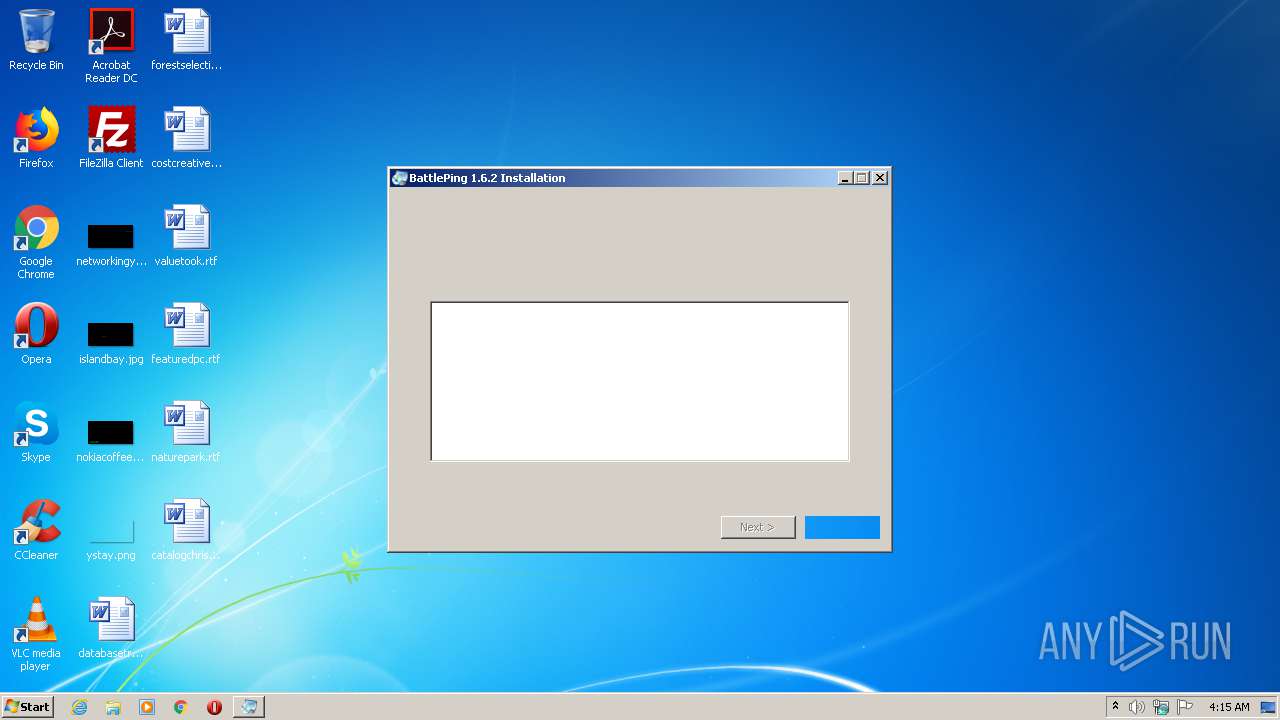
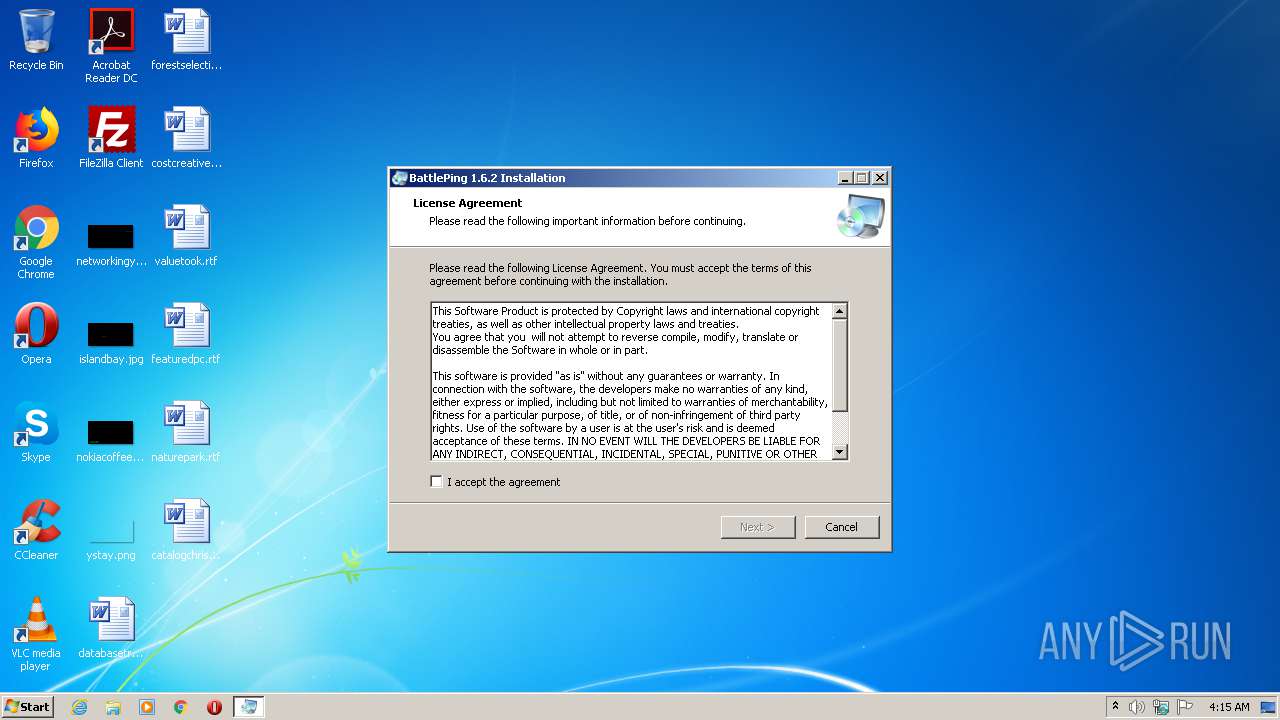
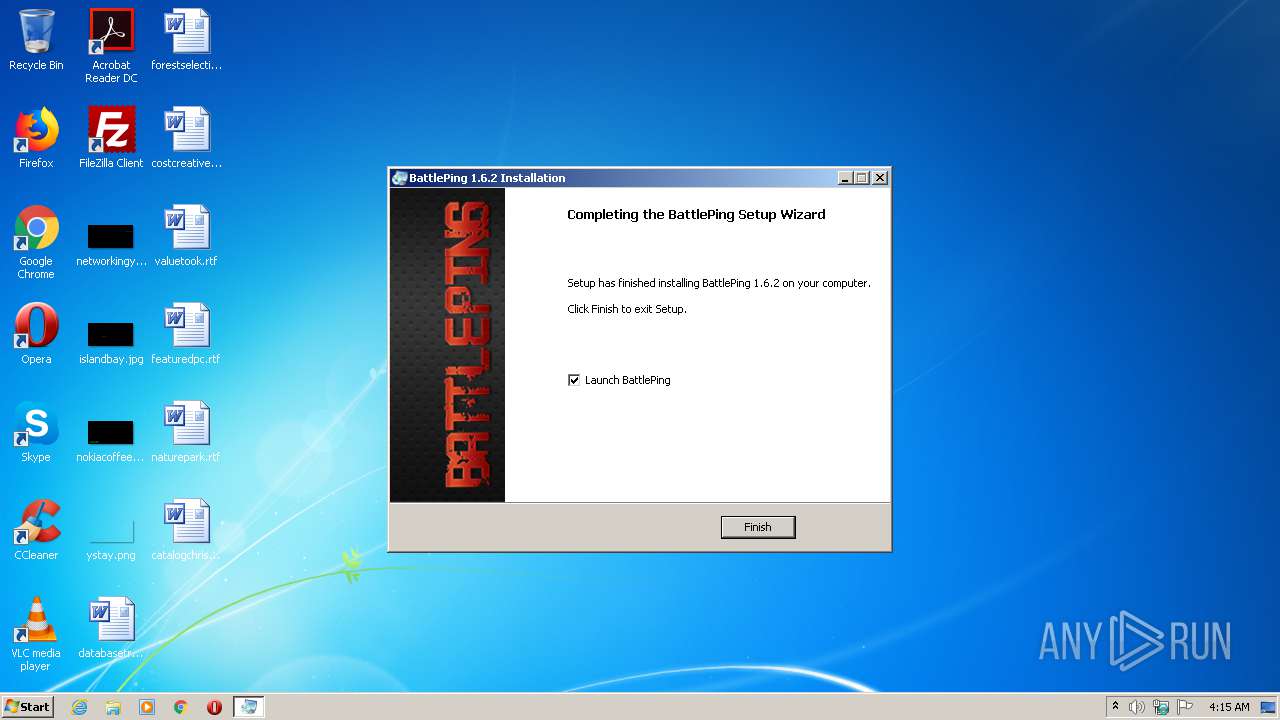
| download: | BattlePing1.6.2.exe |
| Full analysis: | https://app.any.run/tasks/911ffbe1-cdbb-41fa-8c42-791d76a31cd0 |
| Verdict: | Malicious activity |
| Analysis date: | March 29, 2021, 03:15:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, InstallShield self-extracting archive |
| MD5: | 3BE4FDA92080D7623060E0B1B32DD635 |
| SHA1: | 2DDFEE449F1A38DB94DE590235695867303C1B7C |
| SHA256: | D32C933DE6213D2D637B483462A07563F5084E26DE8A70721F370A3E047E0700 |
| SSDEEP: | 98304:MB/anNs80yKU5i5D2ACpvWzU218/tKqnaUFGzgEhRKiWQaOOV1tV1iM7CyFv/xV:Md80yKUUKv8K/tPaUFfEh0iWWOV1tV1p |
MALICIOUS
Drops executable file immediately after starts
- BattlePing1.6.2.exe (PID: 2644)
Application was dropped or rewritten from another process
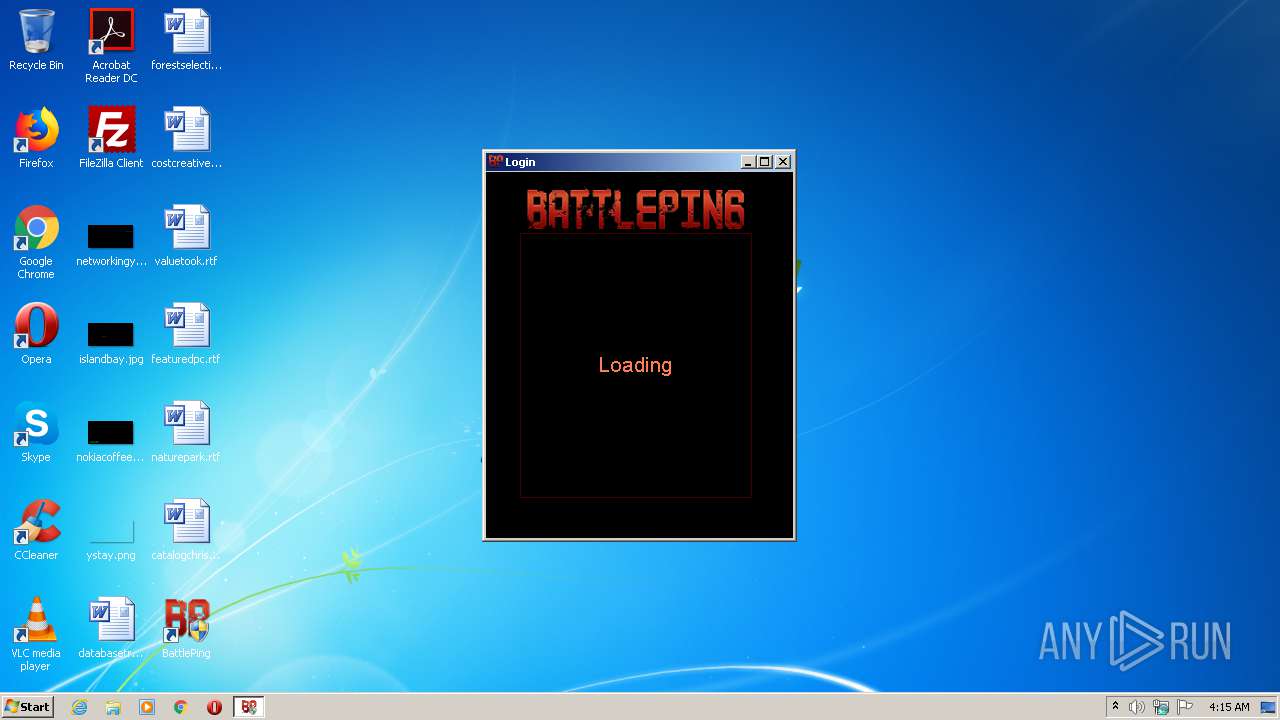
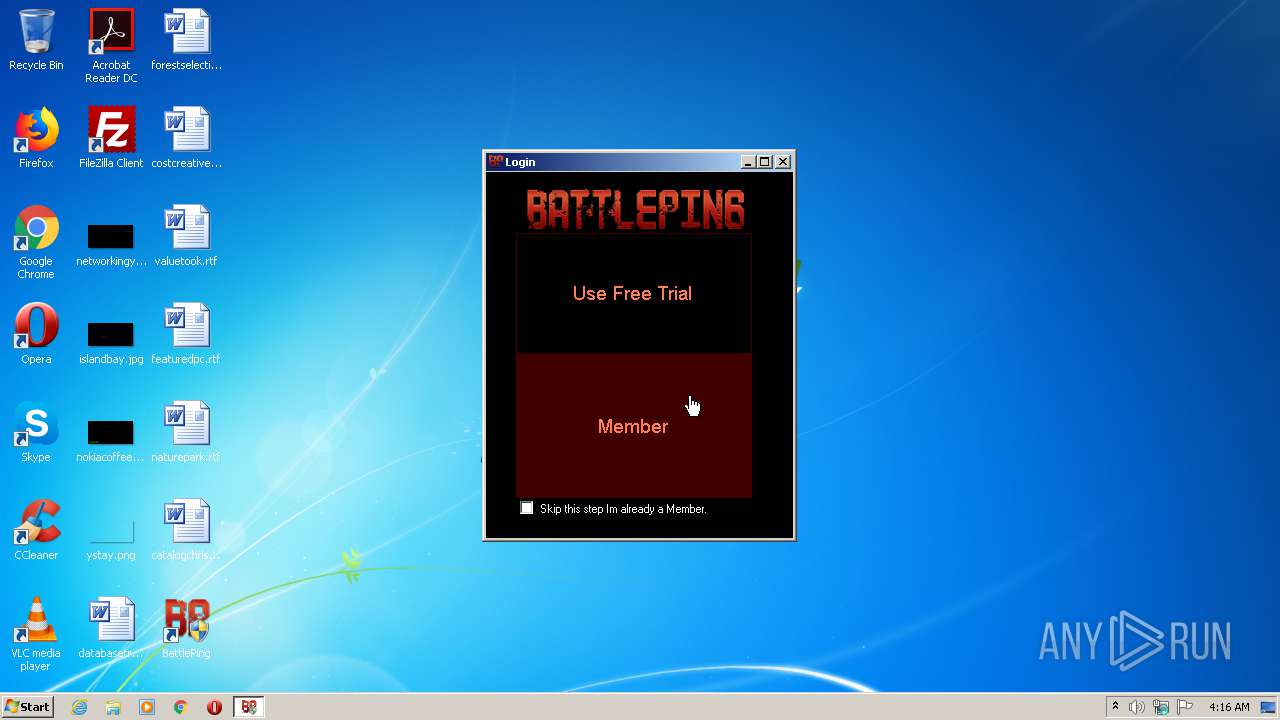
- BattlePing.exe (PID: 4016)
- wyUpdate.exe (PID: 2984)
- ss5capengine_battleping.exe (PID: 2532)
- ss5capcmd.exe (PID: 1964)
- ss5capcmd.exe (PID: 3316)
- ss5capcmd.exe (PID: 2820)
- ss5capcmd.exe (PID: 668)
Loads dropped or rewritten executable
- BattlePing.exe (PID: 4016)
- ss5capengine_battleping.exe (PID: 2532)
Changes settings of System certificates
- BattlePing.exe (PID: 4016)
SUSPICIOUS
Executable content was dropped or overwritten
- BattlePing1.6.2.exe (PID: 2644)
- ss5capengine_battleping.exe (PID: 2532)
Drops a file with a compile date too recent
- BattlePing1.6.2.exe (PID: 2644)
Drops a file that was compiled in debug mode
- BattlePing1.6.2.exe (PID: 2644)
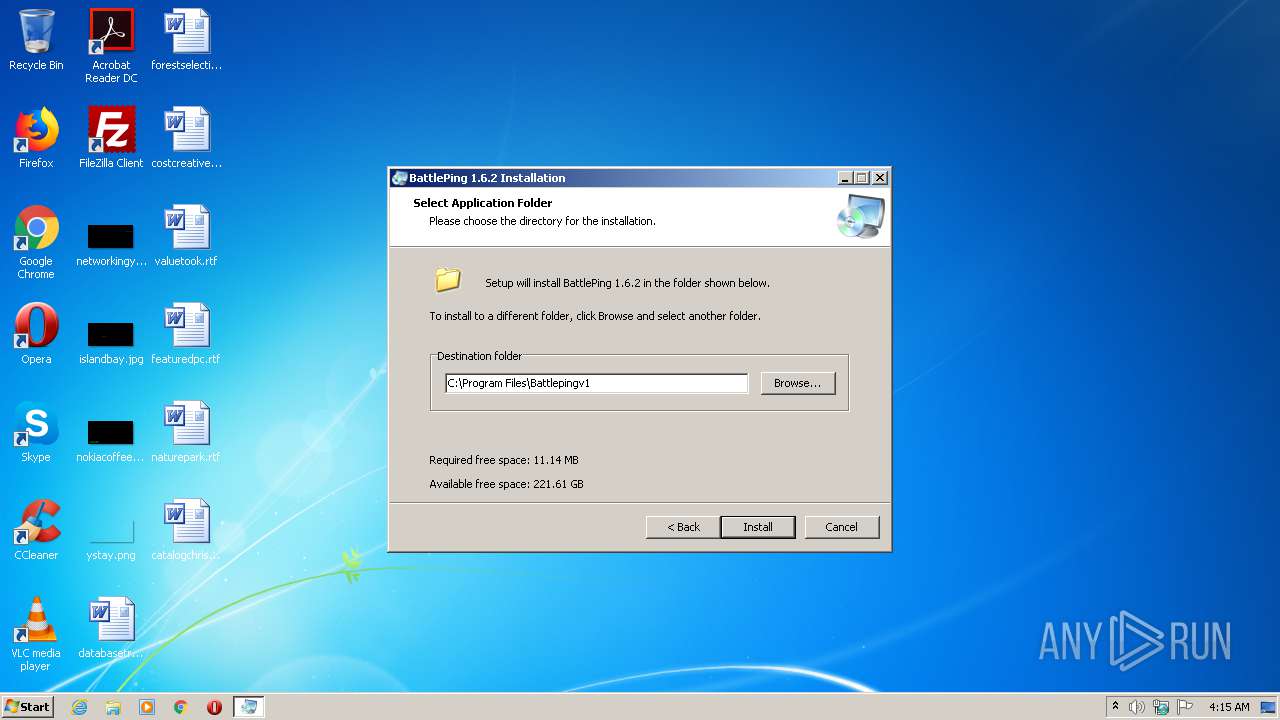
Creates a directory in Program Files
- BattlePing1.6.2.exe (PID: 2644)
Creates files in the program directory
- BattlePing1.6.2.exe (PID: 2644)
- BattlePing.exe (PID: 4016)
- ss5capengine_battleping.exe (PID: 2532)
Drops a file with too old compile date
- BattlePing1.6.2.exe (PID: 2644)
Adds / modifies Windows certificates
- BattlePing.exe (PID: 4016)
Creates a software uninstall entry
- BattlePing1.6.2.exe (PID: 2644)
Creates files in the user directory
- BattlePing.exe (PID: 4016)
- ss5capengine_battleping.exe (PID: 2532)
Reads internet explorer settings
- BattlePing.exe (PID: 4016)
Creates or modifies windows services
- ss5capengine_battleping.exe (PID: 2532)
INFO
Reads settings of System Certificates
- BattlePing.exe (PID: 4016)
Reads the hosts file
- ss5capengine_battleping.exe (PID: 2532)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (37.4) |
|---|---|---|
| .scr | | | Windows screen saver (34.5) |
| .exe | | | Win32 Executable (generic) (11.9) |
| .exe | | | Win16/32 Executable Delphi generic (5.4) |
| .exe | | | Generic Win/DOS Executable (5.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 560128 |
| InitializedDataSize: | 140800 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x89b7c |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.6.2.0 |
| ProductVersionNumber: | 1.6.2.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | |
| FileDescription: | Setup |
| FileVersion: | 1.0.0.0 |
| InternalName: | - |
| LegalCopyright: | |
| LegalTrademarks: | - |
| OriginalFileName: | - |
| ProductName: | |
| ProductVersion: | 1.0.0.0 |
| Comments: | This installation was built with Actual Installer: http://www.actualinstaller.com |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| CompanyName: | - |
| FileDescription: | Setup |
| FileVersion: | 1.0.0.0 |
| InternalName: | - |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFilename: | - |
| ProductName: | - |
| ProductVersion: | 1.0.0.0 |
| Comments: | This installation was built with Actual Installer: http://www.actualinstaller.com |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00088BE4 | 0x00088C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.5101 |
DATA | 0x0008A000 | 0x00001E24 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.12616 |
BSS | 0x0008C000 | 0x00000D25 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0008D000 | 0x00002AC8 | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.97152 |
.tls | 0x00090000 | 0x00000010 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00091000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.164765 |
.reloc | 0x00092000 | 0x0000A3FC | 0x0000A400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.70283 |
.rsrc | 0x0009D000 | 0x00013230 | 0x00013400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 5.33627 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.34983 | 1186 | Latin 1 / Western European | Russian - Russia | RT_MANIFEST |
2 | 6.27095 | 2216 | Latin 1 / Western European | Russian - Russia | RT_ICON |
3 | 4.91152 | 1384 | Latin 1 / Western European | Russian - Russia | RT_ICON |
4 | 5.63207 | 9640 | Latin 1 / Western European | Russian - Russia | RT_ICON |
5 | 5.8896 | 4264 | Latin 1 / Western European | Russian - Russia | RT_ICON |
6 | 6.03907 | 1128 | Latin 1 / Western European | Russian - Russia | RT_ICON |
7 | 2.91604 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
4077 | 2.78503 | 180 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4078 | 3.16895 | 1024 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4079 | 3.26295 | 912 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
comdlg32.dll |
gdi32.dll |
kernel32.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
version.dll |
Total processes
55
Monitored processes
9
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 668 | "C:\Program Files\Battlepingv1\bp\ss5capcmd.exe" 1 6 1 | C:\Program Files\Battlepingv1\bp\ss5capcmd.exe | — | BattlePing.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 1964 | "C:\Program Files\Battlepingv1\bp\ss5capcmd.exe" 2 3 0 MjA3LjE0OC44MS44MQ== 443 0 bm8= Li5ALi4uJC5jLi4uLnUuVG4uQC5FLi4uSS4uQS4uOC4uLjYyLm0uLg== LldTLi4yLmR0Li4ubS4ubC4qLi5MLjIuTS4uLi14LlQuZC4uKzsu | C:\Program Files\Battlepingv1\bp\ss5capcmd.exe | — | BattlePing.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2532 | "C:\Program Files\Battlepingv1\bp\ss5capengine_battleping.exe" start 53237 NO_AUTOACTIVE magicnum:4085369 | C:\Program Files\Battlepingv1\bp\ss5capengine_battleping.exe | BattlePing.exe | ||||||||||||
User: admin Company: www.networktunnel.net Integrity Level: HIGH Description: ss5cap engine Exit code: 0 Version: 2.0.0.0 Modules
| |||||||||||||||
| 2644 | "C:\Users\admin\AppData\Local\Temp\BattlePing1.6.2.exe" | C:\Users\admin\AppData\Local\Temp\BattlePing1.6.2.exe | explorer.exe | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Setup Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2820 | "C:\Program Files\Battlepingv1\bp\ss5capcmd.exe" 6 4 | C:\Program Files\Battlepingv1\bp\ss5capcmd.exe | — | BattlePing.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2984 | "C:\Program Files\Battlepingv1\wyUpdate.exe" /autoupdate | C:\Program Files\Battlepingv1\wyUpdate.exe | BattlePing.exe | ||||||||||||
User: admin Company: wyDay Integrity Level: HIGH Description: wyUpdate Exit code: 3 Version: 2.6.18.4 Modules
| |||||||||||||||
| 3316 | "C:\Program Files\Battlepingv1\bp\ss5capcmd.exe" 3 1 | C:\Program Files\Battlepingv1\bp\ss5capcmd.exe | — | BattlePing.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3592 | "C:\Users\admin\AppData\Local\Temp\BattlePing1.6.2.exe" | C:\Users\admin\AppData\Local\Temp\BattlePing1.6.2.exe | — | explorer.exe | |||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Setup Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 4016 | "C:\Program Files\Battlepingv1\BattlePing.exe" | C:\Program Files\Battlepingv1\BattlePing.exe | BattlePing1.6.2.exe | ||||||||||||
User: admin Company: BattlePing Integrity Level: HIGH Description: BattlePing Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
493
Read events
418
Write events
73
Delete events
2
Modification events
| (PID) Process: | (2644) BattlePing1.6.2.exe | Key: | HKEY_CURRENT_USER\Software\NetworkTunnel\ss5capengine |
| Operation: | write | Name: | license |
Value: lfrzP8pB/3NBkTy72VkpFp7SK1T0DjMGUJxClZbotM229U8x5bqX+6+VnwiuR0ok+lCuLpD+od7kCaomtFsJ9dPJXF6rnWcCL4rDYytkag== | |||
| (PID) Process: | (2644) BattlePing1.6.2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{DB480AC3-1578-B8DC-3F8F-786A2A4E3BC7} |
| Operation: | write | Name: | DisplayName |
Value: BattlePing | |||
| (PID) Process: | (2644) BattlePing1.6.2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{DB480AC3-1578-B8DC-3F8F-786A2A4E3BC7} |
| Operation: | write | Name: | DisplayVersion |
Value: 1.6.2 | |||
| (PID) Process: | (2644) BattlePing1.6.2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{DB480AC3-1578-B8DC-3F8F-786A2A4E3BC7} |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\Battlepingv1\BattlePing.exe | |||
| (PID) Process: | (2644) BattlePing1.6.2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{DB480AC3-1578-B8DC-3F8F-786A2A4E3BC7} |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\Battlepingv1 | |||
| (PID) Process: | (2644) BattlePing1.6.2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{DB480AC3-1578-B8DC-3F8F-786A2A4E3BC7} |
| Operation: | write | Name: | EstimatedSize |
Value: 11407 | |||
| (PID) Process: | (2644) BattlePing1.6.2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{DB480AC3-1578-B8DC-3F8F-786A2A4E3BC7} |
| Operation: | write | Name: | InstallDate |
Value: 20210329 | |||
| (PID) Process: | (2644) BattlePing1.6.2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{DB480AC3-1578-B8DC-3F8F-786A2A4E3BC7} |
| Operation: | write | Name: | HelpLink |
Value: | |||
| (PID) Process: | (2644) BattlePing1.6.2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{DB480AC3-1578-B8DC-3F8F-786A2A4E3BC7} |
| Operation: | write | Name: | Publisher |
Value: BattlePing | |||
| (PID) Process: | (2644) BattlePing1.6.2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{DB480AC3-1578-B8DC-3F8F-786A2A4E3BC7} |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\Battlepingv1\Uninstall.exe | |||
Executable files
26
Suspicious files
22
Text files
69
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2644 | BattlePing1.6.2.exe | C:\Users\admin\AppData\Local\Temp\AITMP072\aisetup.cab | compressed | |
MD5:— | SHA256:— | |||
| 2644 | BattlePing1.6.2.exe | C:\Users\admin\AppData\Local\Temp\AITMP072\L(Default).rtf | text | |
MD5:— | SHA256:— | |||
| 2644 | BattlePing1.6.2.exe | C:\Users\admin\AppData\Local\Temp\AITMP072\aiuninstall.ini | text | |
MD5:— | SHA256:— | |||
| 2644 | BattlePing1.6.2.exe | C:\Users\admin\AppData\Local\Temp\AITMP072\aifile.dat | compressed | |
MD5:— | SHA256:— | |||
| 2644 | BattlePing1.6.2.exe | C:\Program Files\Battlepingv1\BattlePing.exe | executable | |
MD5:— | SHA256:— | |||
| 2644 | BattlePing1.6.2.exe | C:\Program Files\Battlepingv1\bp\info.txt | text | |
MD5:— | SHA256:— | |||
| 2644 | BattlePing1.6.2.exe | C:\Users\admin\AppData\Local\Temp\AITMP072\aiwizard.bmp | image | |
MD5:— | SHA256:— | |||
| 2644 | BattlePing1.6.2.exe | C:\Users\admin\AppData\Local\Temp\AITMP072\aisetup.ini | text | |
MD5:— | SHA256:— | |||
| 2644 | BattlePing1.6.2.exe | C:\Users\admin\AppData\Local\Temp\AITMP072\AIUninstall.exe | executable | |
MD5:— | SHA256:— | |||
| 2644 | BattlePing1.6.2.exe | C:\Program Files\Battlepingv1\AutomaticUpdater.dll | executable | |
MD5:2863FE94130E9C2E83198F64D328BB9E | SHA256:80E08B87C32E5D4090FC3B08657D98F5AAAC4C60B275ADCC69B026829CCF3B1B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
6
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
— | — | GET | 200 | 151.139.128.14:80 | http://crl.comodoca.com/AAACertificateServices.crl | US | der | 506 b | whitelisted |
2984 | wyUpdate.exe | GET | 200 | 216.245.193.18:80 | http://battleping.com/bpupdate/updatebattleping/wyserver.wys | US | compressed | 564 b | unknown |
4016 | BattlePing.exe | GET | 200 | 216.245.193.18:80 | http://battleping.com/bpnewsnew.php | US | html | 2.20 Kb | unknown |
2532 | ss5capengine_battleping.exe | POST | 200 | 45.79.89.129:80 | http://www.networktunnel.net/php/activeit.php | US | text | 395 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4016 | BattlePing.exe | 104.20.63.85:443 | wyday.com | Cloudflare Inc | US | shared |
— | — | 151.139.128.14:80 | crl.comodoca.com | Highwinds Network Group, Inc. | US | suspicious |
2984 | wyUpdate.exe | 216.245.193.18:80 | battleping.com | Limestone Networks, Inc. | US | unknown |
4016 | BattlePing.exe | 216.245.193.18:80 | battleping.com | Limestone Networks, Inc. | US | unknown |
2532 | ss5capengine_battleping.exe | 45.79.89.129:80 | www.networktunnel.net | Linode, LLC | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
wyday.com |
| unknown |
crl.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
battleping.com |
| unknown |
www.networktunnel.net |
| unknown |