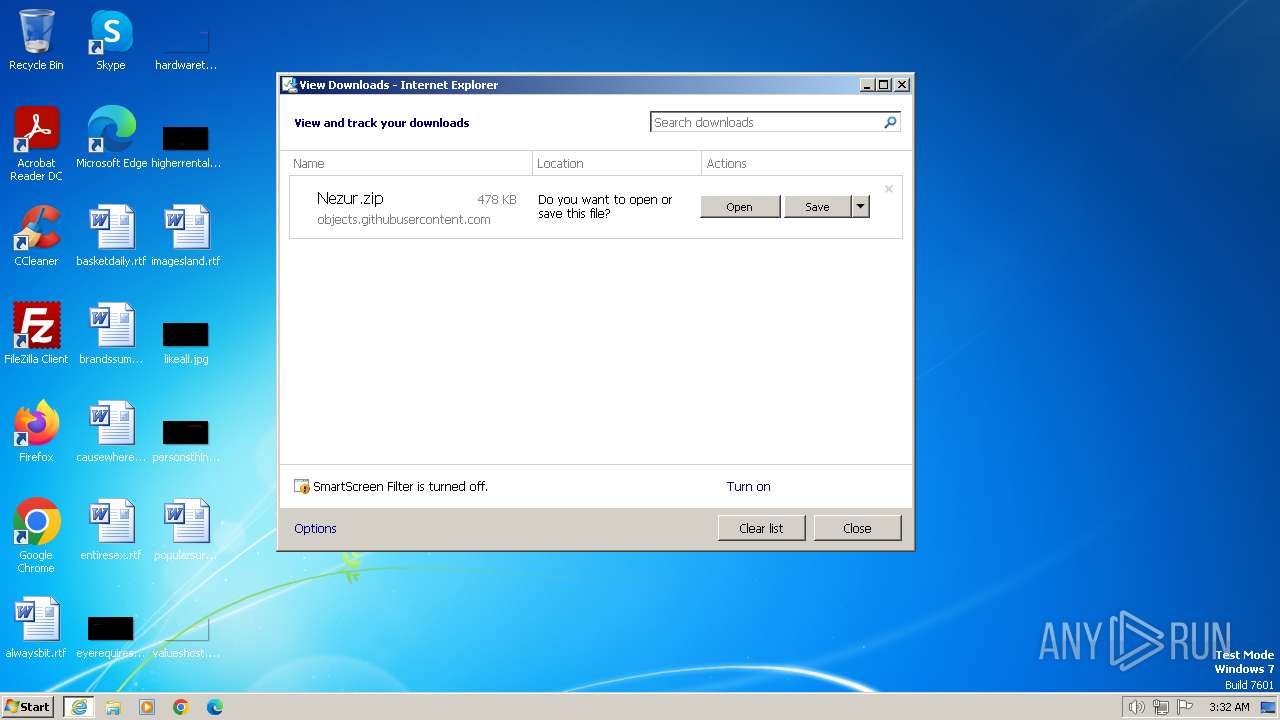
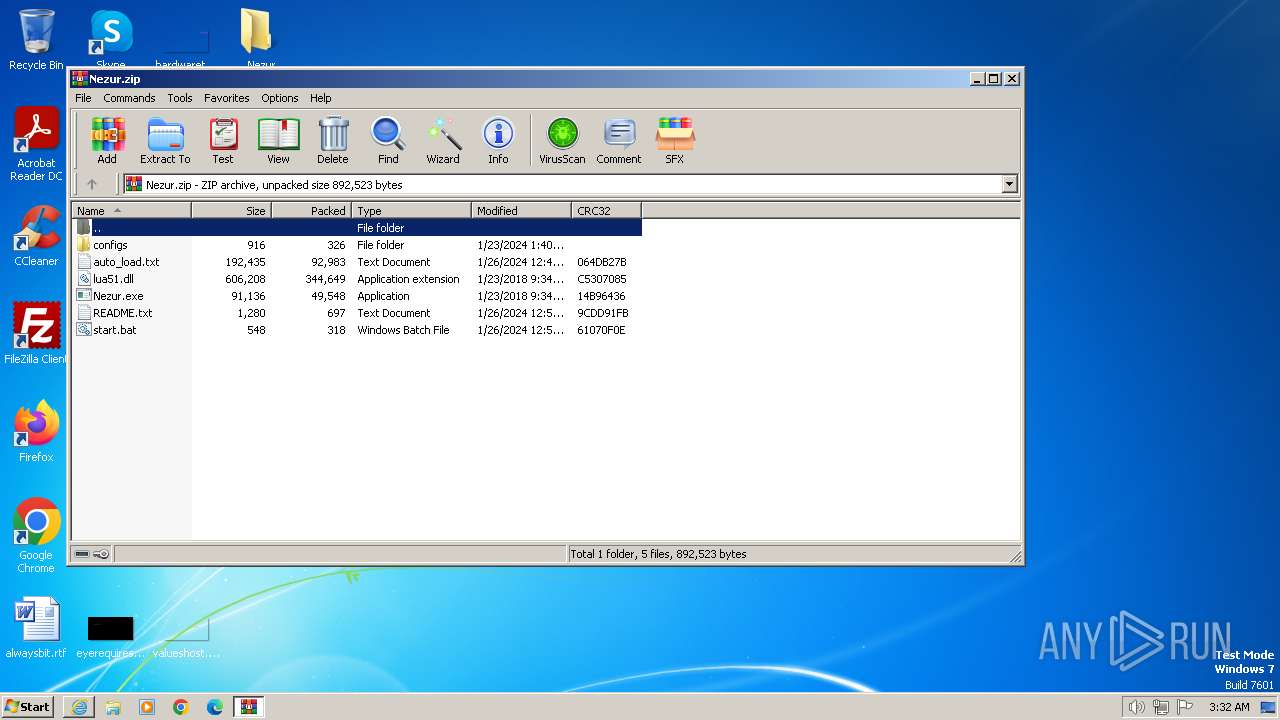
| URL: | https://github.com/microsoft/terminal/files/14065211/Nezur.zip |
| Full analysis: | https://app.any.run/tasks/f91a237c-74bd-402c-9ca5-24ba22cdf53b |
| Verdict: | Malicious activity |
| Analysis date: | February 11, 2024, 03:32:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | A449076F07D5B767F9CAF38D9CA5181D |
| SHA1: | 35E2E135A380AA13FB21D6A20FA43543138A9222 |
| SHA256: | D3553FF2EA0B9559F1F51F2B616FD120FAE58D5DEAF9B9019ADEC6CD23941E1A |
| SSDEEP: | 3:N8tEd46WYsRAXxwEfU7GN:2uu6RsdQN |
MALICIOUS
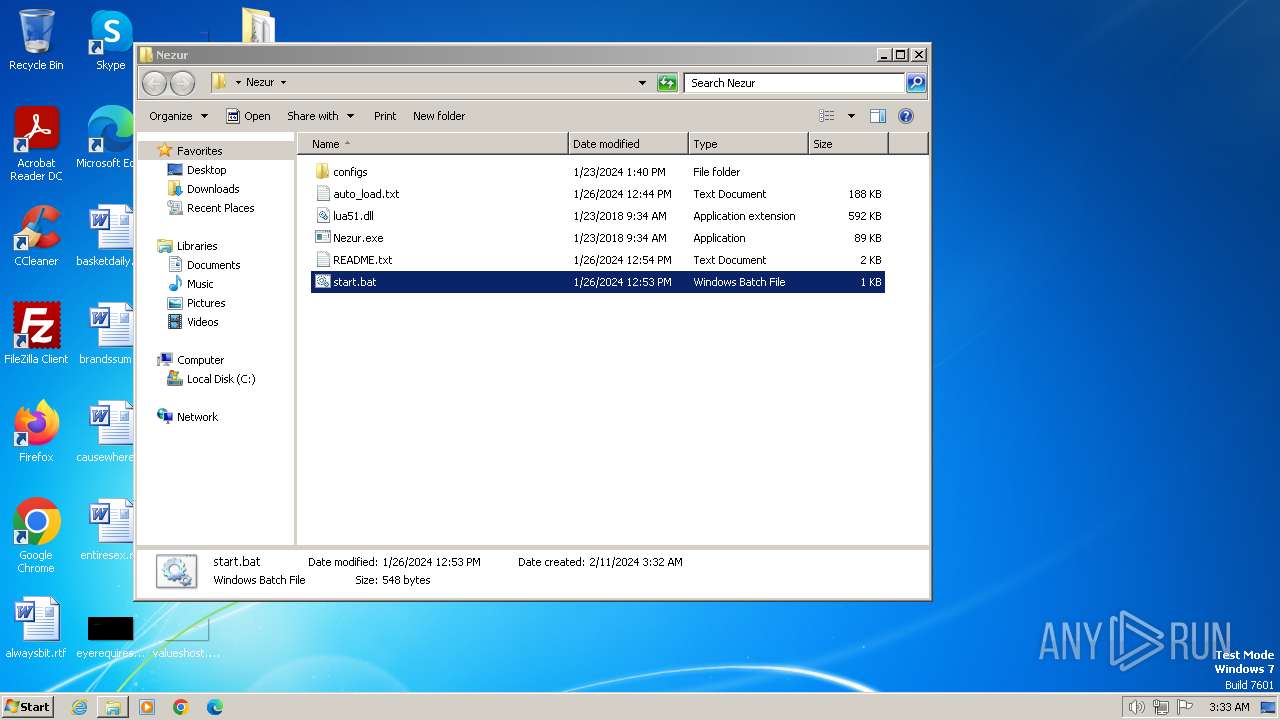
Drops the executable file immediately after the start
- Nezur.exe (PID: 448)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 3500)
- Nezur.exe (PID: 448)
The process executes VB scripts
- cmd.exe (PID: 2320)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 2320)
- cmd.exe (PID: 3616)
Runs shell command (SCRIPT)
- wscript.exe (PID: 3544)
Reads the Internet Settings
- wscript.exe (PID: 3544)
- cmd.exe (PID: 2320)
- Nezur.exe (PID: 448)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 3544)
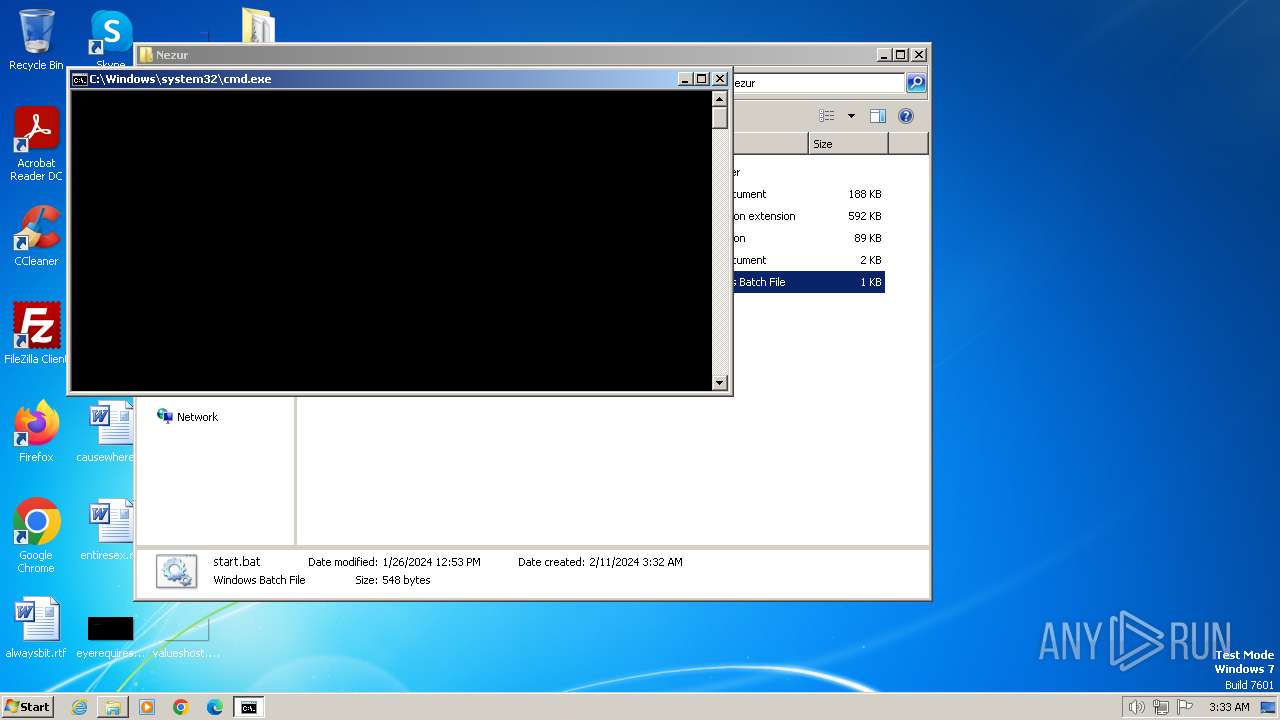
Executing commands from a ".bat" file
- wscript.exe (PID: 3544)
Reads settings of System Certificates
- Nezur.exe (PID: 448)
Checks for external IP
- Nezur.exe (PID: 448)
Checks Windows Trust Settings
- Nezur.exe (PID: 448)
Connects to the server without a host name
- Nezur.exe (PID: 448)
Executable content was dropped or overwritten
- Nezur.exe (PID: 448)
INFO
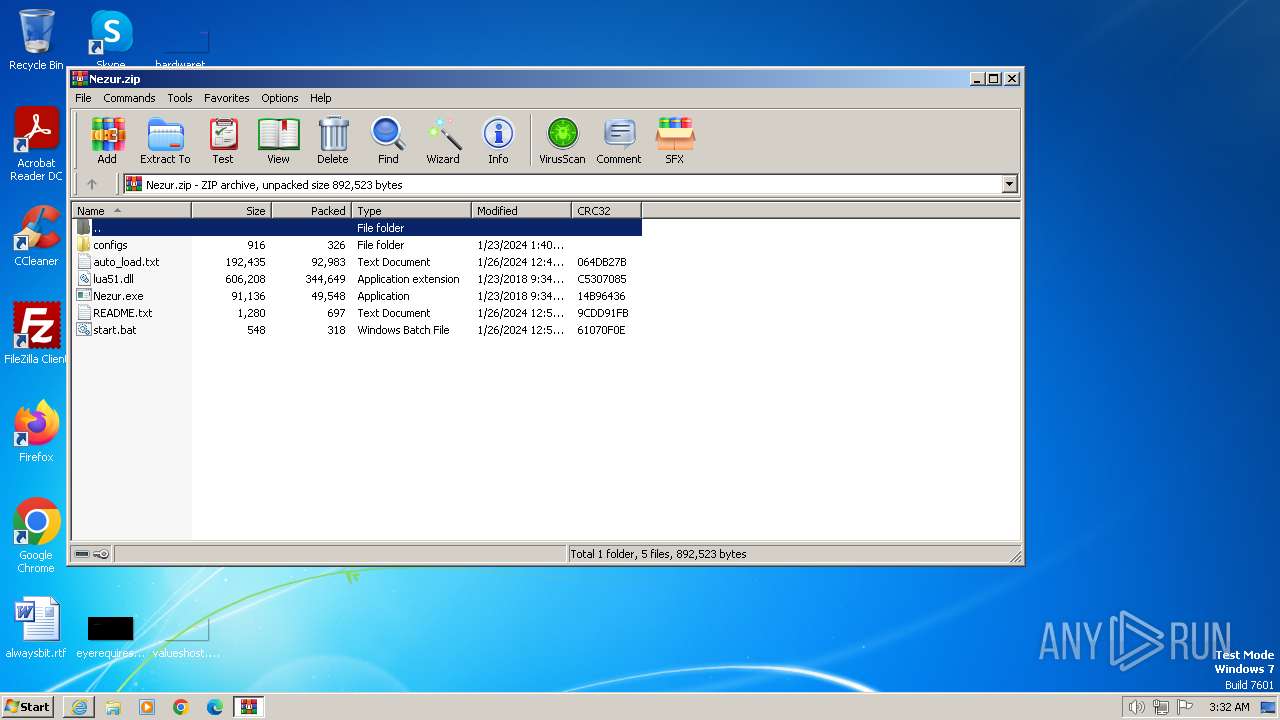
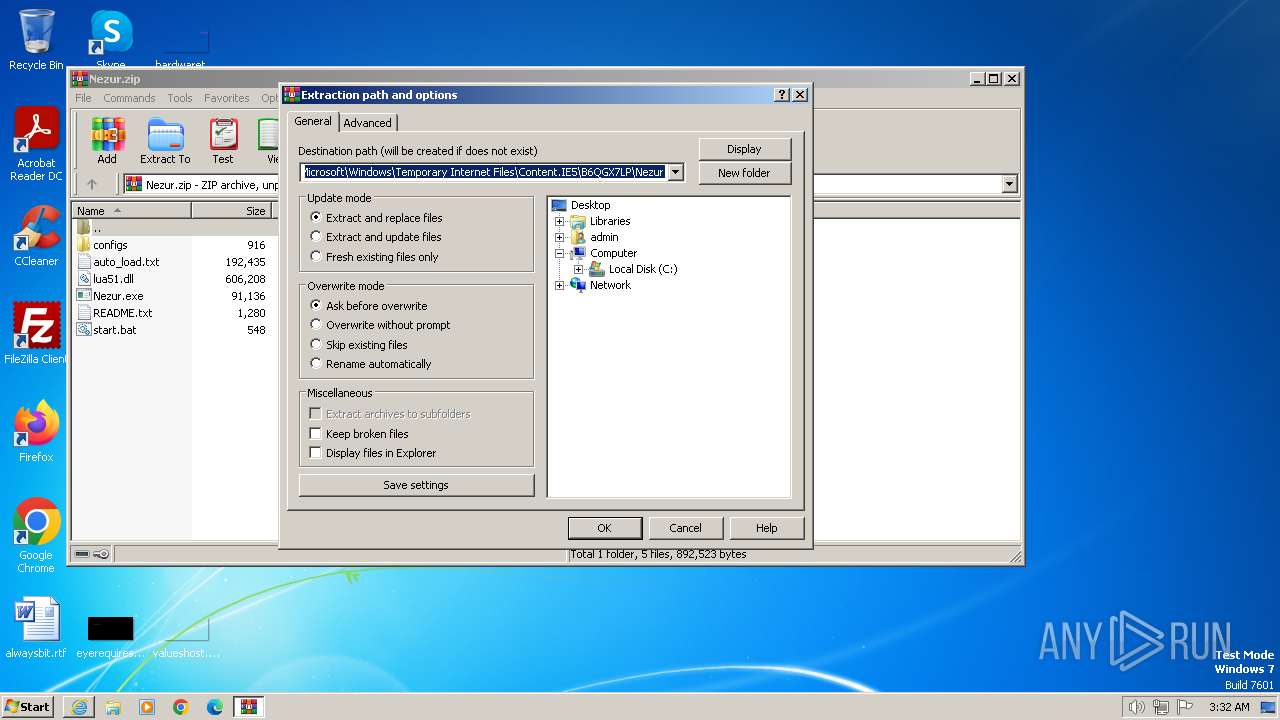
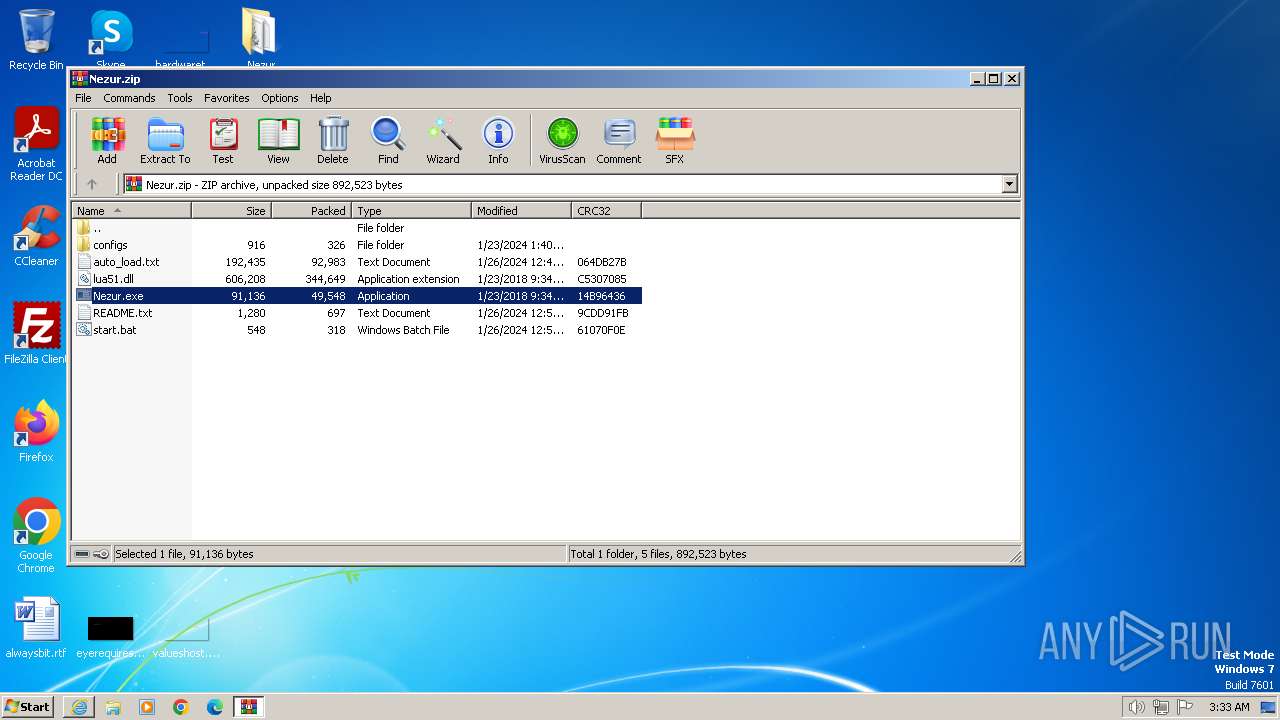
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3500)
The process uses the downloaded file
- WinRAR.exe (PID: 3500)
- iexplore.exe (PID: 2472)
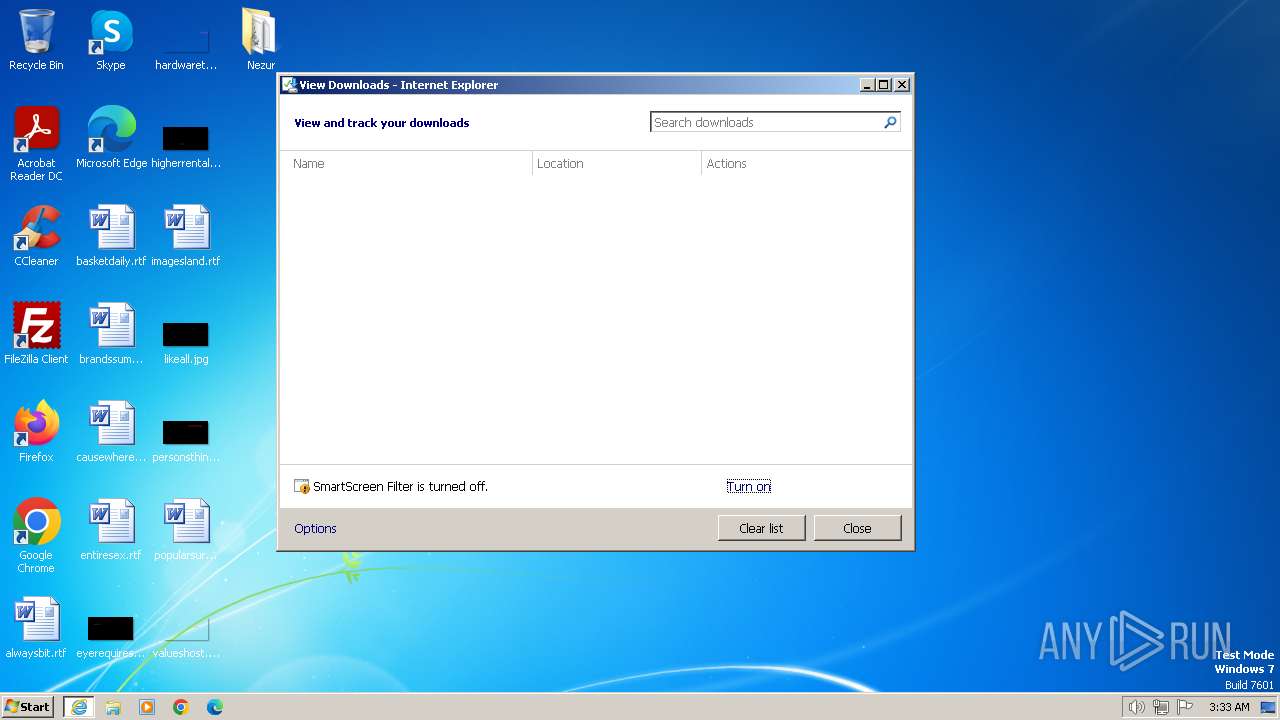
Modifies the phishing filter of IE
- iexplore.exe (PID: 2472)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3500)
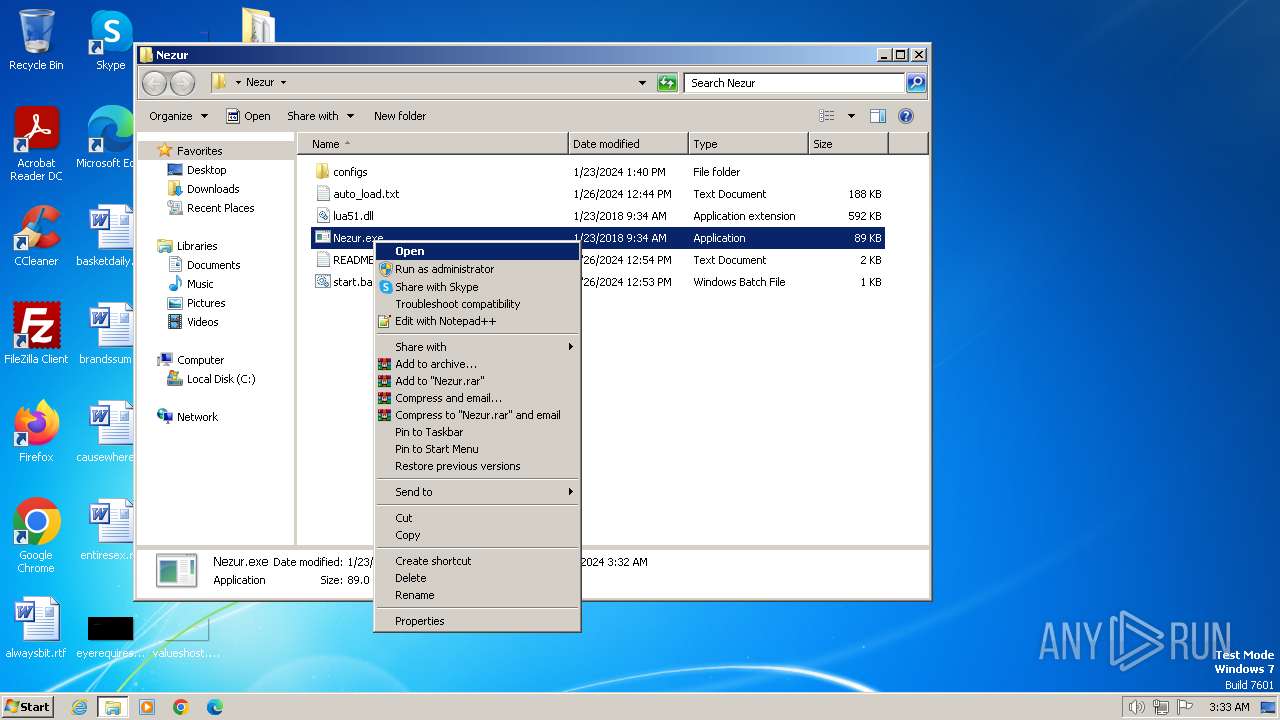
Manual execution by a user
- Nezur.exe (PID: 2072)
- Nezur.exe (PID: 2100)
- cmd.exe (PID: 2320)
- Nezur.exe (PID: 3260)
- notepad.exe (PID: 2308)
Checks supported languages
- Nezur.exe (PID: 2100)
- Nezur.exe (PID: 2908)
- Nezur.exe (PID: 2072)
- Nezur.exe (PID: 448)
- Nezur.exe (PID: 3260)
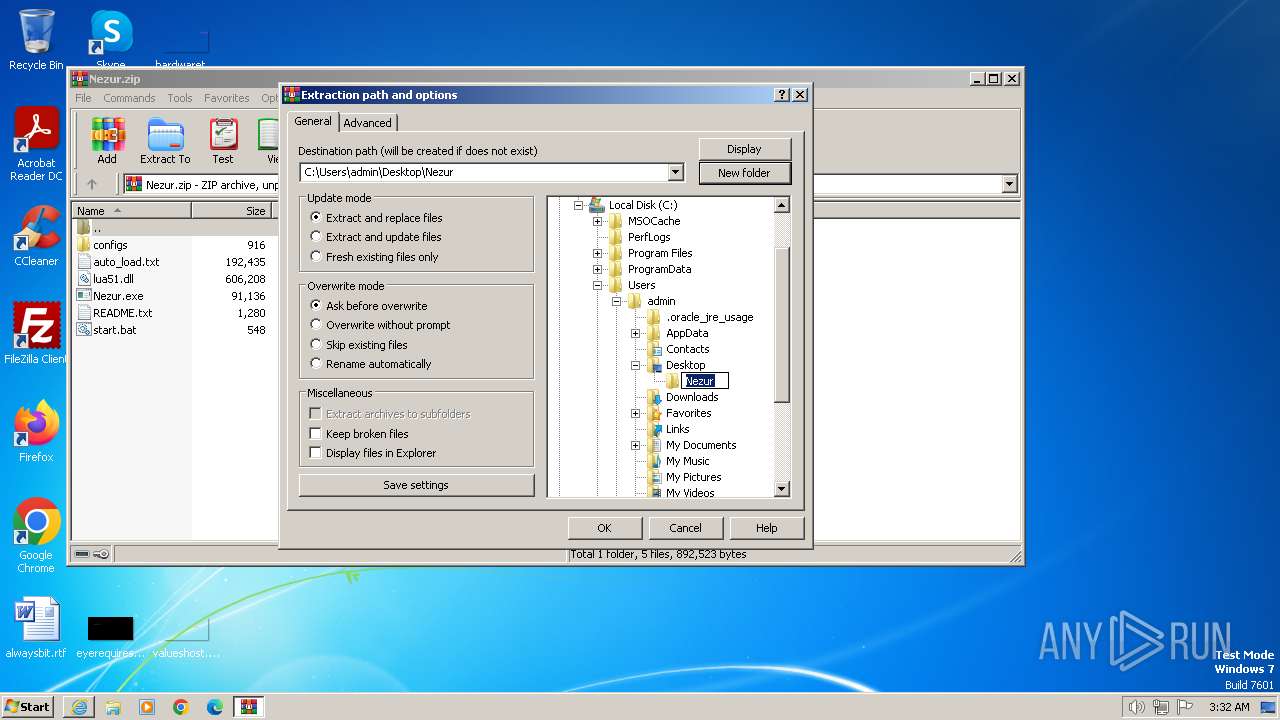
Creates files or folders in the user directory
- Nezur.exe (PID: 448)
Reads the computer name
- Nezur.exe (PID: 448)
Reads the machine GUID from the registry
- Nezur.exe (PID: 448)
Reads the software policy settings
- Nezur.exe (PID: 448)
Checks proxy server information
- Nezur.exe (PID: 448)
Creates files in the program directory
- Nezur.exe (PID: 448)
Application launched itself
- iexplore.exe (PID: 2472)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
69
Monitored processes
15
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
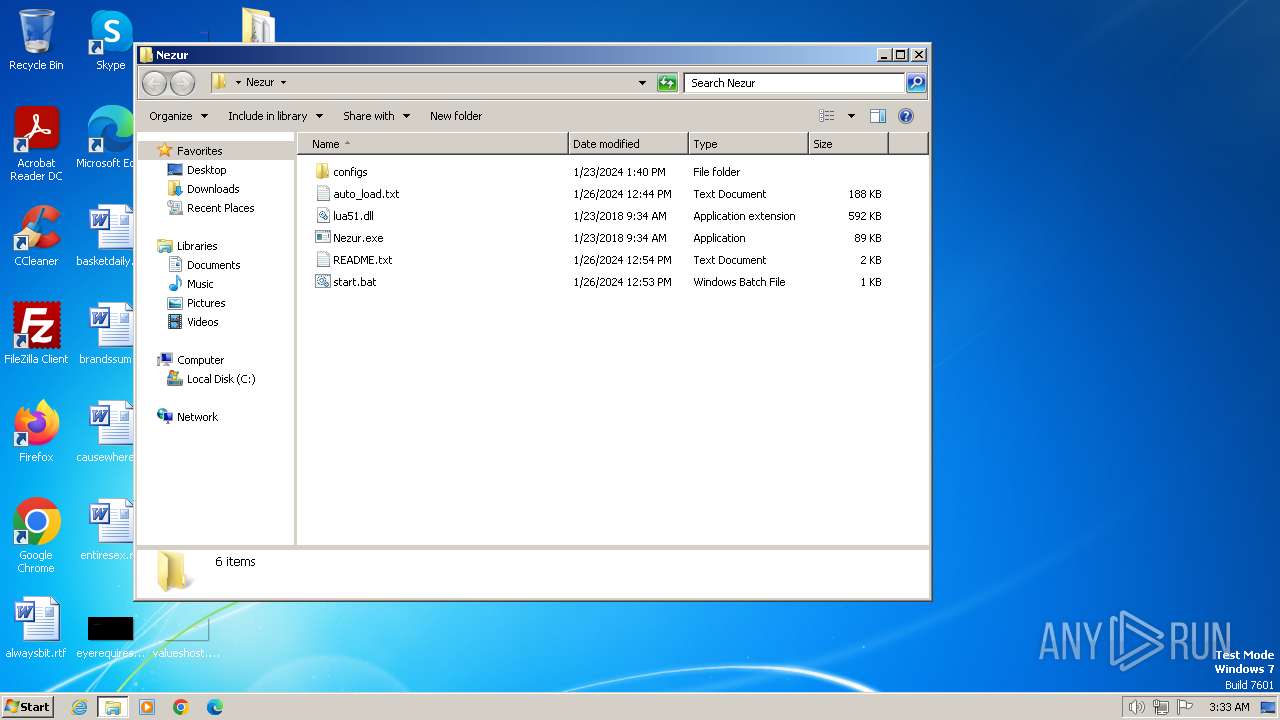
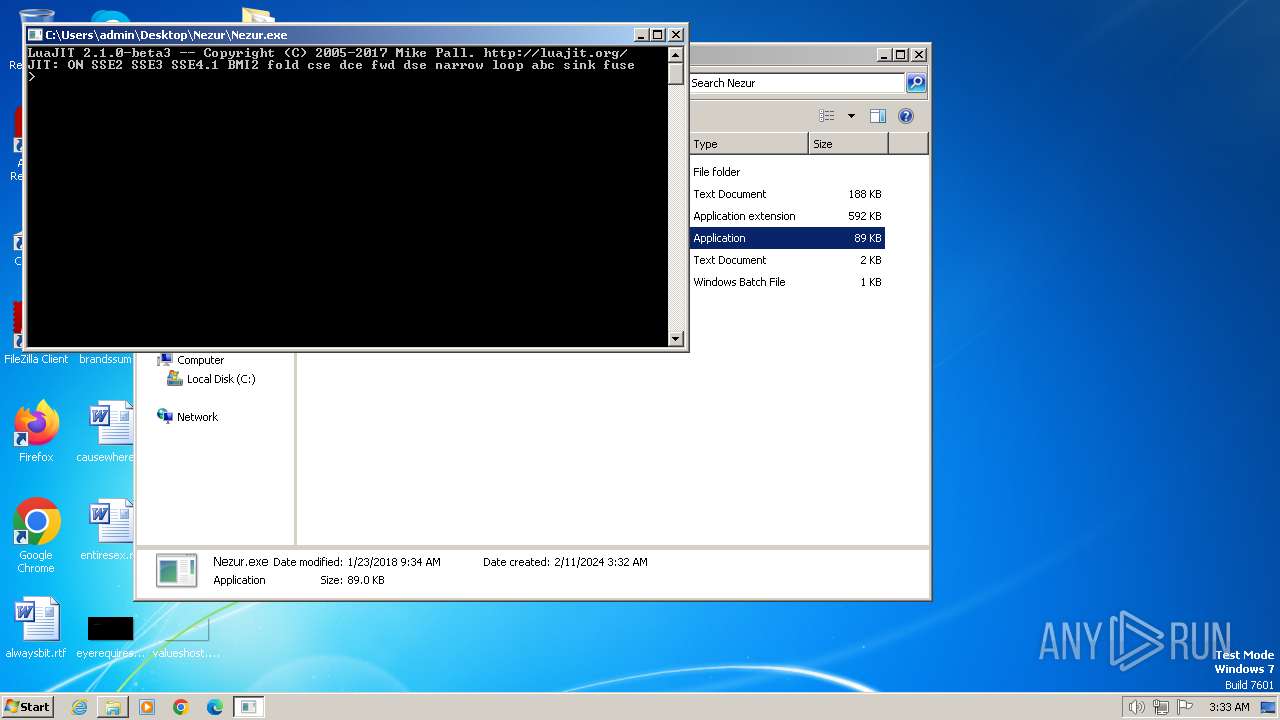
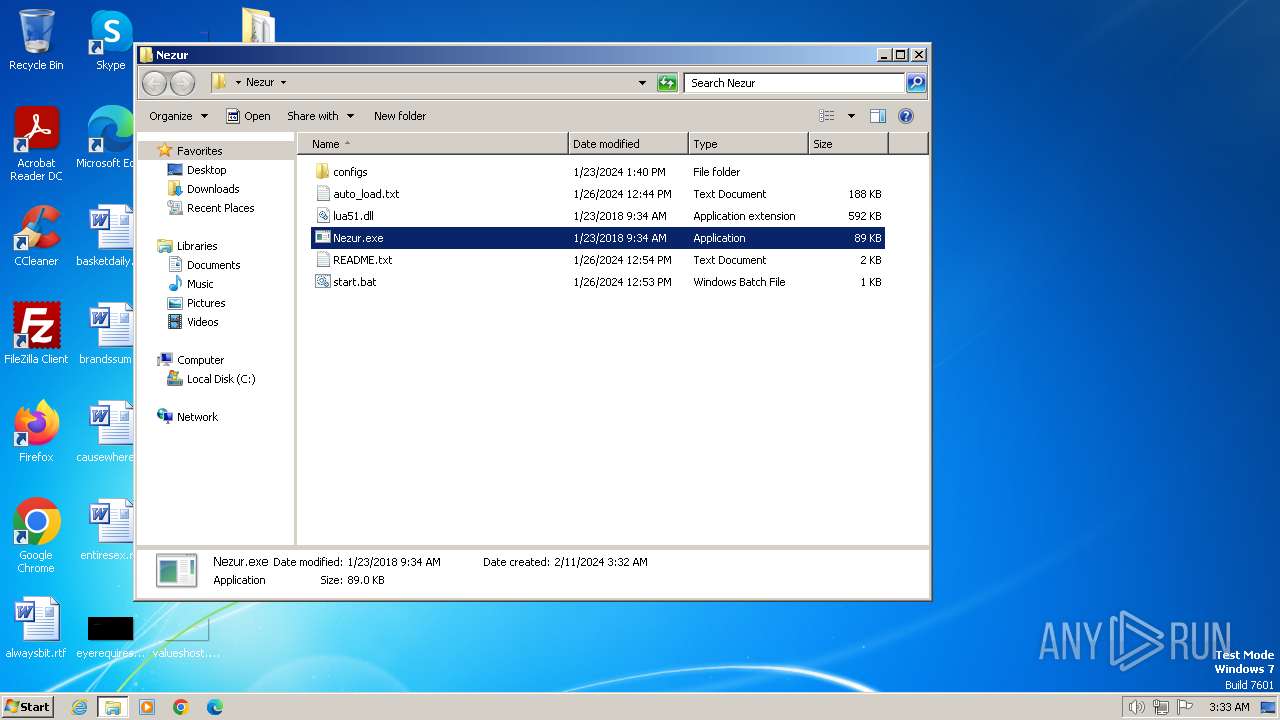
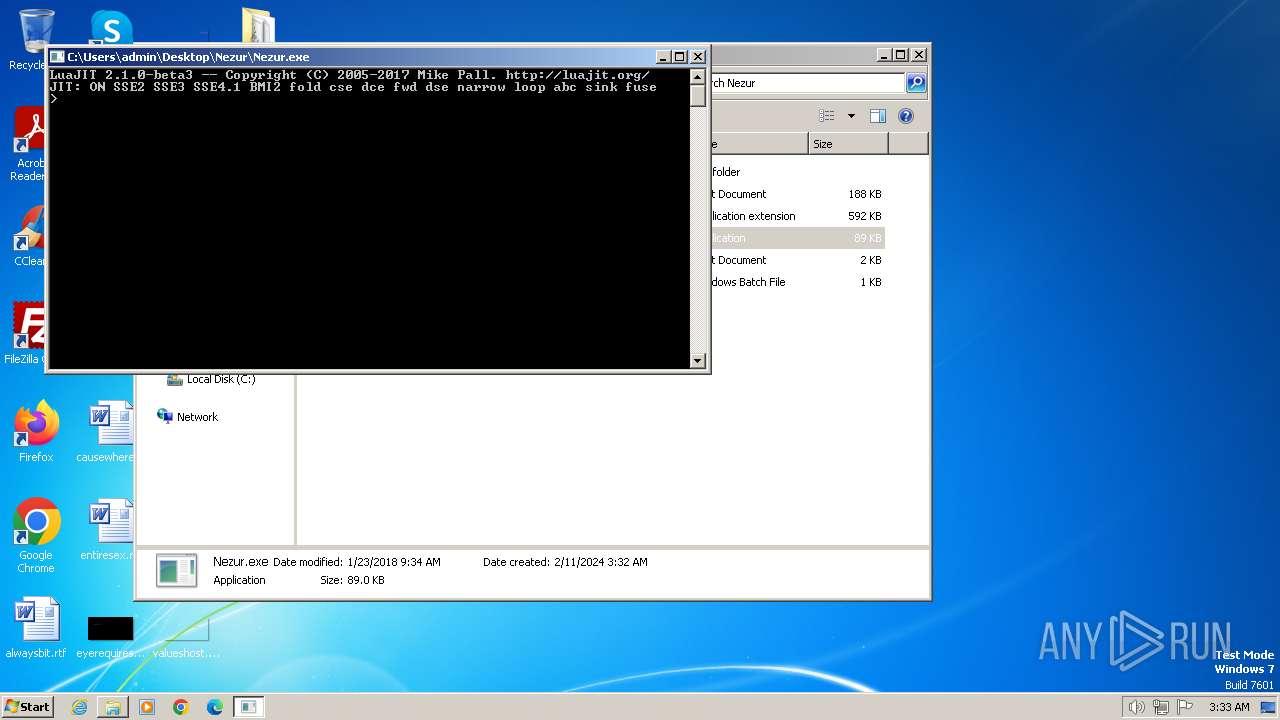
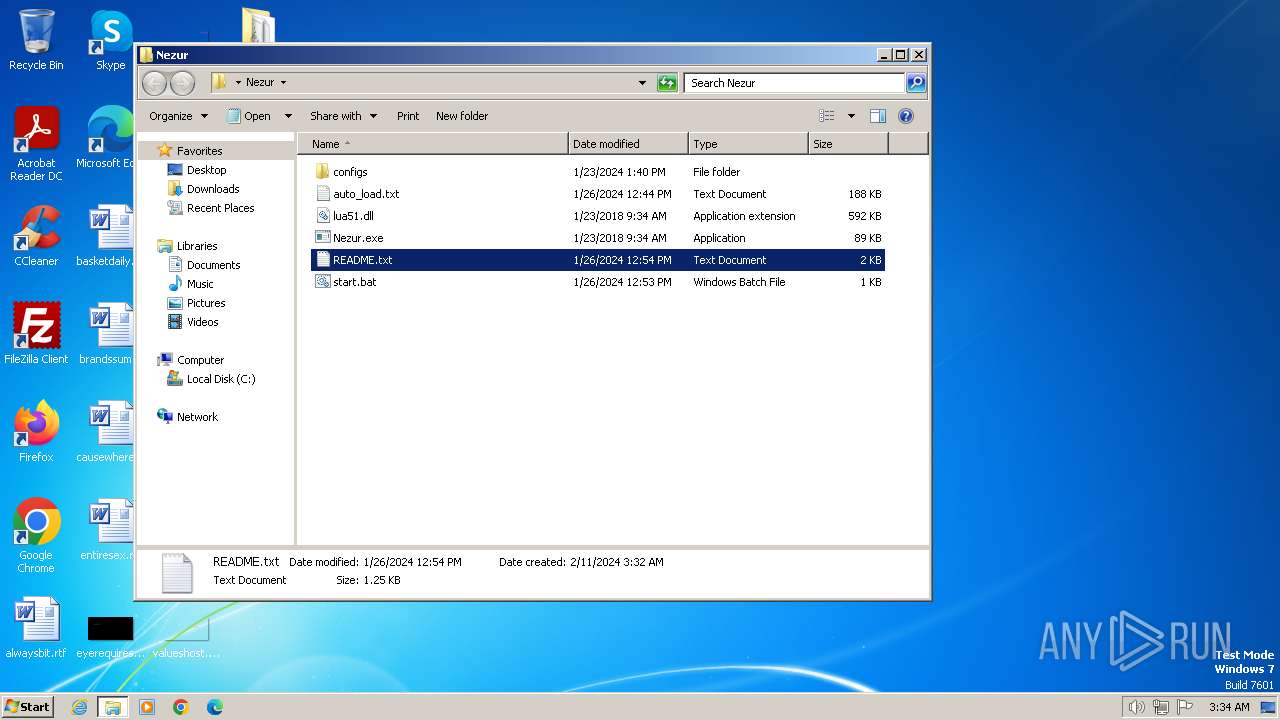
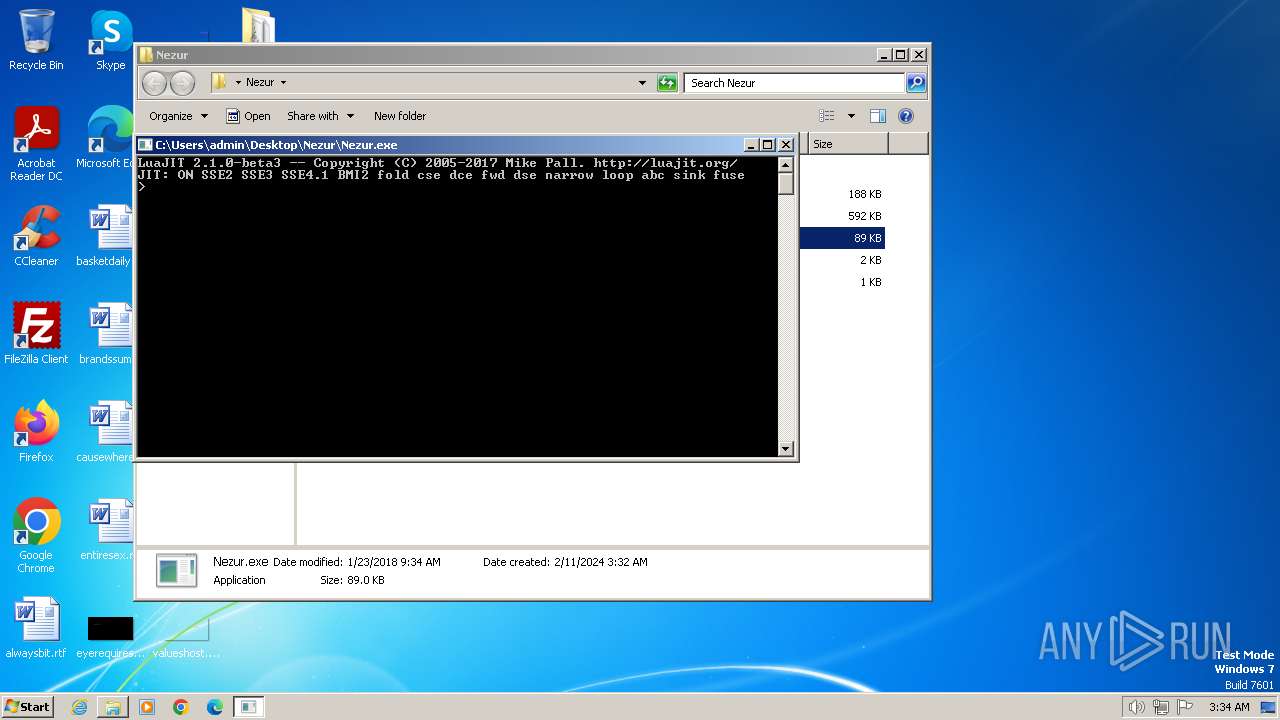
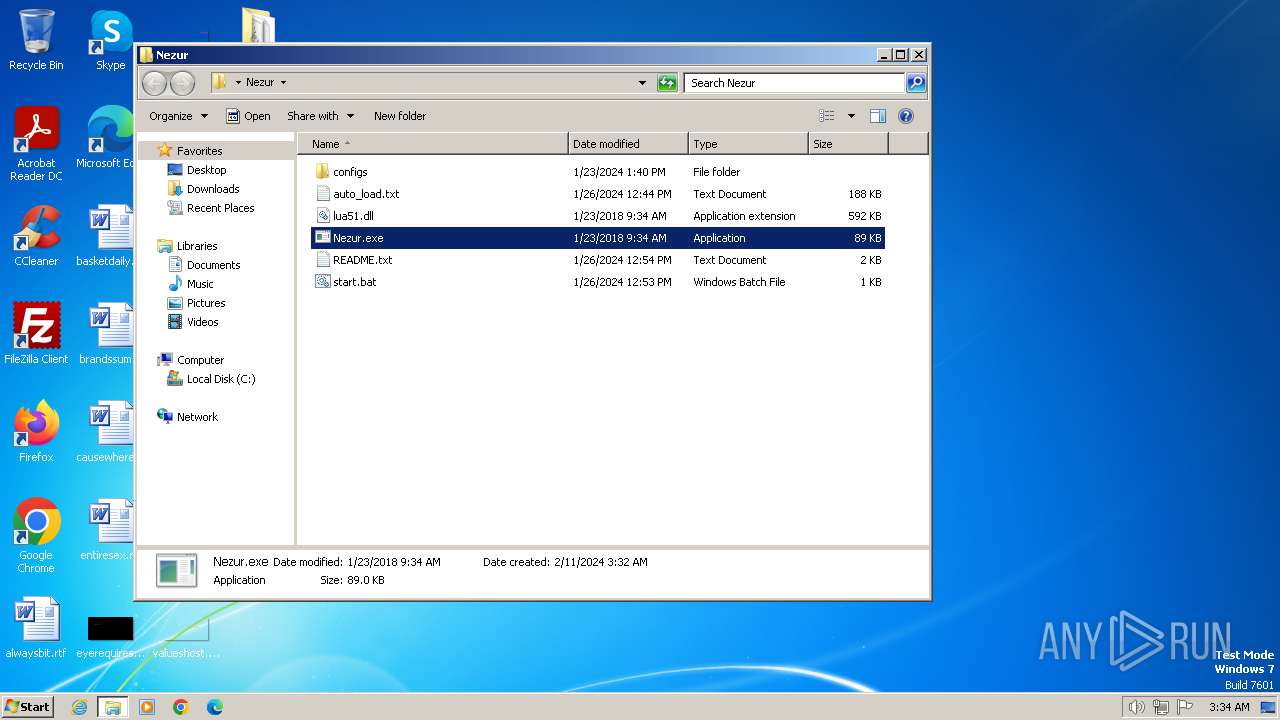
| 448 | Nezur.exe auto_load.txt | C:\Users\admin\Desktop\Nezur\Nezur.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 480 | "C:\Windows\system32\cacls.exe" "C:\Windows\system32\config\system" | C:\Windows\System32\cacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Control ACLs Program Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2072 | "C:\Users\admin\Desktop\Nezur\Nezur.exe" | C:\Users\admin\Desktop\Nezur\Nezur.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225786 Modules
| |||||||||||||||
| 2100 | "C:\Users\admin\Desktop\Nezur\Nezur.exe" | C:\Users\admin\Desktop\Nezur\Nezur.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225786 Modules
| |||||||||||||||
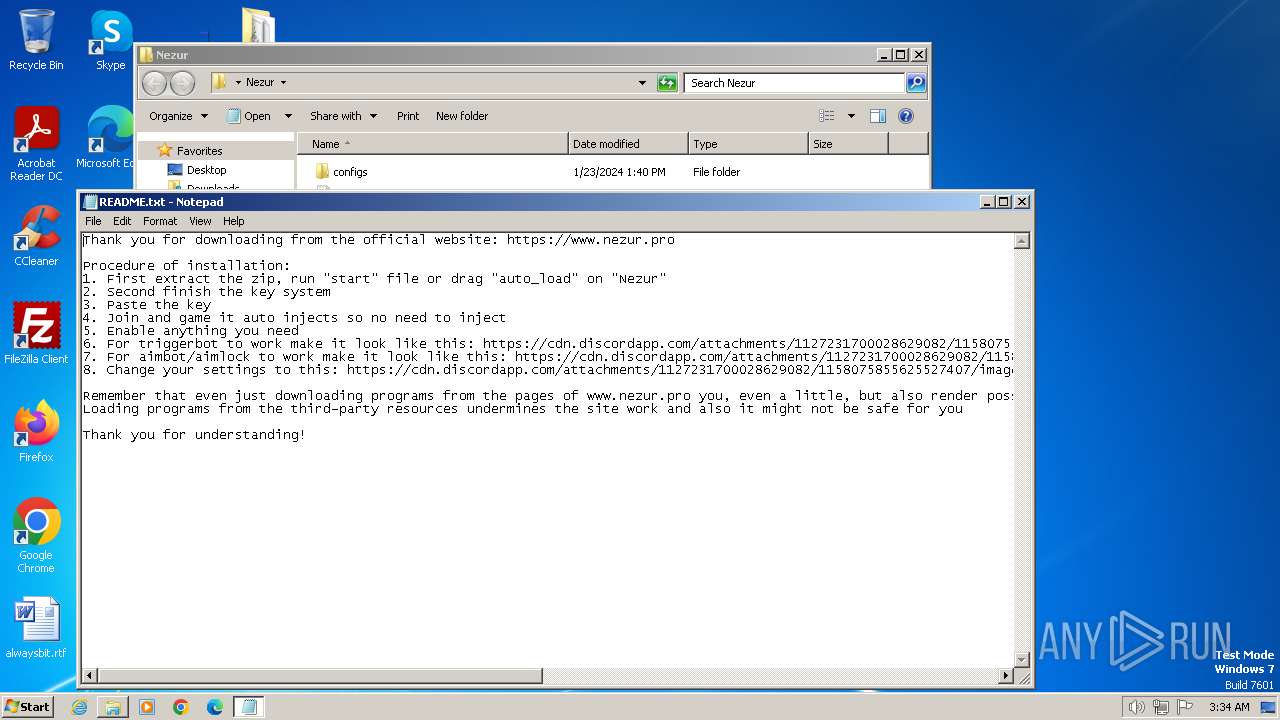
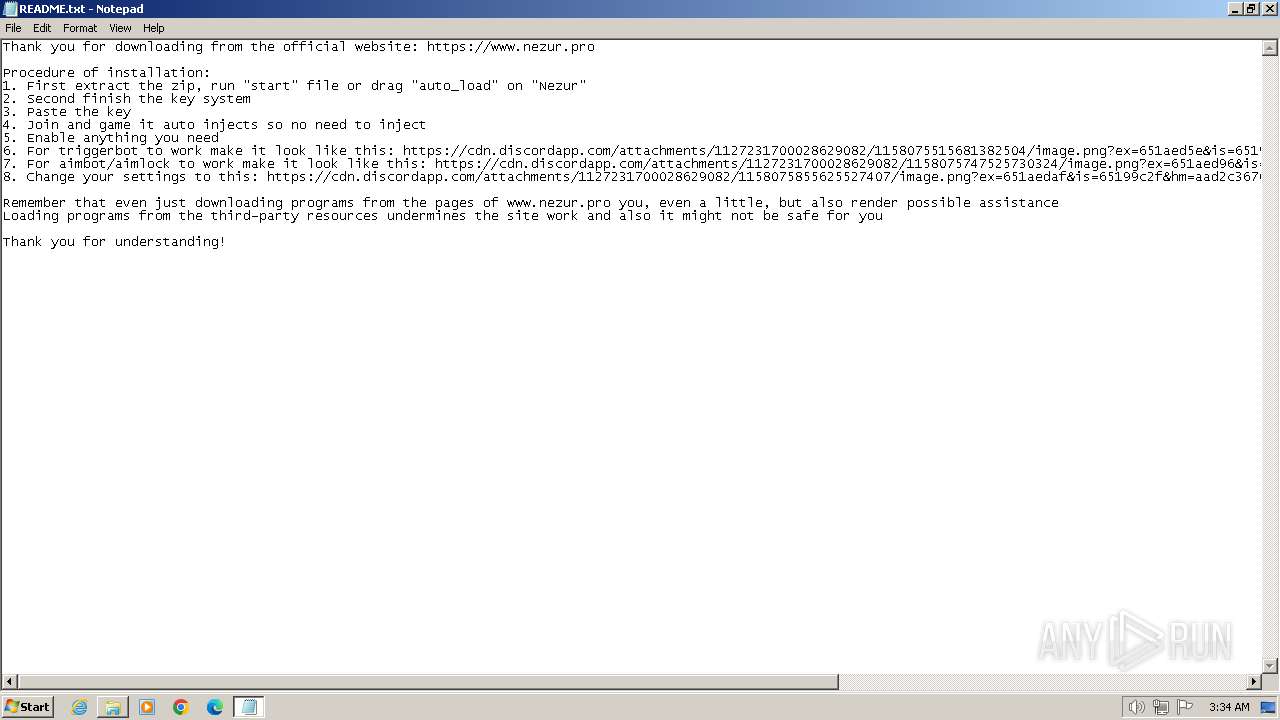
| 2308 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\Nezur\README.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2320 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\Desktop\Nezur\start.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2472 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://github.com/microsoft/terminal/files/14065211/Nezur.zip" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2804 | "C:\Windows\system32\cacls.exe" "C:\Windows\system32\config\system" | C:\Windows\System32\cacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Control ACLs Program Exit code: 5 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
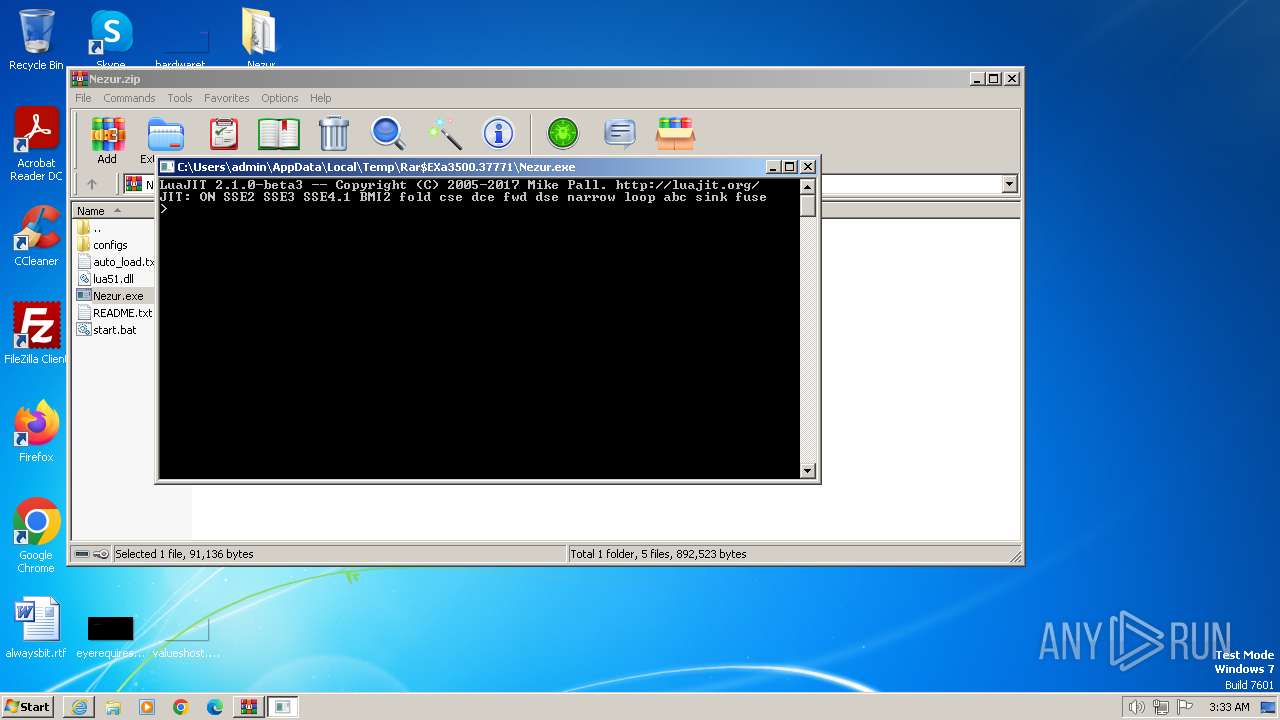
| 2908 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3500.37771\Nezur.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3500.37771\Nezur.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225786 Modules
| |||||||||||||||
| 3260 | "C:\Users\admin\Desktop\Nezur\Nezur.exe" | C:\Users\admin\Desktop\Nezur\Nezur.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225786 Modules
| |||||||||||||||
Total events
36 832
Read events
36 603
Write events
184
Delete events
45
Modification events
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31087770 | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 76469034 | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31087771 | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
6
Suspicious files
13
Text files
12
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3348 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\50CD3D75D026C82E2E718570BD6F44D0_D222662A57BAA60D2F5EA0D2CC7B2F1C | binary | |
MD5:0DBAACC5AF6AD66E35F0B7BEDD34F6C1 | SHA256:FB449D4371F8713F9E9D18CC35F9FFEA9A5EE7C01F75FA66CC9B1CE51C6FEAAA | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\50CD3D75D026C82E2E718570BD6F44D0_D222662A57BAA60D2F5EA0D2CC7B2F1C | binary | |
MD5:916E19D9AC0239ECE9B698F16D3A512B | SHA256:5358E8B739FC68BA08A7EBC642717B8DBAA2C02ACC08131DCB46C9CDD6806006 | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\TF0JWWFH.txt | text | |
MD5:C5418FE1555CC51CCF48FD2D182E6AE0 | SHA256:F30846C4B4925DDFC65103DB48E4A08F807EC006251E94E489216B0984B153D0 | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | binary | |
MD5:7F8FB4BE75362F6F39E793B29E4EE620 | SHA256:C53D726C8513E331389BAD46CB7663FDC6283B747FBCD7AF19424F2825B2EC1E | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_ADE4E4D3A3BCBCA5C39C54D362D88565 | binary | |
MD5:8FE65314F791E619C6227963093FF22B | SHA256:7785F1B9FB31B0C8E2EA64C29EB617C9BA97557111BC3668F53F35EE839050EA | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | binary | |
MD5:47484F8667C44200E4DA0F0E9C0D4659 | SHA256:38C6BD6BC1E8EB32E777D4F64A883801BE16B469407A9D0C377B4436024EAE0A | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:016A1E848DA622BB6F5AEE9D7B1E97A4 | SHA256:18078DB9EE8B069A87CAB3EFAF912463A2C48C233D29A479318DCD24CB3F30DE | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\Nezur[1].zip | compressed | |
MD5:2F5833175EAFC89DD0C23BFDD27A1D23 | SHA256:62253C05DD989444FFCA0674969DF1E6553550441909CA3B602E90648842081D | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\5C0TP2RD.txt | text | |
MD5:14D287F0D8FF701B367E13E38A1132D0 | SHA256:224FA2EC3280656DD6EBFABB51586A93A7BFB4C550C6E2F89D5FADB1D57AA70B | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\Nezur.zip.f888hpp.partial | compressed | |
MD5:AF97DDA652B878779309C854DBB05475 | SHA256:9B022527C62A75E4646DF18D77ACCEA72E30BBE6E35BE379F14DFF5E2951C922 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
24
DNS requests
9
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3348 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?c9f2b763ba05a2db | unknown | — | — | unknown |
3348 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?14266dff8470122f | unknown | — | — | unknown |
3348 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAfy81yHqHeveu%2FpR5k1Jb0%3D | unknown | binary | 471 b | unknown |
3348 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQrHR6YzPN2BNbByL0VoiTIBBMAOAQUCrwIKReMpTlteg7OM8cus%2B37w3oCEAzQqL7GMs%2FmReygqbCE%2Bxw%3D | unknown | binary | 313 b | unknown |
3348 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | unknown | binary | 471 b | unknown |
1080 | svchost.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?c503292d7802e201 | unknown | compressed | 65.2 Kb | unknown |
1080 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?1b8fee253118cbef | unknown | compressed | 65.2 Kb | unknown |
2472 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?49cb245571b3d6d6 | unknown | — | — | unknown |
2472 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?9aee5c2adfb08fdb | unknown | — | — | unknown |
2472 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3348 | iexplore.exe | 140.82.121.3:443 | github.com | GITHUB | US | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3348 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
3348 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3348 | iexplore.exe | 185.199.110.133:443 | objects.githubusercontent.com | FASTLY | US | unknown |
1080 | svchost.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
2472 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
2472 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
github.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
objects.githubusercontent.com |
| shared |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ip-api.com |
| shared |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
448 | Nezur.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
448 | Nezur.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |