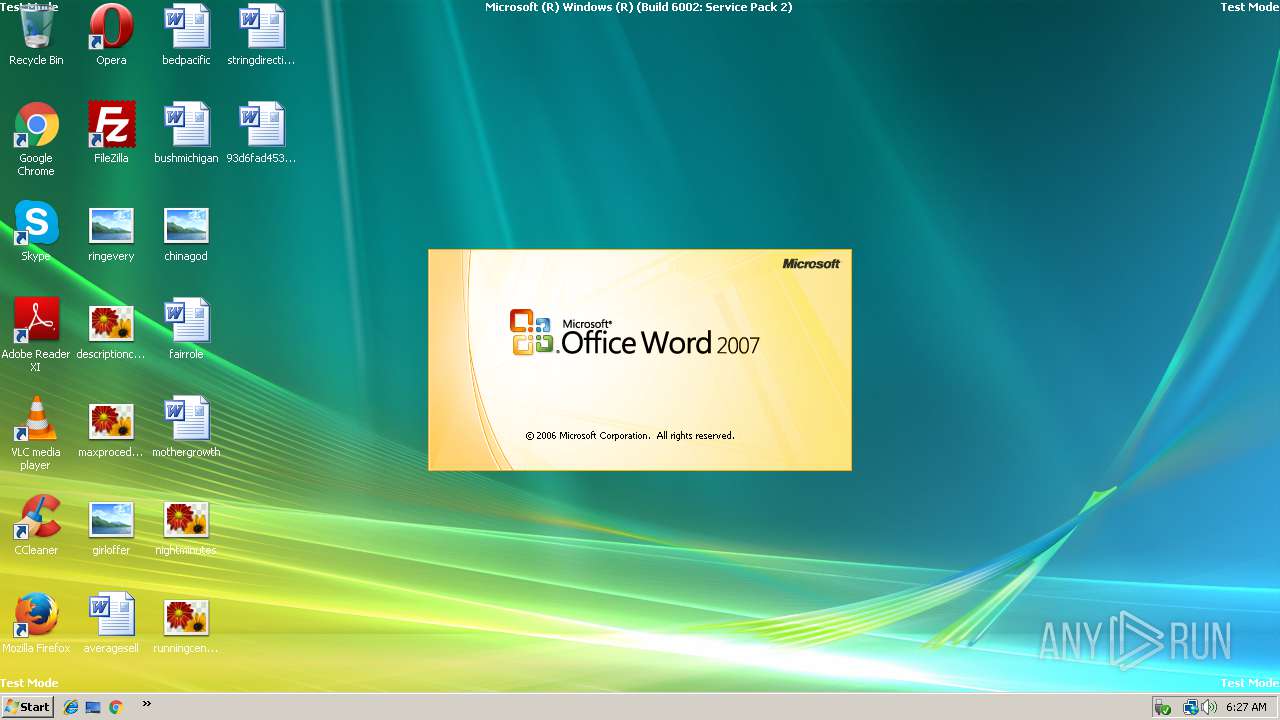
| File name: | 93d6fad4530958a6c48cb45b34d8f531ca132bab23462362.rtf |
| Full analysis: | https://app.any.run/tasks/189120f4-b1ed-4bc3-9266-4f278ce3a01c |
| Verdict: | Malicious activity |
| Analysis date: | January 18, 2019, 06:26:42 |
| OS: | Windows Vista Business Service Pack 2 (build: 6002, 64 bit) |
| Indicators: | |
| MIME: | text/rtf |
| File info: | Rich Text Format data, unknown version |
| MD5: | A3F72730D90B8A695D2E67CE24955E45 |
| SHA1: | 93D6FAD4530958A6C48CB45B34D8F531CA132BAB |
| SHA256: | D3658E835ABF468584629D6FFD5A92A9547EBC1955F99E26F1075870C98025C4 |
| SSDEEP: | 1536:3zfUoyfpfSdN5GDajbbH6jN9wGgDlc+bt94yH6:3zfFbbaAjjC |
MALICIOUS
Suspicious connection from the Equation Editor
- EQNEDT32.EXE (PID: 1752)
SUSPICIOUS
Creates files in the user directory
- WINWORD.EXE (PID: 2240)
Reads Internet Cache Settings
- EQNEDT32.EXE (PID: 1752)
Reads the machine GUID from the registry
- WINWORD.EXE (PID: 2240)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2240)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rtf | | | Rich Text Format (100) |
|---|
Total processes
36
Monitored processes
3
Malicious processes
1
Suspicious processes
0
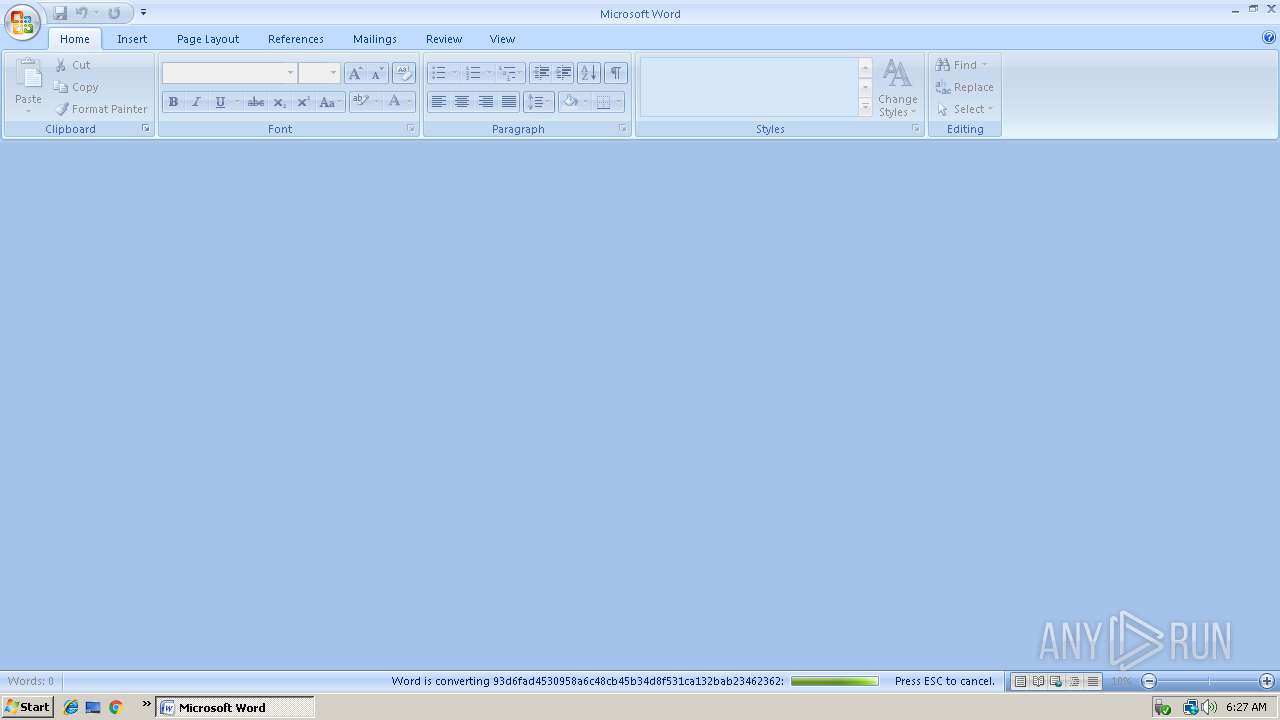
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1752 | "C:\Program Files (x86)\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files (x86)\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
| 2240 | "C:\Program Files (x86)\Microsoft Office\Office12\WINWORD.EXE" /n /dde | C:\Program Files (x86)\Microsoft Office\Office12\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Office Word Exit code: 0 Version: 12.0.4518.1014 Modules
| |||||||||||||||
| 2692 | splwow64 | C:\Windows\splwow64.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Thunking Spooler APIS from 32 to 64 Process Exit code: 0 Version: 6.0.6001.18000 (longhorn_rtm.080118-1840) Modules
| |||||||||||||||
Total events
236
Read events
211
Write events
21
Delete events
4
Modification events
| (PID) Process: | (2240) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\12.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | {n4 |
Value: 7B6E3400C0080000010000000000000000000000 | |||
| (PID) Process: | (2240) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\12.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2240) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\12.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2240) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00002119210000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1311899659 | |||
| (PID) Process: | (2240) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00002119210000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1311899667 | |||
| (PID) Process: | (2240) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00002119210000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1311899668 | |||
| (PID) Process: | (2240) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\12.0\Word |
| Operation: | write | Name: | MTTT |
Value: C0080000949D28D9F6AED40100000000 | |||
| (PID) Process: | (2240) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00002119210000000000000000F01FEC\Usage |
| Operation: | write | Name: | EXCELFiles |
Value: 1311899660 | |||
| (PID) Process: | (2240) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\12.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ls4 |
Value: 6C733400C008000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2240) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\MountPoints2\{74a12f5d-6e42-11e8-b514-806e6f6e6963} |
| Operation: | write | Name: | BaseClass |
Value: Drive | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2240 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2240 | WINWORD.EXE | C:\Users\admin\Desktop\~$d6fad4530958a6c48cb45b34d8f531ca132bab23462362.rtf | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
2
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1752 | EQNEDT32.EXE | GET | — | 51.75.90.104:80 | http://goone-88.ga/z.exe | GB | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1752 | EQNEDT32.EXE | 51.75.90.104:80 | goone-88.ga | — | GB | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
wpad |
| unknown |
goone-88.ga |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1044 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .ga Domain |