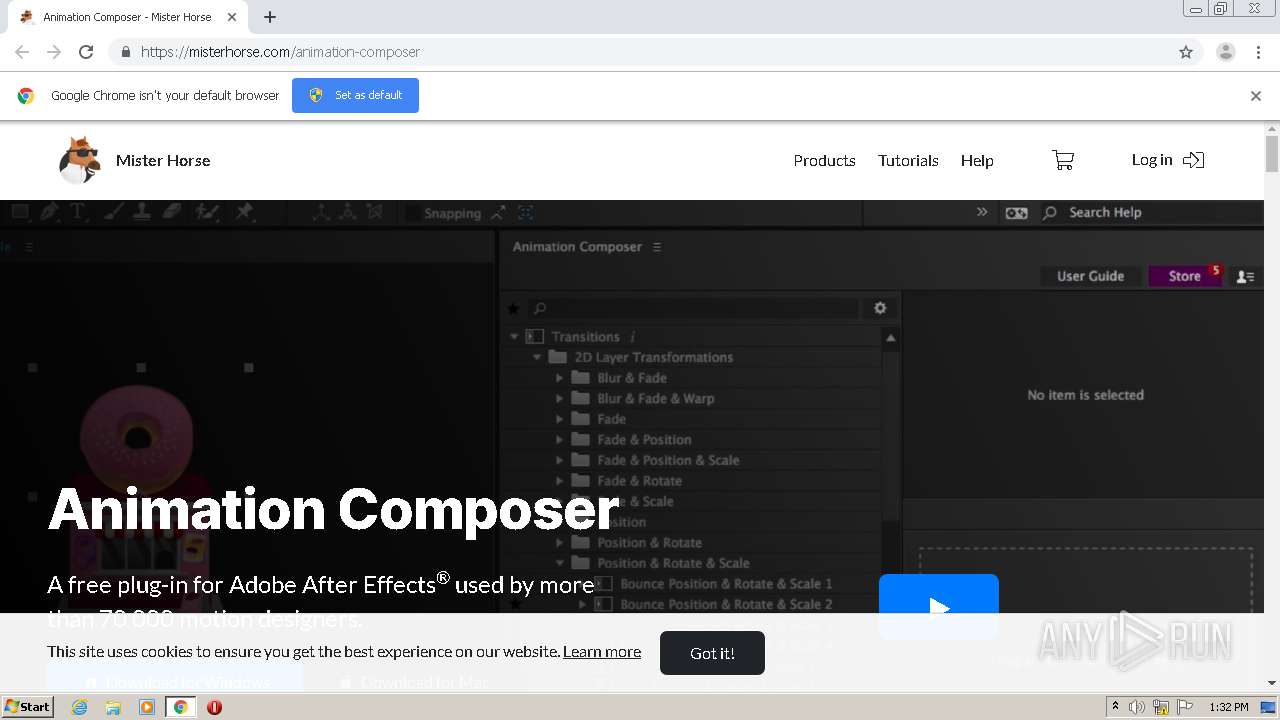
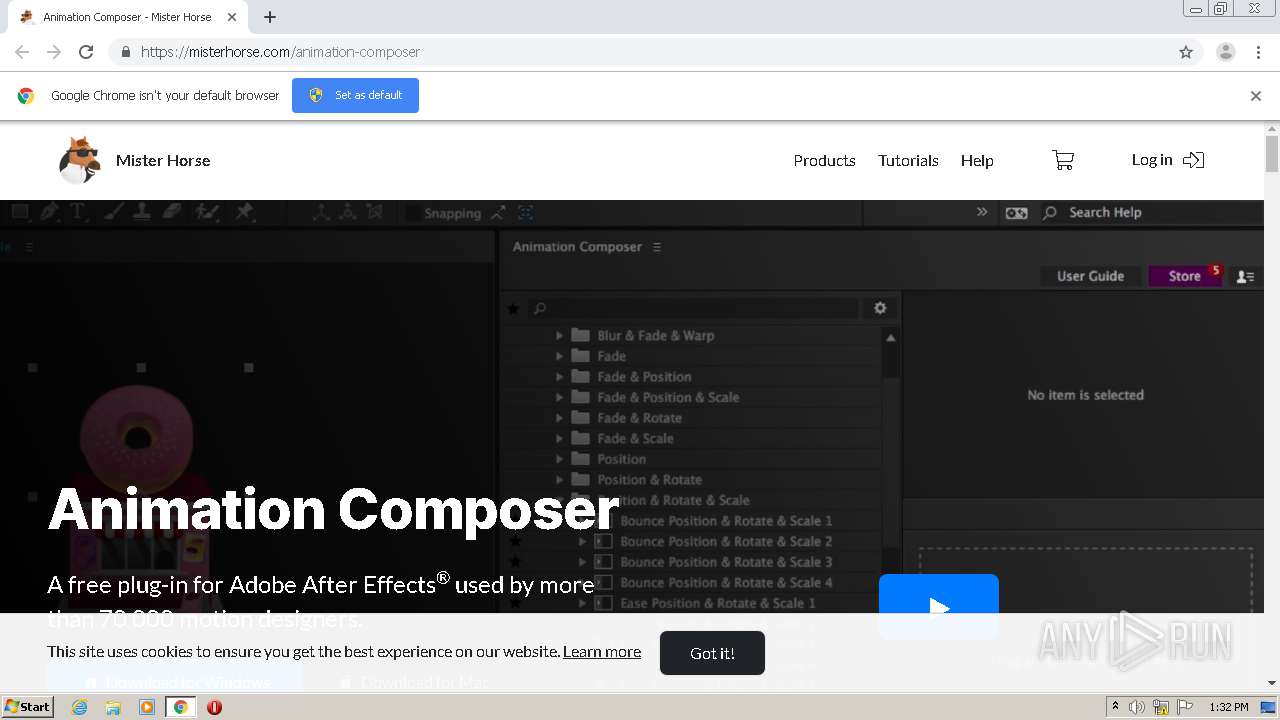
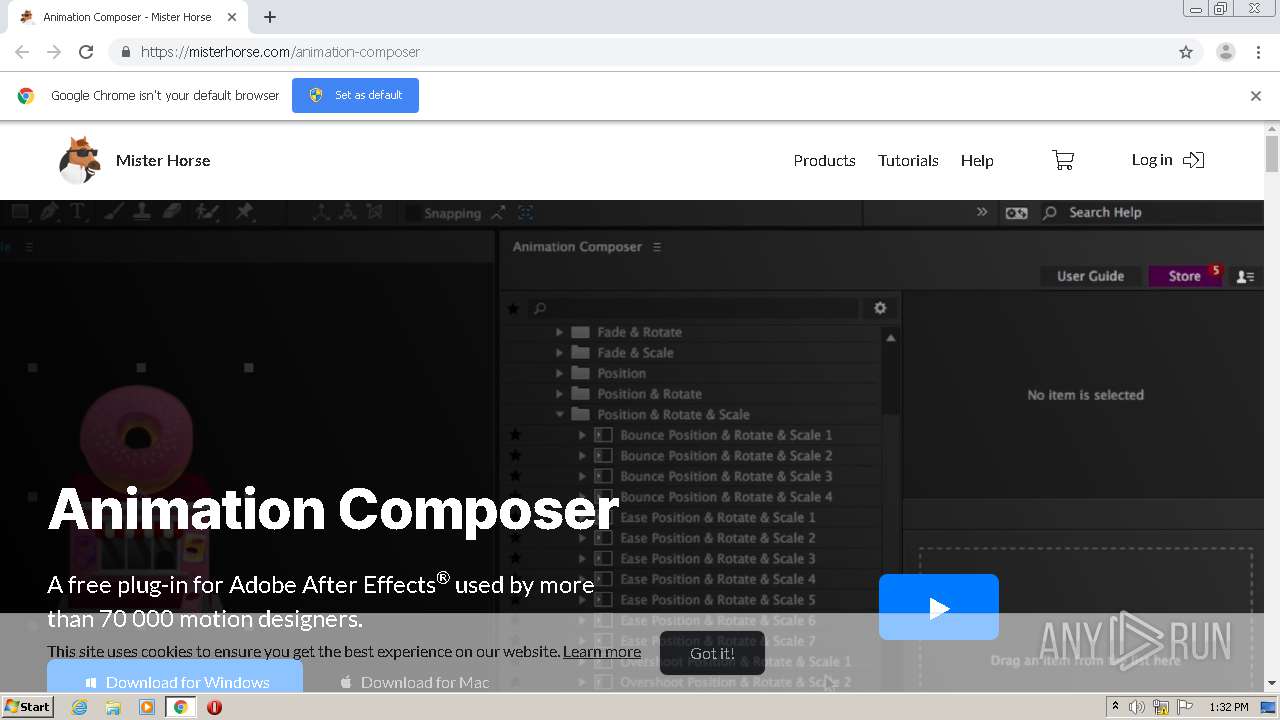
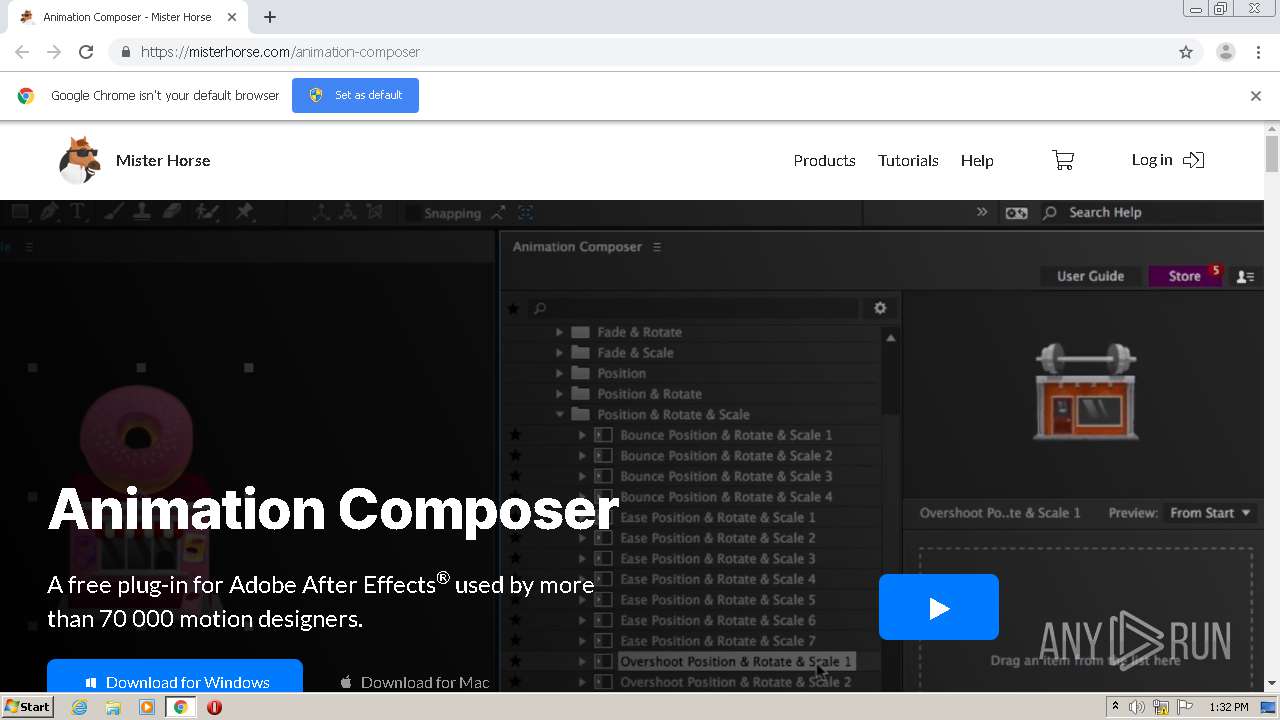
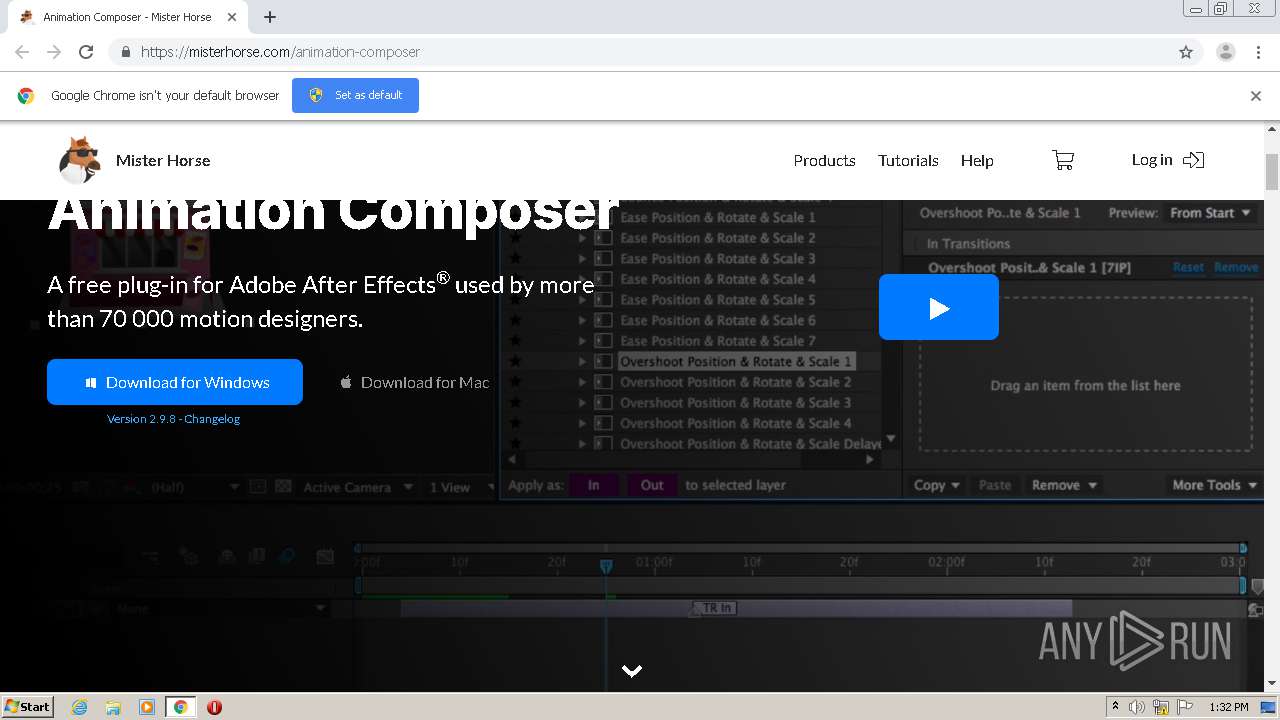
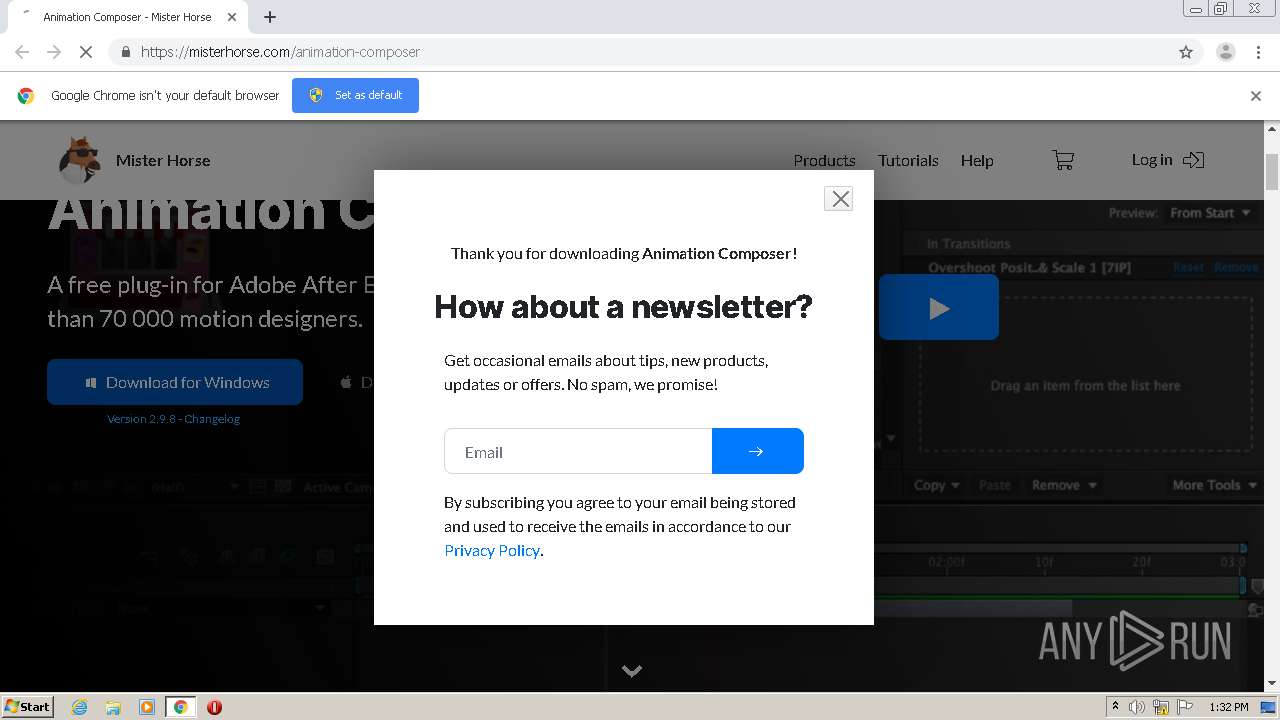
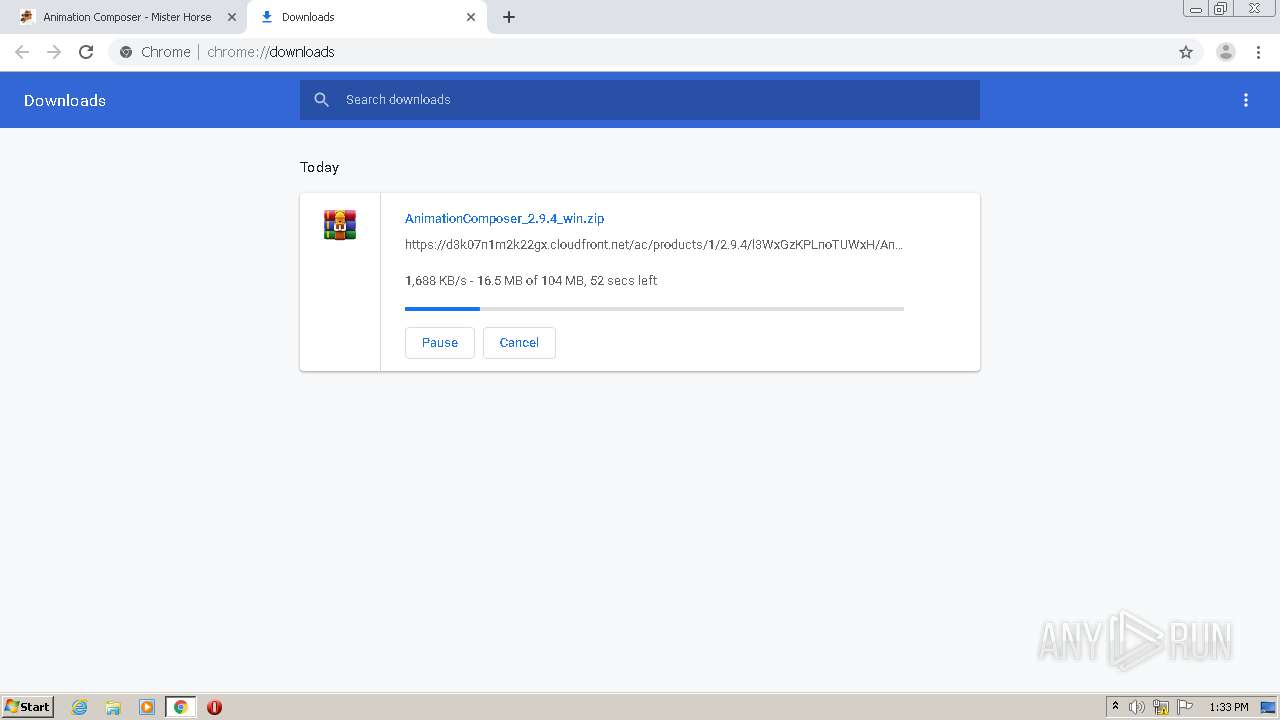
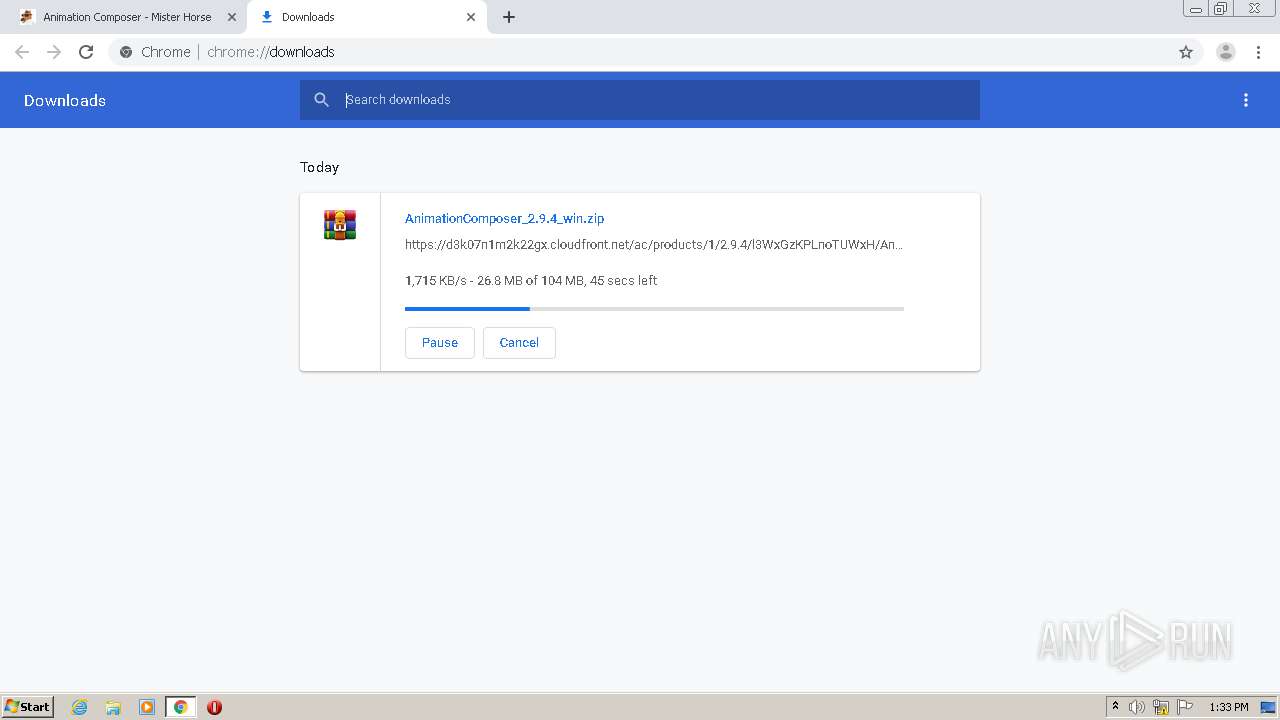
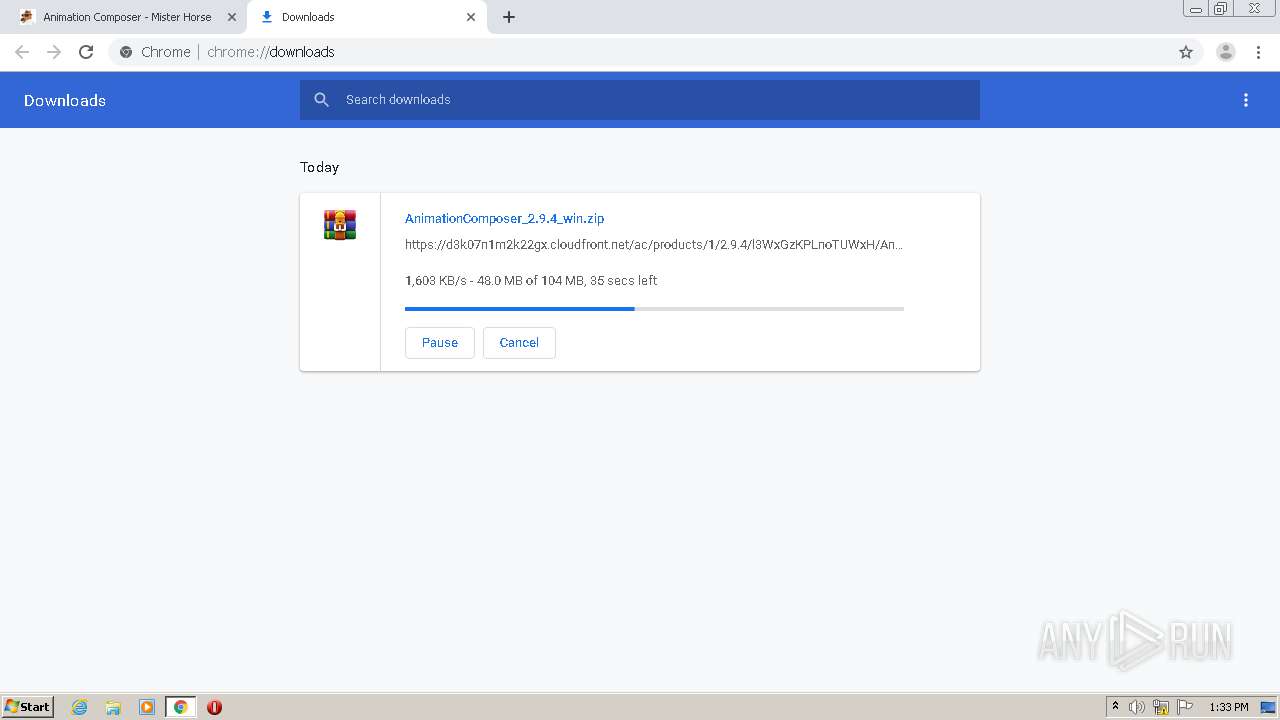
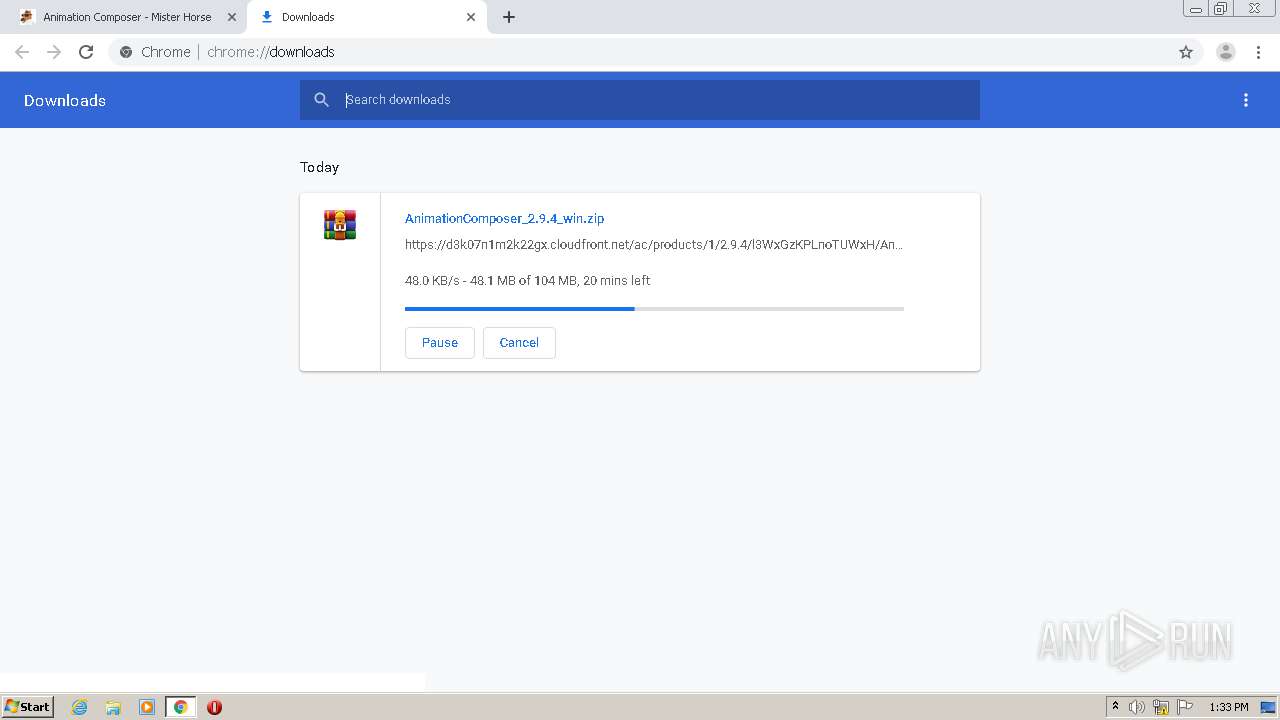
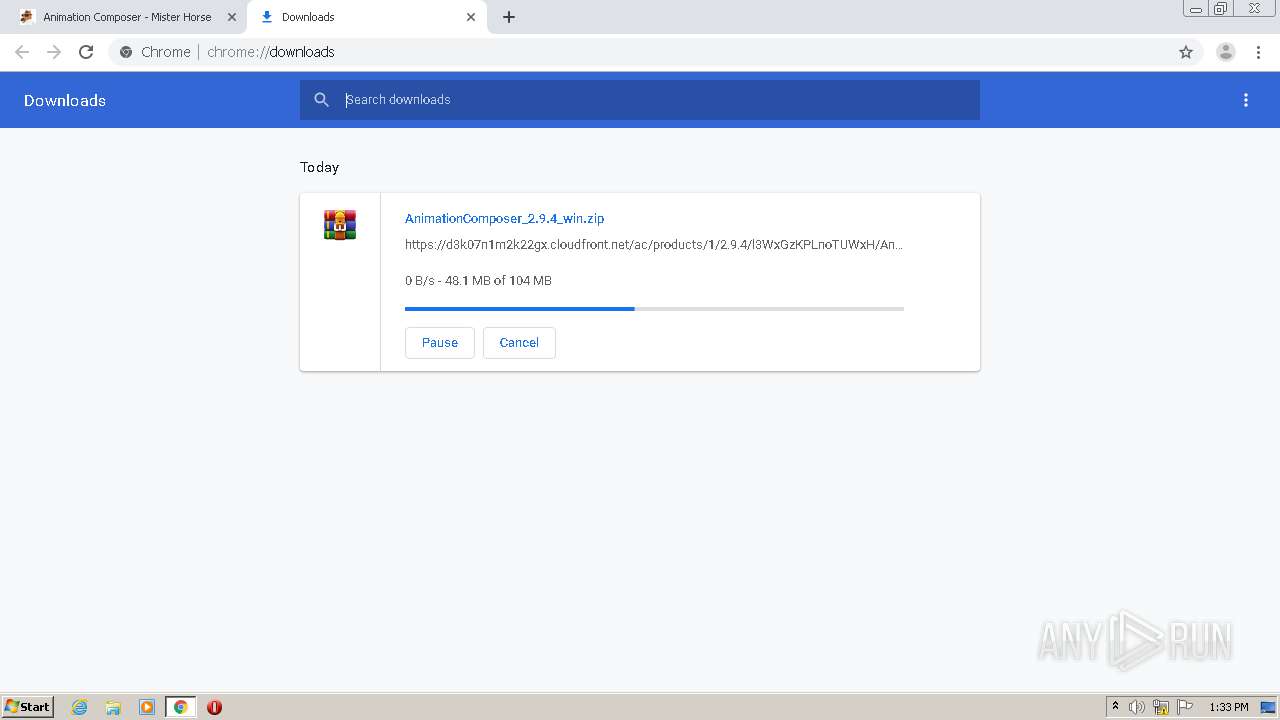
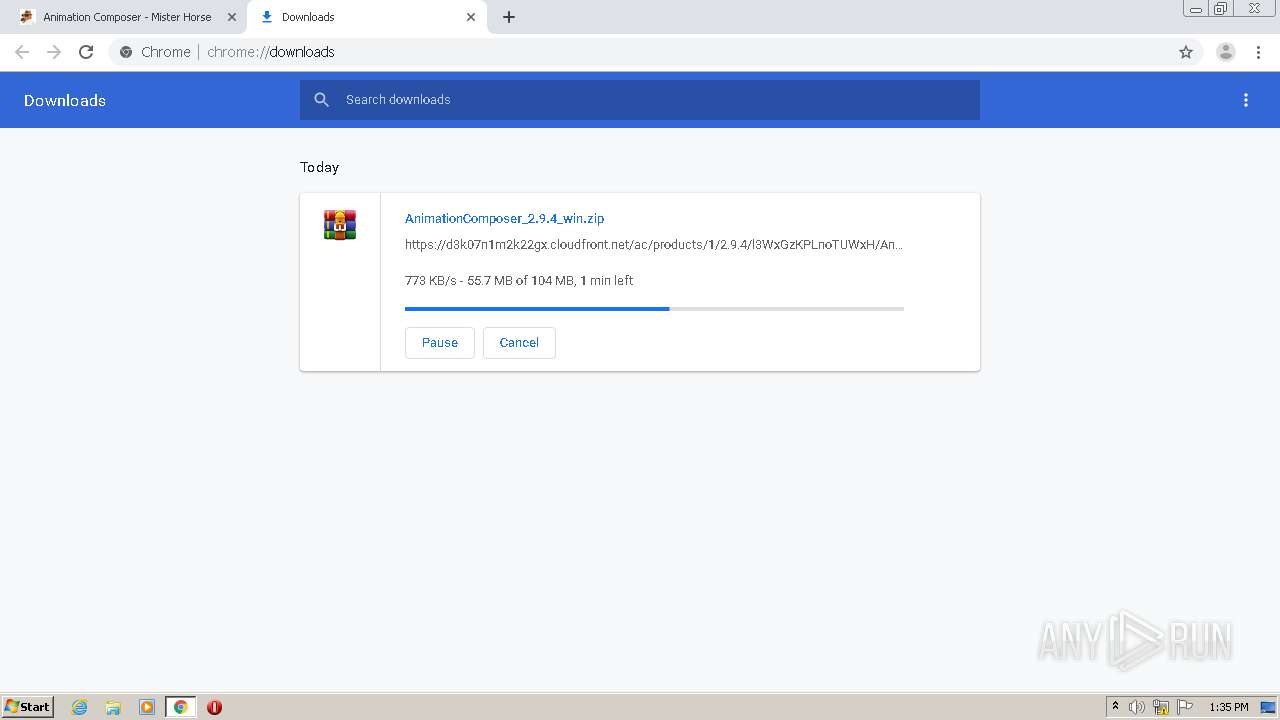
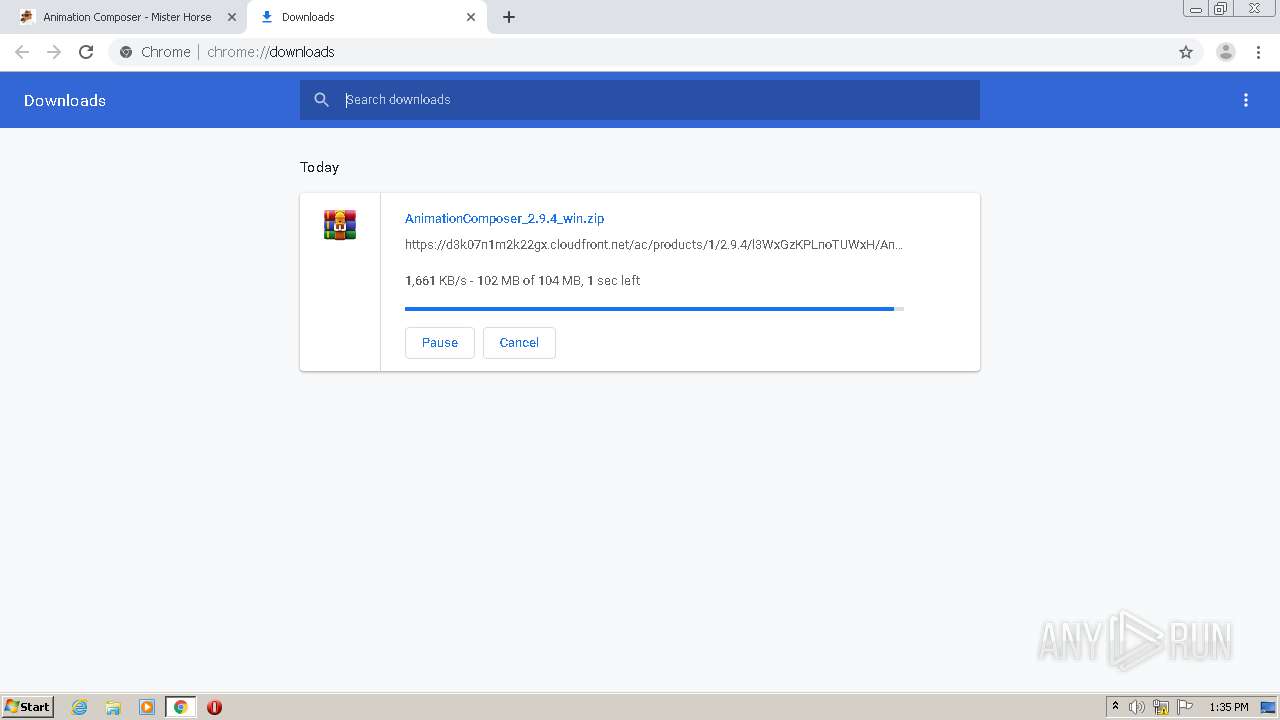
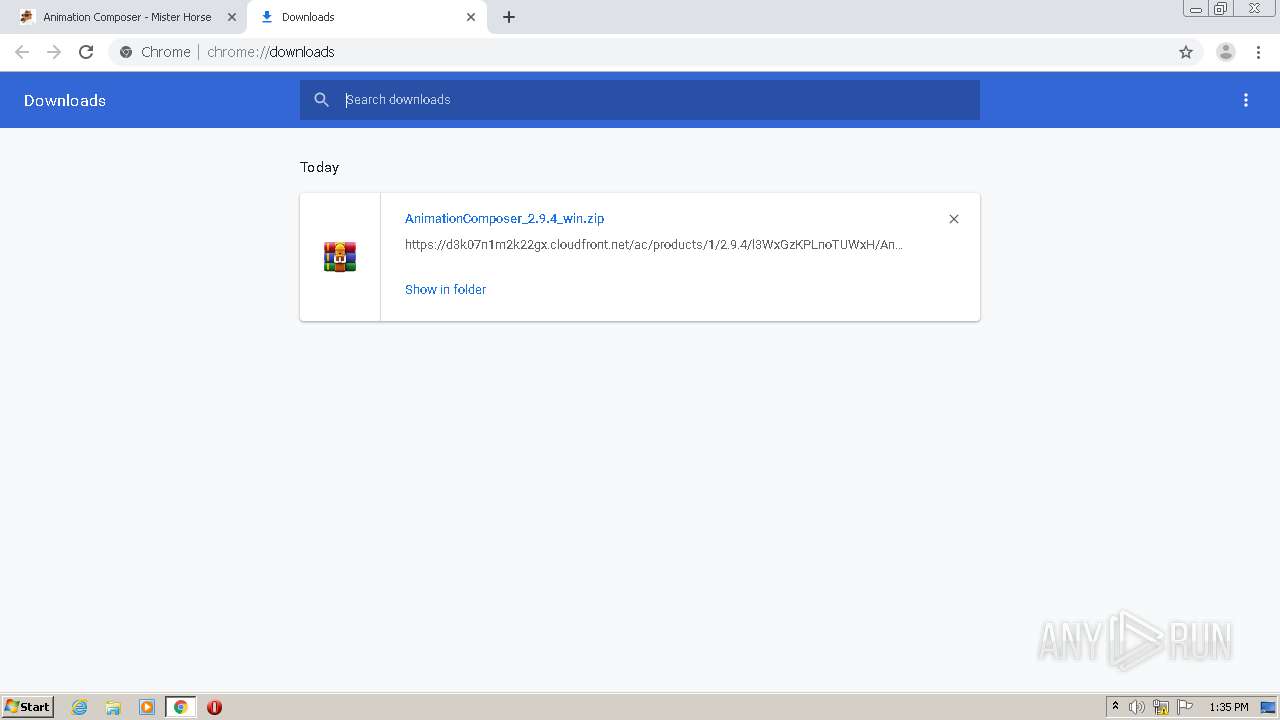
| URL: | https://misterhorse.com/animation-composer |
| Full analysis: | https://app.any.run/tasks/939bf21e-3e67-484a-856a-b933d3917383 |
| Verdict: | No threats detected |
| Analysis date: | August 10, 2020, 12:32:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F1BF6F4133A23950C940FC38AD35E0B0 |
| SHA1: | 0237F016EAB98ED6FD25C0DBC7EA58881B83F15F |
| SHA256: | D2FCA2FE54C44E008804C78E9D7AC25CCFE802B4EC6D1AFC038649AE5BB895D3 |
| SSDEEP: | 3:N8rNKXSGE4IERL8KW:2rNKXST45RAh |
MALICIOUS
No malicious indicators.SUSPICIOUS
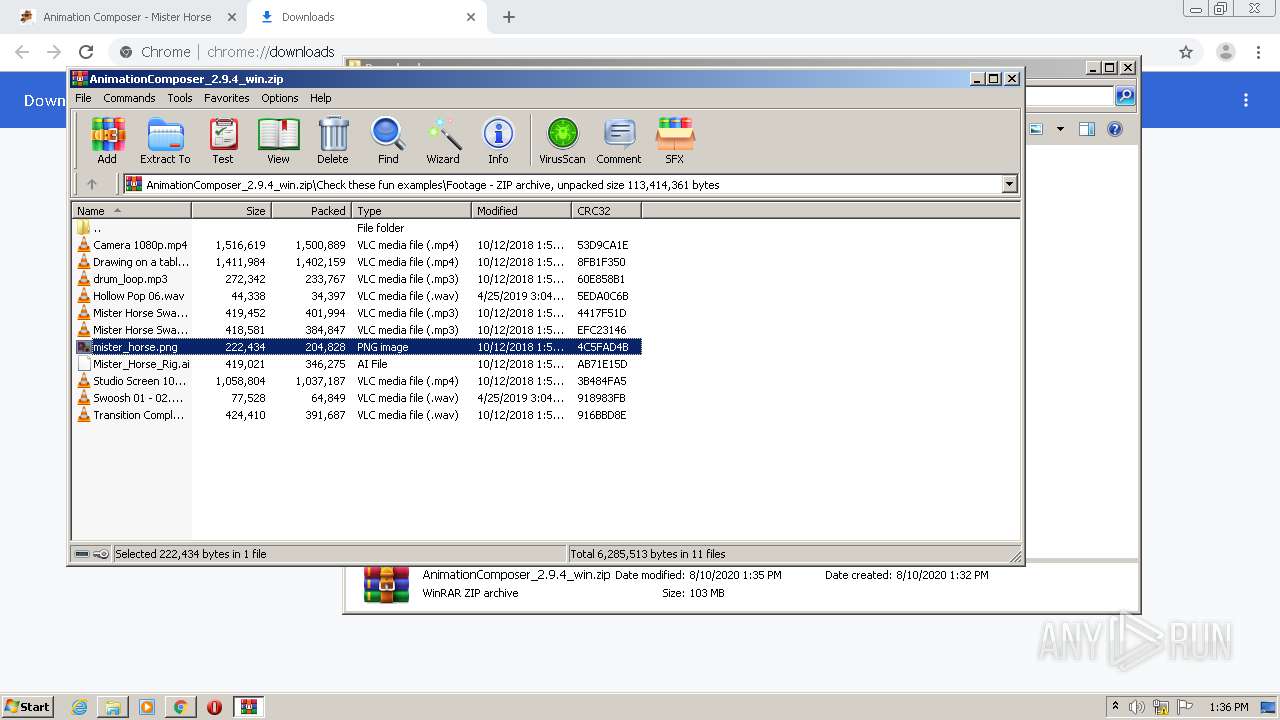
Creates files in the user directory
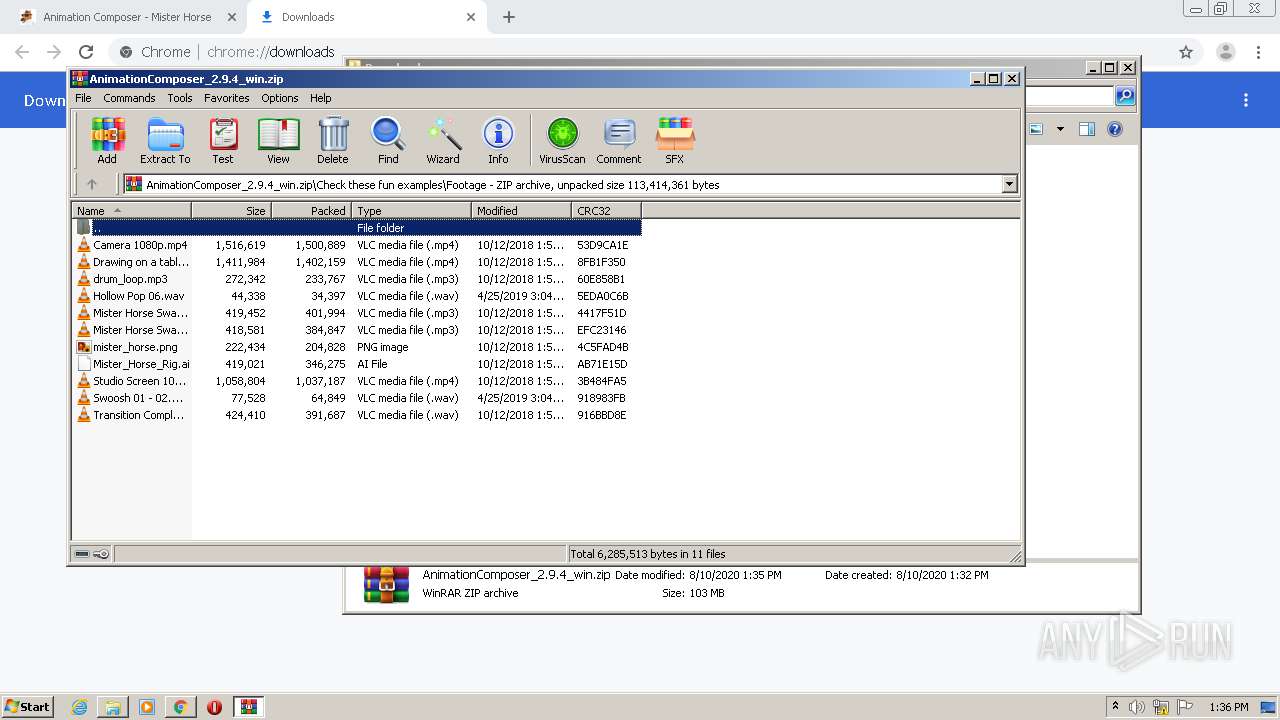
- vlc.exe (PID: 2336)
- vlc.exe (PID: 2360)
Uses RUNDLL32.EXE to load library
- WinRAR.exe (PID: 3788)
INFO
Application launched itself
- chrome.exe (PID: 2252)
Reads the hosts file
- chrome.exe (PID: 896)
- chrome.exe (PID: 2252)
Reads Internet Cache Settings
- chrome.exe (PID: 2252)
Reads settings of System Certificates
- chrome.exe (PID: 896)
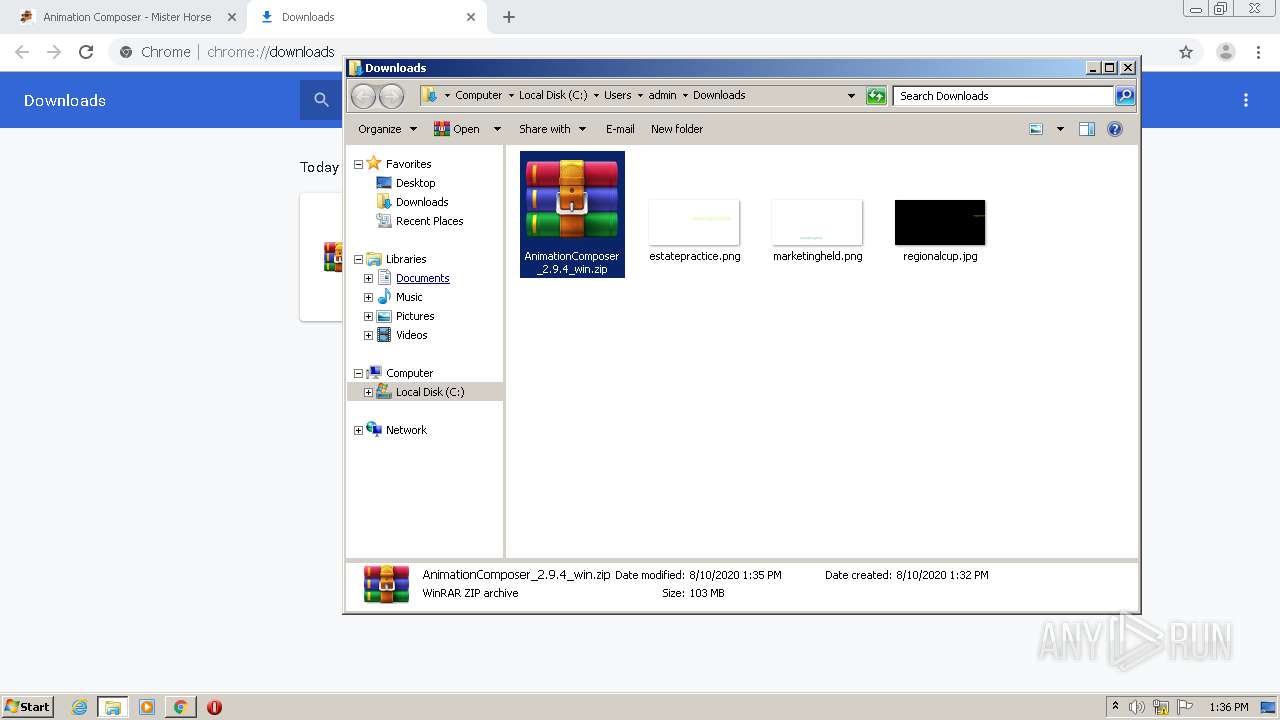
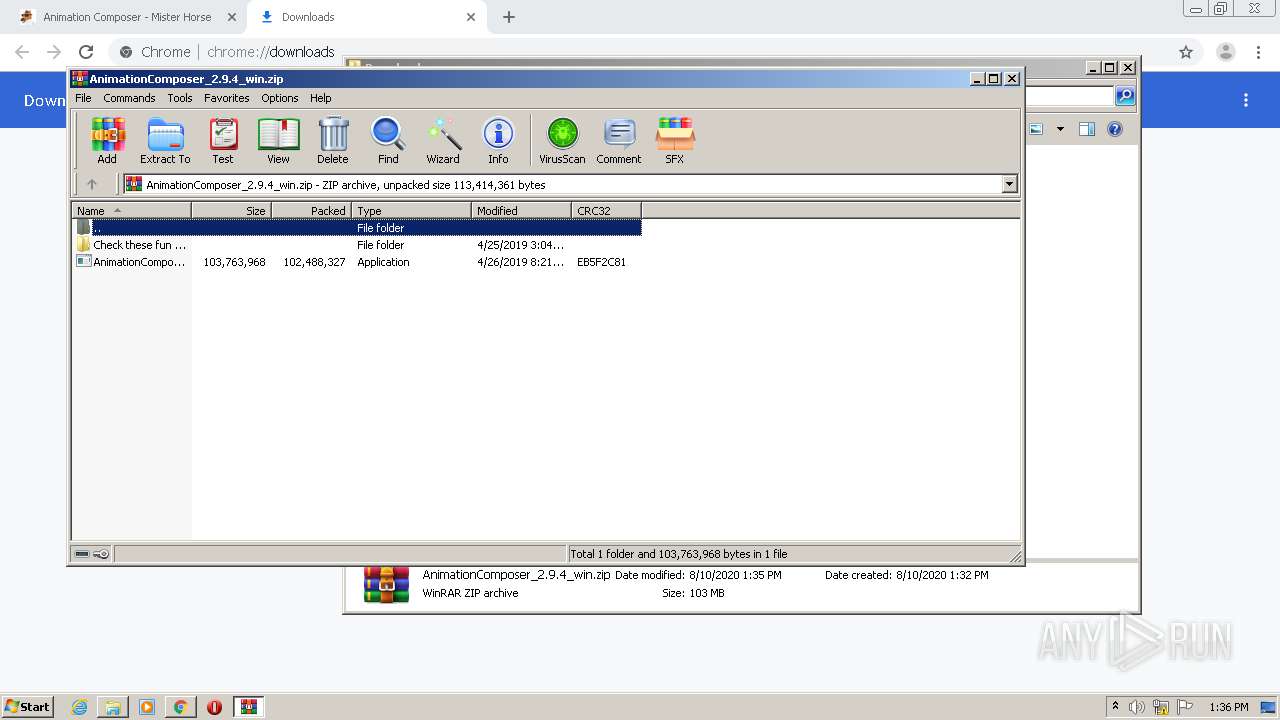
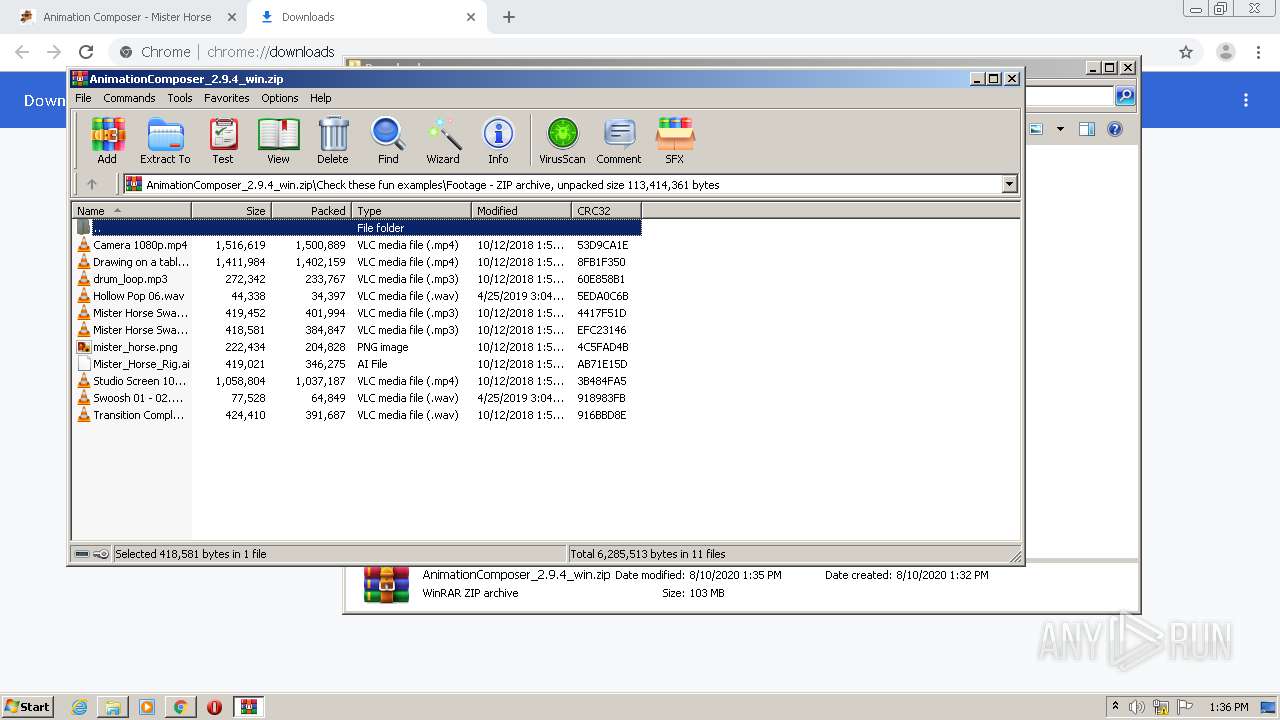
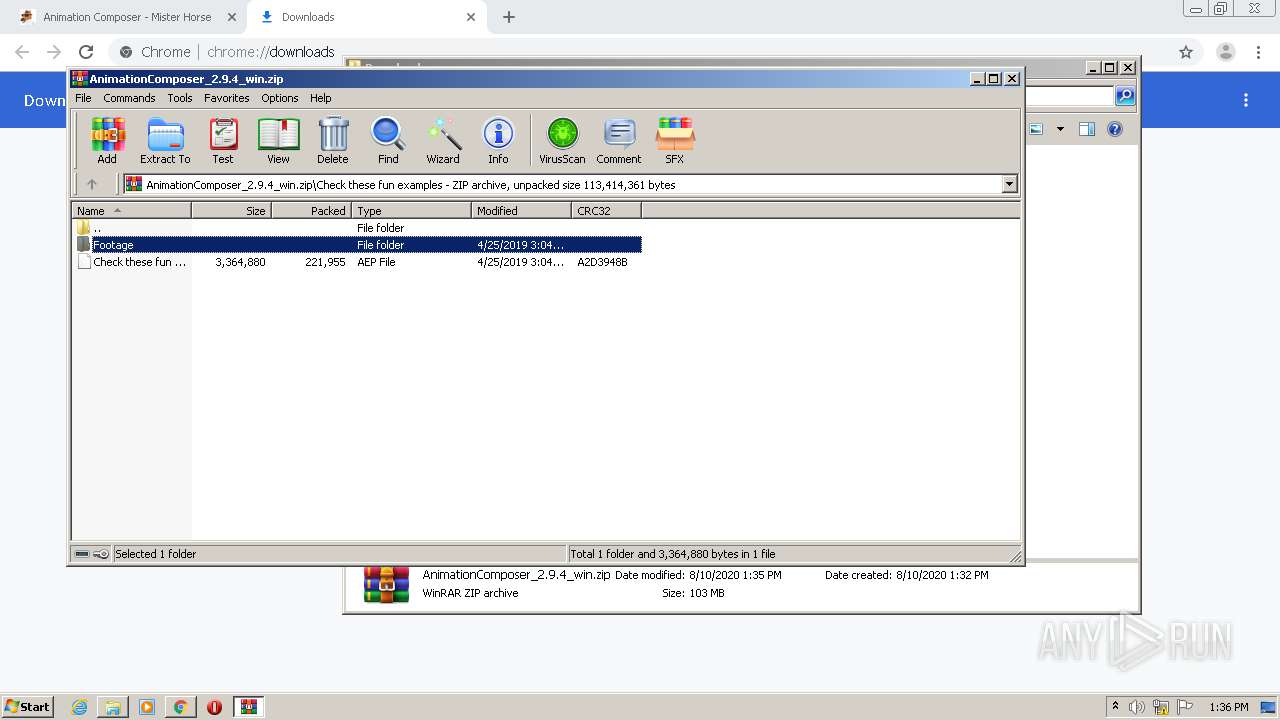
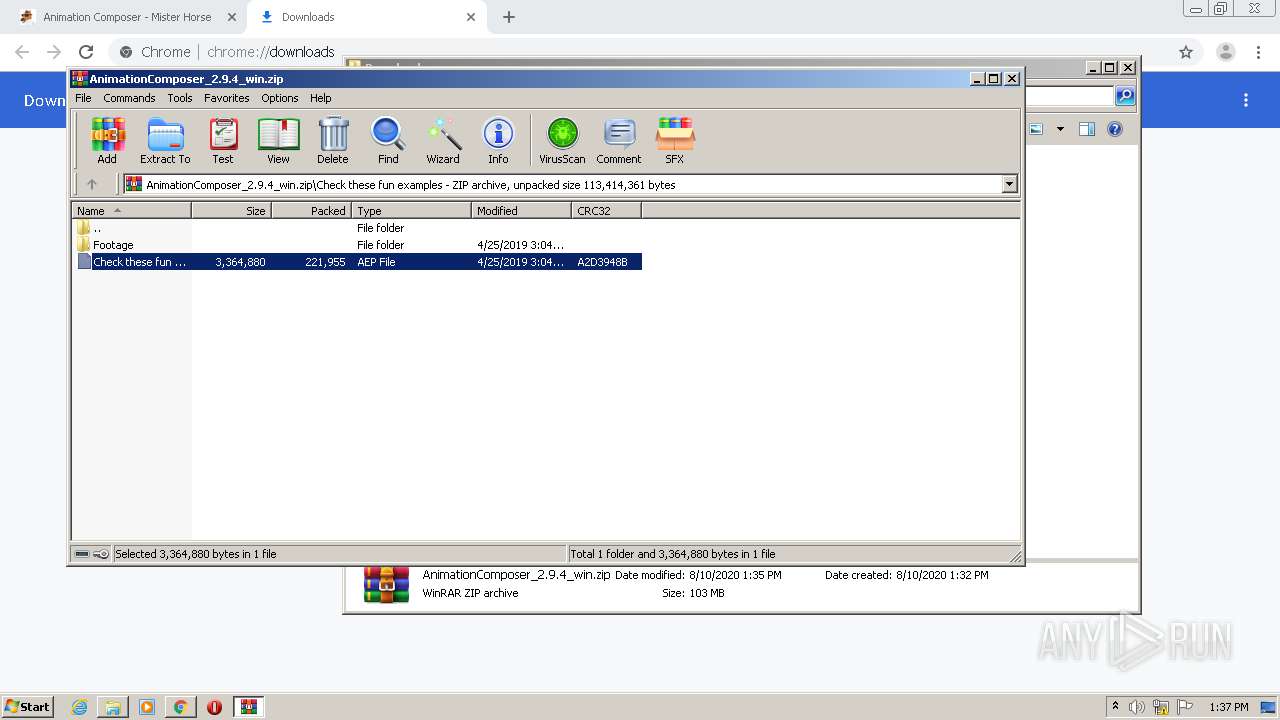
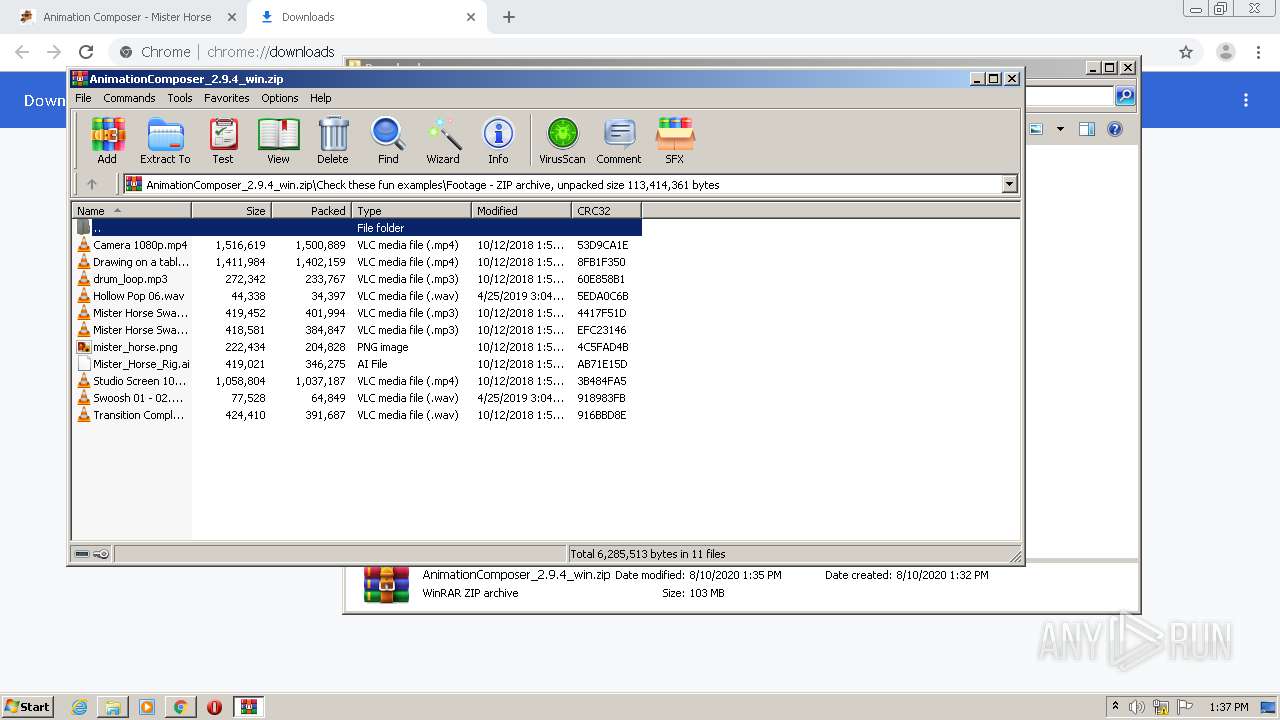
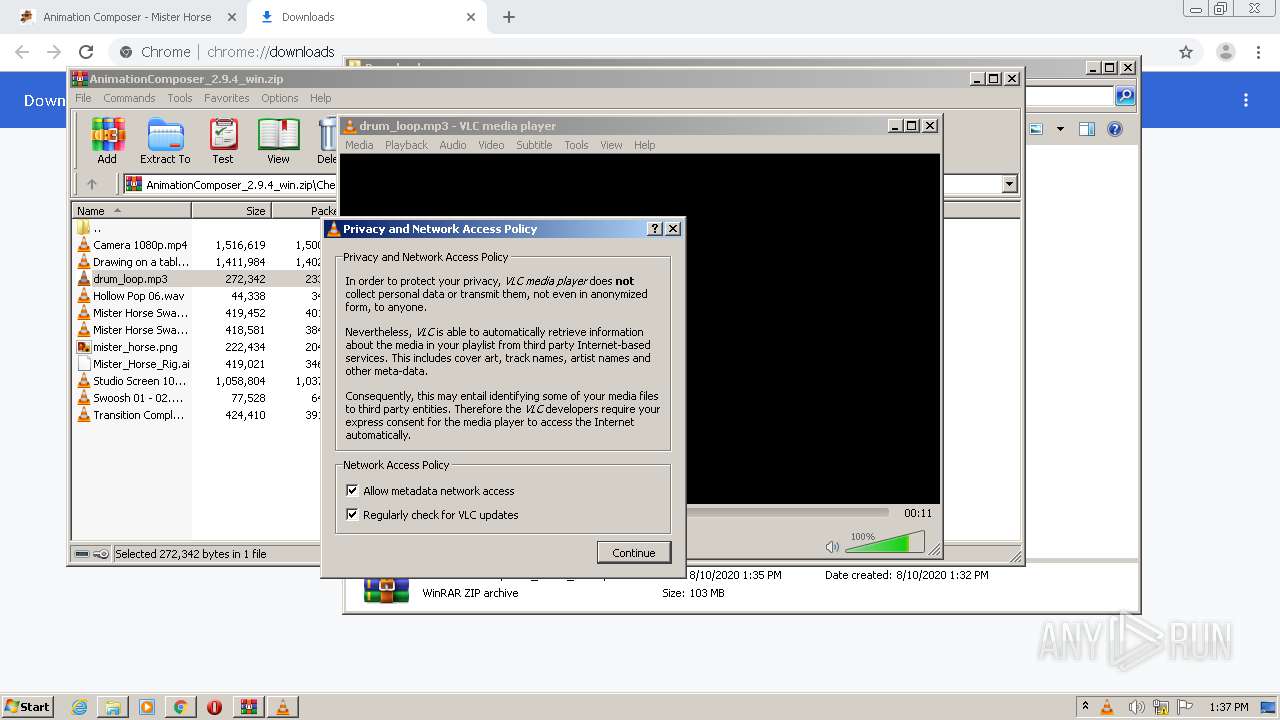
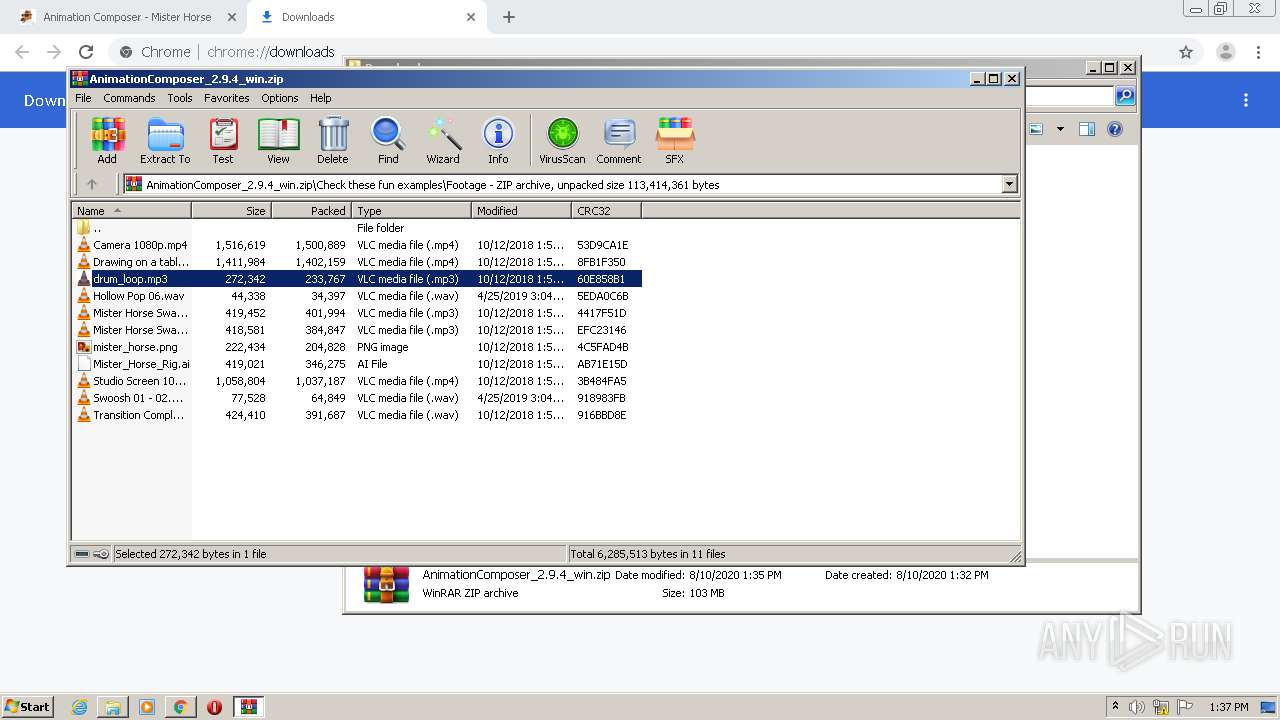
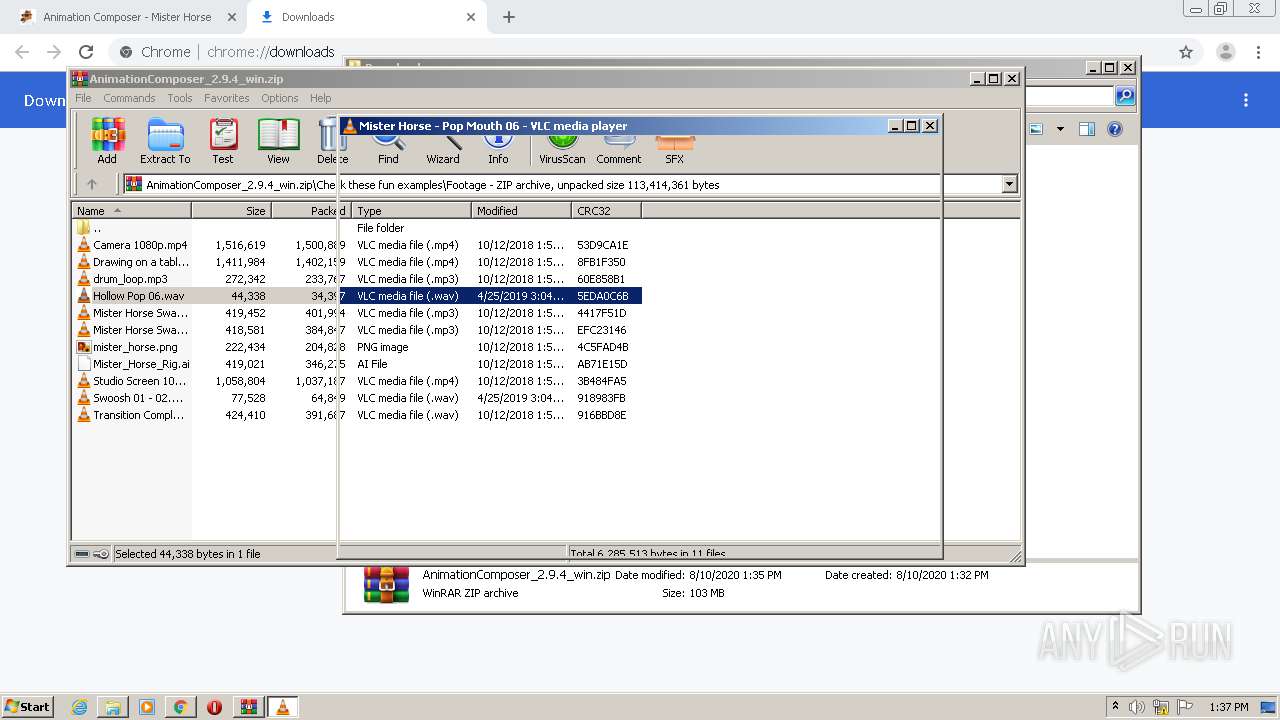
Manual execution by user
- WinRAR.exe (PID: 3788)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
65
Monitored processes
24
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,8491502707095798261,12482712264944810567,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=13043057609706815113 --mojo-platform-channel-handle=1604 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,8491502707095798261,12482712264944810567,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18198829642685550391 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3704 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,8491502707095798261,12482712264944810567,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14431224669461770080 --mojo-platform-channel-handle=500 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1004,8491502707095798261,12482712264944810567,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=7688983690134498407 --mojo-platform-channel-handle=3636 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1840 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2232 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://misterhorse.com/animation-composer" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1004,8491502707095798261,12482712264944810567,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=6023088307289926608 --mojo-platform-channel-handle=956 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
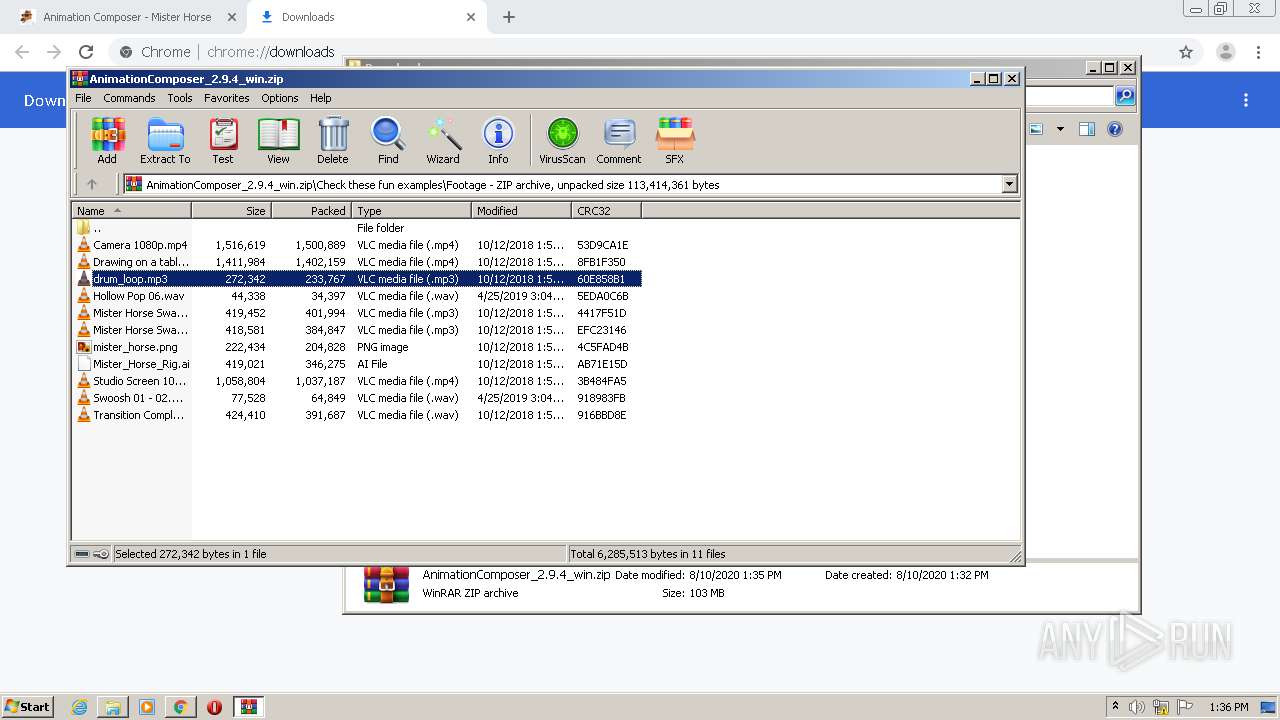
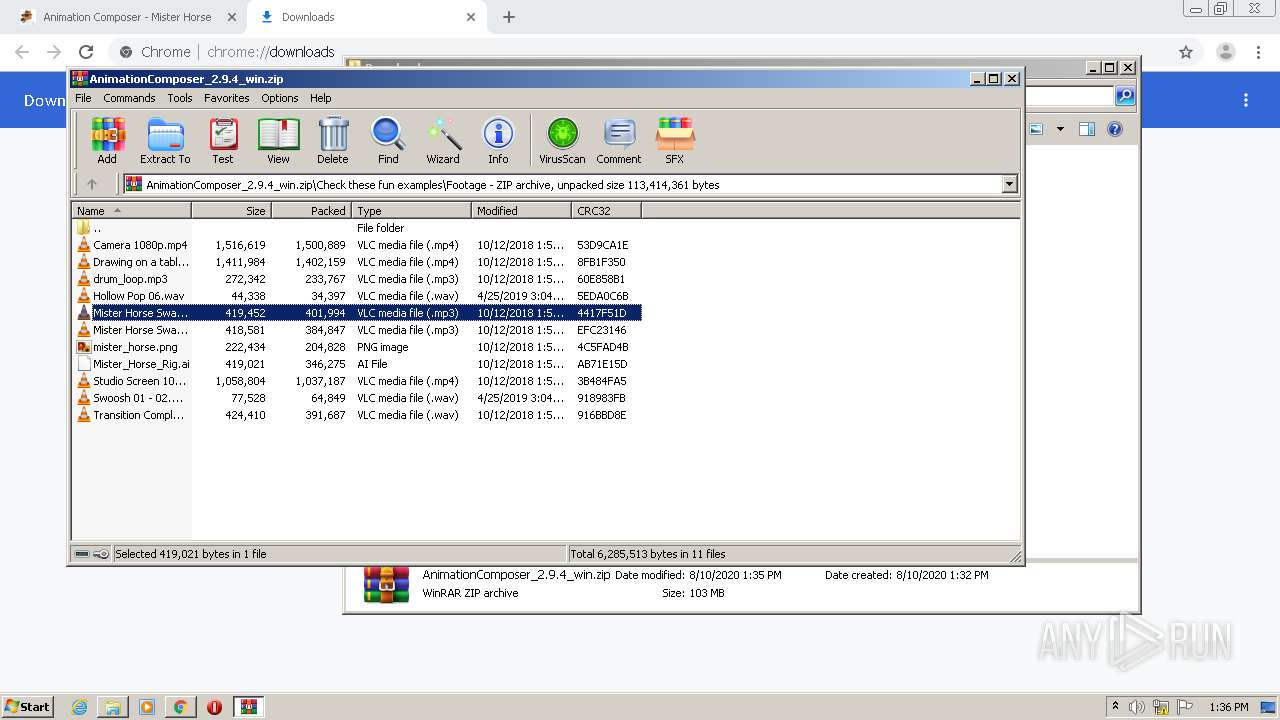
| 2336 | "C:\Program Files\VideoLAN\VLC\vlc.exe" --started-from-file "C:\Users\admin\AppData\Local\Temp\Rar$DIa3788.37334\Hollow Pop 06.wav" | C:\Program Files\VideoLAN\VLC\vlc.exe | WinRAR.exe | ||||||||||||
User: admin Company: VideoLAN Integrity Level: MEDIUM Description: VLC media player Exit code: 0 Version: 2.2.6 Modules
| |||||||||||||||
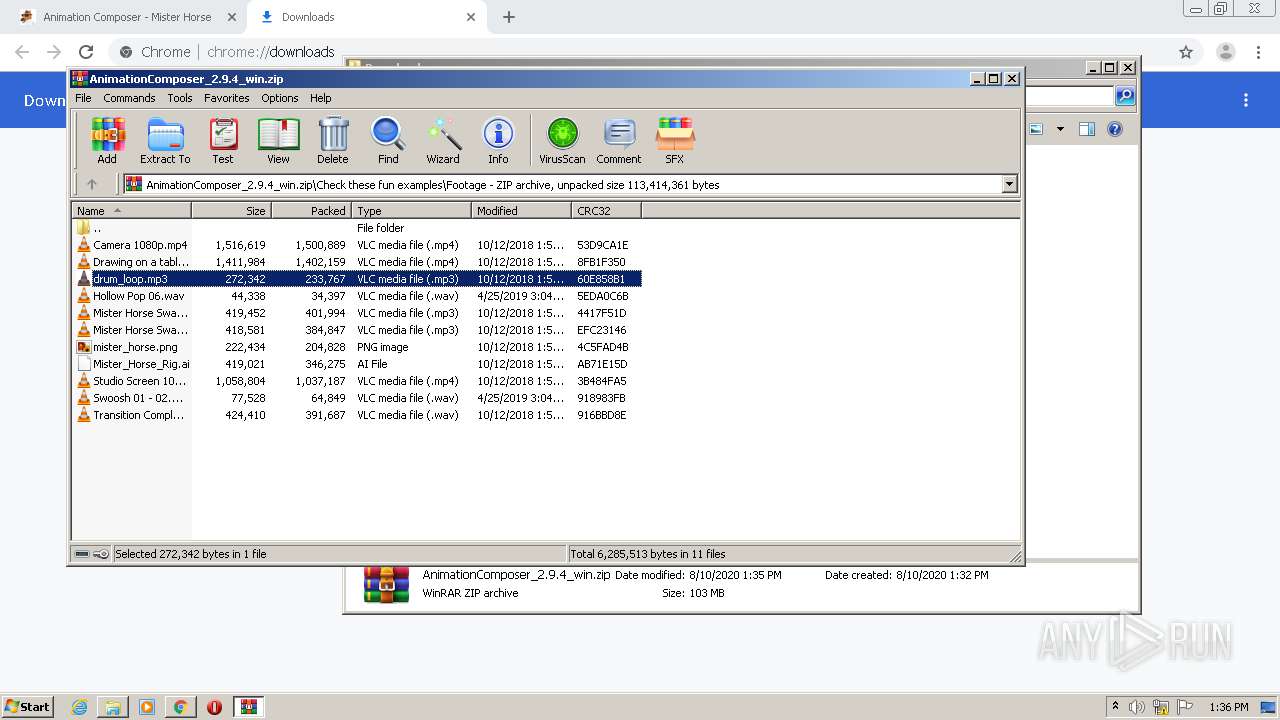
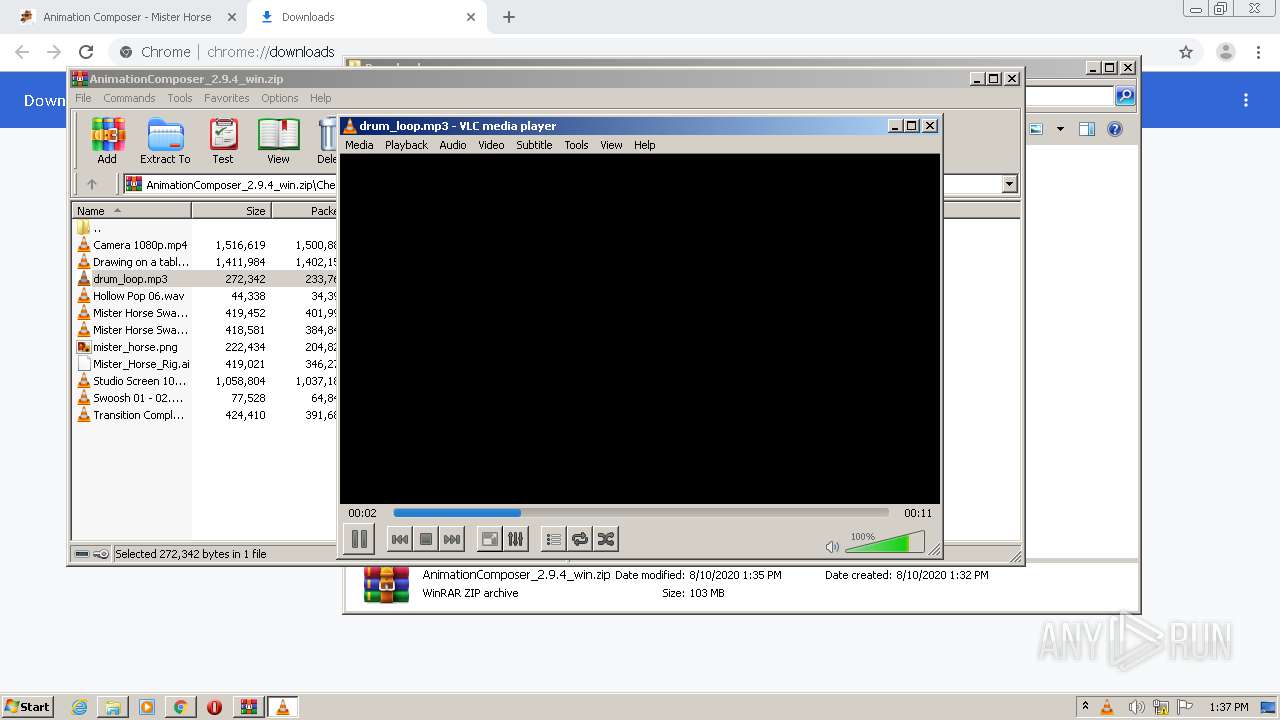
| 2360 | "C:\Program Files\VideoLAN\VLC\vlc.exe" --started-from-file "C:\Users\admin\AppData\Local\Temp\Rar$DIa3788.36154\drum_loop.mp3" | C:\Program Files\VideoLAN\VLC\vlc.exe | WinRAR.exe | ||||||||||||
User: admin Company: VideoLAN Integrity Level: MEDIUM Description: VLC media player Exit code: 0 Version: 2.2.6 Modules
| |||||||||||||||
| 2404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,8491502707095798261,12482712264944810567,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1976833120409703881 --mojo-platform-channel-handle=3708 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 298
Read events
2 170
Write events
123
Delete events
5
Modification events
| (PID) Process: | (2252) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2252) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2252) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2252) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2252) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2252) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2252) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2252) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (2252) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2252) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2252-13241536357581875 |
Value: 259 | |||
Executable files
0
Suspicious files
35
Text files
94
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2252 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2252 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF14e770.TMP | — | |
MD5:— | SHA256:— | |||
| 2252 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\84e3afee-e0ef-48b6-85c8-f64520fc10ce.tmp | — | |
MD5:— | SHA256:— | |||
| 2252 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2252 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2252 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\000001.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2252 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
| 2252 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF14e713.TMP | text | |
MD5:— | SHA256:— | |||
| 2252 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF14e741.TMP | text | |
MD5:— | SHA256:— | |||
| 2252 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
41
DNS requests
26
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
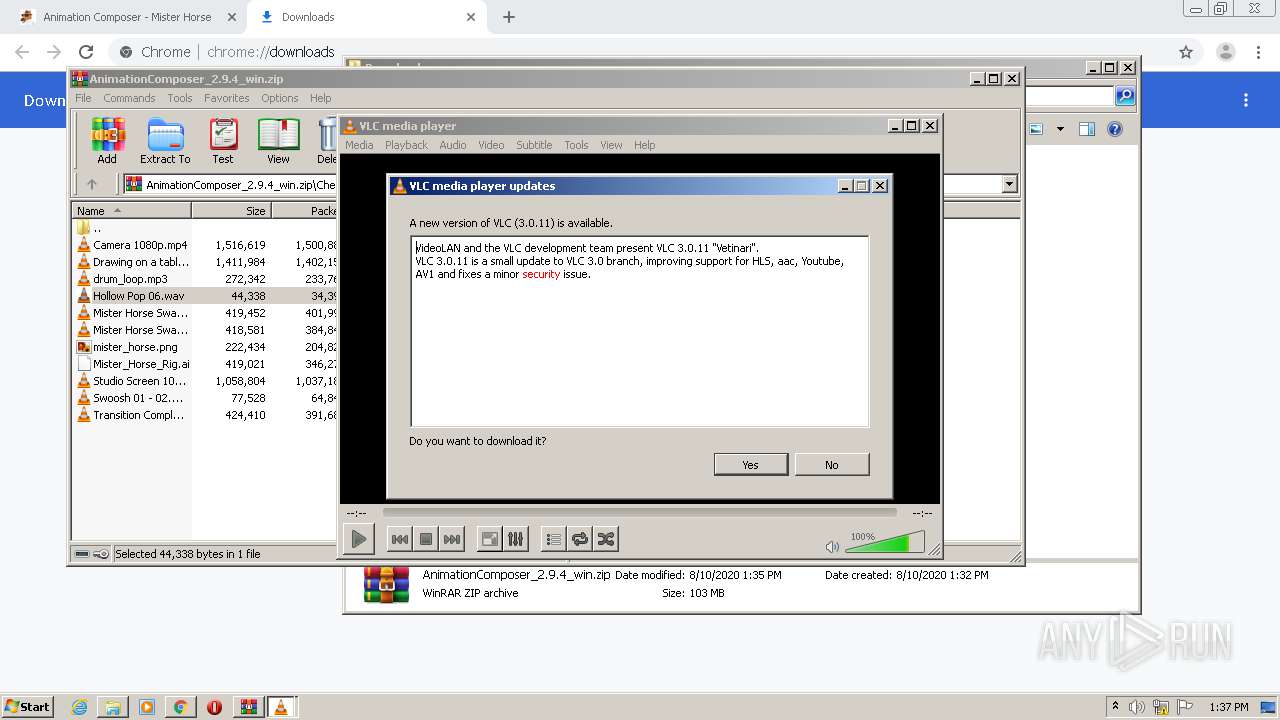
2336 | vlc.exe | GET | — | 64.31.0.51:80 | http://mirror.lstn.net/videolan/vlc/3.0.11/win32/vlc-3.0.11-win32.exe | US | — | — | suspicious |
2336 | vlc.exe | GET | 302 | 195.154.241.219:80 | http://get.videolan.org/vlc/3.0.11/win32/vlc-3.0.11-win32.exe | FR | html | 113 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
896 | chrome.exe | 172.217.23.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
896 | chrome.exe | 172.217.16.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
896 | chrome.exe | 34.77.137.73:443 | misterhorse.com | — | US | unknown |
896 | chrome.exe | 172.217.21.227:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
896 | chrome.exe | 91.201.28.212:443 | misterhorse.postaffiliatepro.com | — | — | unknown |
896 | chrome.exe | 172.217.16.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
896 | chrome.exe | 13.35.253.156:443 | d23mmnx9ld45h.cloudfront.net | — | US | unknown |
896 | chrome.exe | 216.58.207.78:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
896 | chrome.exe | 52.218.109.144:443 | misterhorse-public-web.s3.eu-west-1.amazonaws.com | Amazon.com, Inc. | IE | unknown |
896 | chrome.exe | 93.184.220.66:443 | platform.twitter.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
misterhorse.com |
| unknown |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
misterhorse.postaffiliatepro.com |
| suspicious |
fonts.gstatic.com |
| whitelisted |
misterhorse-public-web.s3.eu-west-1.amazonaws.com |
| unknown |
www.google-analytics.com |
| whitelisted |
d23mmnx9ld45h.cloudfront.net |
| malicious |
platform.twitter.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2336 | vlc.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
Process | Message |
|---|---|
vlc.exe | core libvlc: one instance mode ENABLED
|
vlc.exe | core libvlc: Running vlc with the default interface. Use 'cvlc' to use vlc without interface.
|
vlc.exe | mpgatofixed32 audio converter error: libmad error: bad main_data_begin pointer
|
vlc.exe | core libvlc: one instance mode ENABLED
|
vlc.exe | core libvlc: Running vlc with the default interface. Use 'cvlc' to use vlc without interface.
|
vlc.exe | core libvlc: Status file authenticated
|