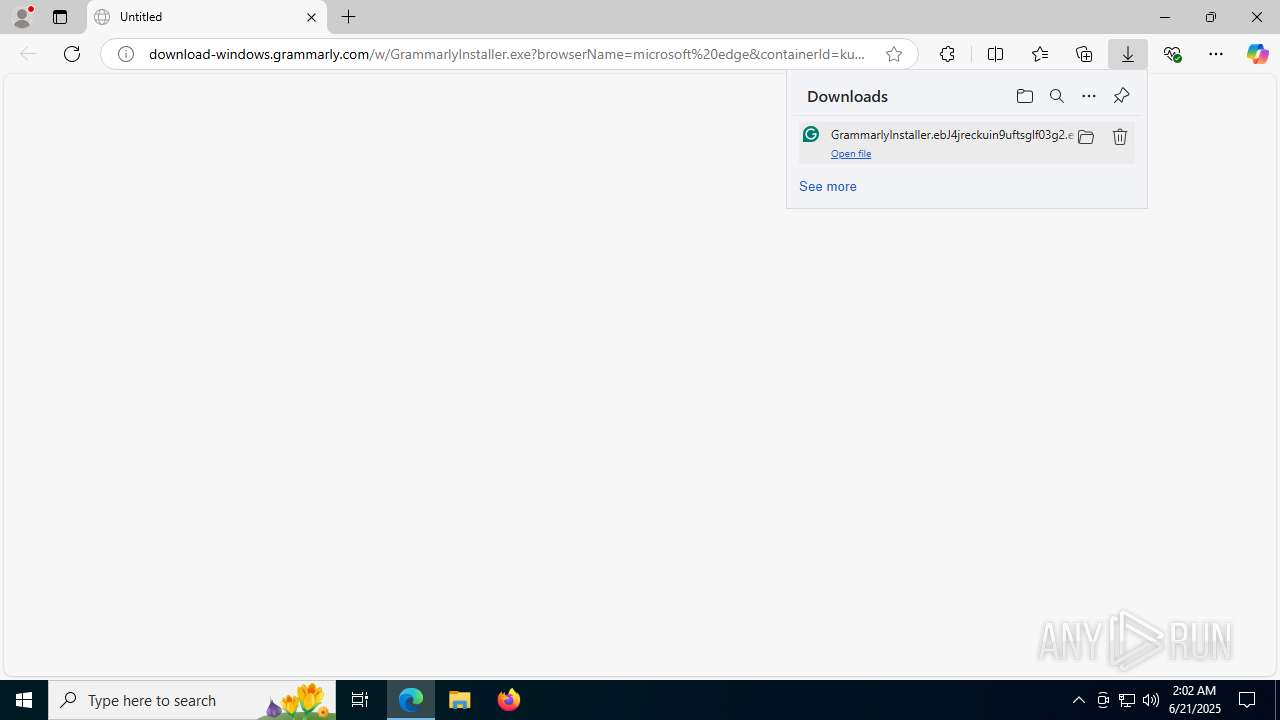
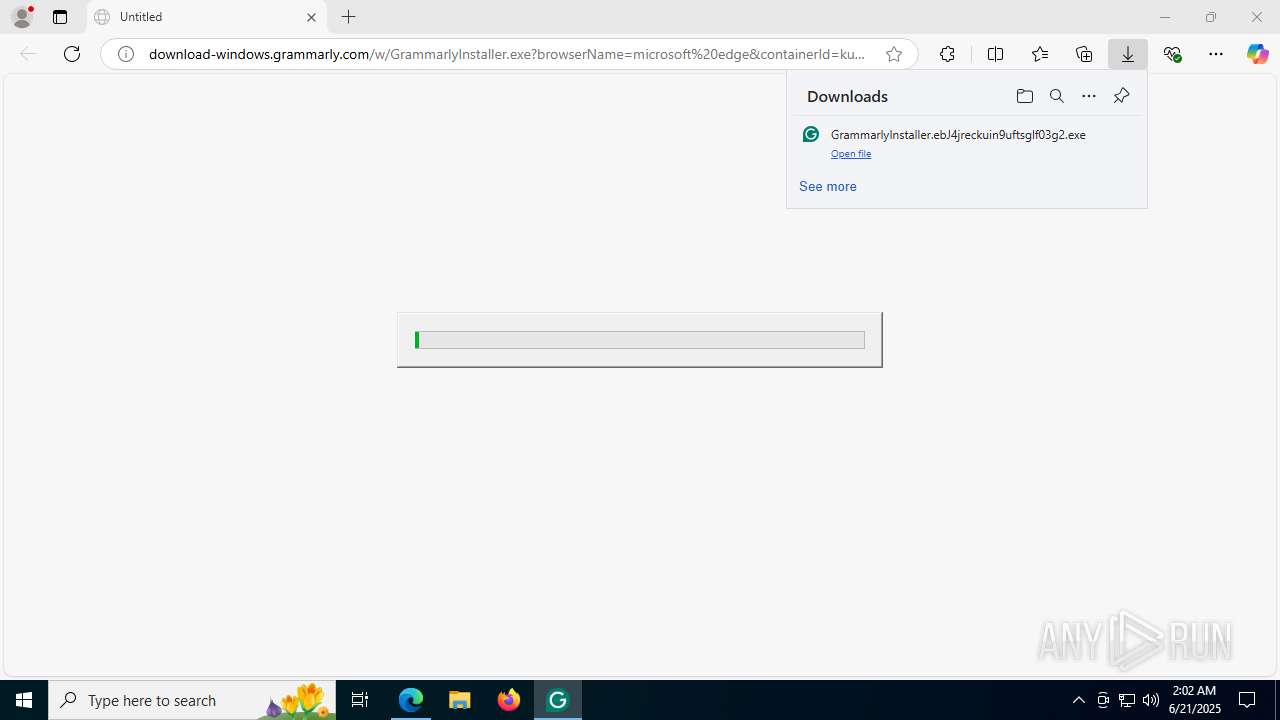
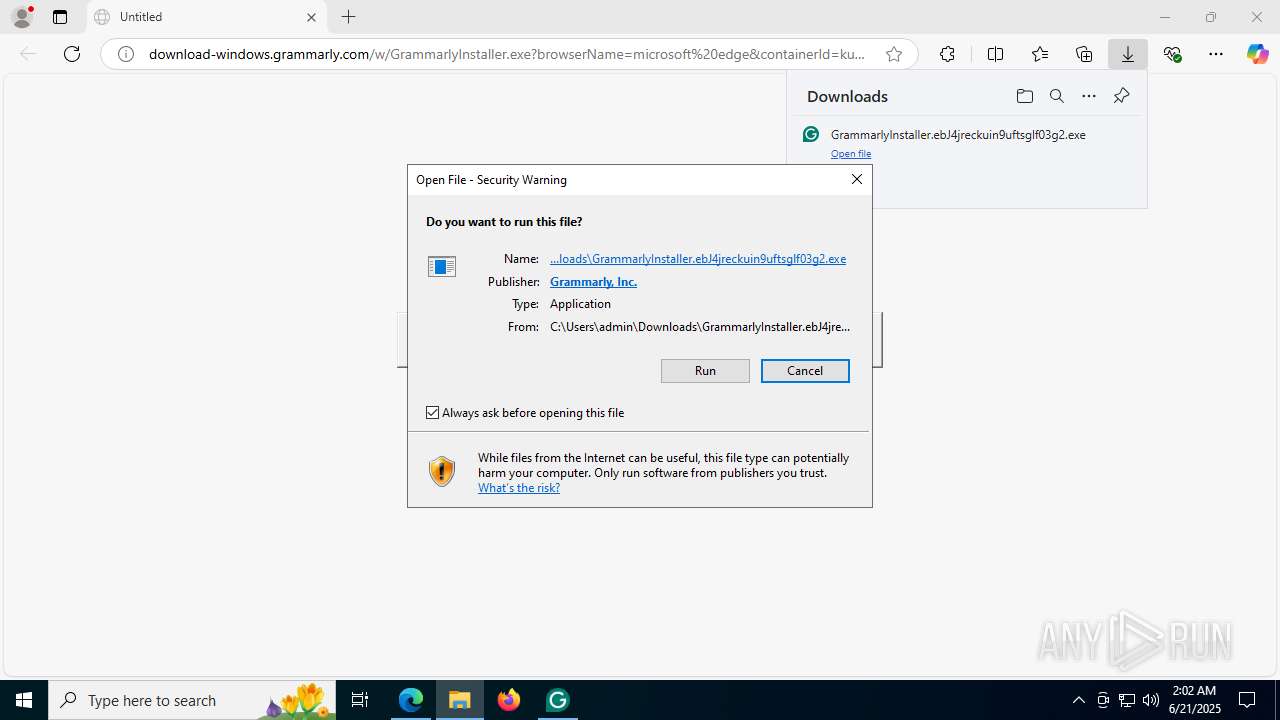
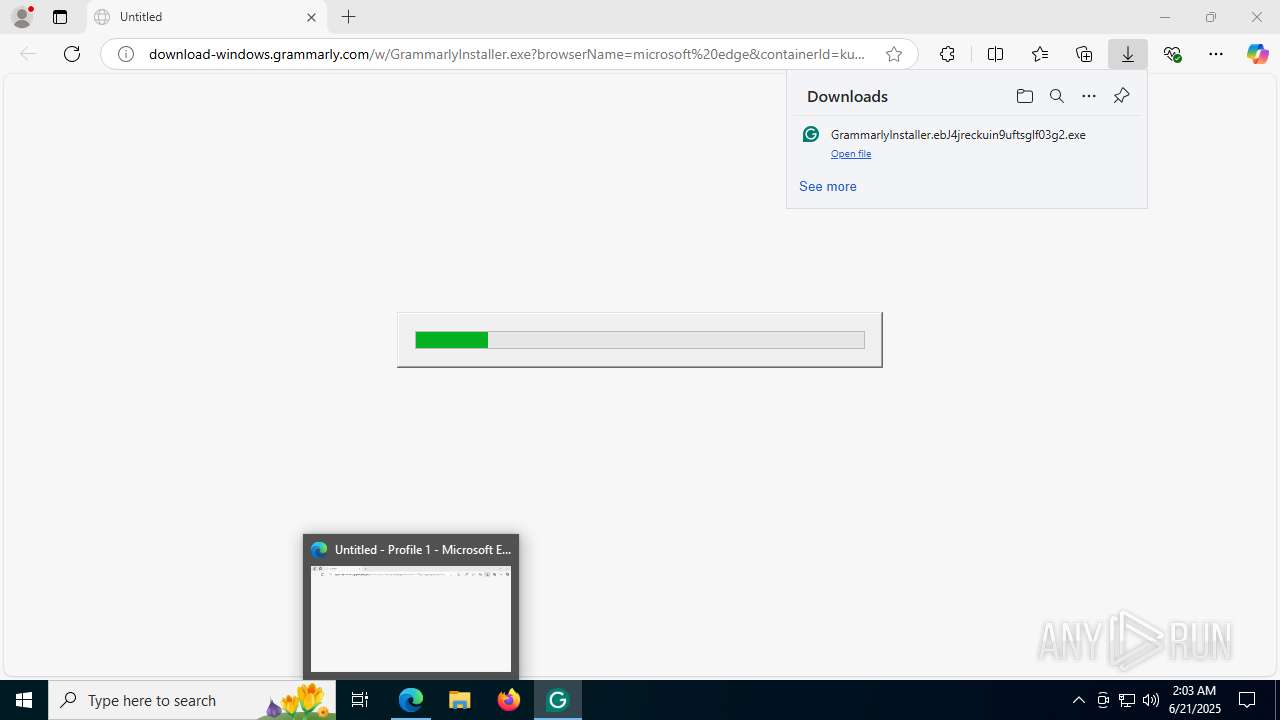
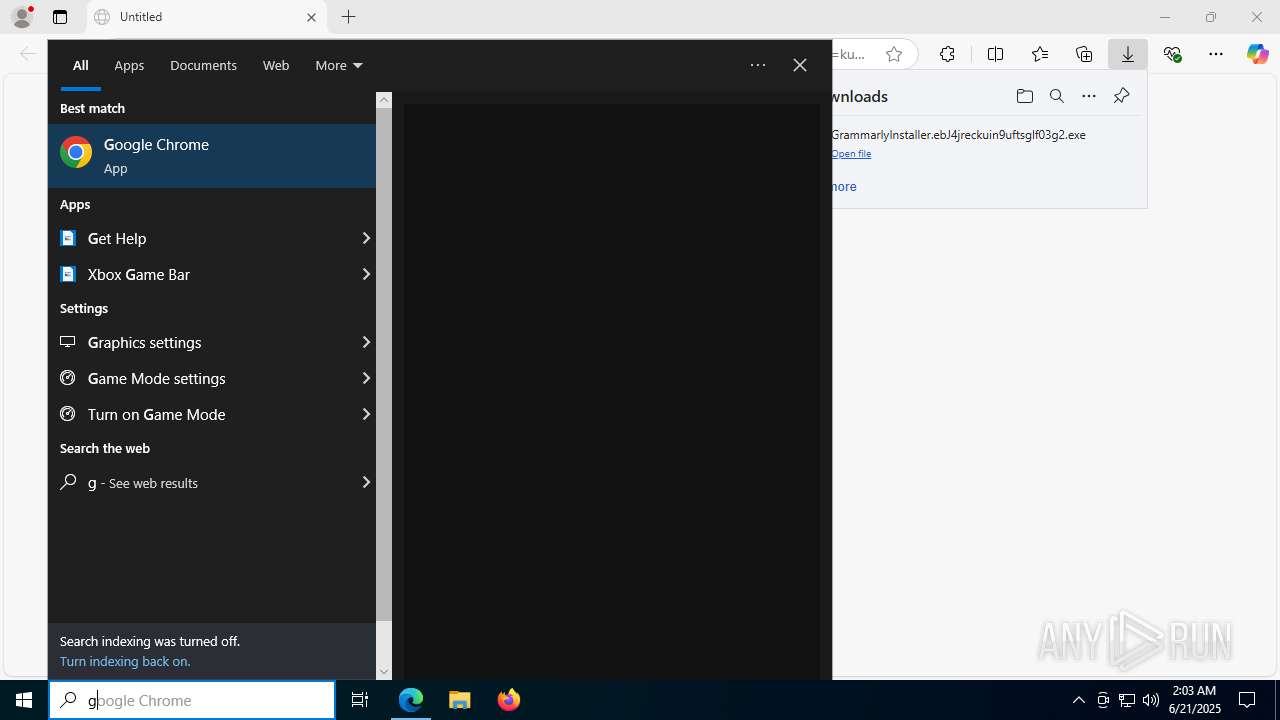
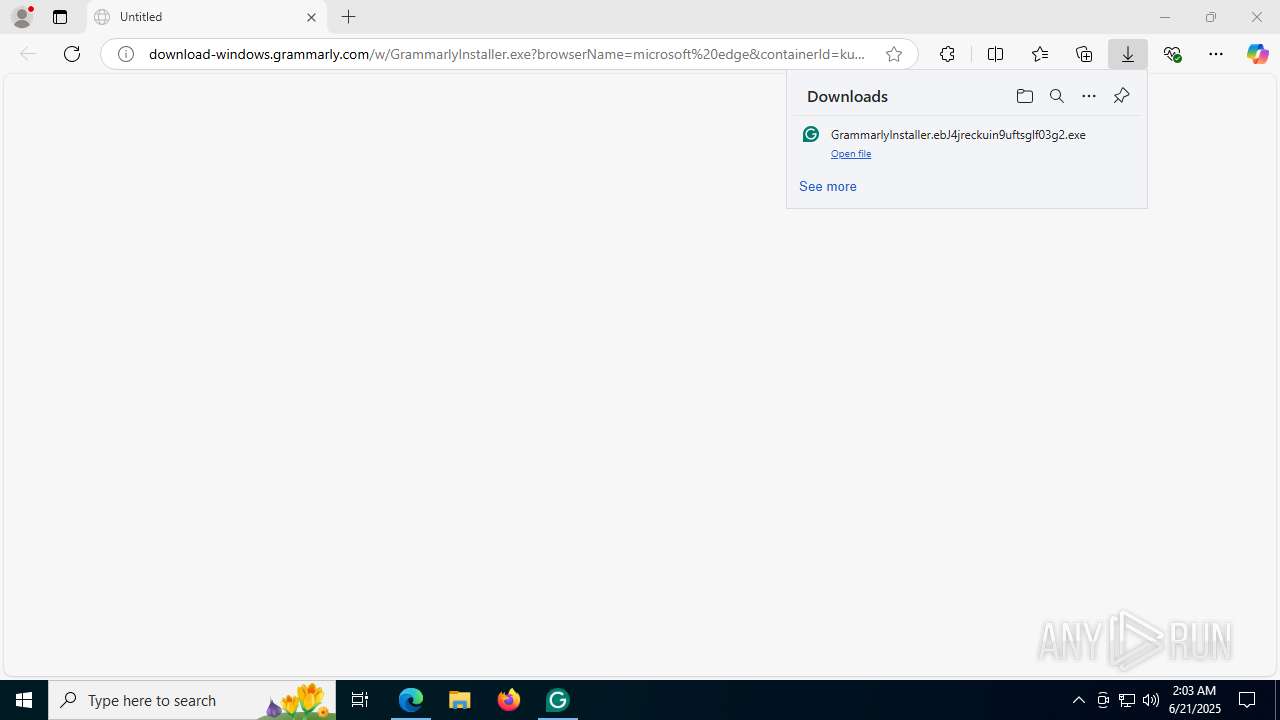
| URL: | download-windows.grammarly.com/w/GrammarlyInstaller.exe?browserName=microsoft%20edge&containerId=kuin9uftsglf03g2&state=bJ4jr&_gl=1*15qebba*_gcl_au*MTI5ODg3OTA3NC4xNzUwNDY2NTYy |
| Full analysis: | https://app.any.run/tasks/ab6b5fe2-6784-4e38-8b7c-23484246a1e3 |
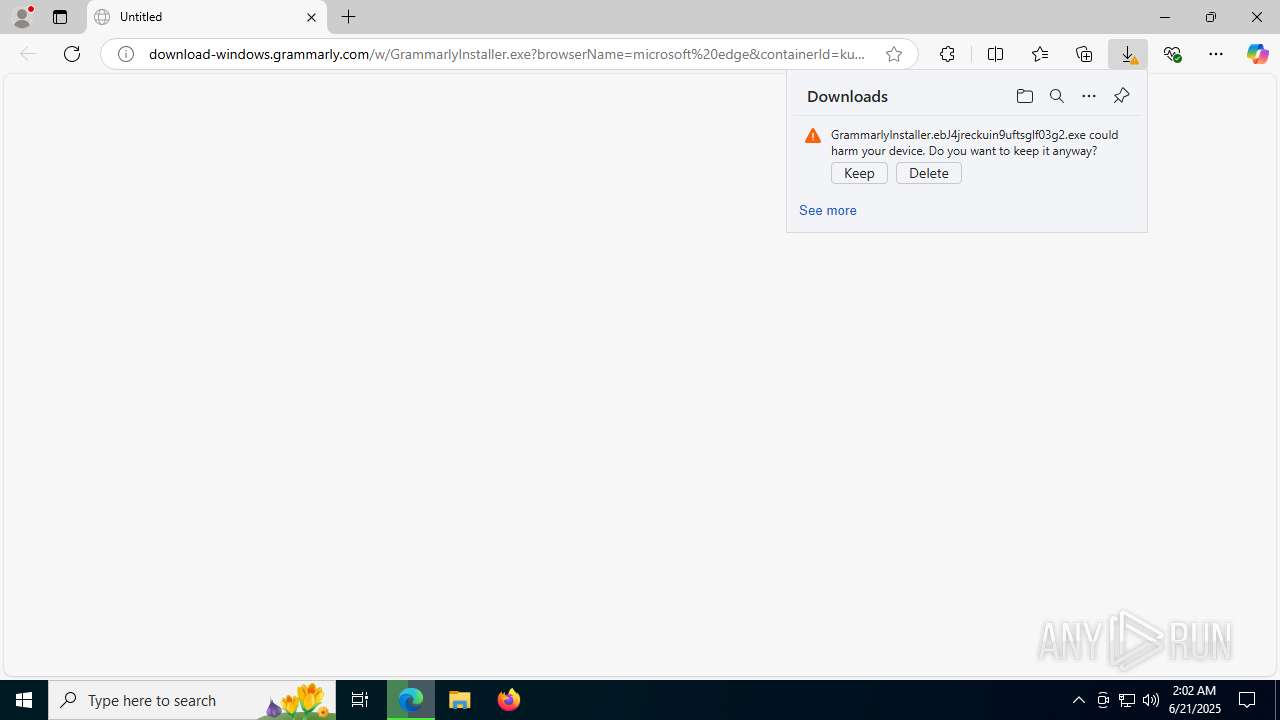
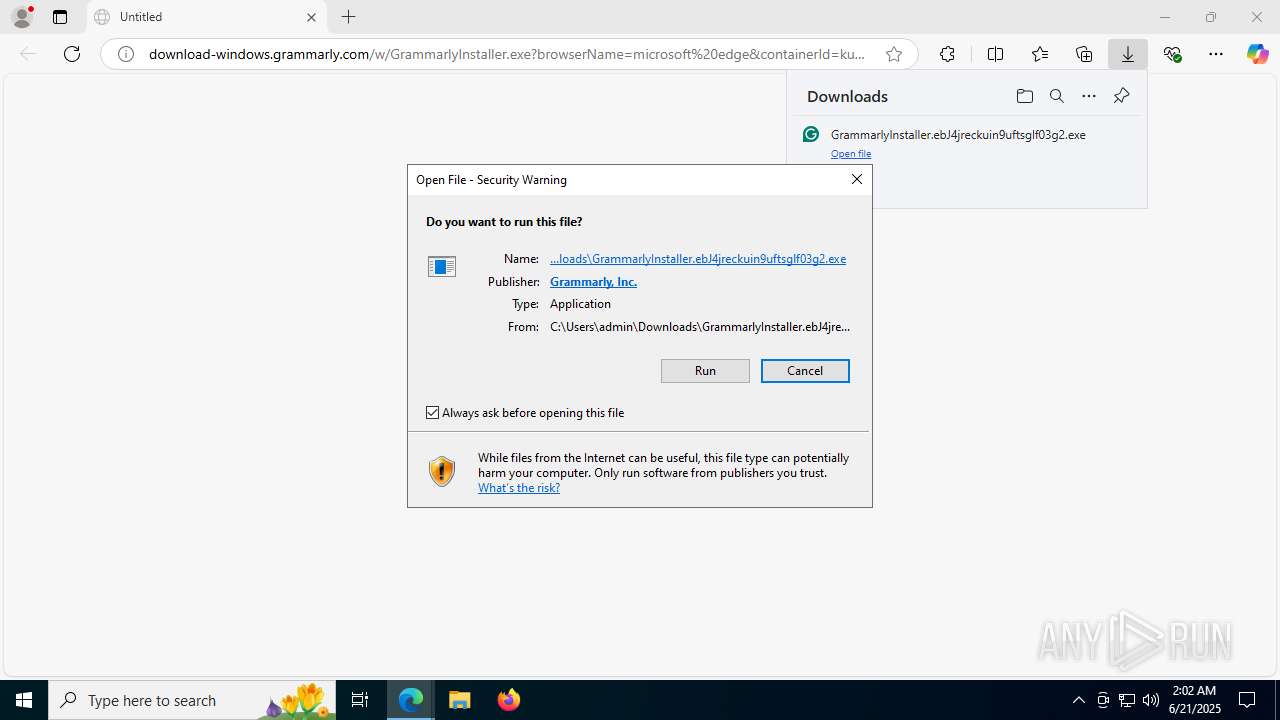
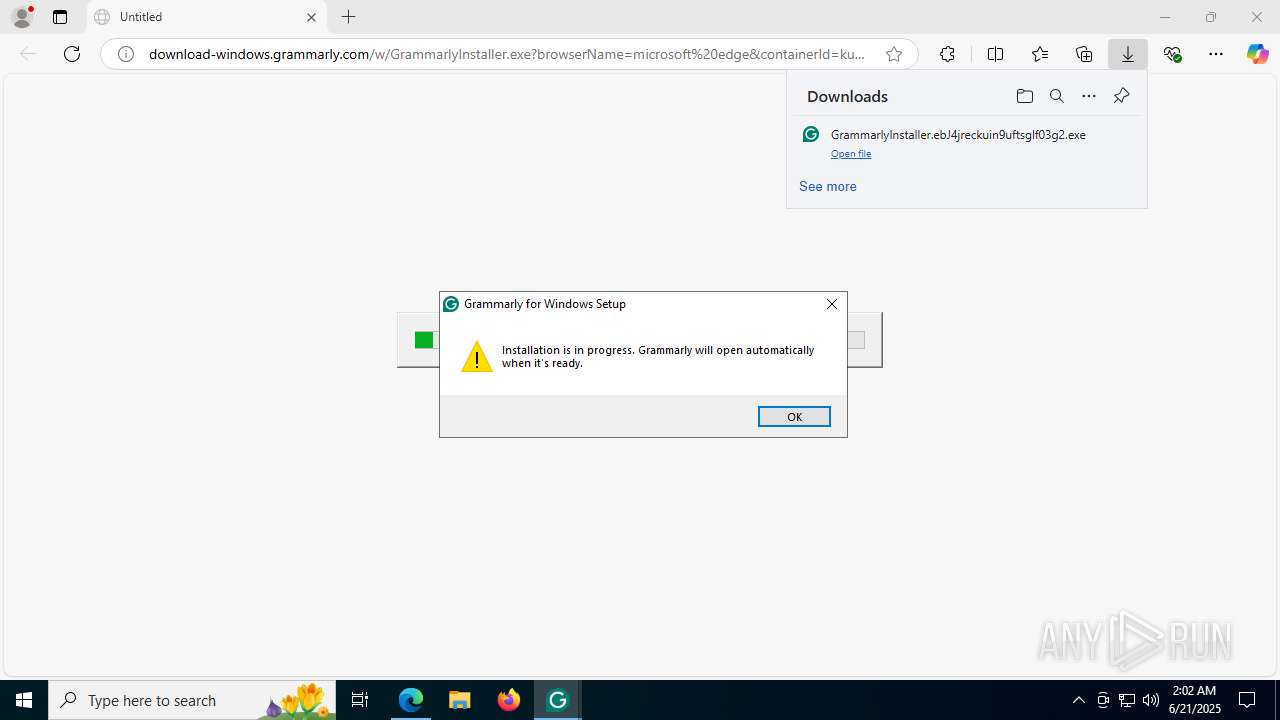
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2025, 02:02:14 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | CE51156A5153826204B9B49F164A32EF |
| SHA1: | 112589463283F479B4325D97A0B1859489236979 |
| SHA256: | D34760888CFE876F1EB12A6C107B969EA9D902C7885F2A228A8012574950DE1D |
| SSDEEP: | 3:ZKVSM1KSwI5Z6dwKXLNWJ30XNYmFPXgtLS4WaWTIvD6IsBdUysAVq1CdL2XrxN:ZlM1KSGPXL2eumF4vxSIvmIsB2ysAAUU |
MALICIOUS
Changes the autorun value in the registry
- MicrosoftEdgeUpdate.exe (PID: 8036)
- GrammarlyInstaller.ebJ4jreckuin9uftsglf03g2.exe (PID: 7924)
The DLL Hijacking
- msedgewebview2.exe (PID: 7696)
SUSPICIOUS
Executable content was dropped or overwritten
- GrammarlyInstaller.ebJ4jreckuin9uftsglf03g2.exe (PID: 7924)
- MicrosoftEdgeUpdate.exe (PID: 8036)
- MicrosoftEdge_X64_137.0.3296.93.exe (PID: 8160)
- MicrosoftEdgeWebview2Setup.exe (PID: 8008)
- GrammarlyInstaller.ebJ4jreckuin9uftsglf03g2.exe (PID: 6140)
- setup.exe (PID: 8064)
- msedgewebview2.exe (PID: 3768)
The process creates files with name similar to system file names
- GrammarlyInstaller.ebJ4jreckuin9uftsglf03g2.exe (PID: 7924)
- GrammarlyInstaller.ebJ4jreckuin9uftsglf03g2.exe (PID: 6140)
Malware-specific behavior (creating "System.dll" in Temp)
- GrammarlyInstaller.ebJ4jreckuin9uftsglf03g2.exe (PID: 7924)
- GrammarlyInstaller.ebJ4jreckuin9uftsglf03g2.exe (PID: 6140)
Starts a Microsoft application from unusual location
- MicrosoftEdgeWebview2Setup.exe (PID: 8008)
- MicrosoftEdgeUpdate.exe (PID: 8036)
Process drops legitimate windows executable
- MicrosoftEdgeWebview2Setup.exe (PID: 8008)
- MicrosoftEdgeUpdate.exe (PID: 8036)
- GrammarlyInstaller.ebJ4jreckuin9uftsglf03g2.exe (PID: 7924)
- MicrosoftEdge_X64_137.0.3296.93.exe (PID: 8160)
- setup.exe (PID: 8064)
- msedgewebview2.exe (PID: 3768)
Starts itself from another location
- MicrosoftEdgeUpdate.exe (PID: 8036)
Creates/Modifies COM task schedule object
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 8084)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 8112)
- MicrosoftEdgeUpdate.exe (PID: 8060)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 8140)
Reads security settings of Internet Explorer
- MicrosoftEdgeUpdate.exe (PID: 8036)
- MicrosoftEdgeUpdate.exe (PID: 7272)
- GrammarlyInstaller.ebJ4jreckuin9uftsglf03g2.exe (PID: 7924)
- Grammarly.Desktop.exe (PID: 2668)
- Grammarly.Desktop.exe (PID: 6796)
- msedgewebview2.exe (PID: 1336)
There is functionality for taking screenshot (YARA)
- GrammarlyInstaller.ebJ4jreckuin9uftsglf03g2.exe (PID: 7924)
- Grammarly.Desktop.exe (PID: 2668)
Application launched itself
- setup.exe (PID: 8064)
- MicrosoftEdgeUpdate.exe (PID: 7272)
- msedgewebview2.exe (PID: 1336)
Creates a software uninstall entry
- setup.exe (PID: 8064)
- GrammarlyInstaller.ebJ4jreckuin9uftsglf03g2.exe (PID: 7924)
Searches for installed software
- setup.exe (PID: 8064)
- msedgewebview2.exe (PID: 1336)
The process checks if it is being run in the virtual environment
- Grammarly.Desktop.exe (PID: 2668)
Get information on the list of running processes
- GrammarlyInstaller.ebJ4jreckuin9uftsglf03g2.exe (PID: 7924)
Reads the date of Windows installation
- Grammarly.Desktop.exe (PID: 2668)
INFO
Application launched itself
- msedge.exe (PID: 2044)
Executable content was dropped or overwritten
- msedge.exe (PID: 2044)
- msedge.exe (PID: 4476)
Reads Environment values
- identity_helper.exe (PID: 7524)
- MicrosoftEdgeUpdate.exe (PID: 8172)
- MicrosoftEdgeUpdate.exe (PID: 2604)
- Grammarly.Desktop.exe (PID: 2668)
- Grammarly.Desktop.exe (PID: 6796)
- msedgewebview2.exe (PID: 1336)
The sample compiled with english language support
- msedge.exe (PID: 2044)
- msedge.exe (PID: 4476)
- GrammarlyInstaller.ebJ4jreckuin9uftsglf03g2.exe (PID: 7924)
- MicrosoftEdgeUpdate.exe (PID: 8036)
- MicrosoftEdge_X64_137.0.3296.93.exe (PID: 8160)
- MicrosoftEdgeWebview2Setup.exe (PID: 8008)
- GrammarlyInstaller.ebJ4jreckuin9uftsglf03g2.exe (PID: 6140)
- setup.exe (PID: 8064)
- msedgewebview2.exe (PID: 3768)
Checks supported languages
- identity_helper.exe (PID: 7524)
- GrammarlyInstaller.ebJ4jreckuin9uftsglf03g2.exe (PID: 7924)
- MicrosoftEdgeUpdate.exe (PID: 8036)
- MicrosoftEdgeUpdate.exe (PID: 8060)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 8084)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 8140)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 8112)
- MicrosoftEdgeUpdate.exe (PID: 8172)
- MicrosoftEdgeUpdate.exe (PID: 768)
- MicrosoftEdgeWebview2Setup.exe (PID: 8008)
- MicrosoftEdgeUpdate.exe (PID: 7272)
- MicrosoftEdge_X64_137.0.3296.93.exe (PID: 8160)
- setup.exe (PID: 8064)
- setup.exe (PID: 7448)
- MicrosoftEdgeUpdateCore.exe (PID: 3840)
- MicrosoftEdgeUpdate.exe (PID: 7820)
- GrammarlyInstaller.ebJ4jreckuin9uftsglf03g2.exe (PID: 6140)
- MicrosoftEdgeUpdate.exe (PID: 2604)
- Grammarly.Desktop.exe (PID: 6796)
- Grammarly.Desktop.exe (PID: 2668)
- msedgewebview2.exe (PID: 4880)
- msedgewebview2.exe (PID: 1336)
- msedgewebview2.exe (PID: 7820)
- msedgewebview2.exe (PID: 8148)
- msedgewebview2.exe (PID: 7568)
- msedgewebview2.exe (PID: 7696)
- msedgewebview2.exe (PID: 8576)
- msedgewebview2.exe (PID: 8360)
- msedgewebview2.exe (PID: 8524)
- msedgewebview2.exe (PID: 9004)
- msedgewebview2.exe (PID: 2072)
- msedgewebview2.exe (PID: 3768)
- msedgewebview2.exe (PID: 4528)
Reads the computer name
- identity_helper.exe (PID: 7524)
- GrammarlyInstaller.ebJ4jreckuin9uftsglf03g2.exe (PID: 7924)
- MicrosoftEdgeUpdate.exe (PID: 8036)
- MicrosoftEdgeUpdate.exe (PID: 8060)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 8112)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 8140)
- MicrosoftEdgeUpdate.exe (PID: 8172)
- MicrosoftEdgeUpdate.exe (PID: 7272)
- MicrosoftEdgeUpdate.exe (PID: 768)
- MicrosoftEdge_X64_137.0.3296.93.exe (PID: 8160)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 8084)
- setup.exe (PID: 8064)
- MicrosoftEdgeUpdateCore.exe (PID: 3840)
- MicrosoftEdgeUpdate.exe (PID: 7820)
- GrammarlyInstaller.ebJ4jreckuin9uftsglf03g2.exe (PID: 6140)
- MicrosoftEdgeUpdate.exe (PID: 2604)
- Grammarly.Desktop.exe (PID: 2668)
- Grammarly.Desktop.exe (PID: 6796)
- msedgewebview2.exe (PID: 1336)
- msedgewebview2.exe (PID: 7696)
- msedgewebview2.exe (PID: 9004)
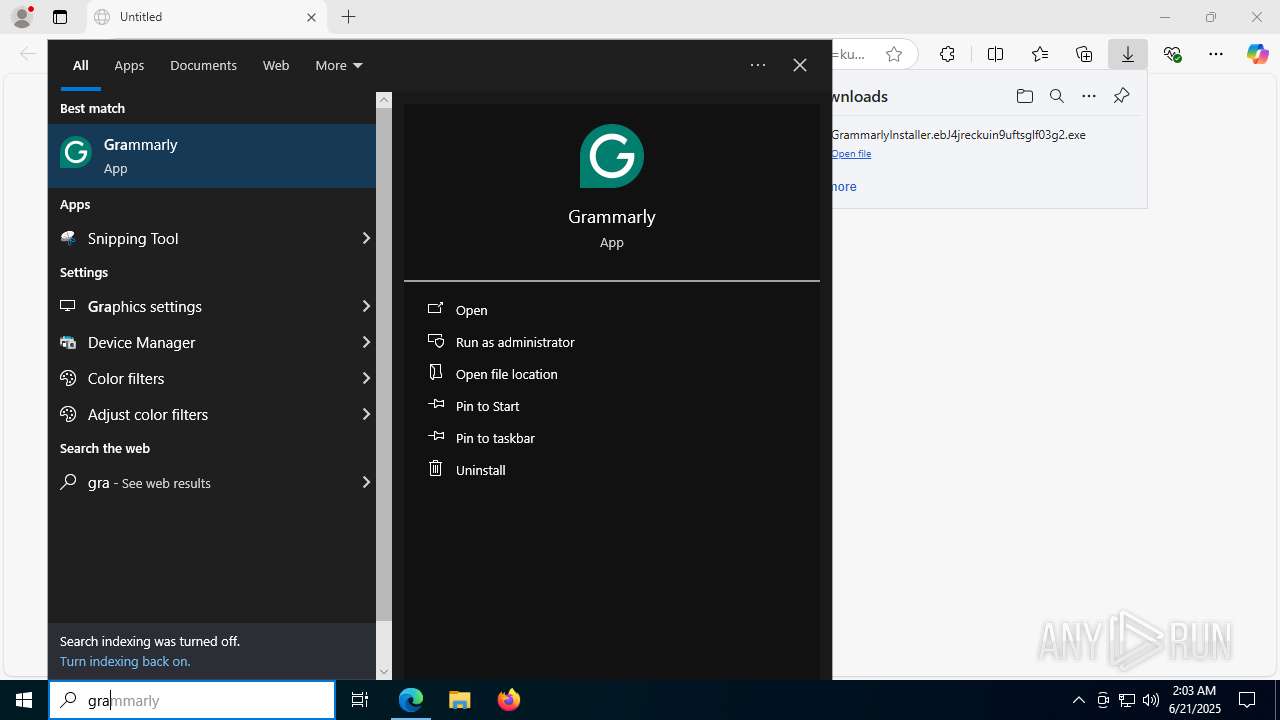
Launching a file from the Downloads directory
- msedge.exe (PID: 2044)
Create files in a temporary directory
- GrammarlyInstaller.ebJ4jreckuin9uftsglf03g2.exe (PID: 7924)
- MicrosoftEdgeWebview2Setup.exe (PID: 8008)
- GrammarlyInstaller.ebJ4jreckuin9uftsglf03g2.exe (PID: 6140)
- msedgewebview2.exe (PID: 1336)
Reads the machine GUID from the registry
- GrammarlyInstaller.ebJ4jreckuin9uftsglf03g2.exe (PID: 7924)
- MicrosoftEdgeUpdate.exe (PID: 7272)
- GrammarlyInstaller.ebJ4jreckuin9uftsglf03g2.exe (PID: 6140)
- Grammarly.Desktop.exe (PID: 2668)
- Grammarly.Desktop.exe (PID: 6796)
- msedgewebview2.exe (PID: 1336)
- msedgewebview2.exe (PID: 9004)
Creates files or folders in the user directory
- MicrosoftEdgeUpdate.exe (PID: 8036)
- MicrosoftEdgeUpdate.exe (PID: 7272)
- MicrosoftEdge_X64_137.0.3296.93.exe (PID: 8160)
- setup.exe (PID: 7448)
- setup.exe (PID: 8064)
- GrammarlyInstaller.ebJ4jreckuin9uftsglf03g2.exe (PID: 7924)
- Grammarly.Desktop.exe (PID: 2668)
- msedgewebview2.exe (PID: 4880)
- msedgewebview2.exe (PID: 7820)
- msedgewebview2.exe (PID: 9004)
- msedgewebview2.exe (PID: 1336)
Launching a file from a Registry key
- MicrosoftEdgeUpdate.exe (PID: 8036)
- GrammarlyInstaller.ebJ4jreckuin9uftsglf03g2.exe (PID: 7924)
Process checks computer location settings
- MicrosoftEdgeUpdate.exe (PID: 8036)
- setup.exe (PID: 8064)
- GrammarlyInstaller.ebJ4jreckuin9uftsglf03g2.exe (PID: 7924)
- msedgewebview2.exe (PID: 1336)
- msedgewebview2.exe (PID: 7568)
- Grammarly.Desktop.exe (PID: 2668)
Checks proxy server information
- MicrosoftEdgeUpdate.exe (PID: 8172)
- MicrosoftEdgeUpdate.exe (PID: 7272)
- MicrosoftEdgeUpdate.exe (PID: 2604)
- Grammarly.Desktop.exe (PID: 2668)
- msedgewebview2.exe (PID: 1336)
- Grammarly.Desktop.exe (PID: 6796)
- slui.exe (PID: 5340)
Reads the software policy settings
- MicrosoftEdgeUpdate.exe (PID: 8172)
- MicrosoftEdgeUpdate.exe (PID: 7272)
- MicrosoftEdgeUpdate.exe (PID: 2604)
- Grammarly.Desktop.exe (PID: 2668)
- Grammarly.Desktop.exe (PID: 6796)
- slui.exe (PID: 5340)
Manual execution by a user
- MicrosoftEdgeUpdateCore.exe (PID: 3840)
- GrammarlyInstaller.ebJ4jreckuin9uftsglf03g2.exe (PID: 6140)
- Grammarly.Desktop.exe (PID: 6796)
Disables trace logs
- Grammarly.Desktop.exe (PID: 2668)
- Grammarly.Desktop.exe (PID: 6796)
Reads CPU info
- msedgewebview2.exe (PID: 1336)
Creates files in the program directory
- Grammarly.Desktop.exe (PID: 2668)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
228
Monitored processes
82
Malicious processes
8
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 768 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe" /handoff "appguid={F3017226-FE2A-4295-8BDF-00C3A9A7E4C5}&appname=Microsoft%20Edge%20Webview2%20Runtime&needsadmin=false" /installsource otherinstallcmd /sessionid "{0CC70A68-5C1F-4F08-A026-5F3B91D00BE1}" /silent | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Exit code: 0 Version: 1.3.177.11 Modules
| |||||||||||||||
| 856 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_xpay_wallet.mojom.EdgeXPayWalletService --lang=en-US --service-sandbox-type=utility --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=7828,i,4508076538719102463,8766473239694528250,262144 --variations-seed-version --mojo-platform-channel-handle=4028 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1296 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" https://auth.grammarly.com/v4/api/oauth2/authorize?client_id=windowsExtension&code_challenge=I5V7VLmbAVC33R_d2DN4YagDFg2sFESLjyYYEKROIv4&redirect_uri=grammarly.windows-extension://oauth&response_mode=query&response_type=code&state=cba632bbab80463b880701ecde3c7e1f&scope=grammarly.capi.all&utm_medium=internal&utm_source=signupHook&utm_campaign=windowsExtension-webOnboarding&auth_cid=WIN-0be97b53-209b-4e6f-9be4-0b12b6f4d25d&screen_hint=signup | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | Grammarly.Desktop.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1336 | "C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\137.0.3296.93\msedgewebview2.exe" --embedded-browser-webview=1 --webview-exe-name=Grammarly.Desktop.exe --webview-exe-version=1.2.169.1689 --user-data-dir="C:\Users\admin\AppData\Roaming\Grammarly\DesktopIntegrations\WebViewUserDataFolder\EBWebView" --noerrdialogs --embedded-browser-webview-dpi-awareness=2 --disable-features=msForceBrowserSignIn --mojo-named-platform-channel-pipe=2668.3644.8440459631721153244 | C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\137.0.3296.93\msedgewebview2.exe | Grammarly.Desktop.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge WebView2 Version: 137.0.3296.93 Modules
| |||||||||||||||
| 1356 | tasklist /NH /FI "IMAGENAME eq Grammarly.Desktop.exe" | C:\Windows\SysWOW64\tasklist.exe | — | GrammarlyInstaller.ebJ4jreckuin9uftsglf03g2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1512 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=7868,i,4508076538719102463,8766473239694528250,262144 --variations-seed-version --mojo-platform-channel-handle=7492 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1812 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=29 --always-read-main-dll --field-trial-handle=8244,i,4508076538719102463,8766473239694528250,262144 --variations-seed-version --mojo-platform-channel-handle=8268 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2044 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "download-windows.grammarly.com/w/GrammarlyInstaller.exe?browserName=microsoft%20edge&containerId=kuin9uftsglf03g2&state=bJ4jr&_gl=1*15qebba*_gcl_au*MTI5ODg3OTA3NC4xNzUwNDY2NTYy" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2072 | "C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\137.0.3296.93\msedgewebview2.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Roaming\Grammarly\DesktopIntegrations\WebViewUserDataFolder\EBWebView" --webview-exe-name=Grammarly.Desktop.exe --webview-exe-version=1.2.169.1689 --embedded-browser-webview=1 --embedded-browser-webview-dpi-awareness=2 --force-high-res-timeticks=disabled --always-read-main-dll --field-trial-handle=1844,i,17025057526242844643,2557918772932813244,262144 --enable-features=ForceSWDCompWhenDCompFallbackRequired,msAggressiveCacheTrimming,msCustomDataPartition,msWebView2NoTabForScreenShare,msWindowsTaskManager --disable-features=BackForwardCache,BackgroundTabLoadingFromPerformanceManager,CloseOmniboxPopupOnInactiveAreaClick,CollectAVProductsInfo,CollectCodeIntegrityInfo,EnableHangWatcher,FilterAdsOnAbusiveSites,GetWifiProtocol,LoginDetection,MediaFoundationCameraUsageMonitoring,PreconnectToSearch,SafetyHub,SegmentationPlatform,SpareRendererForSitePerProcess,Ukm,WebPayments,msAITrackerClassification,msAbydosForWindowlessWV2,msAffirmVirtualCard,msAllowChromeWebstore,msAllowMSAPrtSSOForNonMSAProfile,msApplicationGuard,msAskBeforeClosingMultipleTabs,msAutoToggleAADPrtSSOForNonAADProfile,msAutofillEdgeCoupons,msAutofillEdgeCouponsAutoApply,msAutofillEdgeServiceRequest,msAutomaticTabFreeze,msBrowserSettingsSupported,msCoarseGeolocationService,msDataProtection,msDesktopMode,msDesktopRewards,msDisableVariationsSeedFetchThrottling,msEEProactiveHistory,msETFOffstoreExtensionFileDataCollection,msETFPasswordTheftDNRActionSignals,msEdgeAdPlatformUI,msEdgeAddWebCapturetoCollections,msEdgeAutofillAdvancedSuggestionsBasic,msEdgeAutofillOneClickAutocomplete,msEdgeAutofillShowDeployedPassword,msEdgeAutofillSs,msEdgeBrowserEssentialsShowUpdateSection,msEdgeCloudConfigService,msEdgeCloudConfigServiceV2,msEdgeCohorts,msEdgeCollectionsPrismExperiment1,msEdgeCollectionsPrismOverallMigration,msEdgeComposeNext,msEdgeEnableNurturingFramework,msEdgeEnclavePrefsBasic,msEdgeEnclavePrefsNotification,msEdgeFaviconService,msEdgeHJTelemetry,msEdgeHubAppSkype,msEdgeImageEditorUI,msEdgeLinkDoctor,msEdgeMouseGestureDefaultEnabled,msEdgeMouseGestureSupported,msEdgeNewDeviceFre,msEdgeOnRampFRE,msEdgeOnRampImport,msEdgePDFCMHighlightUX,msEdgePasswordIris,msEdgePasswordIrisSaveBubble,msEdgeProngPersonalization,msEdgeReadingView,msEdgeRose,msEdgeSendTabToSelf,msEdgeSettingsImport,msEdgeSettingsImportV2,msEdgeShoppingPersistentStorage,msEdgeShoppingUI,msEdgeSmartFind,msEdgeSuperDragDefaultEnabled,msEdgeSuperDragDropSupported,msEdgeTipping,msEdgeTranslate,msEdgeUseCaptivePortalService,msEdgeWebContentFilteringFeedback,msEdgeWorkSearchBanner,msEnableCustomJobMemoryLimitsOnXbox,msEnableMIPForPDF,msEnablePdfUpsell,msEnableThirdPartyScanning,msEnableWebSignInCta,msEnableWebToBrowserSignIn,msEndpointDlp,msEntityExtraction,msExtensionTelemetryFramework,msExternalTaskManager,msFileSystemAccessDirectoryIterationBlocklistCheck,msForceBrowserSignIn,msForeignSessionsPage,msGeolocationAccessService,msGeolocationOSLocationPermissionFallback,msGeolocationSQMService,msGeolocationService,msGrowthInfraLaunchSourceLogging,msGuidedSwitchAllowed,msHubPinPersist,msImplicitSignin,msIrm,msIrmv2,msKlarnaVirtualCard,msLoadStatistics,msLogIsEdgePinnedToTaskbarOnLaunch,msMIPCrossTenantPdfViewSupport,msMdatpWebSiteDlp,msNotificationPermissionForPWA,msOnHoverSearchInSidebar,msOpenOfficeDocumentsInWebViewer,msPasswordBreachDetection,msPdfAnnotationsVisibility,msPdfDataRecovery,msPdfDigitalSignatureRead,msPdfFreeText,msPdfFreeTextForCJK,msPdfHighlightMode,msPdfInking,msPdfKeyphraseSupport,msPdfOOUI,msPdfPopupMarkerRenderer,msPdfShare,msPdfSharedLibrary,msPdfTextNote,msPdfTextNoteMoreMenu,msPdfThumbnailCache,msPdfUnderside,msPdfViewRestore,msPersonalizationUMA,msPriceComparison,msPromptDefaultHandlerForPDF,msReactiveSearch,msReadAloud,msReadAloudPdf,msRedirectToShoreline,msRevokeExtensions,msSaasDlp,msShoppingTrigger,msShorelineSearch,msShorelineSearchFindOnPageWebUI,msShowOfflineGameEntrance,msShowReadAloudIconInAddressBar,msShowUXForAADPrtSSOForNonAADProfile,msSuspendMessageForNewSessionWhenHavingPendingNavigation,msSyncEdgeCollections,msTabResourceStats,msTokenizationAutofillInlineEnabled,msTouchMode,msTriggeringSignalGenerator,msUserUnderstanding,msVideoSuperResolutionUI,msWalletBuyNow,msWalletCheckout,msWalletDiagnosticDataLogger,msWalletHubEntry,msWalletHubIntlP3,msWalletPartialCard,msWalletPasswordCategorization,msWalletPasswordCategorizationPlatformExpansion,msWalletTokenizationCardMetadata,msWalletTokenizedAutofill,msWebAssist,msWebAssistHistorySearchService,msWebOOUI,msWindowsUserActivities,msZipPayVirtualCard --variations-seed-version --mojo-platform-channel-handle=4924 /prefetch:8 | C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\137.0.3296.93\msedgewebview2.exe | — | msedgewebview2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge WebView2 Exit code: 0 Version: 137.0.3296.93 Modules
| |||||||||||||||
| 2196 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=27 --always-read-main-dll --field-trial-handle=6056,i,4508076538719102463,8766473239694528250,262144 --variations-seed-version --mojo-platform-channel-handle=5432 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
51 419
Read events
49 854
Write events
1 494
Delete events
71
Modification events
| (PID) Process: | (2044) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2044) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2044) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2044) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 07B90BA7A1962F00 | |||
| (PID) Process: | (2044) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\394036 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {2251C3CF-212B-4205-B822-DD57E759F0C5} | |||
| (PID) Process: | (2044) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2044) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\394036 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {A40DB003-B39E-4FFD-907B-9BA332AF5BB0} | |||
| (PID) Process: | (2044) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (2044) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: E1931CA7A1962F00 | |||
| (PID) Process: | (2044) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
Executable files
392
Suspicious files
504
Text files
177
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2044 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF17666a.TMP | — | |
MD5:— | SHA256:— | |||
| 2044 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2044 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF17666a.TMP | — | |
MD5:— | SHA256:— | |||
| 2044 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2044 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF17667a.TMP | — | |
MD5:— | SHA256:— | |||
| 2044 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2044 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF17668a.TMP | — | |
MD5:— | SHA256:— | |||
| 2044 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2044 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF176699.TMP | — | |
MD5:— | SHA256:— | |||
| 2044 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
41
TCP/UDP connections
270
DNS requests
339
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4476 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:IW-uX8pI9vceu-r_JDXO5QUN1gjOzU3gP2Nk4NDYUyI&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
2044 | msedge.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
1380 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2044 | msedge.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
7436 | svchost.exe | GET | — | 199.232.214.172:80 | http://msedge.f.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/374fbcab-db99-484d-b624-ce059f21ef35?P1=1751076156&P2=404&P3=2&P4=jZSBmJ2MwPKFqozkUqlwUqRAR4zDaE4s19o0VjLZ2zqPf0ah7SwpzrIWQQ35ObcYq8my4maPLEytEDZZ0BEJ5g%3d%3d | unknown | — | — | whitelisted |
7436 | svchost.exe | HEAD | 200 | 23.50.131.74:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1751064498&P2=404&P3=2&P4=fhbvry%2fVXe2YVnwTL1jAEC9jobIqFBMMbWB%2fsBM9sOzF4c%2fePcQEaYhn%2f%2fLZD1mGJruloPrDCxPkndJu4ZpIuw%3d%3d | unknown | — | — | whitelisted |
7436 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.f.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/374fbcab-db99-484d-b624-ce059f21ef35?P1=1751076156&P2=404&P3=2&P4=jZSBmJ2MwPKFqozkUqlwUqRAR4zDaE4s19o0VjLZ2zqPf0ah7SwpzrIWQQ35ObcYq8my4maPLEytEDZZ0BEJ5g%3d%3d | unknown | — | — | whitelisted |
7568 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.55.104.190:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7568 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4648 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4476 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4476 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4476 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4476 | msedge.exe | 2.16.241.220:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
4476 | msedge.exe | 18.172.112.48:80 | download-windows.grammarly.com | — | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
download-windows.grammarly.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
www.bing.com |
| whitelisted |
edgeassetservice.azureedge.net |
| whitelisted |
client.wns.windows.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7436 | svchost.exe | Misc activity | ET INFO Packed Executable Download |
4476 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to sentry .io |
4476 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to sentry .io |
4476 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
4476 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
4476 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
4476 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
4476 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
4476 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
Process | Message |
|---|---|
msedgewebview2.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Roaming\Grammarly\DesktopIntegrations directory exists )
|