| File name: | exam_testing_engine_setup.exe |
| Full analysis: | https://app.any.run/tasks/d4aa9e56-6425-4526-8678-9f39428bb2ef |
| Verdict: | Malicious activity |
| Analysis date: | May 03, 2018, 09:46:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | DBD4DD8A0A395C12E4FC7EBC5F07DC86 |
| SHA1: | 83B6E17EBAE1F5DE3FA043A3C5CEF5497D13DCCC |
| SHA256: | D323DF43145CC6062E9CB38CE302D5C882807B35D77E6C094B598451A8F7B960 |
| SSDEEP: | 393216:rEsm9xMwTxoXAPvtx1jqNVdVu0+M+YHkgeMgnDu:roPT+wBSdVu0+M+G9eMgna |
MALICIOUS
Application was dropped or rewritten from another process
- player.exe (PID: 2704)
- player.exe (PID: 3772)
Application loaded dropped or rewritten executable
- player.exe (PID: 2704)
- player.exe (PID: 3772)
SUSPICIOUS
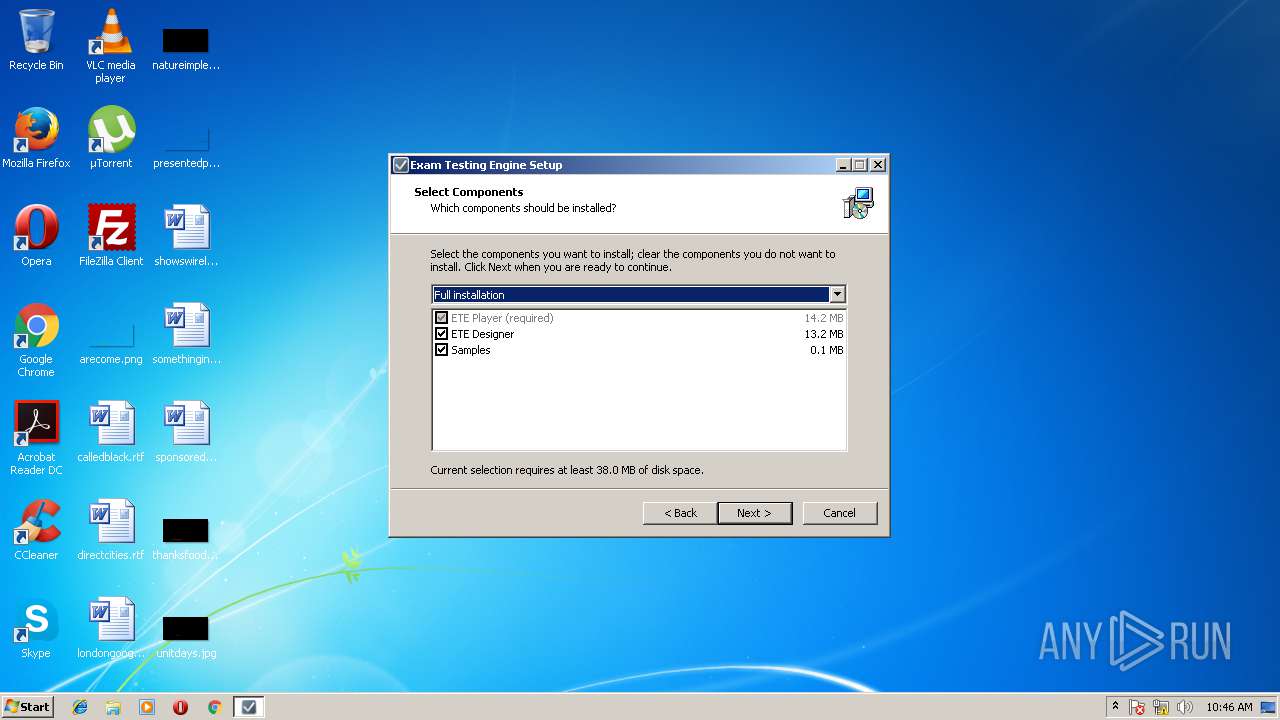
Creates files in the program directory
- player.exe (PID: 3772)
- player.exe (PID: 2704)
Modifies the open verb of a shell class
- exam_testing_engine_setup.tmp (PID: 2676)
INFO
Dropped object may contain URL's
- exam_testing_engine_setup.tmp (PID: 2676)
Application was dropped or rewritten from another process
- exam_testing_engine_setup.tmp (PID: 4092)
- exam_testing_engine_setup.tmp (PID: 2676)
Loads rich edit control libraries
- exam_testing_engine_setup.tmp (PID: 2676)
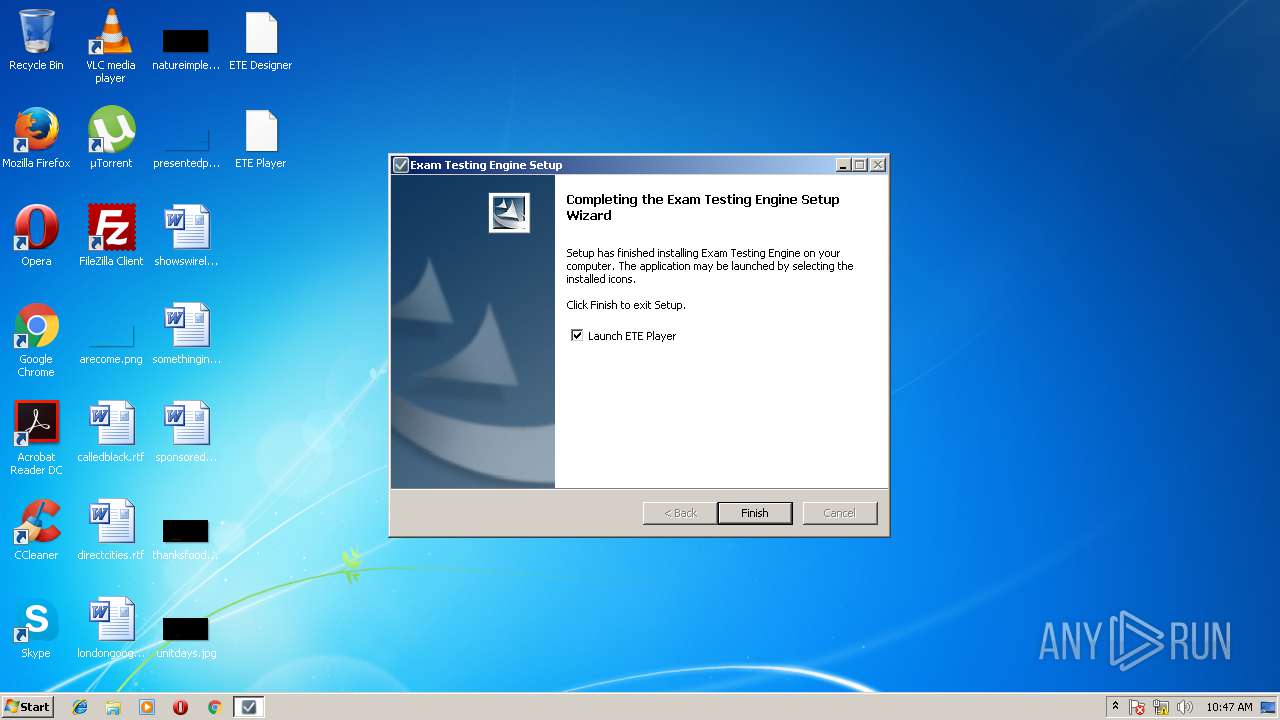
Creates a software uninstall entry
- exam_testing_engine_setup.tmp (PID: 2676)
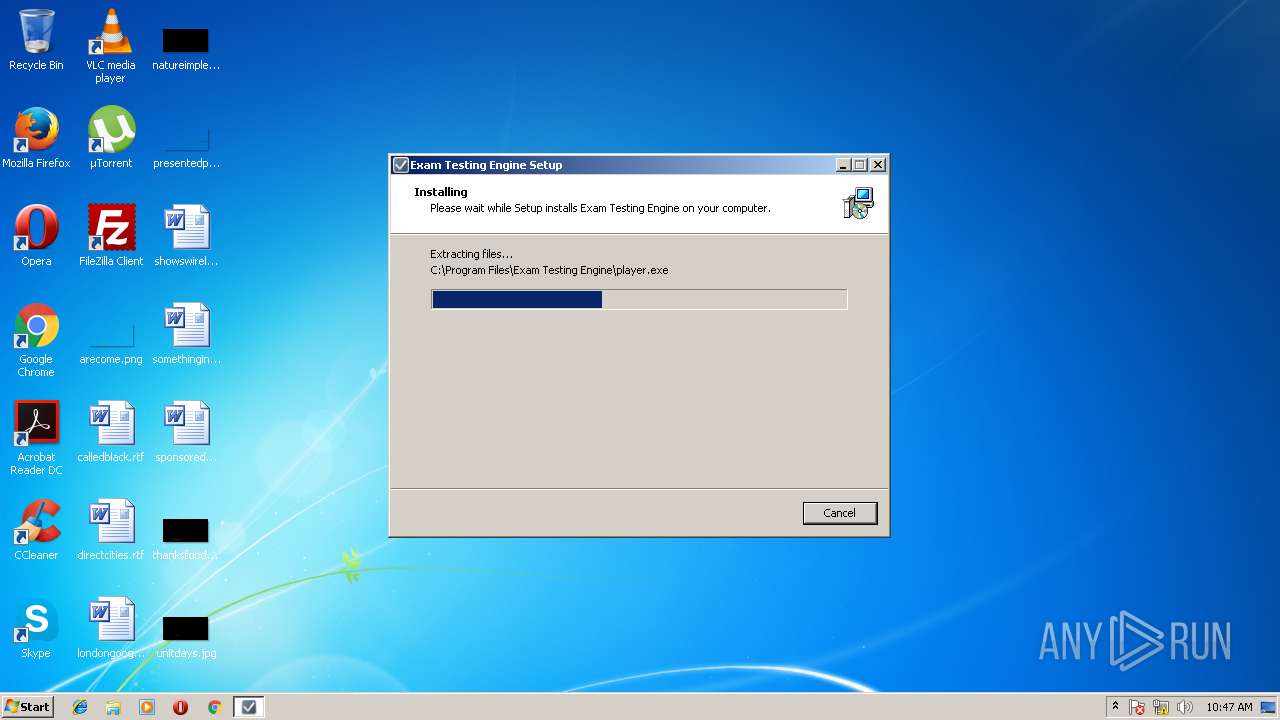
Creates files in the program directory
- exam_testing_engine_setup.tmp (PID: 2676)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (81.5) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10.5) |
| .exe | | | Win32 Executable (generic) (3.3) |
| .exe | | | Win16/32 Executable Delphi generic (1.5) |
| .exe | | | Generic Win/DOS Executable (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 41472 |
| InitializedDataSize: | 380928 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xaa98 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
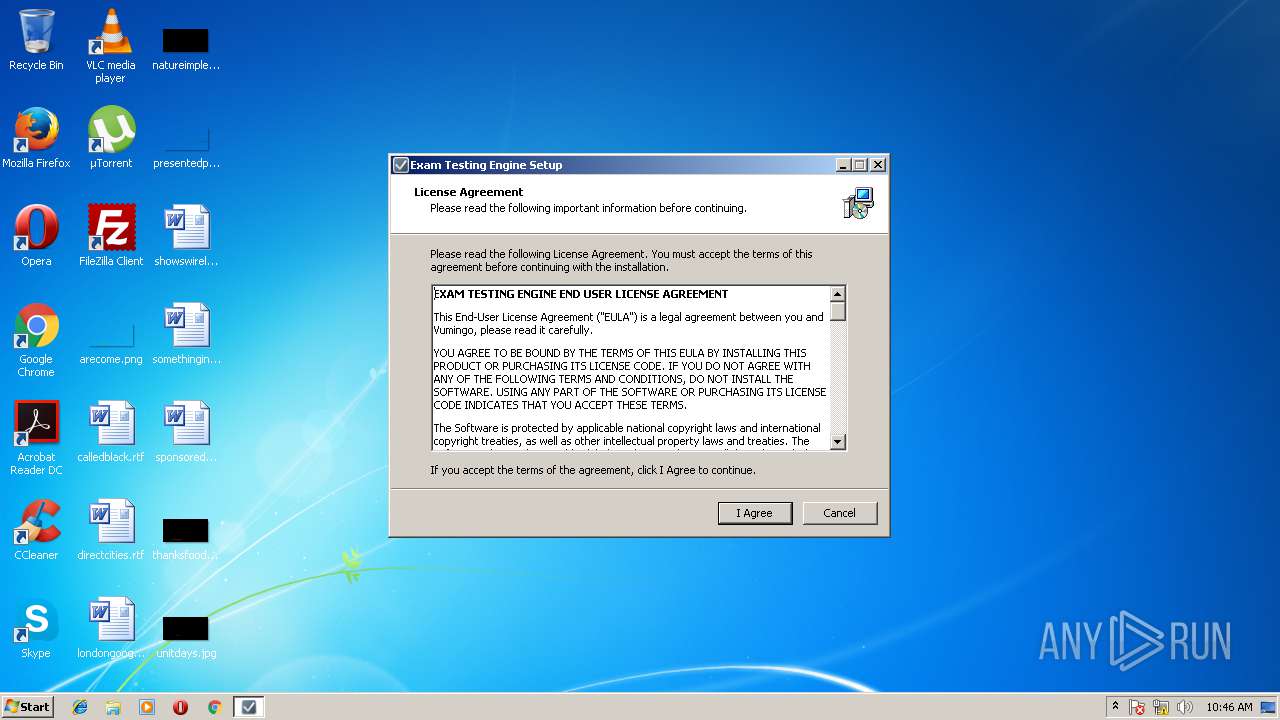
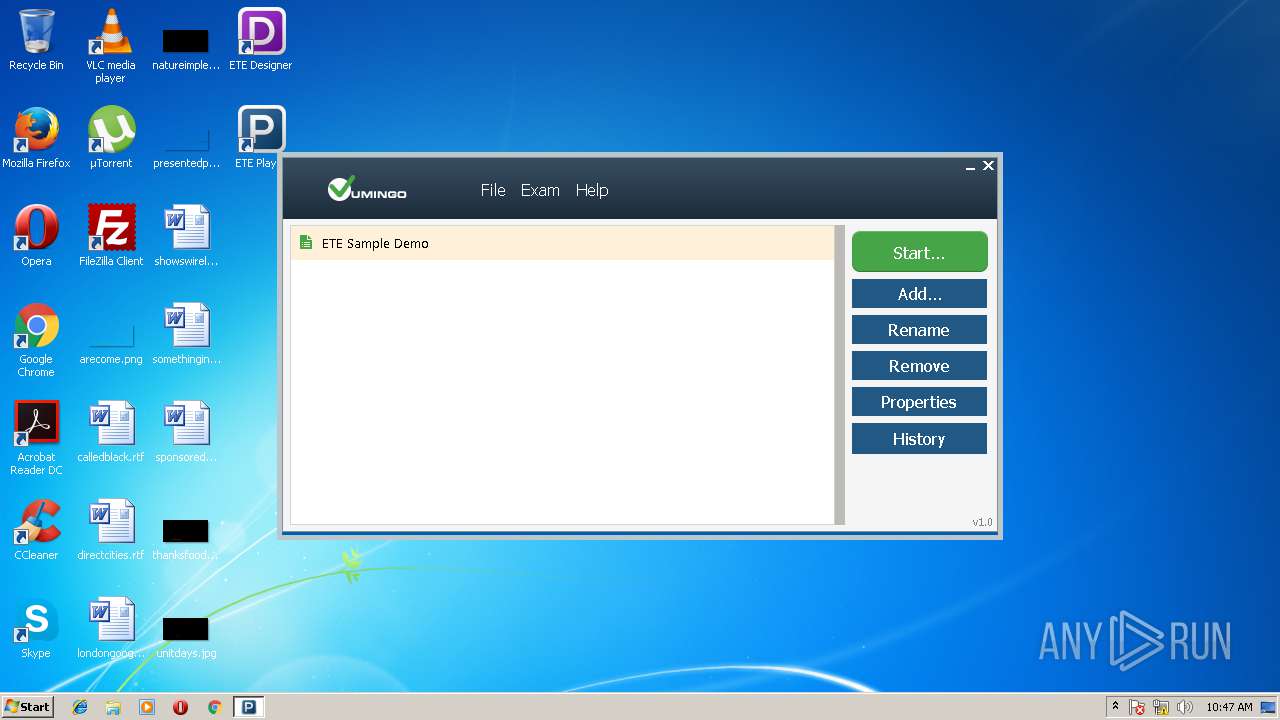
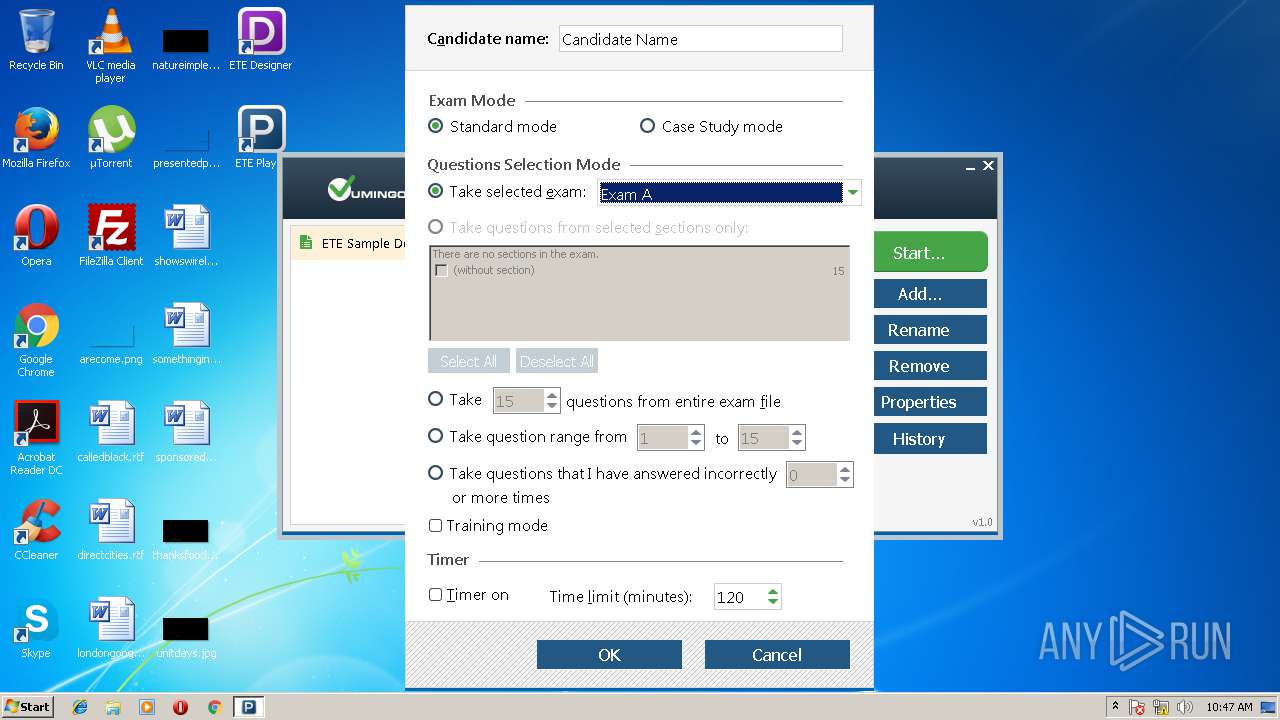
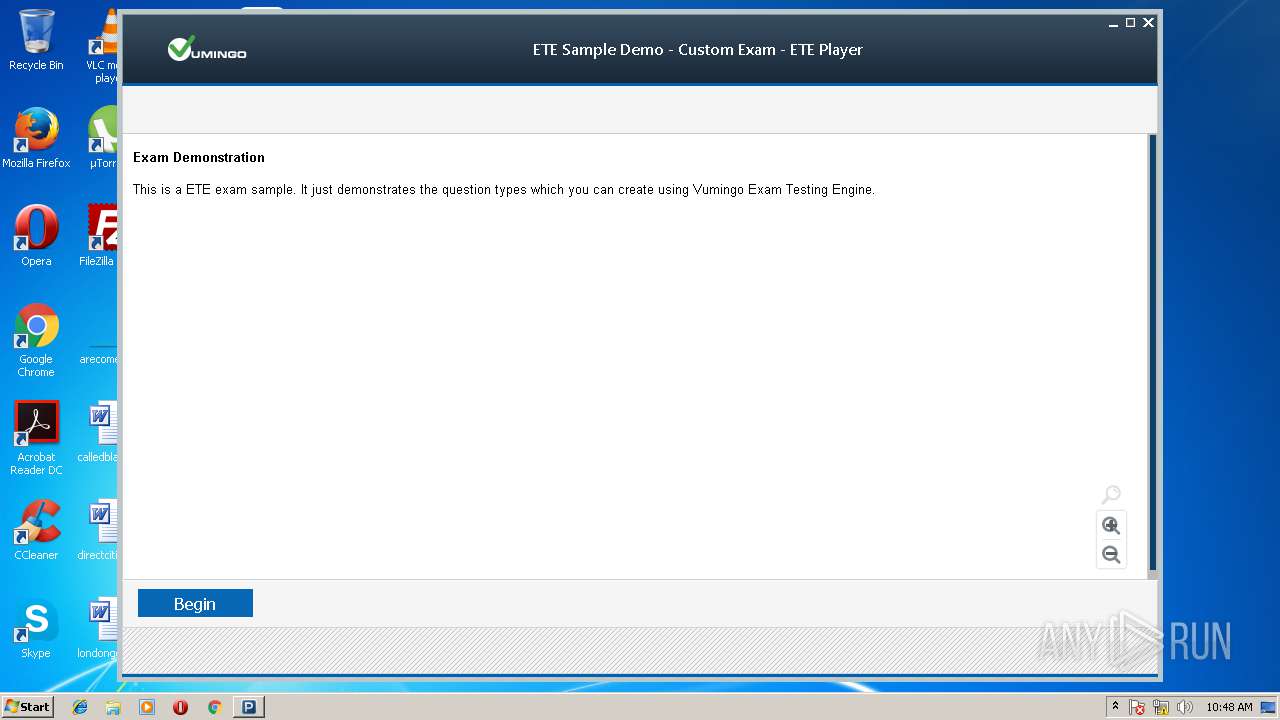
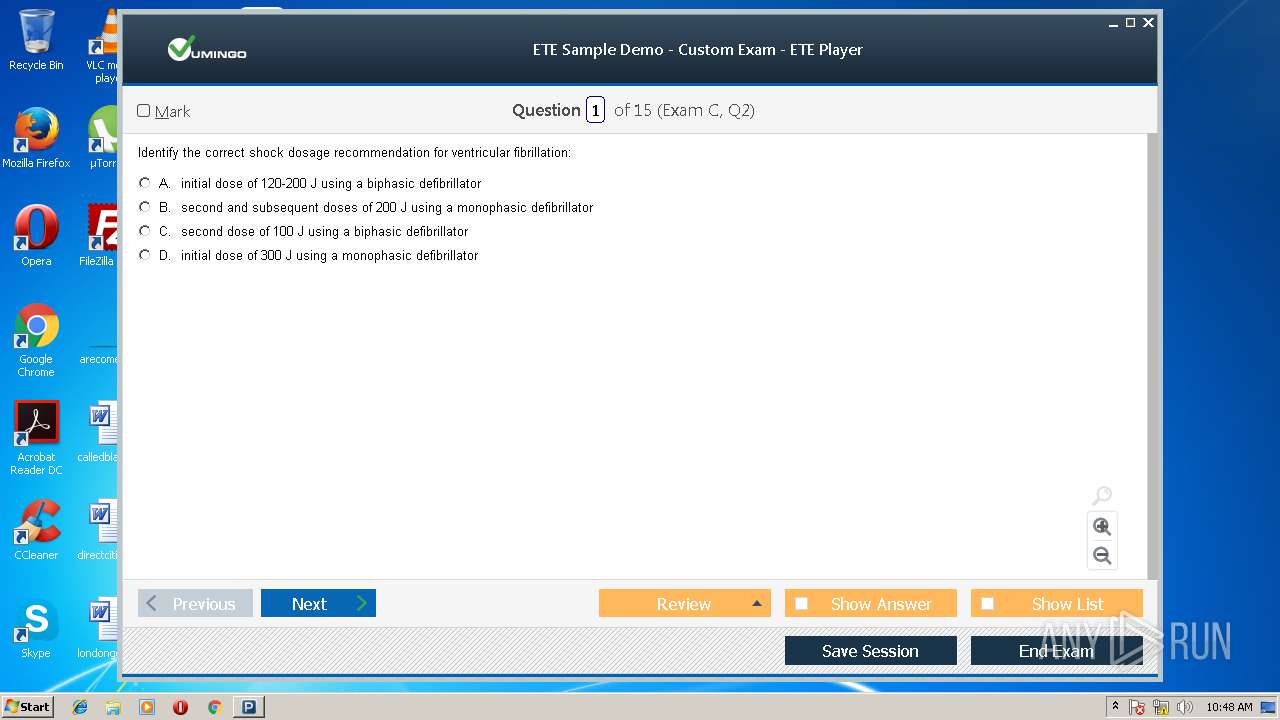
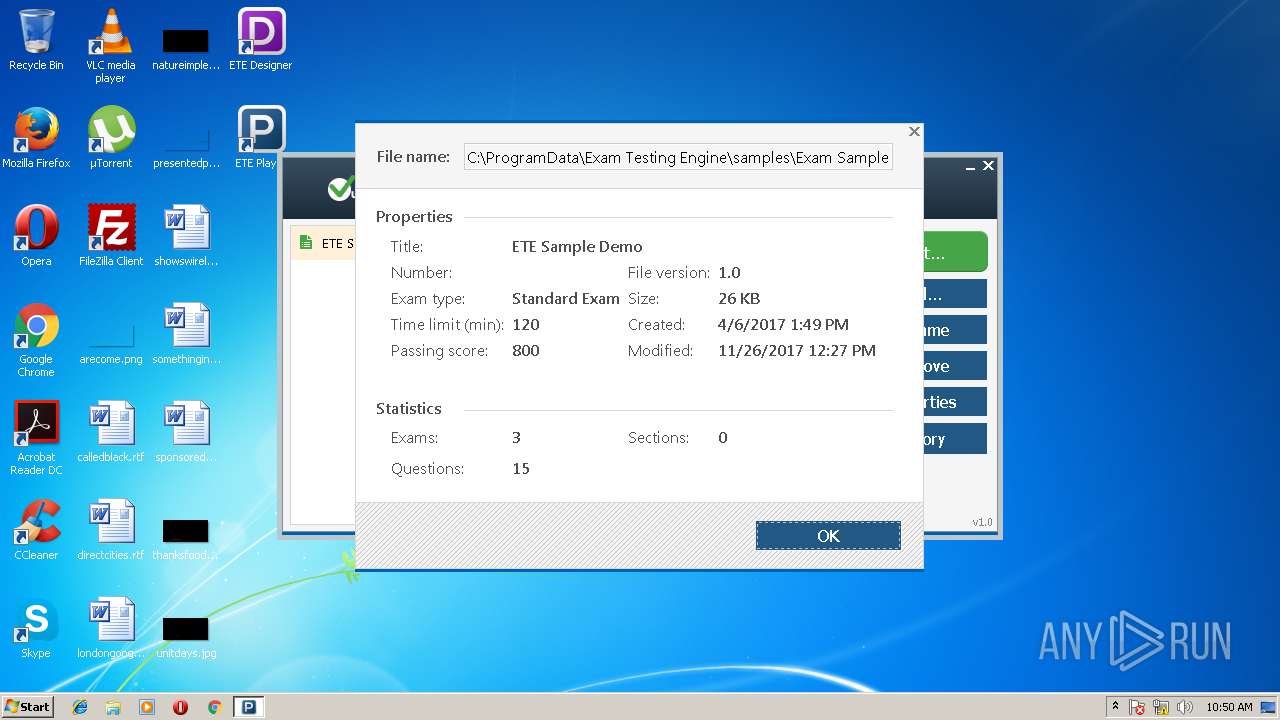
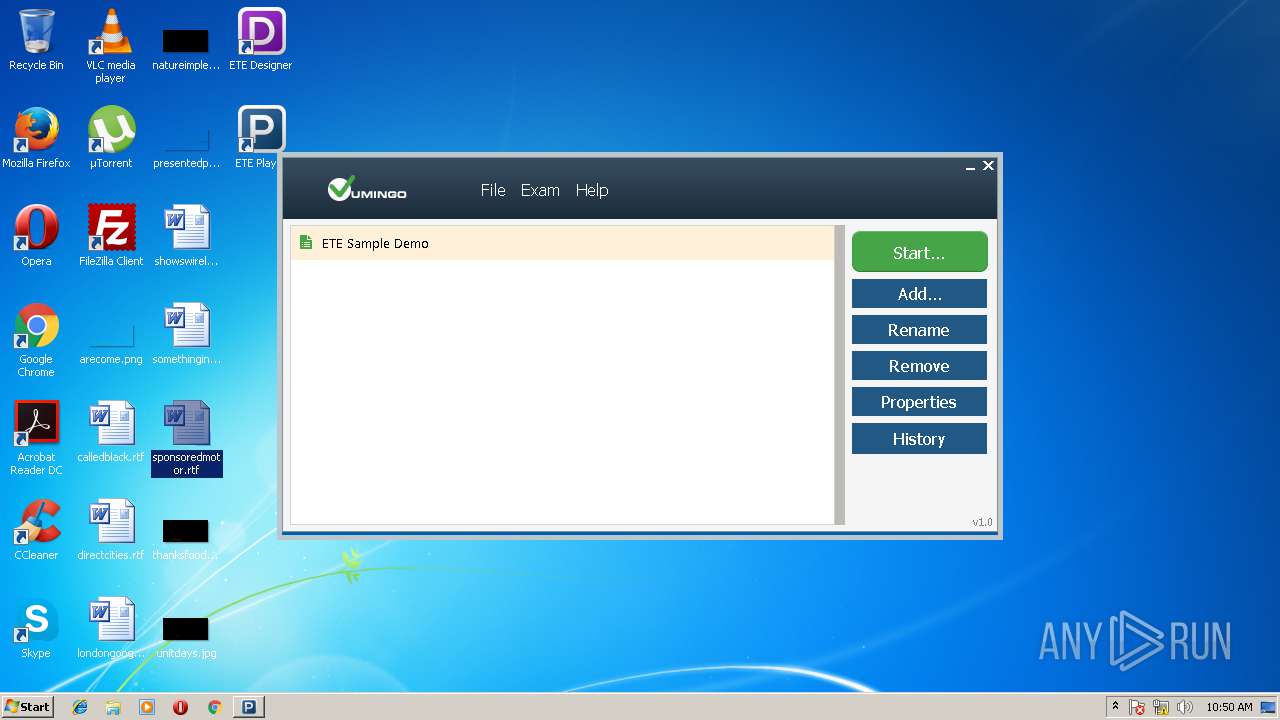
| CompanyName: | Vumingo |
| FileDescription: | Exam Testing Engine Setup |
| FileVersion: | |
| LegalCopyright: | |
| ProductName: | Exam Testing Engine |
| ProductVersion: |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Vumingo |
| FileDescription: | Exam Testing Engine Setup |
| FileVersion: | - |
| LegalCopyright: | - |
| ProductName: | Exam Testing Engine |
| ProductVersion: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x0000A1D0 | 0x0000A200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.64375 |
DATA | 0x0000C000 | 0x00000250 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.74012 |
BSS | 0x0000D000 | 0x00000E94 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000E000 | 0x0000097C | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.48608 |
.tls | 0x0000F000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00010000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.190489 |
.reloc | 0x00011000 | 0x0000091C | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00012000 | 0x0005BF28 | 0x0005C000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.11791 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 6.24323 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 6.13745 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 6.12749 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 6.06662 | 67624 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 6.06844 | 270376 | Latin 1 / Western European | English - United States | RT_ICON |
4089 | 3.21823 | 754 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4090 | 3.31515 | 780 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4091 | 3.25024 | 718 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 2.86149 | 104 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
40
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2100 | "C:\Users\admin\AppData\Local\Temp\exam_testing_engine_setup.exe" /SPAWNWND=$20136 /NOTIFYWND=$2013A | C:\Users\admin\AppData\Local\Temp\exam_testing_engine_setup.exe | exam_testing_engine_setup.tmp | ||||||||||||
User: admin Company: Vumingo Integrity Level: HIGH Description: Exam Testing Engine Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 2676 | "C:\Users\admin\AppData\Local\Temp\is-1SK2E.tmp\exam_testing_engine_setup.tmp" /SL5="$50132,16448147,423424,C:\Users\admin\AppData\Local\Temp\exam_testing_engine_setup.exe" /SPAWNWND=$20136 /NOTIFYWND=$2013A | C:\Users\admin\AppData\Local\Temp\is-1SK2E.tmp\exam_testing_engine_setup.tmp | exam_testing_engine_setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
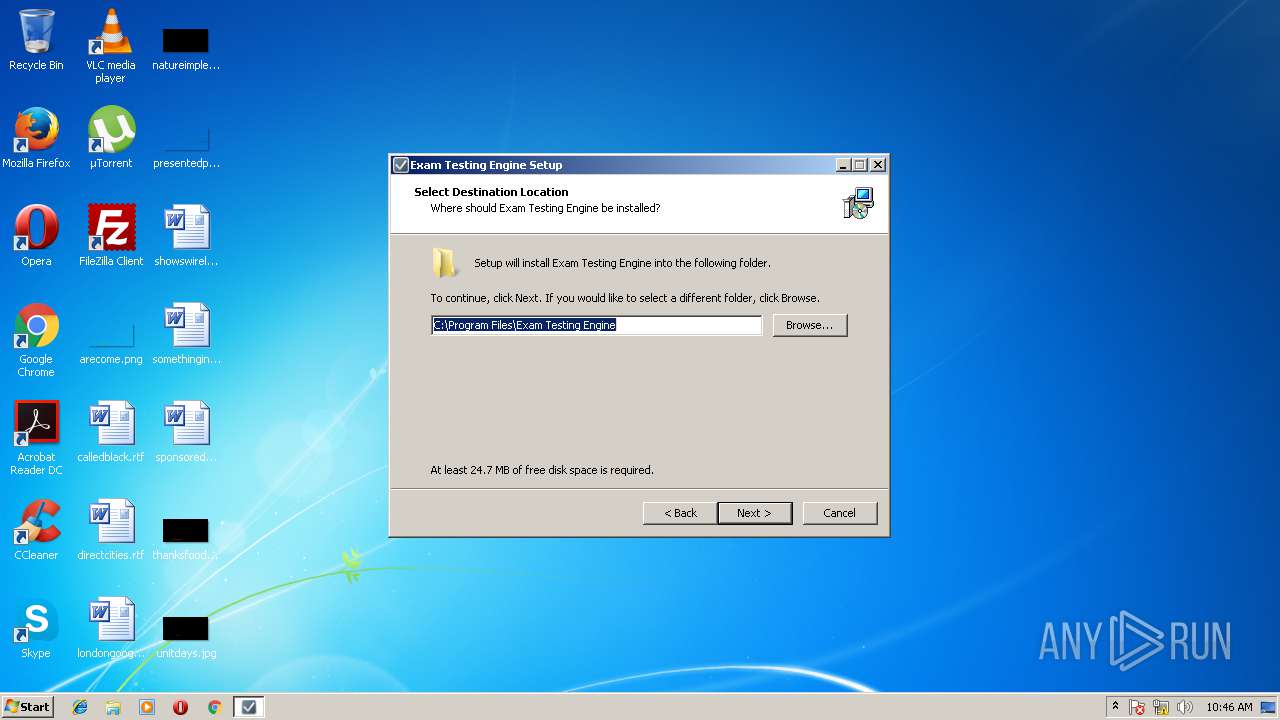
| 2704 | "C:\Program Files\Exam Testing Engine\player.exe" | C:\Program Files\Exam Testing Engine\player.exe | — | exam_testing_engine_setup.tmp | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3224 | "C:\Users\admin\AppData\Local\Temp\exam_testing_engine_setup.exe" | C:\Users\admin\AppData\Local\Temp\exam_testing_engine_setup.exe | explorer.exe | ||||||||||||
User: admin Company: Vumingo Integrity Level: MEDIUM Description: Exam Testing Engine Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 3772 | "C:\Program Files\Exam Testing Engine\player.exe" | C:\Program Files\Exam Testing Engine\player.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 4092 | "C:\Users\admin\AppData\Local\Temp\is-T5LH0.tmp\exam_testing_engine_setup.tmp" /SL5="$2013A,16448147,423424,C:\Users\admin\AppData\Local\Temp\exam_testing_engine_setup.exe" | C:\Users\admin\AppData\Local\Temp\is-T5LH0.tmp\exam_testing_engine_setup.tmp | — | exam_testing_engine_setup.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
Total events
661
Read events
594
Write events
61
Delete events
6
Modification events
| (PID) Process: | (2676) exam_testing_engine_setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 740A0000B89D0DA3C3E2D301 | |||
| (PID) Process: | (2676) exam_testing_engine_setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: E8B15BA32FC55D1AF4ED9F88A8288436D85FE7EA4AD2D195C8AD51095E253753 | |||
| (PID) Process: | (2676) exam_testing_engine_setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2676) exam_testing_engine_setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Users\admin\AppData\Local\Temp\is-FFCDR.tmp\vcredist_x86.exe | |||
| (PID) Process: | (2676) exam_testing_engine_setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 64C5B0A0C67B9A1ABB7C4F44CD84EA8941F8790A8F99B96719F582593DC6CA19 | |||
| (PID) Process: | (2676) exam_testing_engine_setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\MenuOrder\Start Menu\Programs\Exam Testing Engine |
| Operation: | write | Name: | Order |
Value: 0800000002000000A403000001000000060000007600000000000000680000004175674D020000000100000056003200AB020000B6369D9A200053616D706C65732E6C6E6B002E0003000400EFBEB6369D9AB6369D9A14000000530061006D0070006C00650073002E006C006E006B0000001A000E0000000A00EFBE000000001A000000000005000000A8000000050000009A0000004175674D020000000100000088003200CA020000B6369D9A2000554E494E53547E312E4C4E4B00005E0003000400EFBEB6369D9AB6369D9A1400000055006E0069006E007300740061006C006C002000560069007300750061006C00200043006500720074004500780061006D002000530075006900740065002E006C006E006B0000001C000E0000000A00EFBE000000001C0000000000050000009A000000020000008C0000004175674D02000000010000007A003200CA020000B6369D9A200056495355414C7E332E4C4E4B0000500003000400EFBEB6369D9AB6369D9A14000000560069007300750061006C00200043006500720074004500780061006D002000440065007300690067006E00650072002E006C006E006B0000001C000E0000000A00EFBE000000001C00000000000500000098000000010000008A0000004175674D020000000100000078003200C3020000B6369D9A200056495355414C7E312E4C4E4B00004E0003000400EFBEB6369D9AB6369D9A14000000560069007300750061006C00200043006500720074004500780061006D0020004D0061006E0061006700650072002E006C006E006B0000001C000E0000000A00EFBE000000001C0000000000050000009E00000003000000900000004175674D02000000010000007E003200CA020000B6369D9A200056495355414C7E322E4C4E4B0000540003000400EFBEB6369D9AB6369D9A14000000560069007300750061006C00200043006500720074004500780061006D002000530075006900740065002000480065006C0070002E006C006E006B0000001C000E0000000A00EFBE000000001C000000000005000000AA000000040000009C0000004175674D02000000010000008A00320037000000B6369D9A200056495355414C7E312E55524C0000600003000400EFBEB6369D9AB6369D9A14000000560069007300750061006C00200043006500720074004500780061006D0020005300750069007400650020006F006E00200074006800650020005700650062002E00750072006C0000001C000E0000000A00EFBE000000001C000000000005000000 | |||
| (PID) Process: | (2676) exam_testing_engine_setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\MenuOrder\Start Menu2\Programs\Exam Testing Engine |
| Operation: | write | Name: | Order |
Value: 0800000002000000A403000001000000060000007600000000000000680000004175674D020000000100000056003200AB020000B6369D9A200053616D706C65732E6C6E6B002E0003000400EFBEB6369D9AB6369D9A14000000530061006D0070006C00650073002E006C006E006B0000001A000E0000000A00EFBE000000001A000000000005000000A8000000050000009A0000004175674D020000000100000088003200CA020000B6369D9A2000554E494E53547E312E4C4E4B00005E0003000400EFBEB6369D9AB6369D9A1400000055006E0069006E007300740061006C006C002000560069007300750061006C00200043006500720074004500780061006D002000530075006900740065002E006C006E006B0000001C000E0000000A00EFBE000000001C0000000000050000009A000000020000008C0000004175674D02000000010000007A003200CA020000B6369D9A200056495355414C7E332E4C4E4B0000500003000400EFBEB6369D9AB6369D9A14000000560069007300750061006C00200043006500720074004500780061006D002000440065007300690067006E00650072002E006C006E006B0000001C000E0000000A00EFBE000000001C00000000000500000098000000010000008A0000004175674D020000000100000078003200C3020000B6369D9A200056495355414C7E312E4C4E4B00004E0003000400EFBEB6369D9AB6369D9A14000000560069007300750061006C00200043006500720074004500780061006D0020004D0061006E0061006700650072002E006C006E006B0000001C000E0000000A00EFBE000000001C0000000000050000009E00000003000000900000004175674D02000000010000007E003200CA020000B6369D9A200056495355414C7E322E4C4E4B0000540003000400EFBEB6369D9AB6369D9A14000000560069007300750061006C00200043006500720074004500780061006D002000530075006900740065002000480065006C0070002E006C006E006B0000001C000E0000000A00EFBE000000001C000000000005000000AA000000040000009C0000004175674D02000000010000008A00320037000000B6369D9A200056495355414C7E312E55524C0000600003000400EFBEB6369D9AB6369D9A14000000560069007300750061006C00200043006500720074004500780061006D0020005300750069007400650020006F006E00200074006800650020005700650062002E00750072006C0000001C000E0000000A00EFBE000000001C000000000005000000 | |||
| (PID) Process: | (2676) exam_testing_engine_setup.tmp | Key: | HKEY_CURRENT_USER\Software\Exam Testing Engine |
| Operation: | write | Name: | path |
Value: C:\Program Files\Exam Testing Engine | |||
| (PID) Process: | (2676) exam_testing_engine_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.ete |
| Operation: | write | Name: | |
Value: etefile | |||
| (PID) Process: | (2676) exam_testing_engine_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\etefile |
| Operation: | write | Name: | |
Value: Exam Testing Engine File | |||
Executable files
12
Suspicious files
4
Text files
4
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2676 | exam_testing_engine_setup.tmp | C:\Program Files\Exam Testing Engine\uninstall\is-R4EIN.tmp | — | |
MD5:— | SHA256:— | |||
| 2676 | exam_testing_engine_setup.tmp | C:\Users\admin\AppData\Local\Temp\is-FFCDR.tmp\is-39F9A.tmp | — | |
MD5:— | SHA256:— | |||
| 2676 | exam_testing_engine_setup.tmp | C:\Program Files\Exam Testing Engine\is-9J8HE.tmp | — | |
MD5:— | SHA256:— | |||
| 2676 | exam_testing_engine_setup.tmp | C:\Program Files\Exam Testing Engine\is-TMREC.tmp | — | |
MD5:— | SHA256:— | |||
| 2676 | exam_testing_engine_setup.tmp | C:\Program Files\Exam Testing Engine\is-M2949.tmp | — | |
MD5:— | SHA256:— | |||
| 2676 | exam_testing_engine_setup.tmp | C:\Program Files\Exam Testing Engine\is-R81C5.tmp | — | |
MD5:— | SHA256:— | |||
| 2676 | exam_testing_engine_setup.tmp | C:\Program Files\Exam Testing Engine\is-065MP.tmp | — | |
MD5:— | SHA256:— | |||
| 2676 | exam_testing_engine_setup.tmp | C:\Program Files\Exam Testing Engine\is-IEQS1.tmp | — | |
MD5:— | SHA256:— | |||
| 2676 | exam_testing_engine_setup.tmp | C:\Program Files\Exam Testing Engine\help\is-1CA7I.tmp | — | |
MD5:— | SHA256:— | |||
| 2676 | exam_testing_engine_setup.tmp | C:\Program Files\Exam Testing Engine\help\is-OJQNI.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
7
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 404 | 138.197.108.120:80 | http://update.vumingo.com/update.xml | US | html | 208 b | unknown |
— | — | GET | 404 | 138.197.108.120:80 | http://update.vumingo.com/update.xml | US | html | 208 b | unknown |
— | — | GET | 404 | 138.197.108.120:80 | http://update.vumingo.com/update.xml | US | html | 208 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 138.197.108.120:443 | update.vumingo.com | Digital Ocean, Inc. | US | unknown |
— | — | 138.197.108.120:80 | update.vumingo.com | Digital Ocean, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
update.vumingo.com |
| unknown |
www.vumingo.com |
| unknown |
license.vumingo.com |
| unknown |