| File name: | 4DD3.exe |
| Full analysis: | https://app.any.run/tasks/b7c7222e-1927-4465-b3f0-48ea637f3a22 |
| Verdict: | Malicious activity |
| Analysis date: | July 17, 2019, 14:31:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (DLL) (console) Intel 80386, for MS Windows |
| MD5: | ED60C95C805DBAEE92C90C3AB930085A |
| SHA1: | EC4FA2E62BE62A7BD1A67157BA46D1B022837575 |
| SHA256: | D35574D2CC42B4EDBF217A86639864422FBE02443250A36EB2CD11B22F165C39 |
| SSDEEP: | 24576:YbhBoIcENh5n8O+0KFaMtZKBaNmPA/I/aa5o:YbnoIcEhn8VkMtZKx/aa5o |
MALICIOUS
Loads dropped or rewritten executable
- DllHost.exe (PID: 2468)
- windanr.exe (PID: 2204)
- explorer.exe (PID: 304)
- svchost.exe (PID: 832)
SUSPICIOUS
Uses RUNDLL32.EXE to load library
- explorer.exe (PID: 304)
Creates files in the user directory
- explorer.exe (PID: 304)
INFO
Loads main object executable
- rundll32.exe (PID: 3696)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:11:20 13:05:02+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 872448 |
| InitializedDataSize: | 406016 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x0000 |
| OSVersion: | 6.1 |
| ImageVersion: | 6.1 |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 6.1.7601.17514 |
| ProductVersionNumber: | 6.1.7601.17514 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | NT Layer DLL |
| FileVersion: | 6.1.7601.17514 (win7sp1_rtm.101119-1850) |
| InternalName: | ntdll.dll |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | ntdll.dll |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 6.1.7601.17514 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 20-Nov-2010 12:05:02 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | NT Layer DLL |
| FileVersion: | 6.1.7601.17514 (win7sp1_rtm.101119-1850) |
| InternalName: | ntdll.dll |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFilename: | ntdll.dll |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 6.1.7601.17514 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 20-Nov-2010 12:05:02 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000D4D66 | 0x000D4E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.81471 |
RT | 0x000D6000 | 0x000001DC | 0x00000200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.59855 |
.data | 0x000D7000 | 0x00008064 | 0x00006C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.683427 |
.rsrc | 0x000E0000 | 0x000560D8 | 0x00056200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.33271 |
.reloc | 0x00137000 | 0x00004C3C | 0x00004E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.67729 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.53644 | 896 | UNKNOWN | English - United States | RT_VERSION |
Exports
Title | Ordinal | Address |
|---|---|---|
8 | 0x000120A0 | |
RtlActivateActivationContextUnsafeFast | 9 | 0x00052FED |
RtlDeactivateActivationContextUnsafeFast | 10 | 0x00053063 |
RtlInterlockedPushListSList | 11 | 0x00035ACC |
RtlUlongByteSwap | 12 | 0x00035B50 |
RtlUlonglongByteSwap | 13 | 0x00035B60 |
RtlUshortByteSwap | 14 | 0x00035B40 |
ExpInterlockedPopEntrySListEnd | 15 | 0x00035A8F |
ExpInterlockedPopEntrySListFault | 16 | 0x00035A8D |
ExpInterlockedPopEntrySListResume | 17 | 0x00035A64 |
Total processes
33
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 832 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2204 | "windanr.exe" | C:\Windows\system32\windanr.exe | — | qemu-ga.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2468 | C:\Windows\system32\DllHost.exe /Processid:{AB8902B4-09CA-4BB6-B78D-A8F59079A8D5} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3696 | "C:\Windows\System32\rundll32.exe" "C:\Users\admin\Desktop\4DD3.exe", #1 | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 064
Read events
970
Write events
94
Delete events
0
Modification events
| (PID) Process: | (2204) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | APPSTARTING |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2204) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | ARROW |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2204) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | CROSS |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2204) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | HAND |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2204) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | HELP |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2204) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | IBEAM |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2204) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | NO |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2204) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZEALL |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2204) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZENESW |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2204) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZENS |
Value: %SystemRoot%\cursors\clearcur.cur | |||
Executable files
0
Suspicious files
4
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 832 | svchost.exe | C:\Windows\SoftwareDistribution\DataStore\DataStore.edb | — | |
MD5:— | SHA256:— | |||
| 832 | svchost.exe | C:\Windows\SoftwareDistribution\DataStore\Logs\edb.chk | binary | |
MD5:— | SHA256:— | |||
| 832 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
| 832 | svchost.exe | C:\Windows\SoftwareDistribution\DataStore\Logs\edb.log | binary | |
MD5:— | SHA256:— | |||
| 304 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\7e4dca80246863e3.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
| 304 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\Network and Internet.lnk | lnk | |
MD5:FB511CEA67F0EF7C5235B37286DCE826 | SHA256:DE9DD12E55FC33F19DDB51D4540612F42DB23E53B5CDE84EE6E80619E56BBFDA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
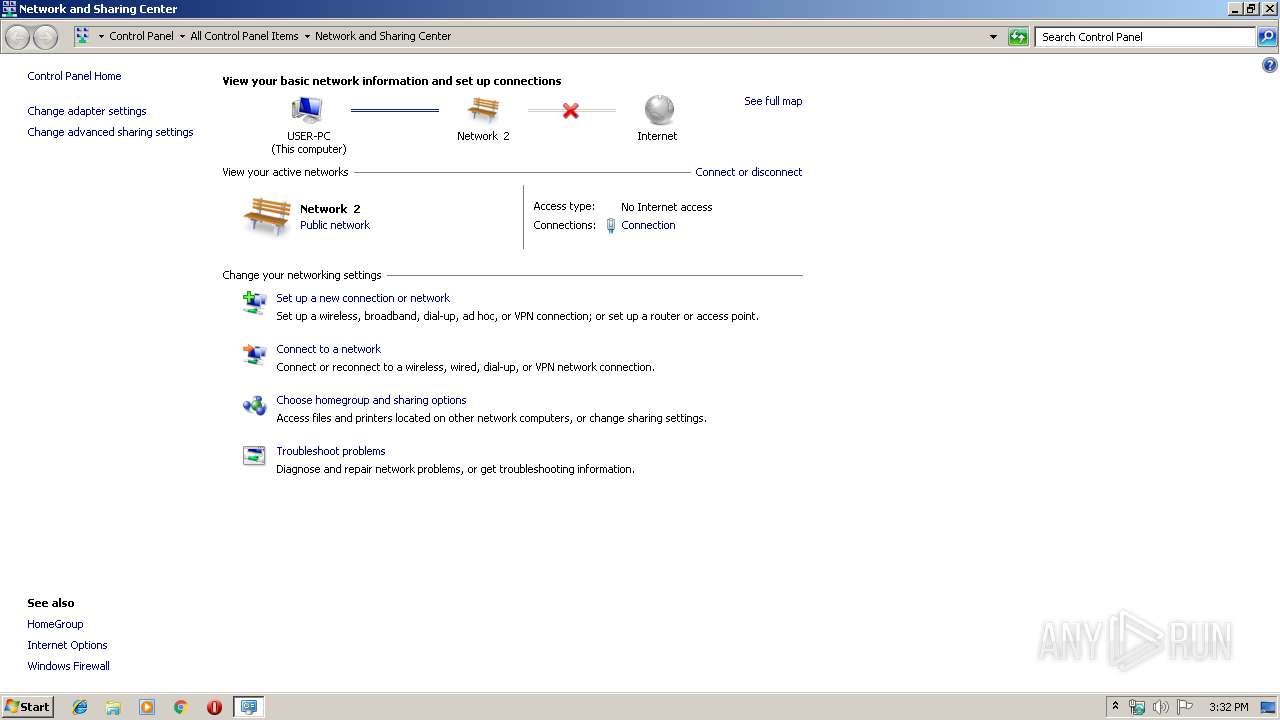
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report