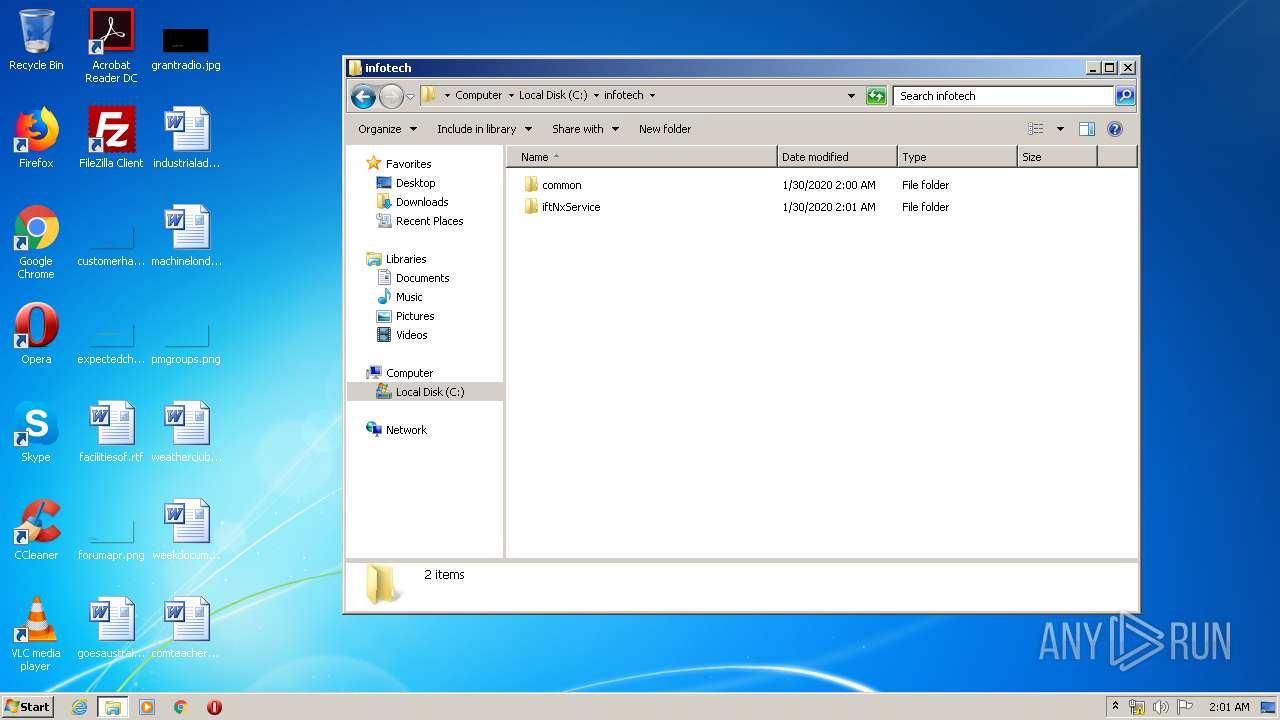
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2184 | 01798128_2.exe | C:\Users\admin\AppData\Local\Temp\nsq7BC1.tmp\ioSpecial.ini | text | |
MD5:— | SHA256:— | |||
| 2184 | 01798128_2.exe | C:\infotech\common\iftWinExSvc.exe | executable | |
MD5:— | SHA256:— | |||
| 2184 | 01798128_2.exe | C:\infotech\common\iftWinExAdapter.dll | executable | |
MD5:— | SHA256:— | |||
| 2184 | 01798128_2.exe | C:\infotech\common\iftCoreEngine.dll | executable | |
MD5:— | SHA256:— | |||
| 2184 | 01798128_2.exe | C:\Users\admin\AppData\Local\Temp\nsq7BC1.tmp\SimpleSC.dll | executable | |
MD5:D63975CE28F801F236C4ACA5AF726961 | SHA256:E0C580BBE48A483075C21277C6E0F23F3CBD6CE3EB2CCD3BF48CF68F05628F43 | |||
| 2184 | 01798128_2.exe | C:\infotech\common\ssleay32.dll | executable | |
MD5:FD6A64E6AE79EB2948FD1AF0C7D259C3 | SHA256:47D2641C300BDBDC8D6BFB23E512E96B5B3FC3037B9B761DBCBA5F9E664C2A17 | |||
| 2184 | 01798128_2.exe | C:\infotech\common\libnspr4.dll | executable | |
MD5:E0B14ED64974C3406A7615B3F90468FF | SHA256:C03549BC7899CAB0A22317F03777380FB1B90D9C76CD25AC0E611E92EE11B7CC | |||
| 2184 | 01798128_2.exe | C:\Users\admin\AppData\Local\Temp\nsq7BC1.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 2184 | 01798128_2.exe | C:\infotech\common\msvcr120.dll | executable | |
MD5:034CCADC1C073E4216E9466B720F9849 | SHA256:86E39B5995AF0E042FCDAA85FE2AEFD7C9DDC7AD65E6327BD5E7058BC3AB615F | |||
| 2184 | 01798128_2.exe | C:\infotech\common\mozjs-24.dll | executable | |
MD5:F77DD66FAC3FA72385FD6AF5B4C69894 | SHA256:6C3CDEC4CEFC586C55746B143A815293F06BD7F9812E17BAC03823219323F53F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report