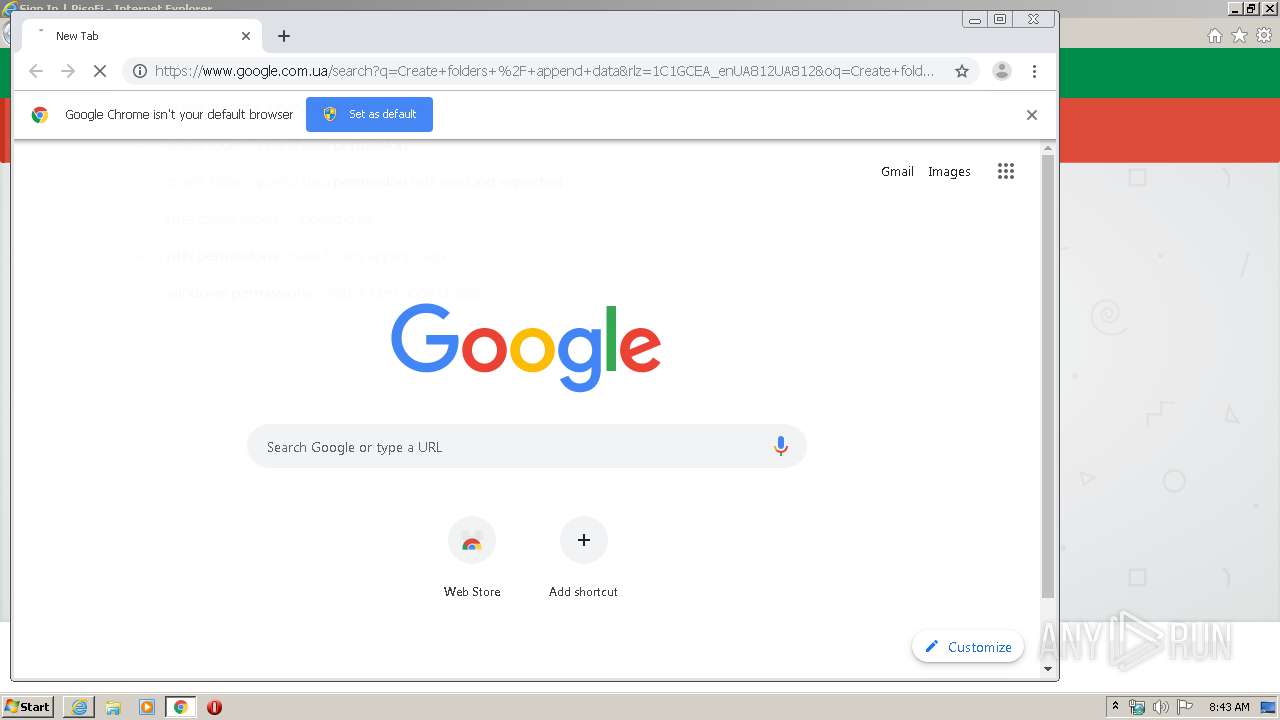
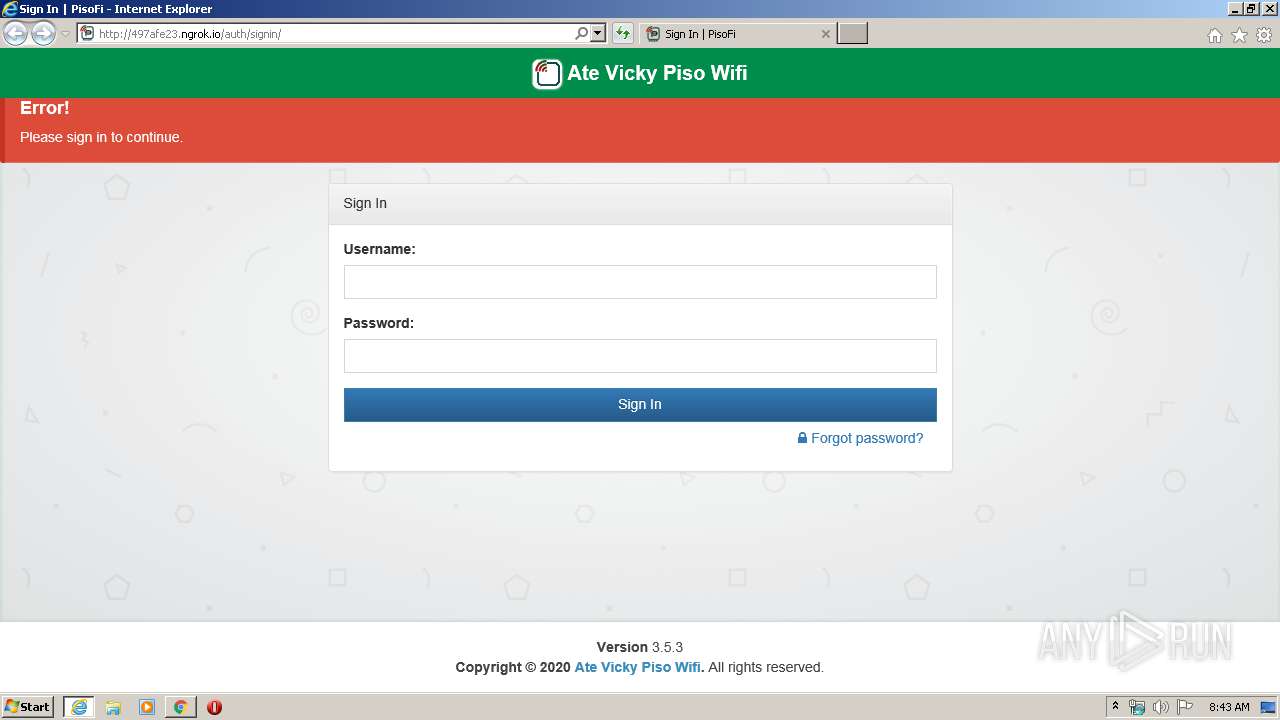
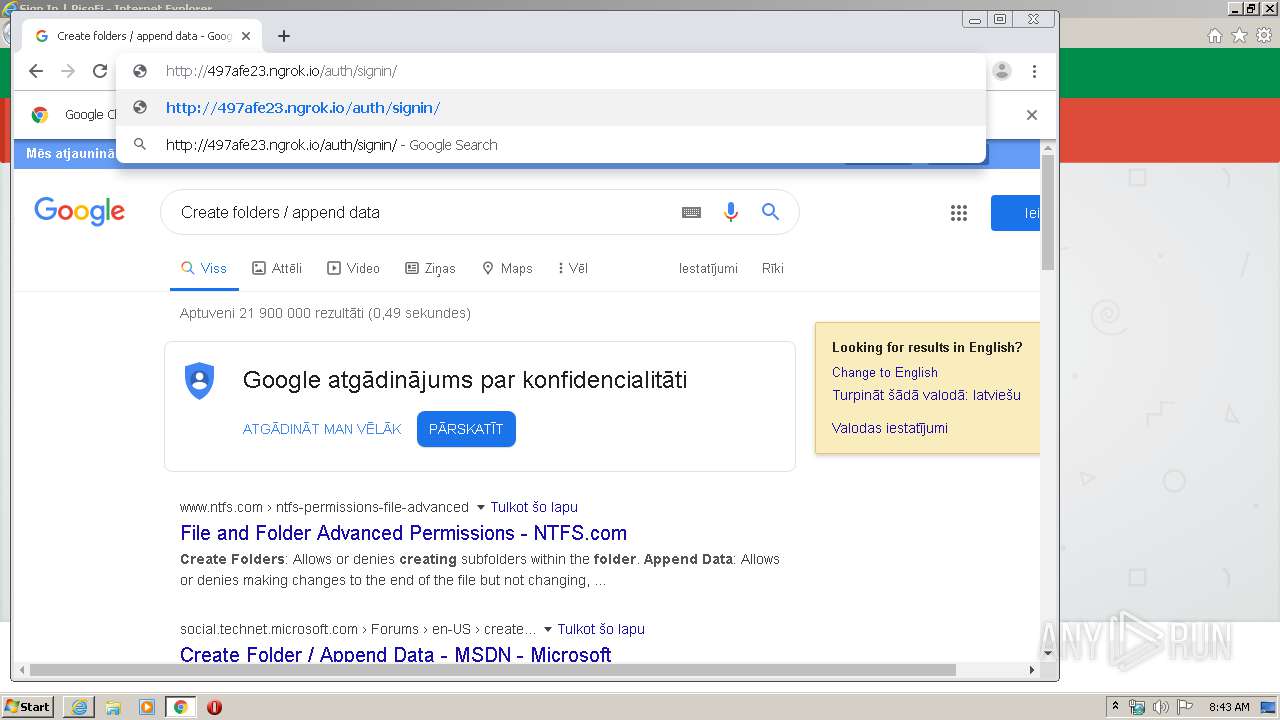
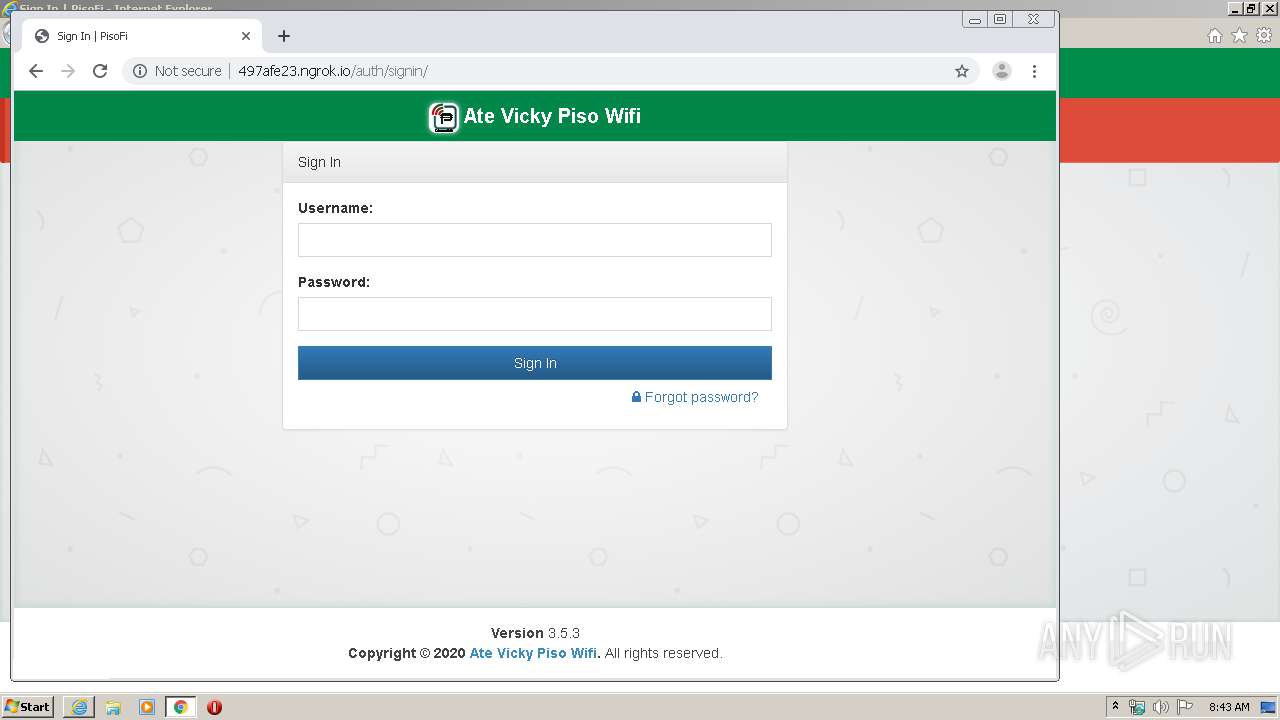
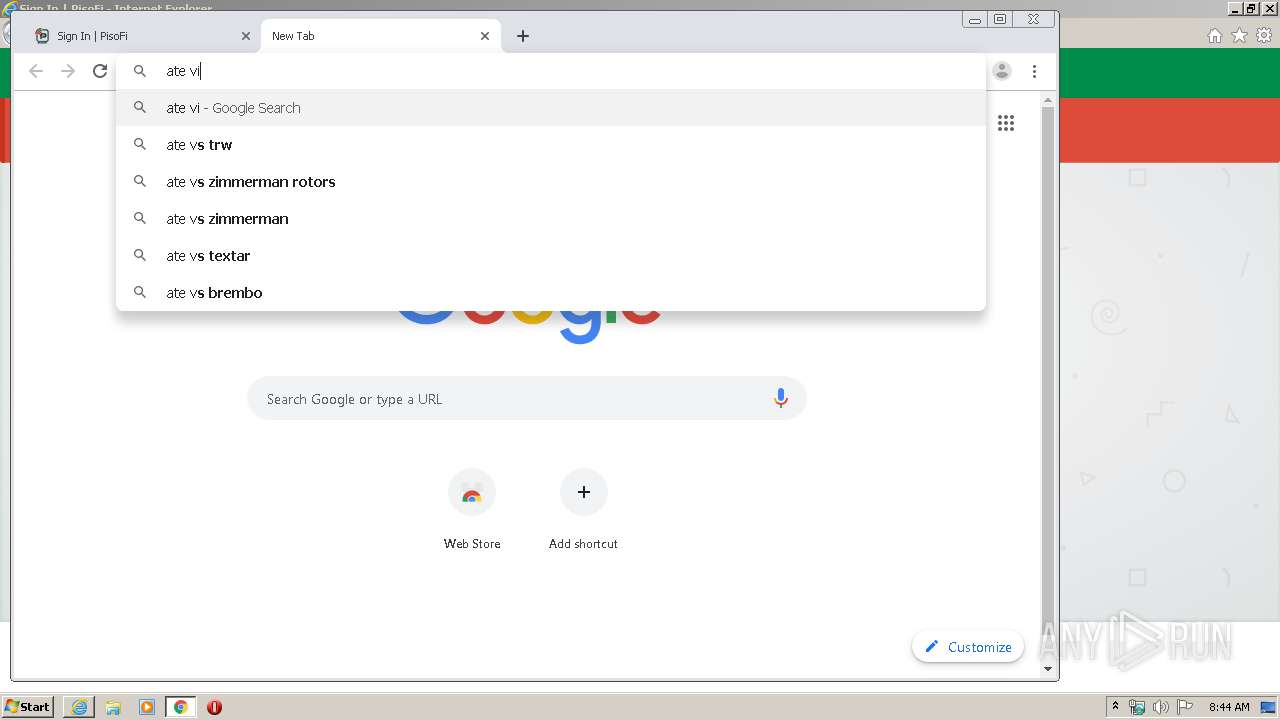
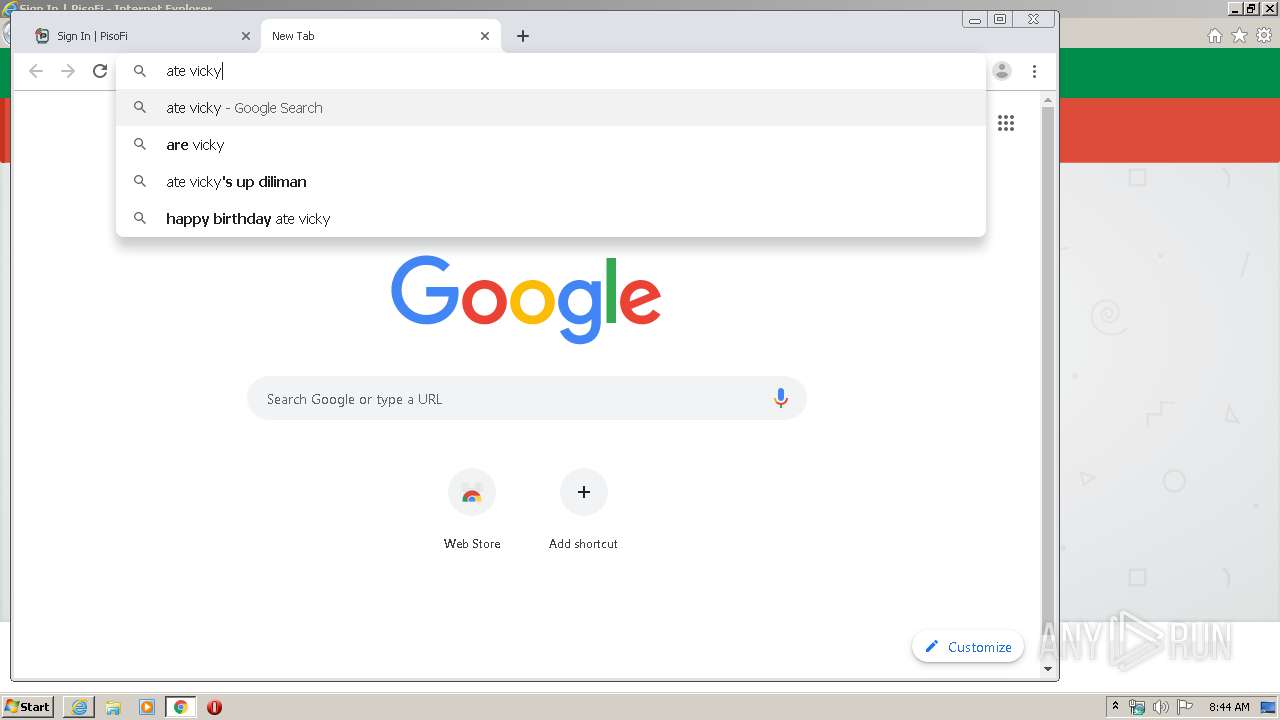
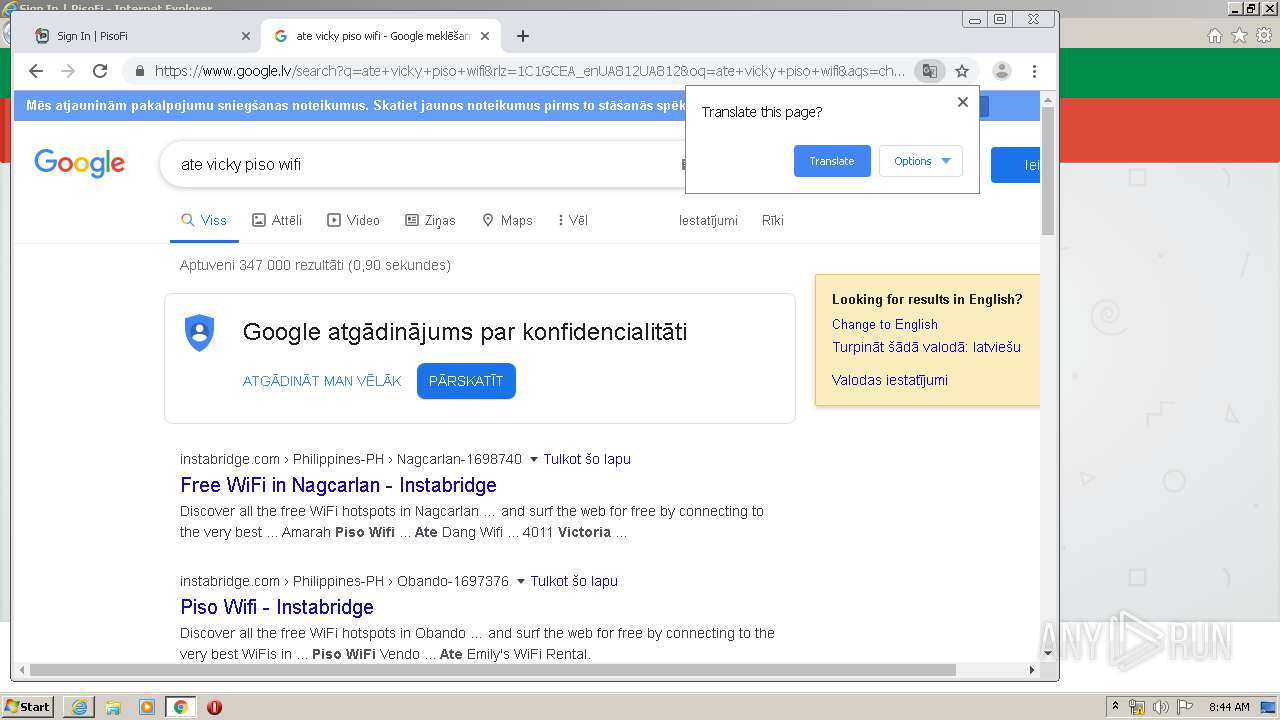
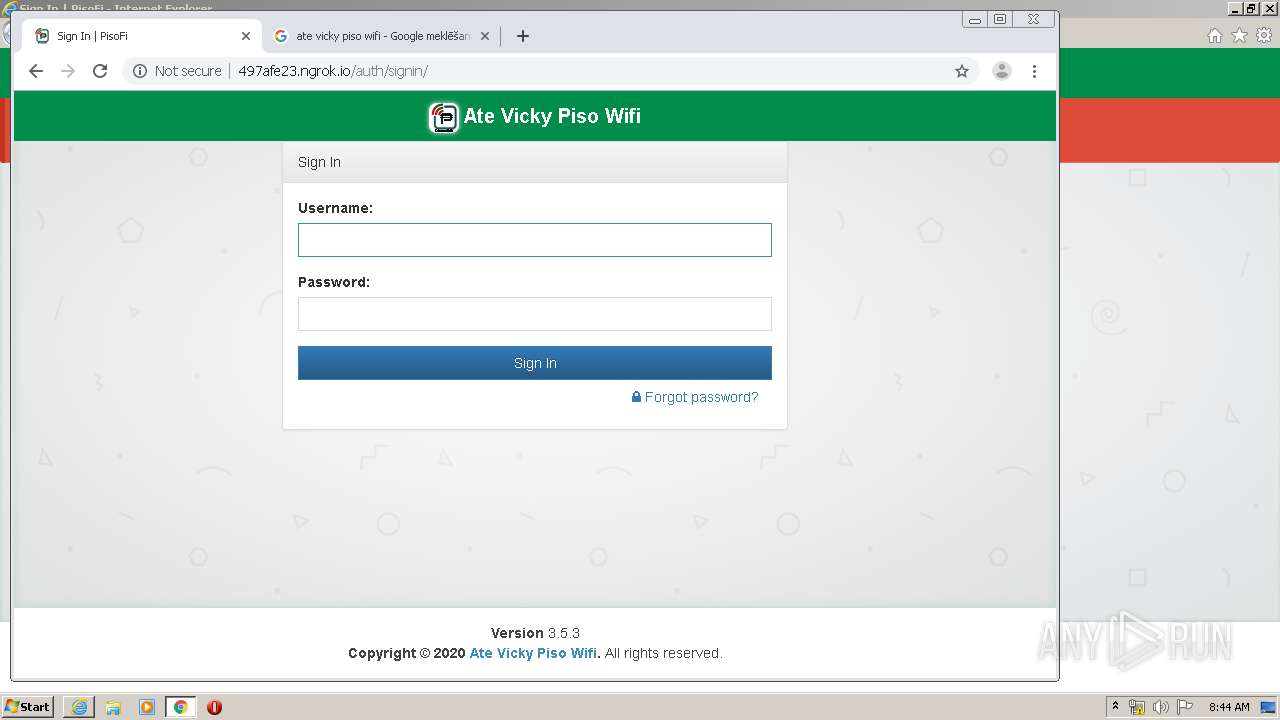
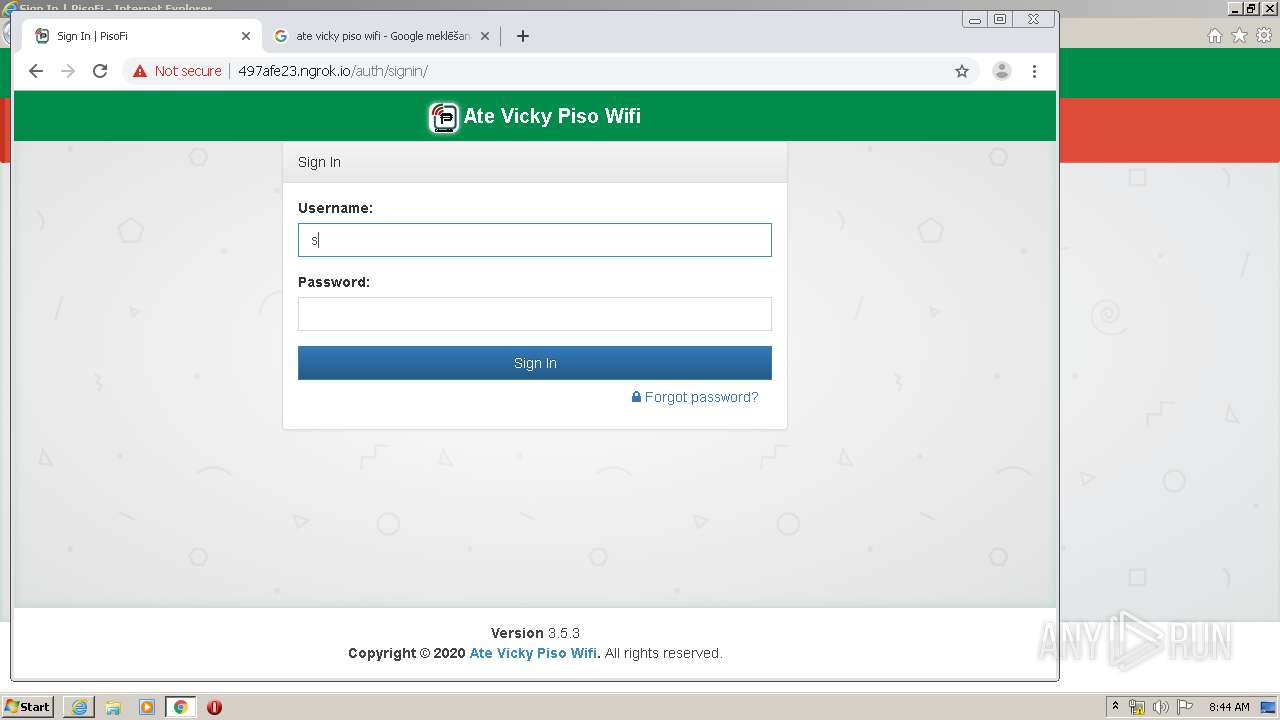
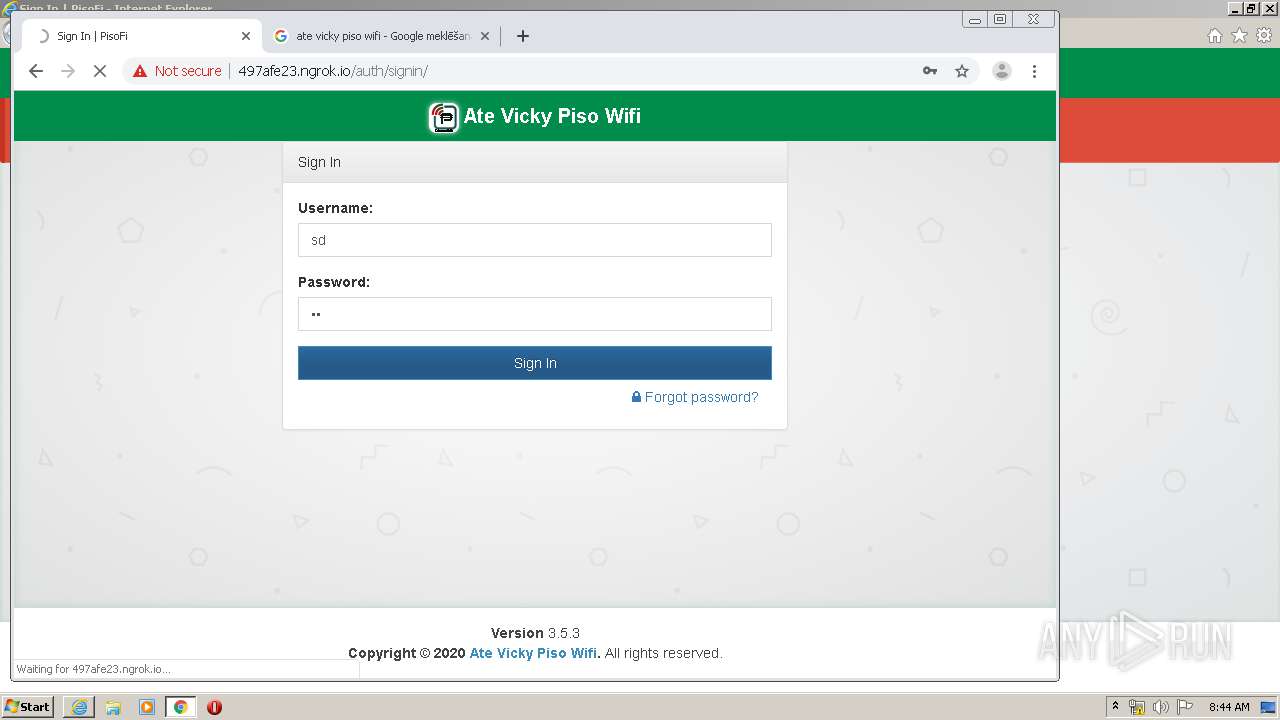
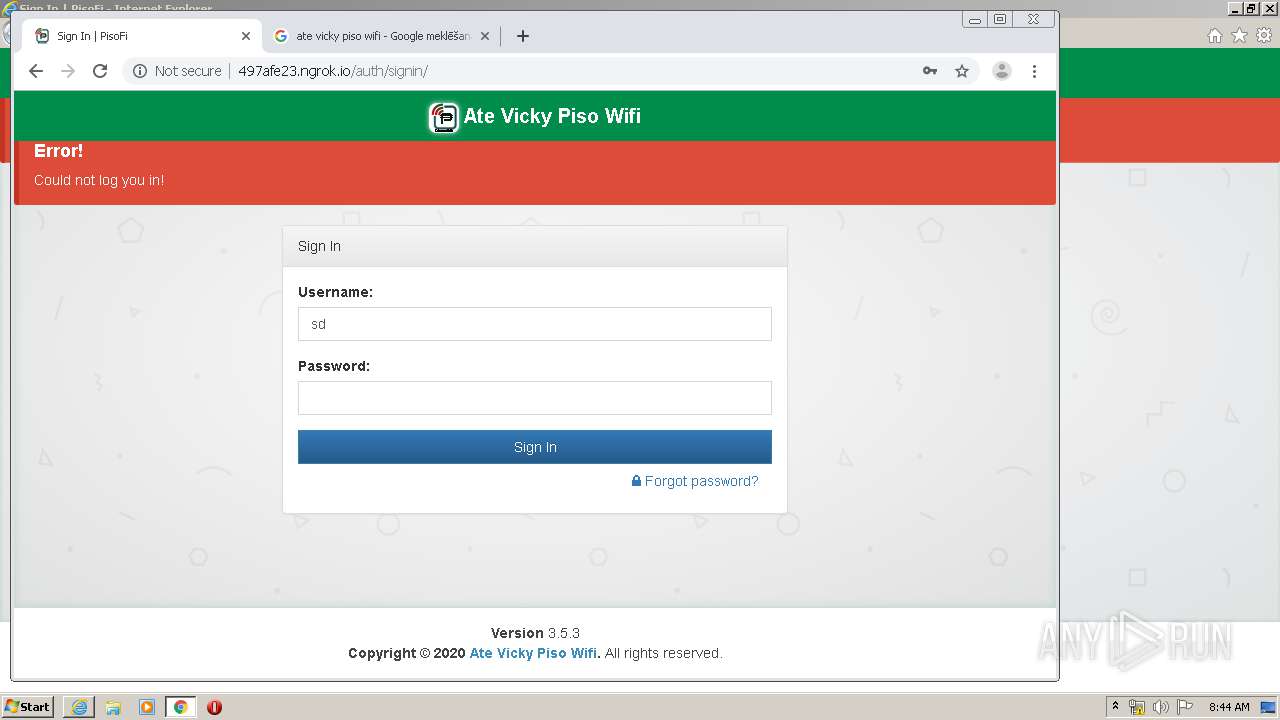
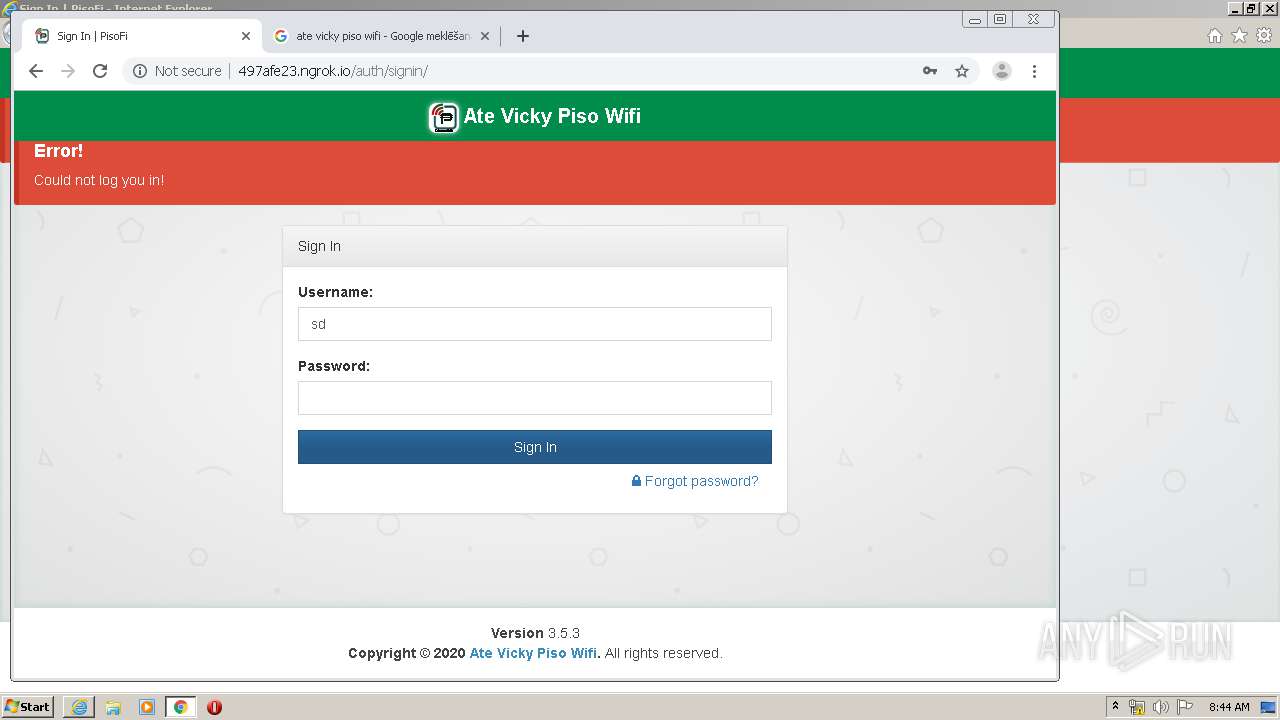
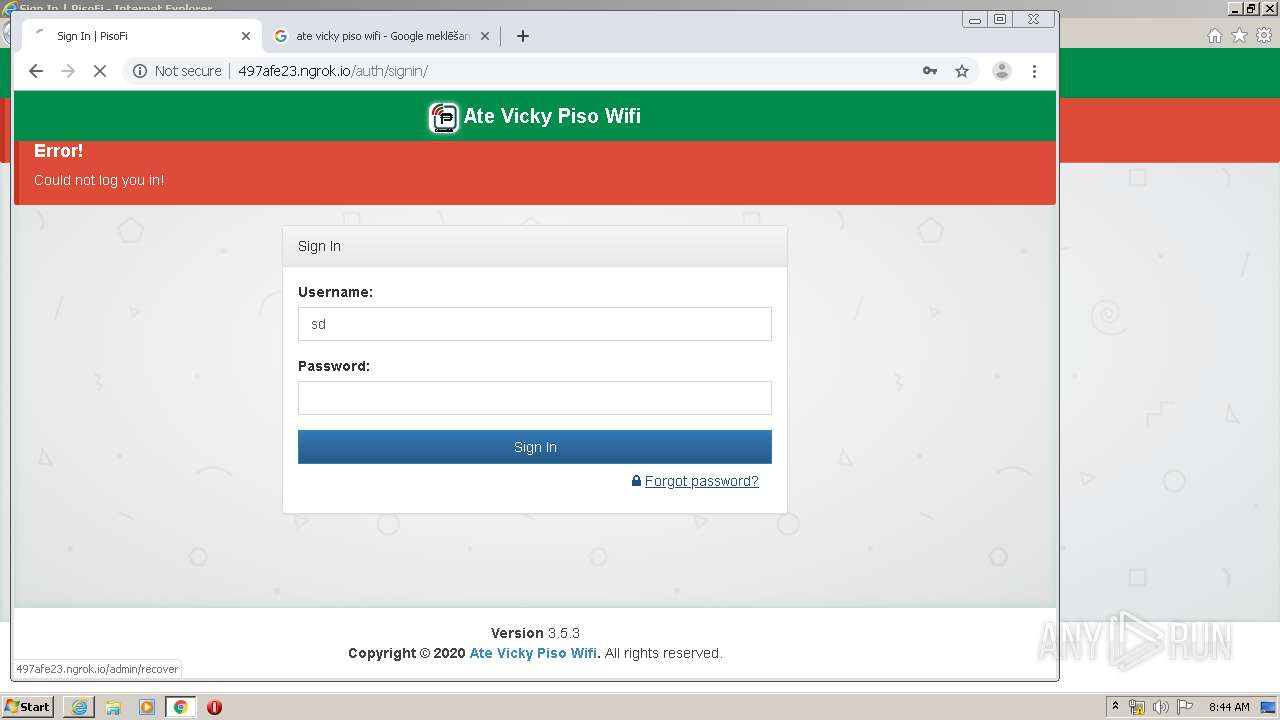
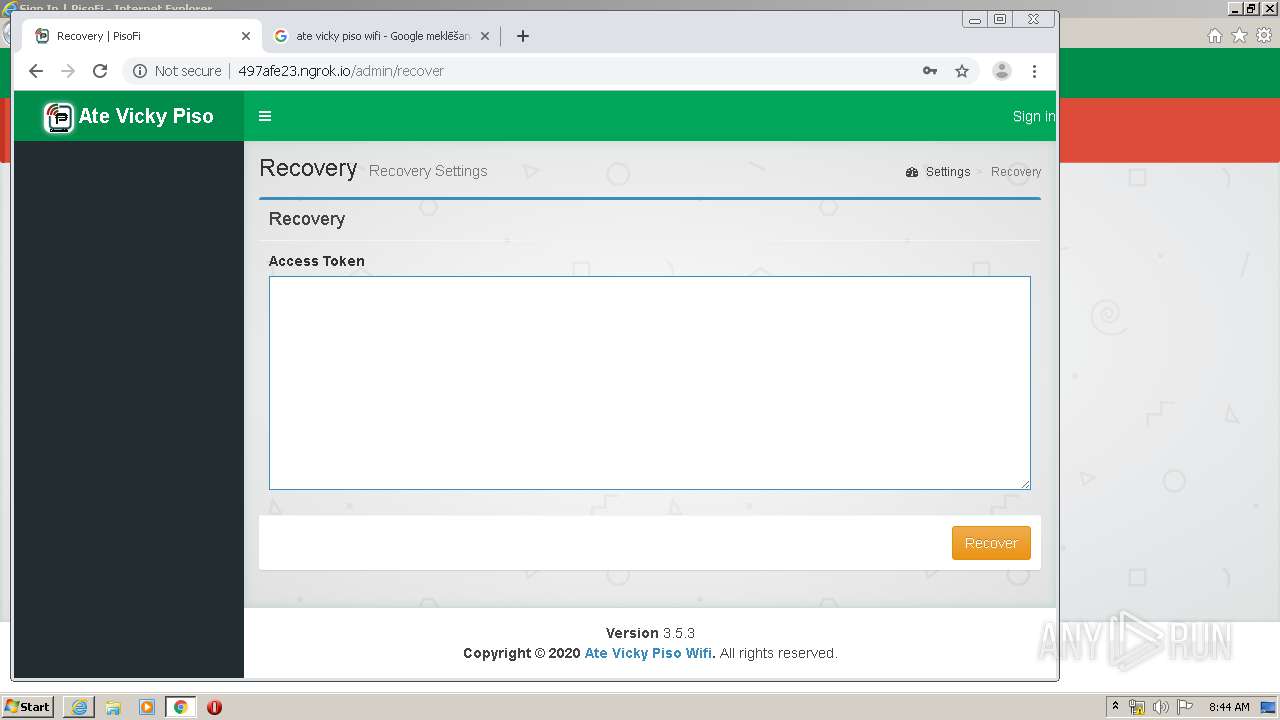
| URL: | http://497afe23.ngrok.io |
| Full analysis: | https://app.any.run/tasks/7b66ba65-262a-4449-a391-ff54b2316268 |
| Verdict: | Malicious activity |
| Analysis date: | February 26, 2020, 08:42:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 9F202A06B26EB8F57F1A7FA9653C189D |
| SHA1: | B798C580936DD5816DF5CC24CADA5B9E20D6CC34 |
| SHA256: | D3610EA9891CB31340CC96570B99A9712A4A5E7F2C59A7EC86F6AD324FA96419 |
| SSDEEP: | 3:N1KXh/CXKw:CXMXB |
MALICIOUS
No malicious indicators.SUSPICIOUS
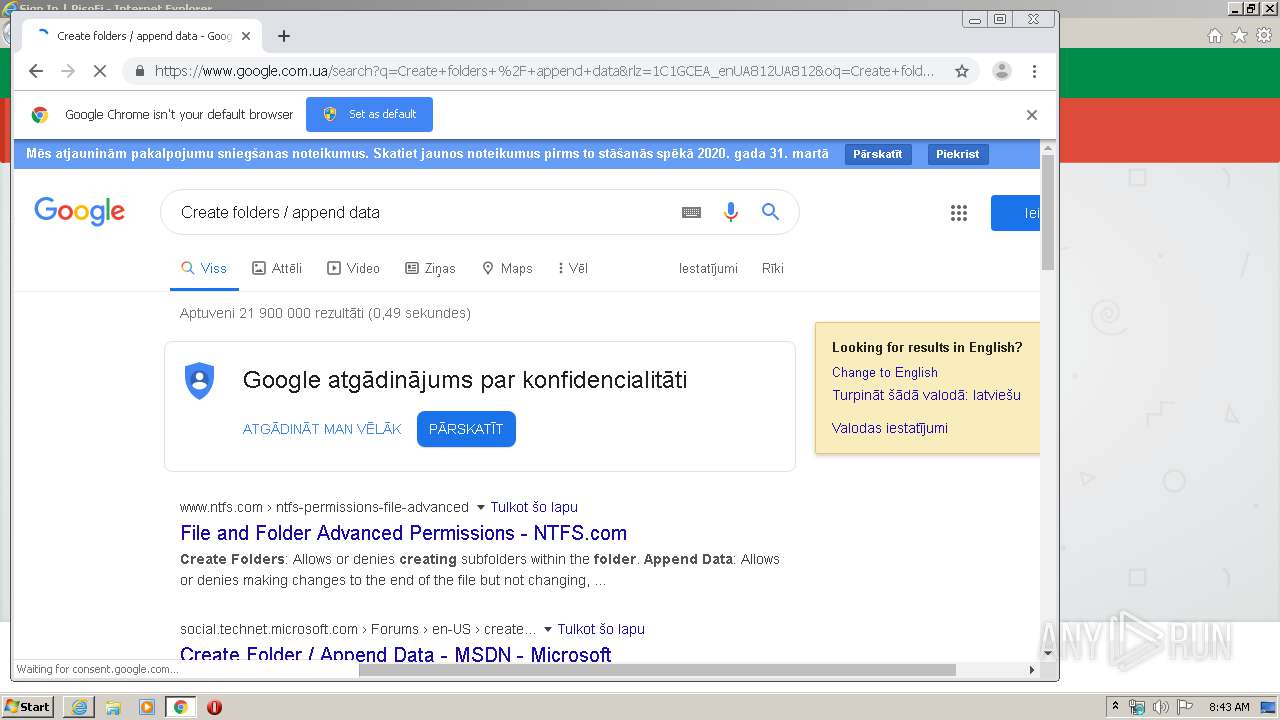
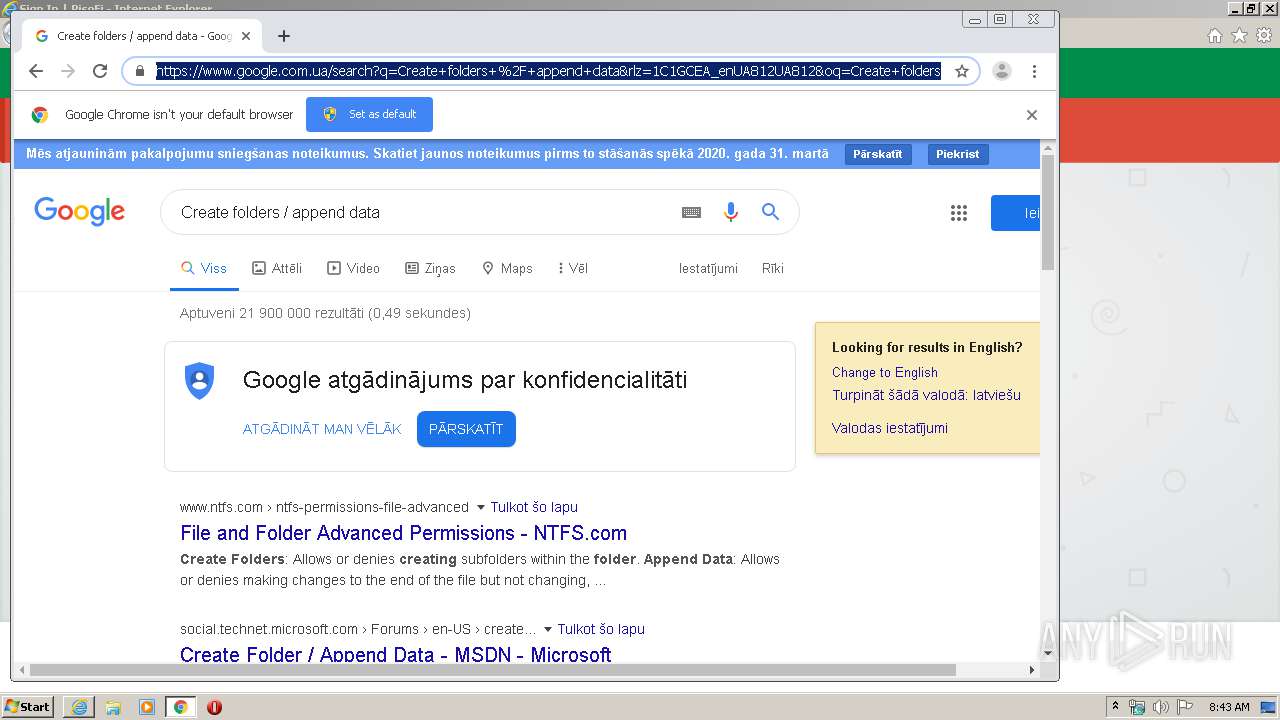
Modifies files in Chrome extension folder
- chrome.exe (PID: 2636)
INFO
Changes internet zones settings
- iexplore.exe (PID: 1720)
Reads Internet Cache Settings
- iexplore.exe (PID: 1720)
- iexplore.exe (PID: 3840)
Reads internet explorer settings
- iexplore.exe (PID: 3840)
Reads the hosts file
- chrome.exe (PID: 1632)
- chrome.exe (PID: 2636)
Creates files in the user directory
- iexplore.exe (PID: 1720)
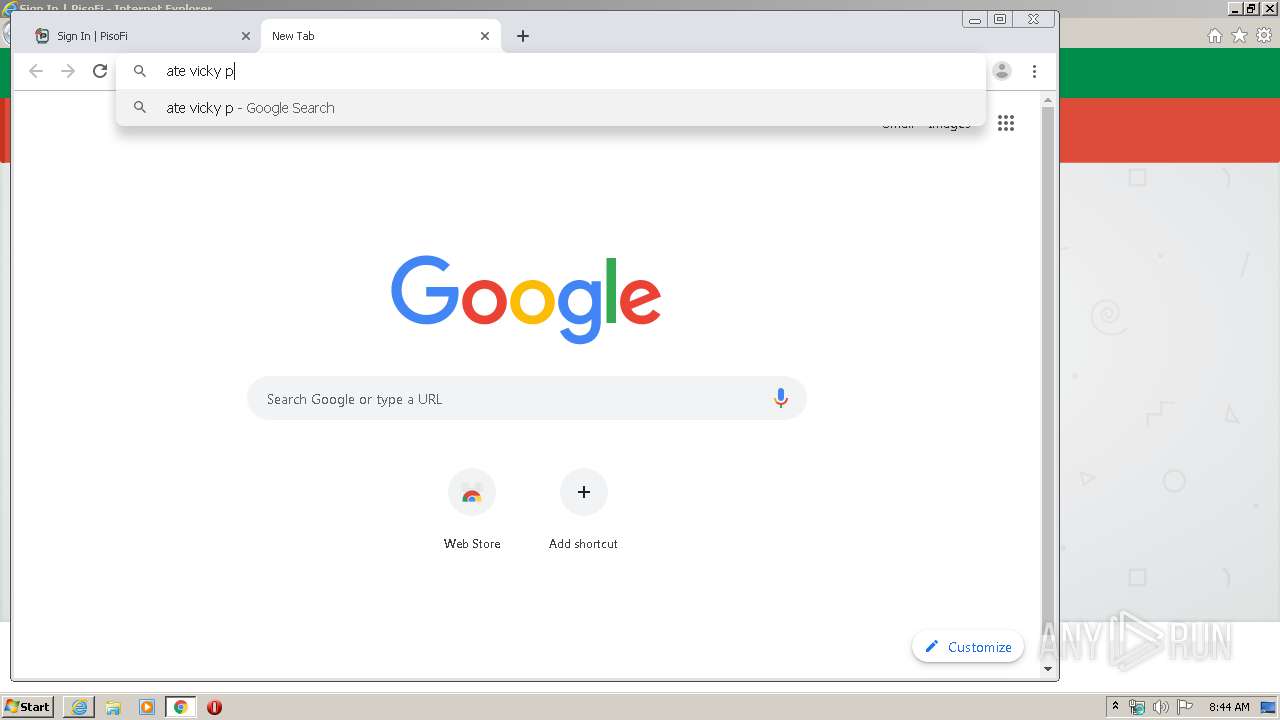
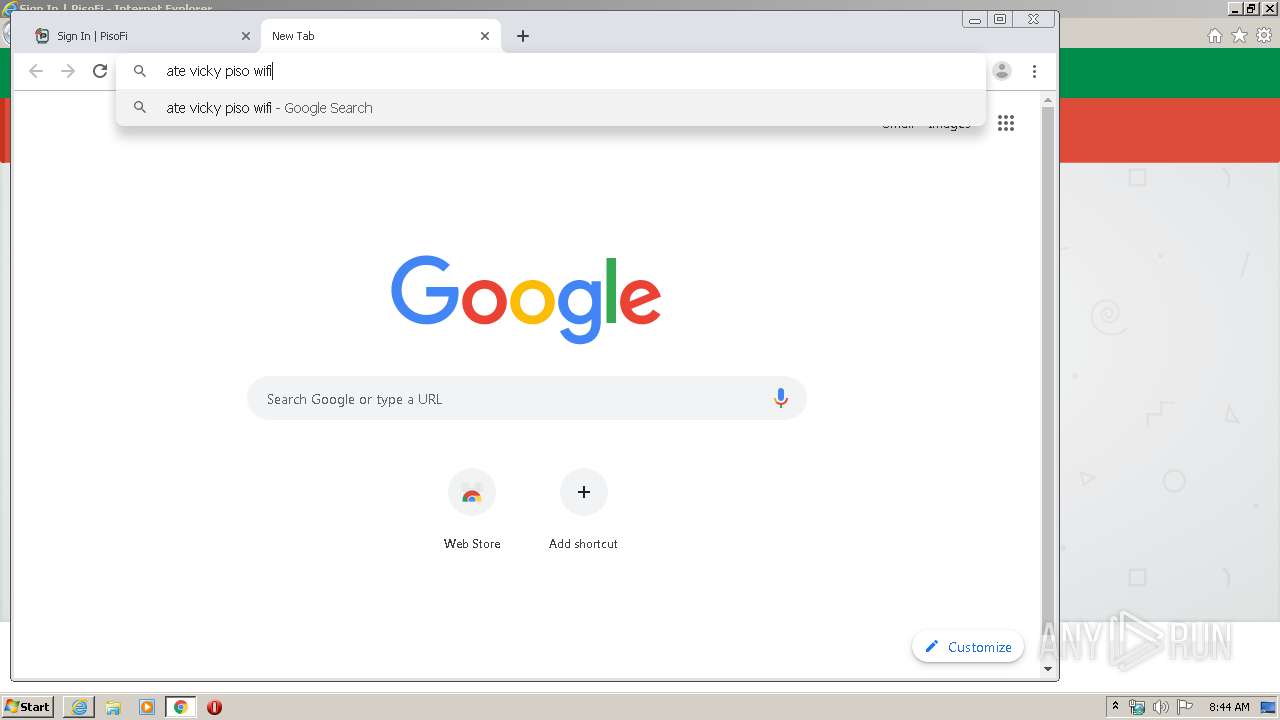
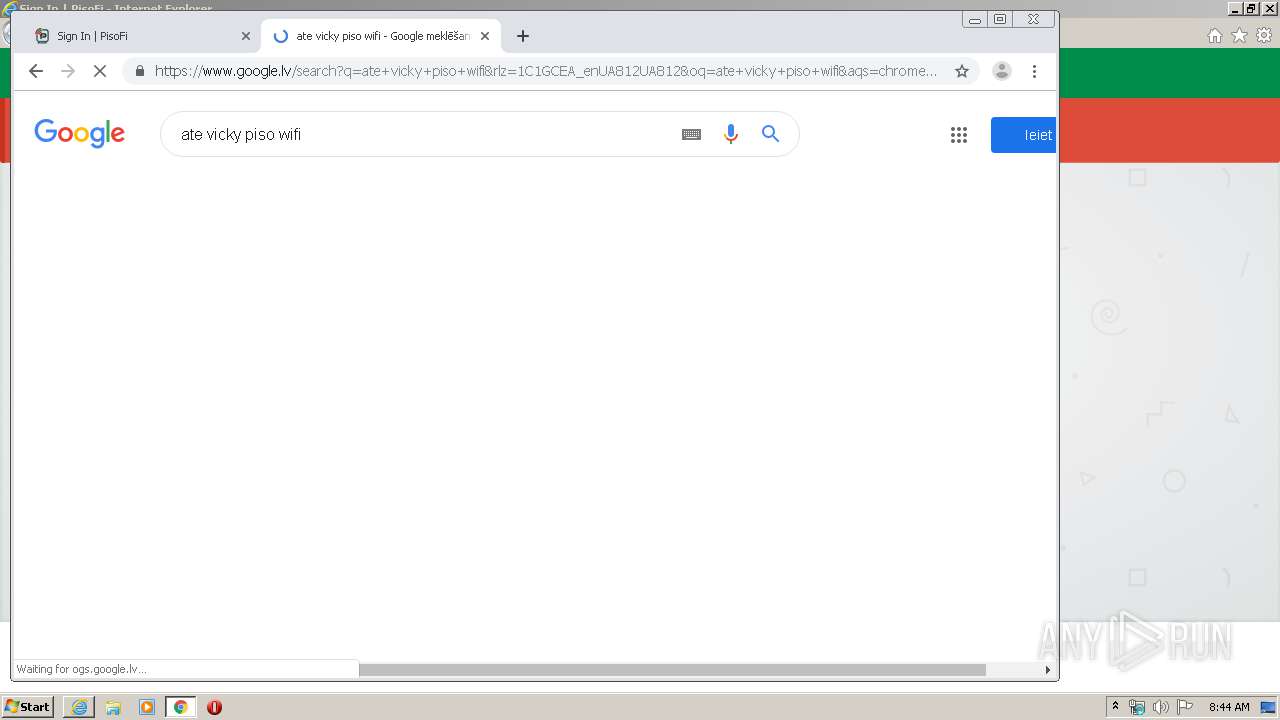
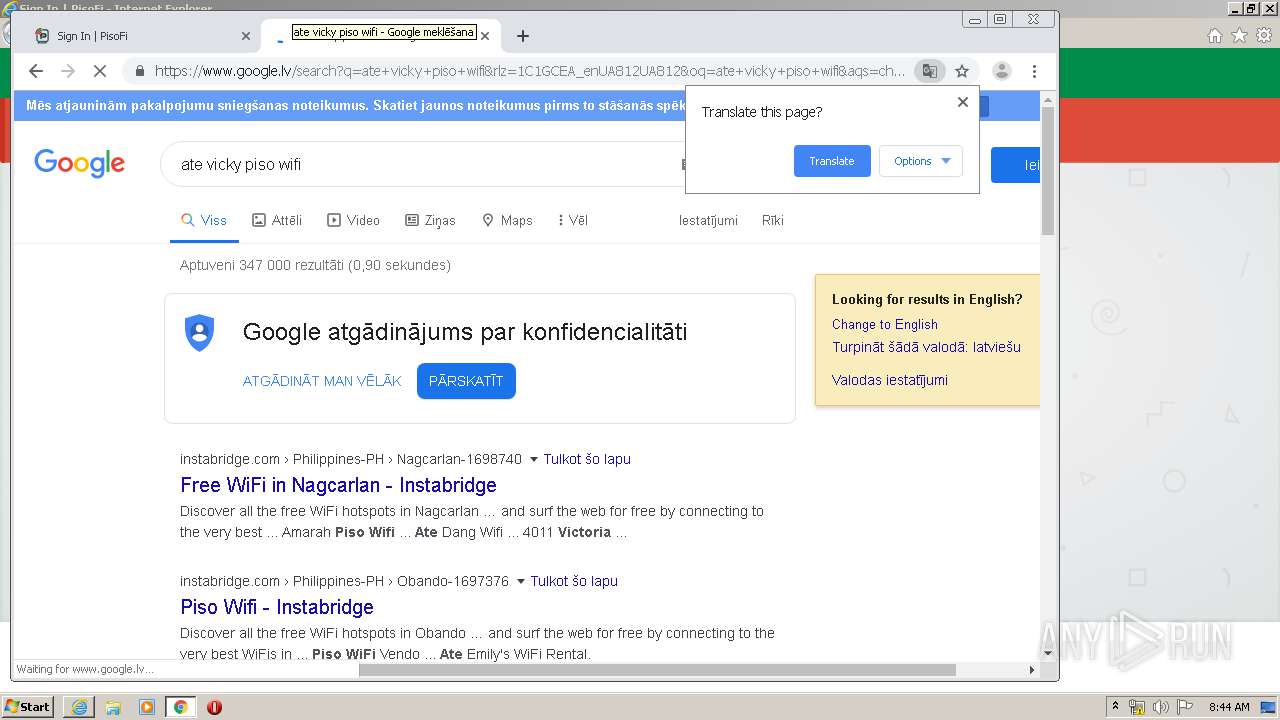
Manual execution by user
- chrome.exe (PID: 2636)
Application launched itself
- chrome.exe (PID: 2636)
Reads settings of System Certificates
- chrome.exe (PID: 1632)
- iexplore.exe (PID: 1720)
Changes settings of System certificates
- iexplore.exe (PID: 1720)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1720)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
74
Monitored processes
37
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,12544525212821876556,8897476227072087094,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17497688016538261032 --renderer-client-id=28 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4344 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,12544525212821876556,8897476227072087094,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16867841161537111372 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2272 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,12544525212821876556,8897476227072087094,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12726087827186934227 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3560 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,12544525212821876556,8897476227072087094,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=9924294484043562698 --mojo-platform-channel-handle=4124 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1024 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,12544525212821876556,8897476227072087094,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8904243634200344343 --mojo-platform-channel-handle=4304 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1256 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6ebaa9d0,0x6ebaa9e0,0x6ebaa9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,12544525212821876556,8897476227072087094,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17295037971689309287 --mojo-platform-channel-handle=3396 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1632 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,12544525212821876556,8897476227072087094,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=929473280879368838 --mojo-platform-channel-handle=1576 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1720 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://497afe23.ngrok.io" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,12544525212821876556,8897476227072087094,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=312416178444681497 --mojo-platform-channel-handle=3768 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
8 525
Read events
1 679
Write events
4 597
Delete events
2 249
Modification events
| (PID) Process: | (1720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3650157062 | |||
| (PID) Process: | (1720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30796928 | |||
| (PID) Process: | (1720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
66
Text files
294
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3840 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\alertify.min[1].js | text | |
MD5:— | SHA256:— | |||
| 3840 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\_all-skins.min[1].css | text | |
MD5:— | SHA256:— | |||
| 3840 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\signin[1].htm | html | |
MD5:— | SHA256:— | |||
| 3840 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\logo[1].svg | image | |
MD5:— | SHA256:— | |||
| 3840 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\boostrap.min[1].css | text | |
MD5:— | SHA256:— | |||
| 3840 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\AdminLTE.min[1].css | text | |
MD5:— | SHA256:— | |||
| 1720 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3840 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\jquery.dataTables.min[1].js | text | |
MD5:280FF6AAABA888CCB486E669FD200B8E | SHA256:7A101BA1668E04321DD15ACB478546DE82BEA05C8887749C8532427577E5DF7A | |||
| 3840 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\bootstrap-theme.min[1].css | text | |
MD5:AB6B02EFEAF178E0247B9504051472FB | SHA256:653E073E97423ADDA5BC3917A241EE8497DD38A48F14BCDE0098A4E54FD0FA5E | |||
| 3840 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\font-awesome.min[1].css | text | |
MD5:269550530CC127B6AA5A35925A7DE6CE | SHA256:799AEB25CC0373FDEE0E1B1DB7AD6C2F6A0E058DFADAA3379689F583213190BD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
59
DNS requests
37
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
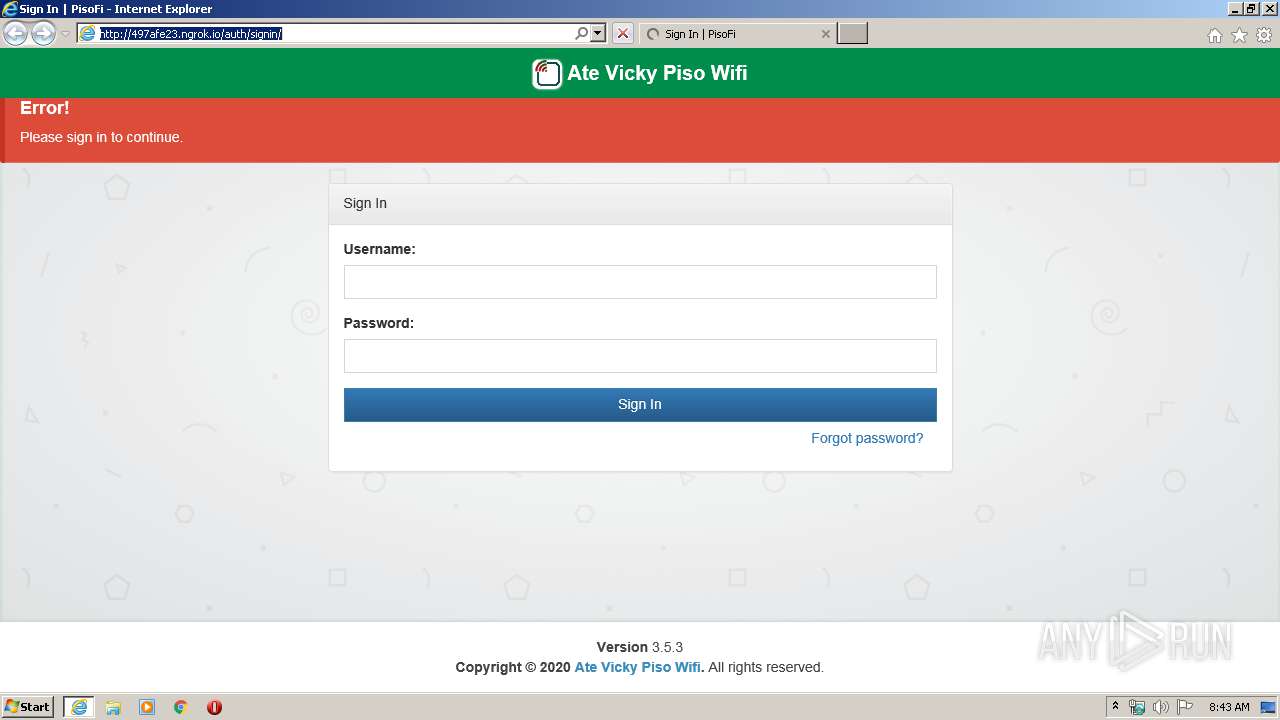
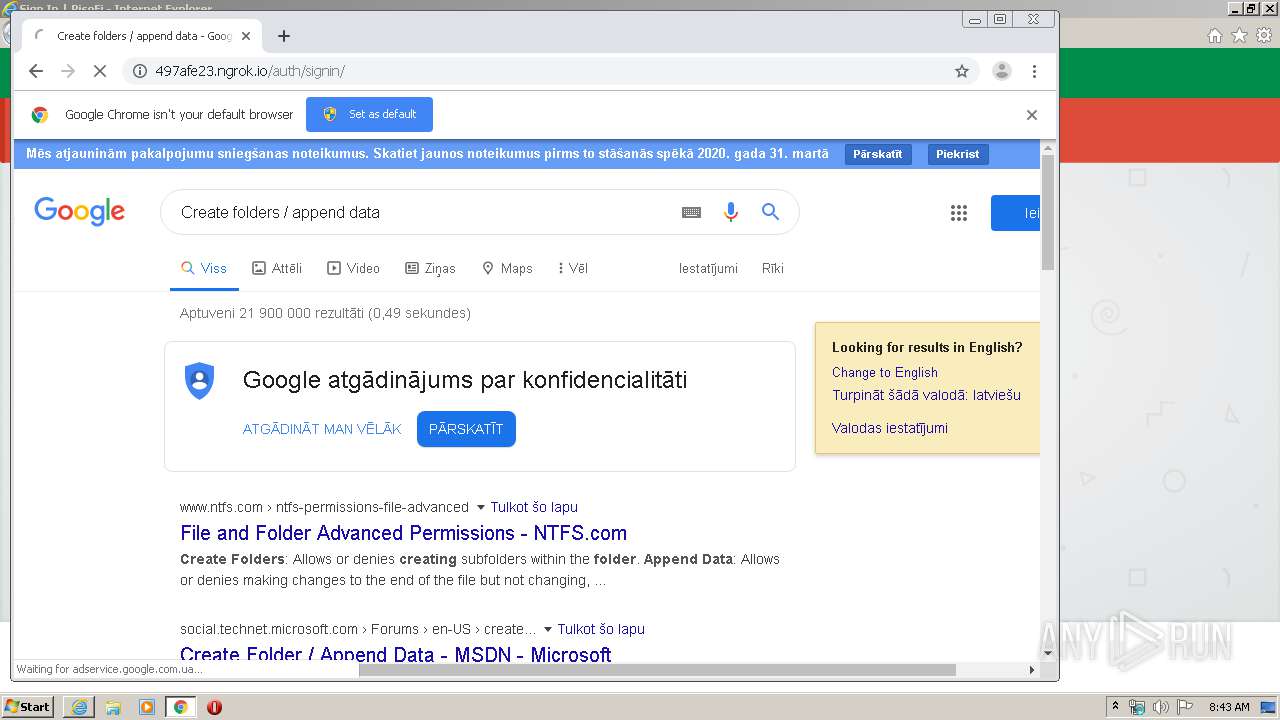
3840 | iexplore.exe | GET | 302 | 3.17.202.129:80 | http://497afe23.ngrok.io/ | US | — | — | malicious |
3840 | iexplore.exe | GET | 302 | 3.17.202.129:80 | http://497afe23.ngrok.io/admin | US | — | — | malicious |
3840 | iexplore.exe | GET | 200 | 3.17.202.129:80 | http://497afe23.ngrok.io/css/themes/boostrap.min.css | US | text | 1.46 Kb | malicious |
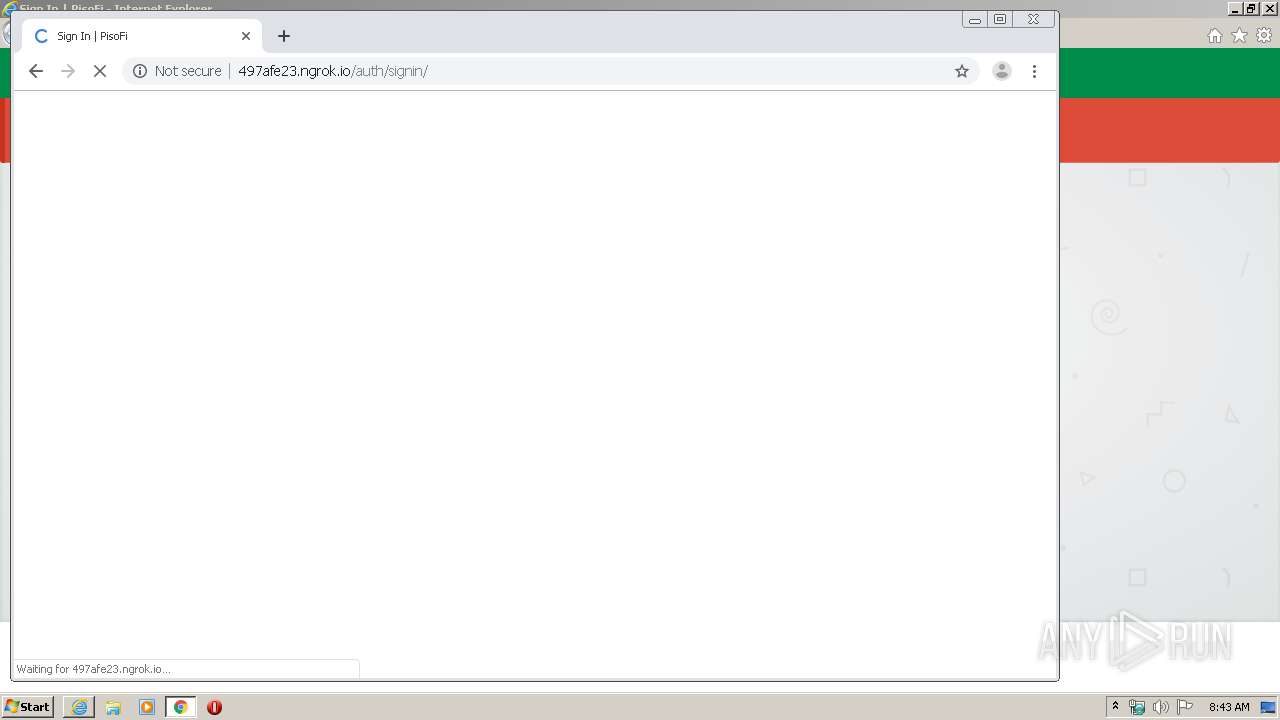
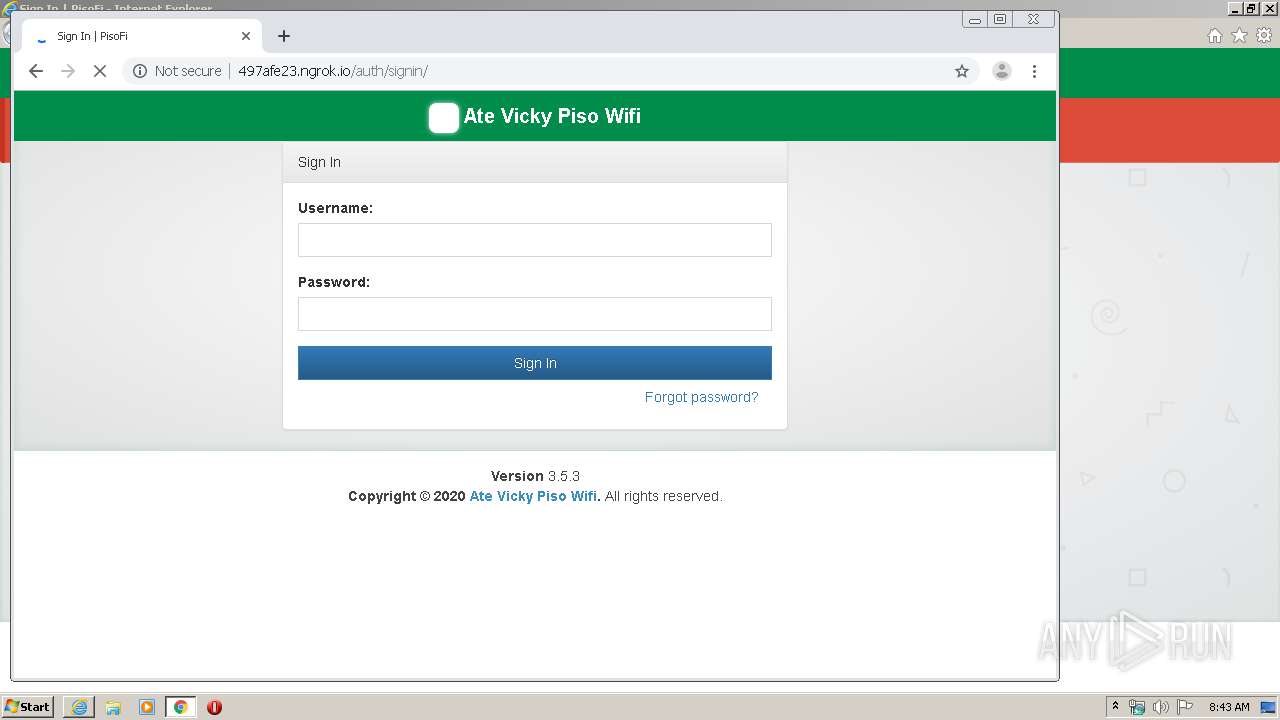
3840 | iexplore.exe | GET | 200 | 3.17.202.129:80 | http://497afe23.ngrok.io/auth/signin/ | US | html | 2.57 Kb | malicious |
3840 | iexplore.exe | GET | 200 | 3.17.202.129:80 | http://497afe23.ngrok.io/css/skins/_all-skins.min.css | US | text | 39.8 Kb | malicious |
3840 | iexplore.exe | GET | 200 | 3.17.202.129:80 | http://497afe23.ngrok.io/plugins/datatables/dataTables.bootstrap.css | US | text | 8.62 Kb | malicious |
3840 | iexplore.exe | GET | 200 | 3.17.202.129:80 | http://497afe23.ngrok.io/js/shiblie.js | US | text | 406 b | malicious |
3840 | iexplore.exe | GET | 200 | 3.17.202.129:80 | http://497afe23.ngrok.io/js/jquery-3.2.1.min.js | US | text | 84.6 Kb | malicious |
3840 | iexplore.exe | GET | 200 | 3.17.202.129:80 | http://497afe23.ngrok.io/plugins/slimScroll/jquery.slimscroll.min.js | US | text | 4.61 Kb | malicious |
3840 | iexplore.exe | GET | 200 | 3.17.202.129:80 | http://497afe23.ngrok.io/css/font-awesome.min.css | US | text | 30.2 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1720 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1720 | iexplore.exe | 3.17.202.129:80 | 497afe23.ngrok.io | — | US | malicious |
1632 | chrome.exe | 216.58.206.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1632 | chrome.exe | 172.217.18.14:443 | apis.google.com | Google Inc. | US | whitelisted |
1632 | chrome.exe | 172.217.16.142:443 | consent.google.com | Google Inc. | US | whitelisted |
1632 | chrome.exe | 172.217.21.206:443 | clients2.google.com | Google Inc. | US | whitelisted |
1632 | chrome.exe | 172.217.22.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1632 | chrome.exe | 172.217.18.110:80 | ogs.google.com.ua | Google Inc. | US | whitelisted |
1632 | chrome.exe | 172.217.16.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
1632 | chrome.exe | 172.217.16.196:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
497afe23.ngrok.io |
| malicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query to a *.ngrok domain (ngrok.io) |
1052 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query to a *.ngrok domain (ngrok.io) |
1632 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Possible Successful Phish - Generic Credential POST to Ngrok.io |
1632 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Possible Successful Phish - Generic Credential POST to Ngrok.io |