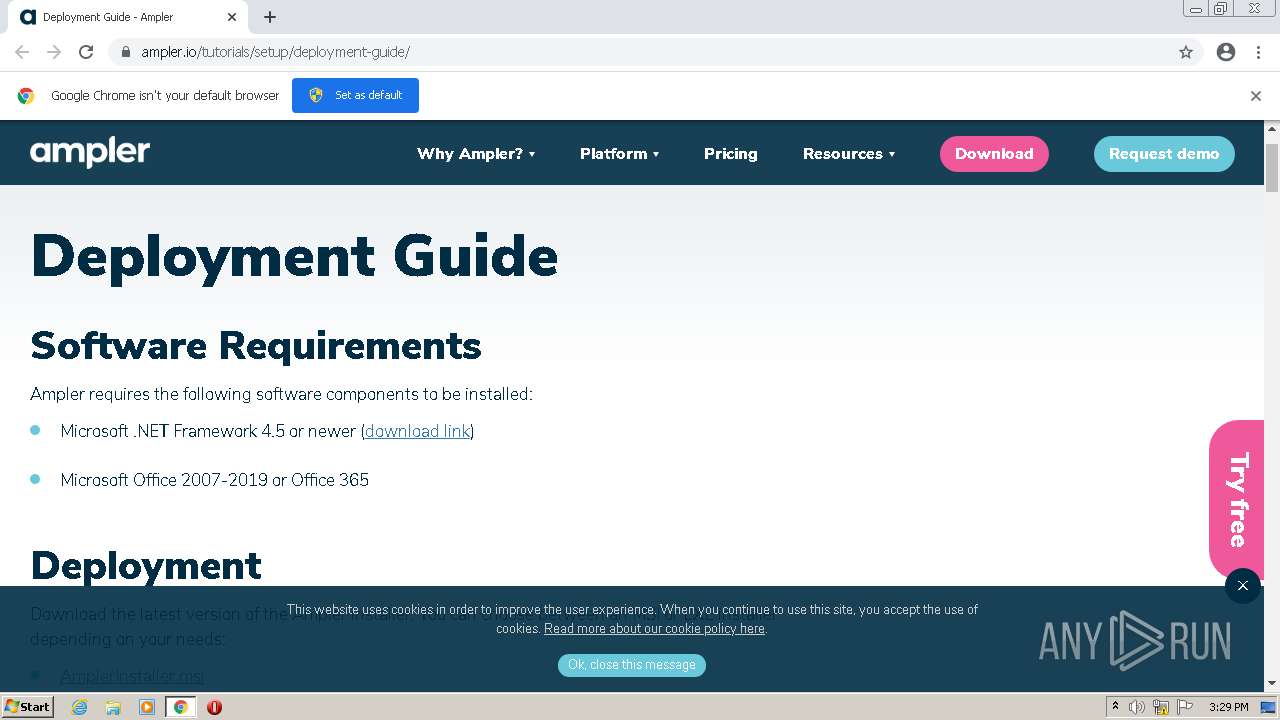
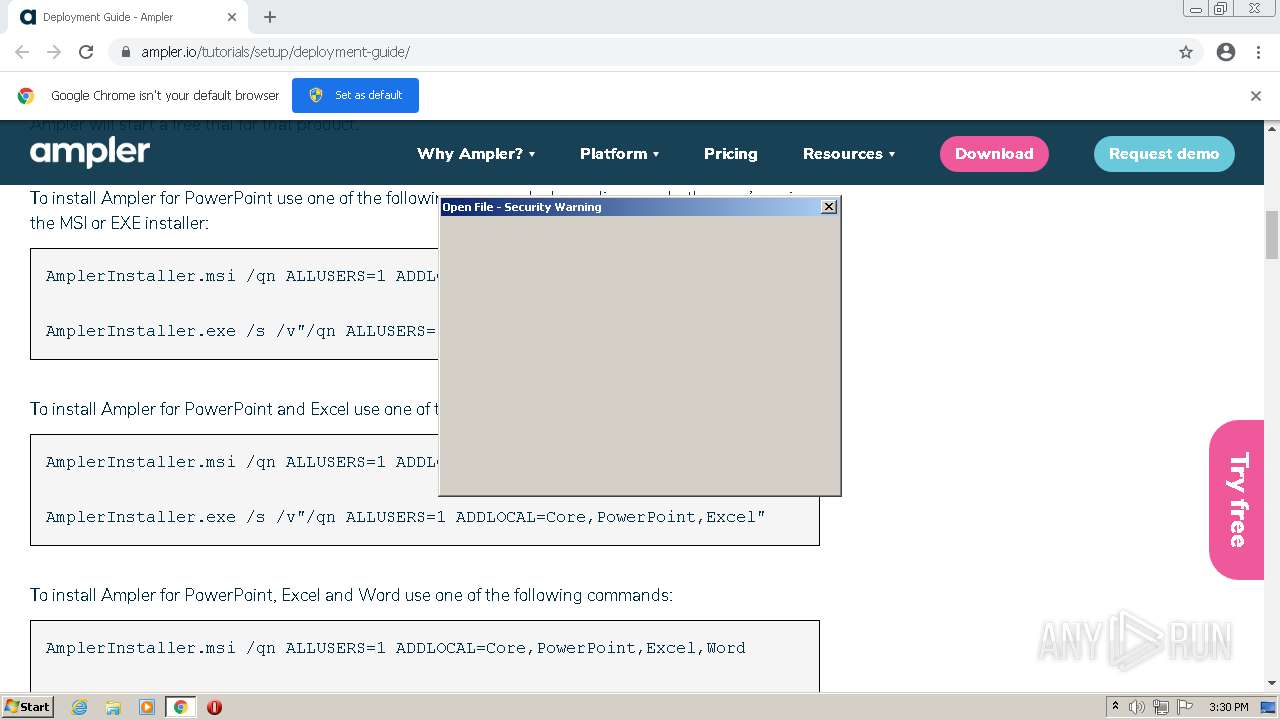
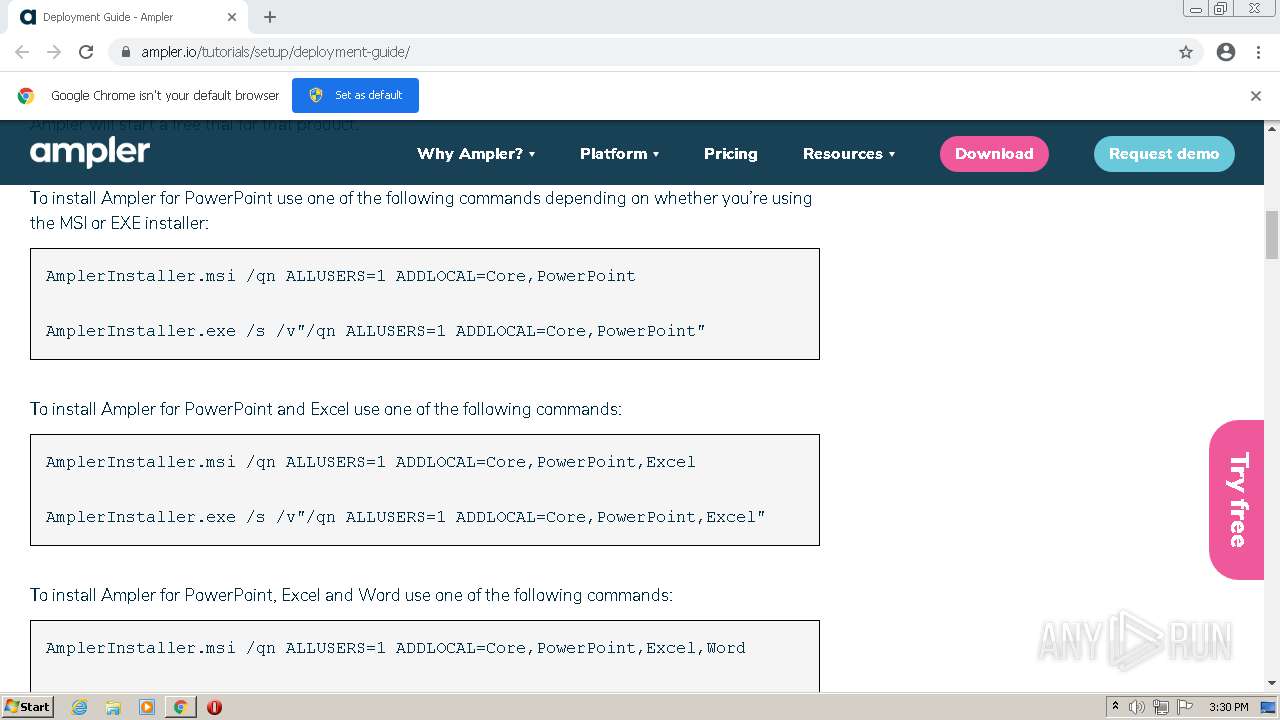
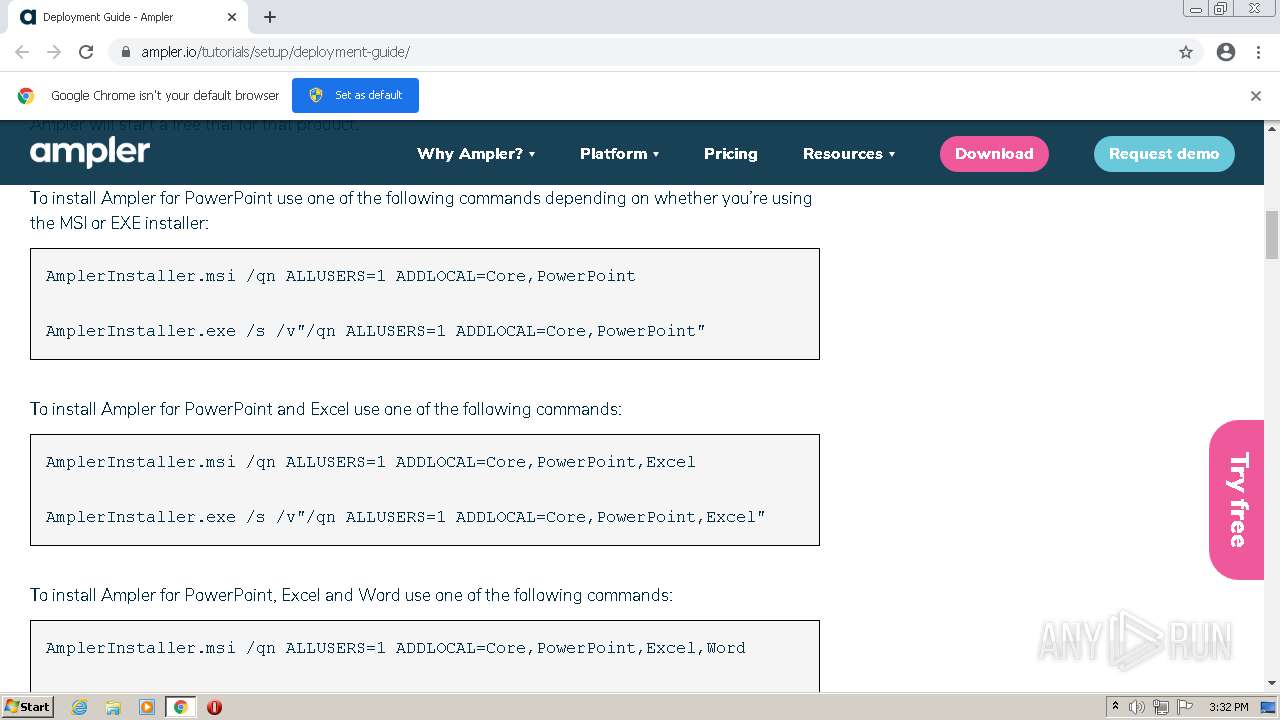
| URL: | https://ampler.io/tutorials/setup/deployment-guide/ |
| Full analysis: | https://app.any.run/tasks/18aec3cb-cab7-4beb-b798-5cf3568f3385 |
| Verdict: | Malicious activity |
| Analysis date: | June 23, 2021, 14:29:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 123EC8A8B1B28E371344175A73AE997C |
| SHA1: | A4504274C9E2EBCFF729DF38F56A4BD9346D5079 |
| SHA256: | D2F24FD6F1281FE7B3E007833829FDCBF5C142176C5947EFBC6AF6824AA962EB |
| SSDEEP: | 3:N8C4Rt1WAyK2LZBAK:2Ly7LLZ2K |
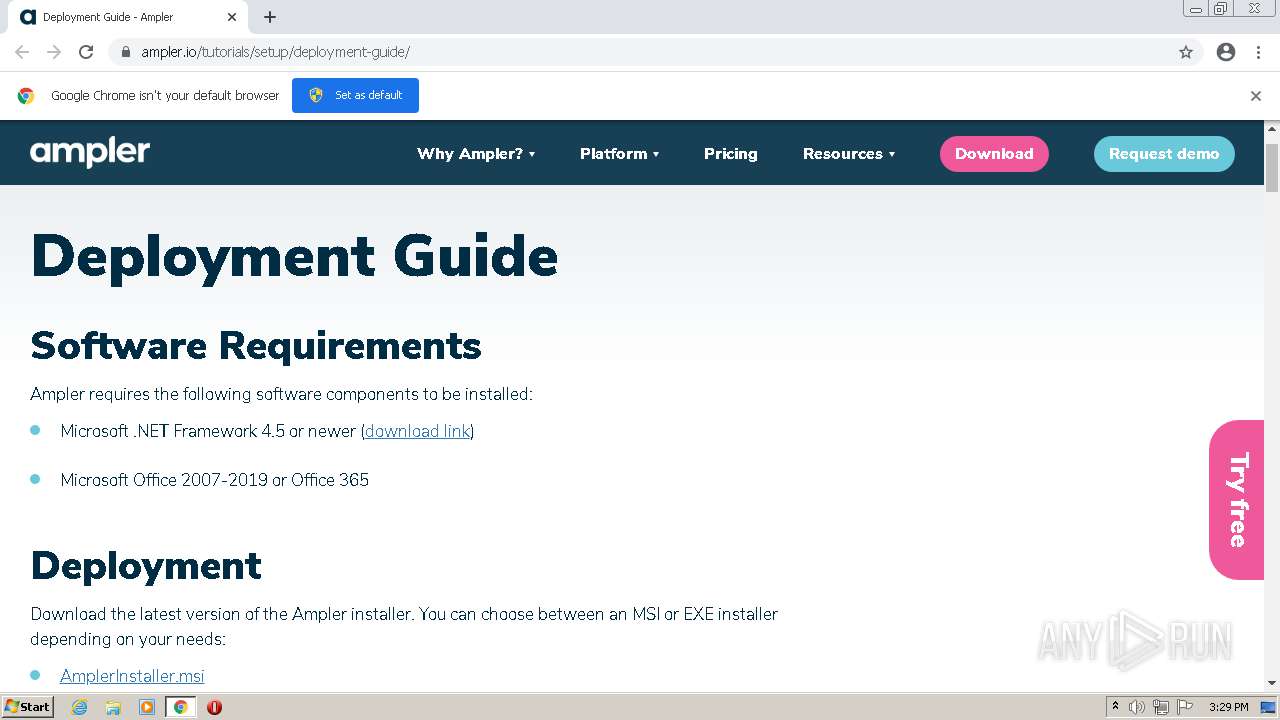
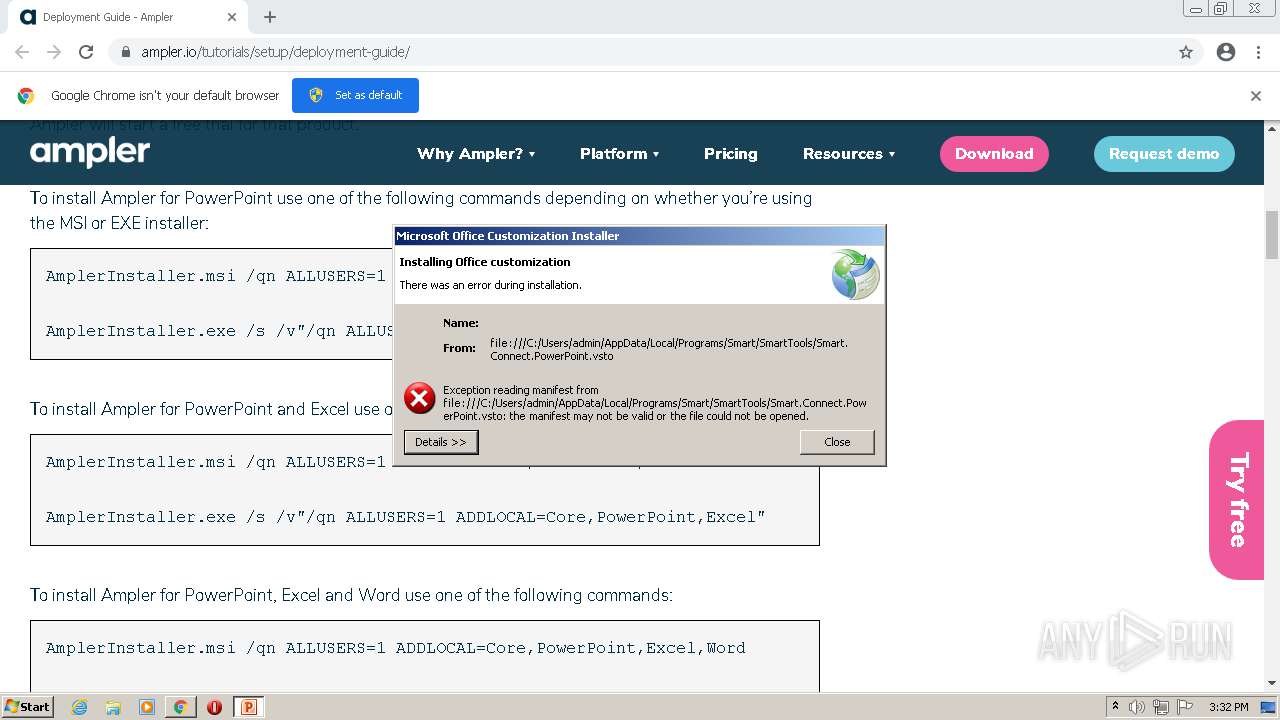
MALICIOUS
Application was dropped or rewritten from another process
- AmplerInstaller.exe (PID: 864)
- Smart.Jobs.exe (PID: 552)
- Smart.Jobs.exe (PID: 3760)
- Smart.Jobs.exe (PID: 2792)
- Smart.Jobs.exe (PID: 116)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 3148)
- MsiExec.exe (PID: 3292)
- Smart.Jobs.exe (PID: 552)
- Smart.Jobs.exe (PID: 3760)
- Smart.Jobs.exe (PID: 2792)
- Smart.Jobs.exe (PID: 116)
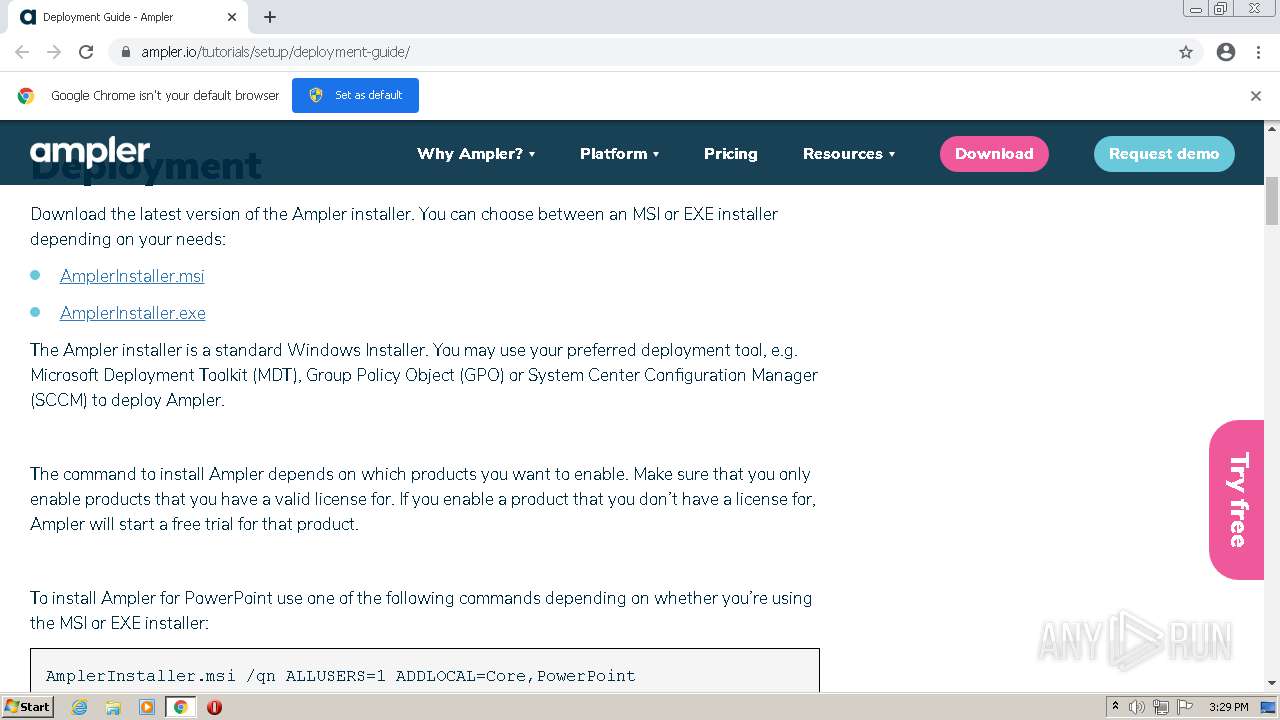
Loads the Task Scheduler COM API
- MsiExec.exe (PID: 3292)
- Smart.Jobs.exe (PID: 552)
Changes settings of System certificates
- MsiExec.exe (PID: 3292)
- msiexec.exe (PID: 276)
Drops executable file immediately after starts
- chrome.exe (PID: 3532)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2436)
- MSIEXEC.EXE (PID: 1304)
- msiexec.exe (PID: 276)
- chrome.exe (PID: 3532)
Reads the computer name
- AmplerInstaller.exe (PID: 864)
- ngen.exe (PID: 2456)
- ngen.exe (PID: 3840)
- ngen.exe (PID: 884)
- ngen.exe (PID: 2452)
- ngen.exe (PID: 2192)
- ngen.exe (PID: 3136)
- ngen.exe (PID: 2820)
- ngen.exe (PID: 2736)
- ngen.exe (PID: 3332)
- ngen.exe (PID: 3532)
- ngen.exe (PID: 3152)
- ngen.exe (PID: 2544)
- ngen.exe (PID: 968)
- ngen.exe (PID: 3124)
- ngen.exe (PID: 2984)
- ngen.exe (PID: 360)
- ngen.exe (PID: 2152)
- ngen.exe (PID: 2268)
- ngen.exe (PID: 396)
- ngen.exe (PID: 2528)
- Smart.Jobs.exe (PID: 552)
- Smart.Jobs.exe (PID: 3760)
- Smart.Jobs.exe (PID: 2792)
- Smart.Jobs.exe (PID: 116)
Checks supported languages
- AmplerInstaller.exe (PID: 864)
- ngen.exe (PID: 2456)
- ngen.exe (PID: 3840)
- ngen.exe (PID: 884)
- ngen.exe (PID: 2820)
- ngen.exe (PID: 3136)
- ngen.exe (PID: 2736)
- ngen.exe (PID: 3332)
- ngen.exe (PID: 3532)
- ngen.exe (PID: 3124)
- ngen.exe (PID: 968)
- ngen.exe (PID: 2984)
- ngen.exe (PID: 3152)
- ngen.exe (PID: 2544)
- ngen.exe (PID: 360)
- ngen.exe (PID: 2152)
- ngen.exe (PID: 396)
- ngen.exe (PID: 2528)
- ngen.exe (PID: 2268)
- cmd.exe (PID: 3716)
- Smart.Jobs.exe (PID: 552)
- Smart.Jobs.exe (PID: 3760)
- Smart.Jobs.exe (PID: 2792)
- Smart.Jobs.exe (PID: 116)
- ngen.exe (PID: 2192)
- ngen.exe (PID: 2452)
Executed as Windows Service
- msiexec.exe (PID: 276)
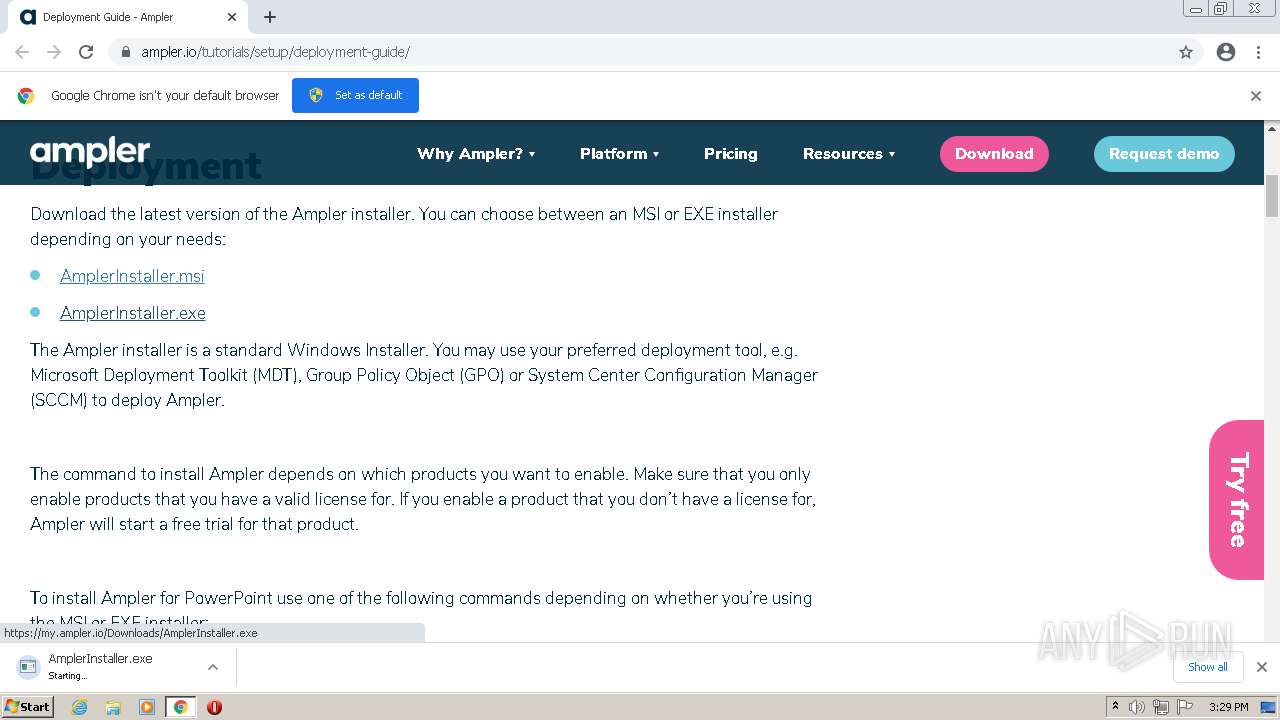
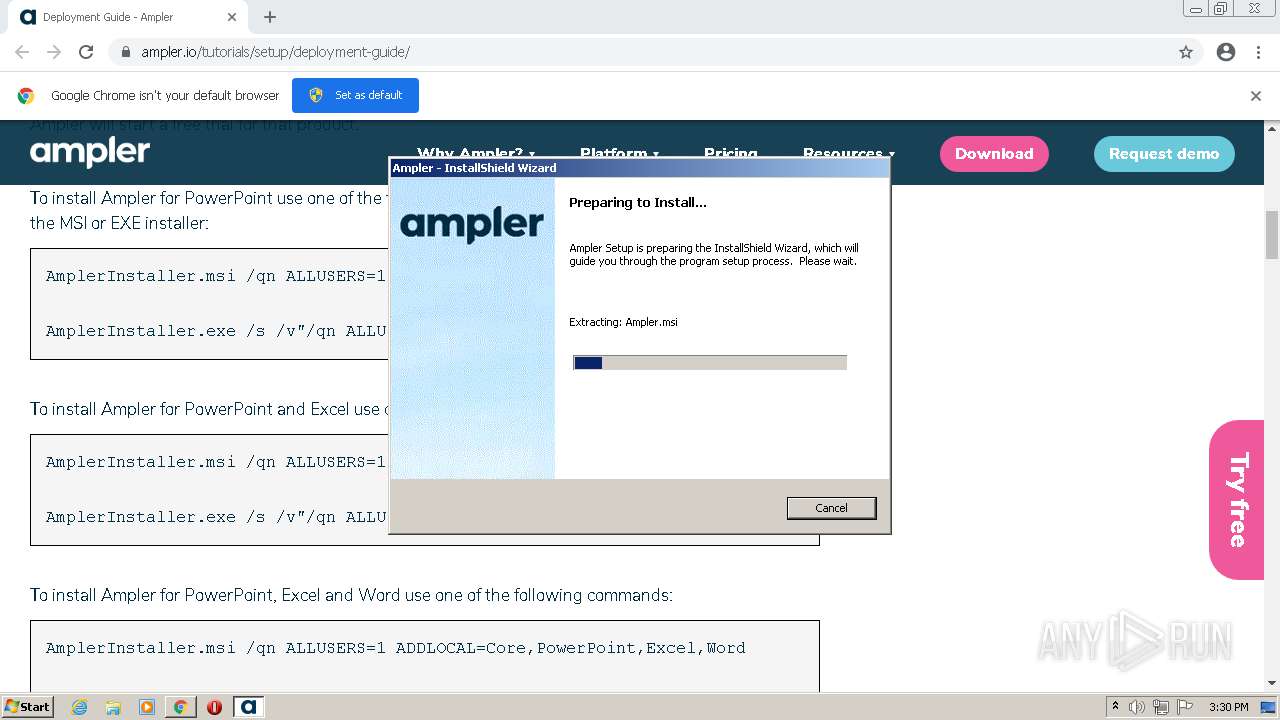
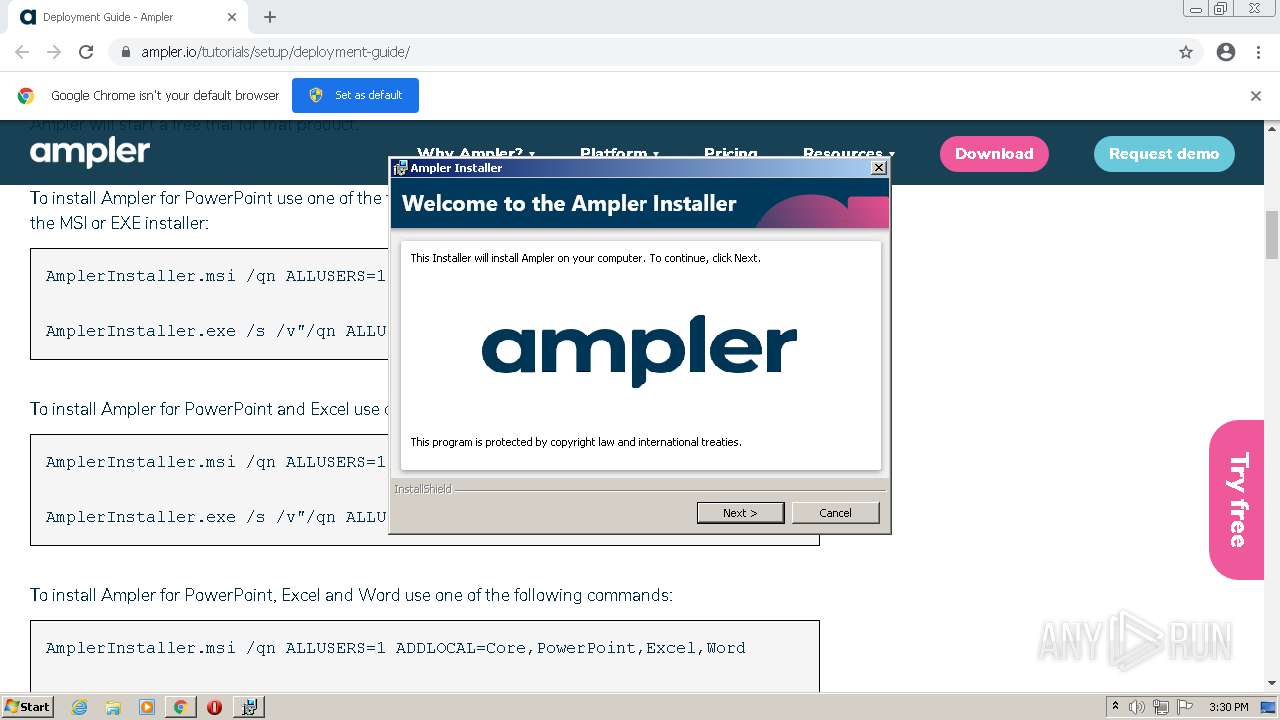
Starts Microsoft Installer
- AmplerInstaller.exe (PID: 864)
Reads Windows owner or organization settings
- MSIEXEC.EXE (PID: 1304)
- msiexec.exe (PID: 276)
Application launched itself
- msiexec.exe (PID: 276)
Reads the Windows organization settings
- MSIEXEC.EXE (PID: 1304)
- msiexec.exe (PID: 276)
Drops a file with too old compile date
- msiexec.exe (PID: 276)
Drops a file that was compiled in debug mode
- msiexec.exe (PID: 276)
- chrome.exe (PID: 3532)
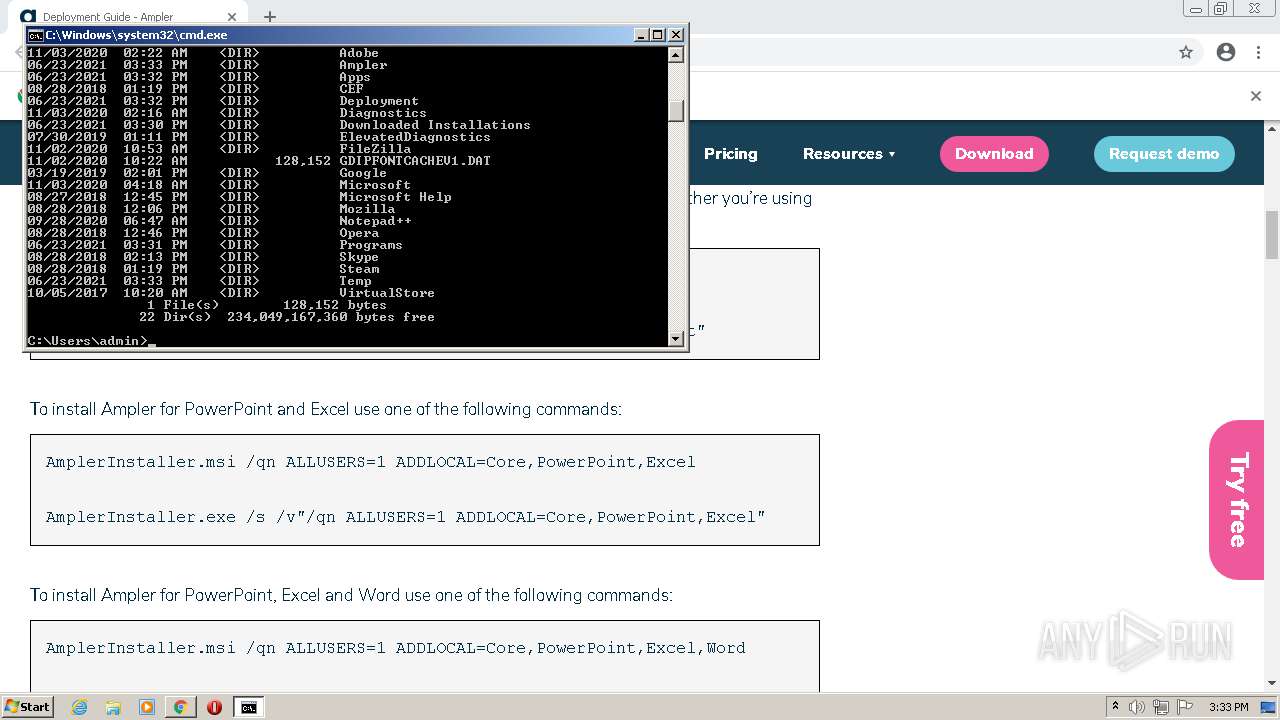
Creates files in the user directory
- msiexec.exe (PID: 276)
- Smart.Jobs.exe (PID: 552)
- Smart.Jobs.exe (PID: 2792)
- Smart.Jobs.exe (PID: 3760)
- Smart.Jobs.exe (PID: 116)
Drops a file with a compile date too recent
- msiexec.exe (PID: 276)
- Smart.Jobs.exe (PID: 2792)
Changes default file association
- msiexec.exe (PID: 276)
Creates a software uninstall entry
- msiexec.exe (PID: 276)
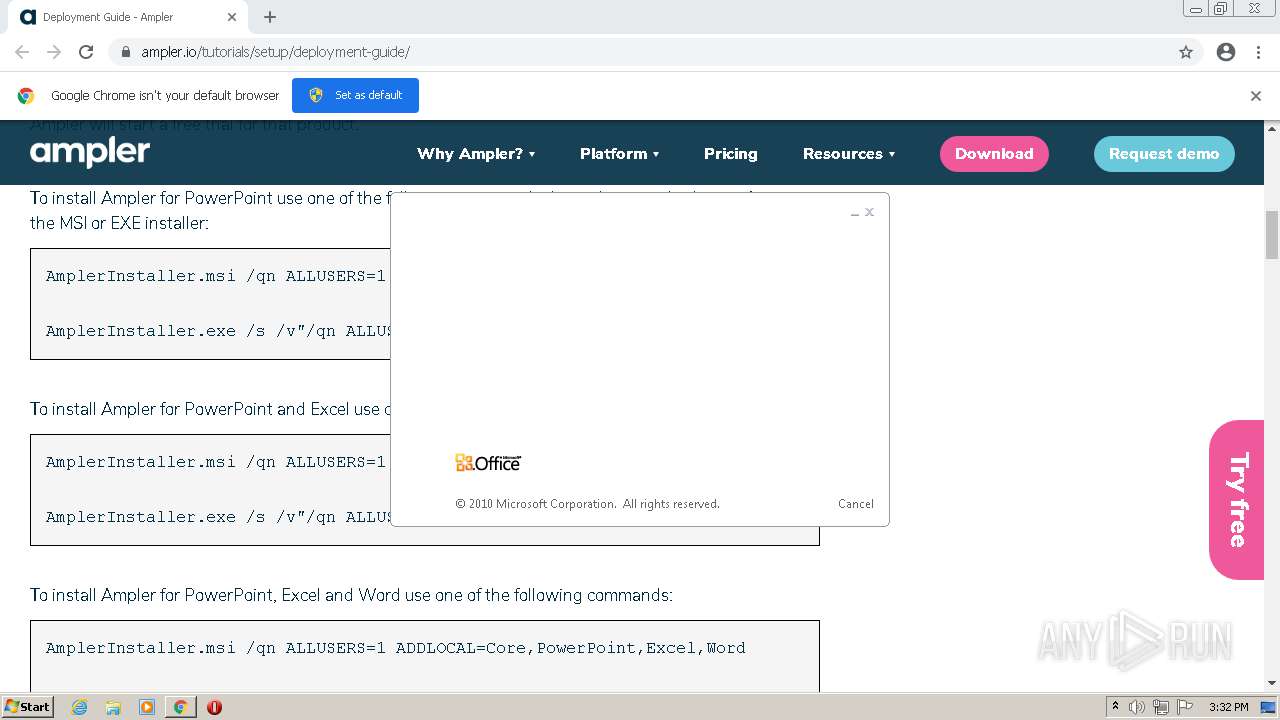
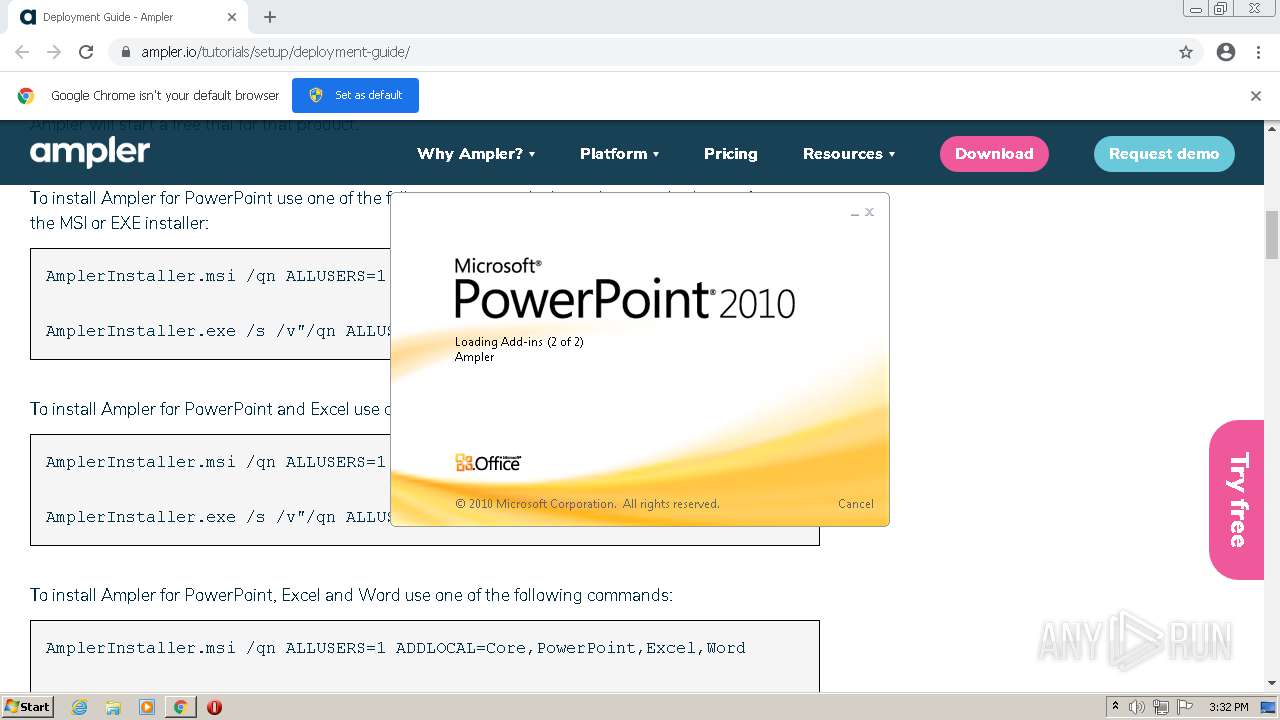
Starts Microsoft Office Application
- MsiExec.exe (PID: 3148)
Executed via Task Scheduler
- Smart.Jobs.exe (PID: 552)
- Smart.Jobs.exe (PID: 3760)
- Smart.Jobs.exe (PID: 2792)
- Smart.Jobs.exe (PID: 116)
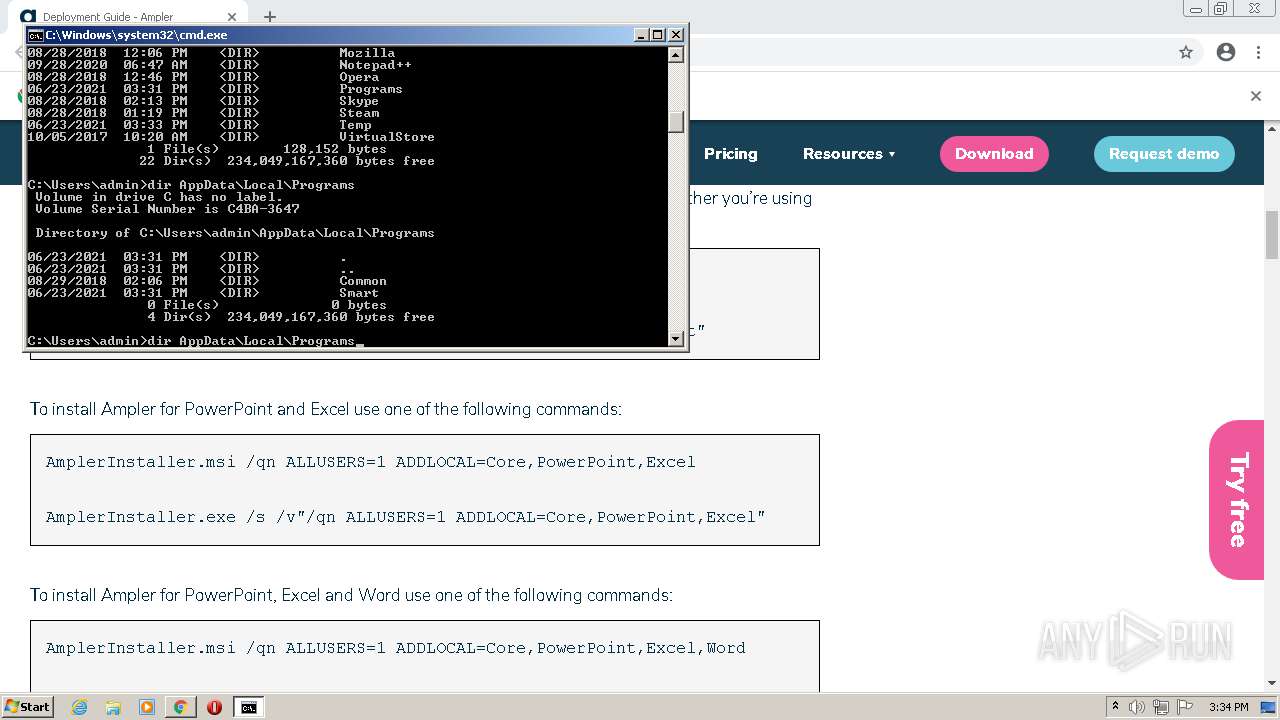
Creates files in the program directory
- Smart.Jobs.exe (PID: 552)
Reads Environment values
- Smart.Jobs.exe (PID: 552)
- Smart.Jobs.exe (PID: 116)
- Smart.Jobs.exe (PID: 3760)
- Smart.Jobs.exe (PID: 2792)
Searches for installed software
- Smart.Jobs.exe (PID: 552)
INFO
Reads the hosts file
- chrome.exe (PID: 2436)
- chrome.exe (PID: 3244)
Checks supported languages
- chrome.exe (PID: 3244)
- chrome.exe (PID: 2436)
- chrome.exe (PID: 2732)
- chrome.exe (PID: 3168)
- chrome.exe (PID: 2524)
- chrome.exe (PID: 2588)
- chrome.exe (PID: 1444)
- chrome.exe (PID: 4004)
- chrome.exe (PID: 3616)
- chrome.exe (PID: 1336)
- chrome.exe (PID: 2364)
- chrome.exe (PID: 1684)
- chrome.exe (PID: 2184)
- chrome.exe (PID: 1336)
- chrome.exe (PID: 2004)
- chrome.exe (PID: 3576)
- chrome.exe (PID: 572)
- chrome.exe (PID: 3568)
- chrome.exe (PID: 2720)
- chrome.exe (PID: 1328)
- MSIEXEC.EXE (PID: 1304)
- msiexec.exe (PID: 276)
- MsiExec.exe (PID: 3148)
- chrome.exe (PID: 2880)
- chrome.exe (PID: 2552)
- chrome.exe (PID: 3152)
- MsiExec.exe (PID: 3292)
- chrome.exe (PID: 1556)
- chrome.exe (PID: 3280)
- chrome.exe (PID: 2104)
- chrome.exe (PID: 2776)
- chrome.exe (PID: 528)
- POWERPNT.EXE (PID: 4012)
- chrome.exe (PID: 2416)
- chrome.exe (PID: 3128)
- chrome.exe (PID: 3532)
- chrome.exe (PID: 2532)
Reads settings of System Certificates
- chrome.exe (PID: 3244)
- chrome.exe (PID: 2436)
- MSIEXEC.EXE (PID: 1304)
- msiexec.exe (PID: 276)
- POWERPNT.EXE (PID: 4012)
- Smart.Jobs.exe (PID: 552)
Reads the computer name
- chrome.exe (PID: 2436)
- chrome.exe (PID: 3616)
- chrome.exe (PID: 3168)
- chrome.exe (PID: 3244)
- chrome.exe (PID: 572)
- chrome.exe (PID: 1684)
- chrome.exe (PID: 2004)
- chrome.exe (PID: 2184)
- chrome.exe (PID: 1336)
- chrome.exe (PID: 2524)
- chrome.exe (PID: 1328)
- MSIEXEC.EXE (PID: 1304)
- msiexec.exe (PID: 276)
- MsiExec.exe (PID: 3148)
- MsiExec.exe (PID: 3292)
- POWERPNT.EXE (PID: 4012)
Application launched itself
- chrome.exe (PID: 2436)
Checks Windows Trust Settings
- chrome.exe (PID: 2436)
- MSIEXEC.EXE (PID: 1304)
- msiexec.exe (PID: 276)
- POWERPNT.EXE (PID: 4012)
Reads the date of Windows installation
- chrome.exe (PID: 1336)
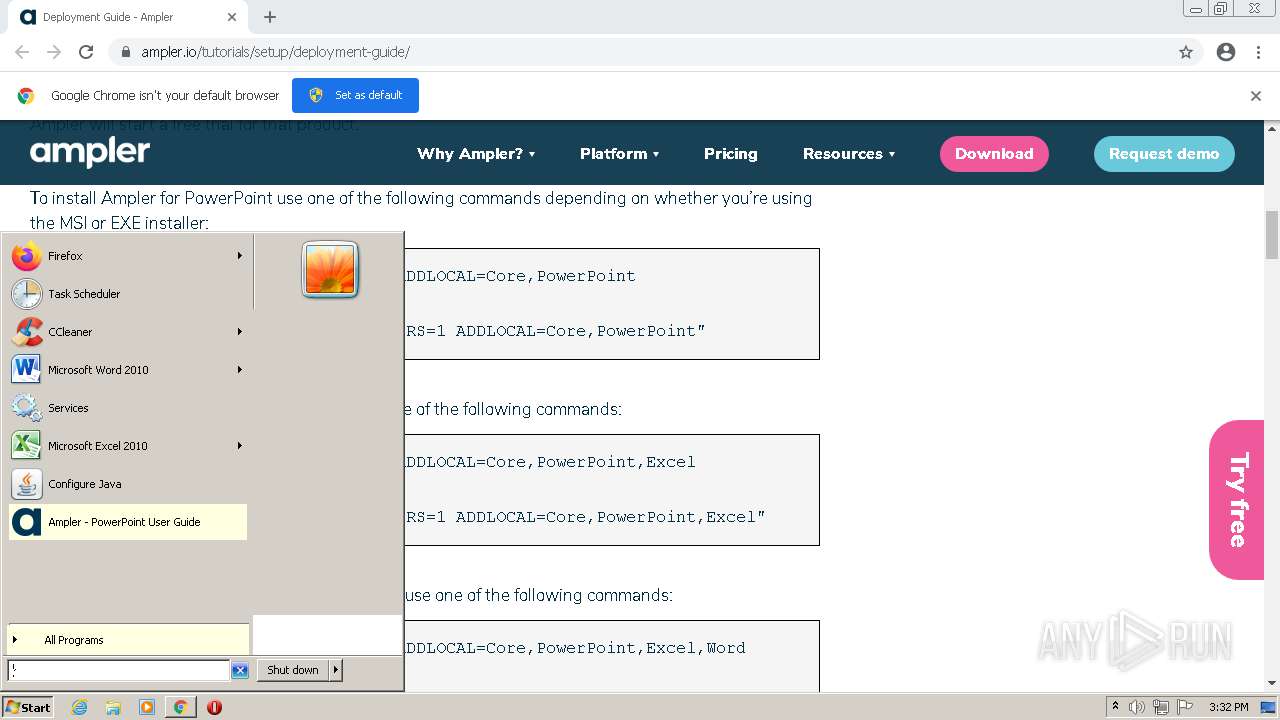
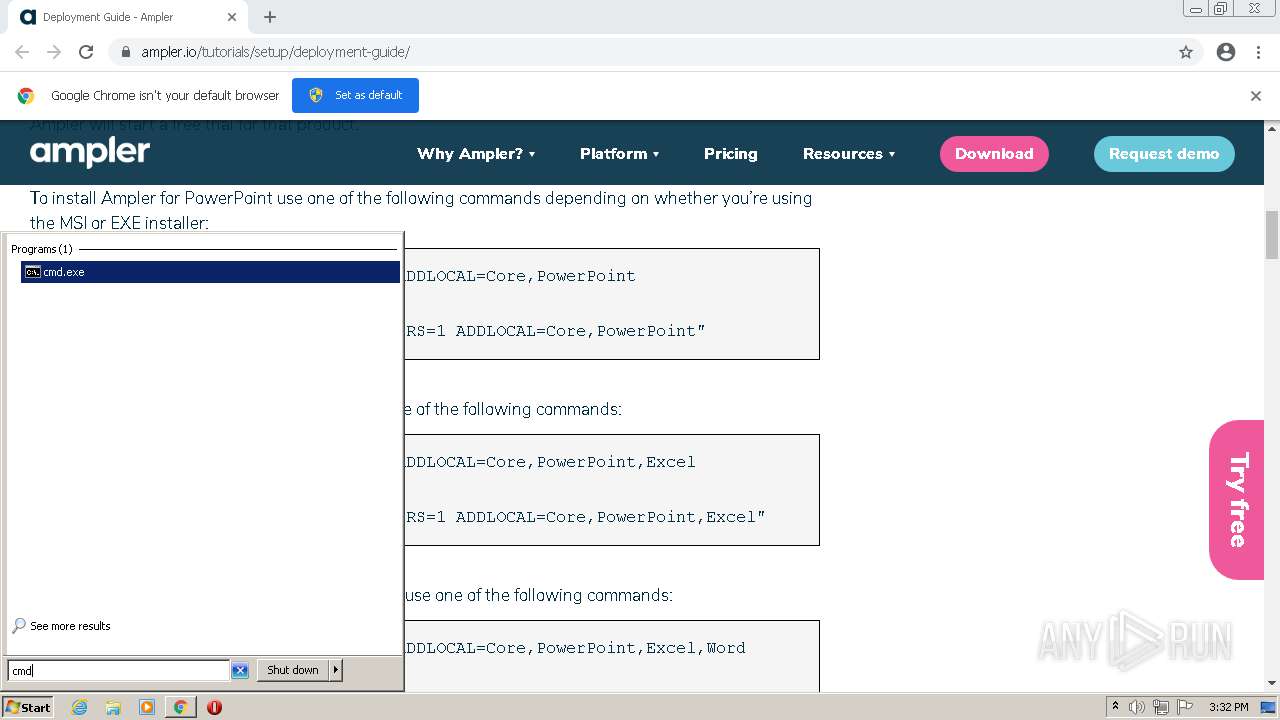
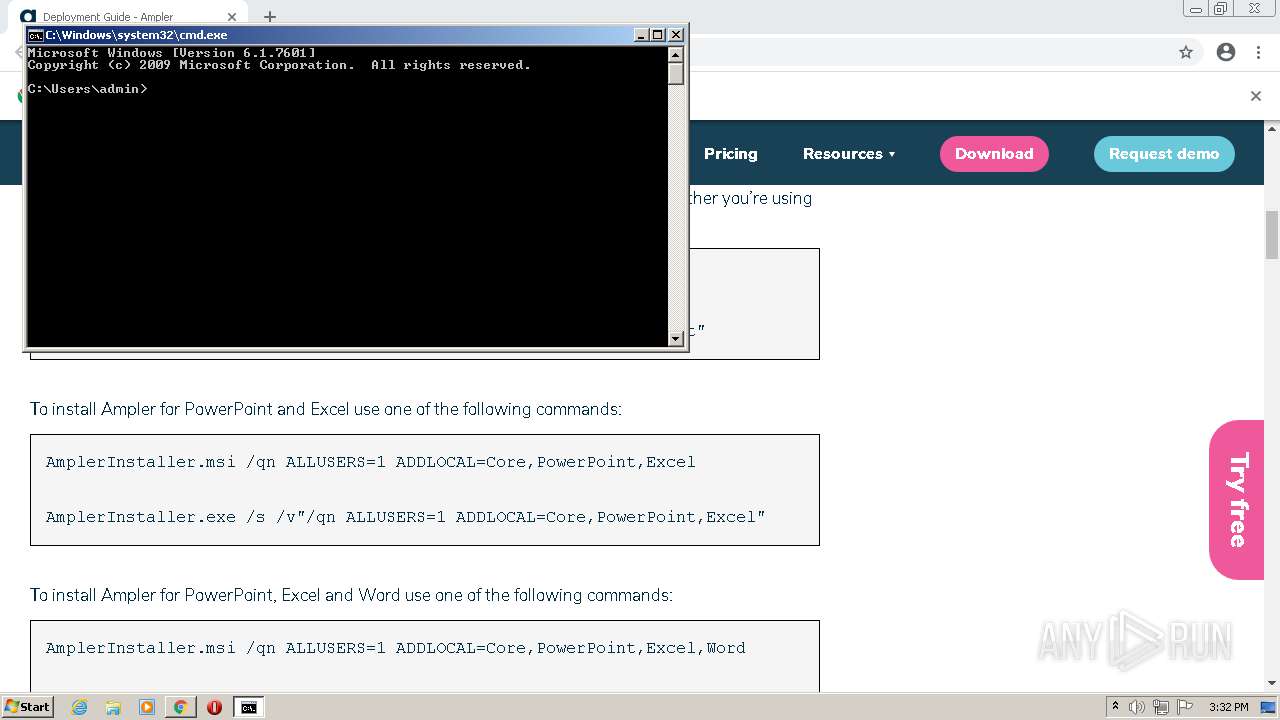
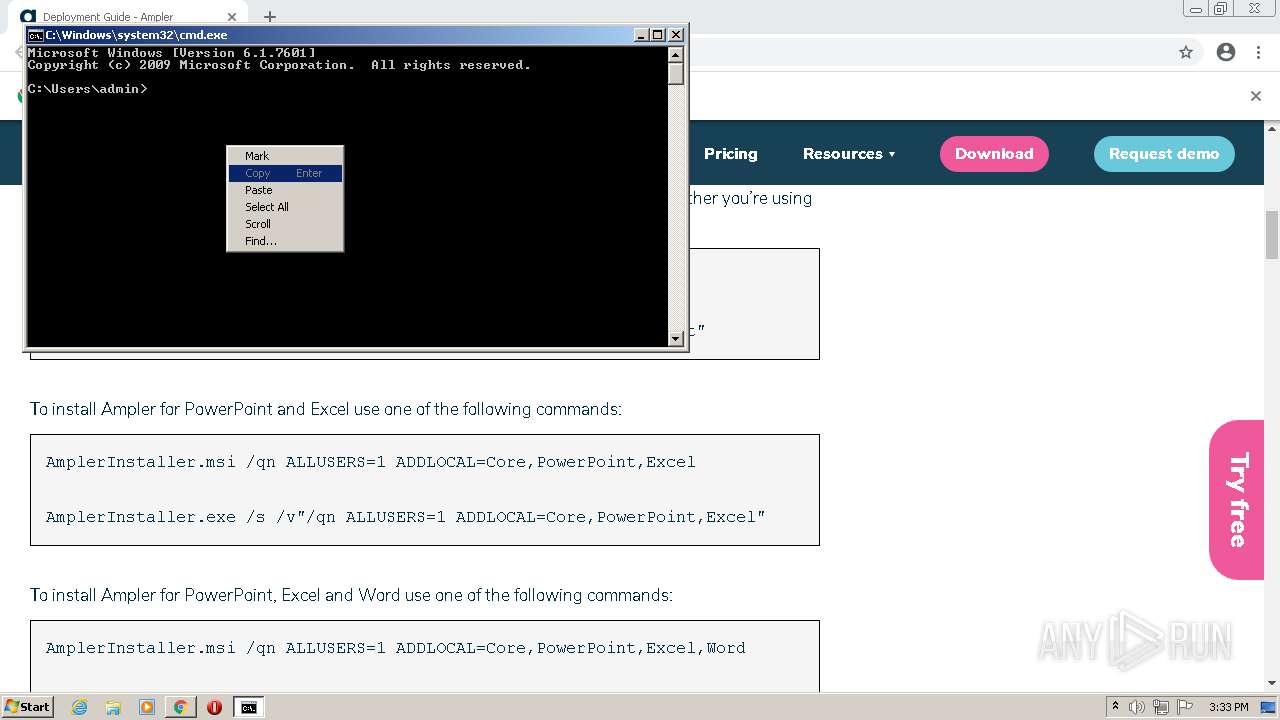
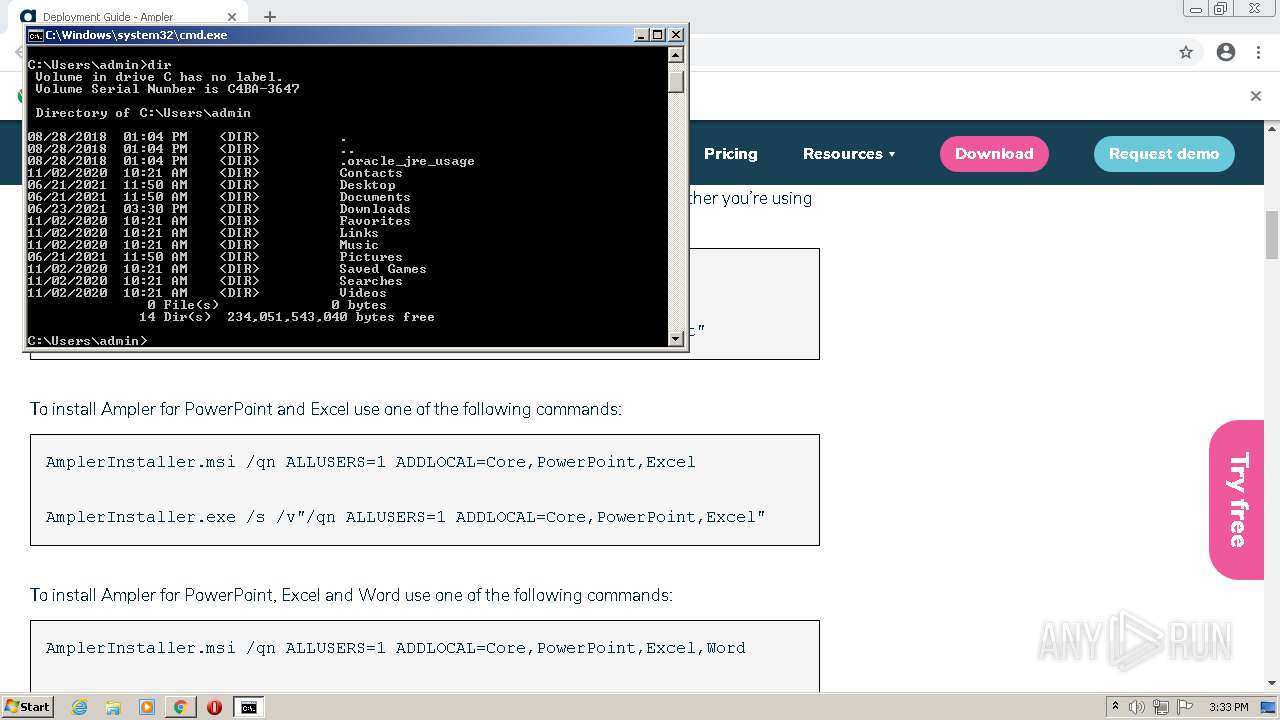
Manual execution by user
- cmd.exe (PID: 3716)
Reads Microsoft Office registry keys
- POWERPNT.EXE (PID: 4012)
- Smart.Jobs.exe (PID: 552)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
124
Monitored processes
63
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
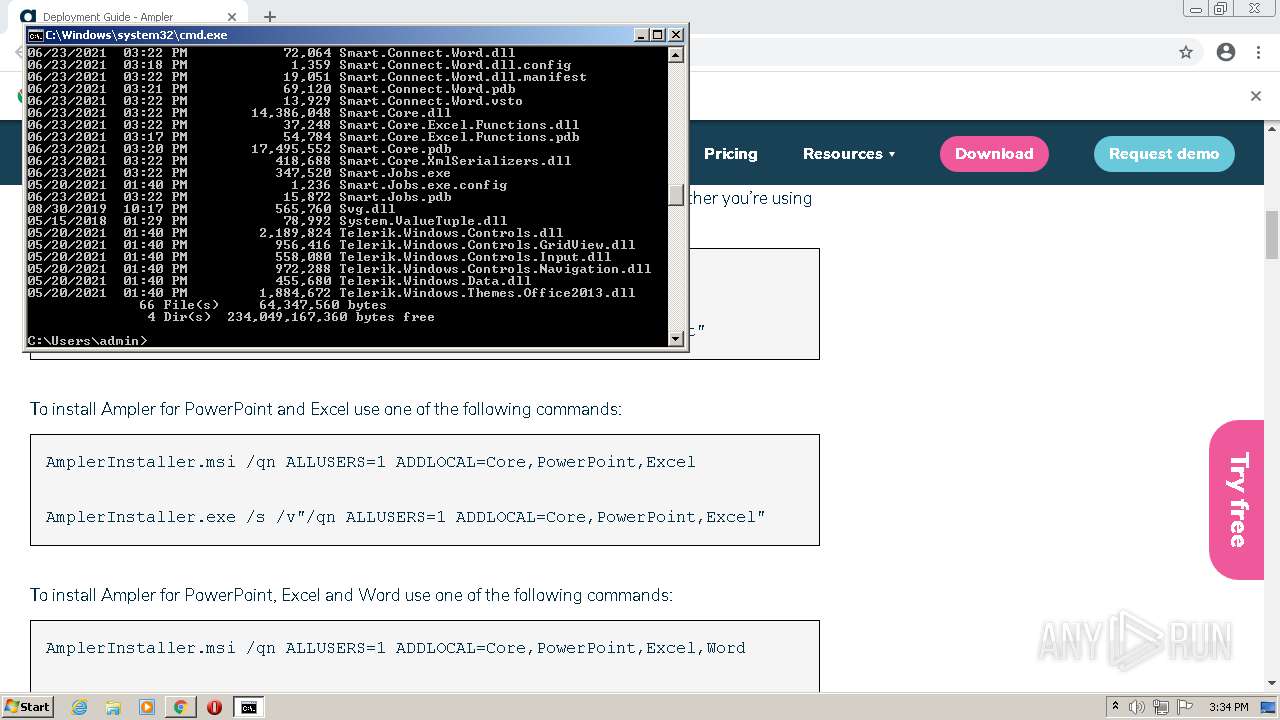
| 116 | C:\Users\admin\AppData\Local\Programs\Smart\SmartTools\Smart.Jobs.exe -Synchronize -App=Word | C:\Users\admin\AppData\Local\Programs\Smart\SmartTools\Smart.Jobs.exe | — | taskeng.exe | |||||||||||
