| File name: | PrntScrnOfAMZOrderID.jpg.exe |
| Full analysis: | https://app.any.run/tasks/4a201a19-5057-4830-ab2d-0ba7e205706f |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2020, 09:02:41 |
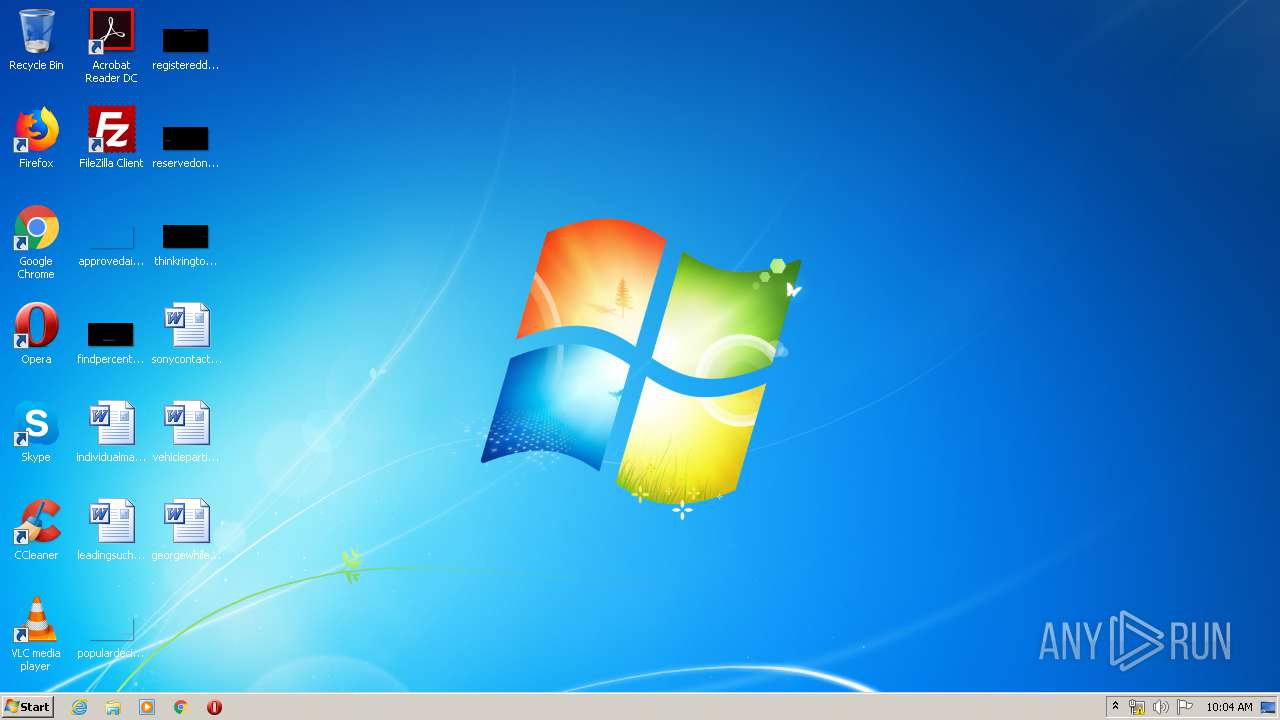
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 40E76DEB2066F8674C4B8276AB787FF2 |
| SHA1: | CC0B9B7D616F4B8338A74A5F44E2F65061F03009 |
| SHA256: | D2E4EF567C497136B0B0B75929EF07643296CA2814B6B0F19303EE29CB194CB1 |
| SSDEEP: | 12288:TzQXRXiF6AERD283g37Zkjjsjj3R+uD07fpMv/G:IZJoqgrZWyB+cG |
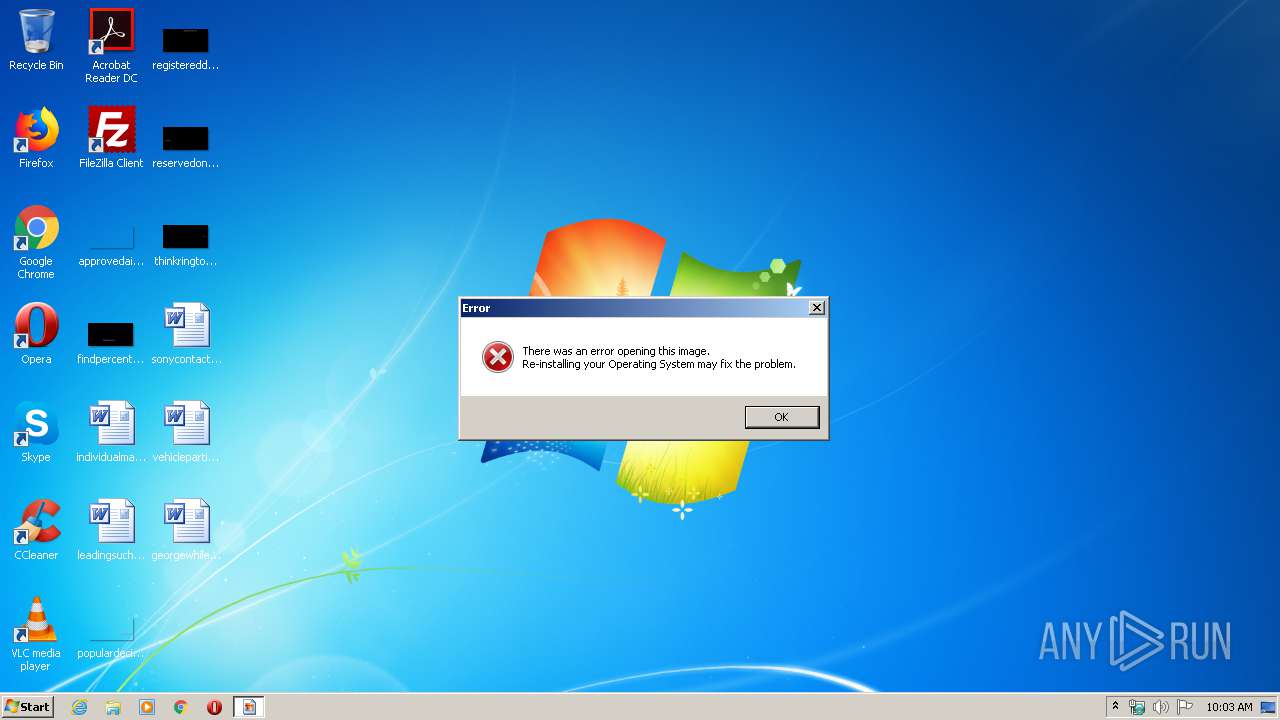
MALICIOUS
Changes the autorun value in the registry
- svchost.exe (PID: 2760)
Uses SVCHOST.EXE for hidden code execution
- PrntScrnOfAMZOrderID.jpg.exe (PID: 3472)
SUSPICIOUS
Executable content was dropped or overwritten
- PrntScrnOfAMZOrderID.jpg.exe (PID: 3472)
- svchost.exe (PID: 2760)
Application launched itself
- PrntScrnOfAMZOrderID.jpg.exe (PID: 3040)
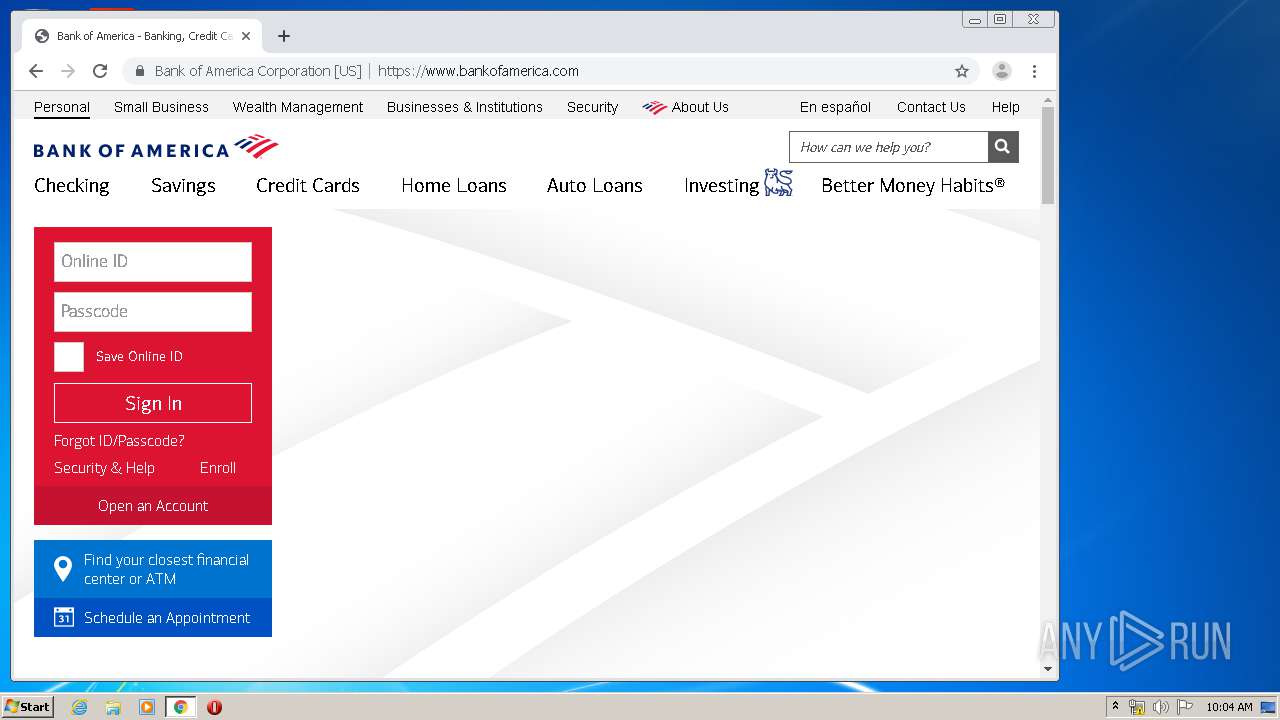
Modifies files in Chrome extension folder
- chrome.exe (PID: 3972)
INFO
Manual execution by user
- chrome.exe (PID: 3972)
Application launched itself
- chrome.exe (PID: 3972)
Reads the hosts file
- chrome.exe (PID: 3688)
- chrome.exe (PID: 3972)
Reads settings of System Certificates
- chrome.exe (PID: 3688)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Borland Delphi 7 (88.6) |
|---|---|---|
| .exe | | | UPX compressed Win32 Executable (3.6) |
| .exe | | | Win32 EXE Yoda's Crypter (3.5) |
| .exe | | | Win32 Executable Delphi generic (1.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 49664 |
| InitializedDataSize: | 20992 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xce04 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x0000C174 | 0x0000C200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.42376 |
DATA | 0x0000E000 | 0x00000C44 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.36664 |
BSS | 0x0000F000 | 0x00000D51 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00010000 | 0x000008A4 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.33651 |
.tls | 0x00011000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00012000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.201539 |
.reloc | 0x00013000 | 0x00001158 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.56195 |
.rsrc | 0x00015000 | 0x00002460 | 0x00002600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.45074 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.95414 | 788 | Latin 1 / Western European | English - United States | RT_STRING |
2 | 3.96628 | 592 | Latin 1 / Western European | English - United States | RT_STRING |
3 | 3.78437 | 370 | Latin 1 / Western European | English - United States | RT_STRING |
4 | 3.66319 | 266 | Latin 1 / Western European | English - United States | RT_STRING |
4092 | 2.84211 | 220 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 2.99785 | 228 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4094 | 3.19198 | 580 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4095 | 3.22874 | 868 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4096 | 3.18442 | 672 | Latin 1 / Western European | UNKNOWN | RT_STRING |
DVCLAL | 4 | 16 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
advapi32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
72
Monitored processes
36
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,721397006358533017,13788920306318688734,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14026438508406746219 --mojo-platform-channel-handle=3564 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=992,721397006358533017,13788920306318688734,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=12391891351904181278 --mojo-platform-channel-handle=2492 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1516 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,721397006358533017,13788920306318688734,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11805038669987851169 --mojo-platform-channel-handle=3760 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,721397006358533017,13788920306318688734,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17213709699997020590 --mojo-platform-channel-handle=4480 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,721397006358533017,13788920306318688734,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9843061976923451839 --mojo-platform-channel-handle=4232 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2060 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,721397006358533017,13788920306318688734,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3724183372670993629 --mojo-platform-channel-handle=2568 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2156 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,721397006358533017,13788920306318688734,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6235171201155792754 --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3156 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2216 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,721397006358533017,13788920306318688734,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10748734486092427416 --mojo-platform-channel-handle=3944 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,721397006358533017,13788920306318688734,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14049350181918821838 --mojo-platform-channel-handle=4156 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
992
Read events
838
Write events
149
Delete events
5
Modification events
| (PID) Process: | (3472) PrntScrnOfAMZOrderID.jpg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Tabs |
| Operation: | write | Name: | fz |
Value: DVd4p5a+Lk3CB89AYWHBc2QyUelUAj5DzBBjvOhuDIJ6kSSxP0WxB4+1XH2W3A3IdSTSCexpag6lTC | |||
| (PID) Process: | (2760) svchost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Tabs |
| Operation: | write | Name: | ovw |
Value: DVd4p5a+Lk3CB89AYWHBc2QyUelUAj5DzBBjvOhuDIJ6kSSxP0WxB4+1XH2W3A3IdSTSCexpag6lTC | |||
| (PID) Process: | (2760) svchost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Tabs |
| Operation: | write | Name: | fzl |
Value: DVd4p5a+Lk3CB89AYWHBc2QyUelUAj5DzBBjvOhuDIJ6kSSxP0WxB4+1XH2W3A3IdSTSCexpaEaNYB | |||
| (PID) Process: | (2760) svchost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows |
| Operation: | write | Name: | Load |
Value: C:\Users\admin\AppData\Local\Microsoft\Windows\mshthtr.exe | |||
| (PID) Process: | (2760) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2760) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2760) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2760) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2760) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2760) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
Executable files
3
Suspicious files
92
Text files
185
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2760 | svchost.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\10911687.tmp | — | |
MD5:— | SHA256:— | |||
| 3972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E8307AB-F84.pma | — | |
MD5:— | SHA256:— | |||
| 3972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\14feca10-88ad-4159-a4bb-cf01d0cadae6.tmp | — | |
MD5:— | SHA256:— | |||
| 3972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2760 | svchost.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\mshthtr.lbt | text | |
MD5:— | SHA256:— | |||
| 3972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFa80761.TMP | text | |
MD5:— | SHA256:— | |||
| 3972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
| 3972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
65
DNS requests
63
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
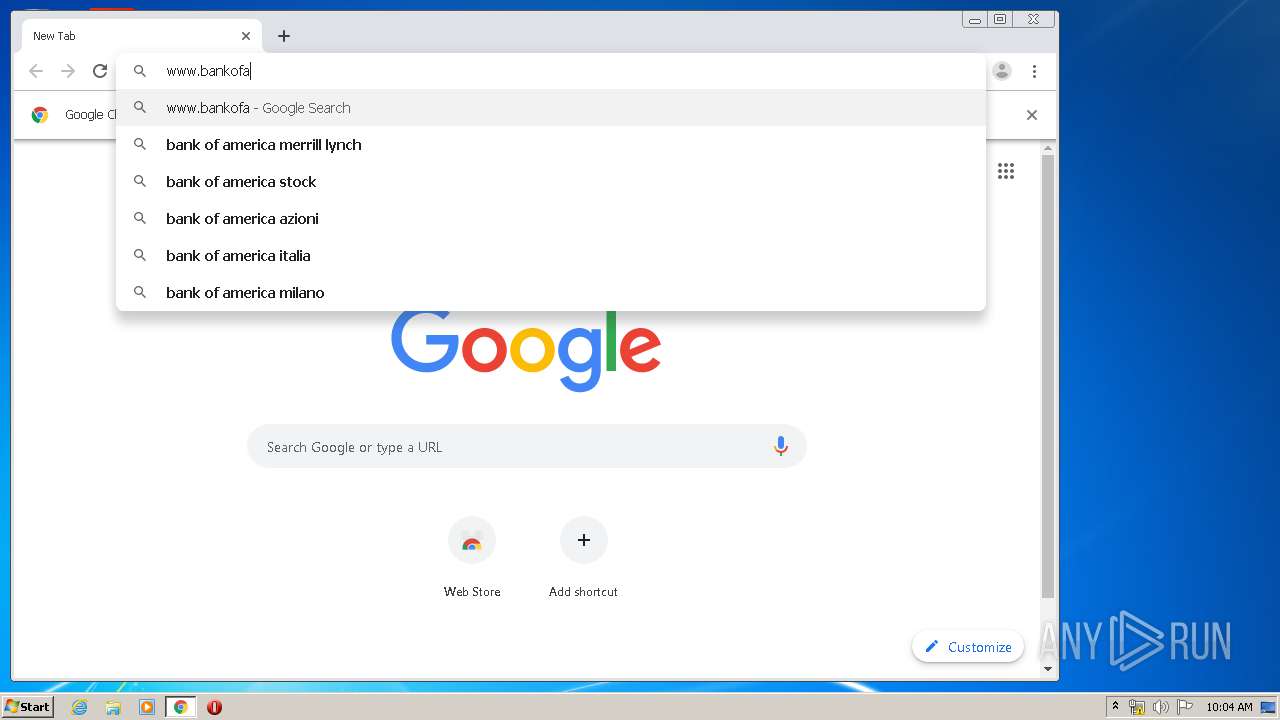
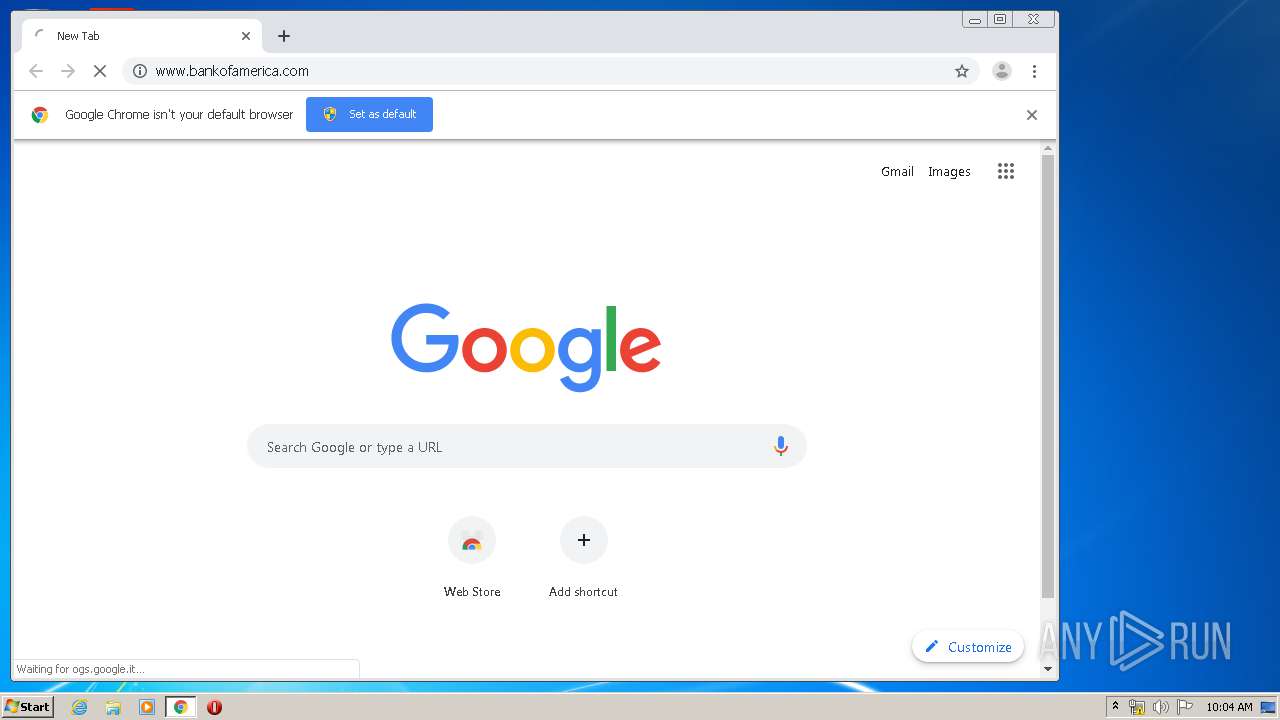
3688 | chrome.exe | GET | 301 | 171.161.203.100:80 | http://www.bankofamerica.com/ | US | — | — | whitelisted |
3688 | chrome.exe | GET | 302 | 172.217.23.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 520 b | whitelisted |
3688 | chrome.exe | GET | 200 | 23.8.12.208:80 | http://ocsp.entrust.net/MEUwQzBBMD8wPTAJBgUrDgMCGgUABBQsSqZpWQuWOxHU9pAda%2B7Lf6V20AQUaJDkZ6SmU4DHhmak8fdLQ%2FuEvW0CBFHTQEQ%3D | NL | der | 1.53 Kb | whitelisted |
3688 | chrome.exe | GET | 200 | 23.8.12.208:80 | http://ocsp.entrust.net/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQnuEQcScL%2FkljKed%2BRzpzFYOq9kwQUw%2FfQtSowra8NkSFwOVTdvIlwxzoCEDZJCOcySzQgAAAAAFTQYJs%3D | NL | der | 1.55 Kb | whitelisted |
3688 | chrome.exe | GET | 200 | 23.8.12.208:80 | http://ocsp.entrust.net/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBQnuEQcScL%2FkljKed%2BRzpzFYOq9kwQUw%2FfQtSowra8NkSFwOVTdvIlwxzoCEQC46QauKdDpigAAAABUz%2FYg | NL | der | 1.55 Kb | whitelisted |
3688 | chrome.exe | GET | 200 | 23.8.12.208:80 | http://ocsp.entrust.net/MEUwQzBBMD8wPTAJBgUrDgMCGgUABBQsSqZpWQuWOxHU9pAda%2B7Lf6V20AQUaJDkZ6SmU4DHhmak8fdLQ%2FuEvW0CBFHTQEQ%3D | NL | der | 1.53 Kb | whitelisted |
3688 | chrome.exe | GET | 200 | 23.8.12.208:80 | http://ocsp.entrust.net/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBQnuEQcScL%2FkljKed%2BRzpzFYOq9kwQUw%2FfQtSowra8NkSFwOVTdvIlwxzoCEQCTeA36GtsRDgAAAABU0PIa | NL | der | 1.55 Kb | whitelisted |
3688 | chrome.exe | GET | 200 | 23.8.12.208:80 | http://ocsp.entrust.net/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBTLXNCzDvBhHecWjg70iJhBW0InywQUanImetAe733nO2lR1GyNn5ASZqsCDGGh59IAAAAAUdNmpg%3D%3D | NL | der | 1.55 Kb | whitelisted |
3688 | chrome.exe | GET | 200 | 23.8.12.208:80 | http://ocsp.entrust.net/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBQnuEQcScL%2FkljKed%2BRzpzFYOq9kwQUw%2FfQtSowra8NkSFwOVTdvIlwxzoCEQD2bMk7hsqhtgAAAABU0O1n | NL | der | 1.55 Kb | whitelisted |
3688 | chrome.exe | GET | 200 | 23.8.12.208:80 | http://ocsp.entrust.net/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBQnuEQcScL%2FkljKed%2BRzpzFYOq9kwQUw%2FfQtSowra8NkSFwOVTdvIlwxzoCEQCnfAmIxcJvCAAAAABU0GRe | NL | der | 1.55 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3688 | chrome.exe | 216.58.206.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3688 | chrome.exe | 172.217.16.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3688 | chrome.exe | 172.217.21.238:443 | apis.google.com | Google Inc. | US | whitelisted |
3688 | chrome.exe | 172.217.21.206:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
3688 | chrome.exe | 172.217.22.36:443 | www.google.com | Google Inc. | US | whitelisted |
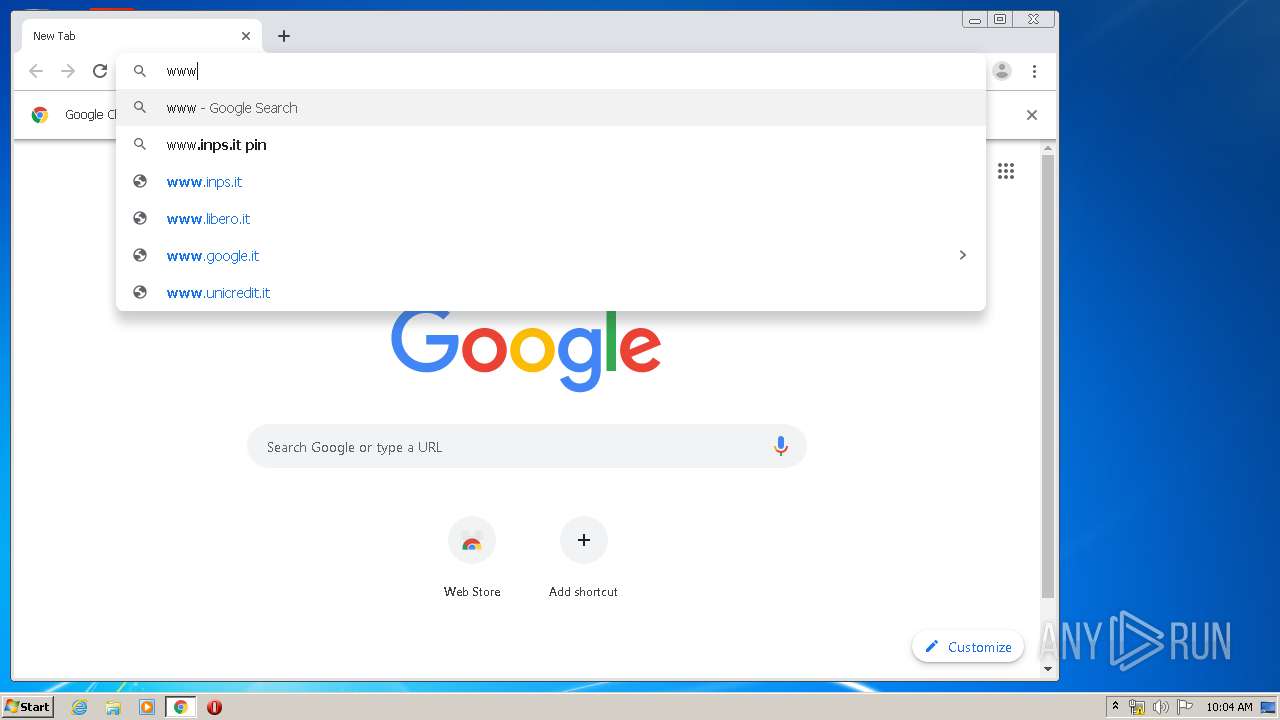
3688 | chrome.exe | 172.217.23.163:443 | www.google.it | Google Inc. | US | whitelisted |
3688 | chrome.exe | 216.58.207.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
3688 | chrome.exe | 74.125.99.91:80 | r5---sn-hpa7kn7s.gvt1.com | Google Inc. | US | whitelisted |
3688 | chrome.exe | 172.217.23.142:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
3688 | chrome.exe | 74.125.153.27:80 | r5---sn-hpa7zned.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |
www.google.com |
| malicious |
www.google.it |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3688 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3688 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
3688 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3688 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
3688 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3688 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
3688 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3688 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
3688 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3688 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |