| File name: | NoDefender.exe |
| Full analysis: | https://app.any.run/tasks/785dbf06-48d9-42ed-9e4f-6439e43d21de |
| Verdict: | Malicious activity |
| Analysis date: | April 15, 2021, 19:09:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 1081EF14554BD43484E7F8822E3BBEB5 |
| SHA1: | A229A5E4514549BFF4BE102B04AF38D72BE77BCA |
| SHA256: | D3427F8A970DC08D0435A3D026B247F2F58EB236B1589A4598BCA57D1A643FFF |
| SSDEEP: | 24576:niLlwm5wxlzt3QdKkyK+siLlwm5wxlzt3QdKkyK+/40xS71+3KmcFMS:i5Ot3vkyK+f5Ot3vkyK+tQ71+3H |
MALICIOUS
Application was dropped or rewritten from another process
- PsExec.exe (PID: 1400)
- PSEXESVC.exe (PID: 580)
- PsExec.exe (PID: 2612)
- PSEXESVC.exe (PID: 2992)
Drops executable file immediately after starts
- PsExec.exe (PID: 1400)
SUSPICIOUS
Reads the computer name
- NoDefender.exe (PID: 3220)
- PsExec.exe (PID: 1400)
- PsExec.exe (PID: 2612)
- PSEXESVC.exe (PID: 2992)
- PSEXESVC.exe (PID: 580)
Checks supported languages
- NoDefender.exe (PID: 3220)
- PsExec.exe (PID: 1400)
- PsExec.exe (PID: 2612)
- PSEXESVC.exe (PID: 2992)
- PSEXESVC.exe (PID: 580)
Executed via COM
- explorer.exe (PID: 3768)
Executable content was dropped or overwritten
- NoDefender.exe (PID: 3220)
