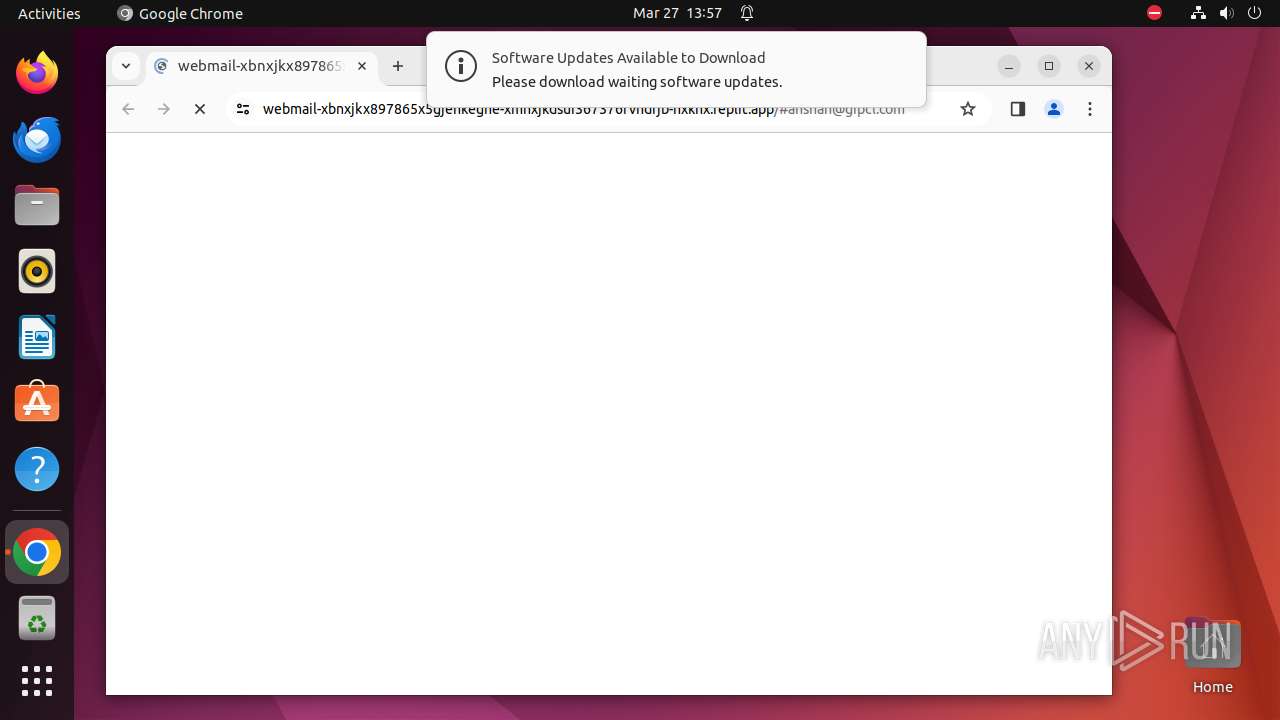
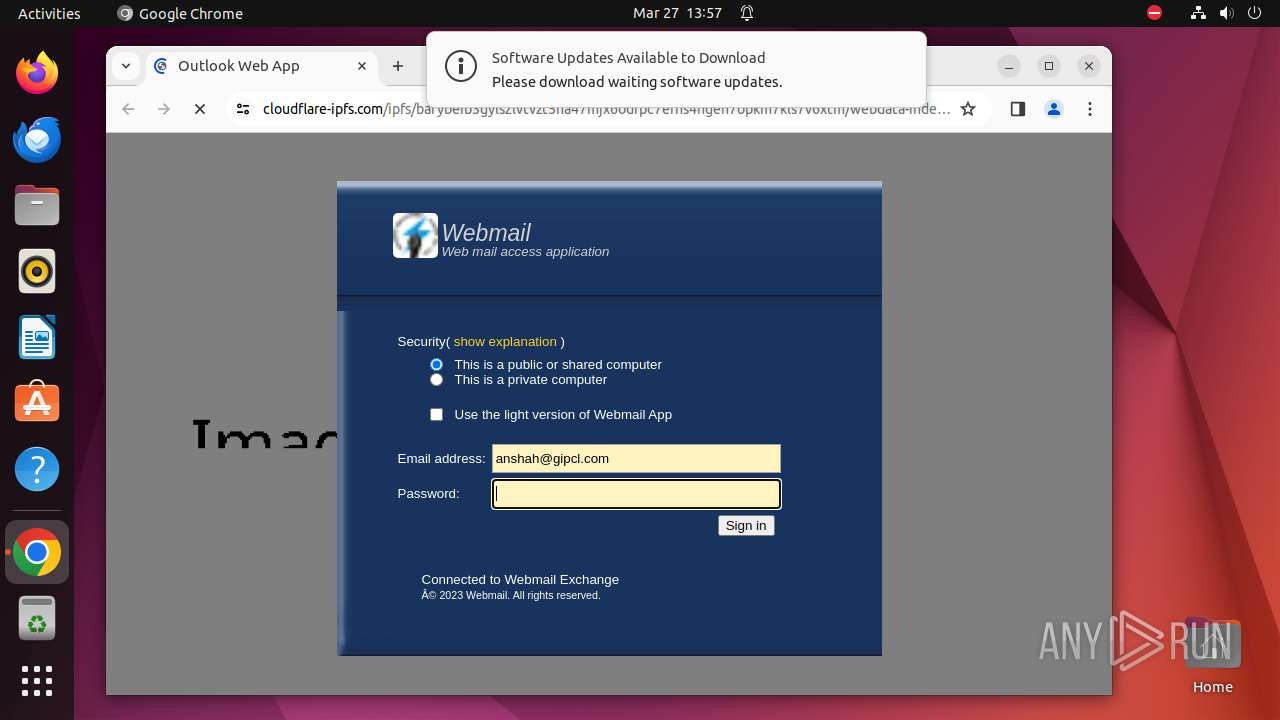
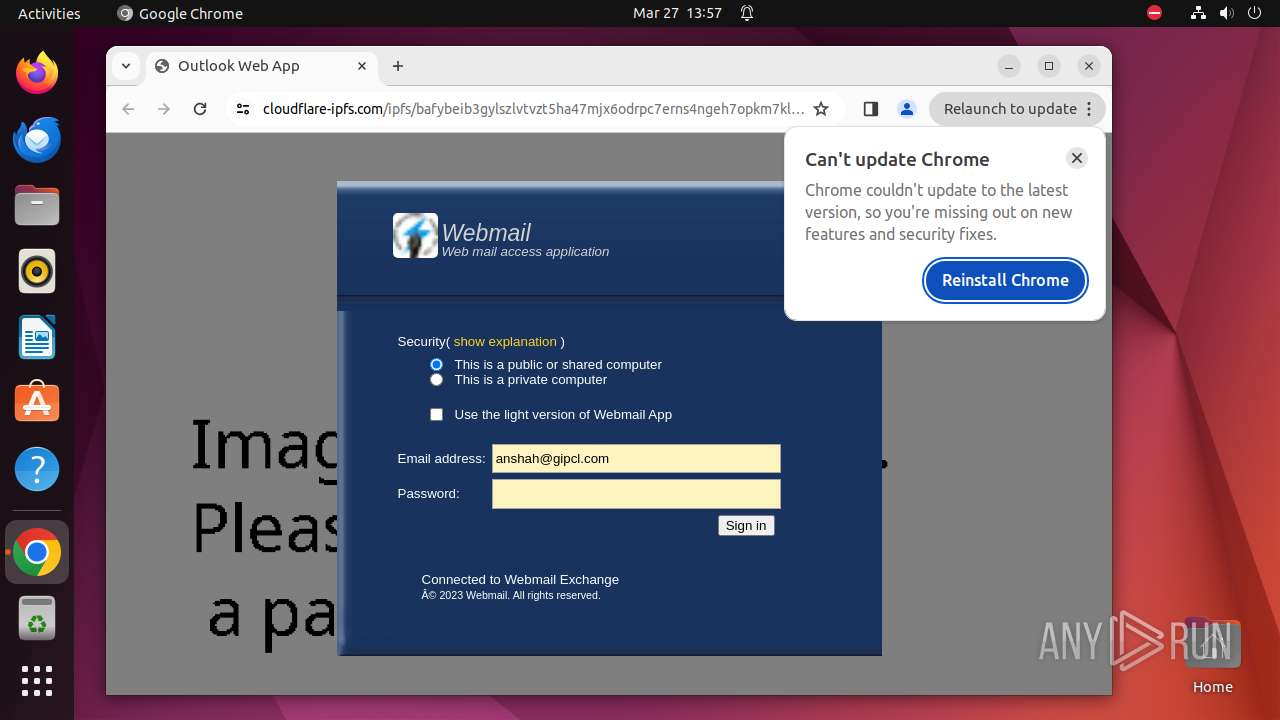
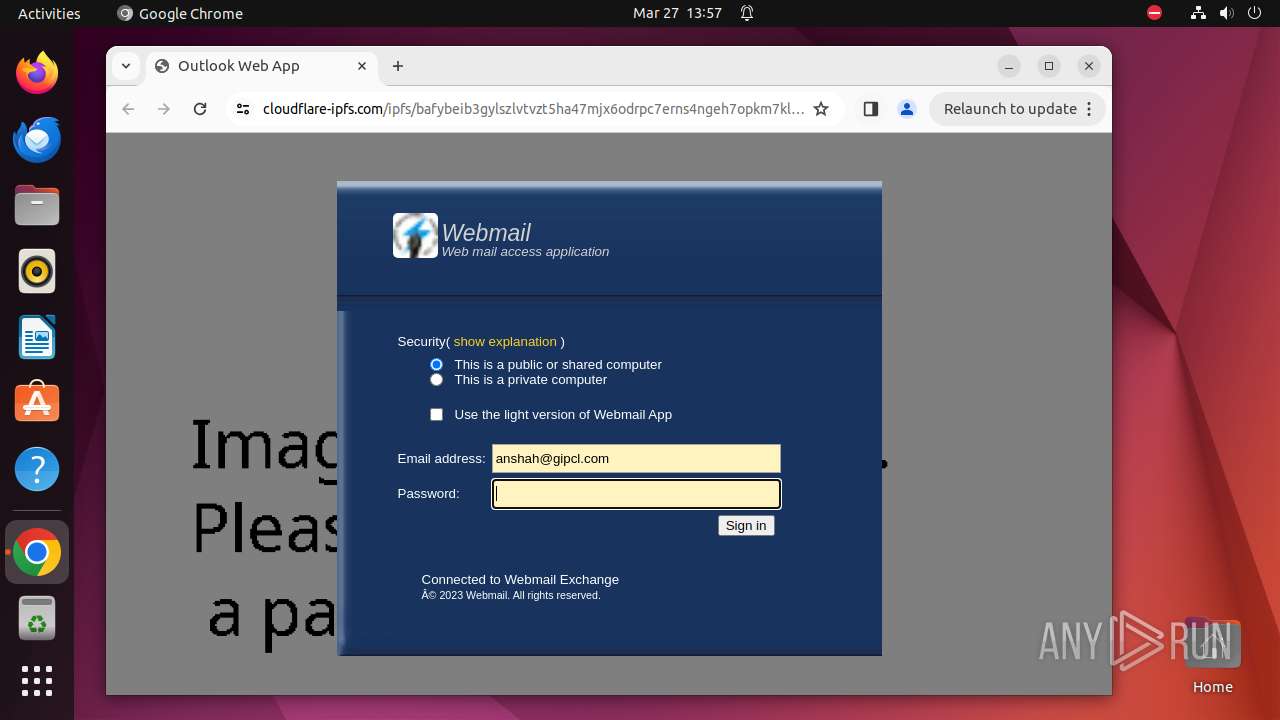
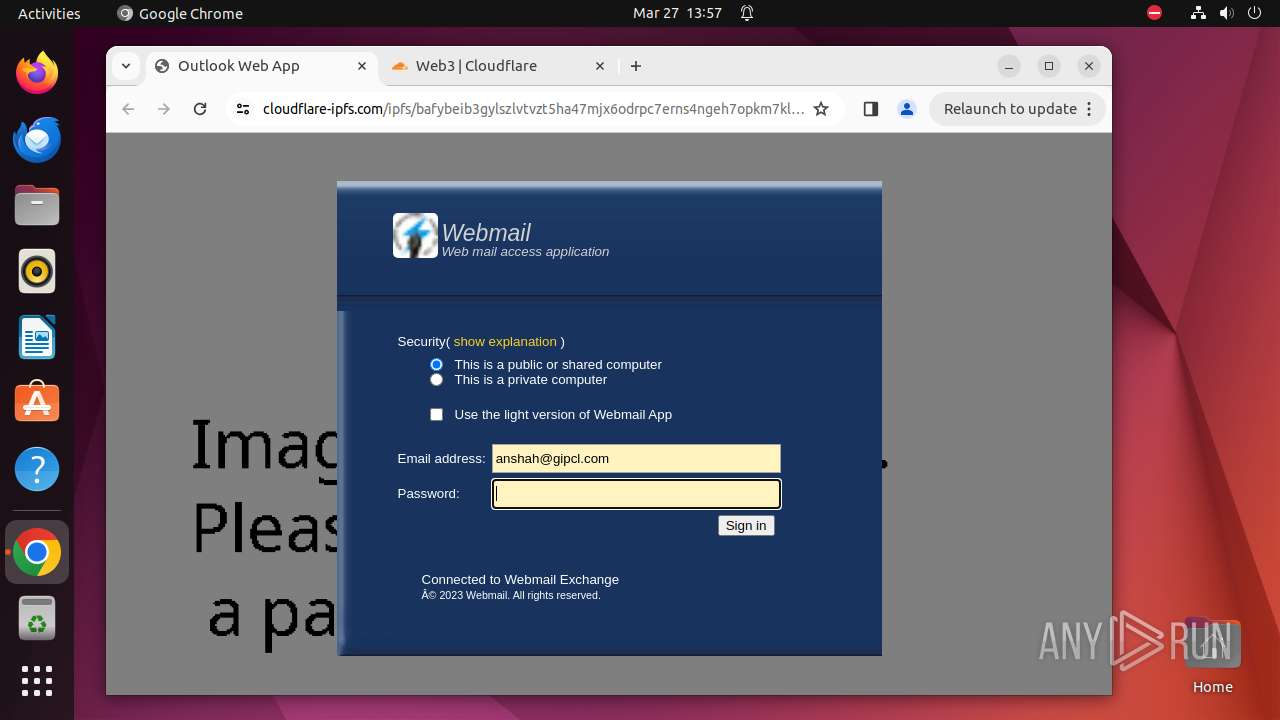
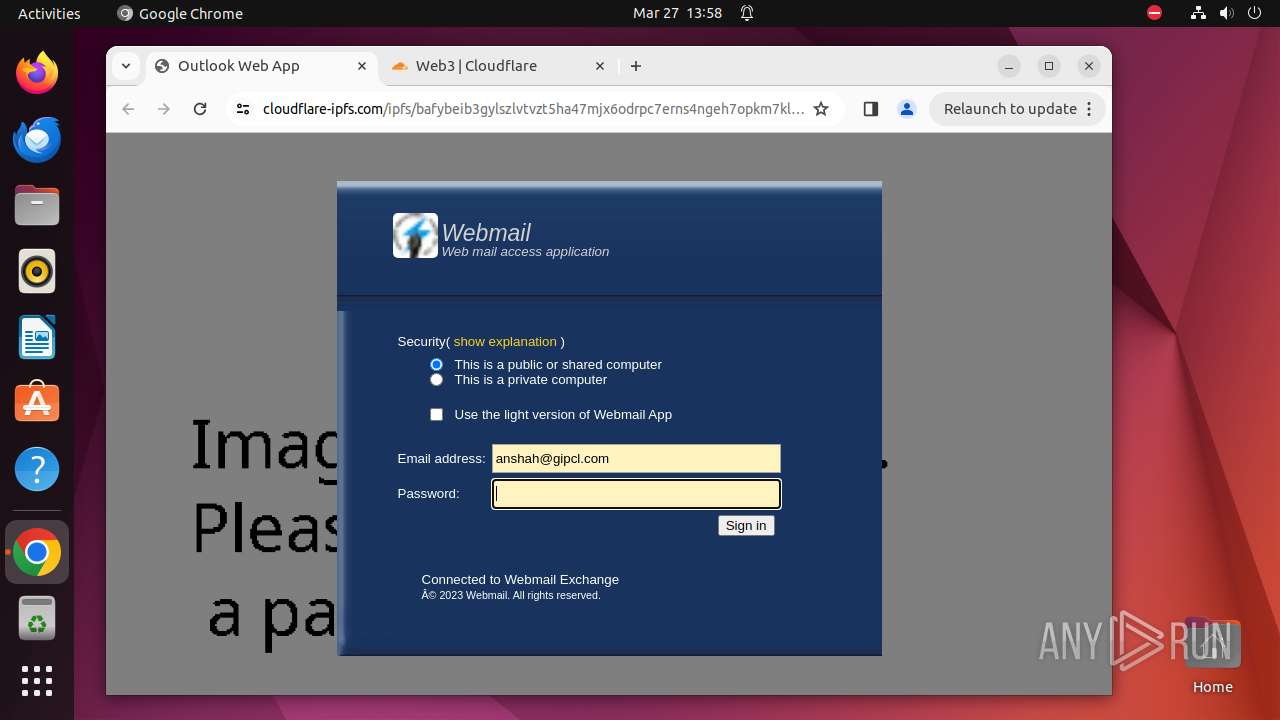
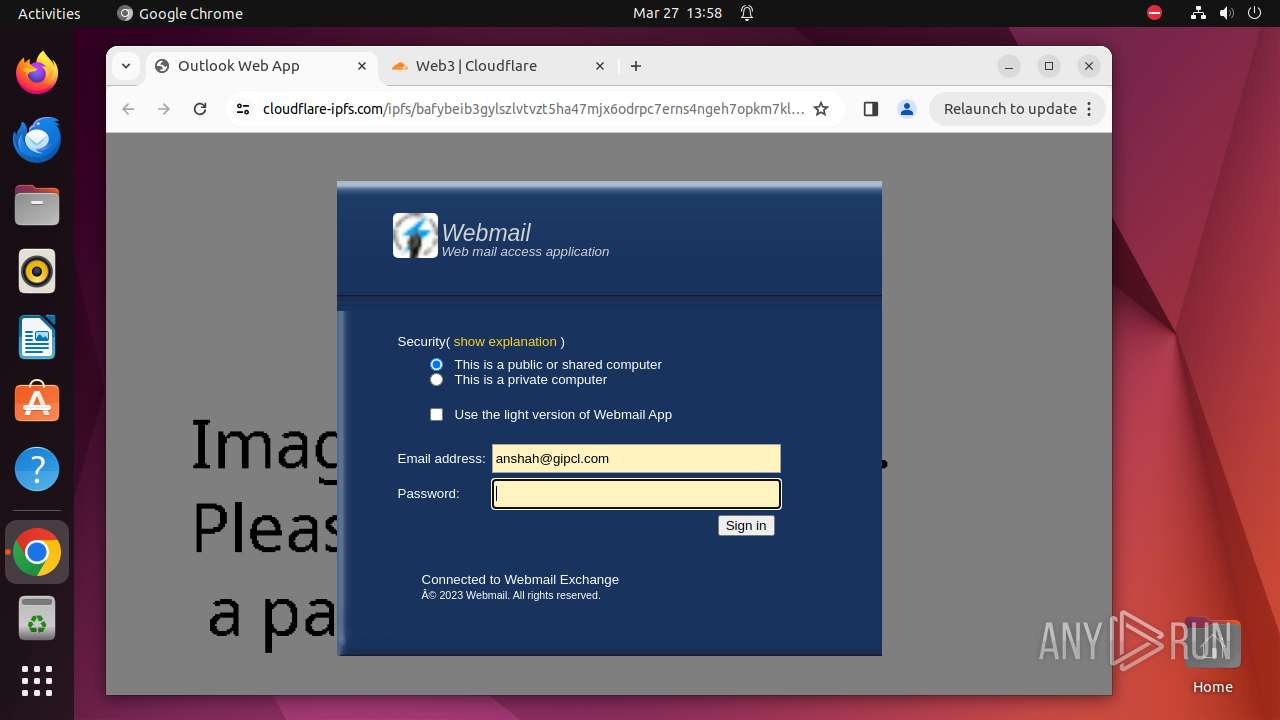
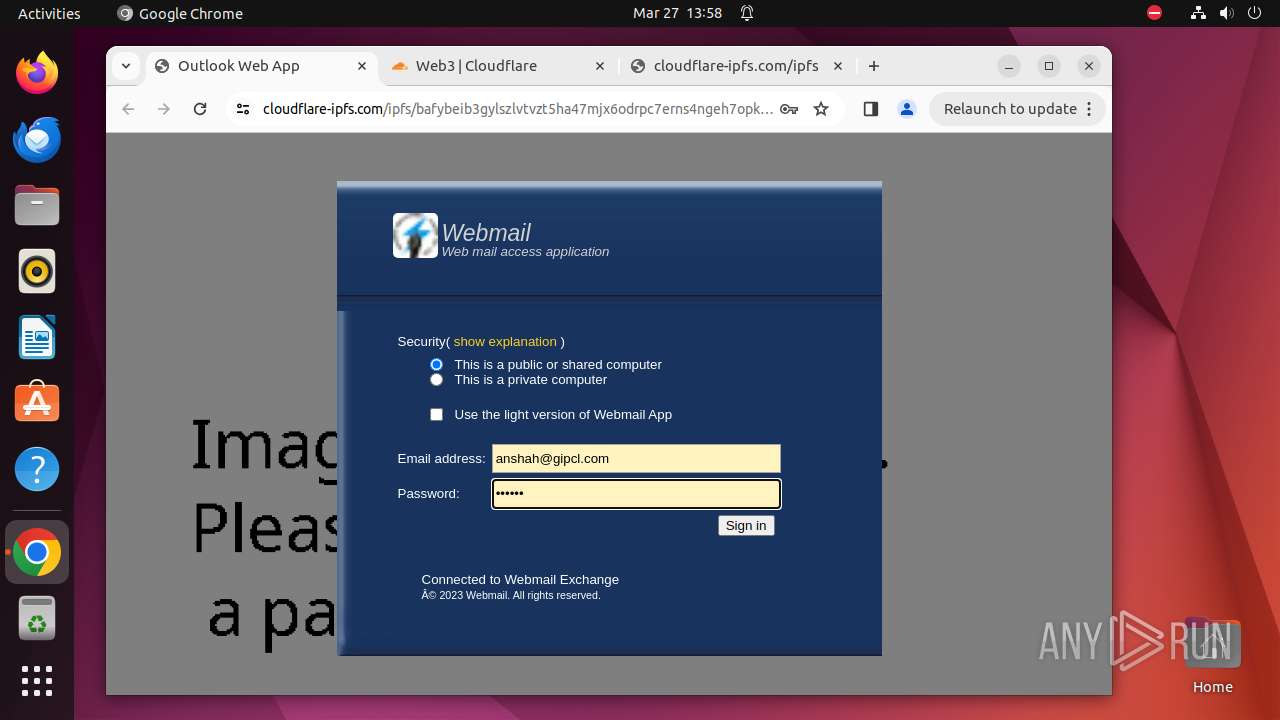
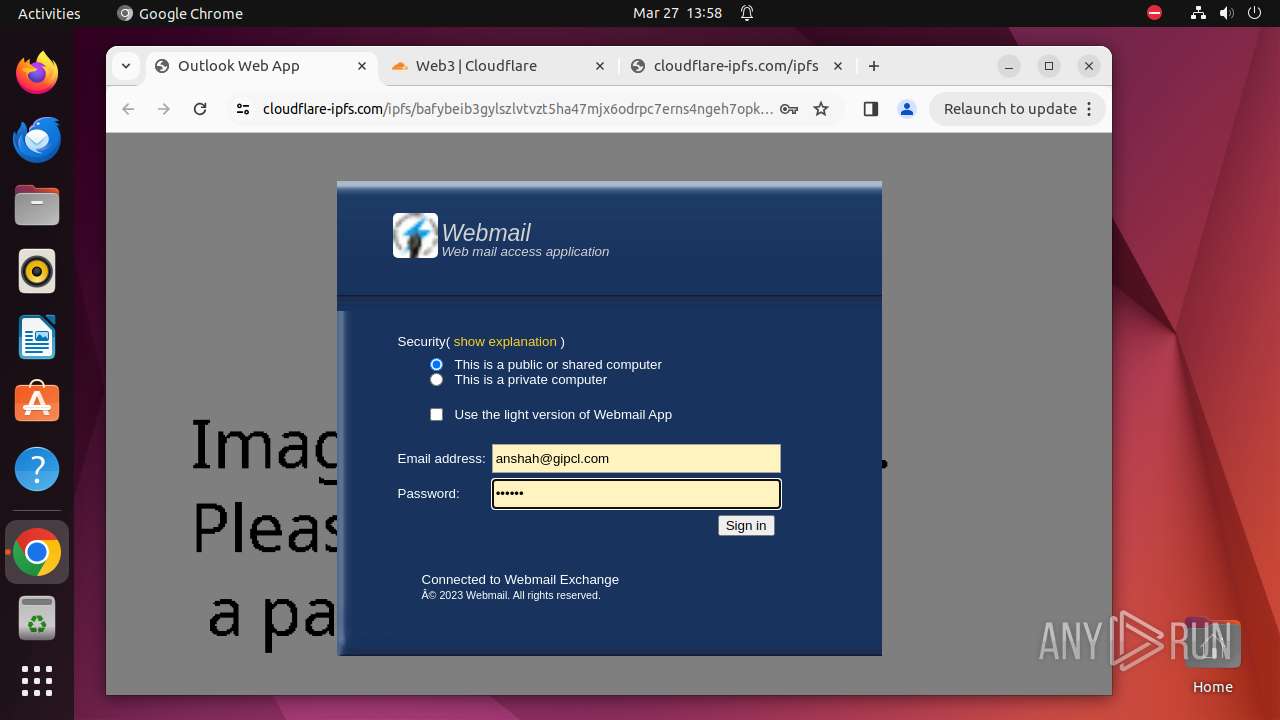
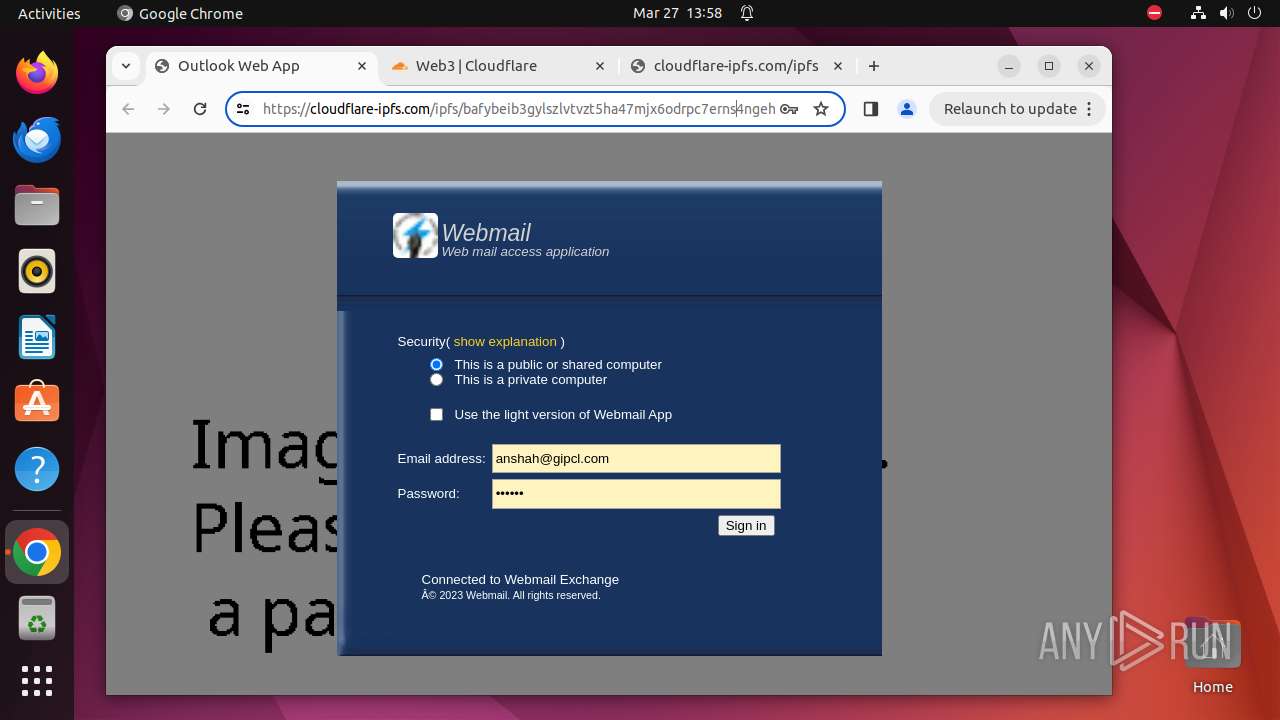
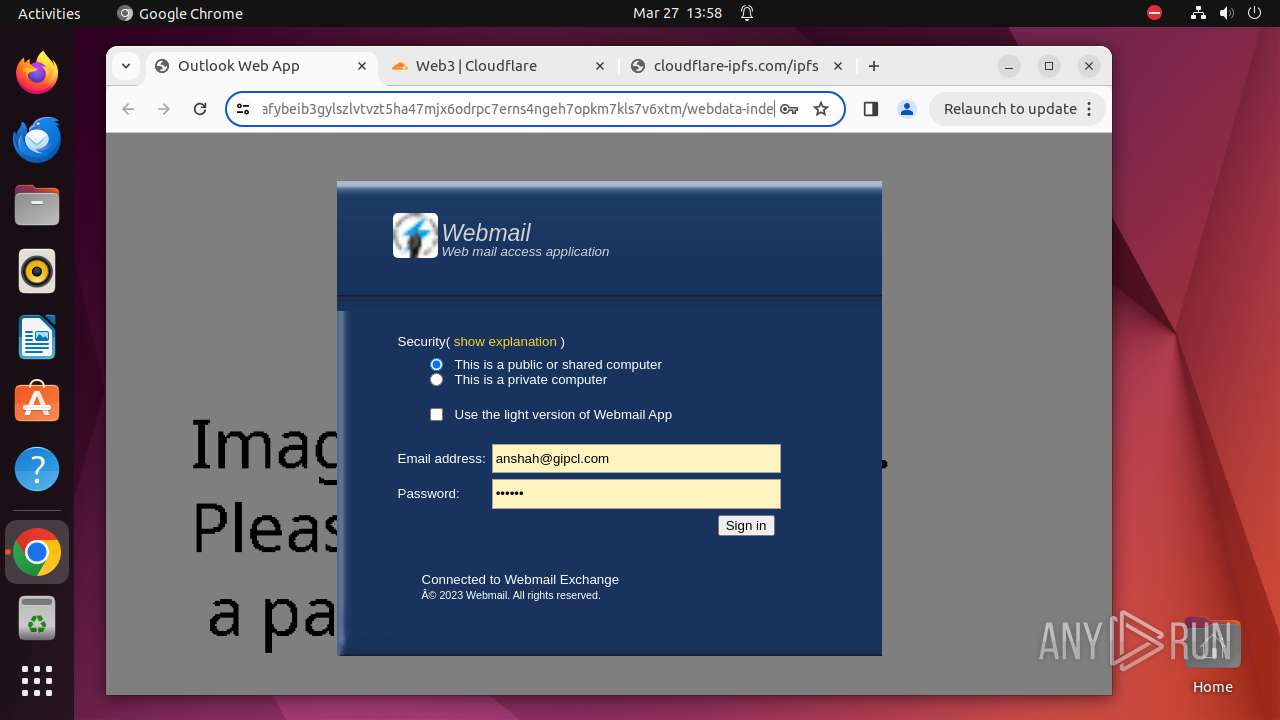
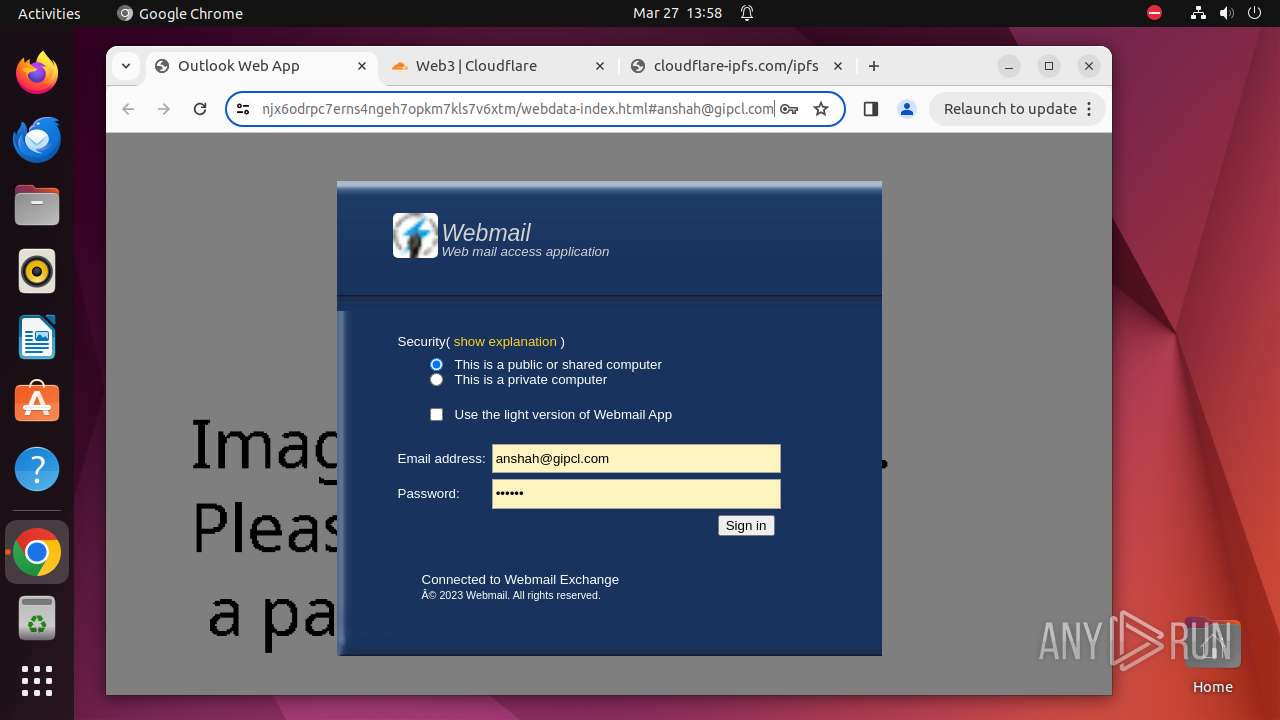
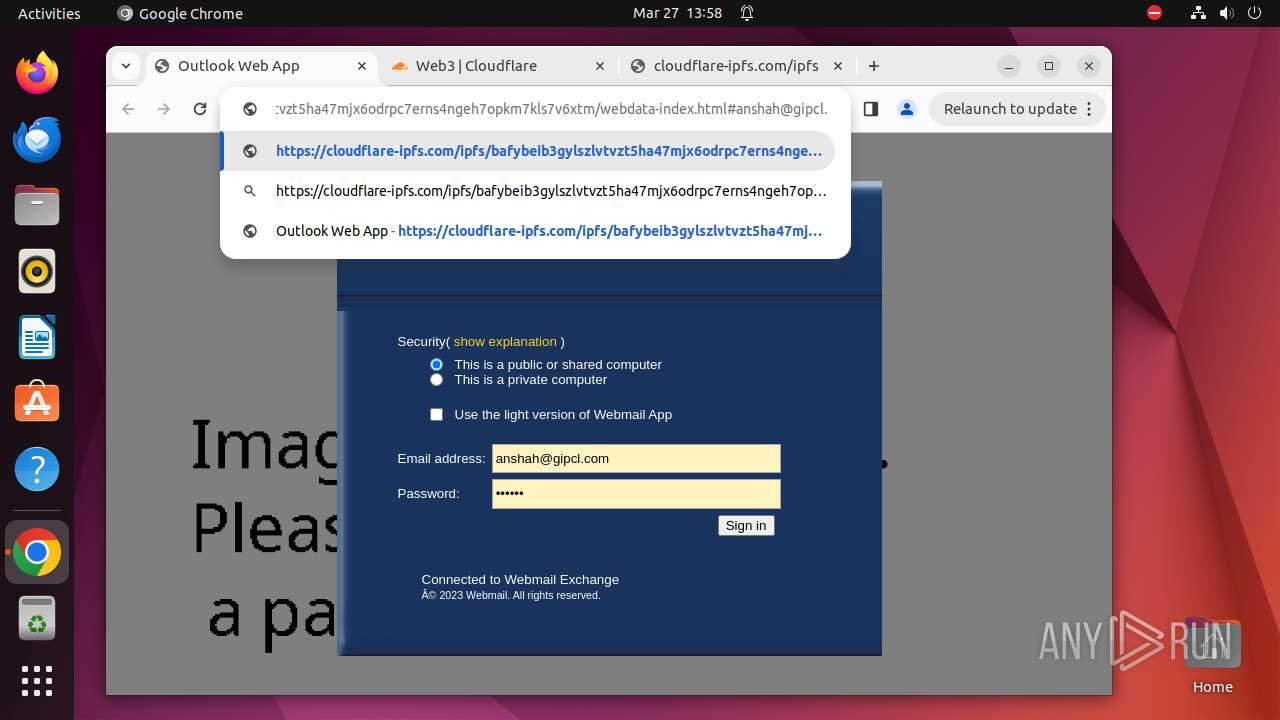
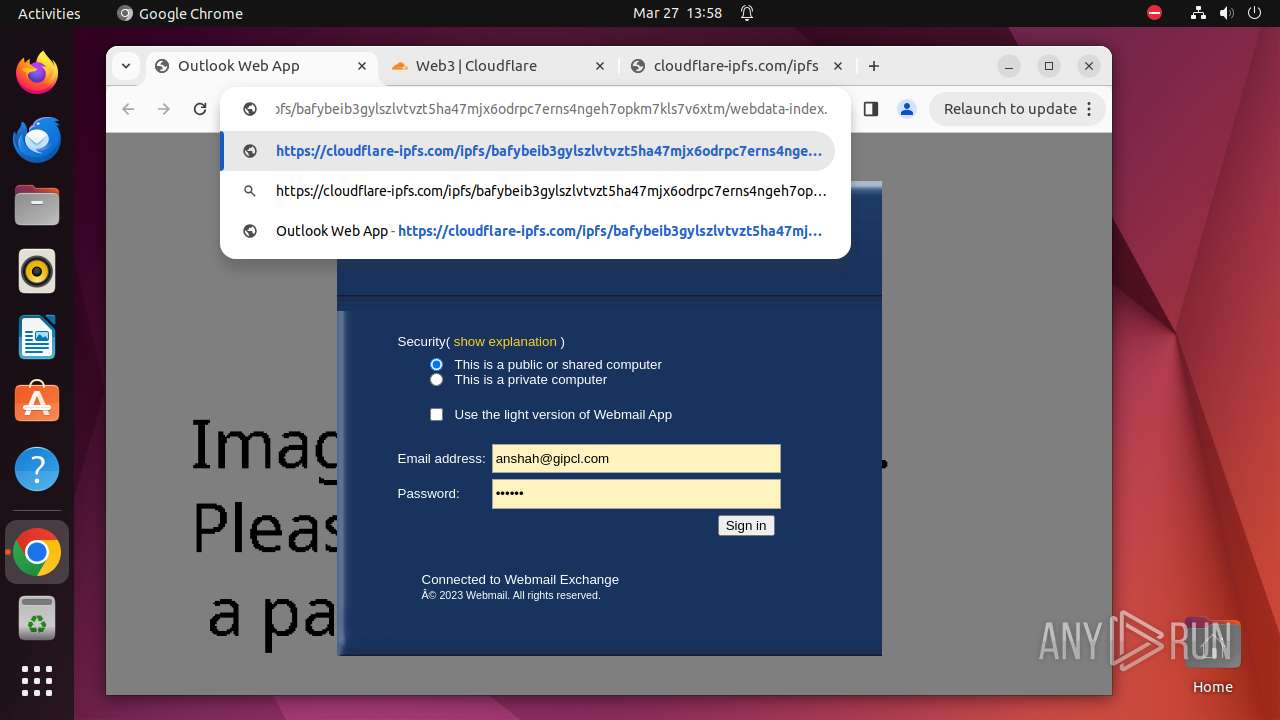
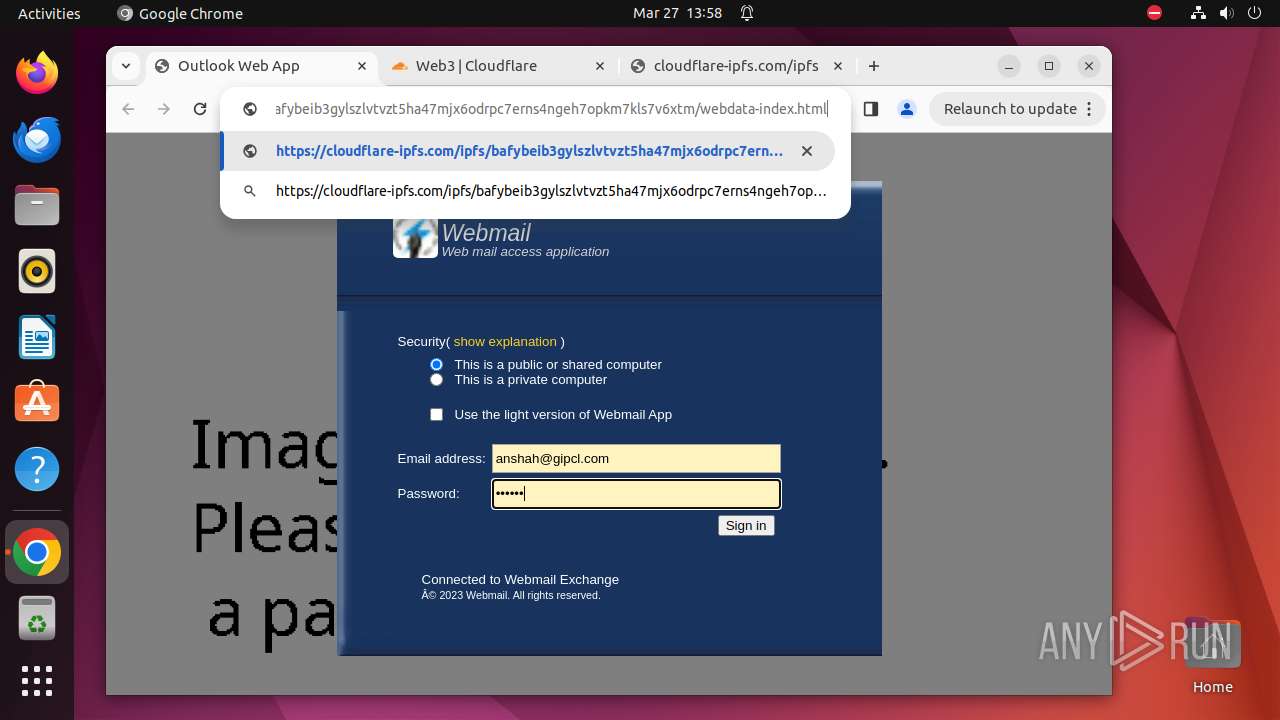
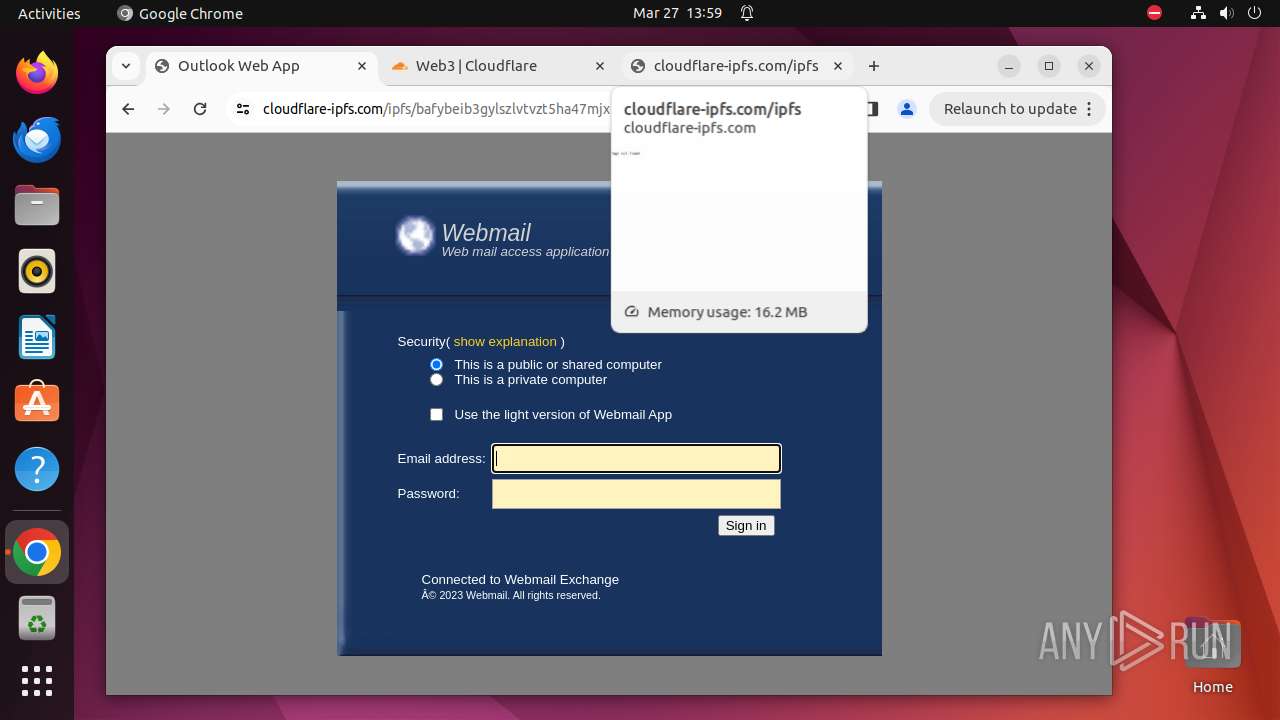
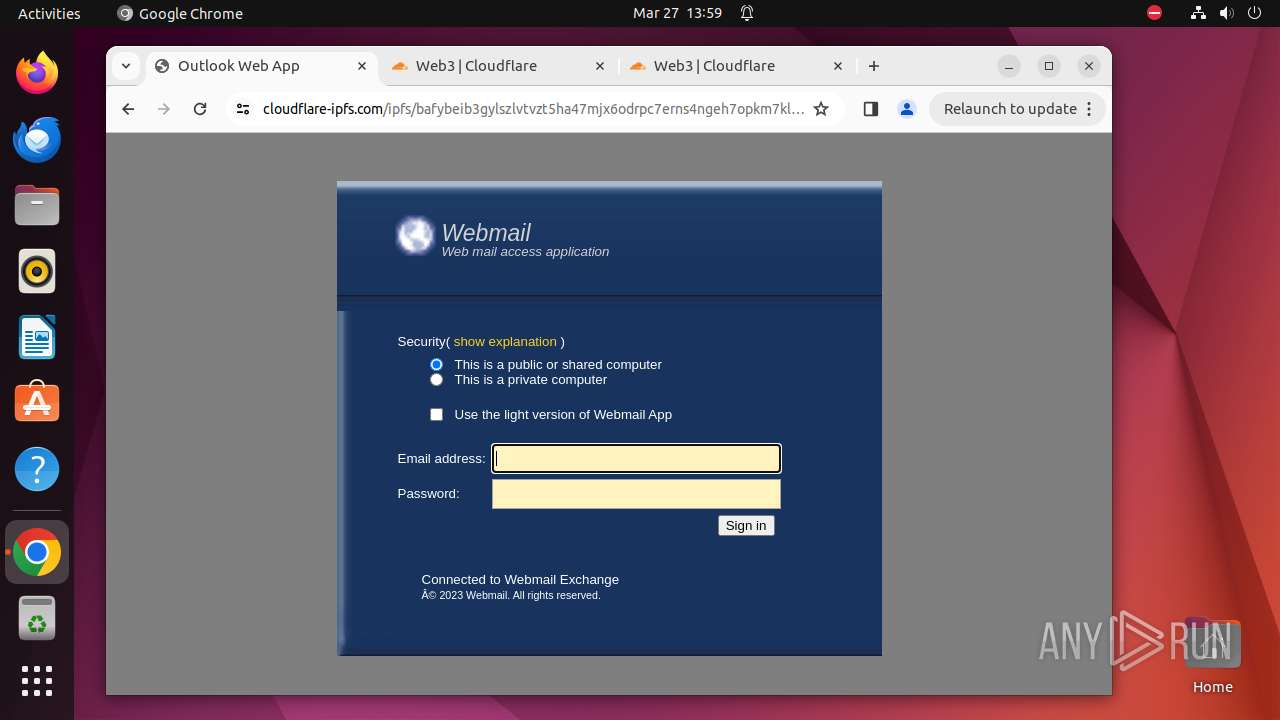
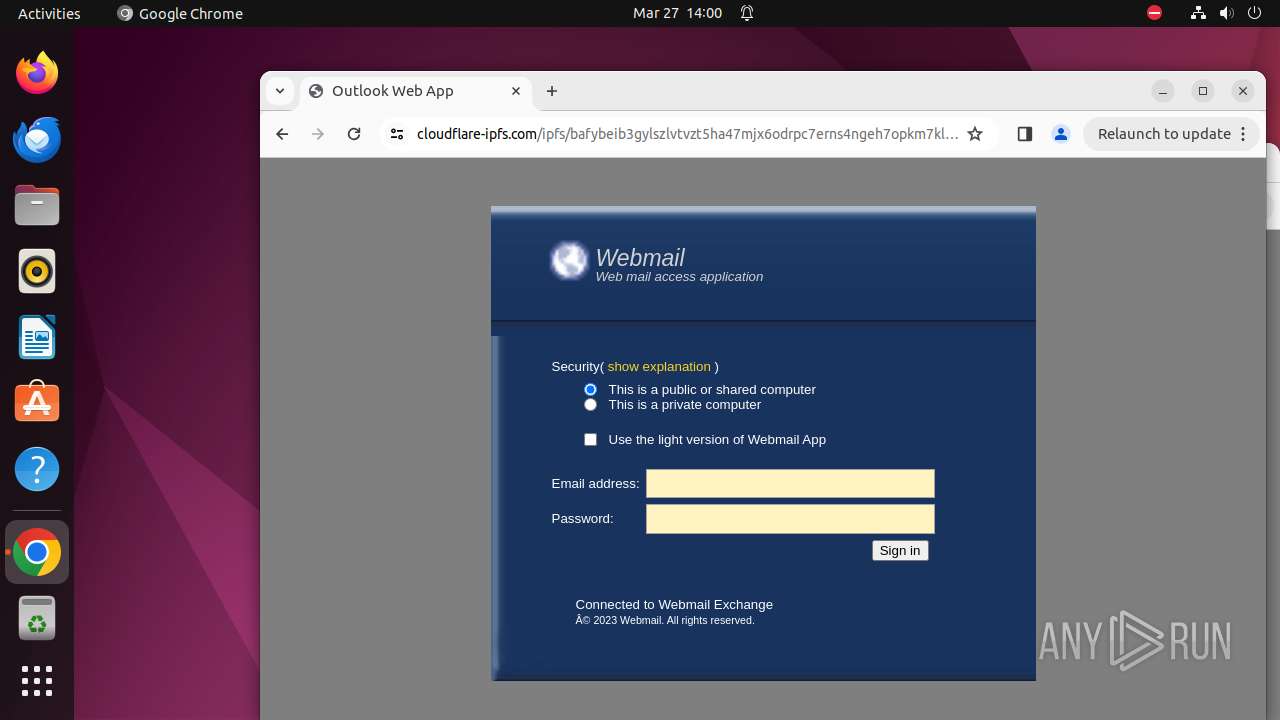
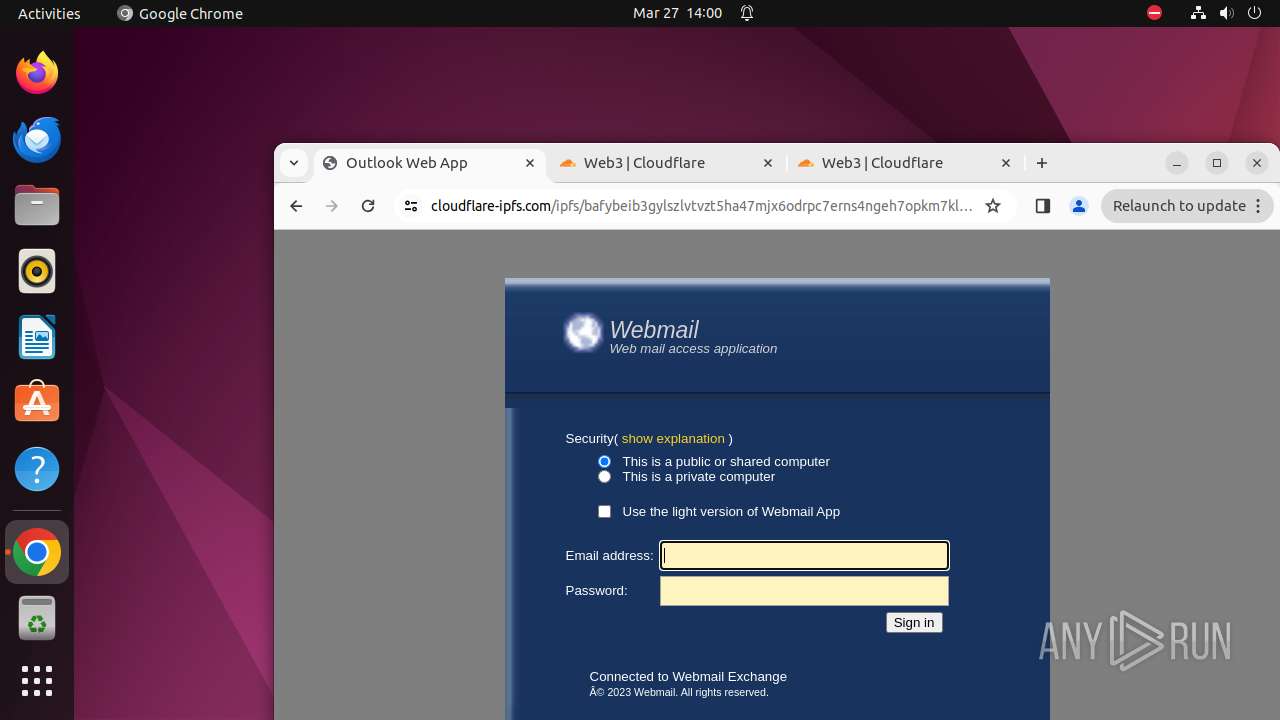
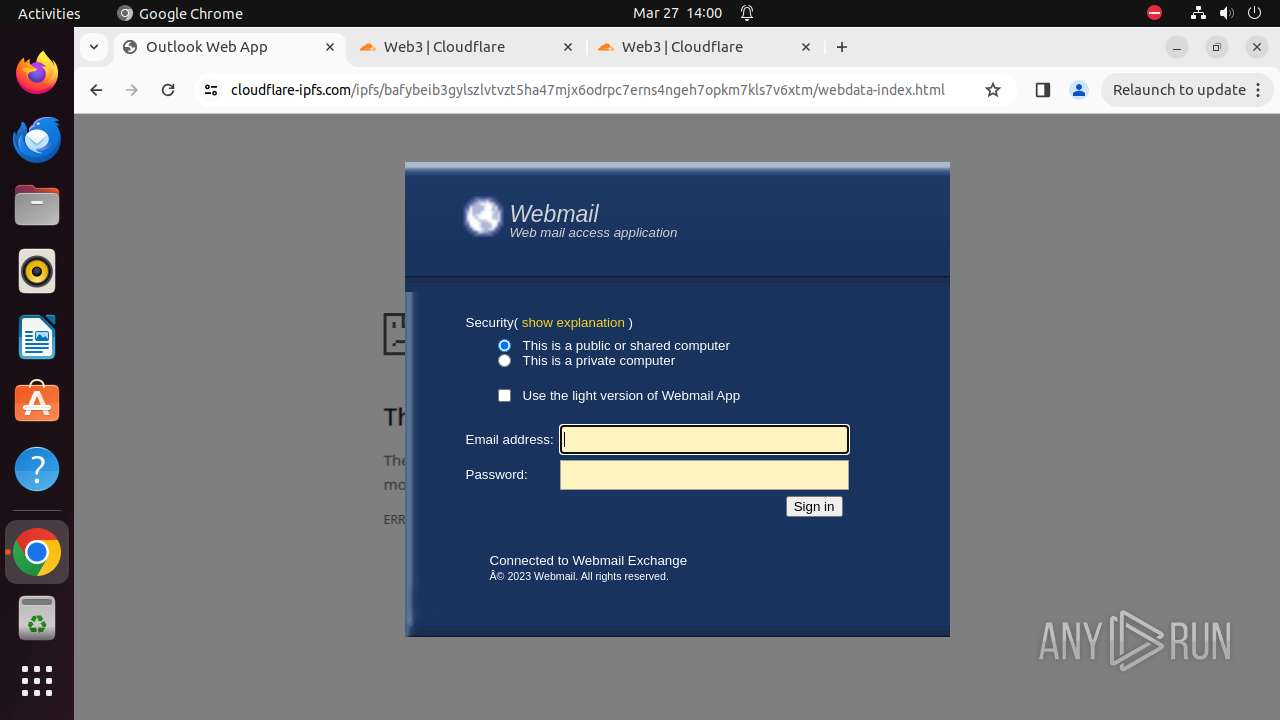
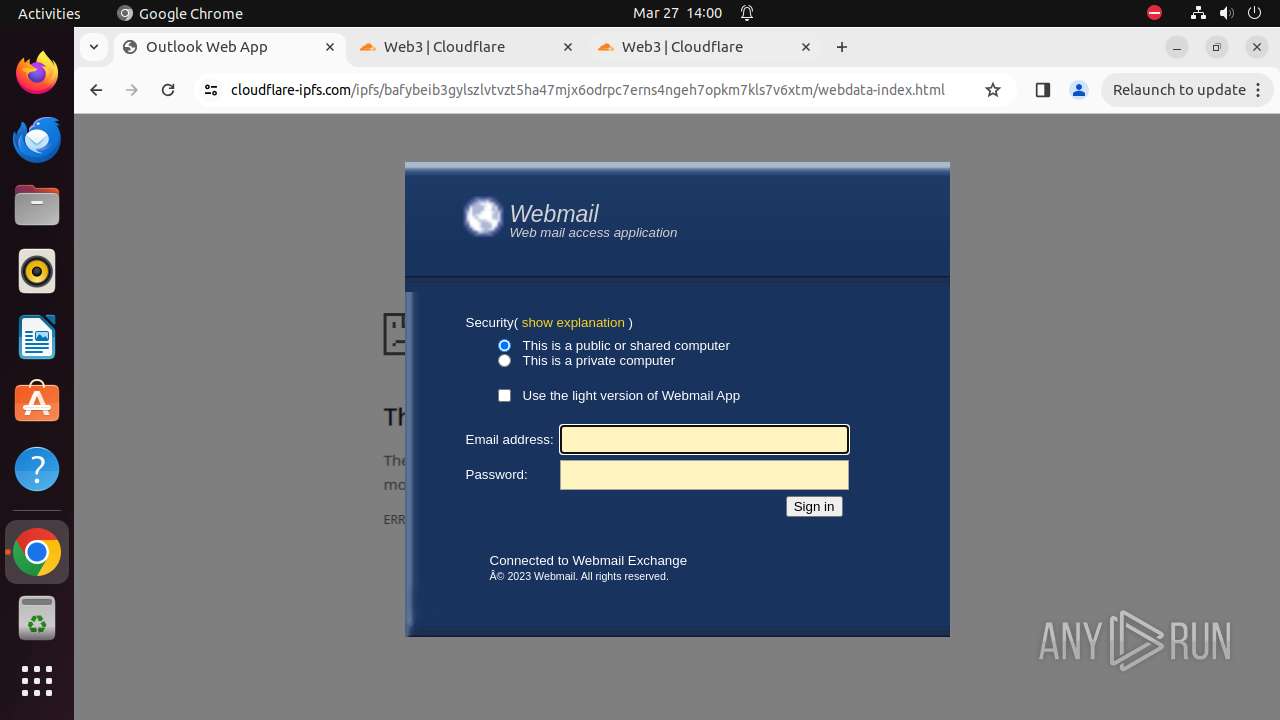
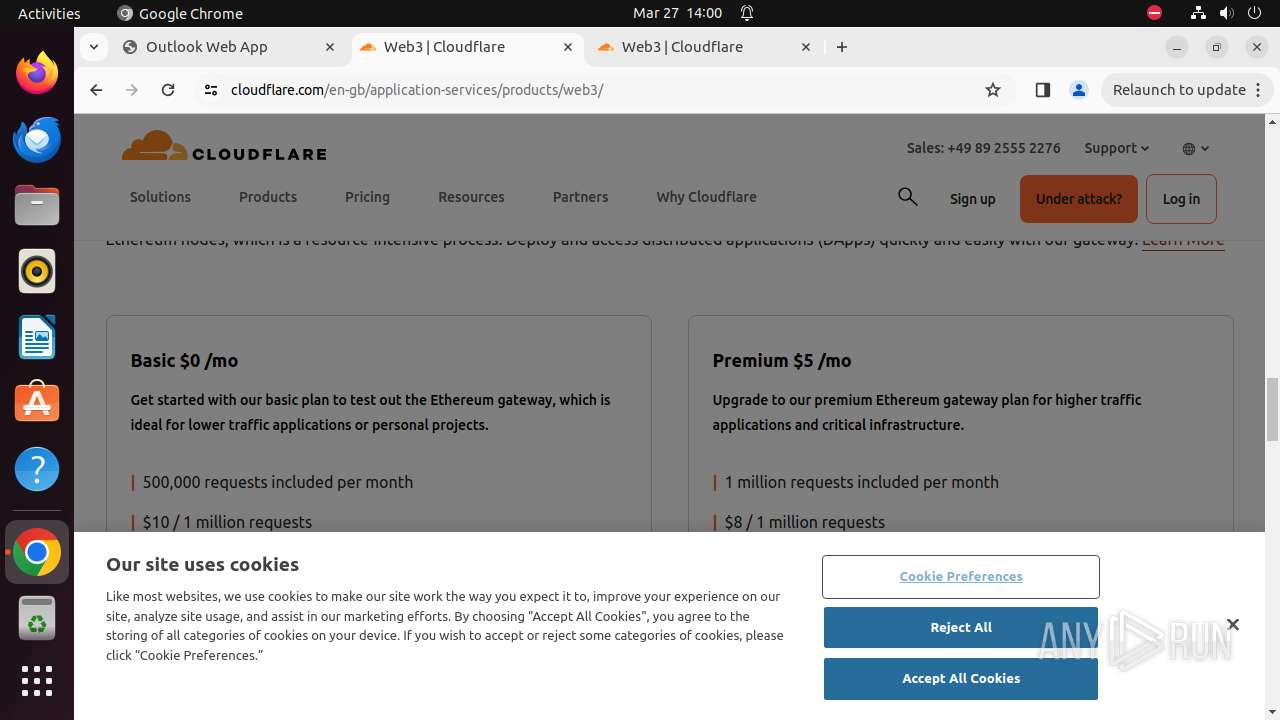
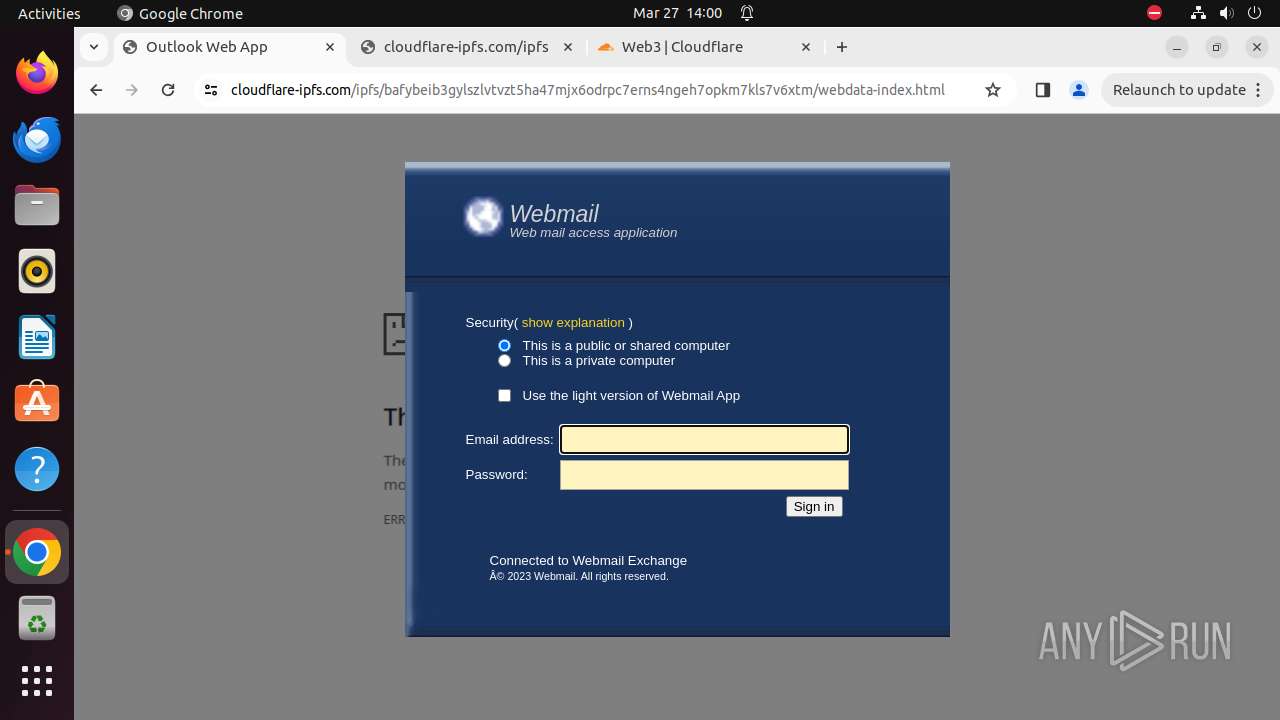
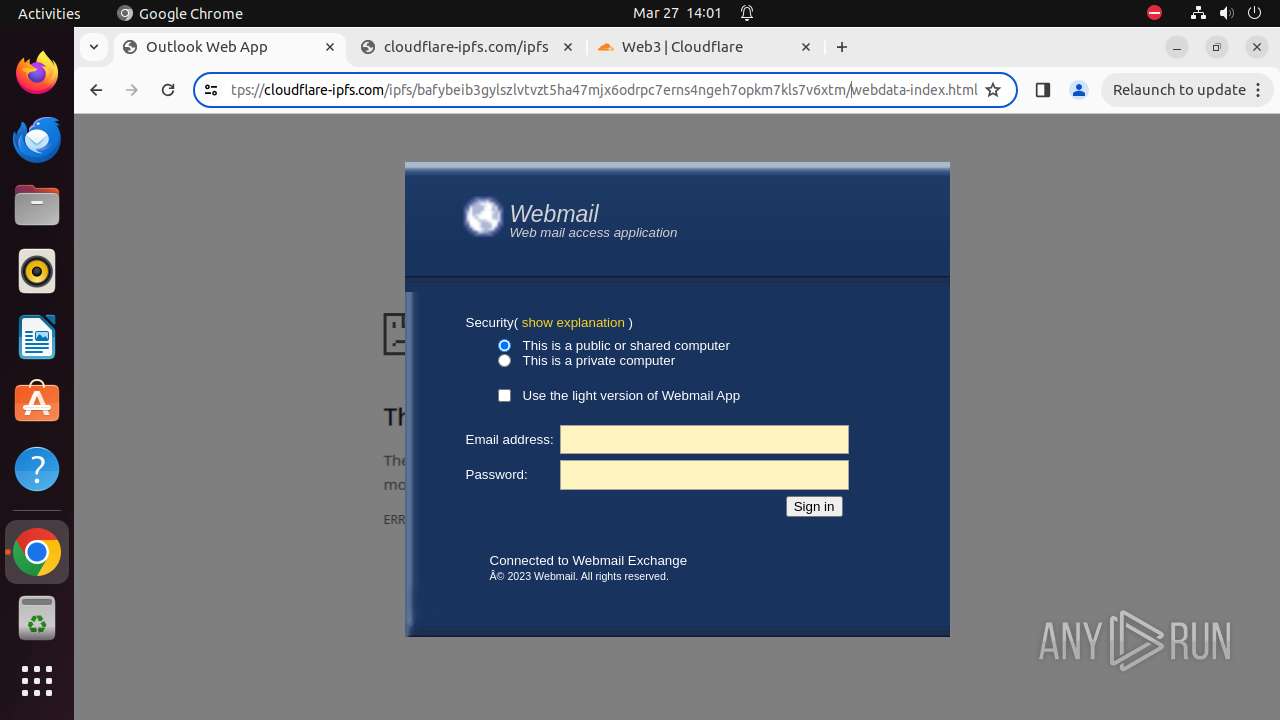
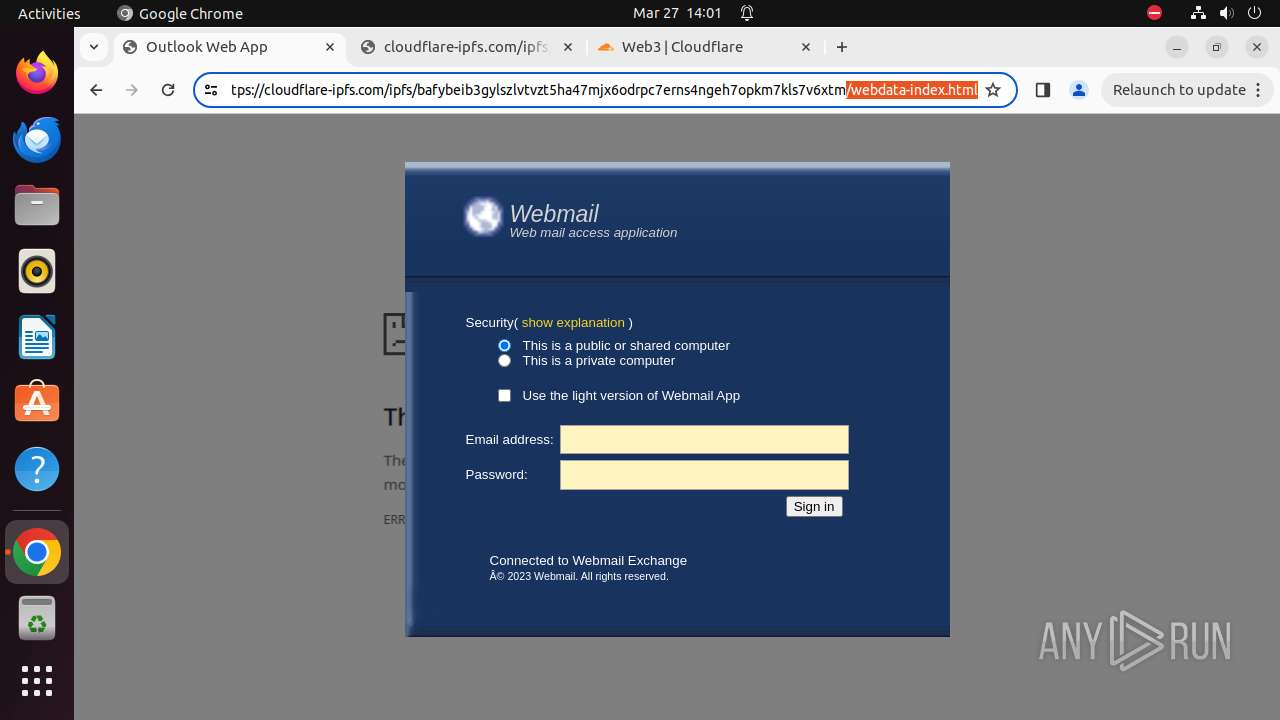
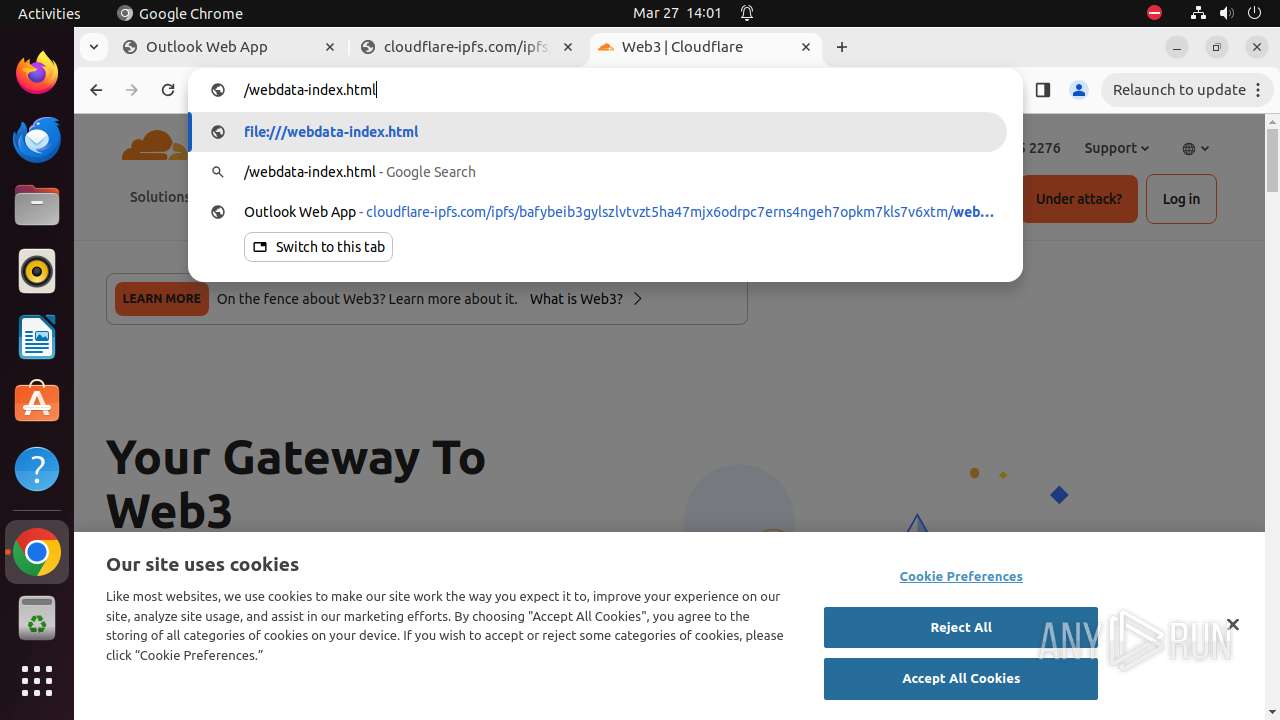
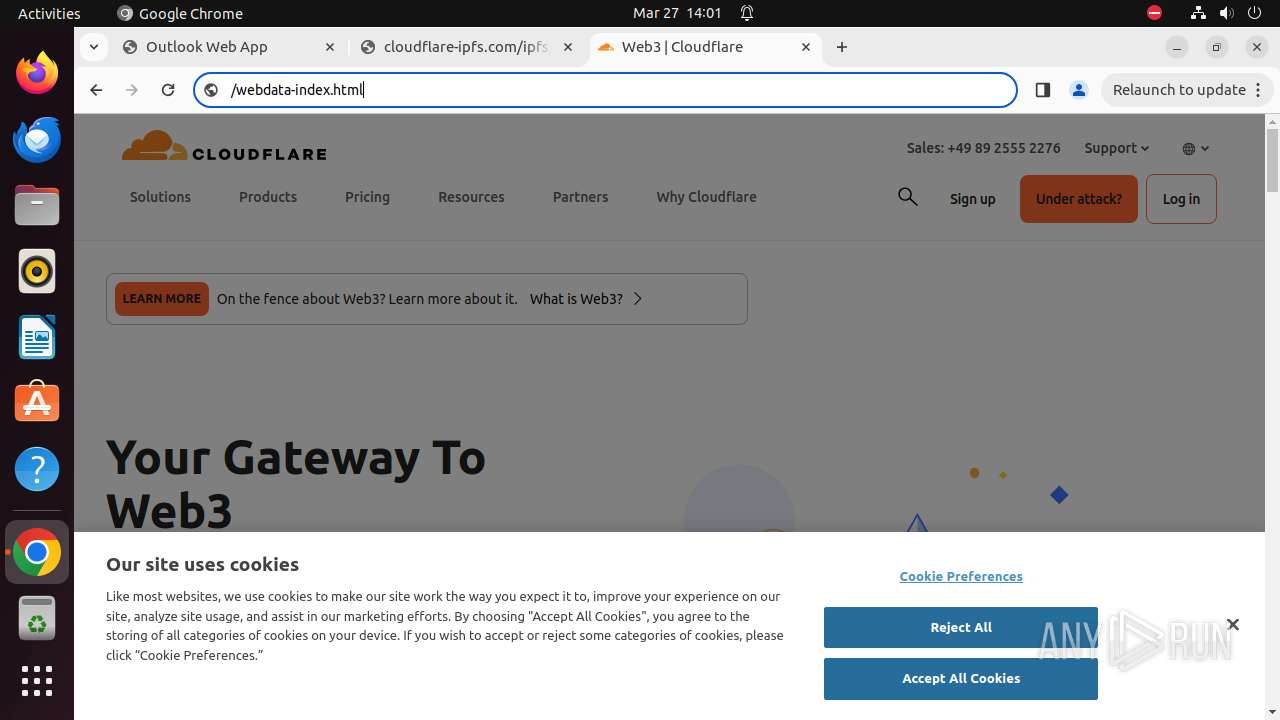
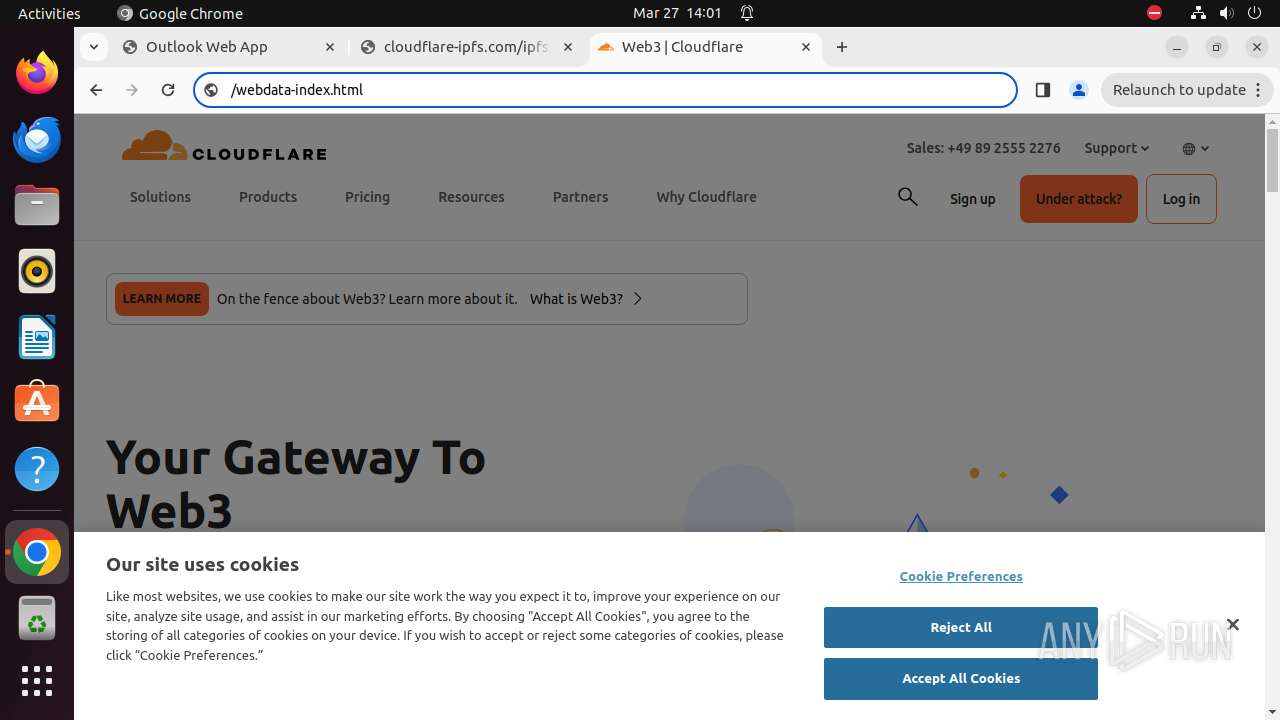
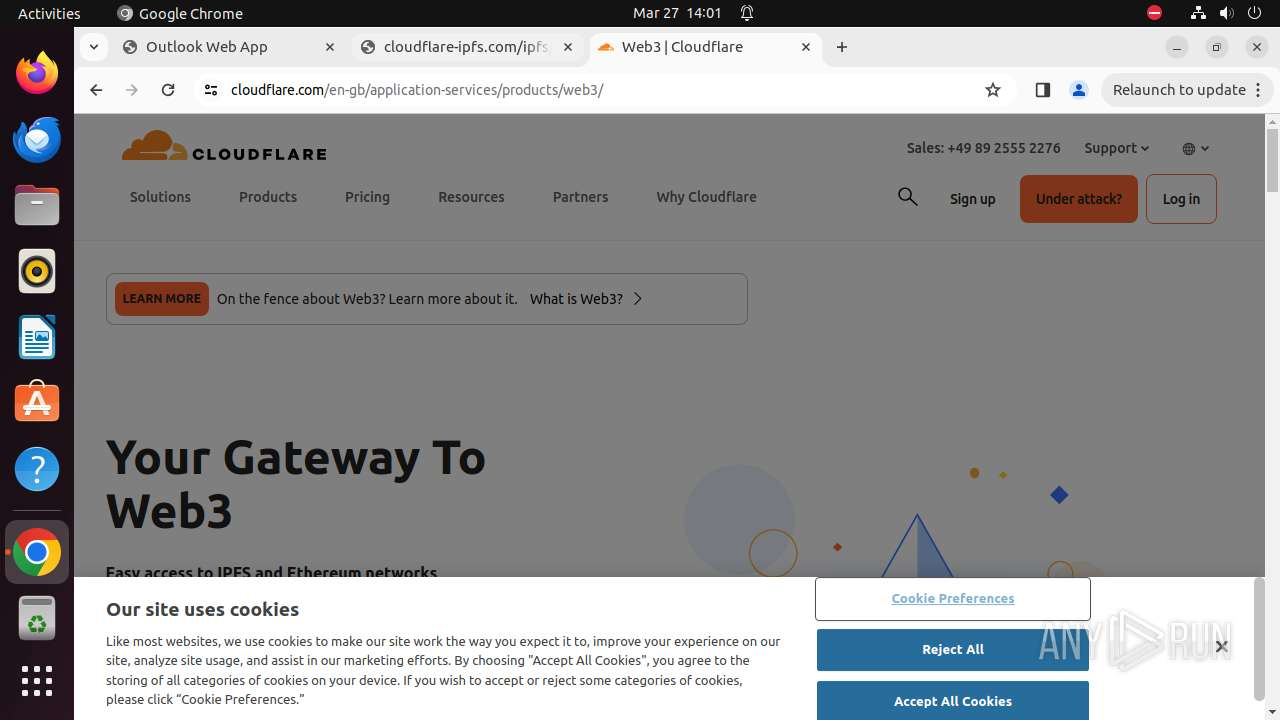
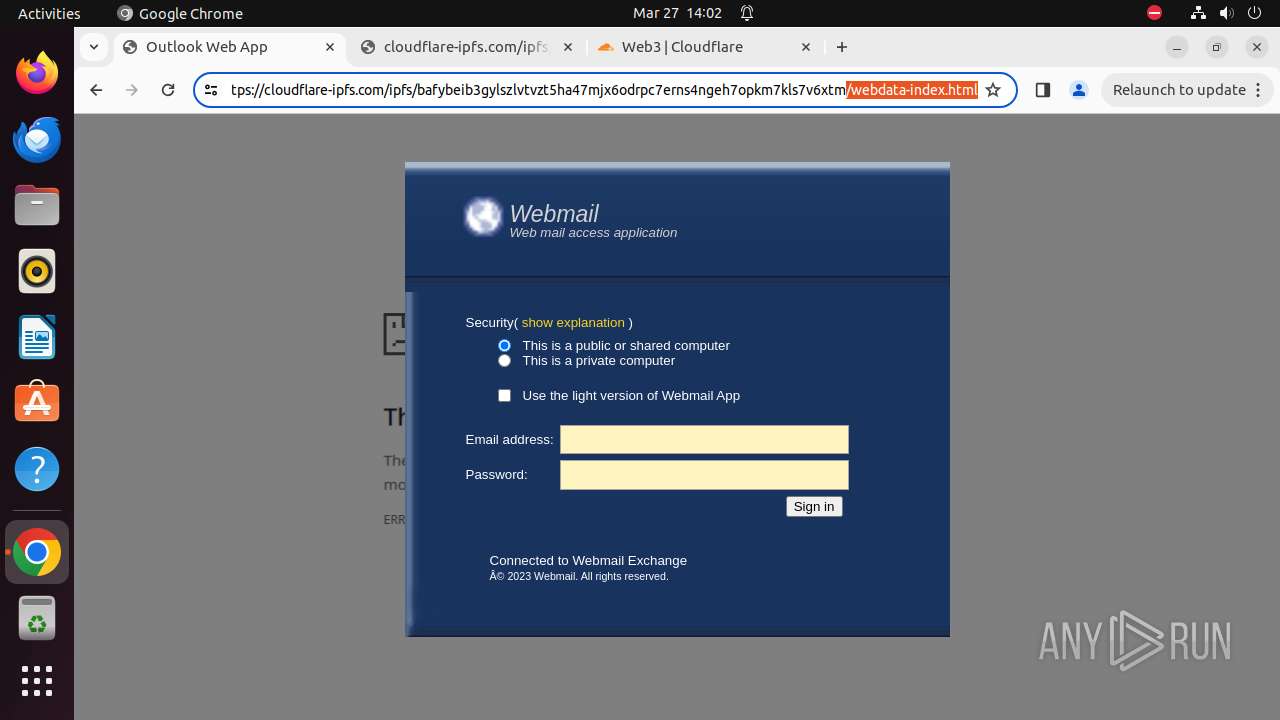
| URL: | https://webmail-xbnxjkx897865x5gjenkeghe-xmnxjkdsui367376rvhdfjb-nxknx.replit.app/#anshah@gipcl.com |
| Full analysis: | https://app.any.run/tasks/8567b824-d8a8-4998-ad81-f9caabab450f |
| Verdict: | Malicious activity |
| Analysis date: | March 27, 2024, 13:57:00 |
| OS: | Ubuntu 22.04.2 |
| Tags: | |
| MD5: | 3AD02B77600018A727C9118DF1451014 |
| SHA1: | 0C82AFFE7493F180F45757F0494284C05267A2C7 |
| SHA256: | D2ED98A1677DEDD6233FB4F0C0324C4544AAFA5BD6FB6074A8ED5C96534AEDC7 |
| SSDEEP: | 3:N8RoEMJg6dcStLOACNANpbL5adOLd8iG1b2:2elJ3PKQp35aKdJ |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
324
Monitored processes
103
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 9299 | /bin/sh -c "DISPLAY=:0 sudo -iu user google-chrome \"https://webmail-xbnxjkx897865x5gjenkeghe-xmnxjkdsui367376rvhdfjb-nxknx\.replit\.app/#anshah@gipcl\.com\" " | /bin/sh | — | any-guest-agent |
User: root Integrity Level: UNKNOWN | ||||
| 9300 | sudo -iu user google-chrome https://webmail-xbnxjkx897865x5gjenkeghe-xmnxjkdsui367376rvhdfjb-nxknx.replit.app/#anshah@gipcl.com | /usr/bin/sudo | — | sh |
User: root Integrity Level: UNKNOWN | ||||
| 9301 | /usr/bin/google-chrome https://webmail-xbnxjkx897865x5gjenkeghe-xmnxjkdsui367376rvhdfjb-nxknx.replit.app/#anshah@gipcl.com | /opt/google/chrome/chrome | — | sudo |
User: user Integrity Level: UNKNOWN | ||||
| 9302 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 9303 | readlink -f /usr/bin/google-chrome | /usr/bin/readlink | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 9304 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 9305 | mkdir -p /home/user/.local/share/applications | /usr/bin/mkdir | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 9306 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 9307 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 9308 | /opt/google/chrome/chrome | — | chrome | |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 9301 | chrome | /9301/fd/63 | — | |
MD5:— | SHA256:— | |||
| 9301 | chrome | /home/user/.config/google-chrome/BrowserMetrics/BrowserMetrics-660425B3-2455.pma | — | |
MD5:— | SHA256:— | |||
| 9301 | chrome | /home/user/.config/google-chrome/Default/Sync Data/LevelDB/LOG | — | |
MD5:— | SHA256:— | |||
| 9301 | chrome | /.com.google.Chrome.tipjz4 | — | |
MD5:— | SHA256:— | |||
| 9301 | chrome | /.com.google.Chrome.XdPmZg | — | |
MD5:— | SHA256:— | |||
| 9301 | chrome | /.com.google.Chrome.kQ7a5V | — | |
MD5:— | SHA256:— | |||
| 9301 | chrome | /home/user/.config/google-chrome/Default/Site Characteristics Database/LOG | — | |
MD5:— | SHA256:— | |||
| 9301 | chrome | /.com.google.Chrome.Agv0z2 | — | |
MD5:— | SHA256:— | |||
| 9301 | chrome | /.com.google.Chrome.C4zvQQ | — | |
MD5:— | SHA256:— | |||
| 9301 | chrome | /home/user/.config/google-chrome/Default/Session Storage/LOG | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
88
DNS requests
106
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 91.189.91.97:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adenfnd66guzd4vn7ffvjgkyl7wq_439/lmelglejhemejginpboagddgdfbepgmp_439_all_ZZ_adbbwdbp45y3tcec5bde2wha5nnq.crx3 | unknown | binary | 46.8 Kb | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/kiabhabjdbkjdpjbpigfodbdjmbglcoo/1.90b91aaa463ef666bf030c7f14b7046738dee86d64321b28cb834d04bbfea4b3/1.4a6508925b2ffec931c1e3931ddeb15ca41d820a8264cd5a962b526e9932bcdf/e7212b90bb1f0ff6252449bbddc556675aa725f13d46408fb87016facb011e35.puff | unknown | binary | 3.21 Kb | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/jx7rkbwas3jtmlgf6ivmagwisi_2024.3.22.0/niikhdgajlphfehepabhhblakbdgeefj_2024.03.22.00_all_pplglefstwrw27olw4xpo7hgs4.crx3 | unknown | binary | 5.92 Kb | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTBmQUFZUHRkSkgtb01uSGNvRHZ2Tm5HQQ/1.0.0.15_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | binary | 3.07 Kb | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad7ymo4xuspiuckympqnpnyov56a_8623/hfnkpimlhhgieaddgfemjhofmfblmnib_8623_all_e77nvdtde6nzgspcgrmkwa5q2a.crx3 | unknown | binary | 26.1 Kb | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/efniojlnjndmcbiieegkicadnoecjjef/1.a20984b62546ce601a8395d3363909bdd9e427ce1c0c3363c2f21e5808dbe9b3/1.6fcc02a365d39485c49c9da8679a9fd979832315b2d47ff7f0ab395b10e303bd/04c228ddca24f61e36e7ead1e61fd583f99fada897f37fdf44d4cf0586a81857.puff | unknown | binary | 22.9 Kb | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/jflookgnkcckhobaglndicnbbgbonegd/1.a00d455e64721d33c650d312ce6208b58e42fb0181b5e89c2f5222eda2b8e712/1.ab8da5b849ba36382f26992fe1b52d72aa457549f31246a0c386d6880fca8afc/36fd7b9c256475d2f7be4667ebf839f5a95a72dd73026ce6889740102eda5182.puff | unknown | binary | 52.2 Kb | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/dadf6agyorjde3tfwh4z77eokq_2024.3.26.1/jflhchccmppkfebkiaminageehmchikm_2024.03.26.01_all_acgpptoffsq5gxw4cn3mpax72bmq.crx3 | unknown | binary | 9.21 Kb | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/jtw2yebqy6ogv6wzfigbjphimy_2024.3.20.0/gonpemdgkjcecdgbnaabipppbmgfggbe_2024.03.20.00_all_acyqzrhkvpmzwu7jrinfxlenms5a.crx3 | unknown | binary | 6.47 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 91.189.91.97:80 | connectivity-check.ubuntu.com | Canonical Group Limited | US | unknown |
— | — | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 66.102.1.84:443 | accounts.google.com | GOOGLE | US | unknown |
— | — | 239.255.255.250:1900 | — | — | — | unknown |
— | — | 142.250.186.99:443 | clientservices.googleapis.com | GOOGLE | US | unknown |
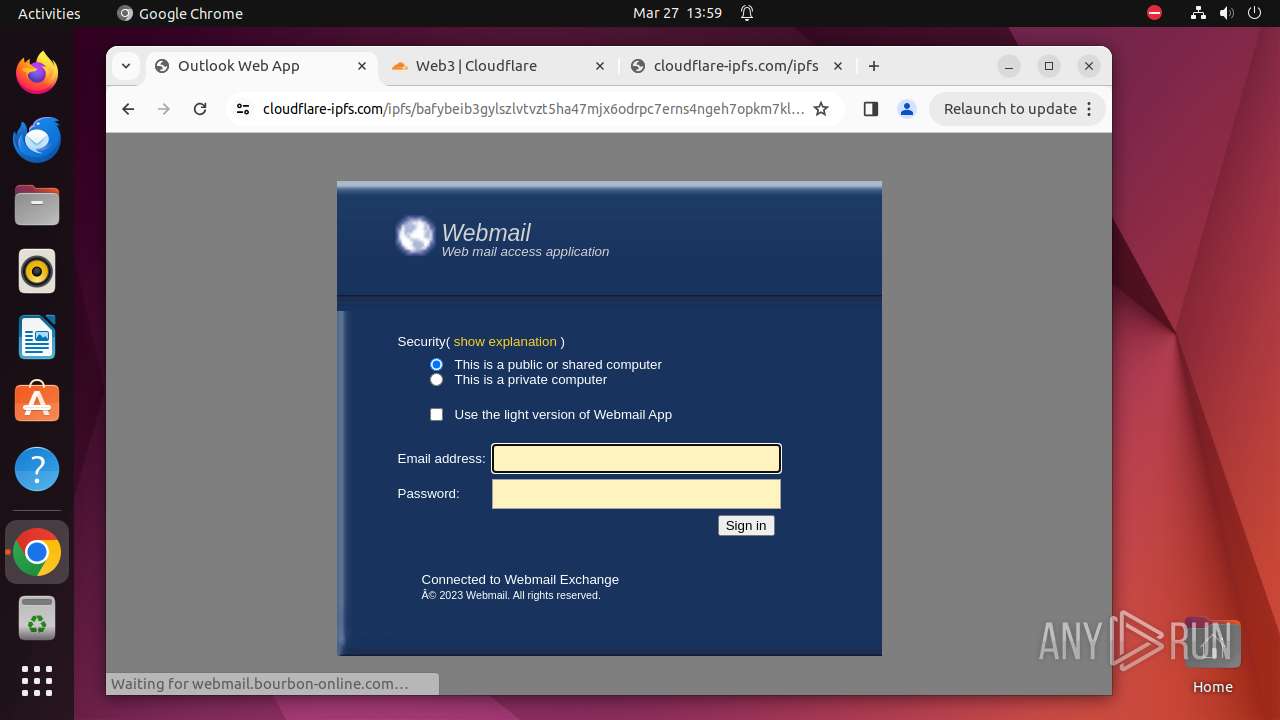
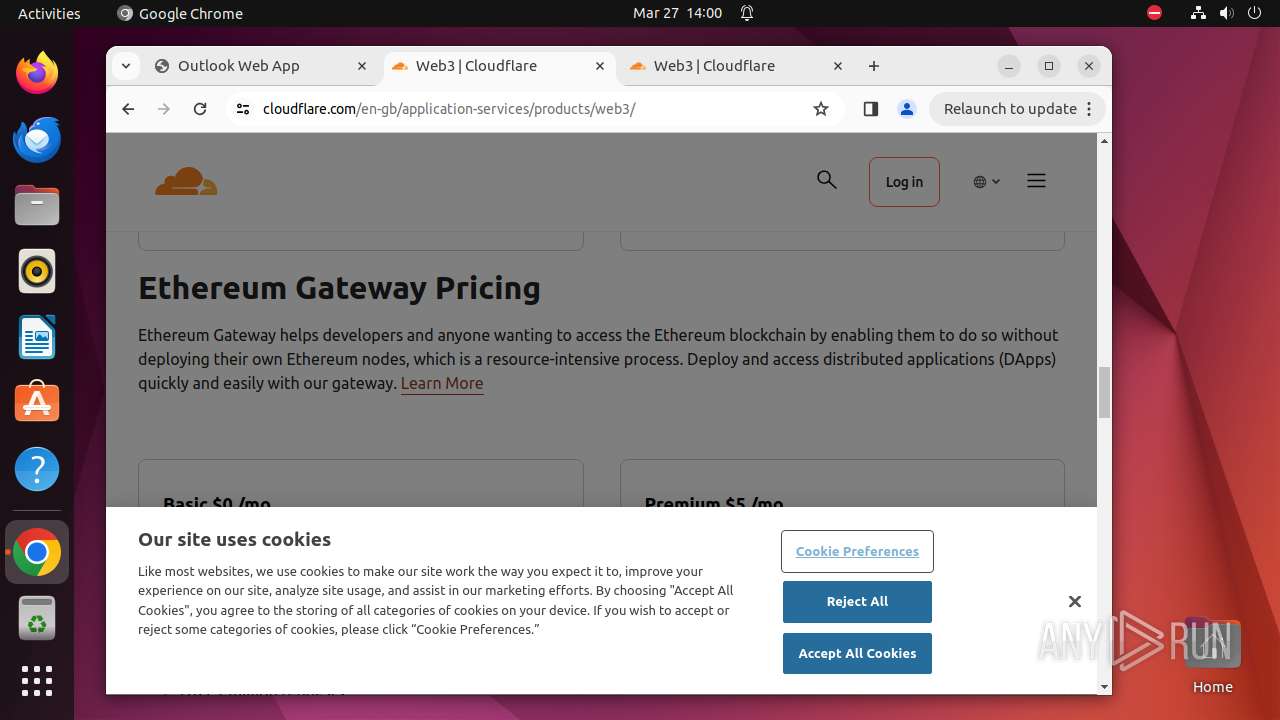
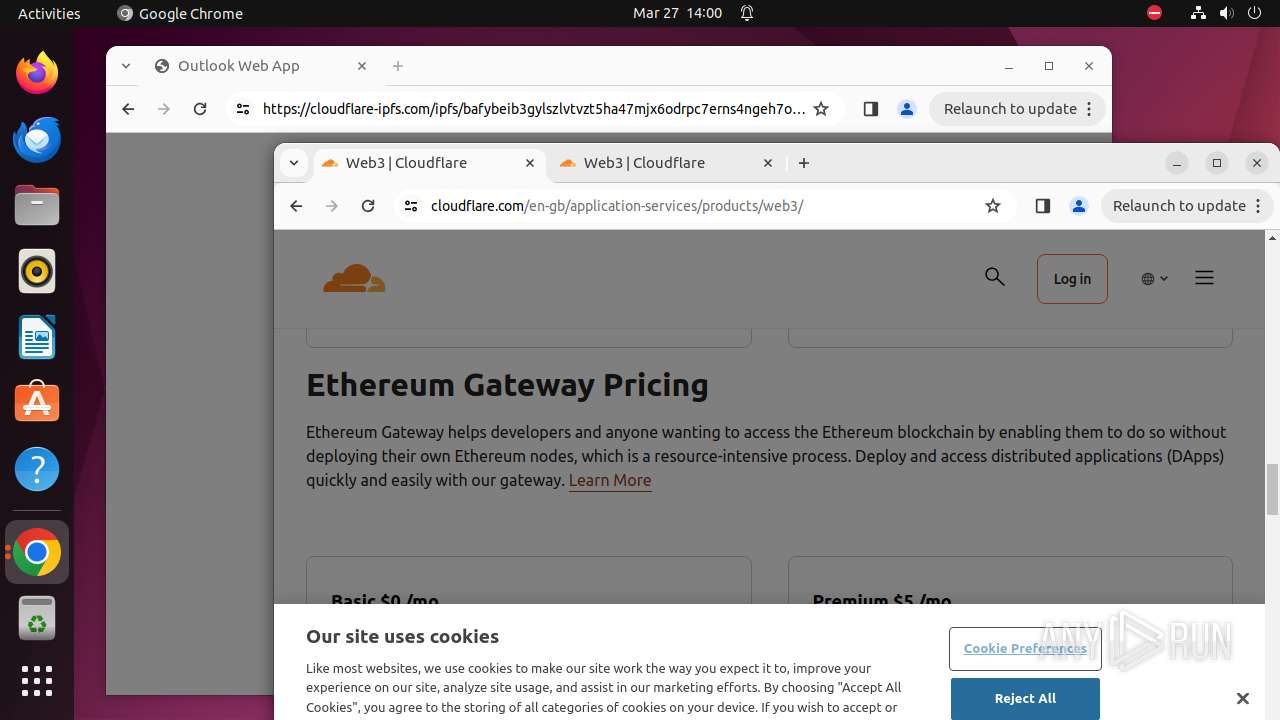
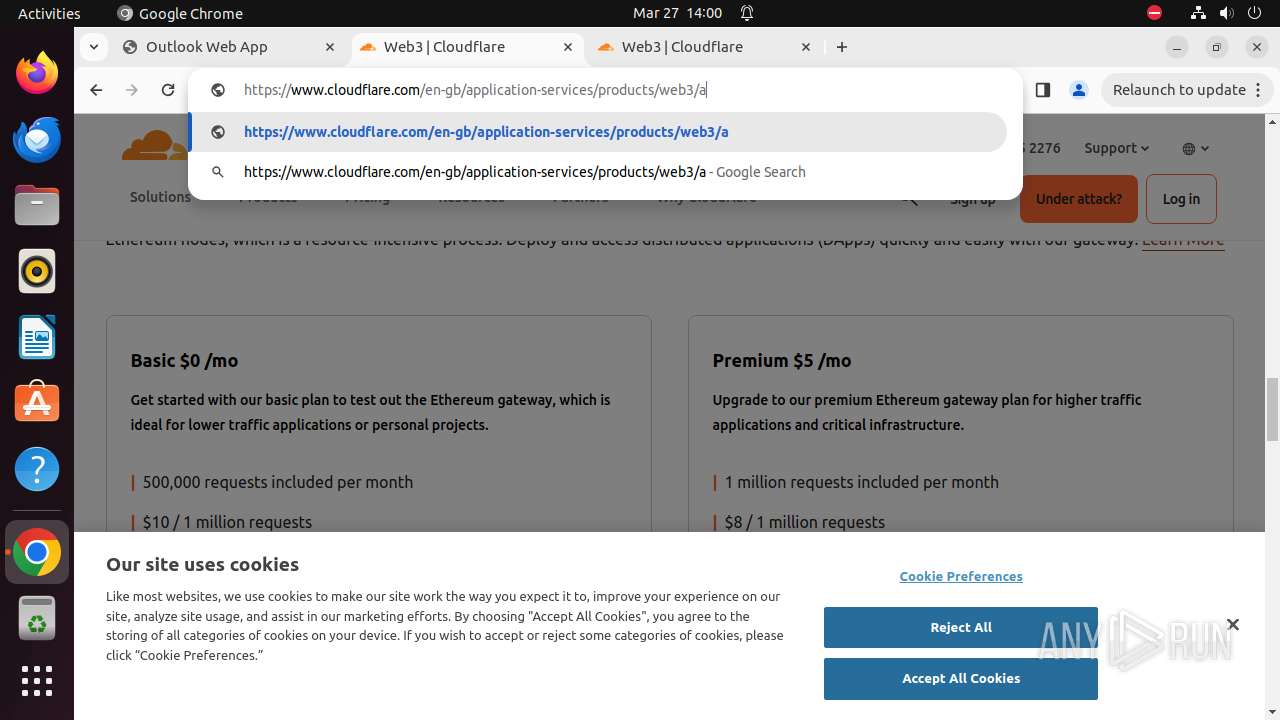
— | — | 34.117.33.233:443 | webmail-xbnxjkx897865x5gjenkeghe-xmnxjkdsui367376rvhdfjb-nxknx.replit.app | GOOGLE-CLOUD-PLATFORM | US | unknown |
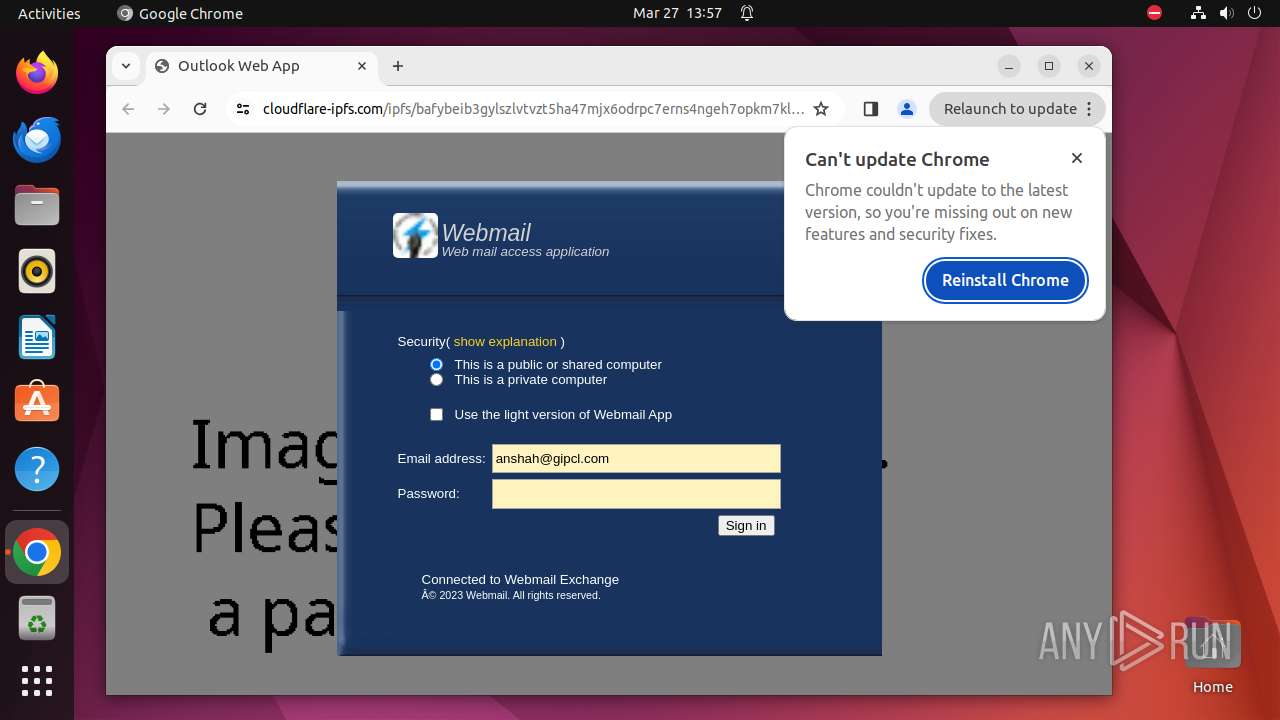
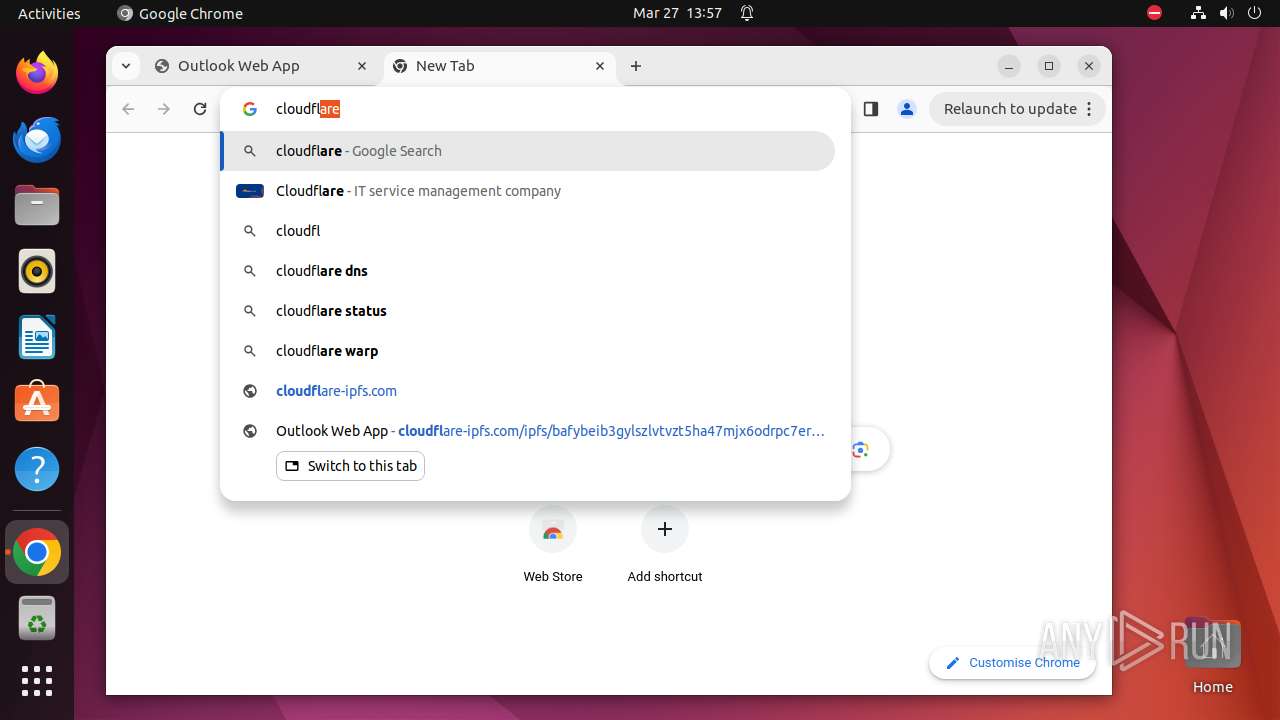
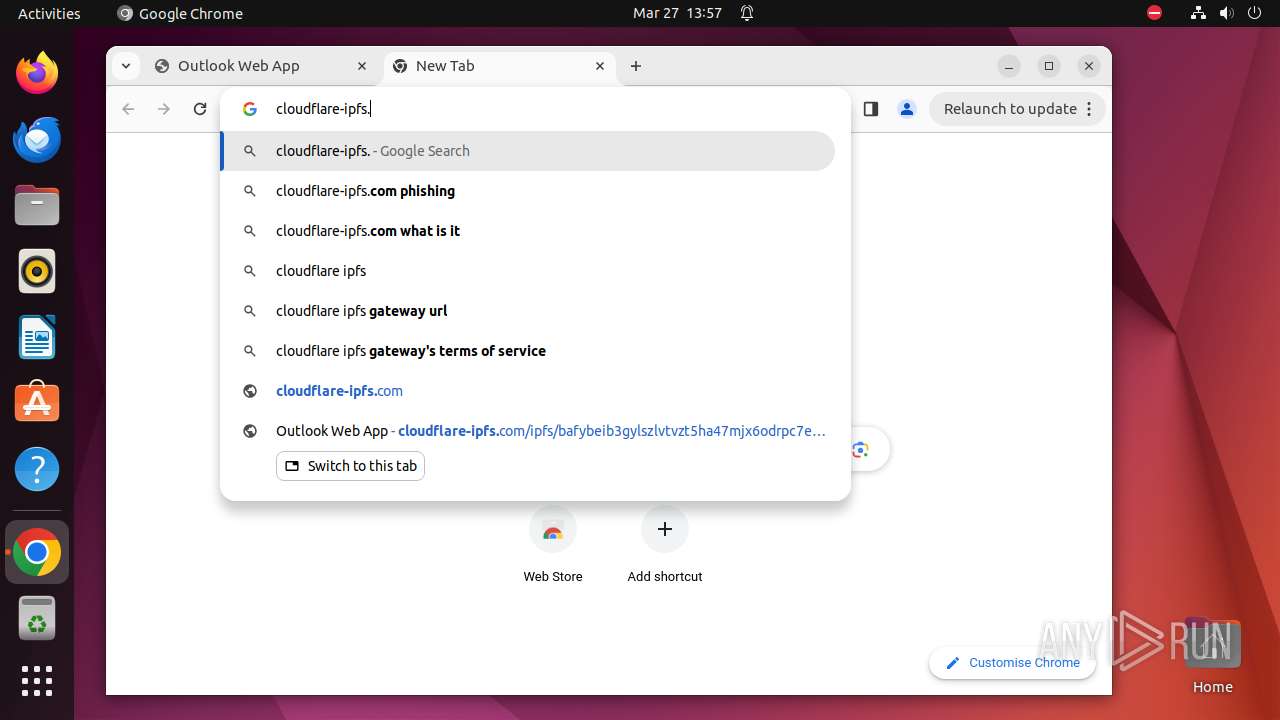
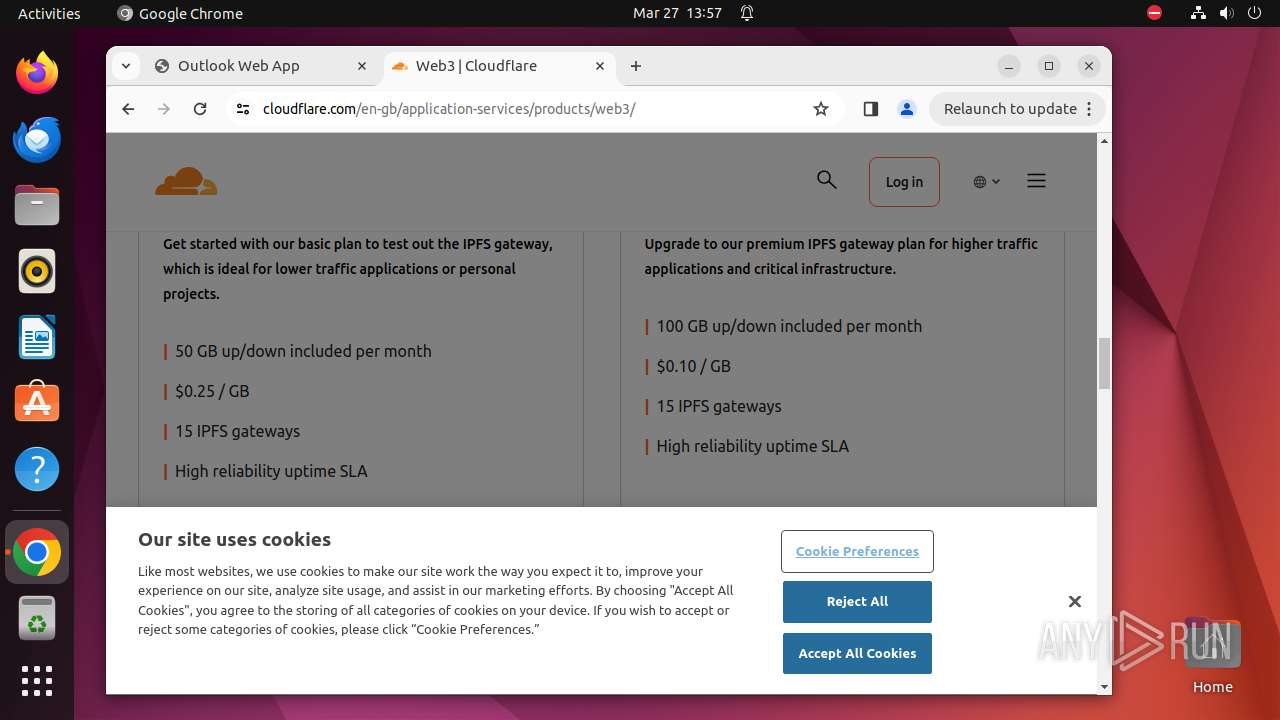
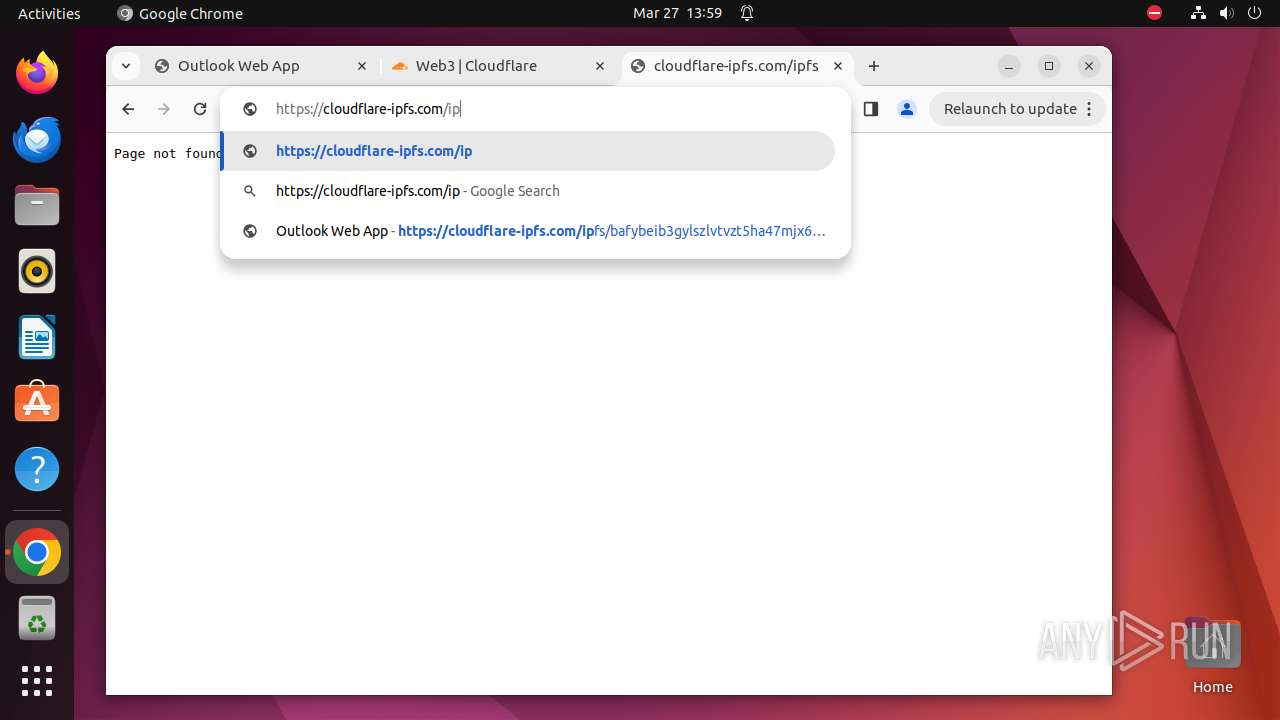
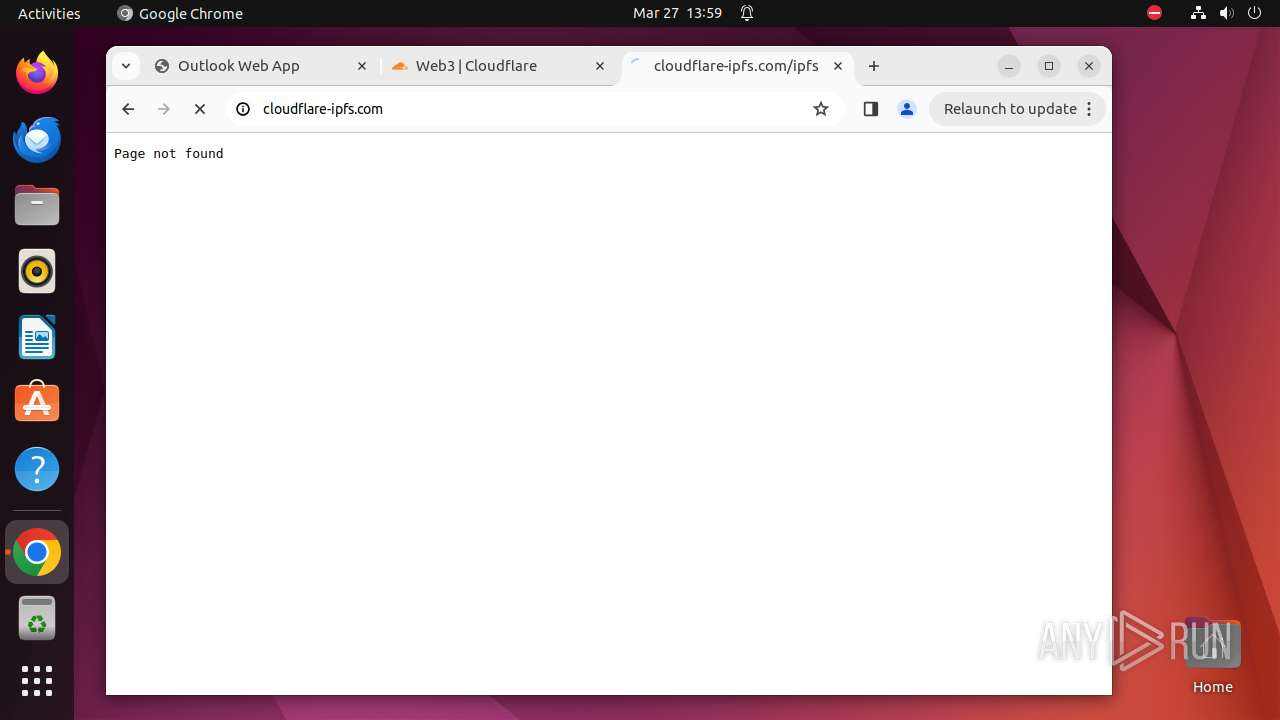
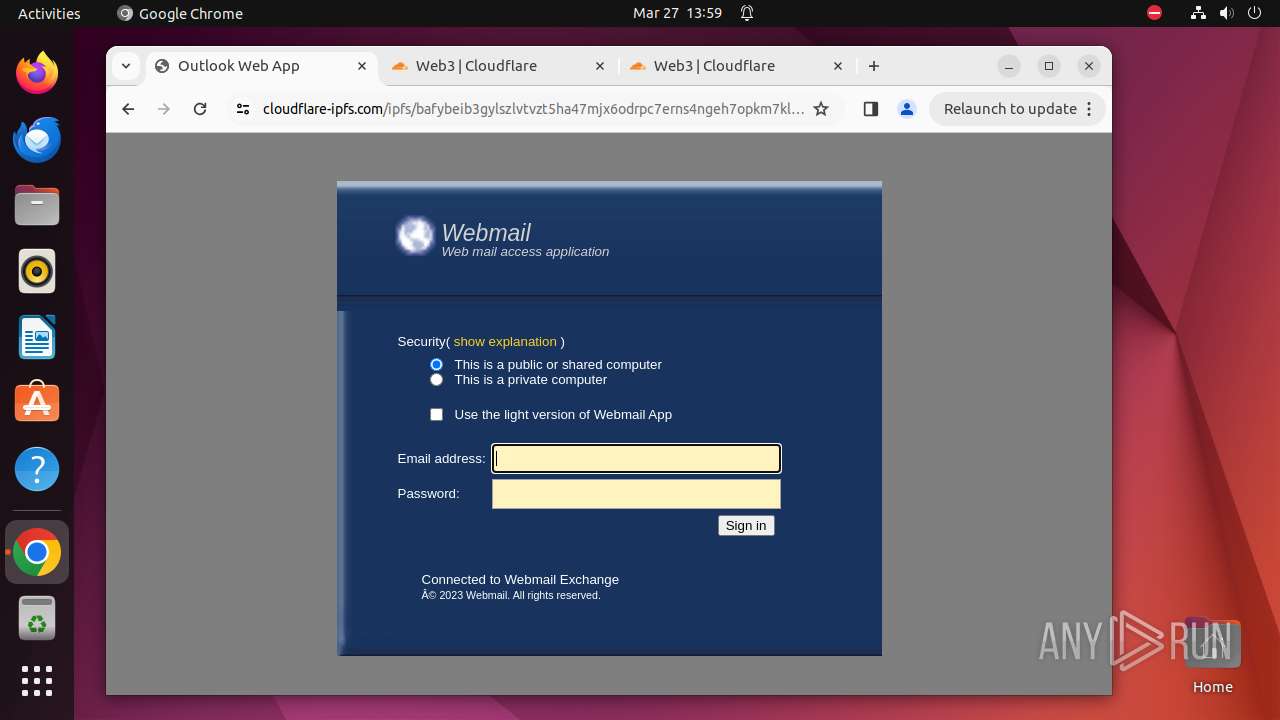
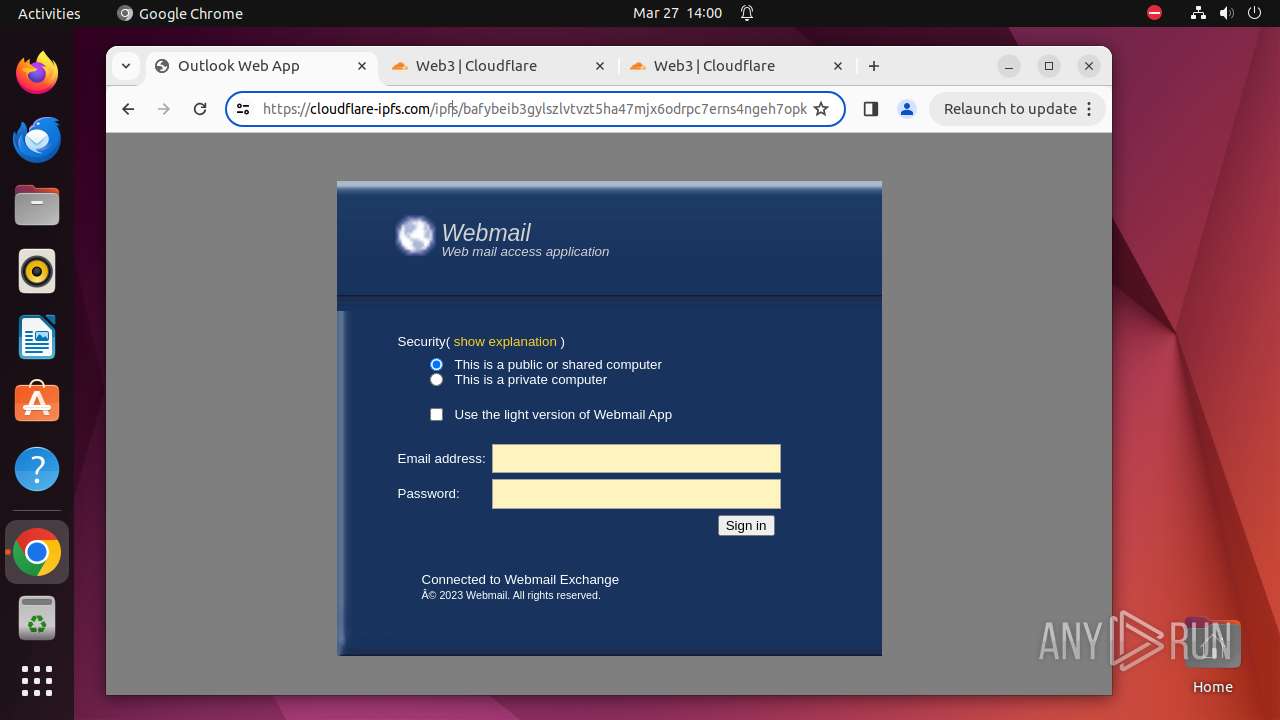
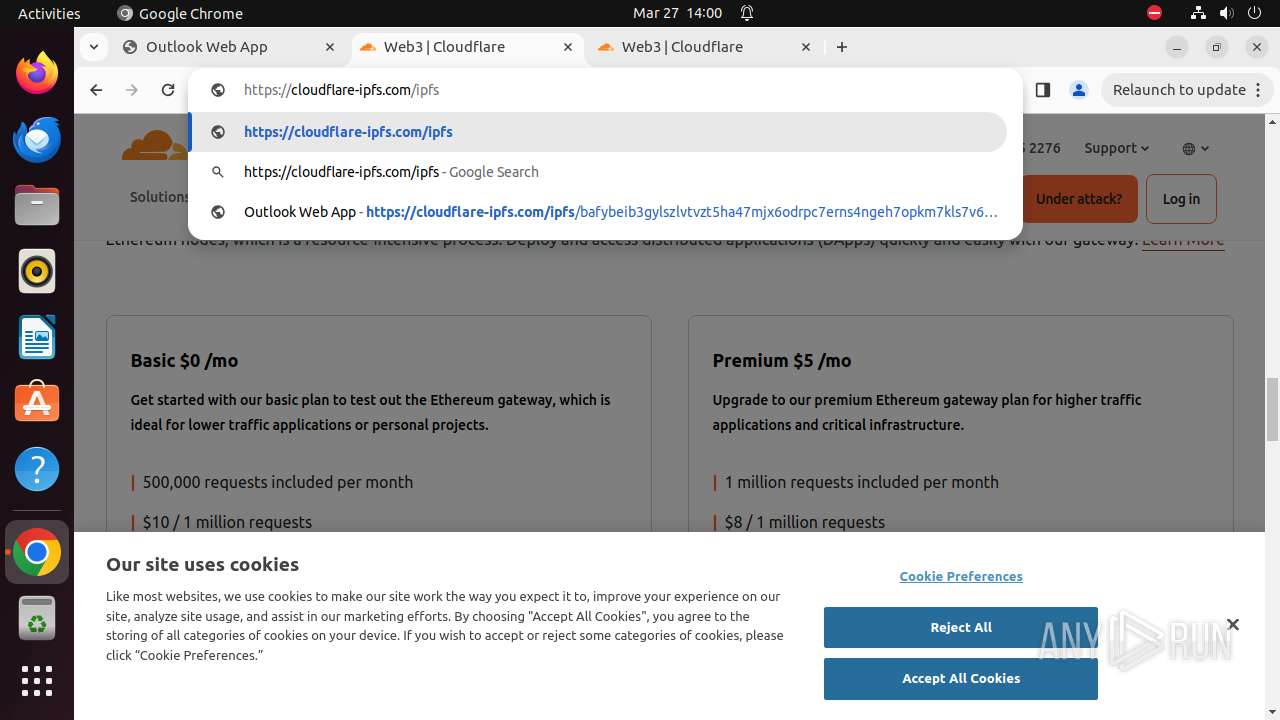
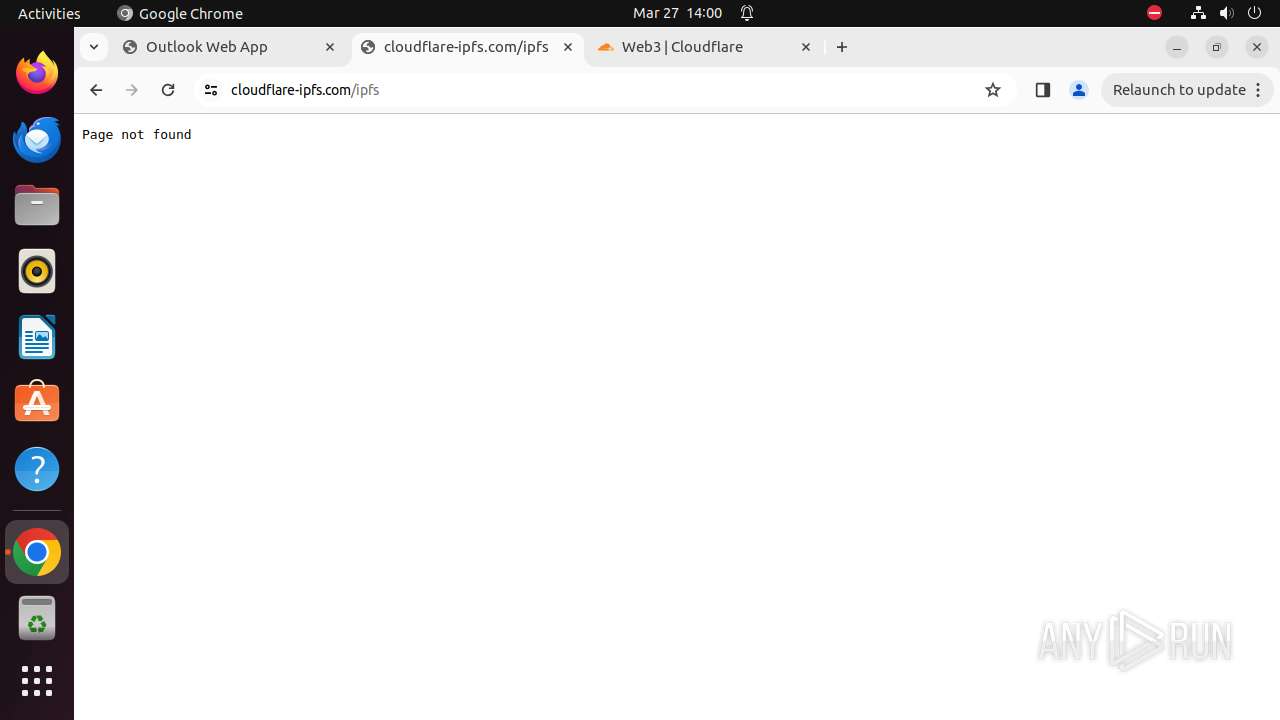
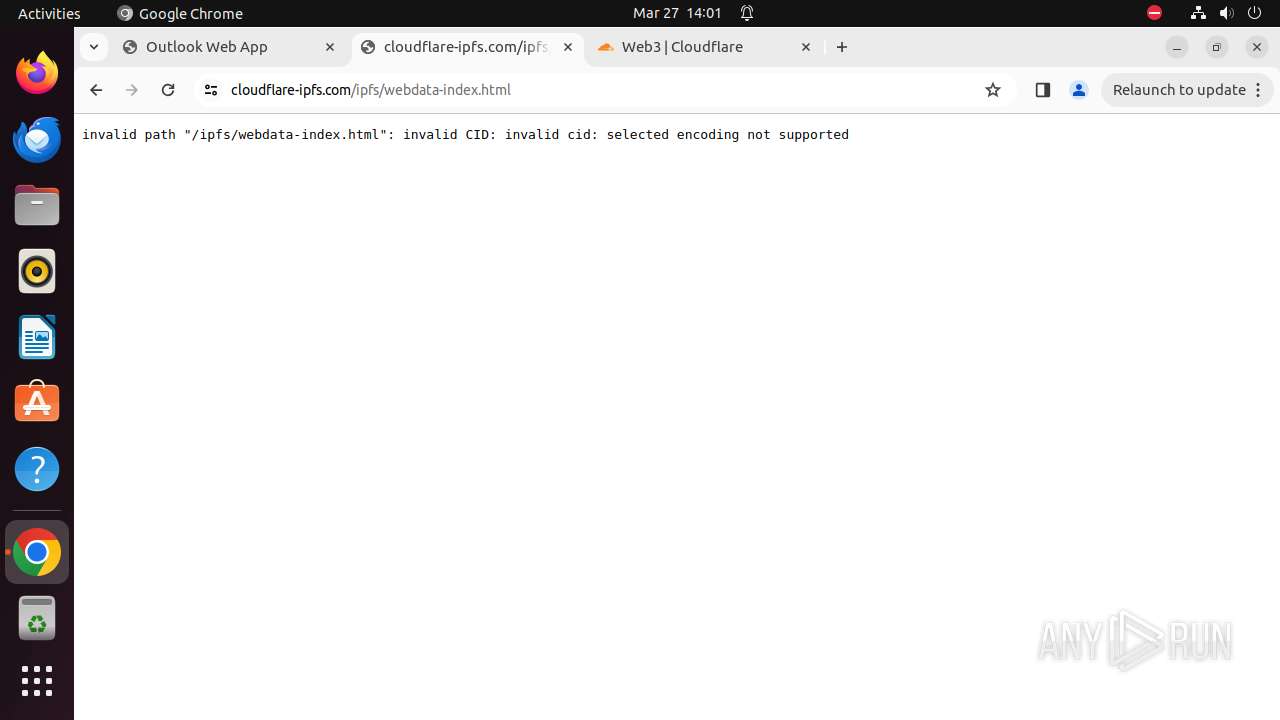
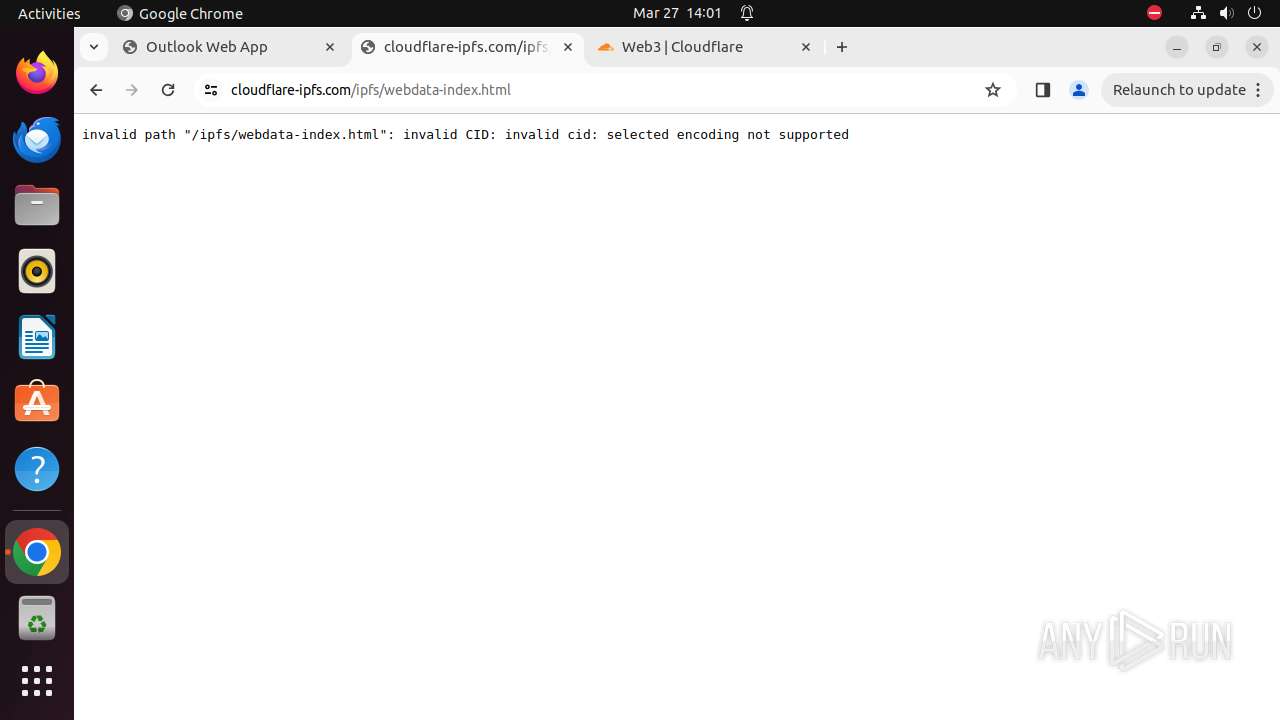
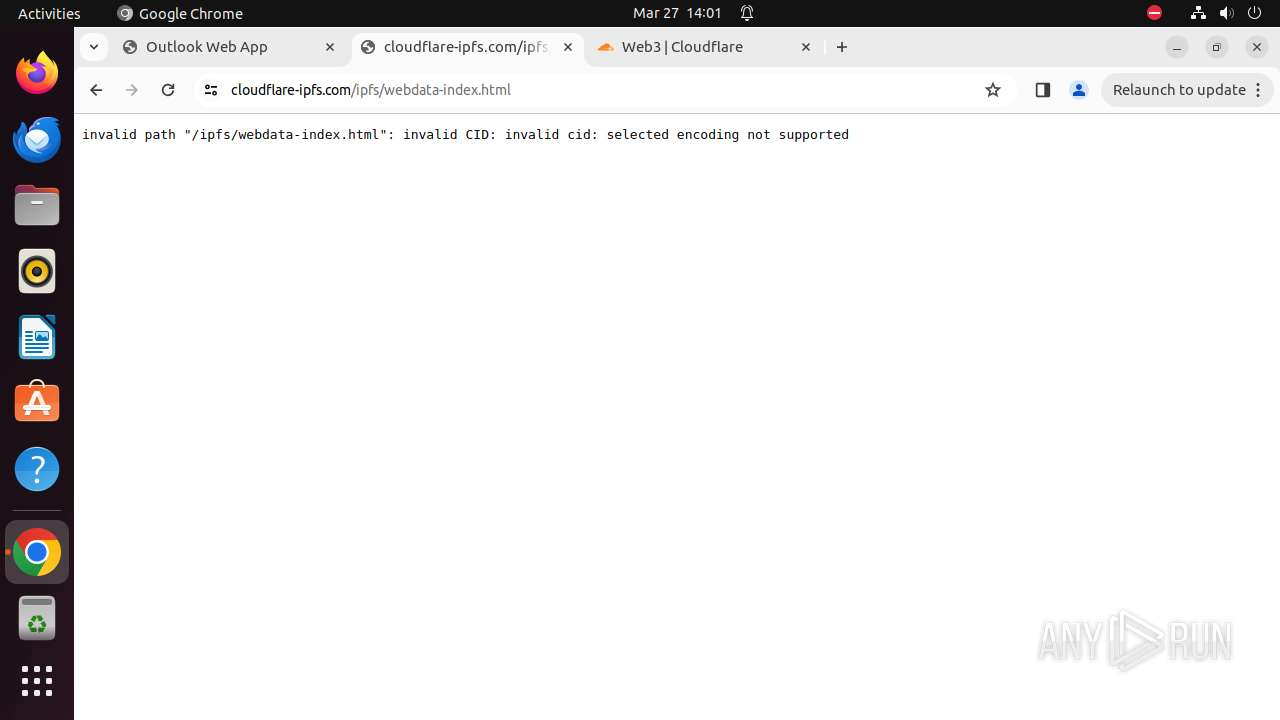
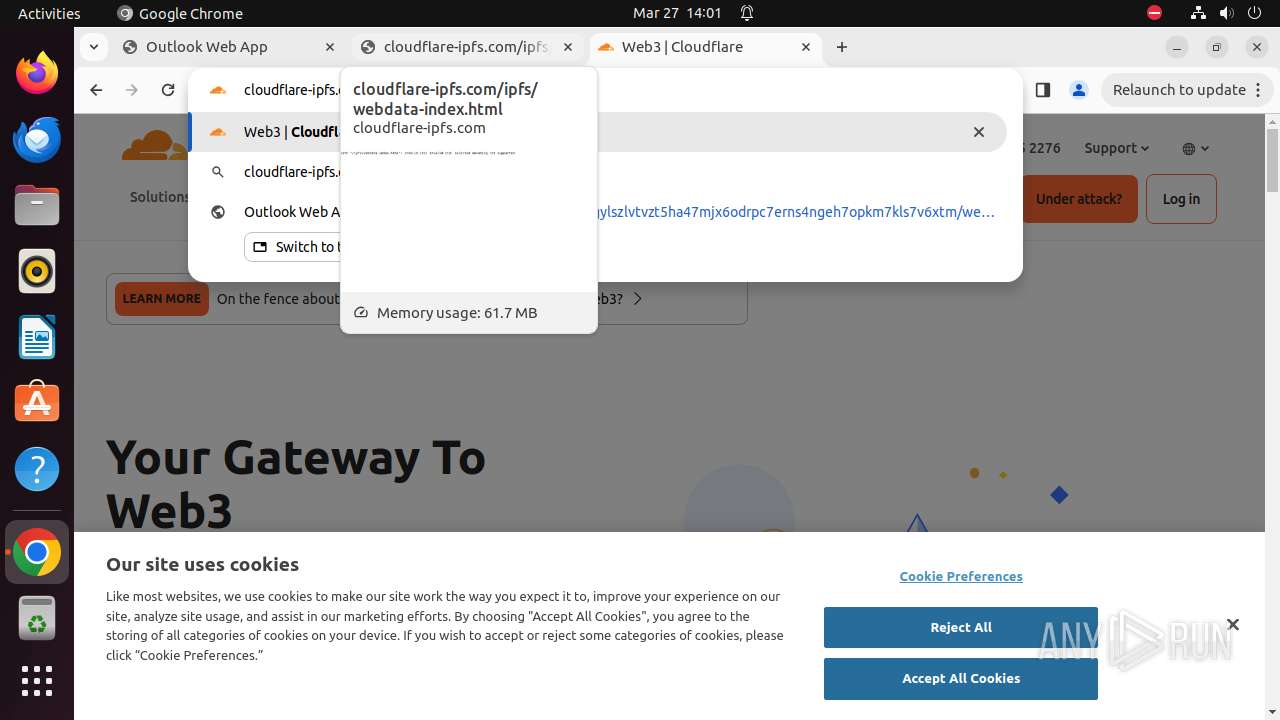
— | — | 104.17.64.14:443 | cloudflare-ipfs.com | CLOUDFLARENET | — | unknown |
— | — | 172.217.23.100:443 | www.google.com | — | — | unknown |
— | — | 142.250.186.106:443 | ajax.googleapis.com | GOOGLE | US | unknown |
— | — | 142.250.186.42:443 | content-autofill.googleapis.com | GOOGLE | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
webmail-xbnxjkx897865x5gjenkeghe-xmnxjkdsui367376rvhdfjb-nxknx.replit.app |
| unknown |
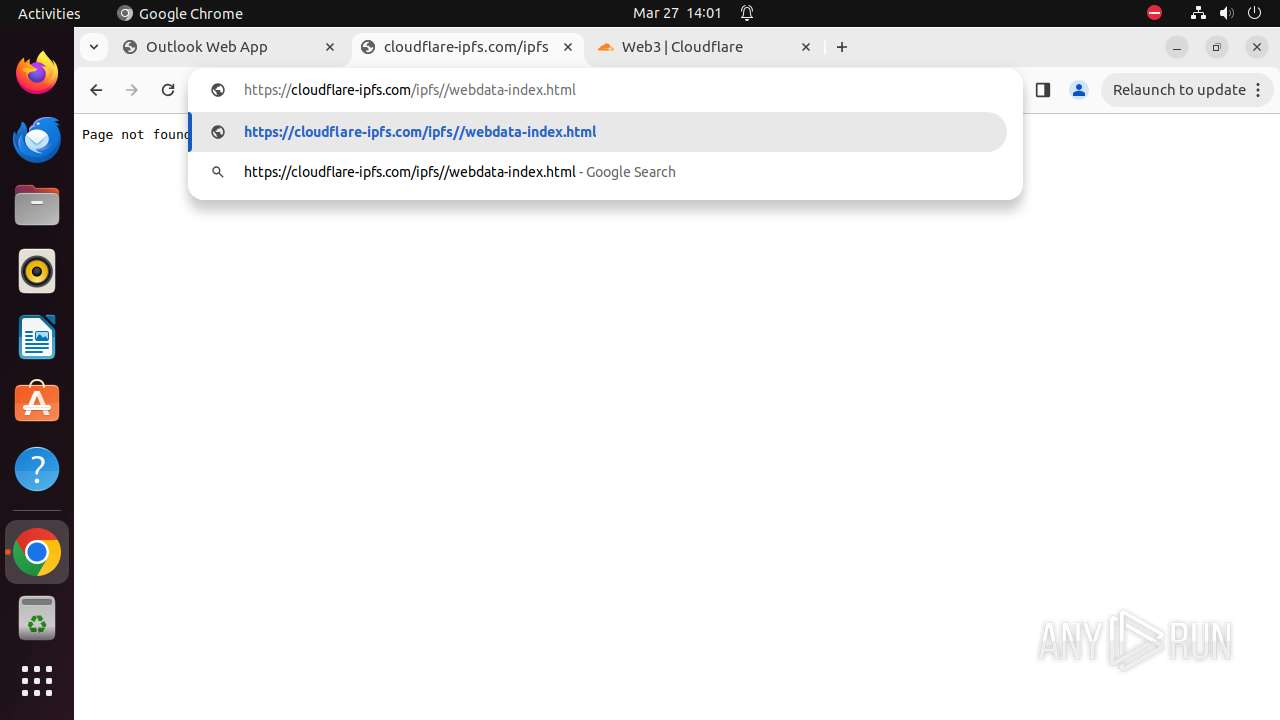
cloudflare-ipfs.com |
| malicious |
ajax.googleapis.com |
| whitelisted |
www.google.com |
| whitelisted |
image.thum.io |
| unknown |
content-autofill.googleapis.com |
| whitelisted |
t0.gstatic.com |
| whitelisted |
webmail.bourbon-online.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
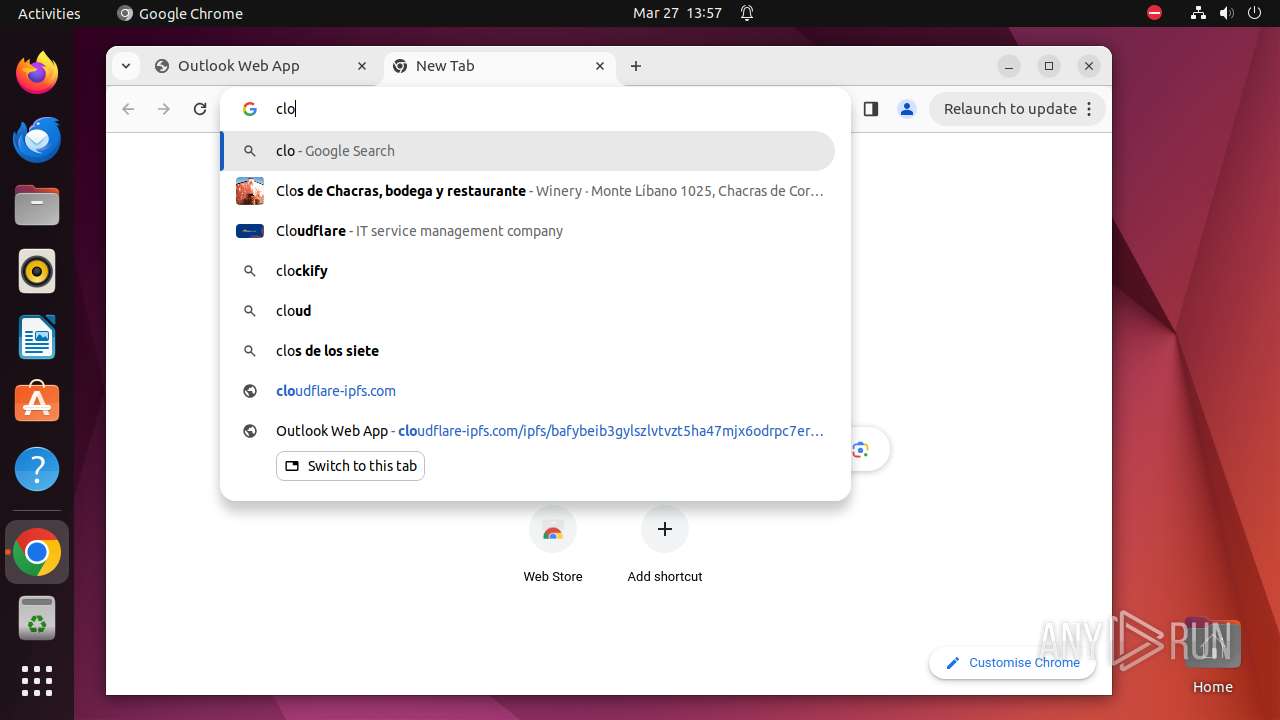
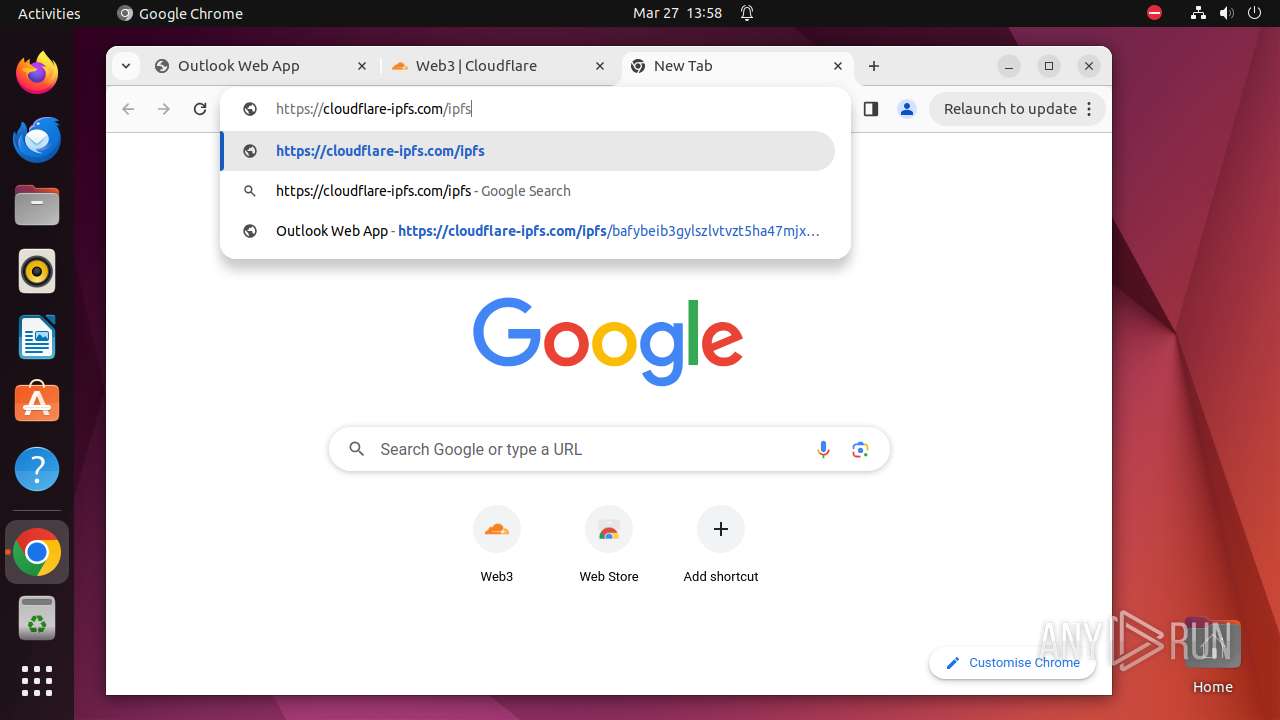
— | — | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Phishing domain was detected (replit .app) |
— | — | Misc activity | ET INFO Peer to Peer File Sharing Service in DNS Lookup (cloudflare-ipfs .com) |
— | — | Misc activity | ET INFO Peer to Peer File Sharing Service in DNS Lookup (cloudflare-ipfs .com) |
— | — | Misc activity | ET INFO Peer to Peer File Sharing Service Domain in TLS SNI (cloudflare-ipfs .com) |
— | — | Misc activity | ET INFO Peer to Peer File Sharing Service Domain in TLS SNI (cloudflare-ipfs .com) |