User: admin Company: Ampler Integrity Level: MEDIUM Description: Ampler Exit code: 1 Version: 21.6.1030 Modules
| |||||||||||||||
| 276 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 360 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe" install "C:\Users\admin\AppData\Local\Programs\Smart\SmartTools\Smart.Core.dll" /nologo /silent | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe | — | MsiExec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Common Language Runtime native compiler Exit code: 4294967295 Version: 4.0.30319.34209 built by: FX452RTMGDR Modules
| |||||||||||||||
| 396 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe" install "C:\Users\admin\AppData\Local\Programs\Smart\SmartTools\Telerik.Windows.Themes.Office2013.dll" /nologo /silent | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe | — | MsiExec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Common Language Runtime native compiler Exit code: 4294967295 Version: 4.0.30319.34209 built by: FX452RTMGDR Modules
| |||||||||||||||
| 528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1032,17188520439176275277,1573488837539348581,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=816 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 552 | C:\Users\admin\AppData\Local\Programs\Smart\SmartTools\Smart.Jobs.exe -Update -Context=User | C:\Users\admin\AppData\Local\Programs\Smart\SmartTools\Smart.Jobs.exe | taskeng.exe | ||||||||||||
User: admin Company: Ampler Integrity Level: MEDIUM Description: Ampler Exit code: 0 Version: 21.6.1030 Modules
| |||||||||||||||
| 572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1032,17188520439176275277,1573488837539348581,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2236 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 864 | "C:\Users\admin\Downloads\AmplerInstaller.exe" | C:\Users\admin\Downloads\AmplerInstaller.exe | — | chrome.exe | |||||||||||
User: admin Company: Ampler Integrity Level: MEDIUM Description: Ampler Installer Exit code: 0 Version: 21.6.1030 Modules
| |||||||||||||||
| 884 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe" uninstall "Smart.Connect.Excel" /nologo /silent | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe | — | MsiExec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Common Language Runtime native compiler Exit code: 4294967295 Version: 4.0.30319.34209 built by: FX452RTMGDR Modules
| |||||||||||||||
| 968 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe" install "C:\Users\admin\AppData\Local\Programs\Smart\SmartTools\Smart.Connect.Word.dll" /nologo /silent | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe | — | MsiExec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Common Language Runtime native compiler Exit code: 4294967295 Version: 4.0.30319.34209 built by: FX452RTMGDR Modules
| |||||||||||||||
Total events
47 825
Read events
47 273
Write events
522
Delete events
30
Modification events
| (PID) Process: | (2436) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2436) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2436) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2436) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2436) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2436) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2436) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2436) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2436) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2436) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
55
Suspicious files
46
Text files
223
Unknown types
51
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2436 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-60D34547-984.pma | — | |
MD5:— | SHA256:— | |||
| 2436 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\8ec8097b-46a3-4bc5-a2eb-87784a88baac.tmp | text | |
MD5:— | SHA256:— | |||
| 2436 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 2436 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFd5479.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 2436 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RFd5499.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 2436 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFd5489.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 2436 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 2436 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 2436 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 2436 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
37
TCP/UDP connections
41
DNS requests
24
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1796 | svchost.exe | HEAD | 200 | 142.250.184.240:80 | http://storage.googleapis.com/update-delta/khaoiebndkojlmppeemjhbpbandiljpe/43/42/e0b8b1fb7c27acac43c236b9f6b029b07f2a3b661b5d8eed22848180aaf4f04e.crxd | US | — | — | whitelisted |
1796 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 7.12 Kb | whitelisted |
1796 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 9.93 Kb | whitelisted |
1796 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 178 Kb | whitelisted |
1796 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 88.7 Kb | whitelisted |
1796 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AM2tNAkwbz_9gDr7uyHgdAI_2654/M0ljB1PD9Udfr4jpk7RksQ | US | binary | 19.6 Kb | whitelisted |
1796 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 43.7 Kb | whitelisted |
1796 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 19.6 Kb | whitelisted |
1796 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ | US | crx | 2.85 Kb | whitelisted |
1796 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTQ3QUFYQzF5VF9DcWNsa0ZkMGdTQmdvQQ/1.0.0.8_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | crx | 12.1 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3244 | chrome.exe | 93.191.156.176:443 | ampler.io | Zitcom A/S | DK | unknown |
3244 | chrome.exe | 142.250.185.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3244 | chrome.exe | 142.250.185.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
3244 | chrome.exe | 142.250.185.77:443 | accounts.google.com | Google Inc. | US | suspicious |
3244 | chrome.exe | 142.250.181.227:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3244 | chrome.exe | 142.250.185.168:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
3244 | chrome.exe | 13.224.193.24:443 | sc.lfeeder.com | — | US | suspicious |
3244 | chrome.exe | 185.59.220.199:443 | load.sumo.com | Datacamp Limited | DE | suspicious |
3244 | chrome.exe | 172.217.18.110:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3244 | chrome.exe | 13.225.74.13:443 | tr.lfeeder.com | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
ampler.io |
| unknown |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
code.jquery.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
sc.lfeeder.com |
| whitelisted |
s.w.org |
| whitelisted |
load.sumo.com |
| whitelisted |