- PsExec.exe (PID: 2612)
- PsExec.exe (PID: 1400)
Drops a file that was compiled in debug mode
- NoDefender.exe (PID: 3220)
- PsExec.exe (PID: 2612)
- PsExec.exe (PID: 1400)
Executed as Windows Service
- PSEXESVC.exe (PID: 580)
- PSEXESVC.exe (PID: 2992)
Uses REG.EXE to modify Windows registry
- PSEXESVC.exe (PID: 580)
- PSEXESVC.exe (PID: 2992)
Removes files from Windows directory
- PsExec.exe (PID: 1400)
- PsExec.exe (PID: 2612)
Creates files in the Windows directory
- PsExec.exe (PID: 2612)
- PsExec.exe (PID: 1400)
INFO
Checks supported languages
- explorer.exe (PID: 3392)
- WISPTIS.EXE (PID: 3964)
- explorer.exe (PID: 3768)
- reg.exe (PID: 740)
- reg.exe (PID: 3156)
Reads the computer name
- WISPTIS.EXE (PID: 3964)
- explorer.exe (PID: 3392)
- explorer.exe (PID: 3768)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| AssemblyVersion: | 1.0.0.0 |
|---|---|
| ProductVersion: | 1.0.0.0 |
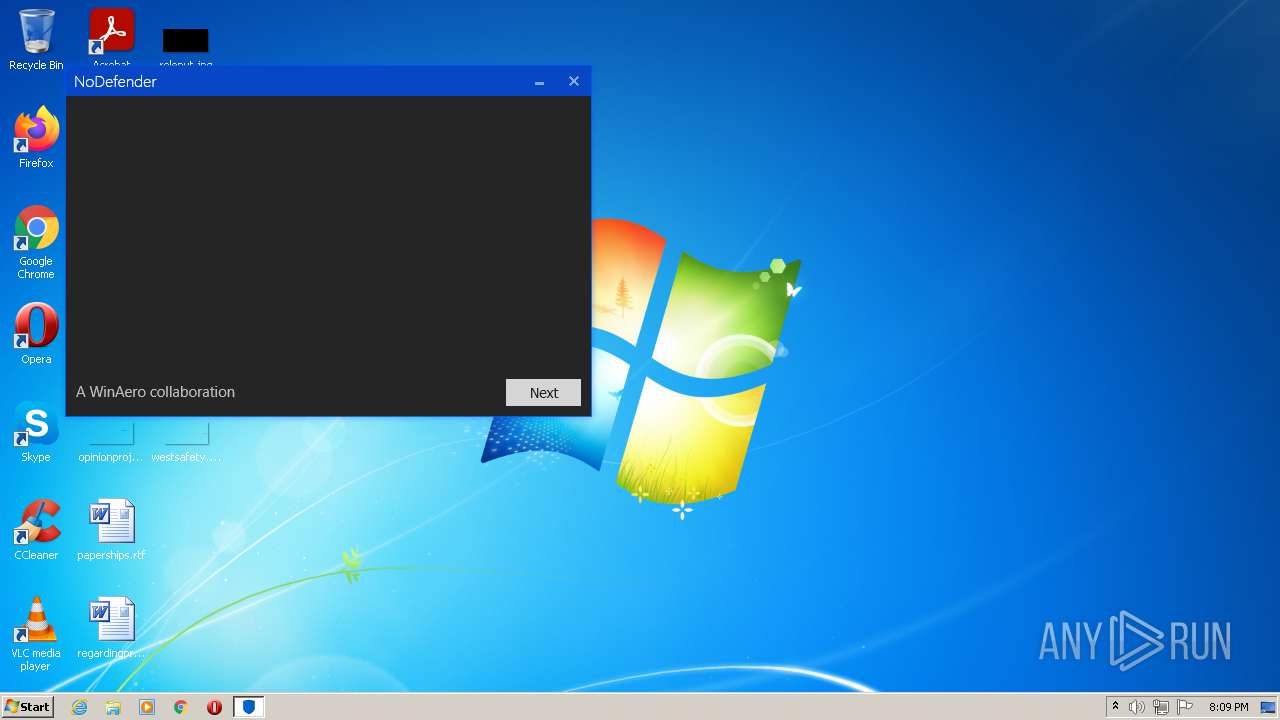
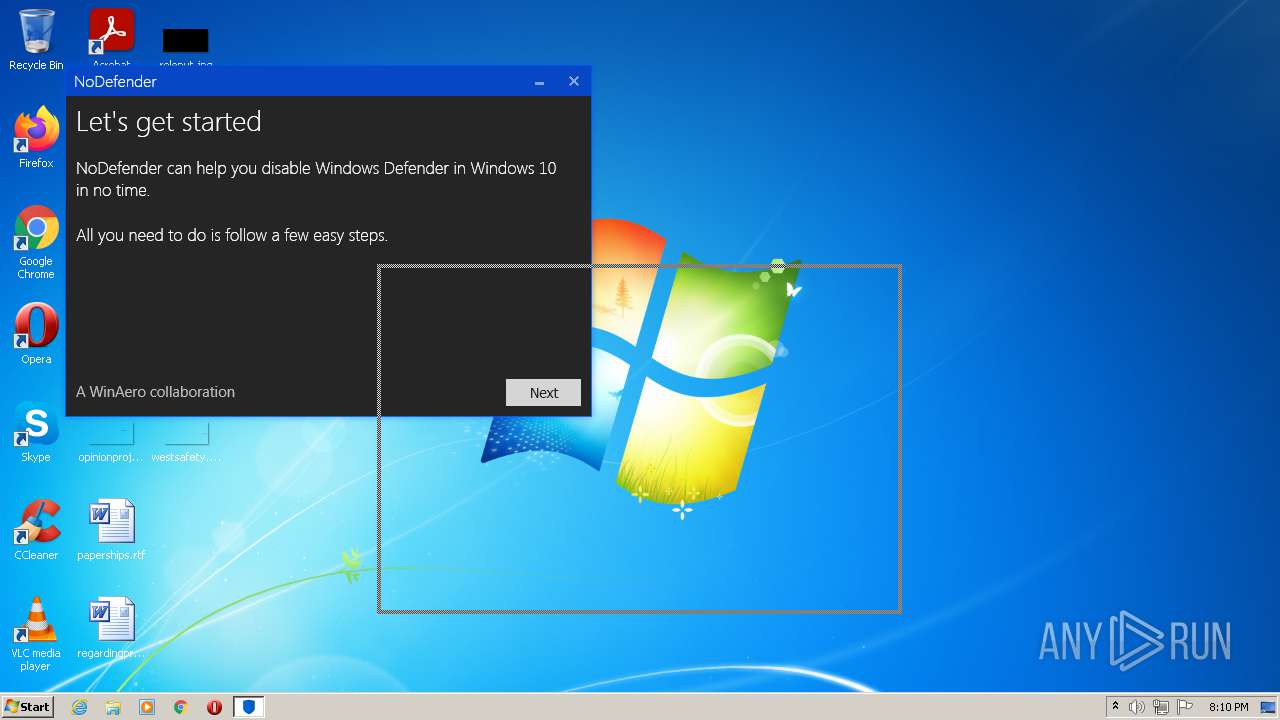
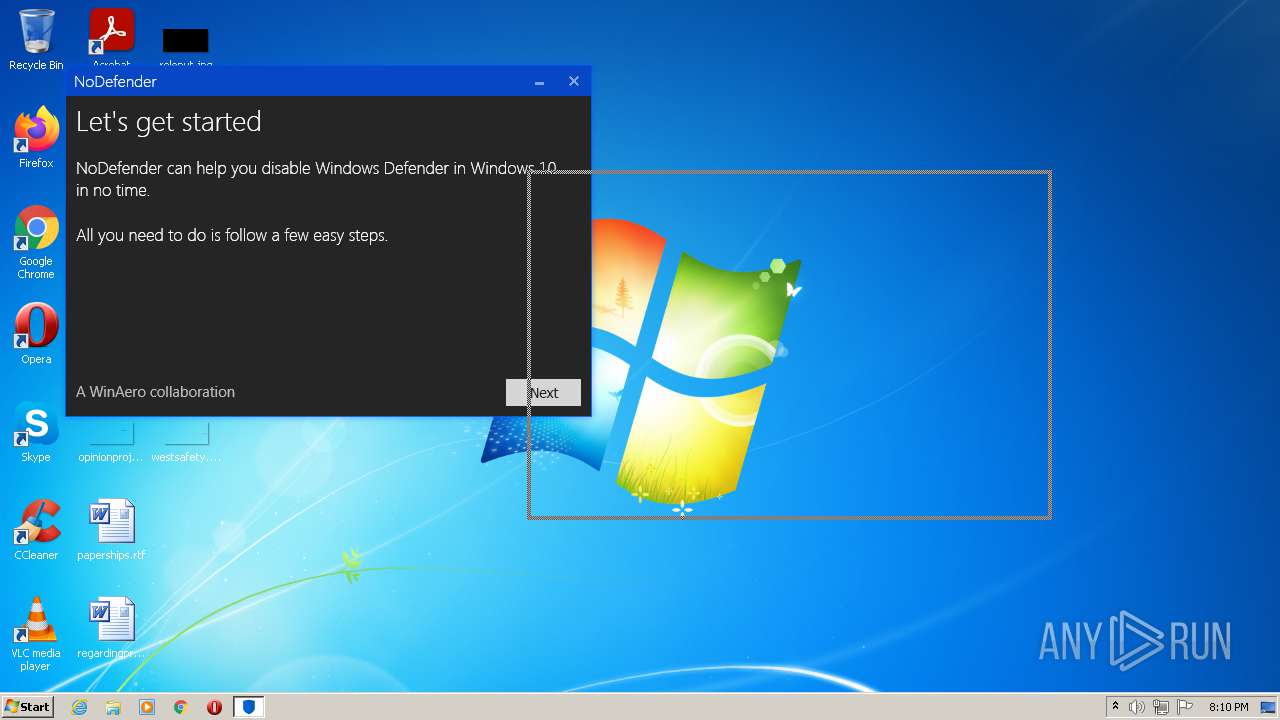
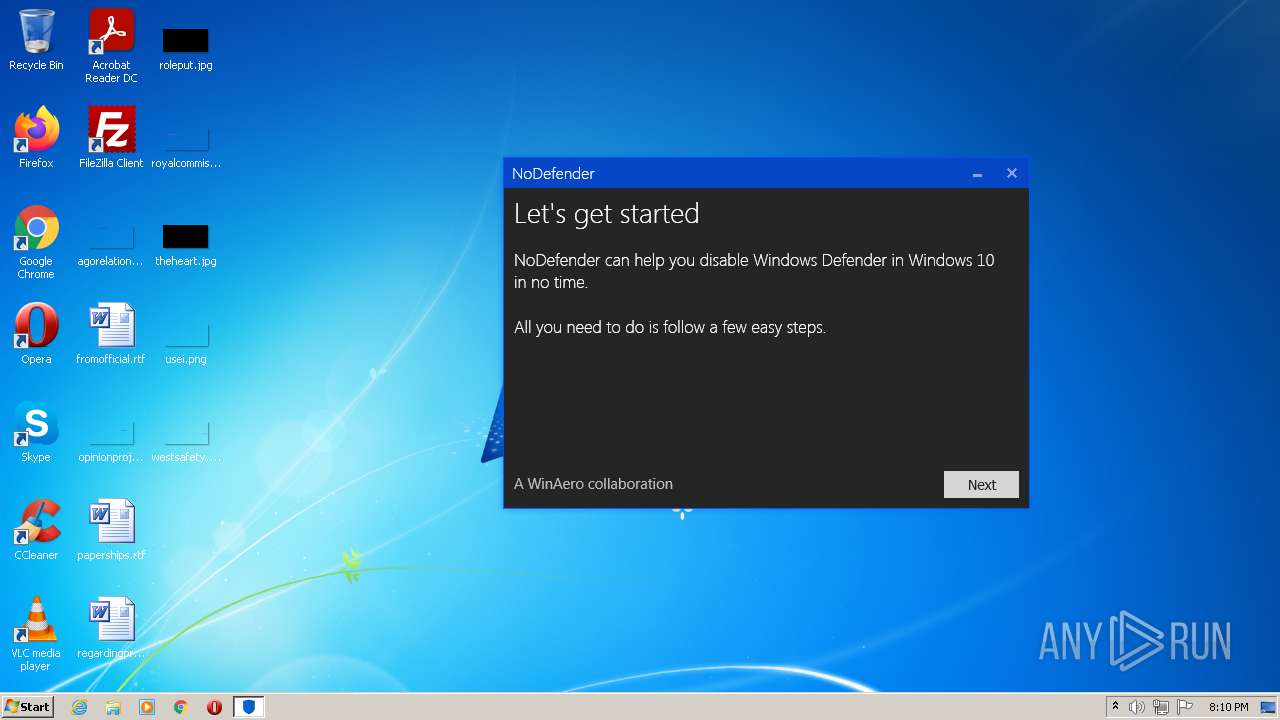
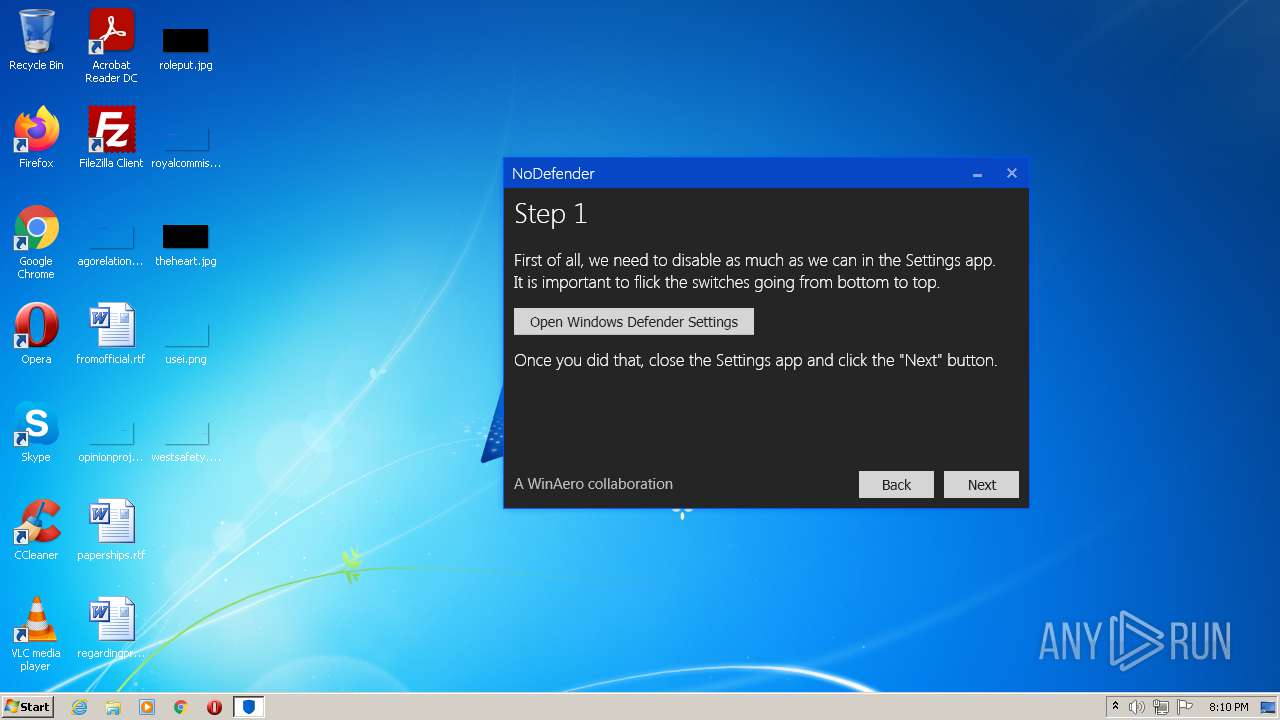
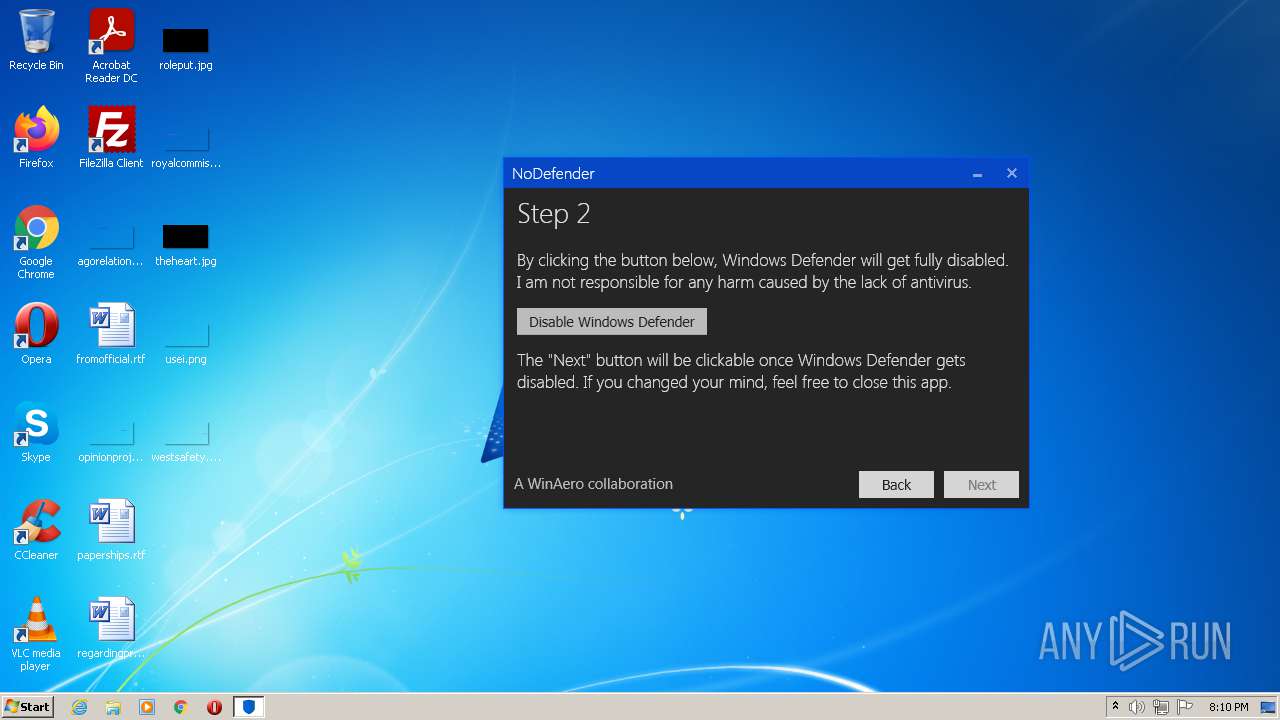
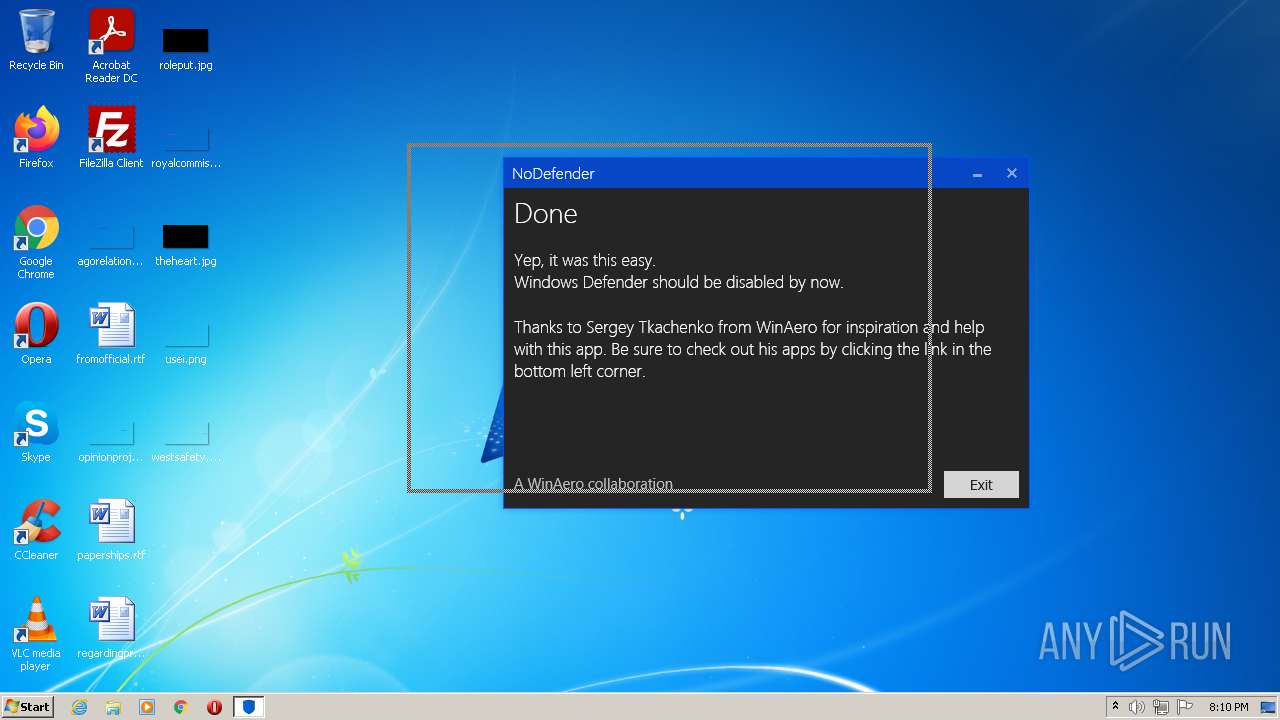
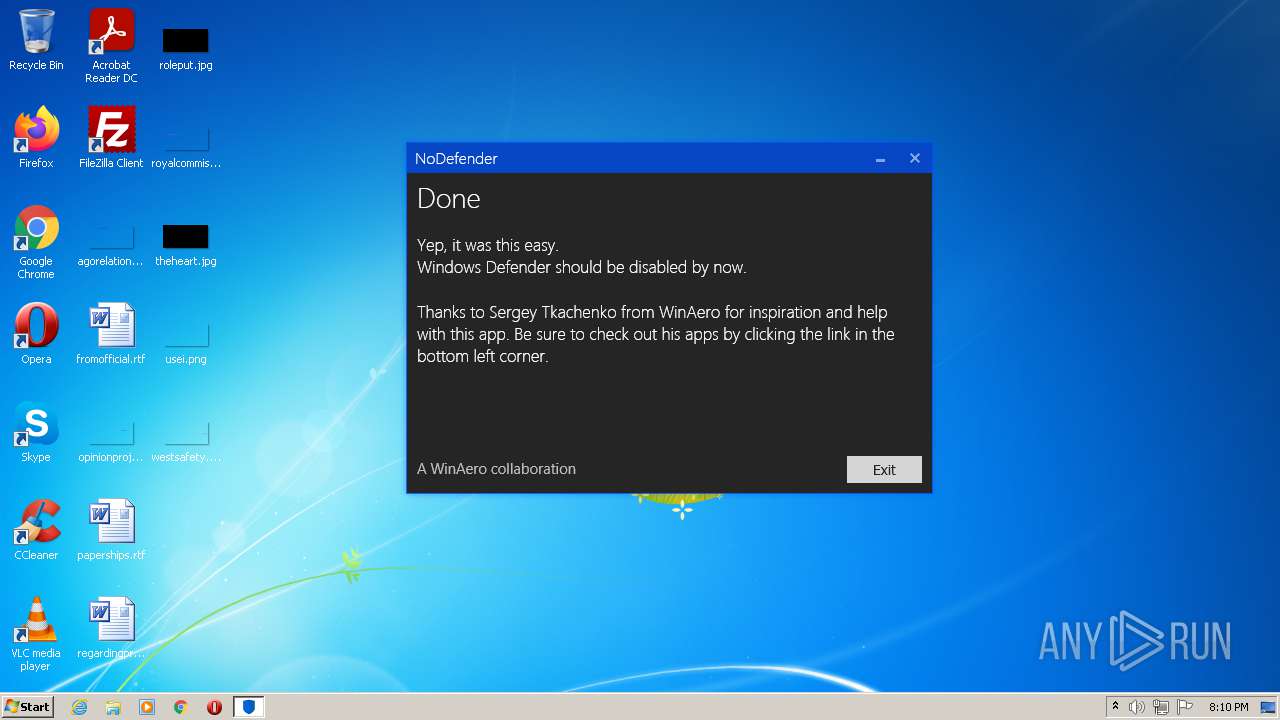
| ProductName: | NoDefender |
| OriginalFileName: | NoDefender.exe |
| LegalCopyright: | Copyright © Lucas M. 2015 |
| InternalName: | NoDefender.exe |
| FileVersion: | 1.0.0.0 |
| FileDescription: | NoDefender |
| CompanyName: | WinAero |
| Comments: | Easily disable Windows Defender in post-March Windows 10 builds. |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x136f0e |
| UninitializedDataSize: | - |
| InitializedDataSize: | 173056 |
| CodeSize: | 1265664 |
| LinkerVersion: | 8 |
| PEType: | PE32 |
| TimeStamp: | 2015:06:01 23:30:50+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Jun-2015 21:30:50 |
| Debug artifacts: |
|
| Comments: | Easily disable Windows Defender in post-March Windows 10 builds. |
| CompanyName: | WinAero |
| FileDescription: | NoDefender |
| FileVersion: | 1.0.0.0 |
| InternalName: | NoDefender.exe |
| LegalCopyright: | Copyright © Lucas M. 2015 |
| OriginalFilename: | NoDefender.exe |
| ProductName: | NoDefender |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 01-Jun-2015 21:30:50 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00134F14 | 0x00135000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.80646 |
.rsrc | 0x00138000 | 0x0002A200 | 0x0002A200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.1989 |
.reloc | 0x00164000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.04075 | 2861 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 7.81097 | 6054 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 2.36498 | 67624 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 2.79445 | 38056 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 2.76328 | 21640 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 2.5431 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 2.96171 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
8 | 2.89678 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
9 | 3.26673 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
10 | 3.4016 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
Imports
mscoree.dll |
Total processes
52
Monitored processes
12
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 580 | C:\Windows\PSEXESVC.exe | C:\Windows\PSEXESVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Sysinternals Integrity Level: SYSTEM Description: PsExec Service Exit code: 0 Version: 2.11 Modules
| |||||||||||||||
| 740 | "reg" import C:\Users\admin\AppData\Local\Temp\DisableApp.reg | C:\Windows\system32\reg.exe | — | PSEXESVC.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1400 | "C:\Users\admin\AppData\Local\Temp\PsExec.exe" -accepteula -s "reg" import C:\Users\admin\AppData\Local\Temp\DisableApp.reg | C:\Users\admin\AppData\Local\Temp\PsExec.exe | NoDefender.exe | ||||||||||||
User: admin Company: Sysinternals - www.sysinternals.com Integrity Level: HIGH Description: Execute processes remotely Exit code: 0 Version: 2.11 Modules
| |||||||||||||||
| 2612 | "C:\Users\admin\AppData\Local\Temp\NoDefender.exe" | C:\Users\admin\AppData\Local\Temp\NoDefender.exe | — | Explorer.EXE | |||||||||||
User: admin Company: WinAero Integrity Level: MEDIUM Description: NoDefender Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2612 | "C:\Users\admin\AppData\Local\Temp\PsExec.exe" -accepteula -s "reg" import C:\Users\admin\AppData\Local\Temp\DisableApp.reg | C:\Users\admin\AppData\Local\Temp\PsExec.exe | NoDefender.exe | ||||||||||||
User: admin Company: Sysinternals - www.sysinternals.com Integrity Level: HIGH Description: Execute processes remotely Exit code: 0 Version: 2.11 Modules
| |||||||||||||||
| 2652 | "C:\Windows\SYSTEM32\WISPTIS.EXE" /ManualLaunch; | C:\Windows\SYSTEM32\WISPTIS.EXE | — | NoDefender.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Pen and Touch Input Component Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2992 | C:\Windows\PSEXESVC.exe | C:\Windows\PSEXESVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Sysinternals Integrity Level: SYSTEM Description: PsExec Service Exit code: 0 Version: 2.11 Modules
| |||||||||||||||
| 3156 | "reg" import C:\Users\admin\AppData\Local\Temp\DisableApp.reg | C:\Windows\system32\reg.exe | — | PSEXESVC.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
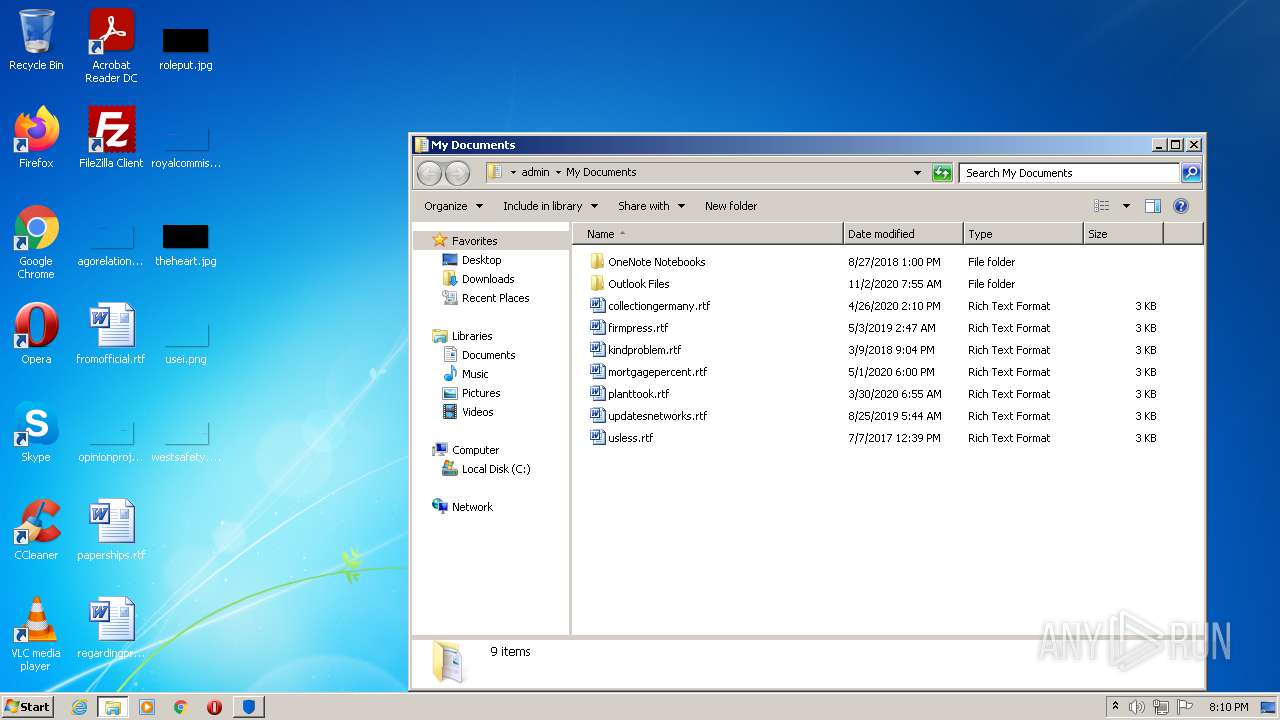
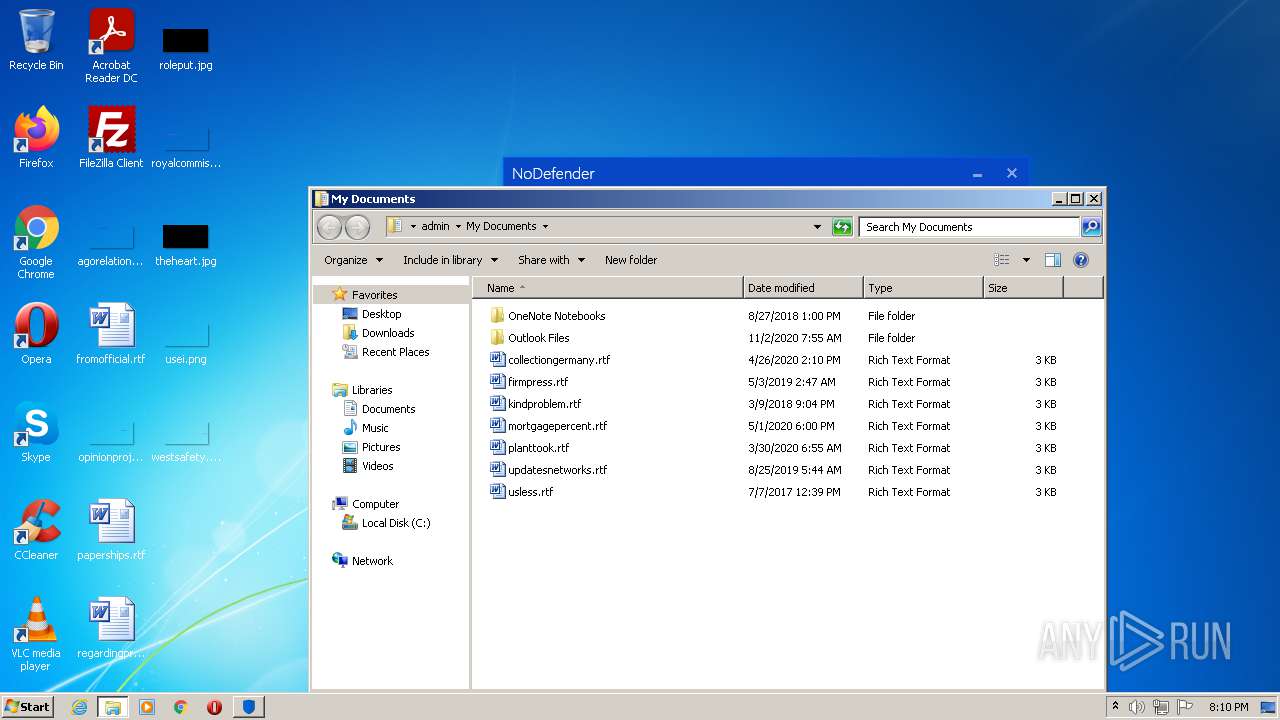
| 3220 | "C:\Users\admin\AppData\Local\Temp\NoDefender.exe" | C:\Users\admin\AppData\Local\Temp\NoDefender.exe | Explorer.EXE | ||||||||||||
User: admin Company: WinAero Integrity Level: HIGH Description: NoDefender Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3392 | "C:\Windows\explorer.exe" C:\Users\admin\AppData\Local\Packages\windows.immersivecontrolpanel_cw5n1h2txyewy\LocalState\Indexed\Settings\en-US\AAA_SettingsPageWindowsDefender.settingcontent-ms | C:\Windows\explorer.exe | — | NoDefender.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
5 079
Read events
4 915
Write events
164
Delete events
0
Modification events
| (PID) Process: | (3220) NoDefender.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: NoDefender.exe | |||
| (PID) Process: | (3220) NoDefender.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3220) NoDefender.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3220) NoDefender.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3220) NoDefender.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3964) WISPTIS.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: WISPTIS.EXE | |||
| (PID) Process: | (3964) WISPTIS.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Wisp\Touch |
| Operation: | write | Name: | TouchGate |
Value: 1 | |||
| (PID) Process: | (3964) WISPTIS.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Wisp\MultiTouch |
| Operation: | write | Name: | MultiTouchEnabled |
Value: 1 | |||
| (PID) Process: | (3964) WISPTIS.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Wisp\Pen\SysEventParameters |
| Operation: | write | Name: | FlickMode |
Value: 1 | |||
| (PID) Process: | (3964) WISPTIS.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Wisp\Pen\SysEventParameters |
| Operation: | write | Name: | TouchFlickTolerance |
Value: 50 | |||
Executable files
3
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1400 | PsExec.exe | \Device\Mup:\USER-PC\pipe\PSEXESVC | — | |
MD5:— | SHA256:— | |||
| 2612 | PsExec.exe | \Device\Mup:\USER-PC\pipe\PSEXESVC | — | |
MD5:— | SHA256:— | |||
| 3220 | NoDefender.exe | C:\Users\admin\AppData\Local\Temp\DisableApp.reg | text | |
MD5:5D116FF41DC7F7A7B5CEC9128D706B55 | SHA256:50E09E0814ED8716AA0AAED5BCCB0FF0E1A3AB6FBCAC152F22C007215A5A9BA4 | |||
| 3220 | NoDefender.exe | C:\Users\admin\AppData\Local\Temp\PsExec.exe | executable | |
MD5:A7F7A0F74C8B48F1699858B3B6C11EDA | SHA256:3B08535B4ADD194F5661E1131C8E81AF373CA322CF669674CF1272095E5CAB95 | |||
| 1400 | PsExec.exe | C:\Windows\PSEXESVC.exe | executable | |
MD5:87DFAC39F577E5F52F0724455E8832A8 | SHA256:6A6A9AA6ED43EB3F857392459C7B05A5A0DF89E00A3214D333949A561BCFF368 | |||
| 2612 | PsExec.exe | C:\Windows\PSEXESVC.exe | executable | |
MD5:87DFAC39F577E5F52F0724455E8832A8 | SHA256:6A6A9AA6ED43EB3F857392459C7B05A5A0DF89E00A3214D333949A561BCFF368 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report