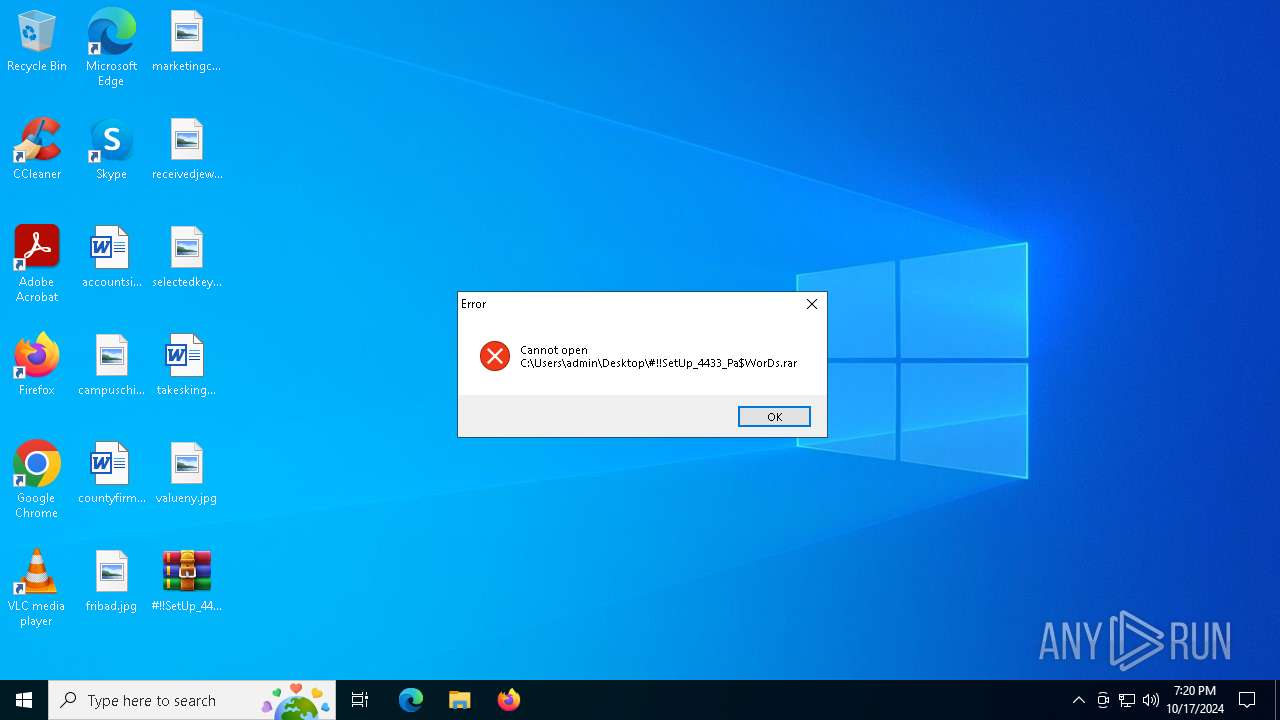
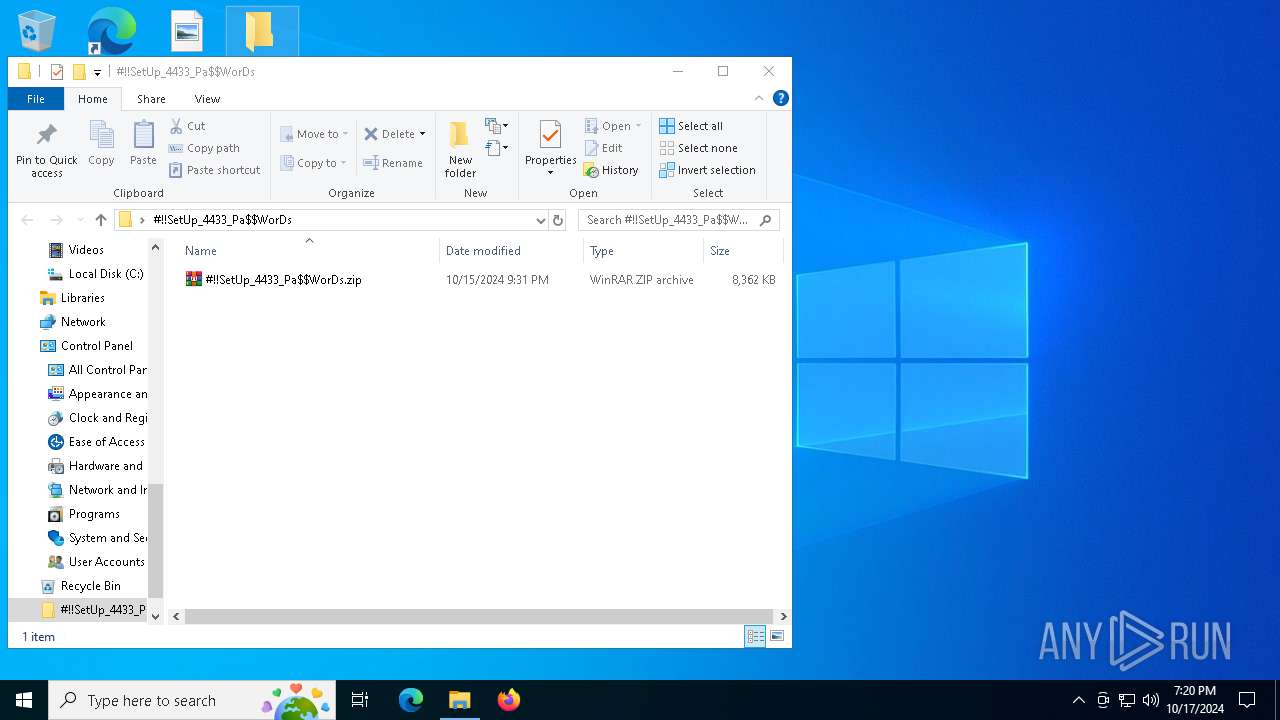
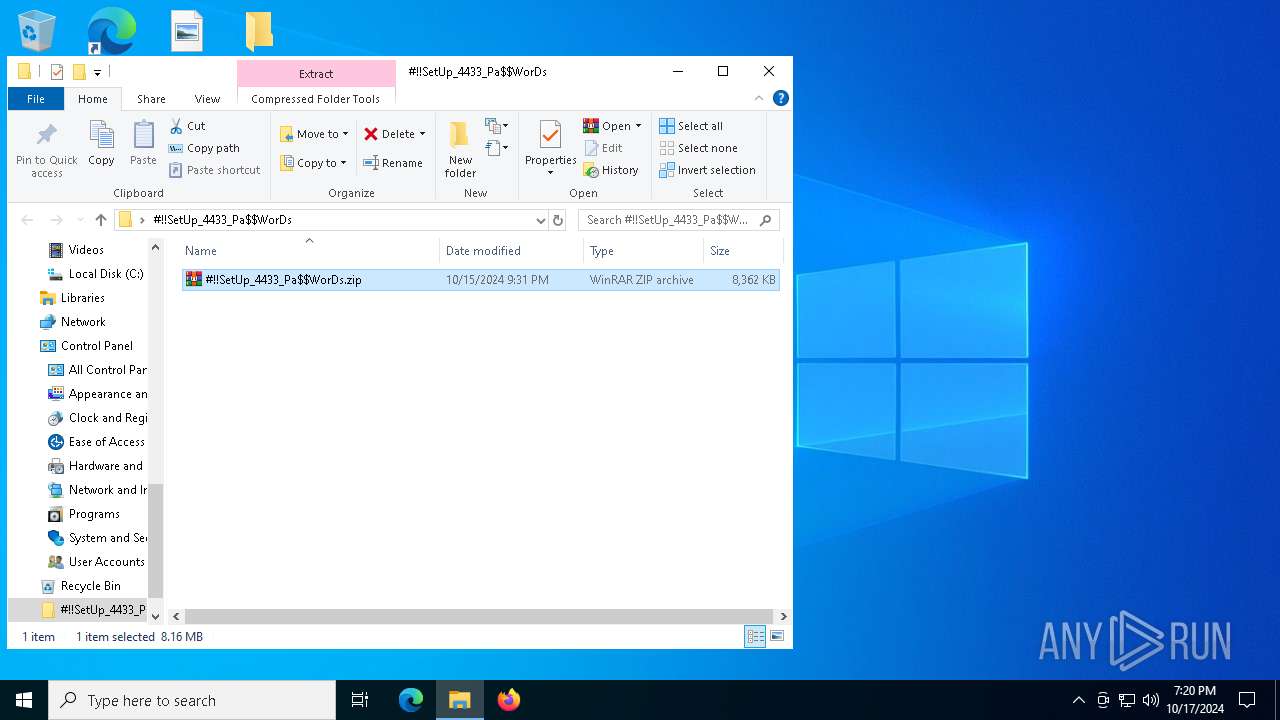
| File name: | #!!SetUp_4433_Pa$WorDs.rar |
| Full analysis: | https://app.any.run/tasks/6010a5a1-a181-46f2-af5c-05a56f535774 |
| Verdict: | Malicious activity |
| Analysis date: | October 17, 2024, 19:20:10 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 5E6BA8C420B47E3914B4B9E2D10E33CB |
| SHA1: | 2B2007A0856E4B4FF06358AFBCFFB6F53F3B36C0 |
| SHA256: | D324C362AF198161F23B25143D3C6F0776888054B4DF9681ACF17F9C56E813B0 |
| SSDEEP: | 98304:P3VFjdbCYwP8CzAj6MJbfKXQl9myoQOqIx+NUNAyID/FM0UZ4Ka96pbzYUtAHOZc:mCO8bqjNVLWIbOx |
MALICIOUS
No malicious indicators.SUSPICIOUS
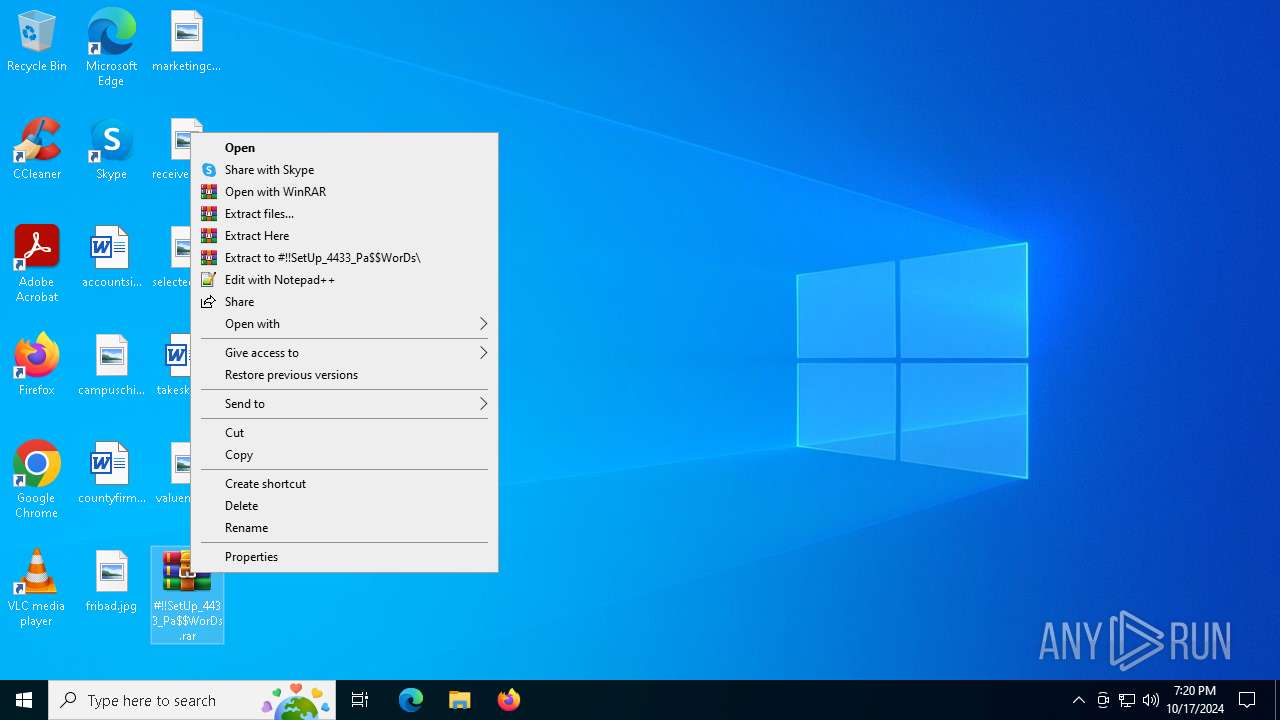
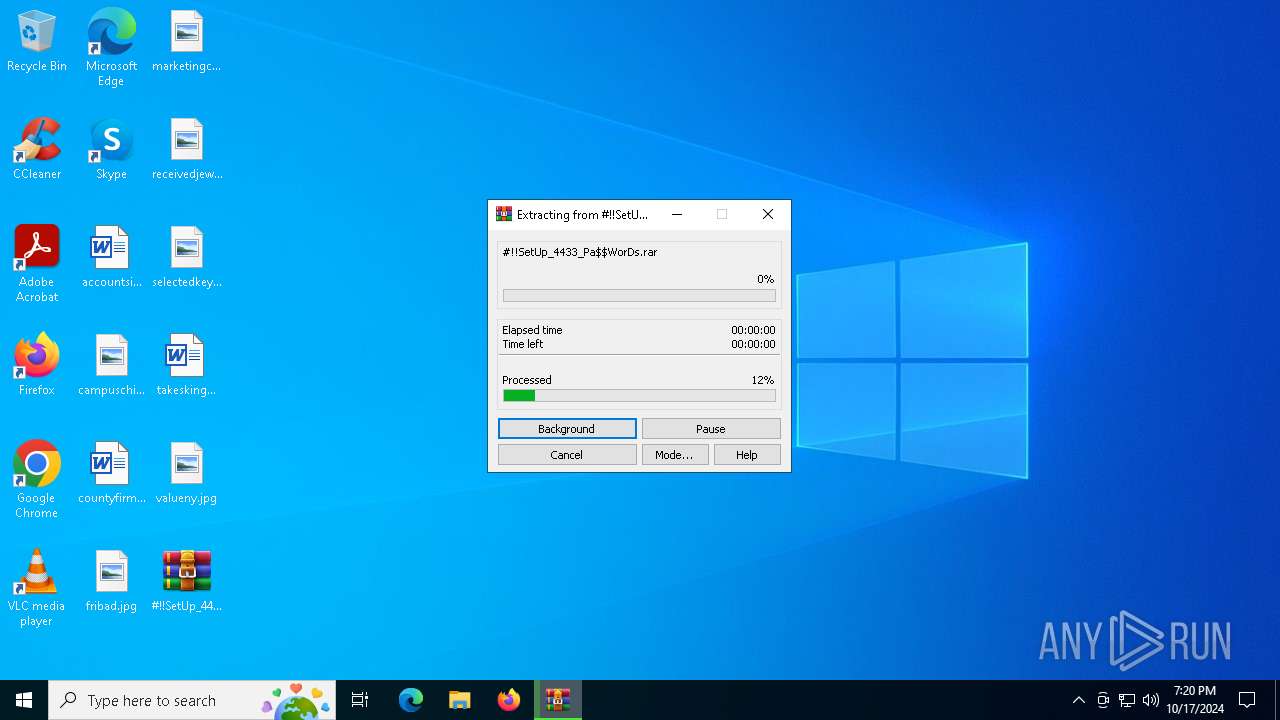
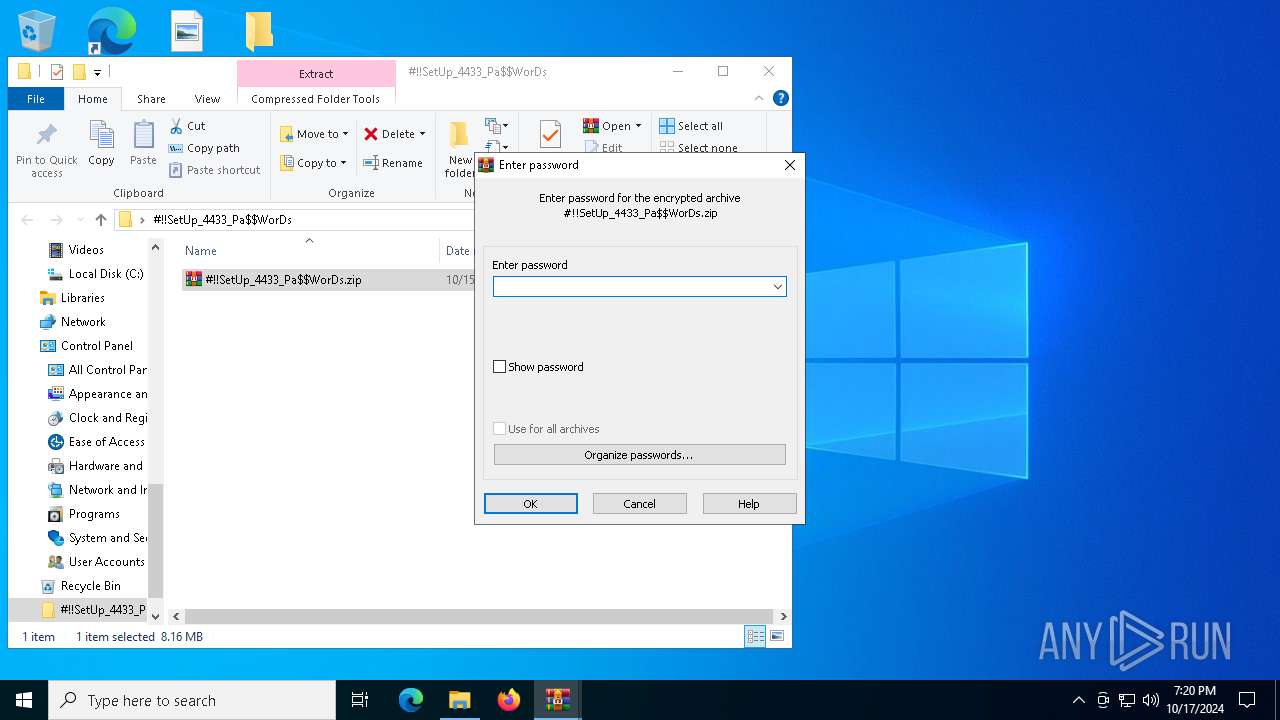
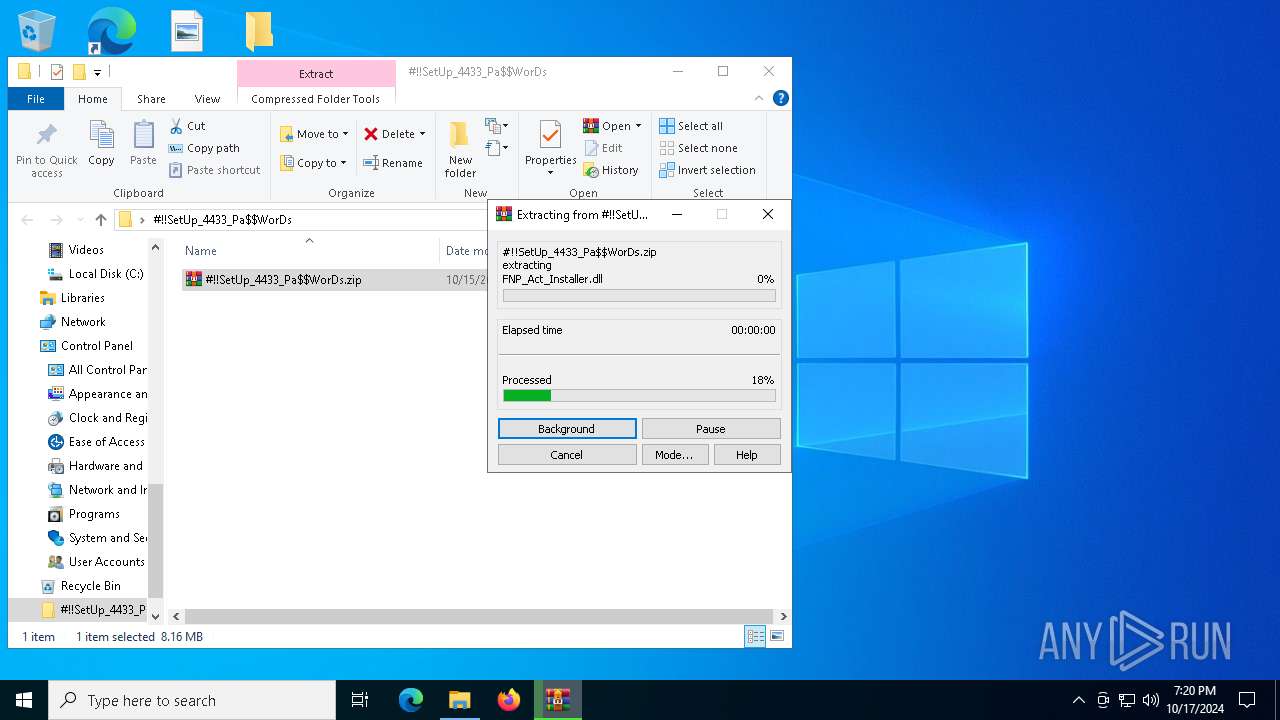
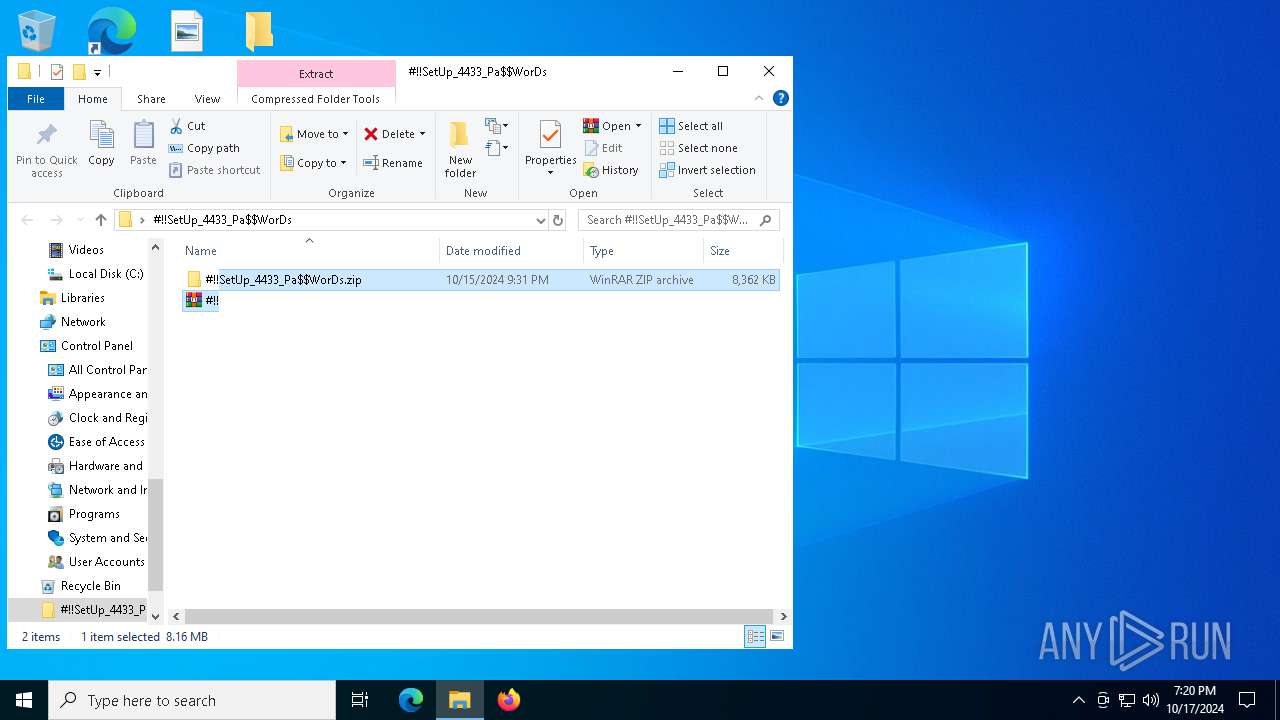
Generic archive extractor
- WinRAR.exe (PID: 1200)
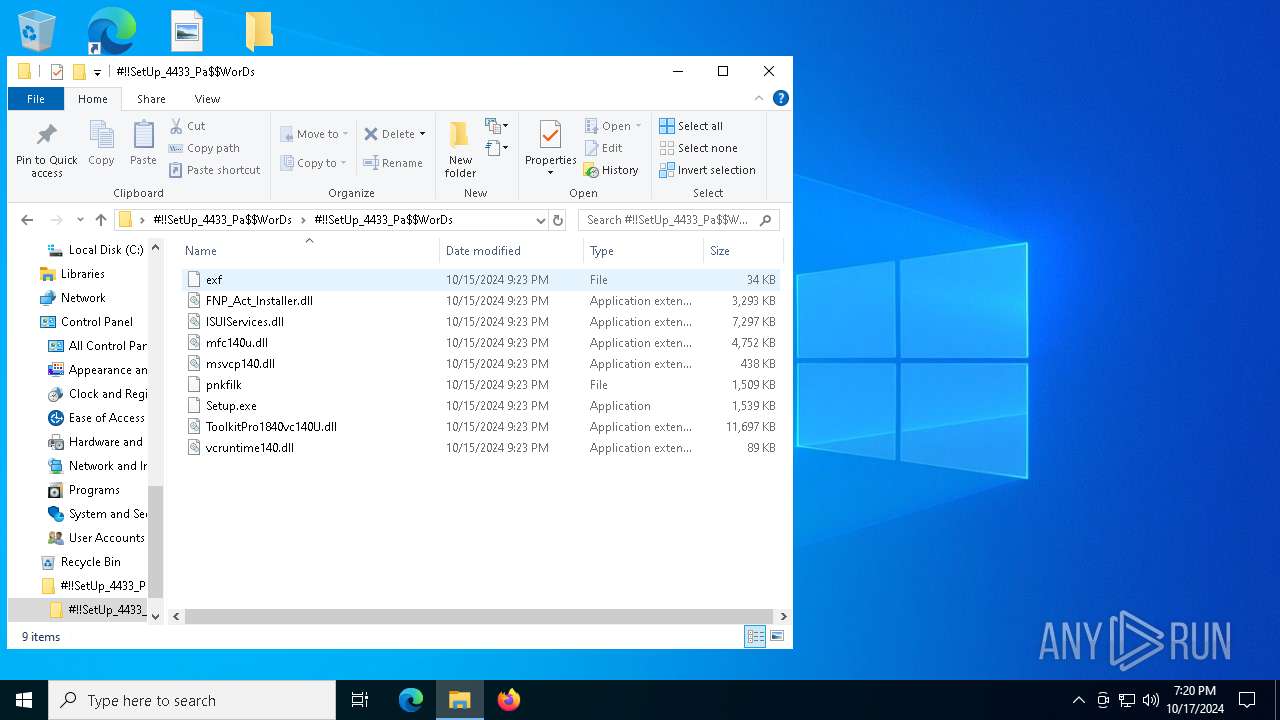
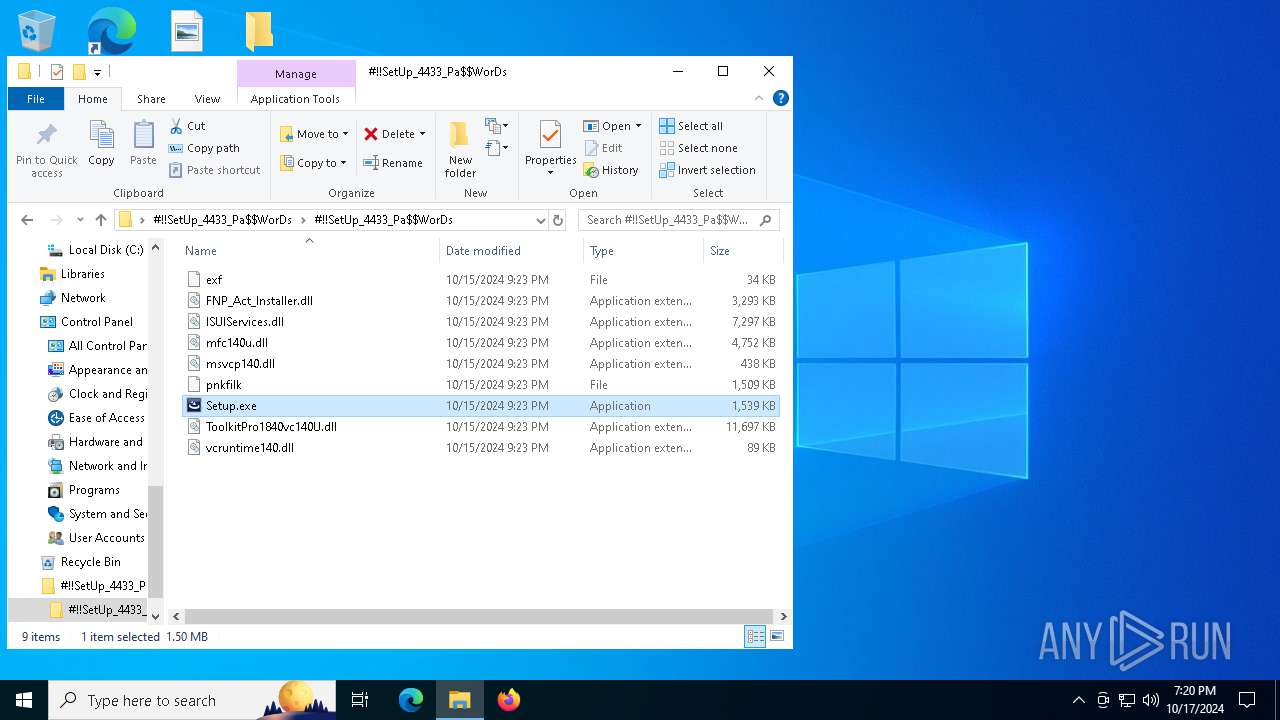
Process drops legitimate windows executable
- WinRAR.exe (PID: 1584)
- Setup.exe (PID: 2576)
Executable content was dropped or overwritten
- Setup.exe (PID: 2576)
The process drops C-runtime libraries
- Setup.exe (PID: 2576)
Starts application with an unusual extension
- Setup.exe (PID: 2576)
INFO
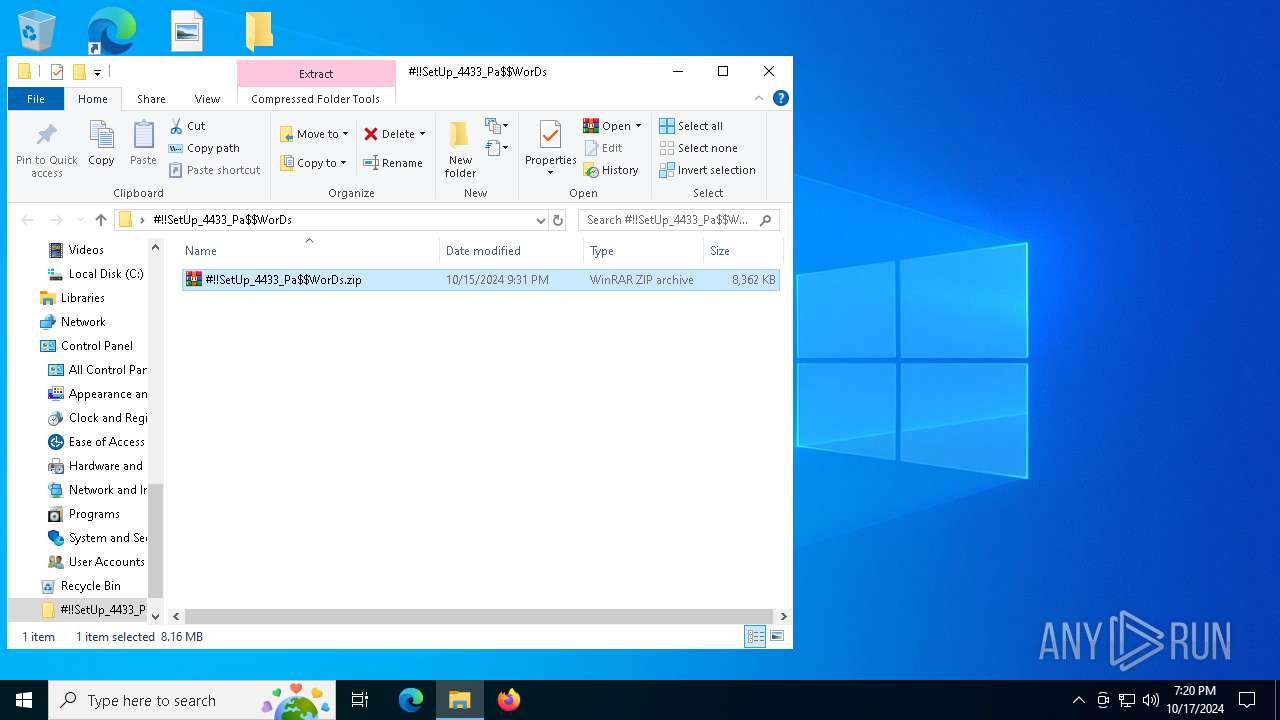
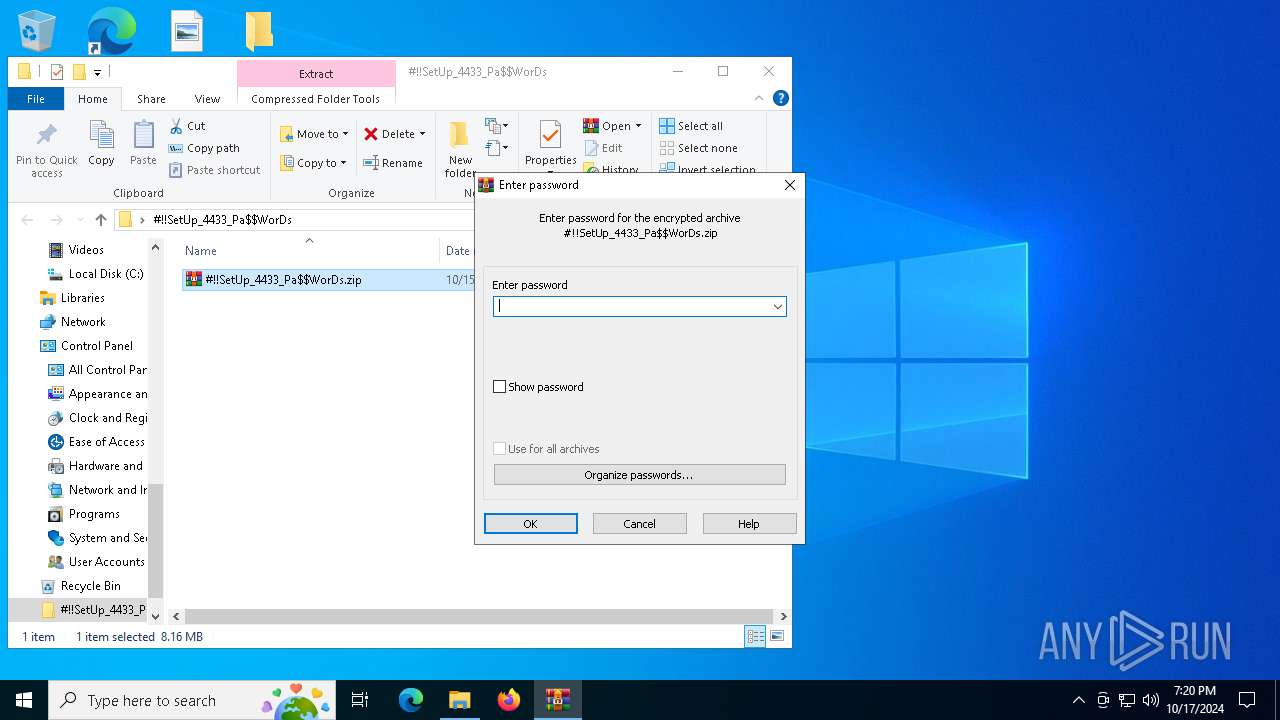
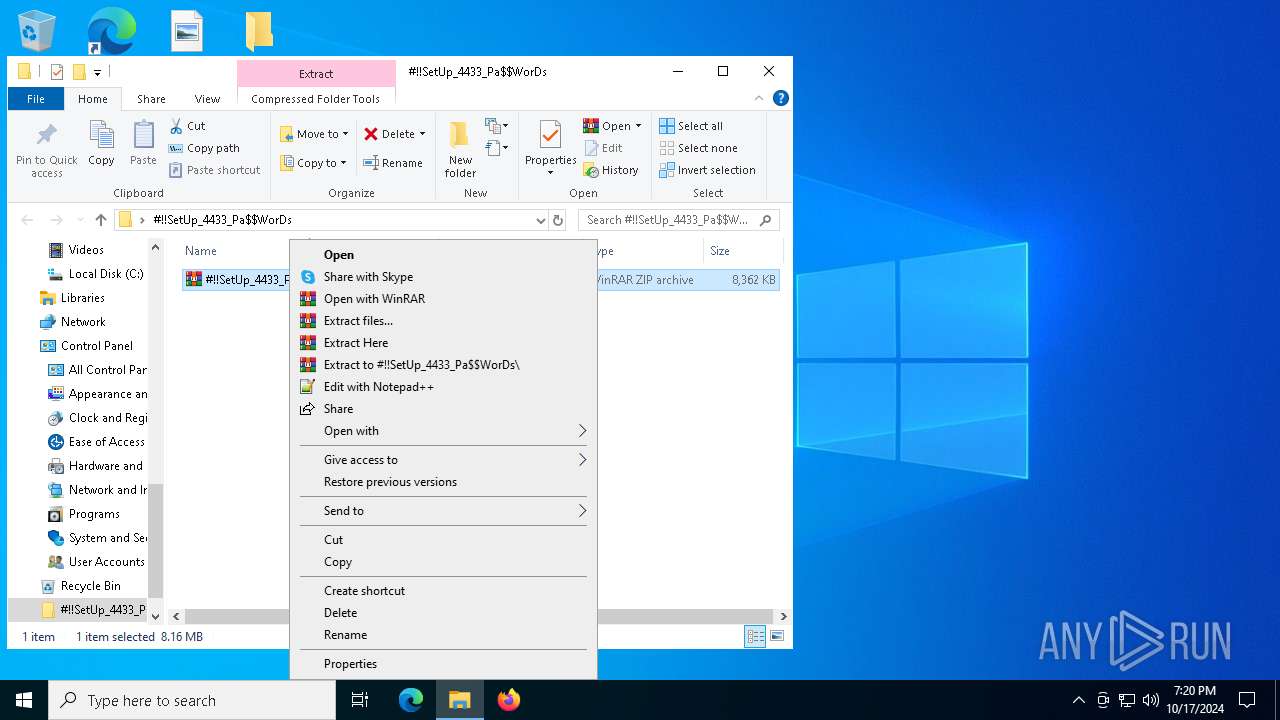
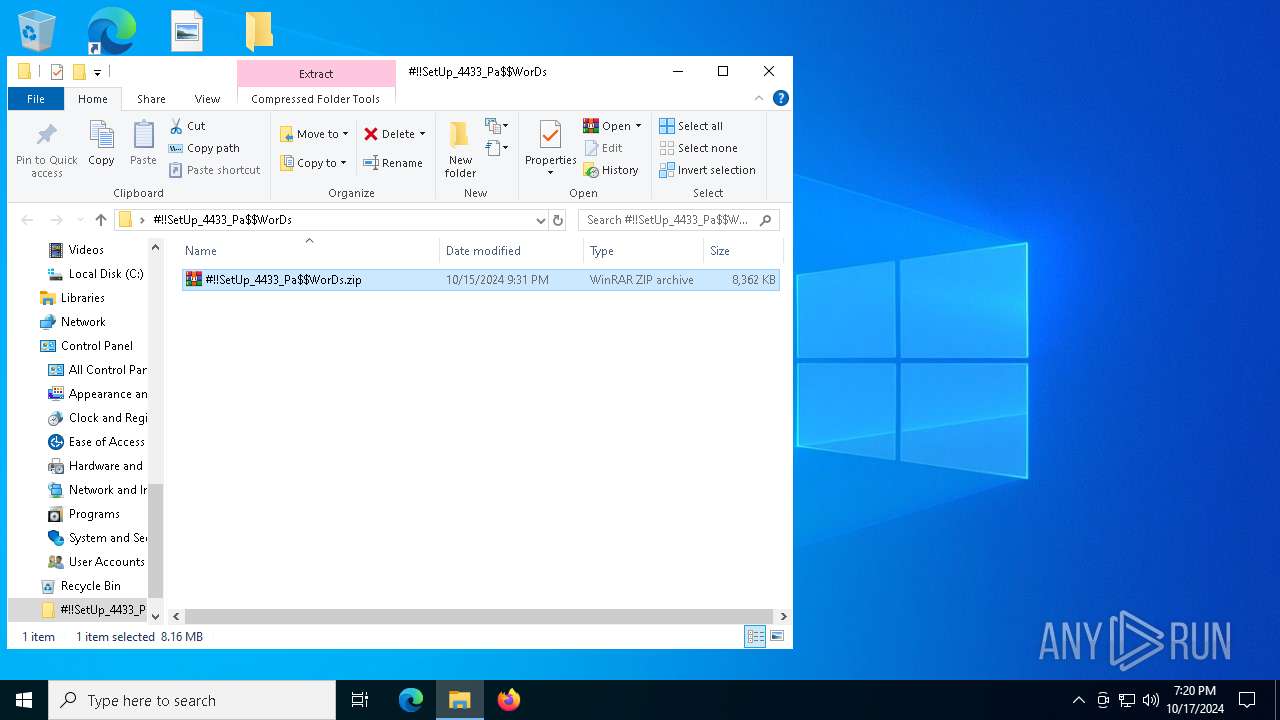
Manual execution by a user
- WinRAR.exe (PID: 1584)
- WinRAR.exe (PID: 6516)
- WinRAR.exe (PID: 6912)
- Setup.exe (PID: 2576)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1584)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
135
Monitored processes
8
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1160 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | more.com | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1200 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\#!!SetUp_4433_Pa$WorDs.rar | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 1 Version: 5.91.0 Modules
| |||||||||||||||
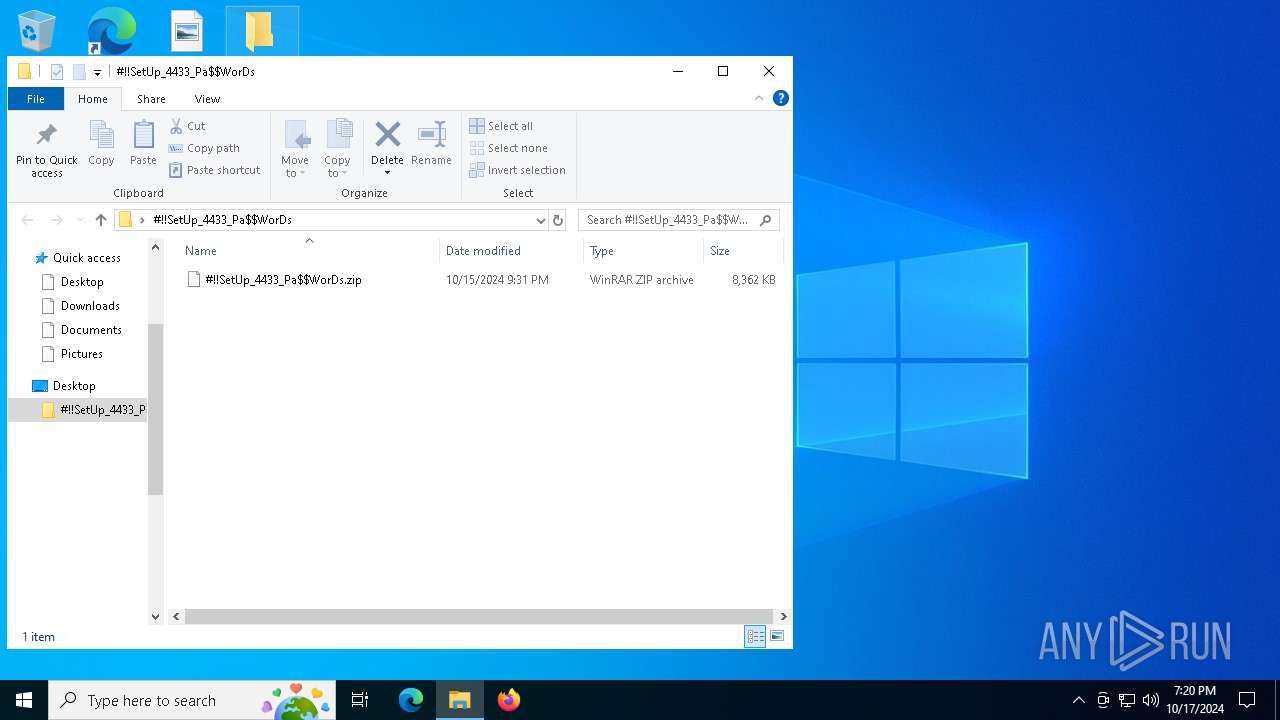
| 1584 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\#!!SetUp_4433_Pa$WorDs\#!!SetUp_4433_Pa$WorDs.zip" C:\Users\admin\Desktop\#!!SetUp_4433_Pa$WorDs\#!!SetUp_4433_Pa$WorDs\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2576 | "C:\Users\admin\Desktop\#!!SetUp_4433_Pa$WorDs\#!!SetUp_4433_Pa$WorDs\Setup.exe" | C:\Users\admin\Desktop\#!!SetUp_4433_Pa$WorDs\#!!SetUp_4433_Pa$WorDs\Setup.exe | explorer.exe | ||||||||||||
User: admin Company: Flexera Integrity Level: MEDIUM Description: InstallShield Activation Wizard Exit code: 1 Version: 27.0.58 Modules
| |||||||||||||||
| 2648 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6436 | C:\WINDOWS\SysWOW64\more.com | C:\Windows\SysWOW64\more.com | — | Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: More Utility Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6516 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\#!!SetUp_4433_Pa$WorDs.rar" C:\Users\admin\Desktop\ | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 6912 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\#!!SetUp_4433_Pa$WorDs\#!!SetUp_4433_Pa$WorDs.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 1 Version: 5.91.0 Modules
| |||||||||||||||
Total events
2 749
Read events
2 726
Write events
23
Delete events
0
Modification events
| (PID) Process: | (1200) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1200) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1200) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1200) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1200) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General\Toolbar\Layout |
| Operation: | write | Name: | Band76_0 |
Value: 4C000000730100000402000000000000F0F0F00000000000000000000000000000000000000000009002060000000000000000003B000000B402000000000000000000000000000001000000 | |||
| (PID) Process: | (1200) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General\Toolbar\Layout |
| Operation: | write | Name: | Band76_1 |
Value: 4C000000730100000500000000000000F0F0F0000000000000000000000000000000000000000000500204000000000000000000180000002A00000000000000000000000000000002000000 | |||
| (PID) Process: | (1200) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General\Toolbar\Layout |
| Operation: | write | Name: | Band76_2 |
Value: 4C000000730100000400000000000000F0F0F00000000000000000000000000000000000000000008E0205000000000000000000180000006400000000000000000000000000000003000000 | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
13
Suspicious files
5
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6516 | WinRAR.exe | C:\Users\admin\Desktop\#!!SetUp_4433_Pa$WorDs\#!!SetUp_4433_Pa$WorDs.zip | — | |
MD5:— | SHA256:— | |||
| 1584 | WinRAR.exe | C:\Users\admin\Desktop\#!!SetUp_4433_Pa$WorDs\#!!SetUp_4433_Pa$WorDs\msvcp140.dll | executable | |
MD5:DC739066C9D0CA961CBA2F320CADE28E | SHA256:74E9268A68118BB1AC5154F8F327887715960CCC37BA9DABBE31ECD82DCBAA55 | |||
| 1584 | WinRAR.exe | C:\Users\admin\Desktop\#!!SetUp_4433_Pa$WorDs\#!!SetUp_4433_Pa$WorDs\mfc140u.dll | executable | |
MD5:266C6A0ADDA7CA07753636B1F8A69F7F | SHA256:3F8176BBC33F75FBCC429800461D84BCDB92D766D968220A9CC31F4CF6987271 | |||
| 2576 | Setup.exe | C:\Users\admin\AppData\Roaming\egemo\FNP_Act_Installer.dll | executable | |
MD5:818ABBBD3717505C01E4E8277406AF8F | SHA256:BC0ACDFB672AD01AD3B658EE51E2EE6523D56EA4BC4C066B390CF9B494E2AA69 | |||
| 1584 | WinRAR.exe | C:\Users\admin\Desktop\#!!SetUp_4433_Pa$WorDs\#!!SetUp_4433_Pa$WorDs\FNP_Act_Installer.dll | executable | |
MD5:818ABBBD3717505C01E4E8277406AF8F | SHA256:BC0ACDFB672AD01AD3B658EE51E2EE6523D56EA4BC4C066B390CF9B494E2AA69 | |||
| 1584 | WinRAR.exe | C:\Users\admin\Desktop\#!!SetUp_4433_Pa$WorDs\#!!SetUp_4433_Pa$WorDs\Setup.exe | executable | |
MD5:48C9A0C76B44A5F2729C876085ADBA4E | SHA256:B5F9377BD27FCF48FB3D81D0196021681739F42A198E8340C27D55192D4BD3AC | |||
| 2576 | Setup.exe | C:\Users\admin\AppData\Roaming\egemo\ISUIServices.dll | executable | |
MD5:8FF059505A66E89BCC87DBB93E41FF0D | SHA256:37B0F6EB77B5BDC02ACE904A0C9DBABA29A0E966F96839BACCA52D207815ADBD | |||
| 2576 | Setup.exe | C:\Users\admin\AppData\Roaming\egemo\mfc140u.dll | executable | |
MD5:266C6A0ADDA7CA07753636B1F8A69F7F | SHA256:3F8176BBC33F75FBCC429800461D84BCDB92D766D968220A9CC31F4CF6987271 | |||
| 1584 | WinRAR.exe | C:\Users\admin\Desktop\#!!SetUp_4433_Pa$WorDs\#!!SetUp_4433_Pa$WorDs\pnkfilk | binary | |
MD5:17A4E124FB020EF5735924E04D0E54CA | SHA256:5718F334B420D14C45450404D4F32CD701CF3EEF2D2F29A836706FCE5A834205 | |||
| 1584 | WinRAR.exe | C:\Users\admin\Desktop\#!!SetUp_4433_Pa$WorDs\#!!SetUp_4433_Pa$WorDs\ToolkitPro1840vc140U.dll | executable | |
MD5:7391B8AC24396F7A06873C49662137DA | SHA256:F983FE7342DECB883AFDDD795A4EF8DA0406907E26900C11DF7559E99F8E6DC9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
52
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6944 | svchost.exe | GET | 200 | 2.16.164.18:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6692 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
624 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6200 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6692 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6940 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5488 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6944 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6944 | svchost.exe | 2.16.164.18:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
6944 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5488 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4360 | SearchApp.exe | 2.23.209.176:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |