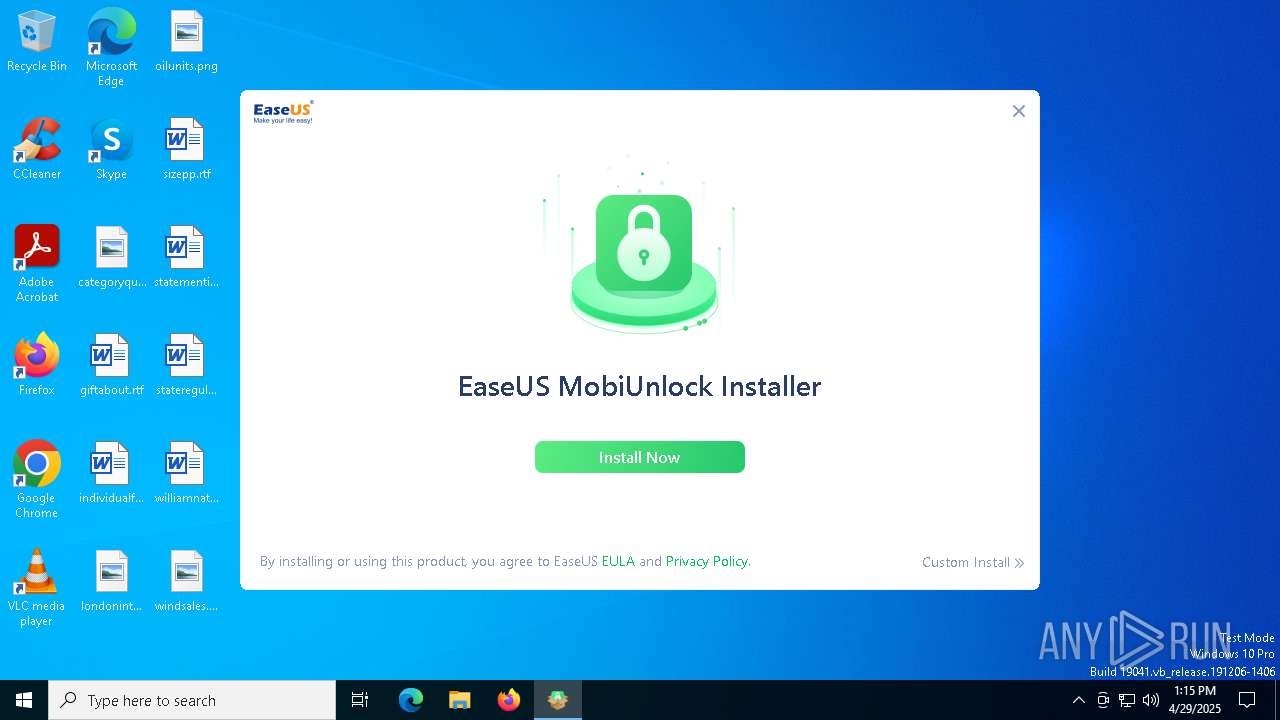
| File name: | mobiunlockforandroid_trial_Installer_20250429.729067.exe |
| Full analysis: | https://app.any.run/tasks/2d2e2d6c-f966-446c-870f-9b976c0a0d91 |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 13:15:19 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | 1439762152CEB27C6A00D4C5AFB48F04 |
| SHA1: | D7E3E9B1976FABC570360CA86568EEEABB59D90C |
| SHA256: | D31794639E394B80C5BF5A4340C3BB22CB53F18448B8DF270DFB6A81D1C6C1C9 |
| SSDEEP: | 49152:8lWG870XkfeoHDgh7TzBzY5oOCIPkFjdzwm0XL2HlBVYHg6DoTrJy0kkgS4FqPcA:8R+RWzBzcEIPkbzwm4L2HlBU9DoZ01He |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:01:30 03:57:48+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26624 |
| InitializedDataSize: | 186368 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x338f |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
135
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | ||||
|---|---|---|---|---|---|---|---|---|
| 5332 | "C:\Users\admin\AppData\Local\Temp\mobiunlockforandroid_trial_Installer_20250429.729067.exe" | C:\Users\admin\AppData\Local\Temp\mobiunlockforandroid_trial_Installer_20250429.729067.exe | — | explorer.exe | ||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| ||||||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
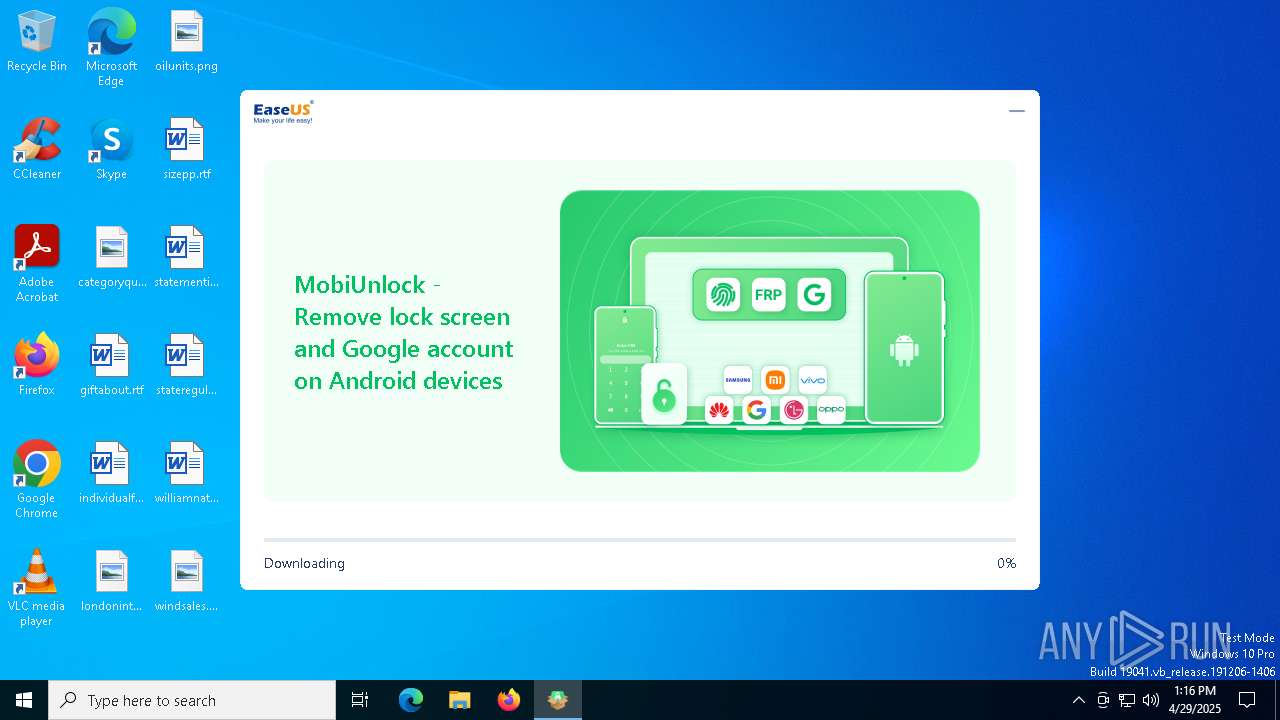
HTTP(S) requests
13
TCP/UDP connections
31
DNS requests
17
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | POST | 200 | 47.252.97.14:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_muandroid_downloader/shards/lb | unknown | — | — | unknown |
— | — | POST | 200 | 47.252.97.14:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_muandroid_downloader/shards/lb | unknown | — | — | unknown |
6544 | svchost.exe | GET | 200 | 2.22.98.7:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6712 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 47.252.97.14:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_muandroid_downloader/shards/lb | unknown | — | — | unknown |
2244 | AliyunWrapExe.exe | POST | 200 | 47.252.97.14:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_muandroid_downloader/shards/lb | unknown | — | — | unknown |
— | — | POST | 200 | 3.167.227.34:80 | http://download.easeus.com/api/index.php/Home/product/config/ | unknown | — | — | unknown |
— | — | GET | 200 | 8.218.236.152:80 | http://track.easeus.com/product/index.php?c=main&a=getstatus&pid=20 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.253.202:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
— | — | 3.167.227.34:80 | download.easeus.com | — | US | unknown |
— | — | 18.245.31.48:443 | d.easeus.com | — | US | unknown |
— | — | 8.218.236.152:80 | track.easeus.com | Alibaba US Technology Co., Ltd. | HK | suspicious |
— | — | 47.252.97.14:80 | easeusinfo.us-east-1.log.aliyuncs.com | Alibaba US Technology Co., Ltd. | US | unknown |
6544 | svchost.exe | 40.126.32.72:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
download.easeus.com |
| unknown |
d.easeus.com |
| unknown |
track.easeus.com |
| unknown |
easeusinfo.us-east-1.log.aliyuncs.com |
| unknown |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |
2244 | AliyunWrapExe.exe | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
2244 | AliyunWrapExe.exe | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
2244 | AliyunWrapExe.exe | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
2244 | AliyunWrapExe.exe | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
2244 | AliyunWrapExe.exe | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
2244 | AliyunWrapExe.exe | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |