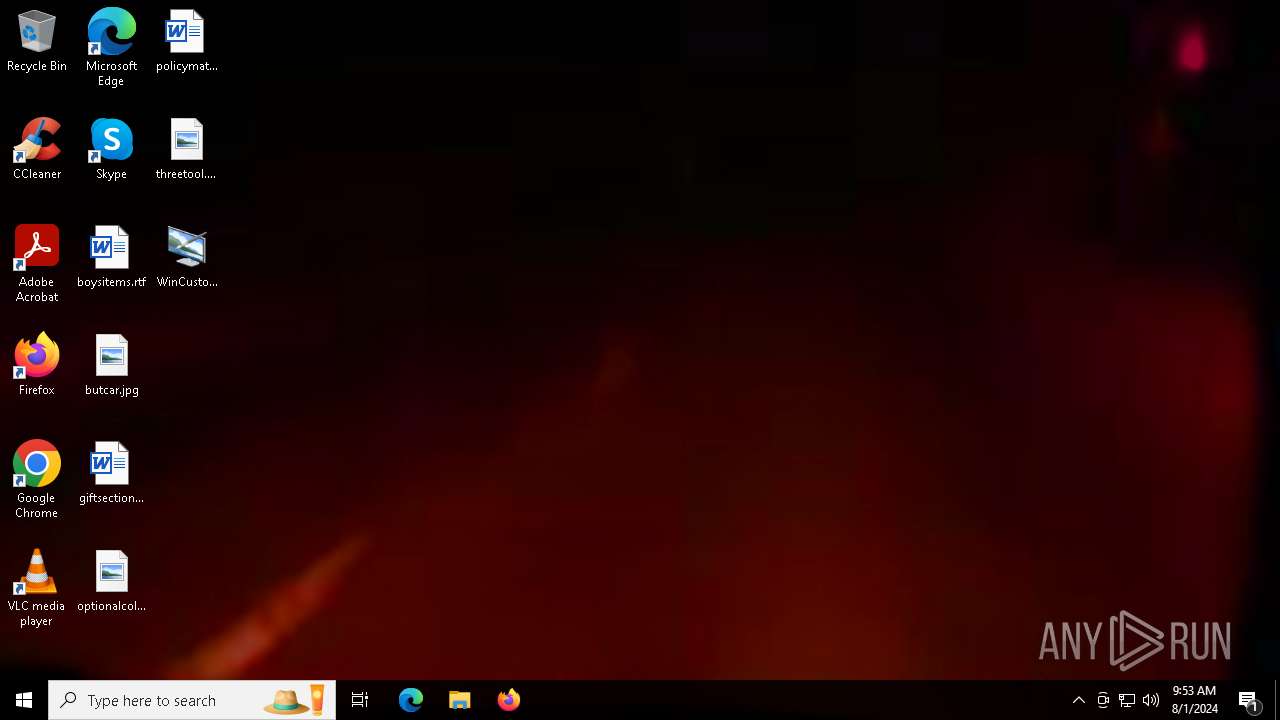
| File name: | WinCustomize.exe |
| Full analysis: | https://app.any.run/tasks/f301fbb3-0ce6-4737-8882-94a08f4322a5 |
| Verdict: | Malicious activity |
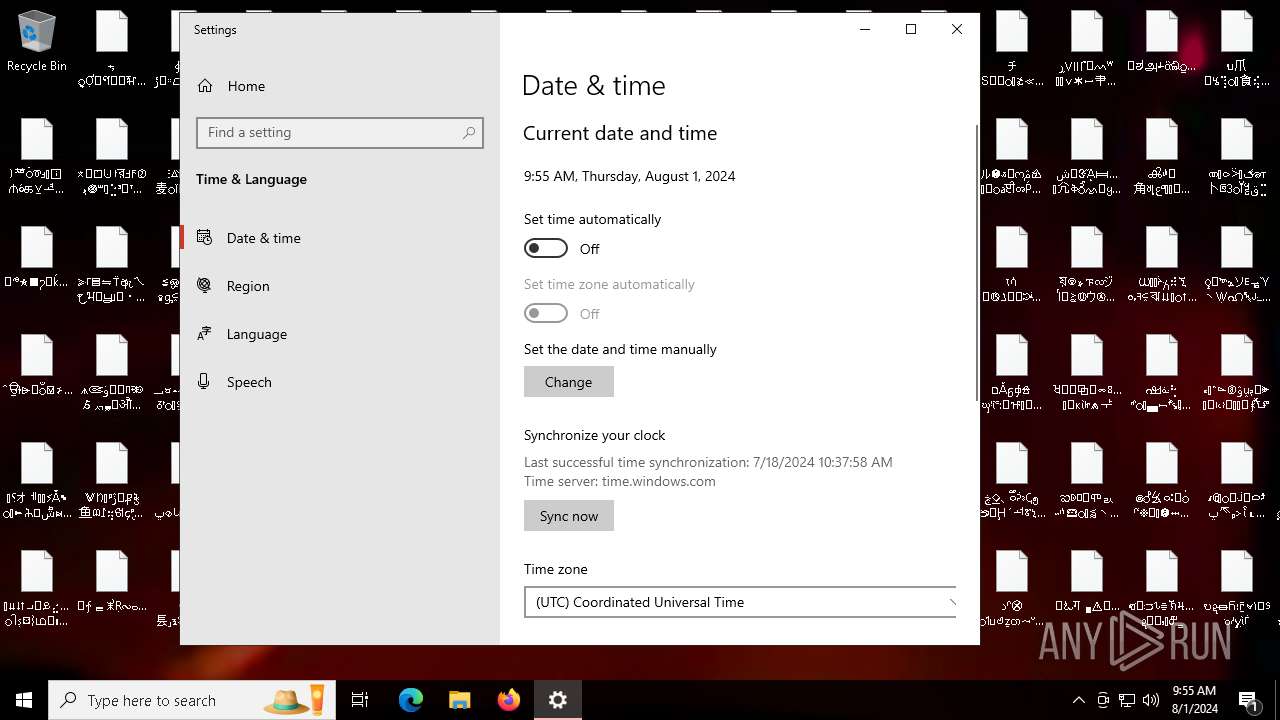
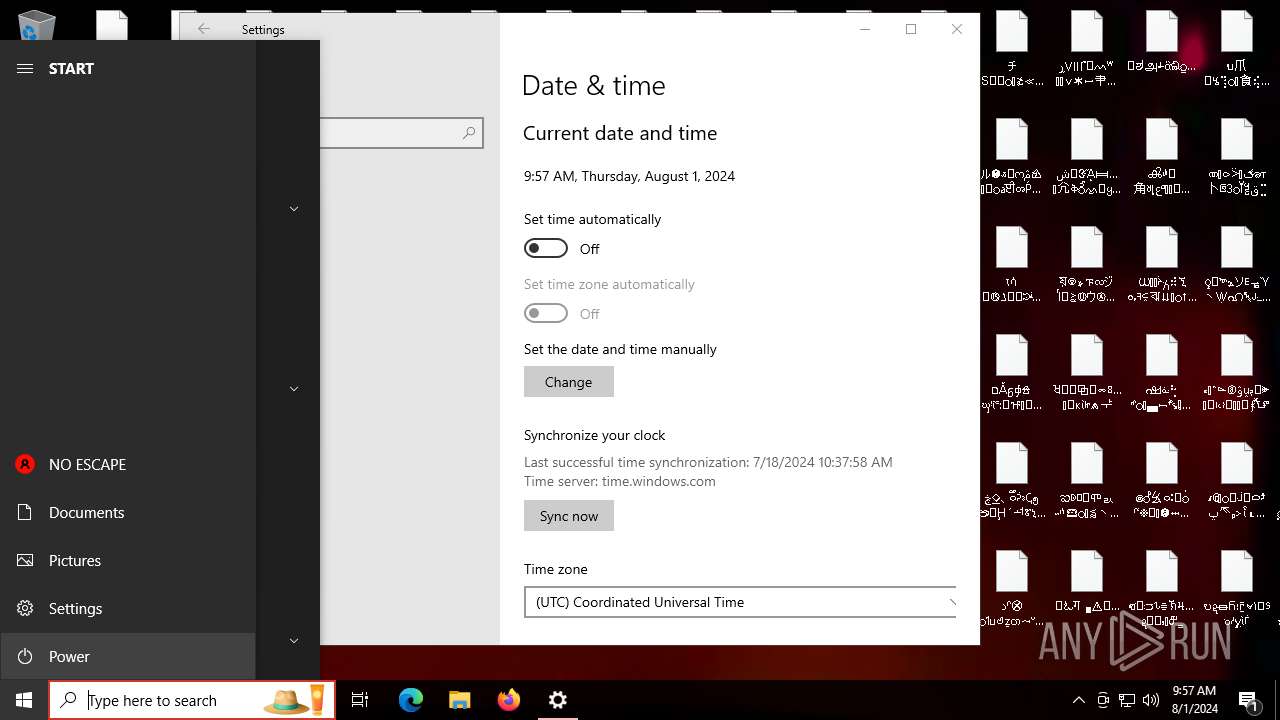
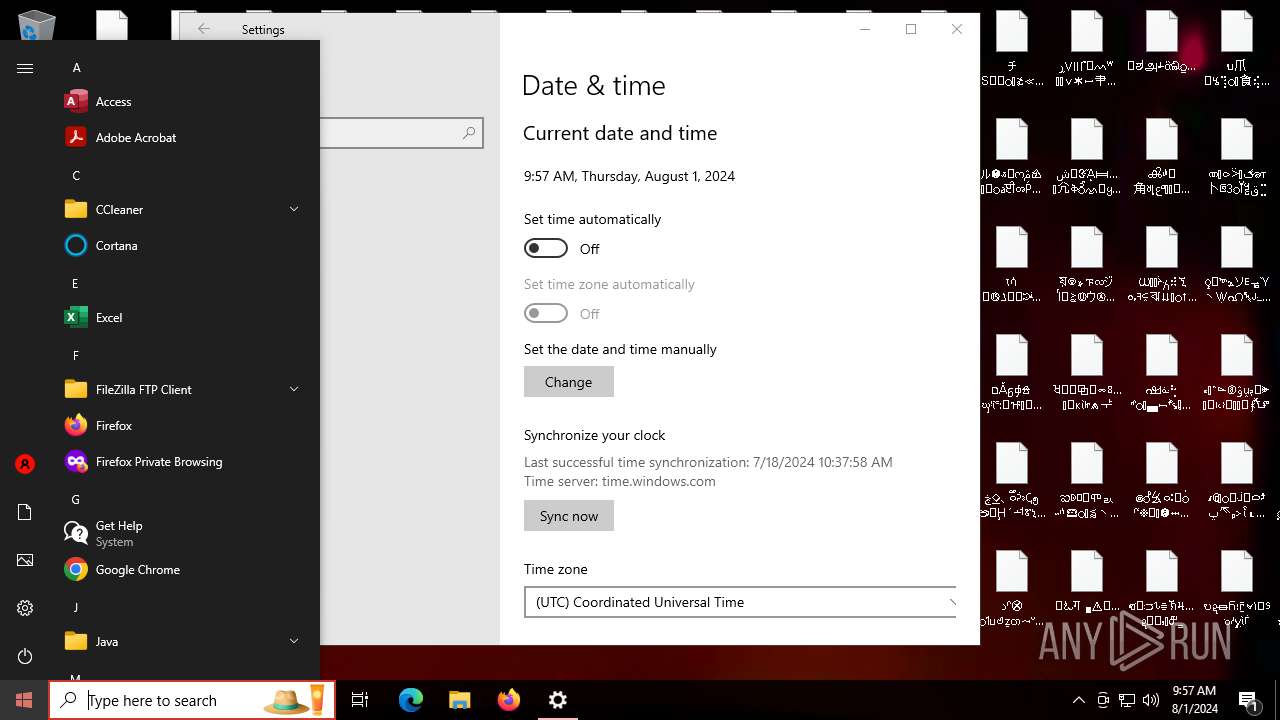
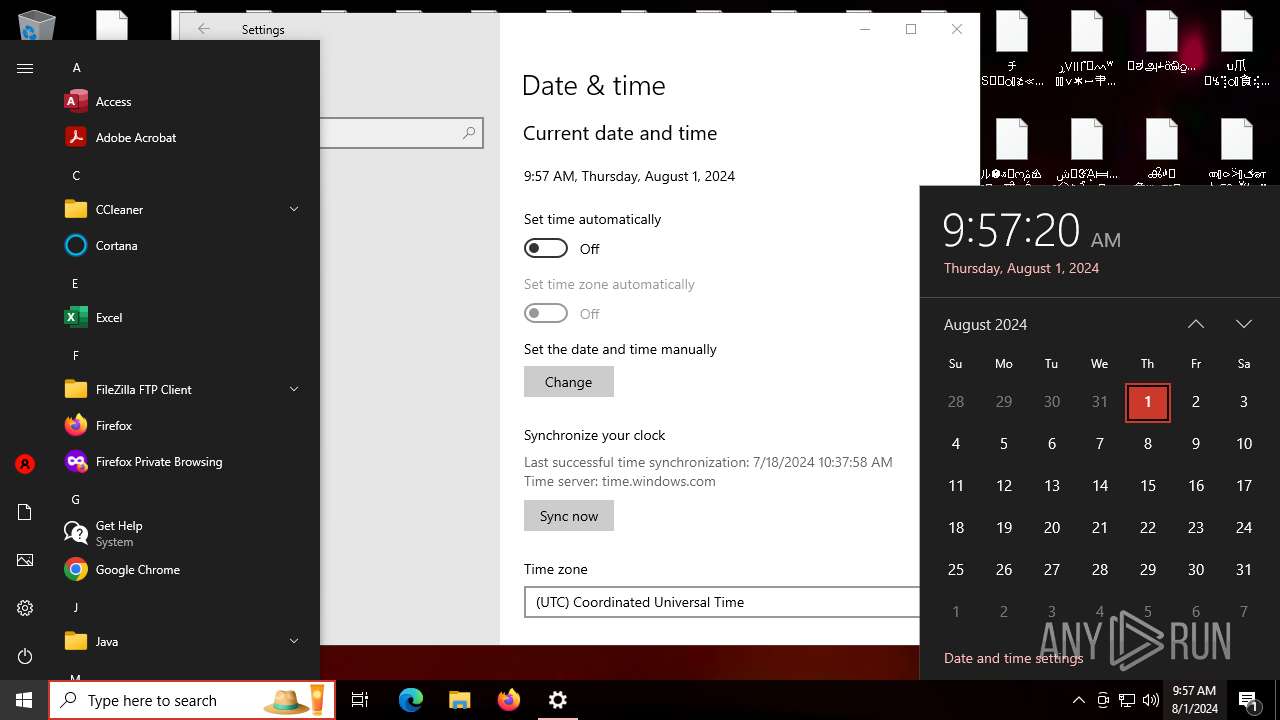
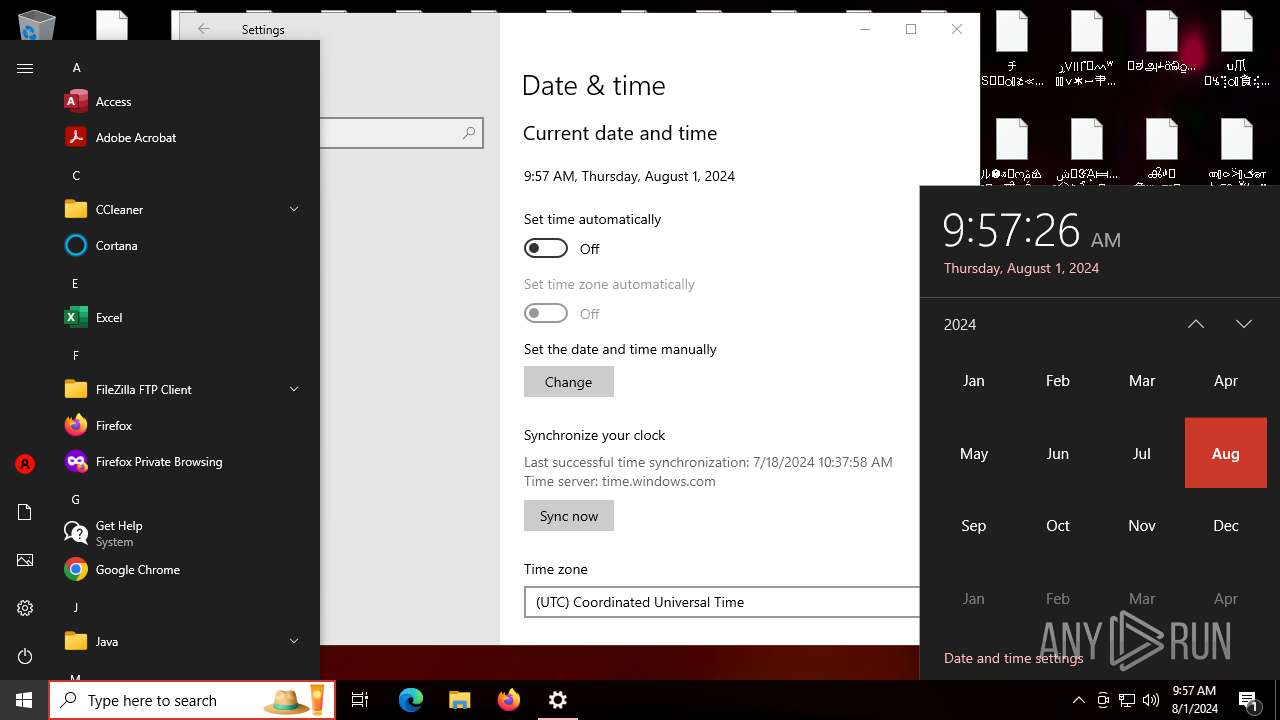
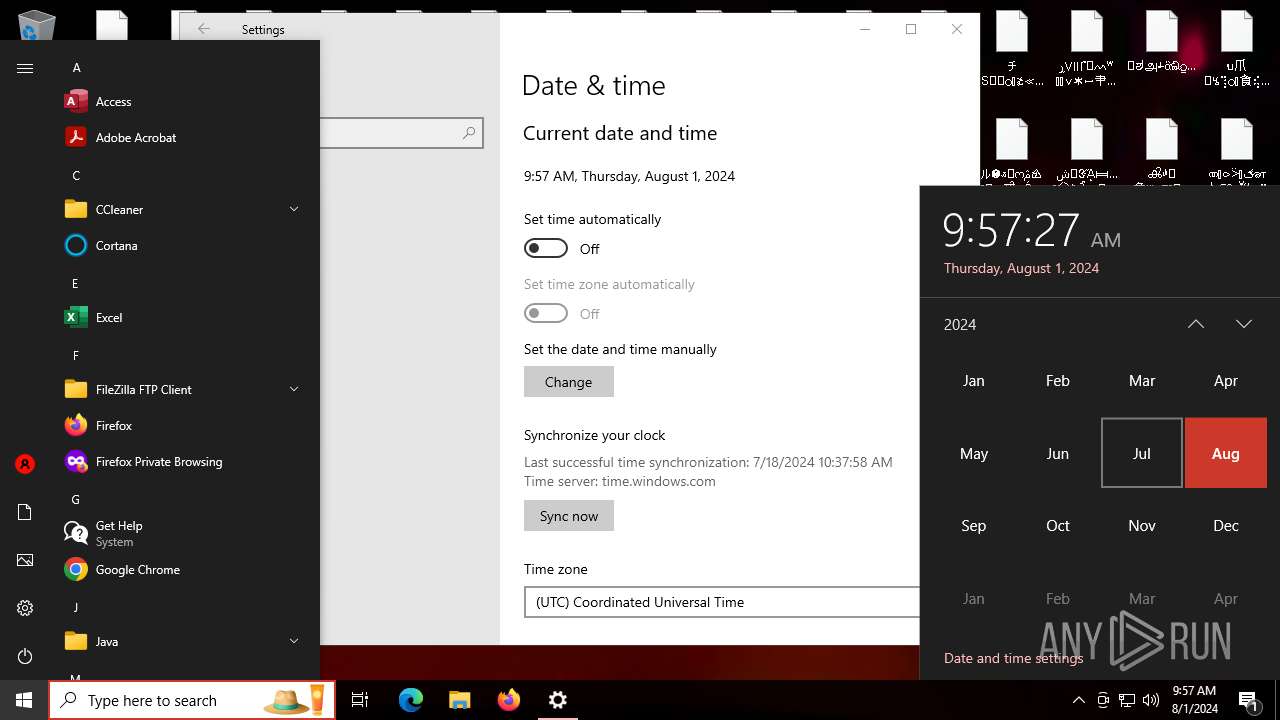
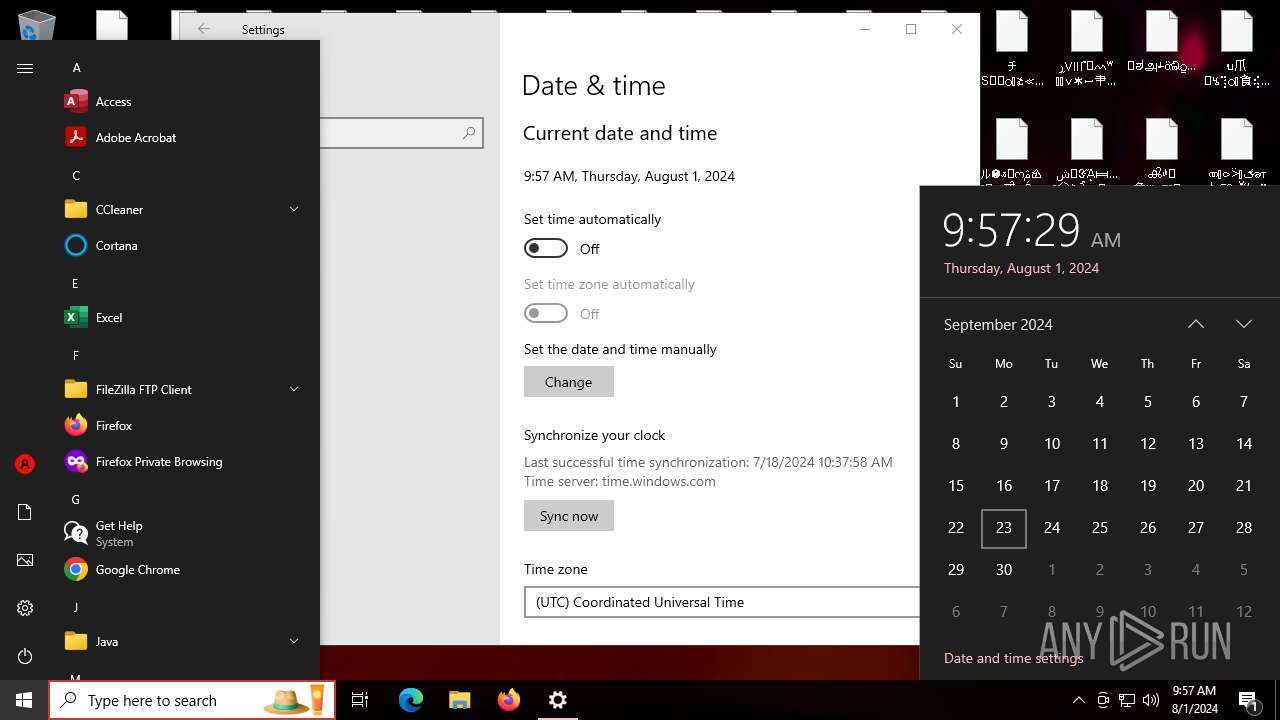
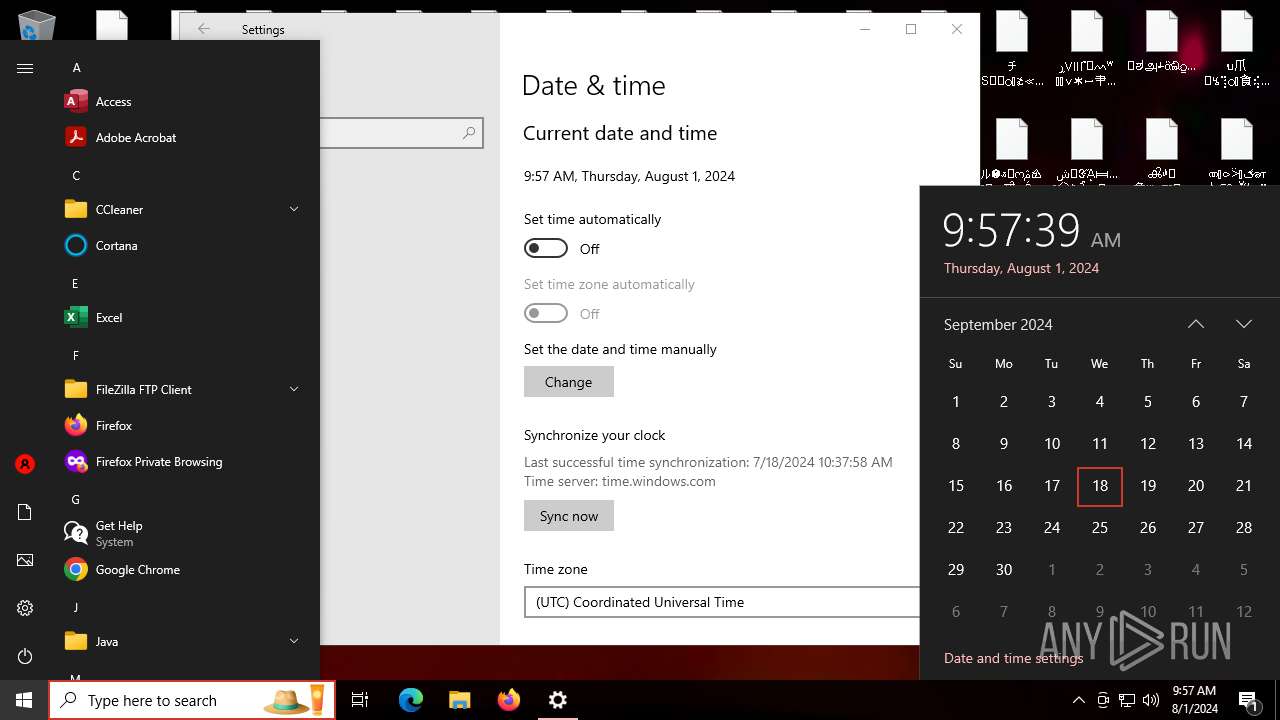
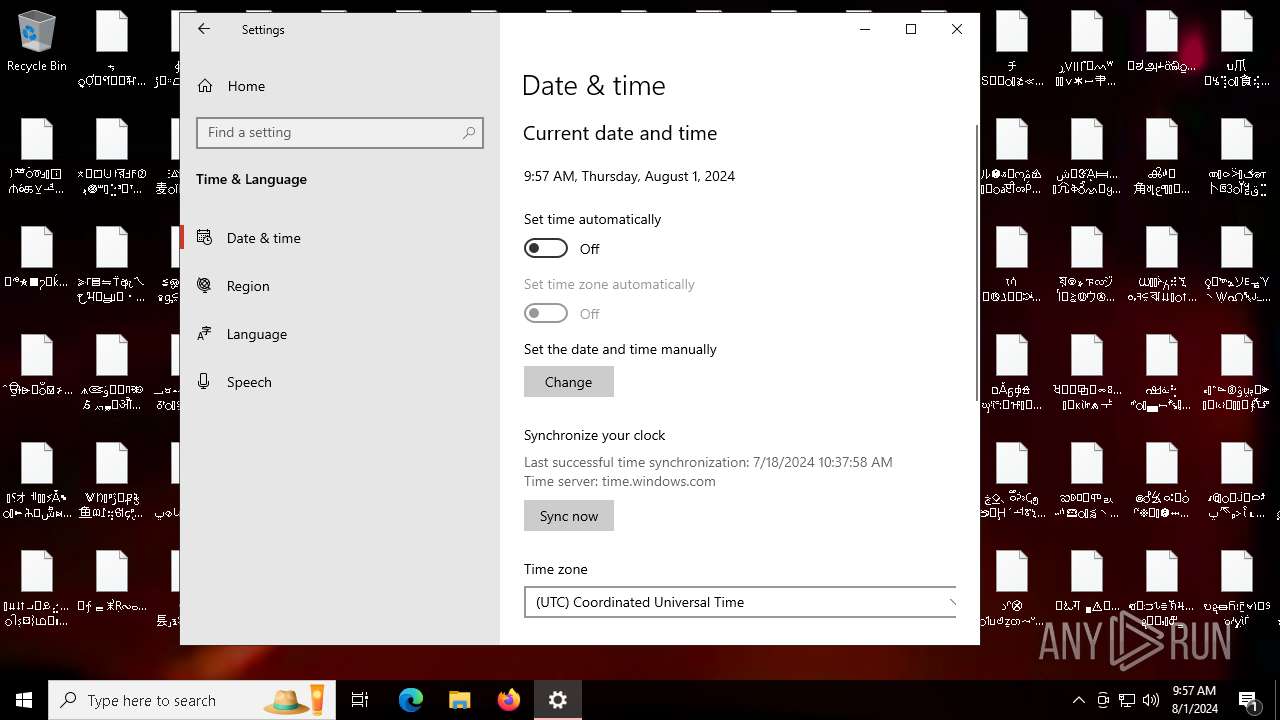
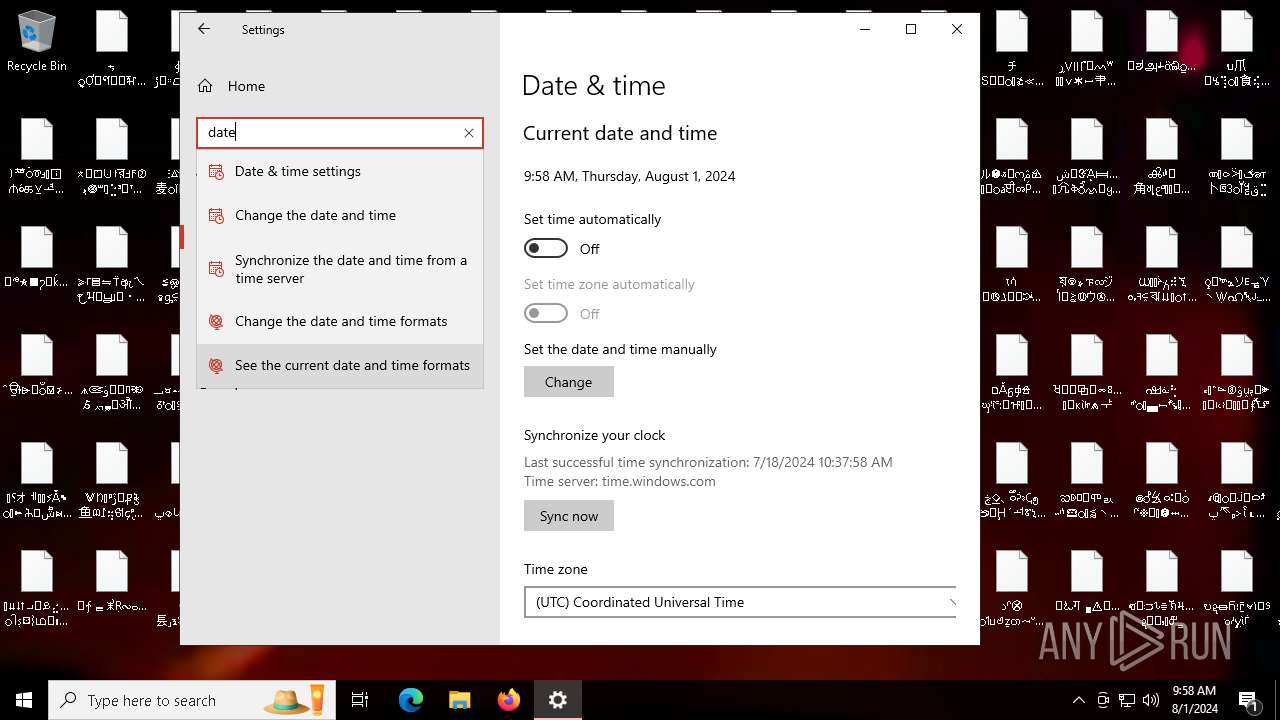
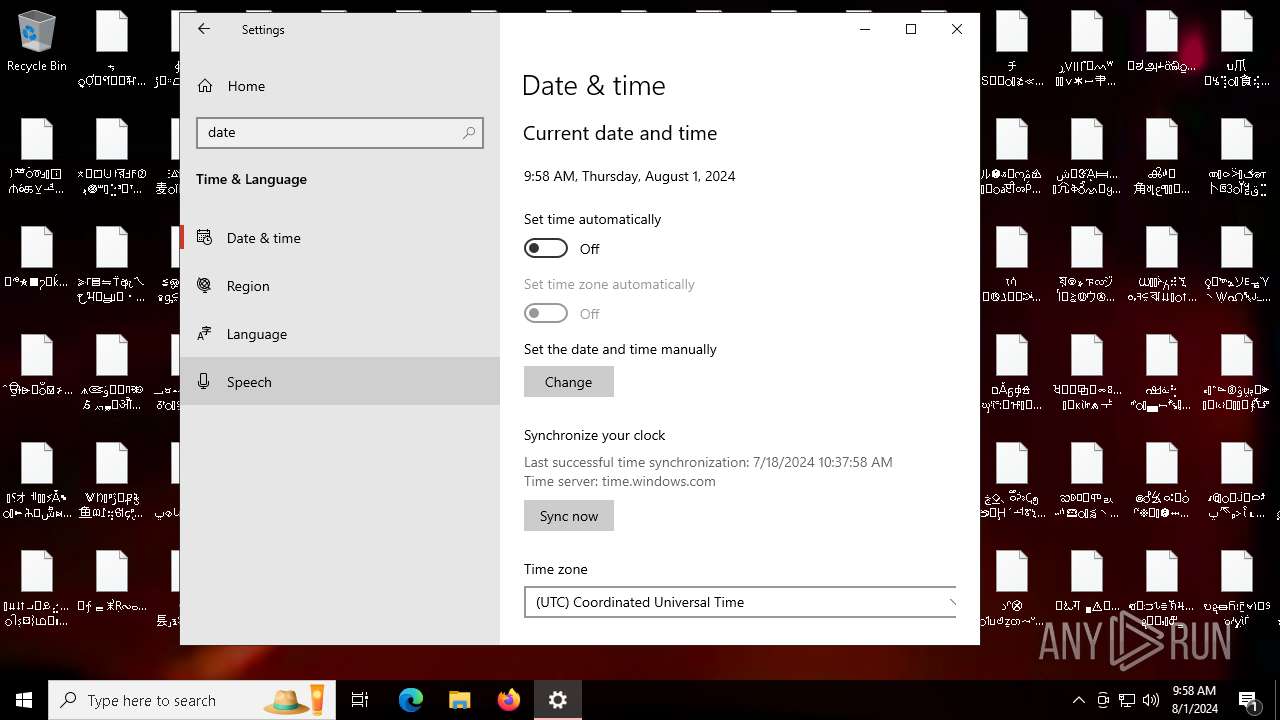
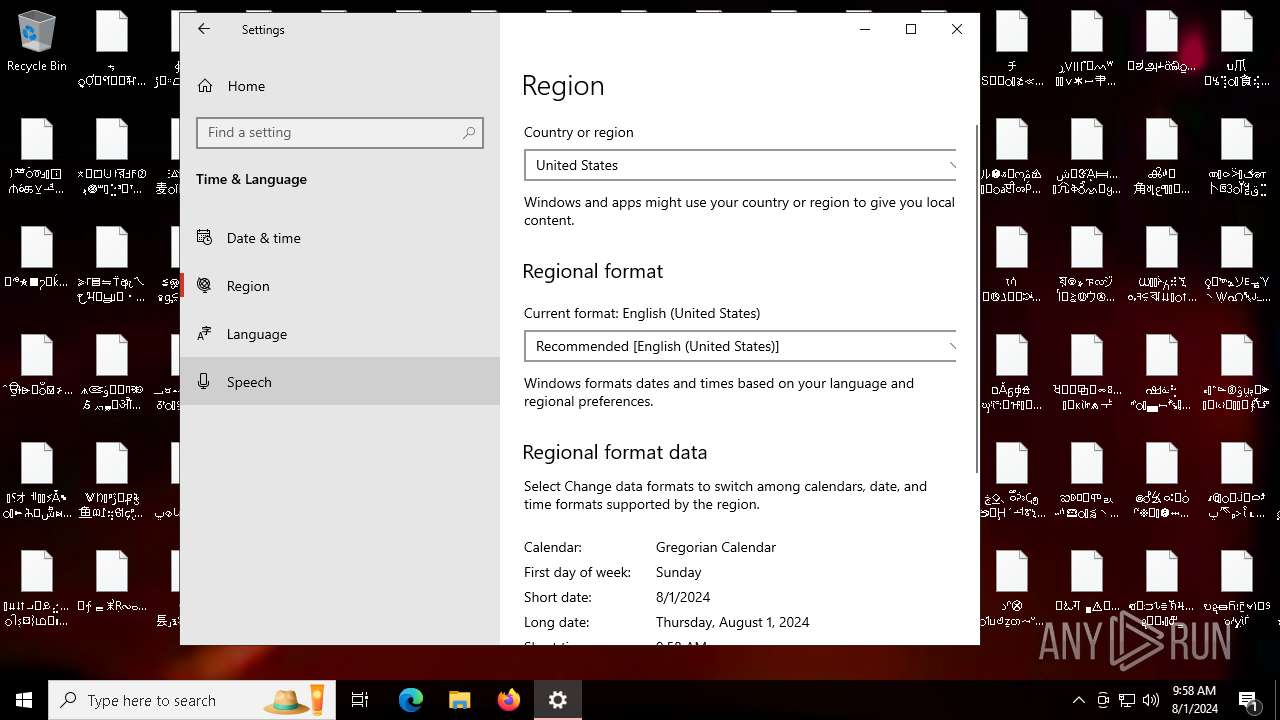
| Analysis date: | August 01, 2024, 09:53:04 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | MS-DOS executable PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows, MZ for MS-DOS |
| MD5: | 989AE3D195203B323AA2B3ADF04E9833 |
| SHA1: | 31A45521BC672ABCF64E50284CA5D4E6B3687DC8 |
| SHA256: | D30D7676A3B4C91B77D403F81748EBF6B8824749DB5F860E114A8A204BCA5B8F |
| SSDEEP: | 12288:85J5X487qJUtcWfkVJ6g5s/cD01oKHQyis2AePsr8nP712TBJ:s487pcZEgwcDpg1L2tbPR2tJ |
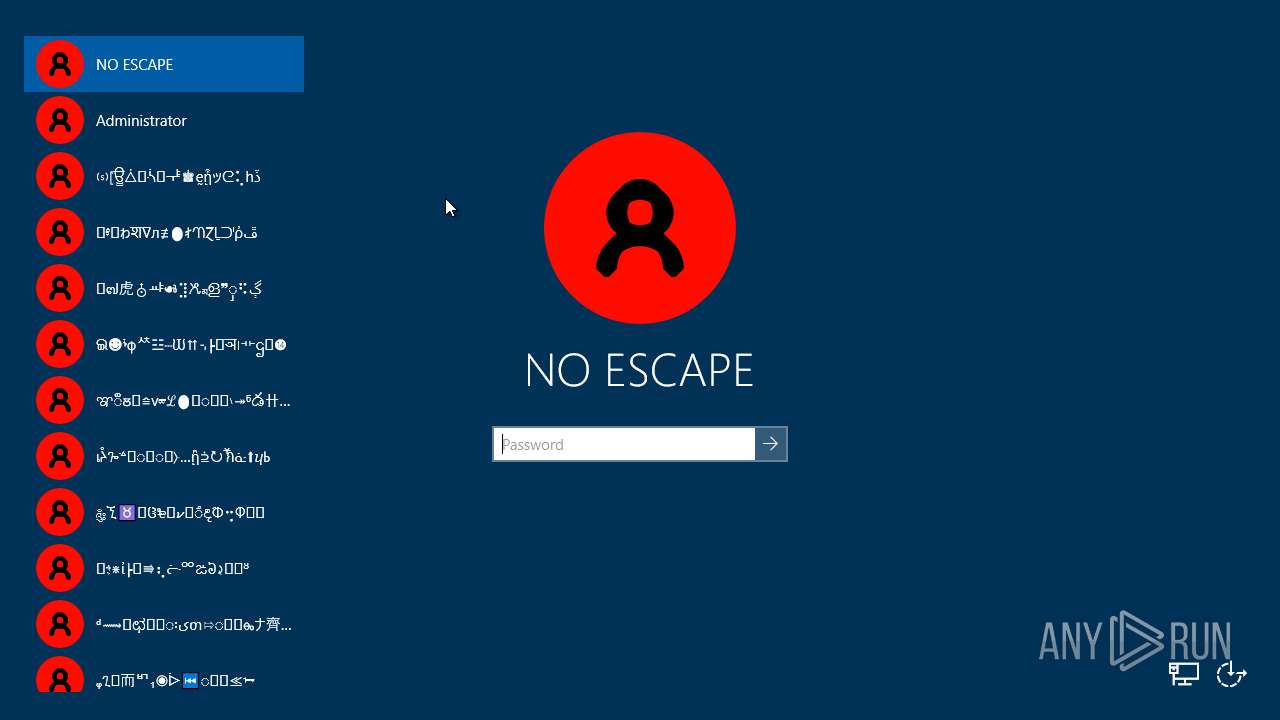
MALICIOUS
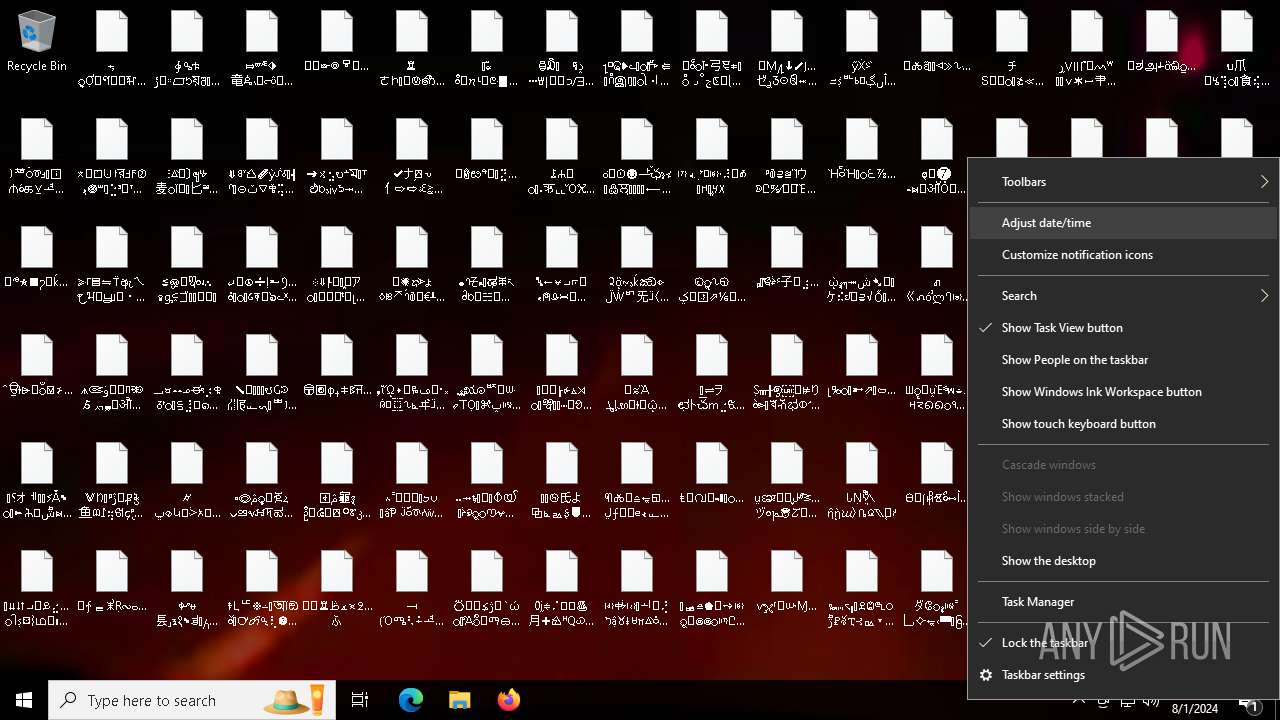
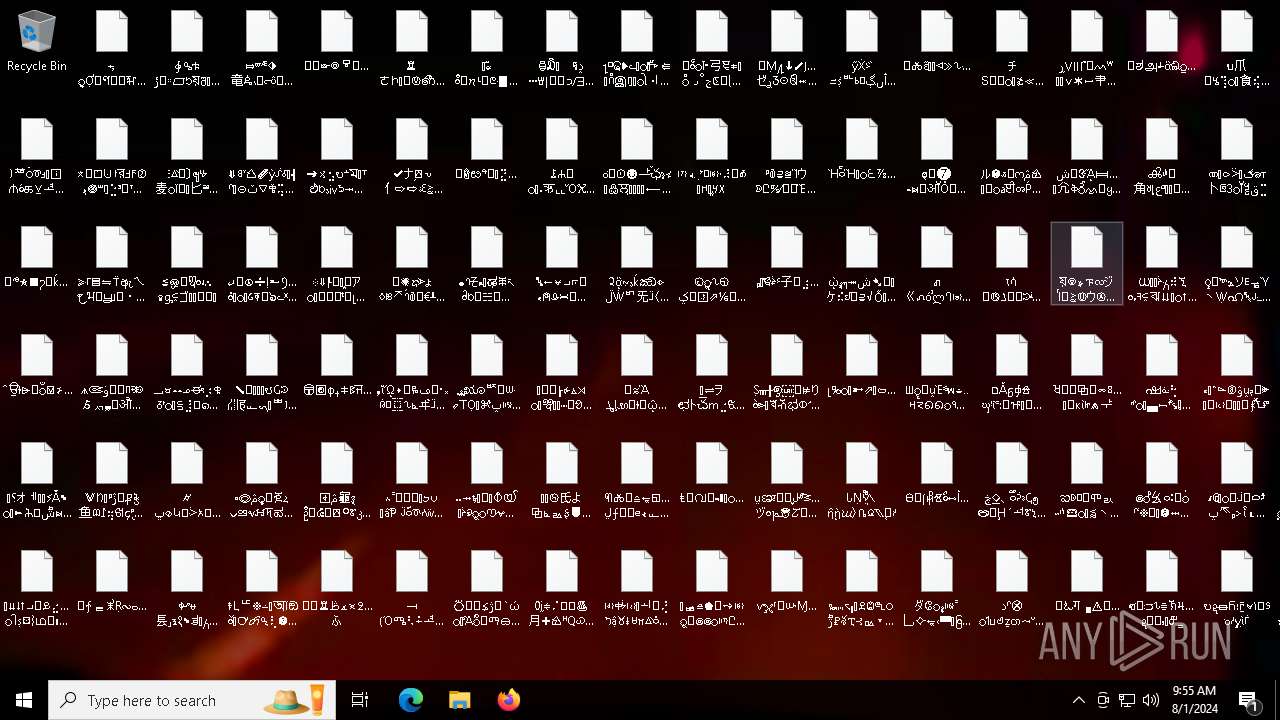
Drops the executable file immediately after the start
- WinCustomize.exe (PID: 6364)
- WinCustomize.exe (PID: 6456)
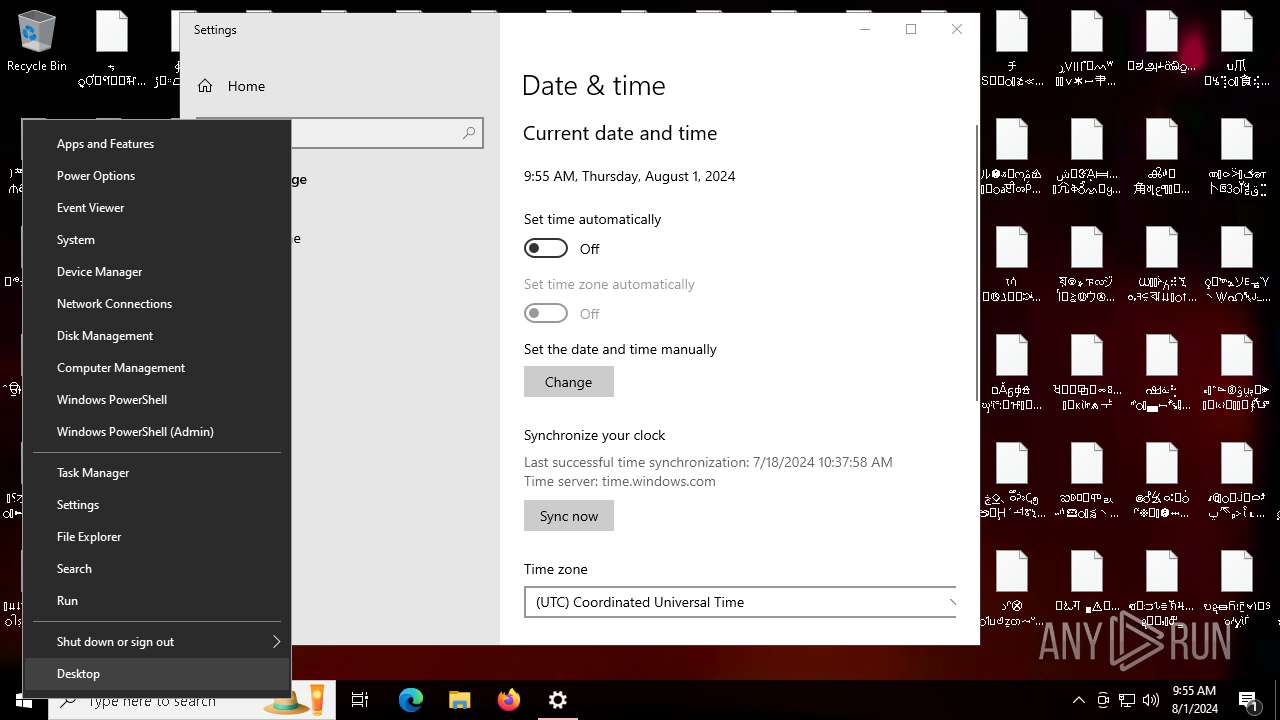
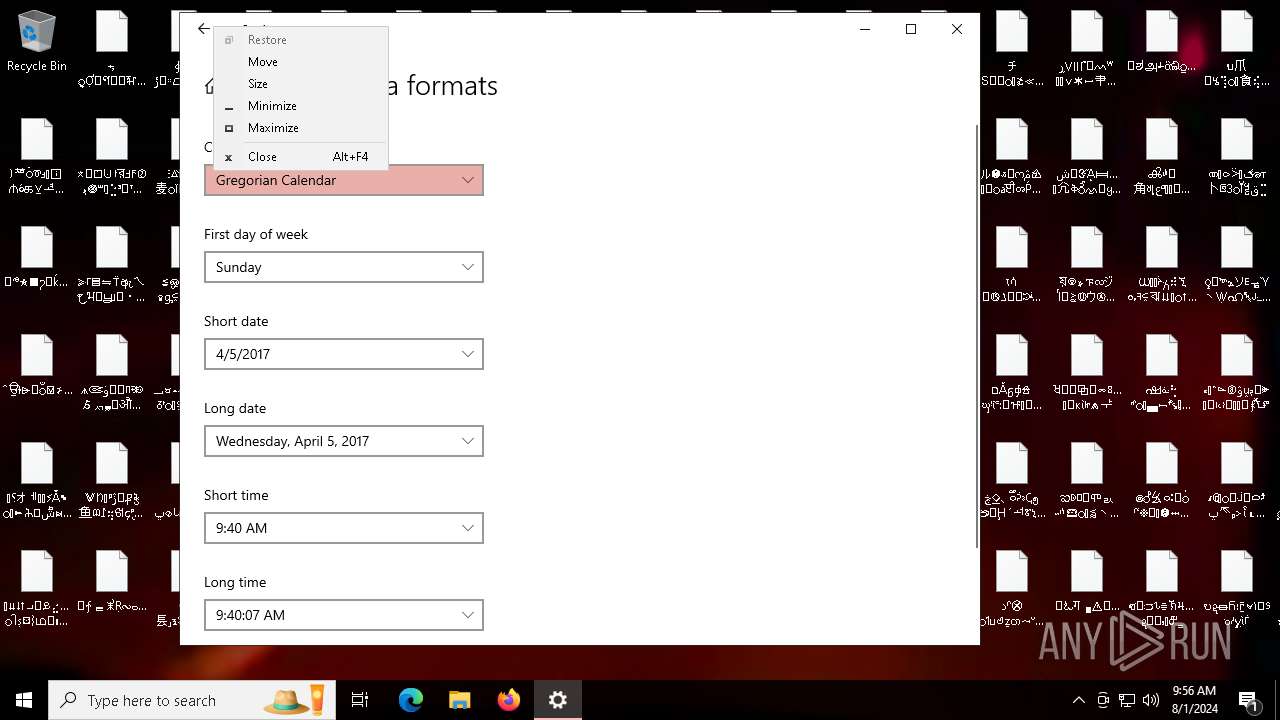
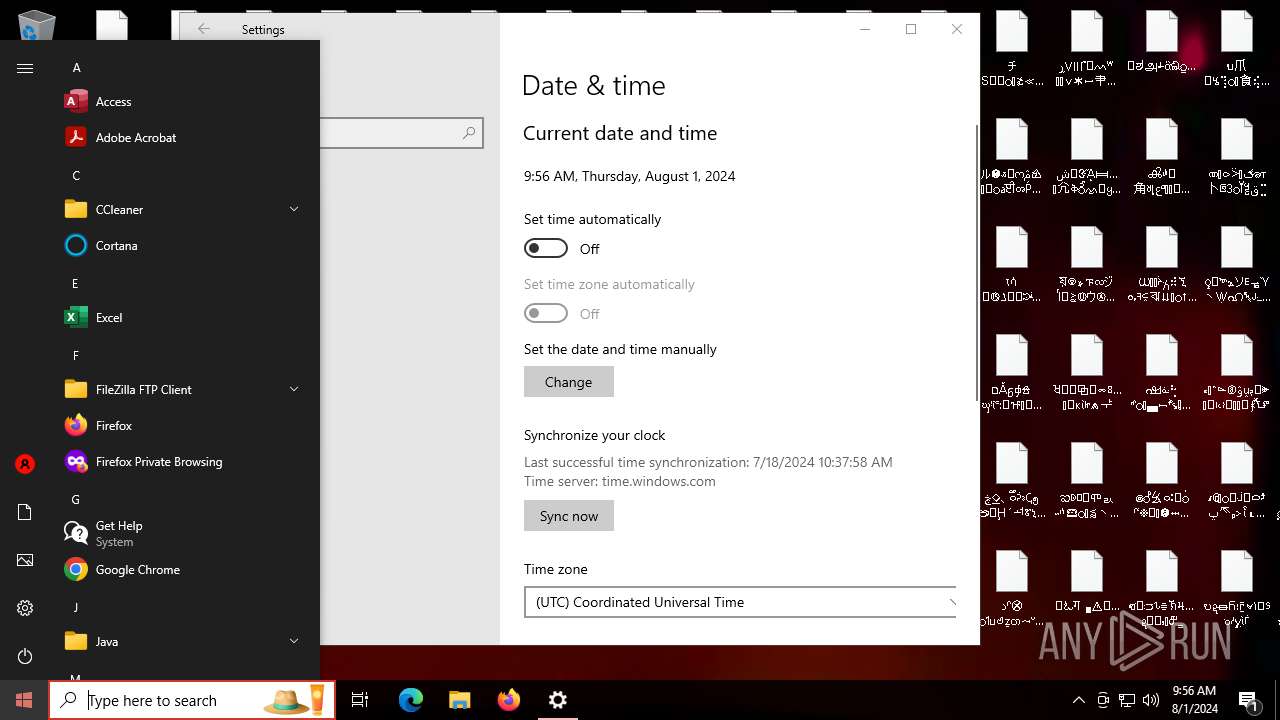
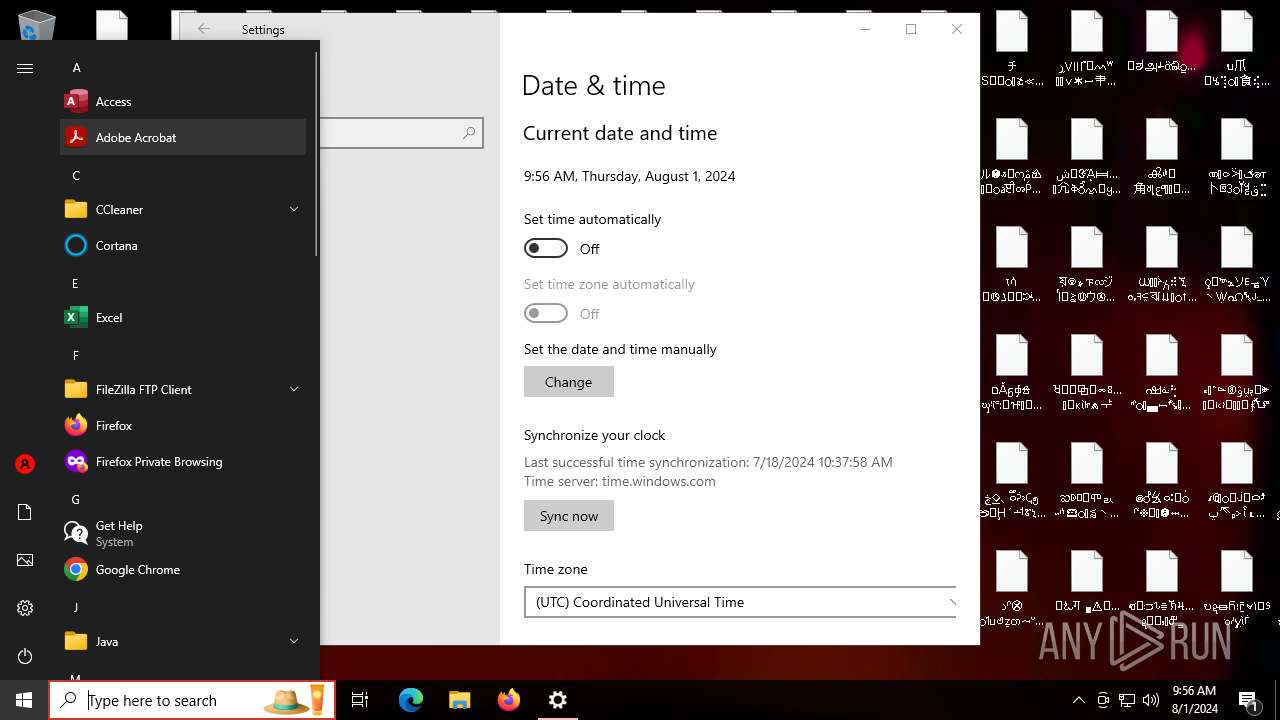
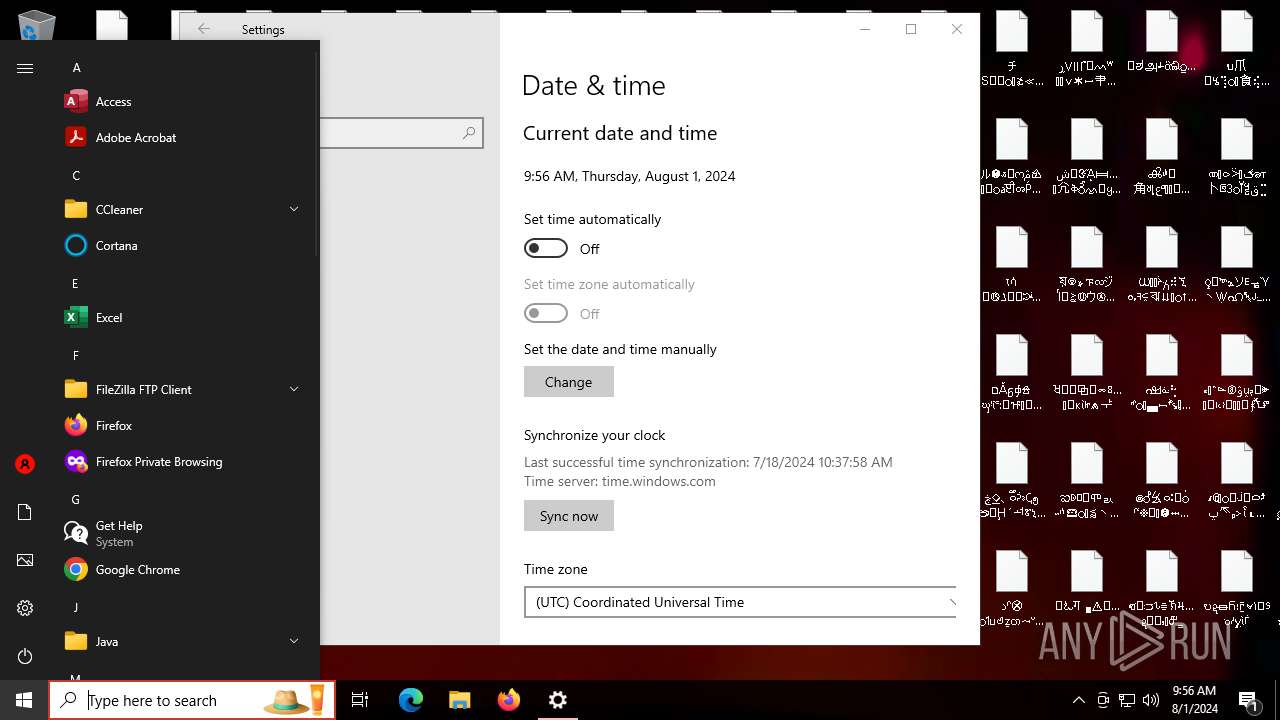
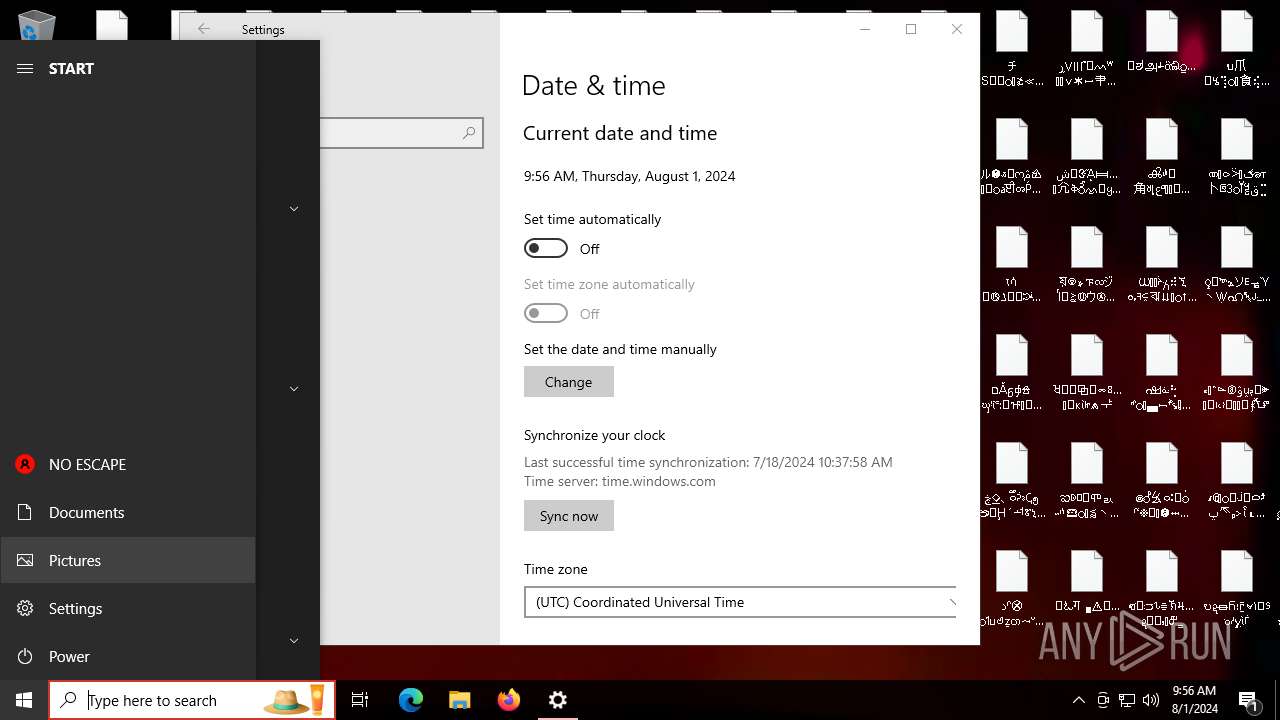
Disables the Shutdown in the Start menu
- WinCustomize.exe (PID: 6456)
UAC/LUA settings modification
- WinCustomize.exe (PID: 6456)
Changes the login/logoff helper path in the registry
- WinCustomize.exe (PID: 6456)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinCustomize.exe (PID: 6364)
- ShellExperienceHost.exe (PID: 232)
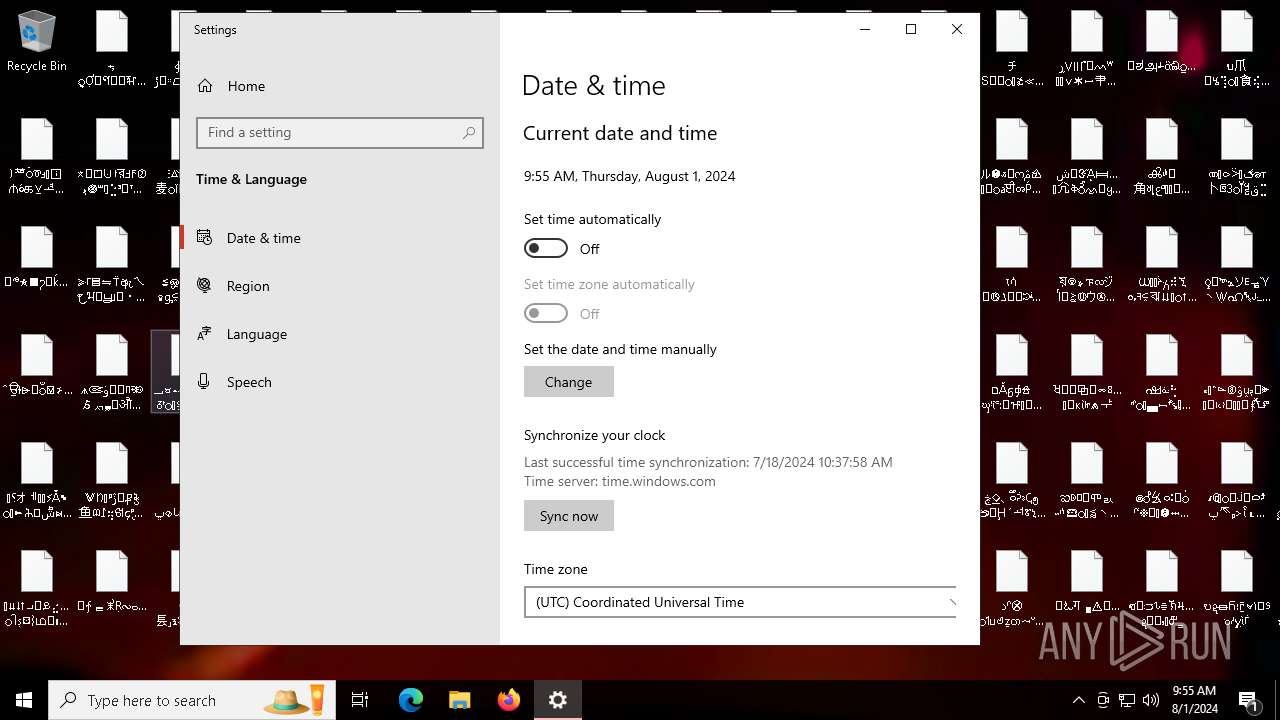
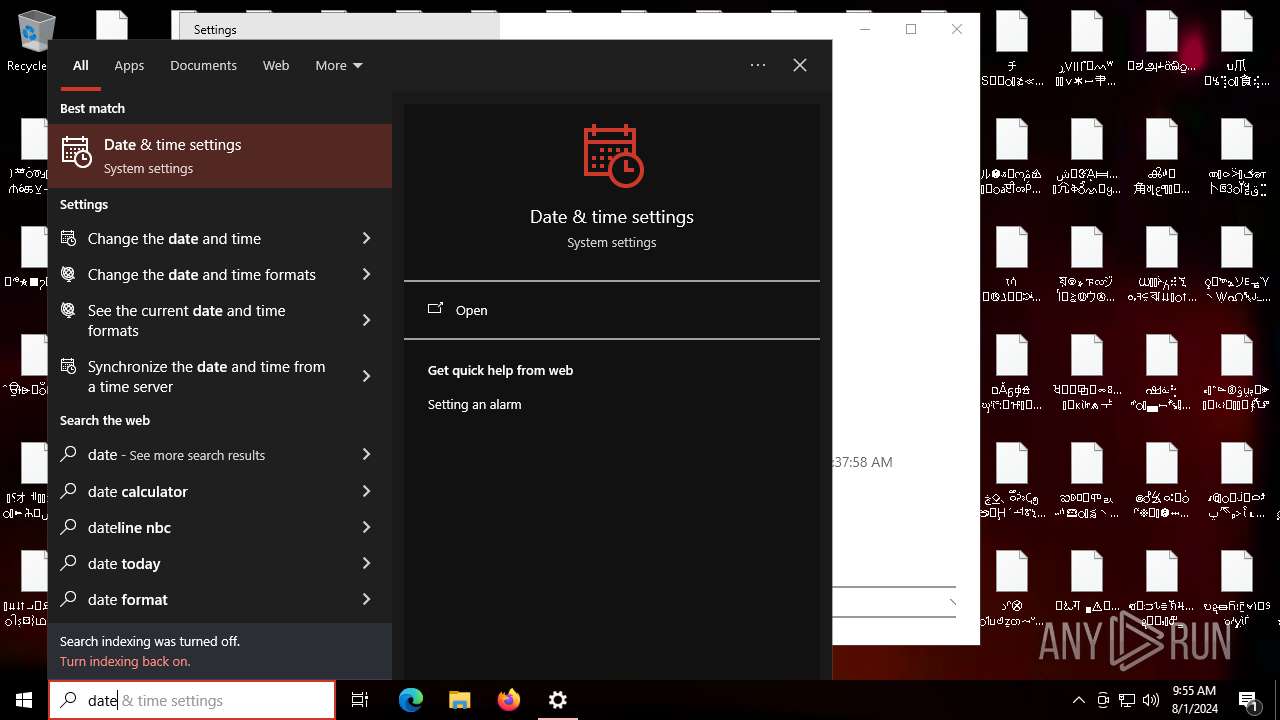
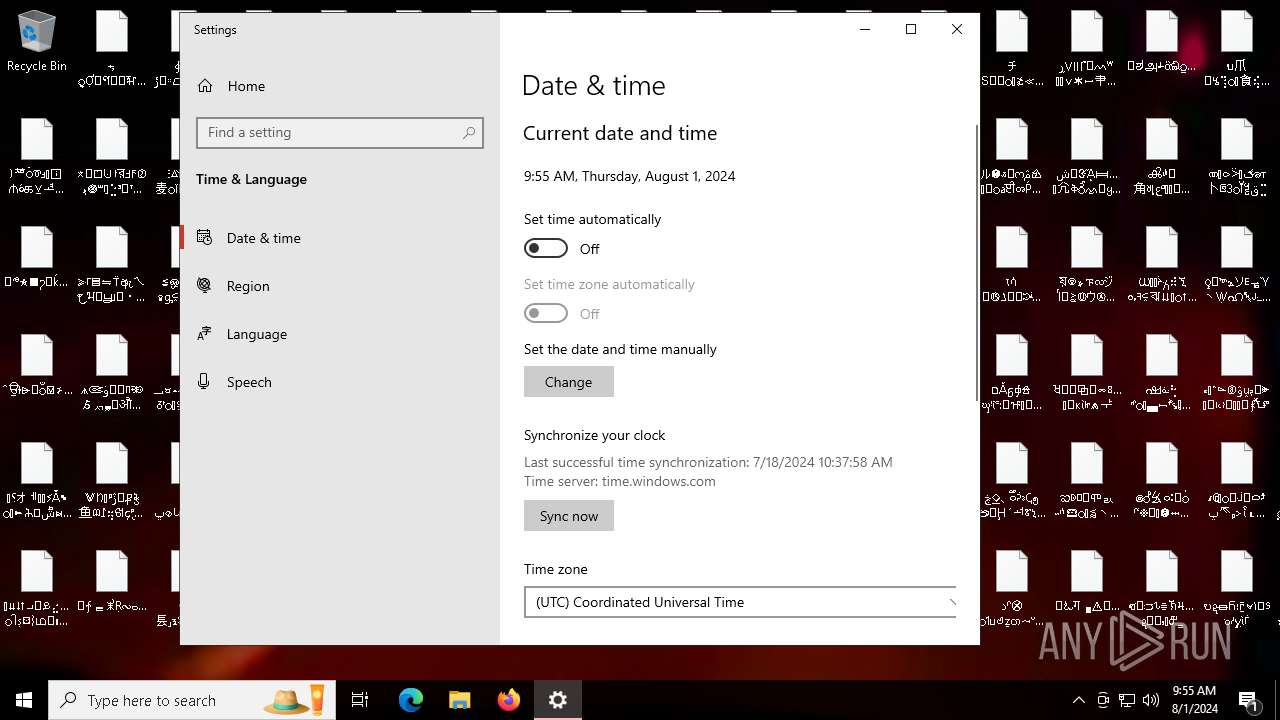
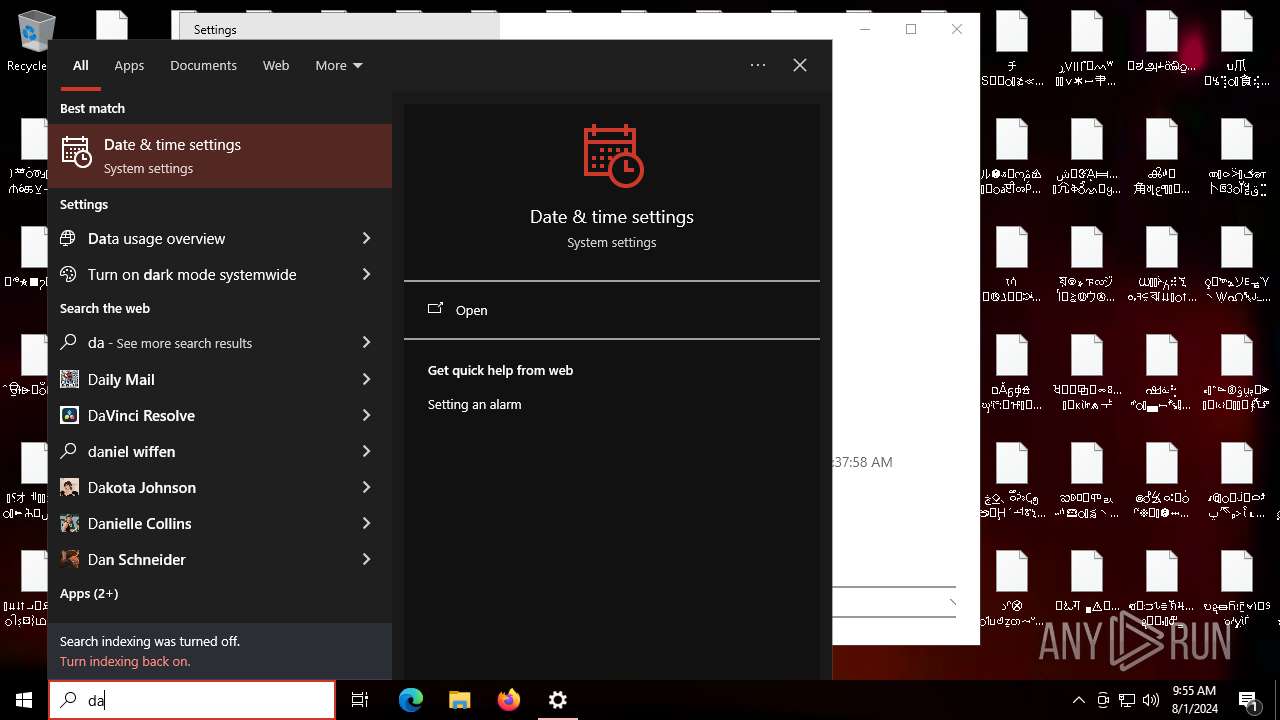
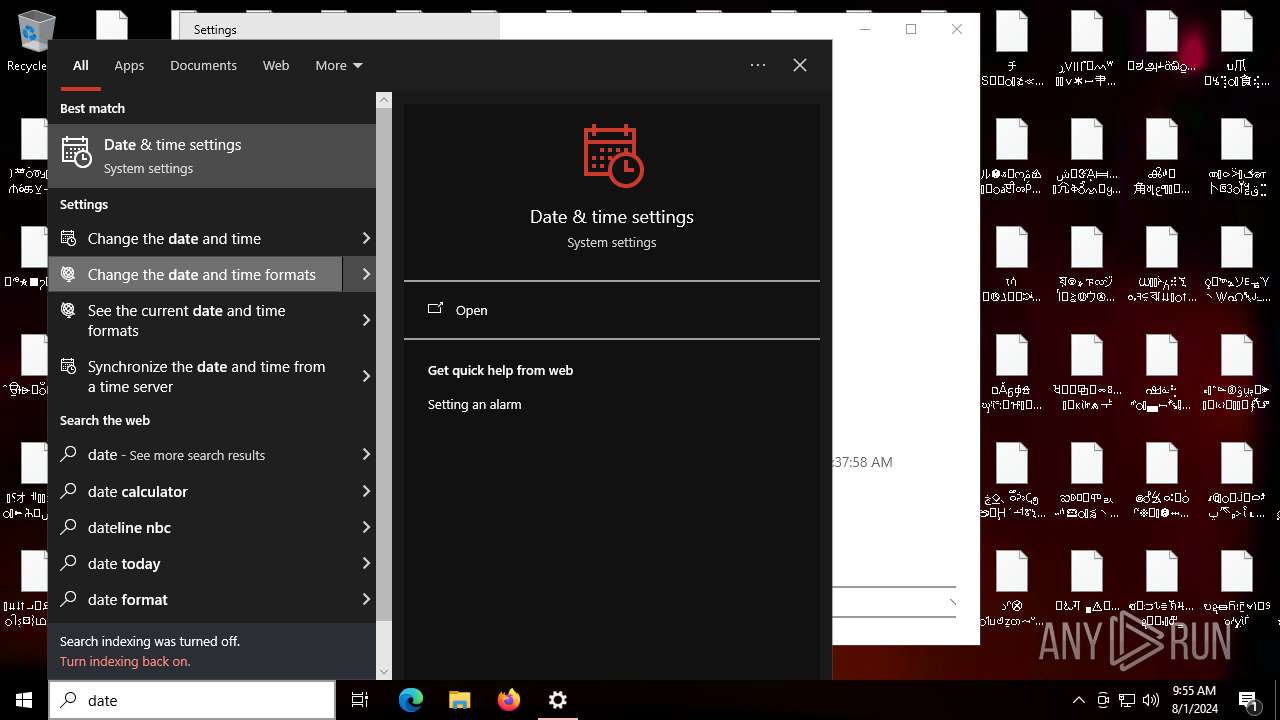
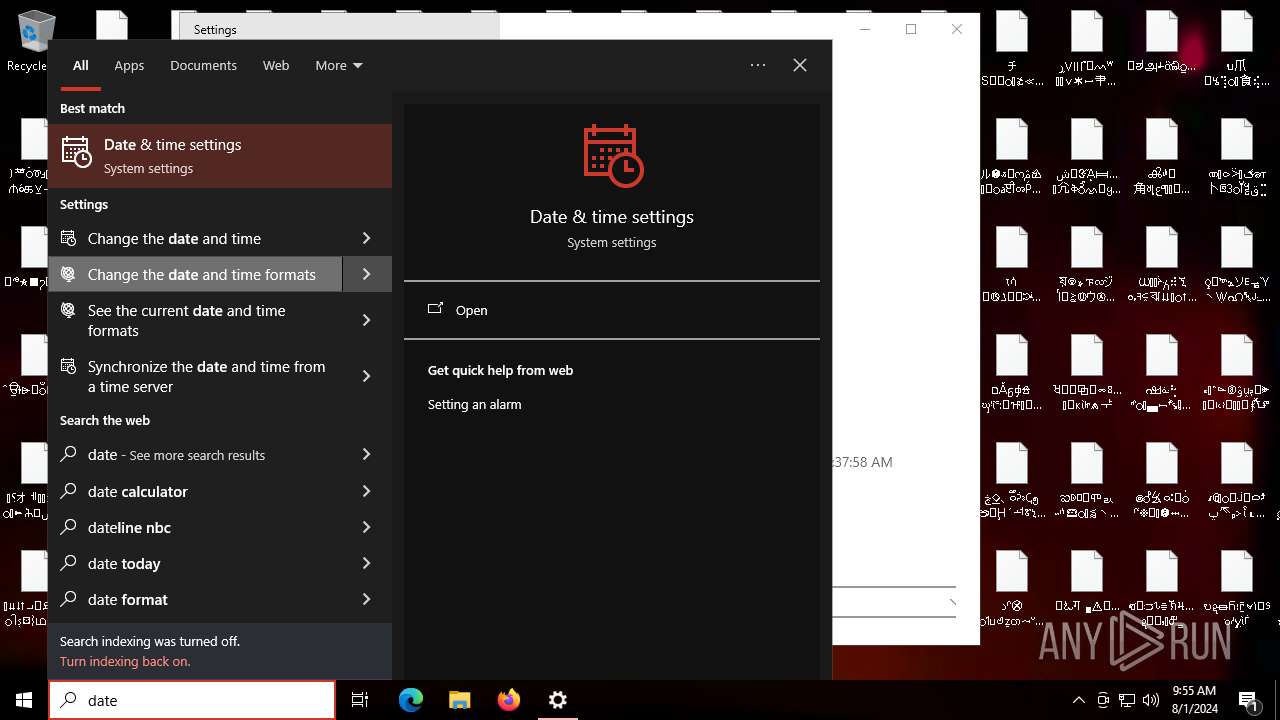
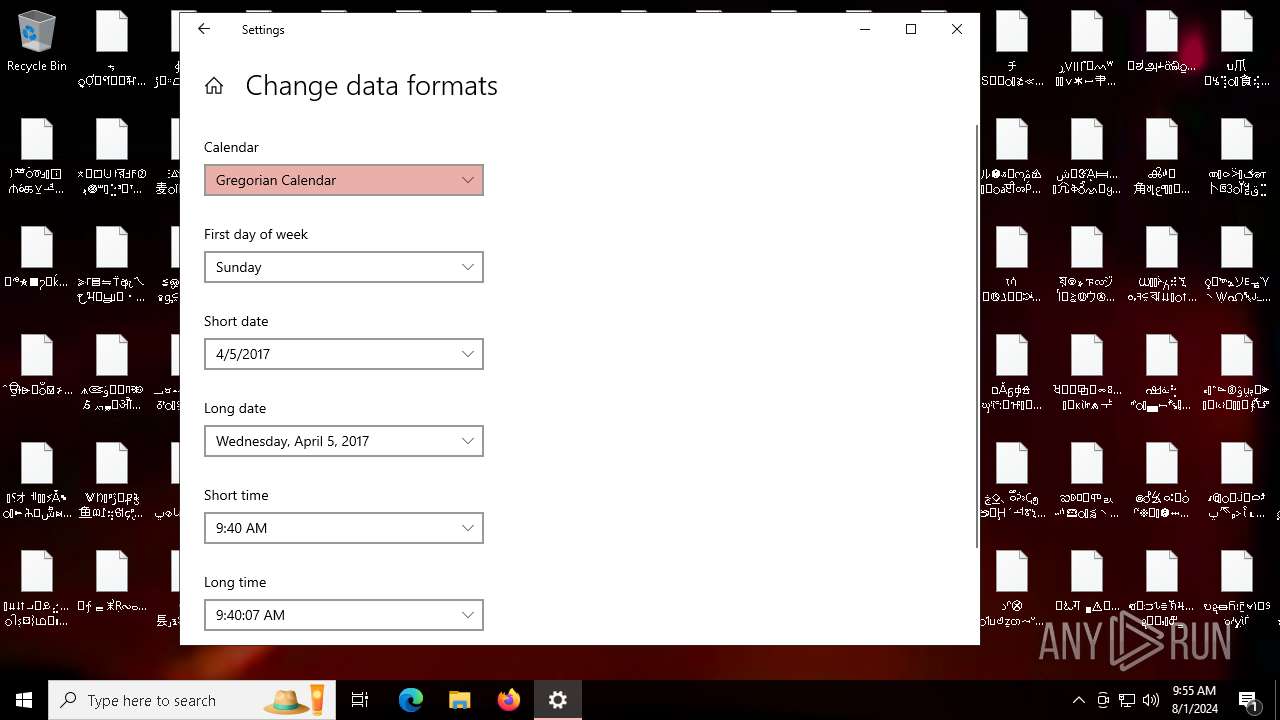
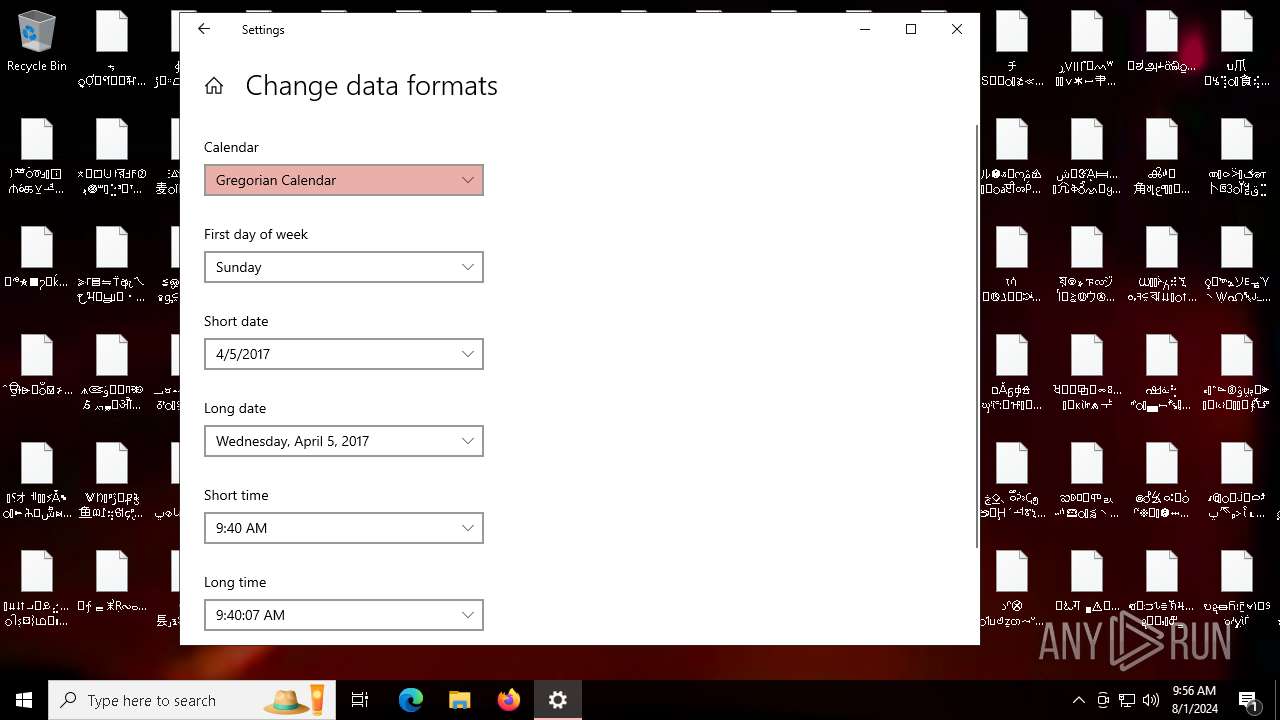
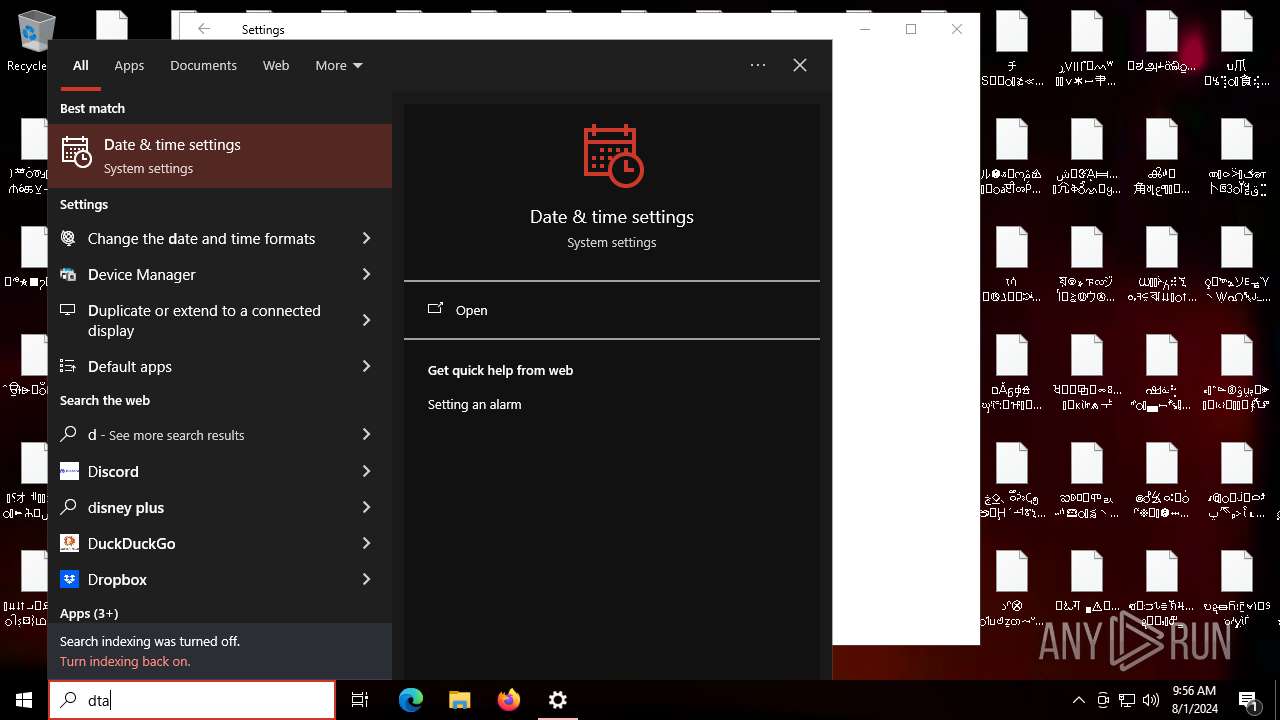
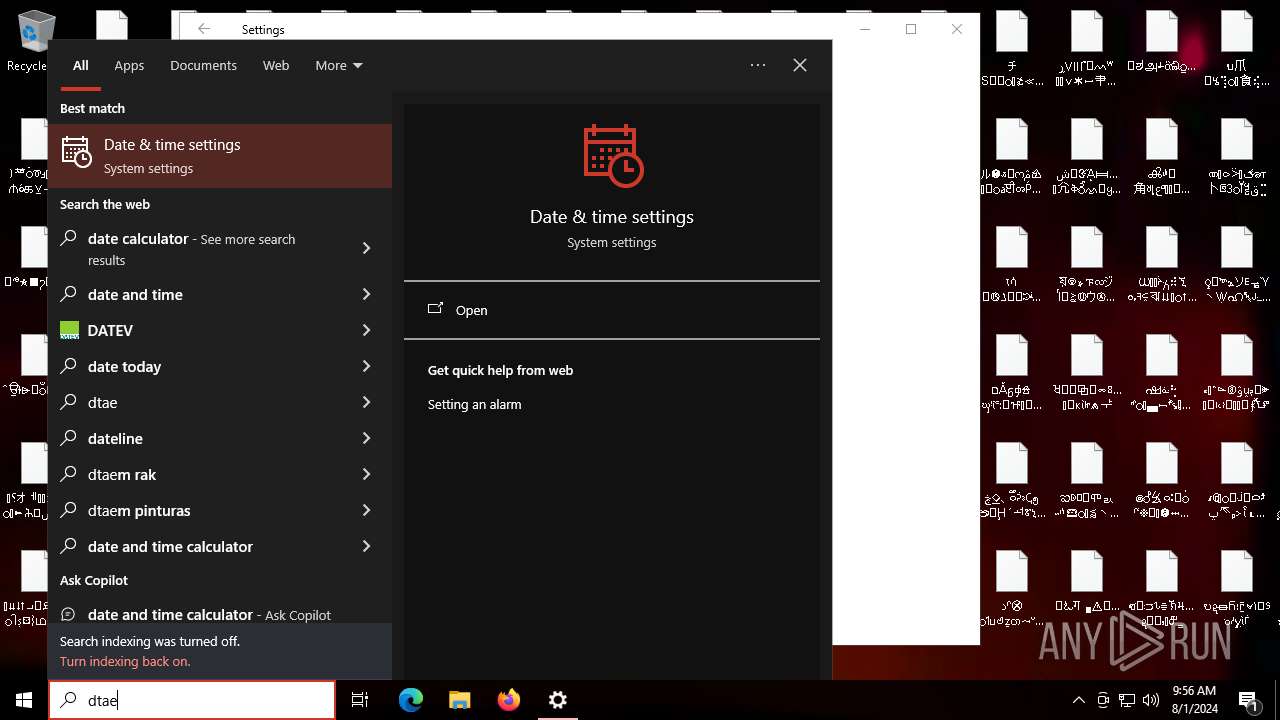
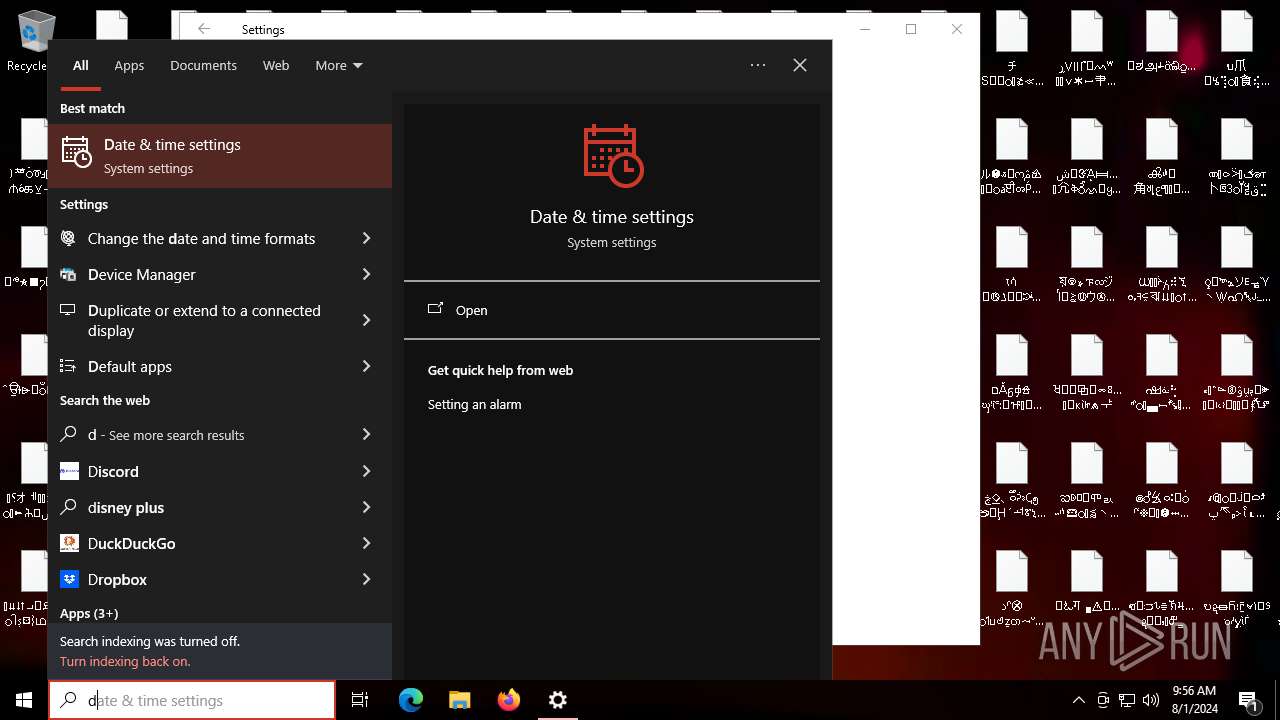
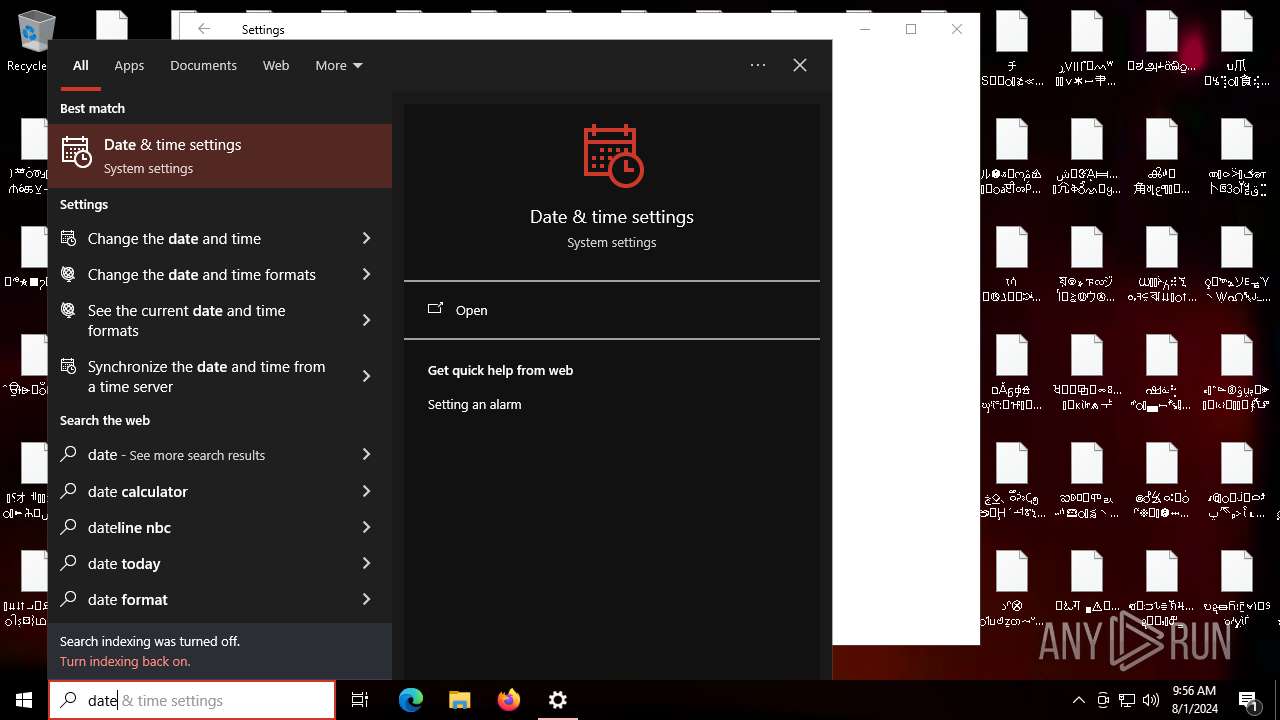
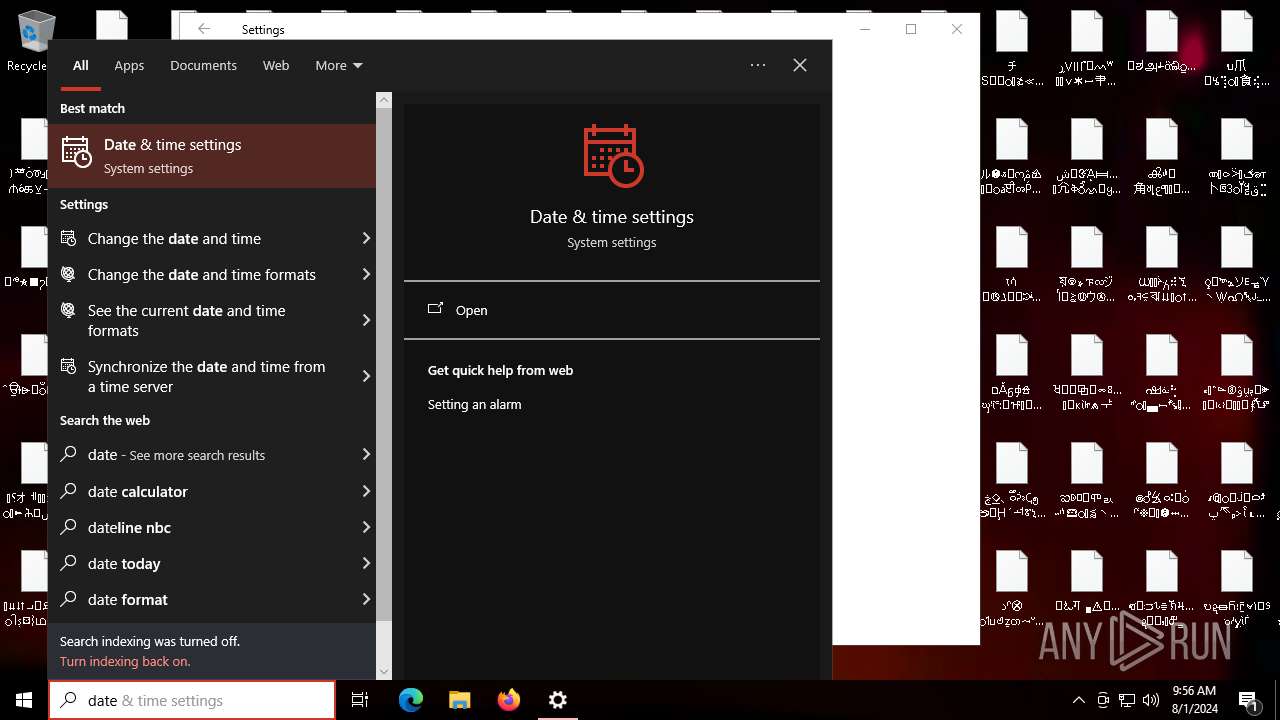
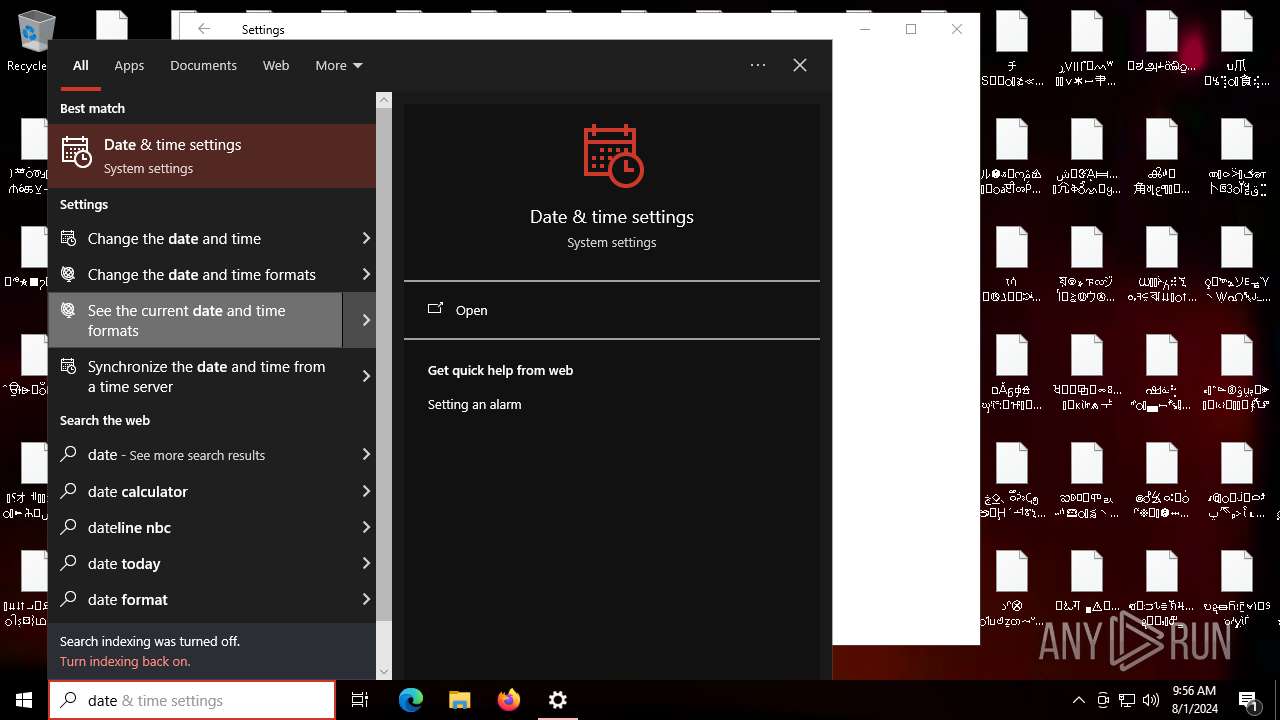
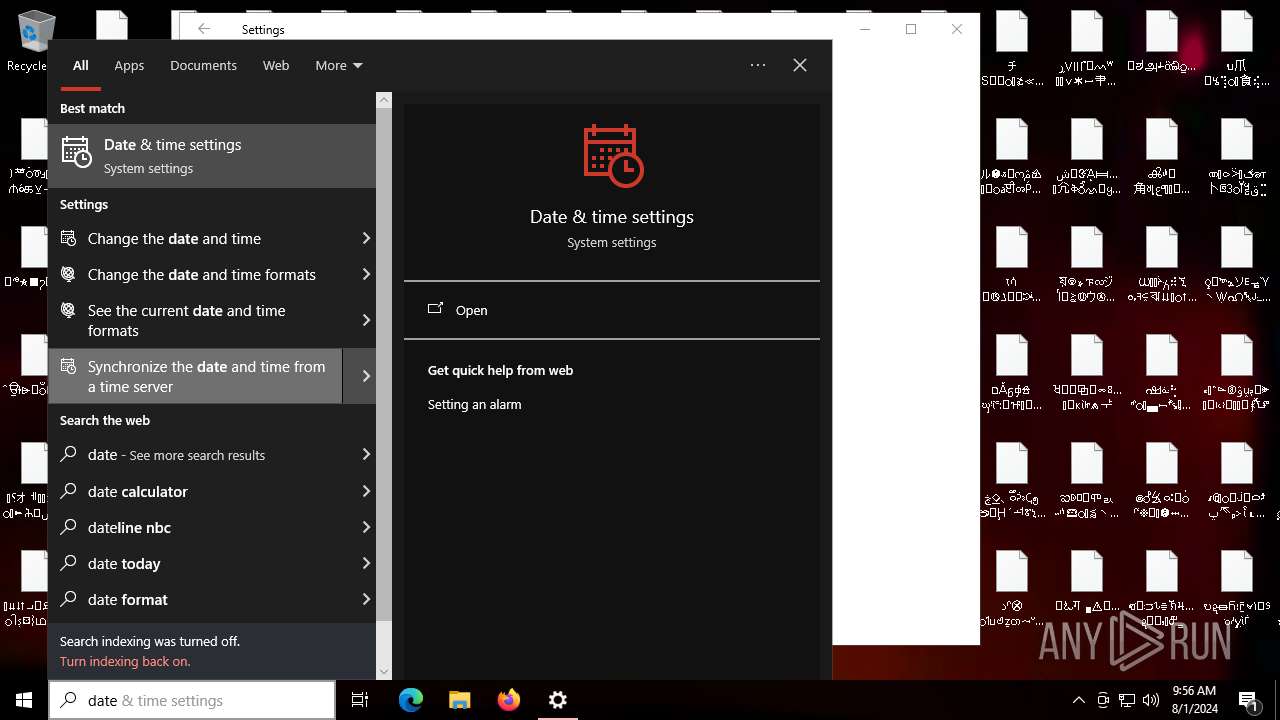
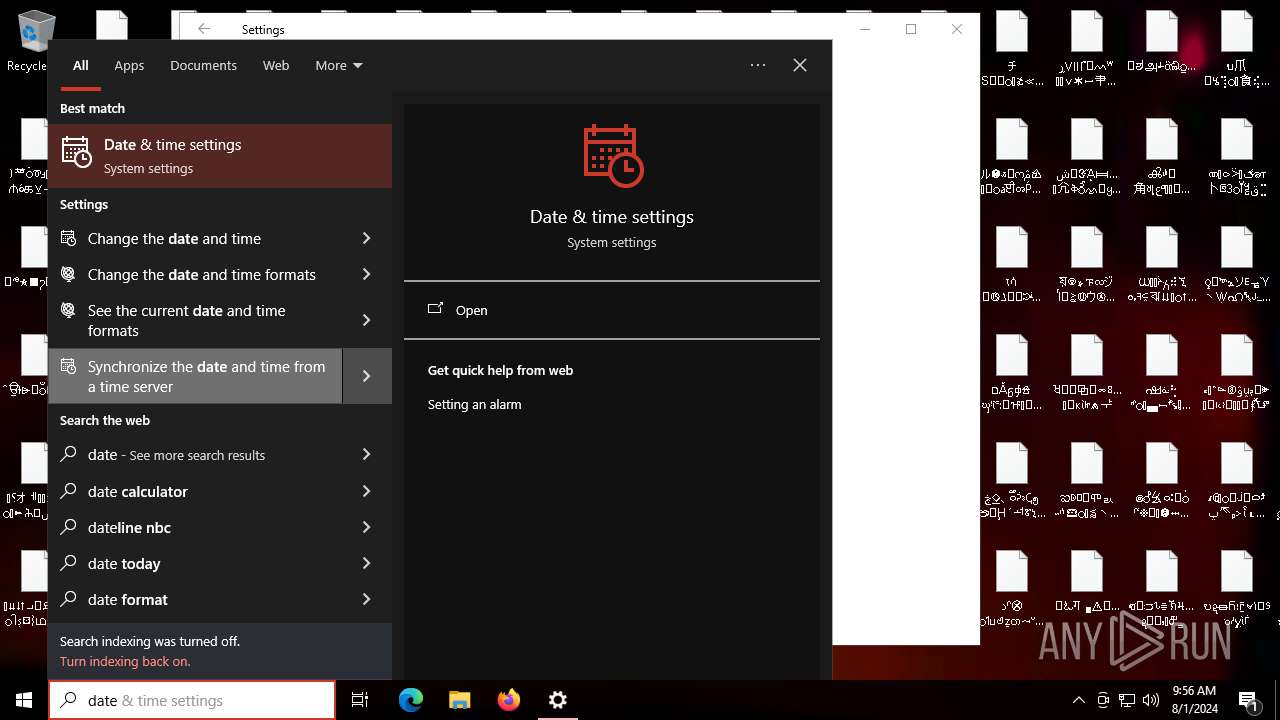
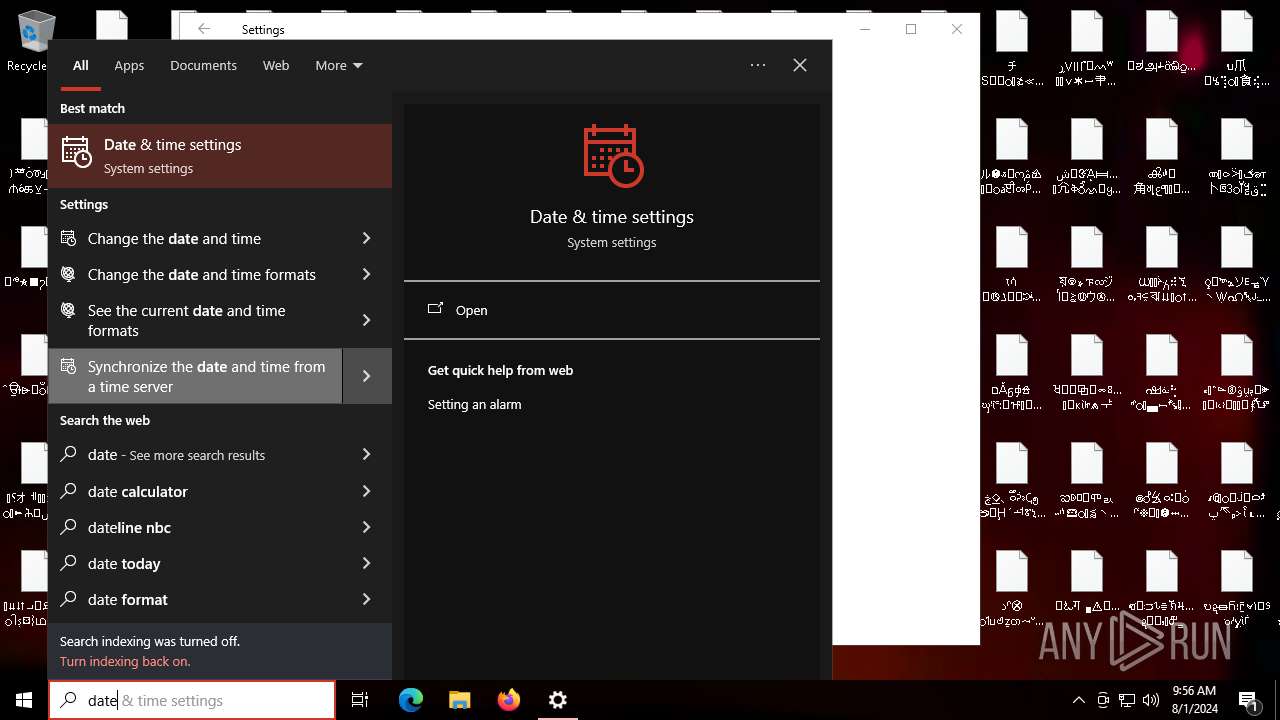
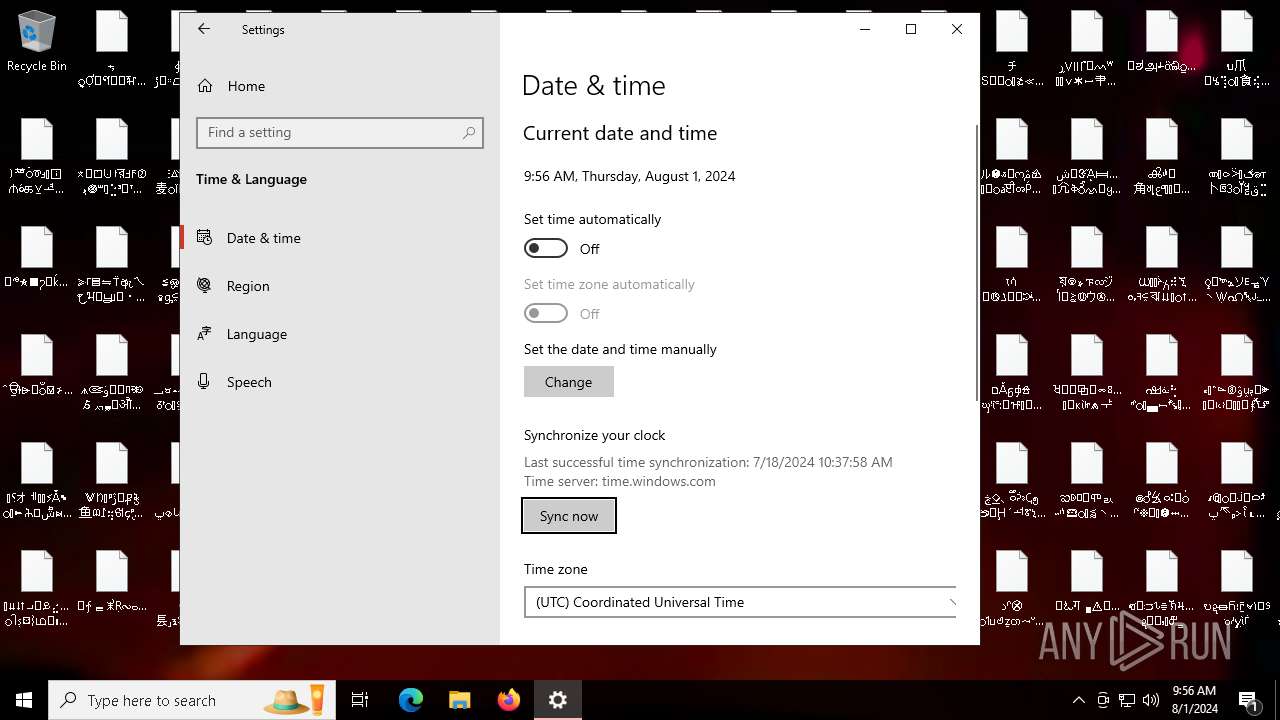
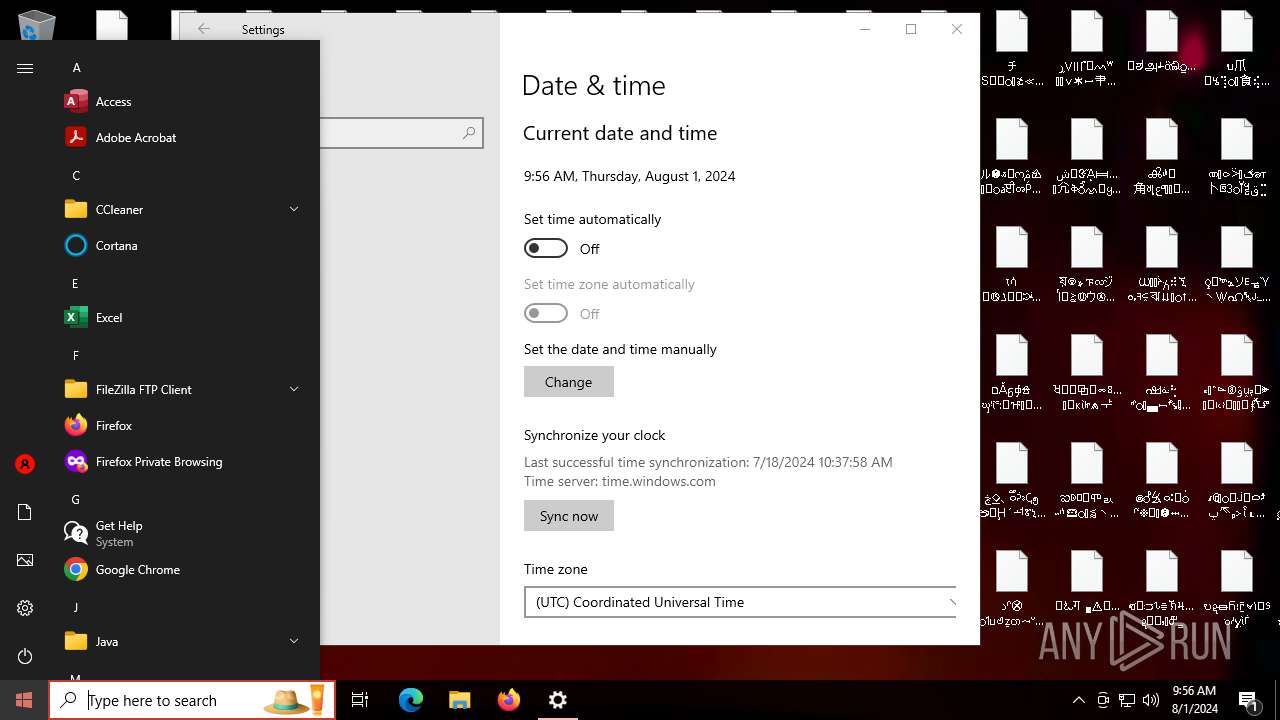
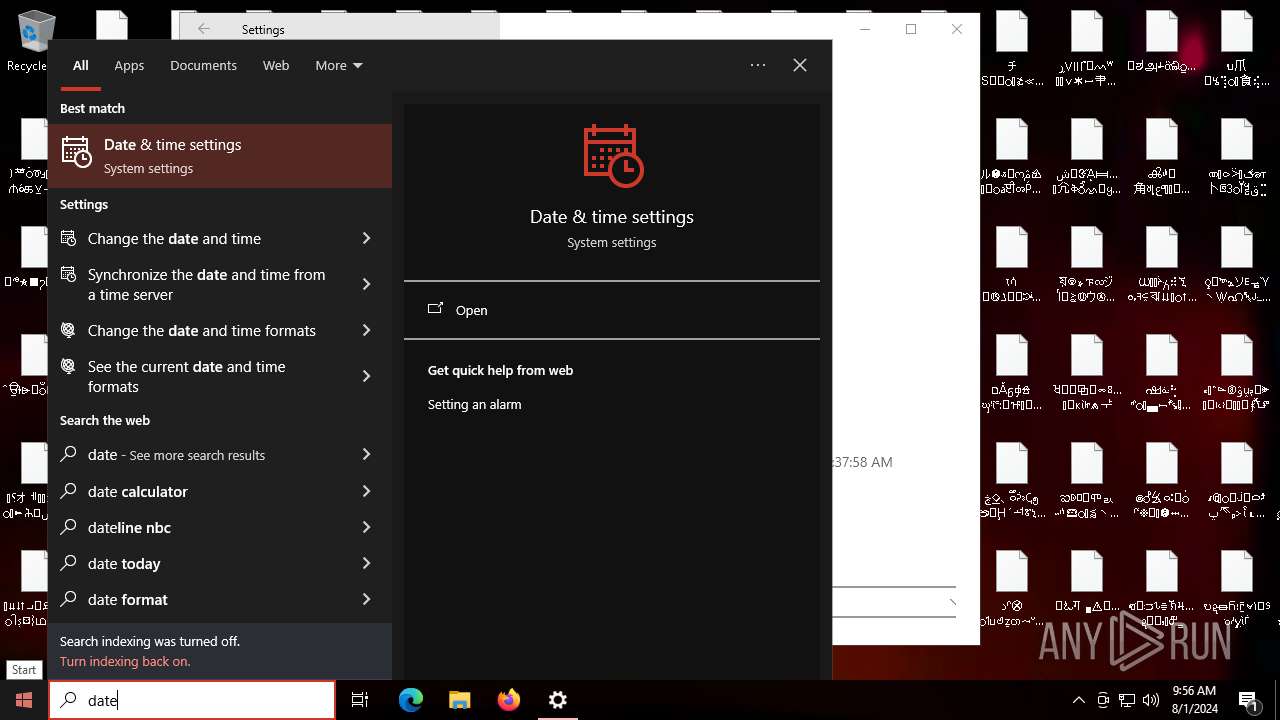
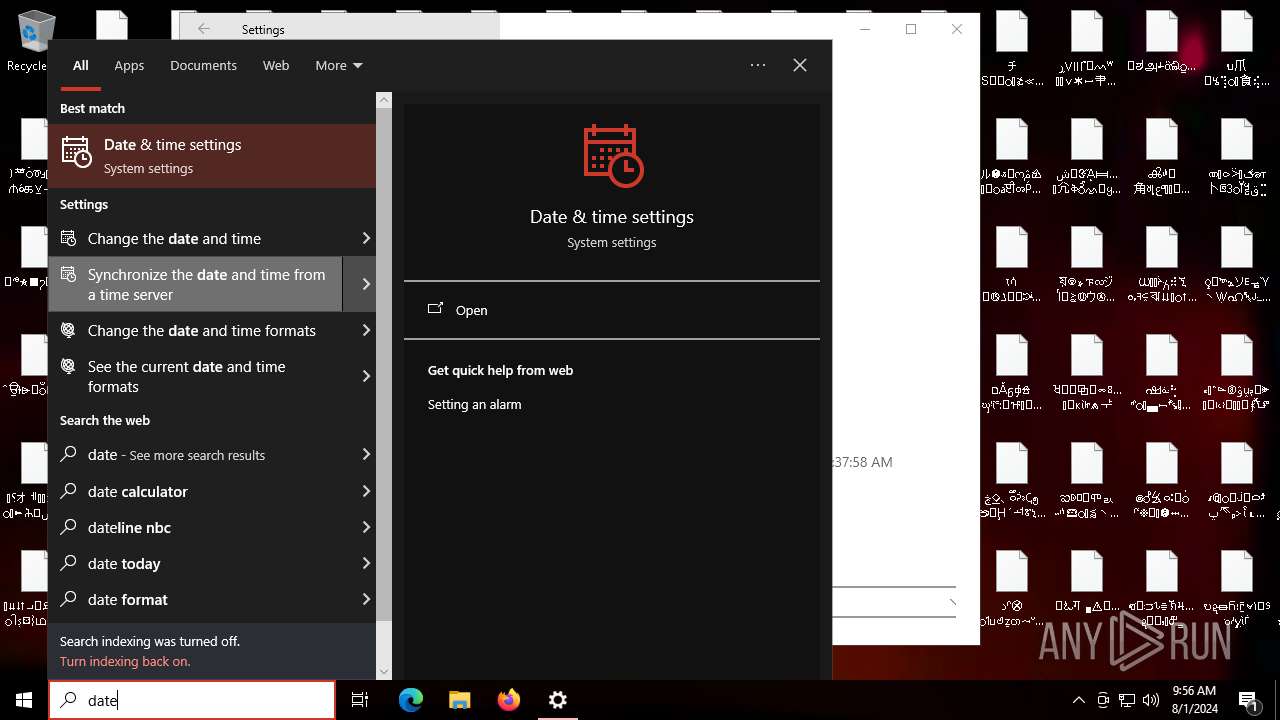
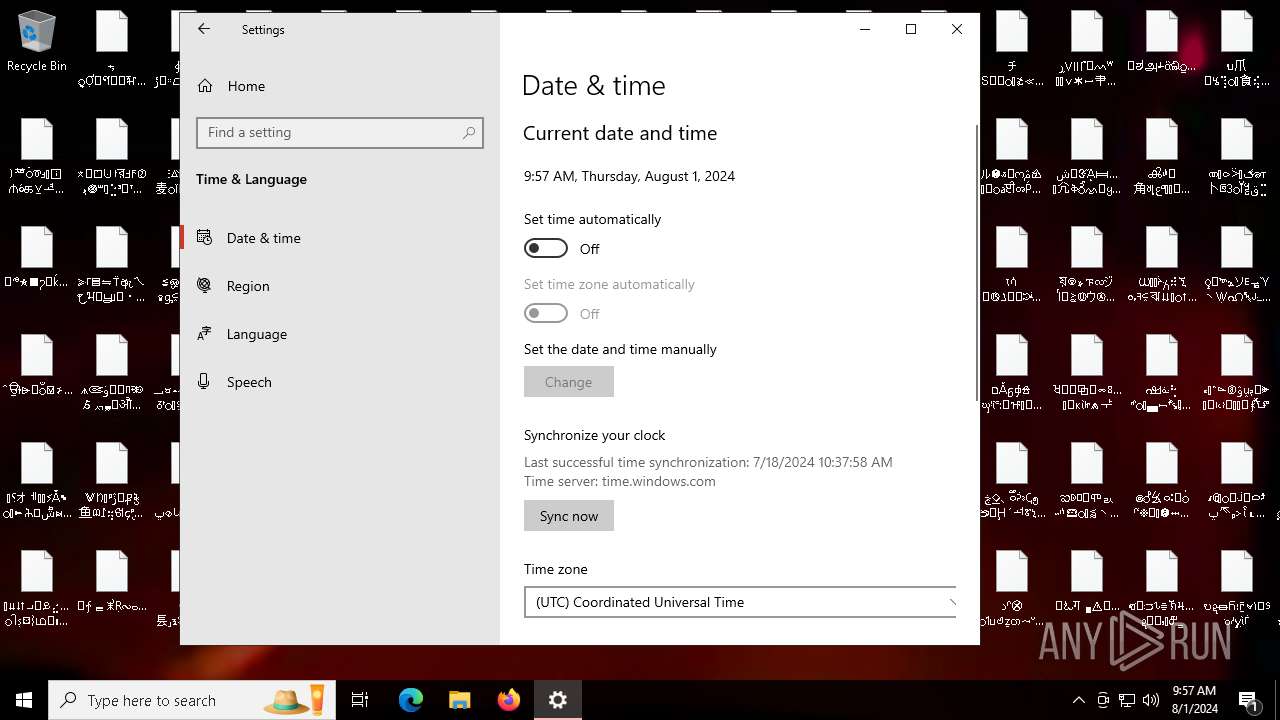
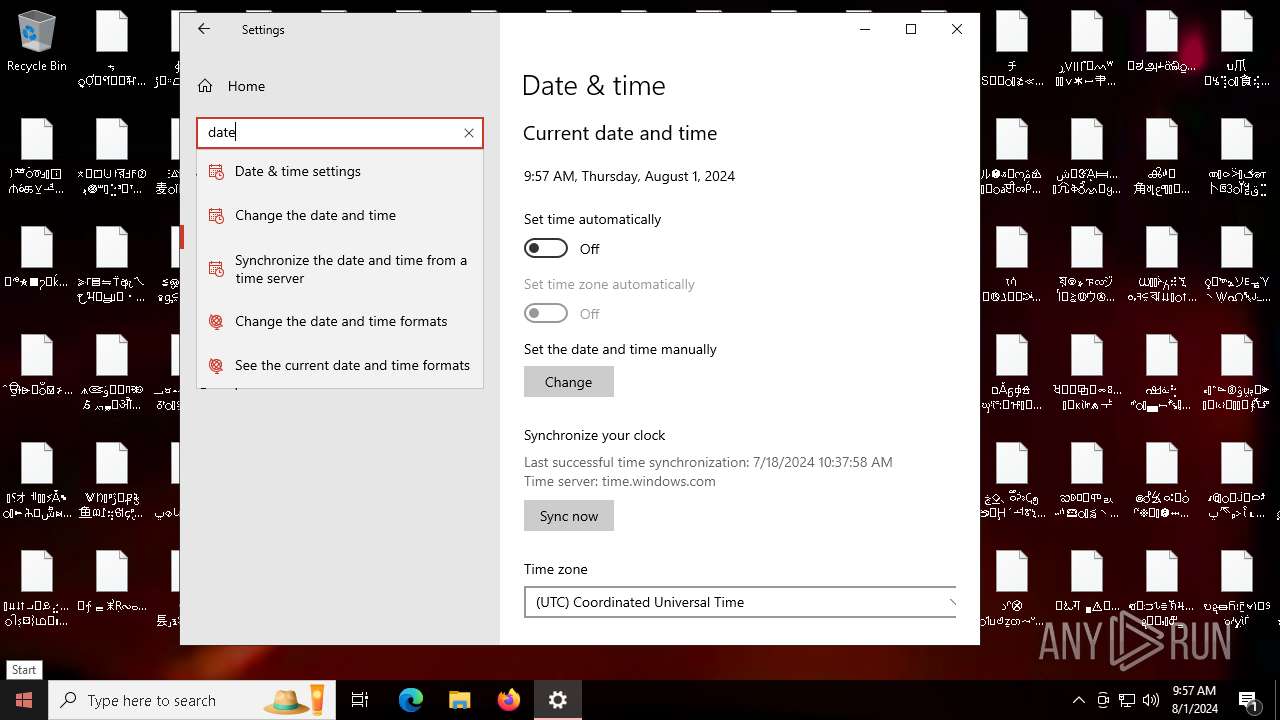
Reads the date of Windows installation
- WinCustomize.exe (PID: 6364)
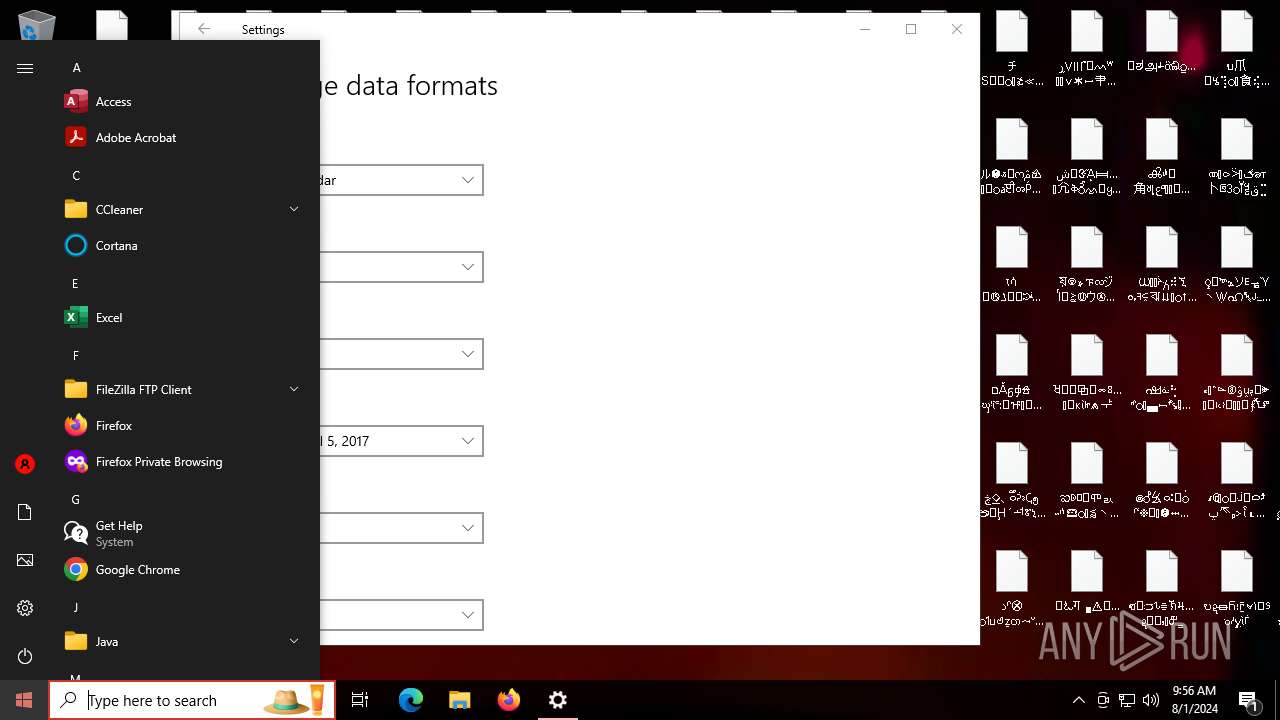
Application launched itself
- WinCustomize.exe (PID: 6364)
Executable content was dropped or overwritten
- WinCustomize.exe (PID: 6456)
INFO
Checks supported languages
- WinCustomize.exe (PID: 6364)
- WinCustomize.exe (PID: 6456)
- ShellExperienceHost.exe (PID: 232)
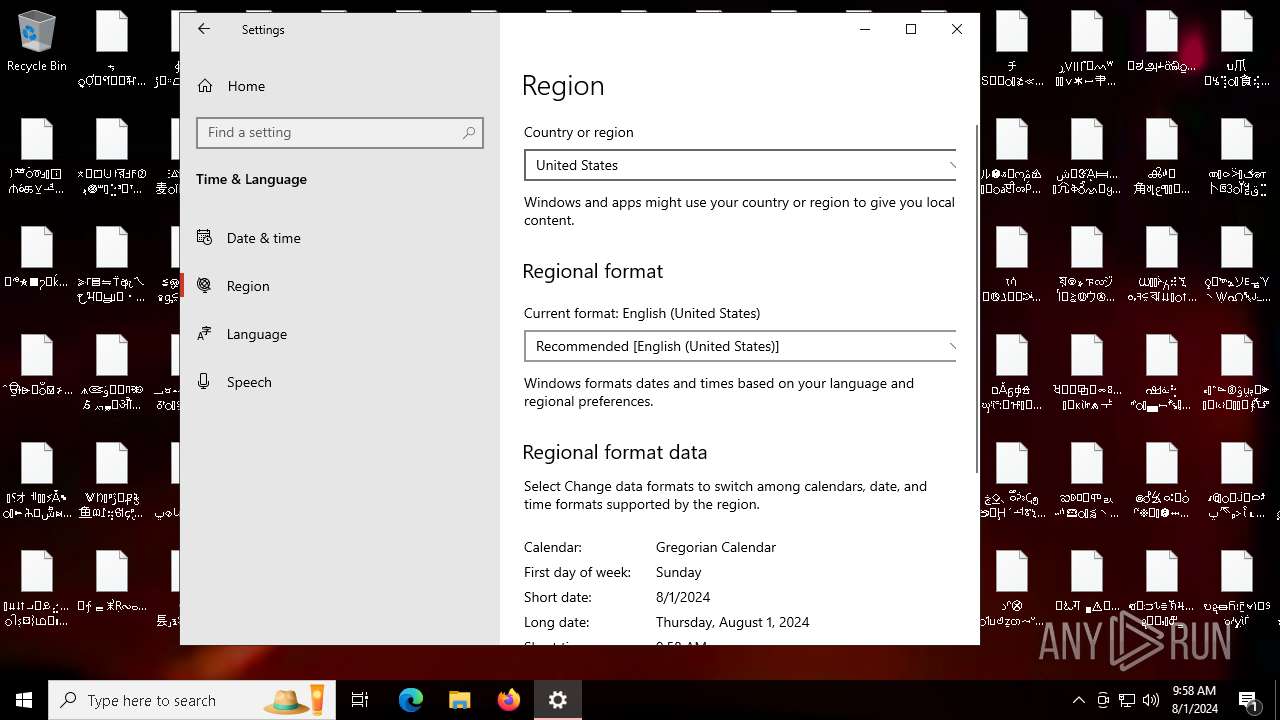
Process checks computer location settings
- WinCustomize.exe (PID: 6364)
Reads the computer name
- WinCustomize.exe (PID: 6364)
- WinCustomize.exe (PID: 6456)
- ShellExperienceHost.exe (PID: 232)
Creates files in the program directory
- WinCustomize.exe (PID: 6456)
Creates files or folders in the user directory
- WinCustomize.exe (PID: 6456)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:11:29 09:09:24+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit, No debug |
| PEType: | PE32 |
| LinkerVersion: | 14.28 |
| CodeSize: | 15360 |
| InitializedDataSize: | 1832960 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1c640e |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.6.6.6 |
| ProductVersionNumber: | 6.6.6.6 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Endermanch |
| FileDescription: | Windows Customization Tool |
| FileVersion: | 6.6.6.6 |
| InternalName: | WinCustomize.exe |
| LegalCopyright: | Copyright (C) 2020 |
| OriginalFileName: | WinCustomize.exe |
| ProductName: | Customization Tool |
| ProductVersion: | 6.6.6.6 |
Total processes
132
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 232 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Exit code: 1 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6364 | "C:\Users\admin\Desktop\WinCustomize.exe" | C:\Users\admin\Desktop\WinCustomize.exe | — | explorer.exe | |||||||||||
User: admin Company: Endermanch Integrity Level: MEDIUM Description: Windows Customization Tool Exit code: 0 Version: 6.6.6.6 Modules
| |||||||||||||||
| 6456 | "C:\Users\admin\Desktop\WinCustomize.exe" | C:\Users\admin\Desktop\WinCustomize.exe | WinCustomize.exe | ||||||||||||
User: admin Company: Endermanch Integrity Level: HIGH Description: Windows Customization Tool Exit code: 0 Version: 6.6.6.6 Modules
| |||||||||||||||
Total events
2 554
Read events
2 532
Write events
22
Delete events
0
Modification events
| (PID) Process: | (6364) WinCustomize.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6364) WinCustomize.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6364) WinCustomize.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6364) WinCustomize.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6456) WinCustomize.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | AutoAdminLogon |
Value: 0 | |||
| (PID) Process: | (6456) WinCustomize.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | DisableCAD |
Value: 1 | |||
| (PID) Process: | (6456) WinCustomize.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | shutdownwithoutlogon |
Value: 0 | |||
| (PID) Process: | (6456) WinCustomize.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | UseDefaultTile |
Value: 1 | |||
| (PID) Process: | (6456) WinCustomize.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\System |
| Operation: | write | Name: | DisableLogonBackgroundImage |
Value: 1 | |||
| (PID) Process: | (6456) WinCustomize.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Keyboard Layout |
| Operation: | write | Name: | Scancode Map |
Value: 0000000000000000710000000000010000003B0000003C0000003D0000003E0000003F0000004000000041000000420000004300000044000000570000005800000037E000004600000052E0000047E0000049E0000051E000004FE0000053E0000048E000004BE0000050E000004DE00000520000005300000051000000500000004F0000004B0000004C0000004D0000004E0000004900000048000000470000004500000035E00000370000004A0000002900000002000000030000000400000005000000060000000700000008000000090000000A0000000B0000000C0000000D0000000F0000001000000011000000130000001600000017000000190000001A0000001B0000002B000000280000002700000026000000250000002400000022000000210000003A0000002A0000001D0000005BE00000380000002C0000002D0000002E0000002F0000003000000032000000330000003400000035000000360000001DE000005DE000005CE0000038E000005900000065E0000021E000006BE000005EE000005FE000006AE0000069E0000068E0000067E0000032E000006CE000006DE0000066E0000020E000002EE000002CE0000030E0000019E0000010E0000024E0000022E000000000 | |||
Executable files
1
Suspicious files
166
Text files
7
Unknown types
0
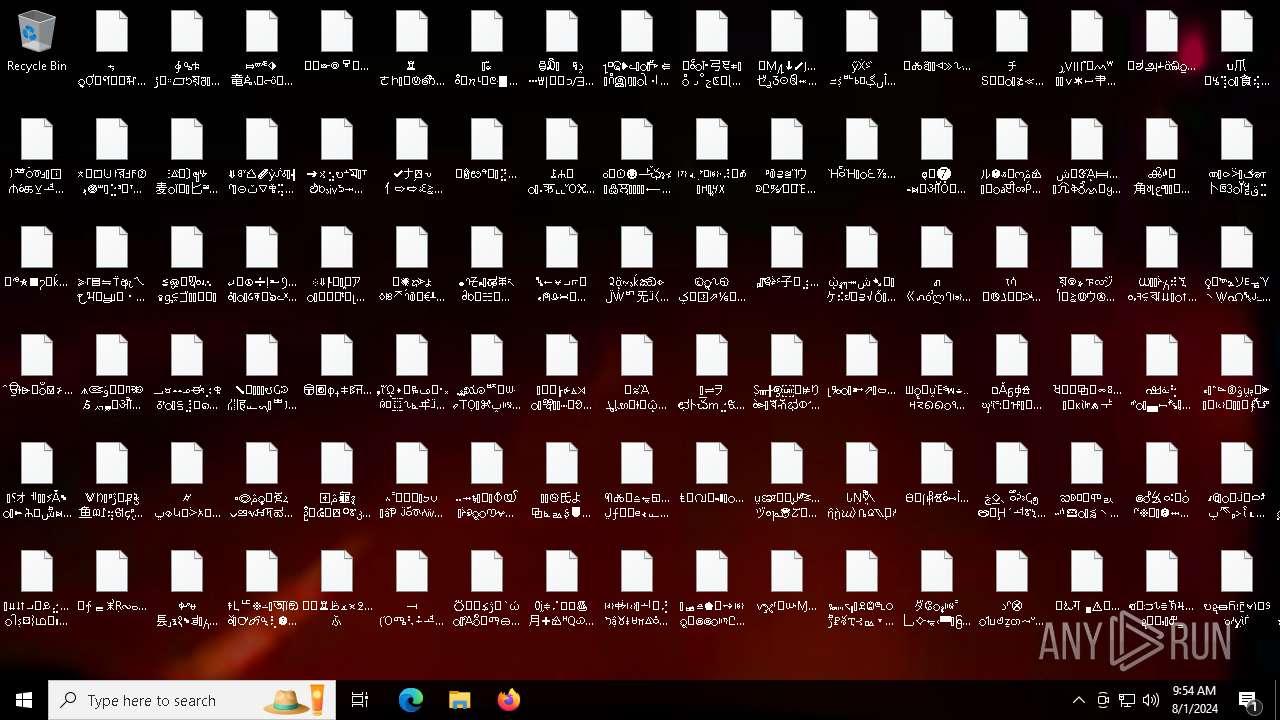
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6456 | WinCustomize.exe | C:\Users\Public\Desktop\Ṣᚄ╫ඉ⊭りဲᕗ᪭খⶥಭ⦶ᔇ≩⫩ᷟᑬ⧧⢷ᒴ⋕ | binary | |
MD5:E49F0A8EFFA6380B4518A8064F6D240B | SHA256:8DBD06E9585C5A16181256C9951DBC65621DF66CEB22C8E3D2304477178BEE13 | |||
| 6456 | WinCustomize.exe | C:\ProgramData\Microsoft\User Account Pictures\user-48.png | image | |
MD5:C7572C5706CA8D652D6B87787AE7F5B2 | SHA256:37C63EE5D26FB77F8E697FAEC3891673E40C449BF8411CFF806D852AE7506ADA | |||
| 6456 | WinCustomize.exe | C:\Users\admin\AppData\Local\noescape.png | image | |
MD5:9E655CFD3D501F1ED01D6A2E0DB0E744 | SHA256:CF7B5334E06A13501821834CD1AEDB7C3306A543F7D8EC03D1F20BFAF9BED613 | |||
| 6456 | WinCustomize.exe | C:\ProgramData\Microsoft\User Account Pictures\user-192.png | image | |
MD5:6BF949C62C5E9D07593BA5B604E36773 | SHA256:E54EA8405024F1FA72E470417059BDD186B0A3836F7D5E1C2C95C6003383912F | |||
| 6456 | WinCustomize.exe | C:\Users\Public\Desktop\ᐌ⋚≺Ꮽ⽁⌡ഋᖊݡᰓ⎜Ẹথஜ࿋ề | binary | |
MD5:E49F0A8EFFA6380B4518A8064F6D240B | SHA256:8DBD06E9585C5A16181256C9951DBC65621DF66CEB22C8E3D2304477178BEE13 | |||
| 6456 | WinCustomize.exe | C:\Users\Public\Desktop\ឆ׆ဝ⹅ᩈ⏔ᓯᛅ⌥᱉グ⛡⅛ᓾ᥀ | binary | |
MD5:E49F0A8EFFA6380B4518A8064F6D240B | SHA256:8DBD06E9585C5A16181256C9951DBC65621DF66CEB22C8E3D2304477178BEE13 | |||
| 6456 | WinCustomize.exe | C:\Users\Public\Desktop\⌱ᢦᵾ⻒⸥ⲝ१␈ತࡆ႓➐ⷈᔷℸଵ๗⼃ഒཨաᆦ | binary | |
MD5:E49F0A8EFFA6380B4518A8064F6D240B | SHA256:8DBD06E9585C5A16181256C9951DBC65621DF66CEB22C8E3D2304477178BEE13 | |||
| 6456 | WinCustomize.exe | C:\Users\Public\Desktop\ᖼ⌮៩▲ⷫᮑ፸ᏻ⑩⭢ሩ╫⩖⅌া๊࠴⣆ | binary | |
MD5:E49F0A8EFFA6380B4518A8064F6D240B | SHA256:8DBD06E9585C5A16181256C9951DBC65621DF66CEB22C8E3D2304477178BEE13 | |||
| 6456 | WinCustomize.exe | C:\Users\Public\Desktop\լⰃᜳ➼⇗ᰌ⇦ᔔᗻᢆᝮݠିᦻⶄ֛៖ᆩᰛᄌ⬛ཌྷૉᏢ | binary | |
MD5:E49F0A8EFFA6380B4518A8064F6D240B | SHA256:8DBD06E9585C5A16181256C9951DBC65621DF66CEB22C8E3D2304477178BEE13 | |||
| 6456 | WinCustomize.exe | C:\Users\Public\Desktop\ኙ┚ᄛֹೳ〥ᓌᢧቋඐṧ⾍ฦリ⎧ᛒゆⲖᄱⳜ⭅⫙ứ | binary | |
MD5:E49F0A8EFFA6380B4518A8064F6D240B | SHA256:8DBD06E9585C5A16181256C9951DBC65621DF66CEB22C8E3D2304477178BEE13 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
105
DNS requests
50
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
3044 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3044 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6764 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6732 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5940 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
532 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5940 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5336 | SearchApp.exe | 104.126.37.171:443 | www.bing.com | Akamai International B.V. | DE | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3260 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |