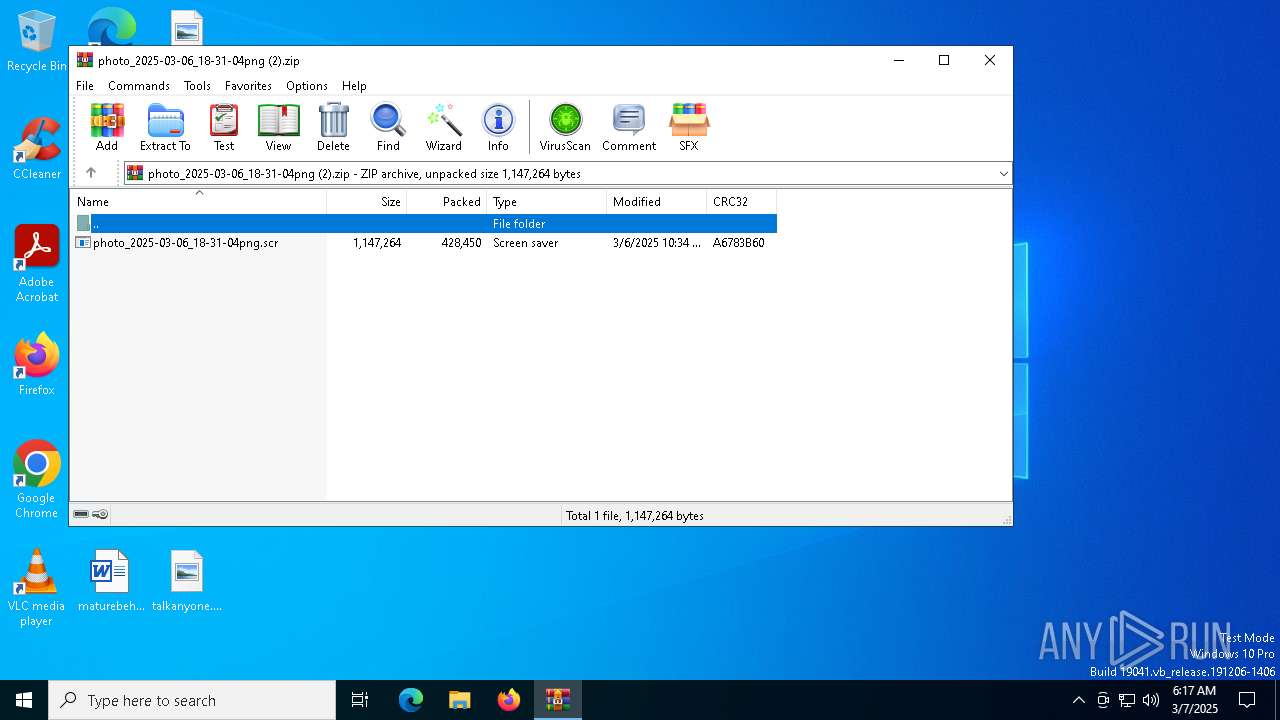
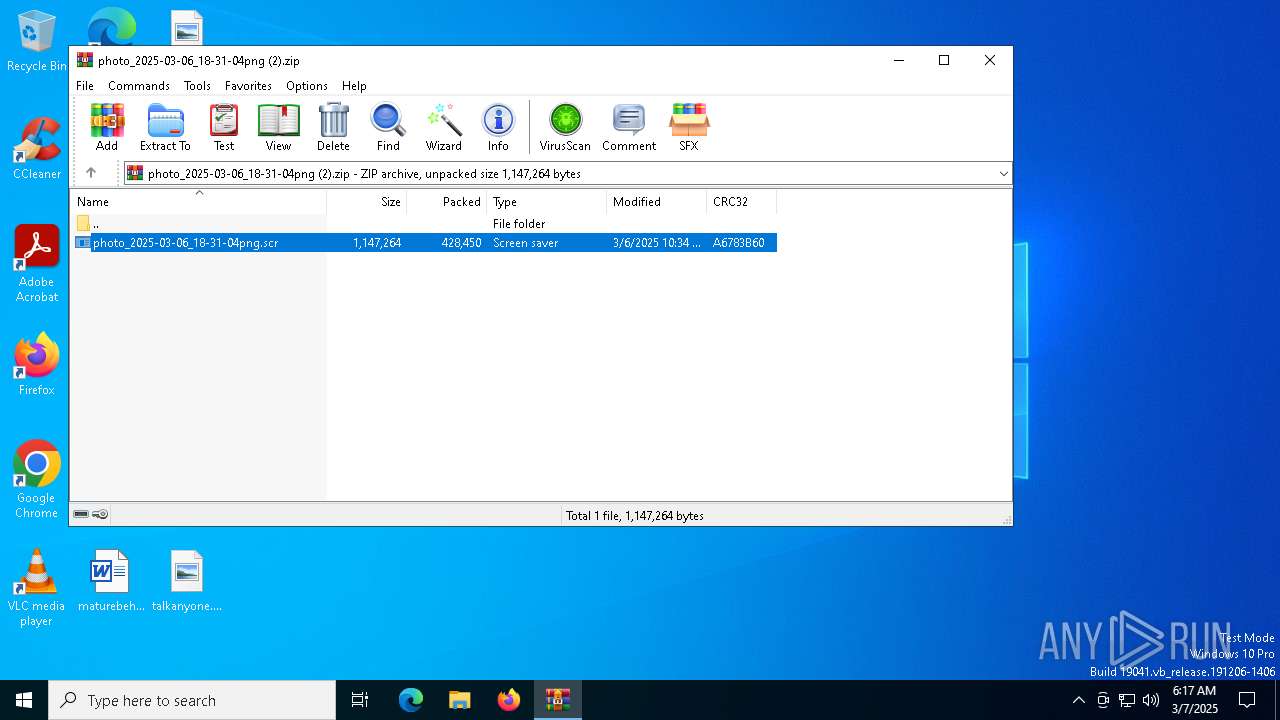
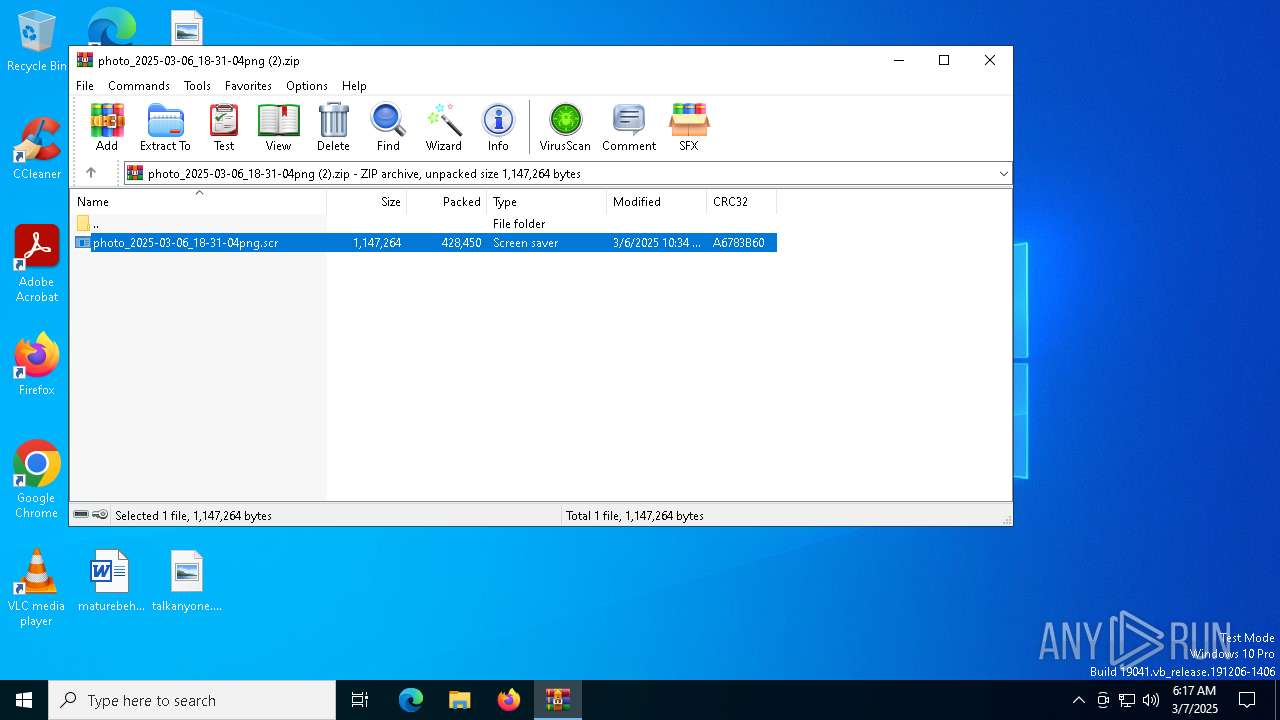
| File name: | photo_2025-03-06_18-31-04png (2).zip |
| Full analysis: | https://app.any.run/tasks/00377c51-f78d-43bc-a0c6-9ba1ee6d5317 |
| Verdict: | Malicious activity |
| Analysis date: | March 07, 2025, 06:17:07 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
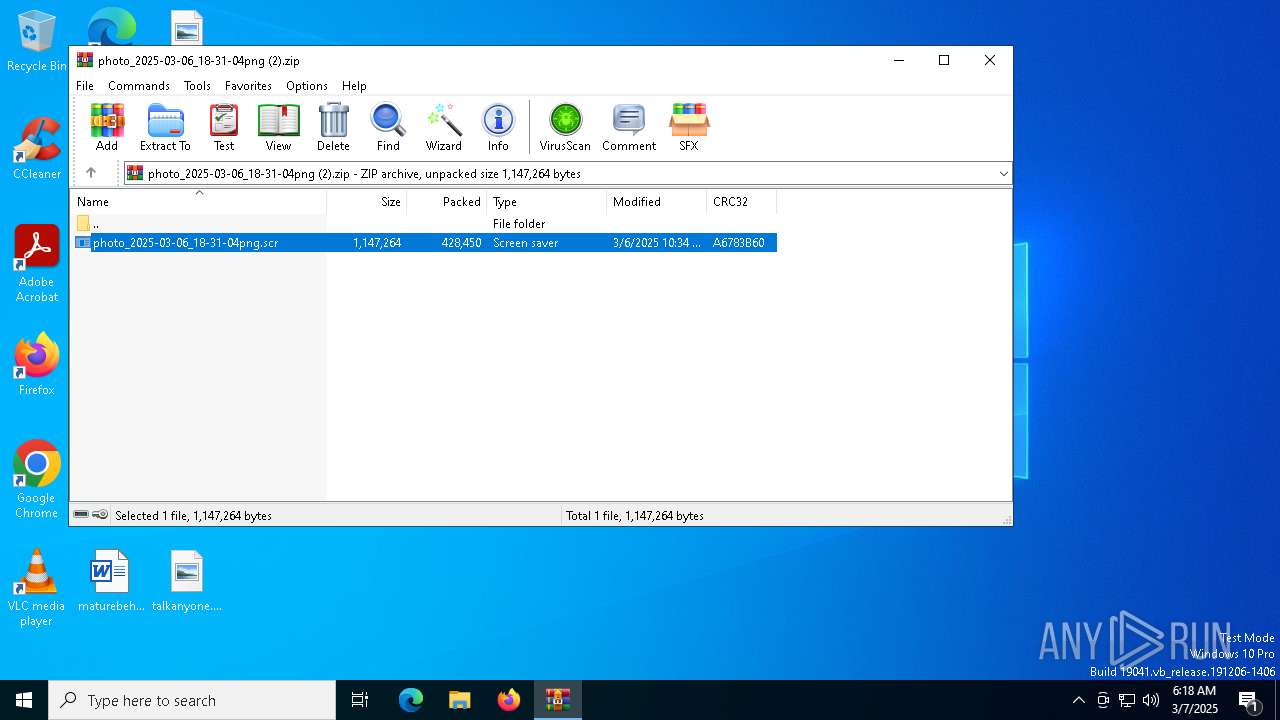
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 42CA60FFB94CECE20F0DB737E2ACC974 |
| SHA1: | D5B63204CA00BEA4E2CC7F3D674CB1D66A34B685 |
| SHA256: | D2E354A8E29287C7B21677587F8993D700C2A8919FE72A017316EFE1BD8DCED9 |
| SSDEEP: | 12288:lOHMa2+7NH6IWlwsNnMWstyIVlS7+ZE0ubDJGfNWv06XKbb14bdEJb7+G:UMa57x6Zl9NnMLtyYlS7KE0ubDJGfN4G |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 7192)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7192)
- photo_2025-03-06_18-31-04png.scr (PID: 7532)
- 1vs5scep.tmp (PID: 8180)
- photo_2025-03-06_18-31-04png.scr (PID: 7388)
- ShellExperienceHost.exe (PID: 2148)
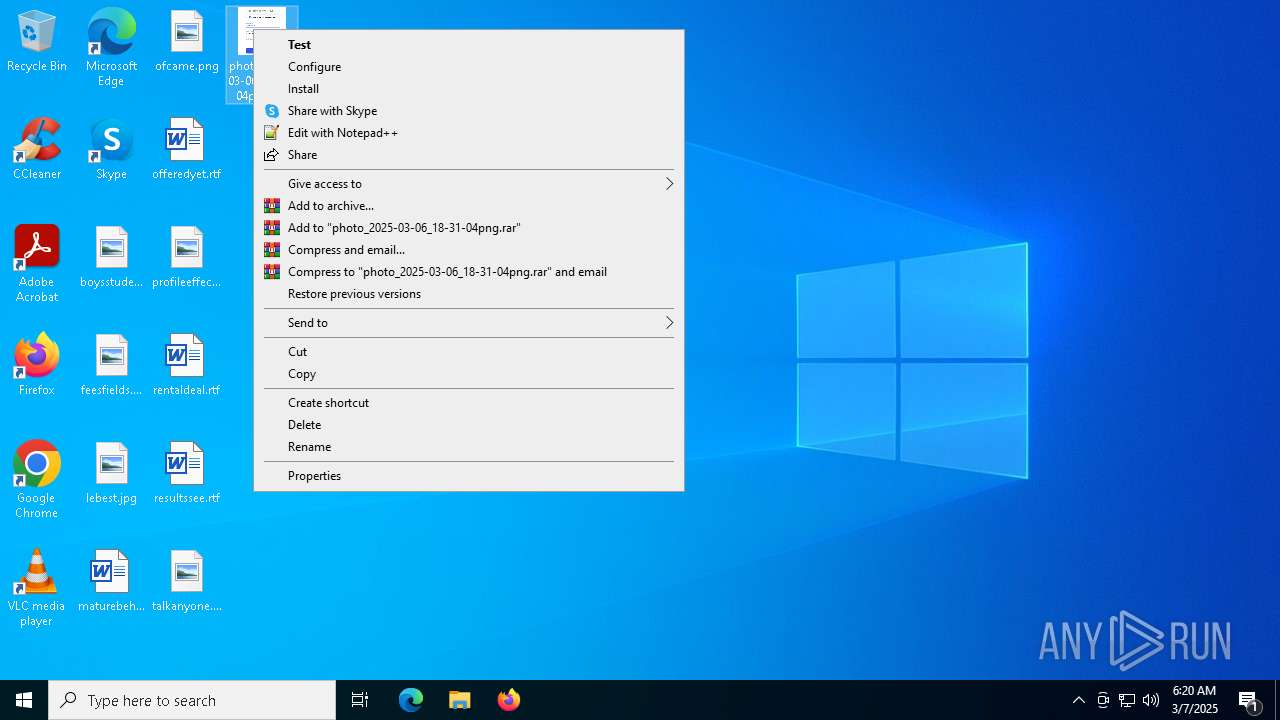
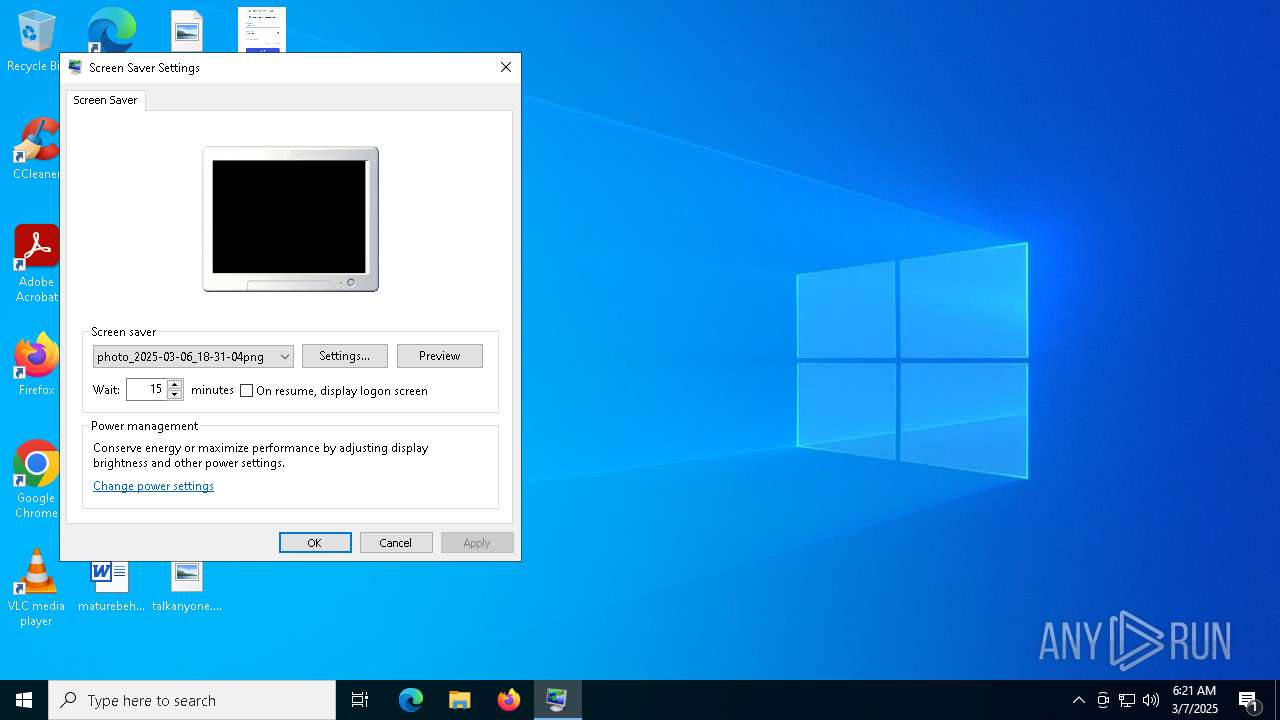
Starts application with an unusual extension
- WinRAR.exe (PID: 7192)
- photo_2025-03-06_18-31-04png.scr (PID: 7532)
- rundll32.exe (PID: 4608)
Connects to the server without a host name
- photo_2025-03-06_18-31-04png.scr (PID: 7532)
- 1vs5scep.tmp (PID: 8180)
- photo_2025-03-06_18-31-04png.scr (PID: 7388)
Likely accesses (executes) a file from the Public directory
- 1vs5scep.tmp (PID: 8180)
Starts itself from another location
- photo_2025-03-06_18-31-04png.scr (PID: 7532)
Executable content was dropped or overwritten
- photo_2025-03-06_18-31-04png.scr (PID: 7532)
Connects to unusual port
- 1vs5scep.tmp (PID: 8180)
INFO
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 8060)
- BackgroundTransferHost.exe (PID: 5404)
- BackgroundTransferHost.exe (PID: 5548)
- BackgroundTransferHost.exe (PID: 5960)
- BackgroundTransferHost.exe (PID: 1180)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 5404)
- rundll32.exe (PID: 4608)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 5404)
- photo_2025-03-06_18-31-04png.scr (PID: 7532)
- 1vs5scep.tmp (PID: 8180)
- slui.exe (PID: 4068)
- photo_2025-03-06_18-31-04png.scr (PID: 7388)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 5404)
- slui.exe (PID: 7444)
- slui.exe (PID: 4068)
Reads the computer name
- photo_2025-03-06_18-31-04png.scr (PID: 7532)
- ShellExperienceHost.exe (PID: 2148)
- 1vs5scep.tmp (PID: 8180)
- photo_2025-03-06_18-31-04png.scr (PID: 7388)
Checks supported languages
- photo_2025-03-06_18-31-04png.scr (PID: 7532)
- 1vs5scep.tmp (PID: 8180)
- ShellExperienceHost.exe (PID: 2148)
- photo_2025-03-06_18-31-04png.scr (PID: 7388)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7192)
Manual execution by a user
- rundll32.exe (PID: 4608)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:03:06 18:34:56 |
| ZipCRC: | 0xa6783b60 |
| ZipCompressedSize: | 428450 |
| ZipUncompressedSize: | 1147264 |
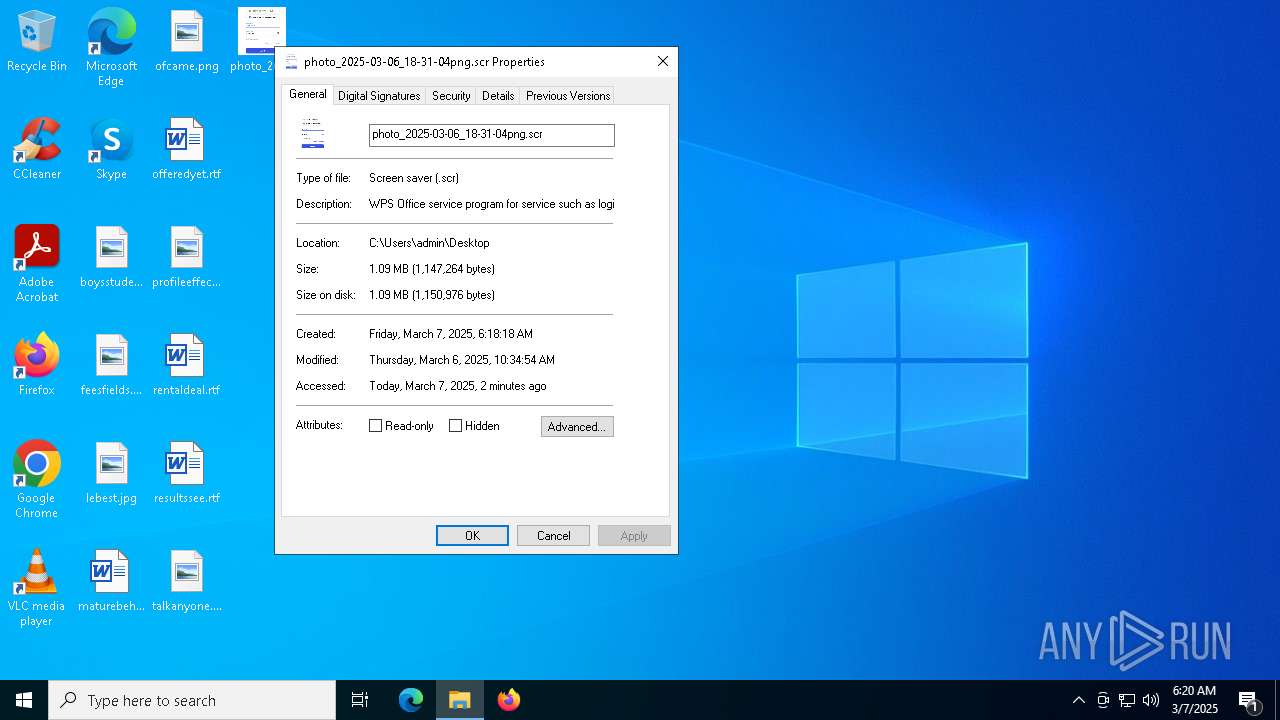
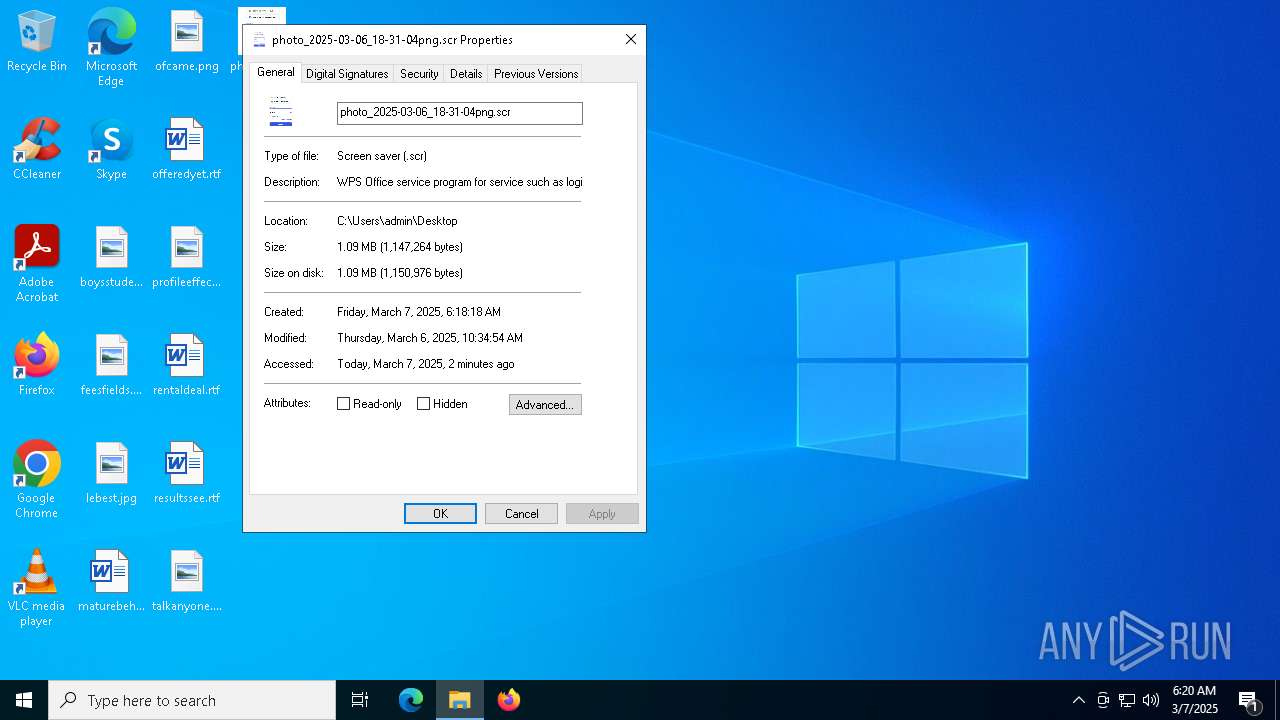
| ZipFileName: | photo_2025-03-06_18-31-04png.scr |
Total processes
153
Monitored processes
15
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1180 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2148 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4068 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4608 | "rundll32.exe" desk.cpl,InstallScreenSaver C:\Users\admin\Desktop\photo_2025-03-06_18-31-04png.scr | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5404 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5548 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5960 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
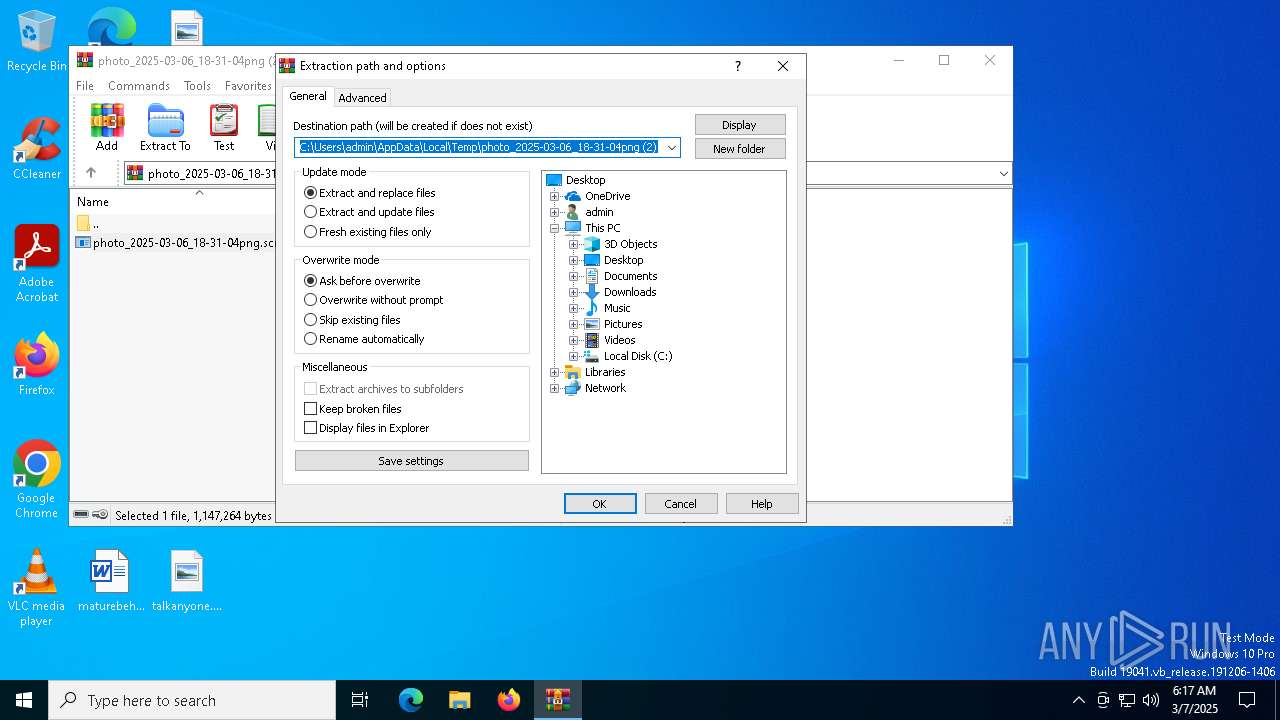
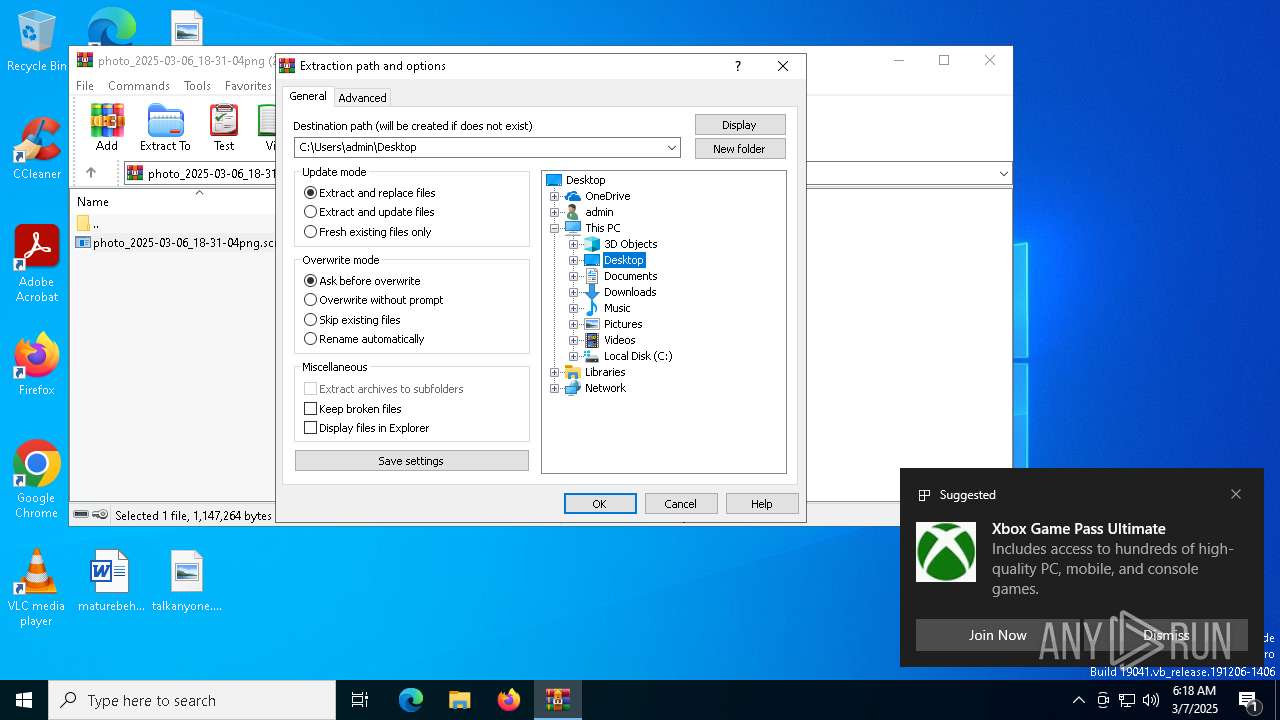
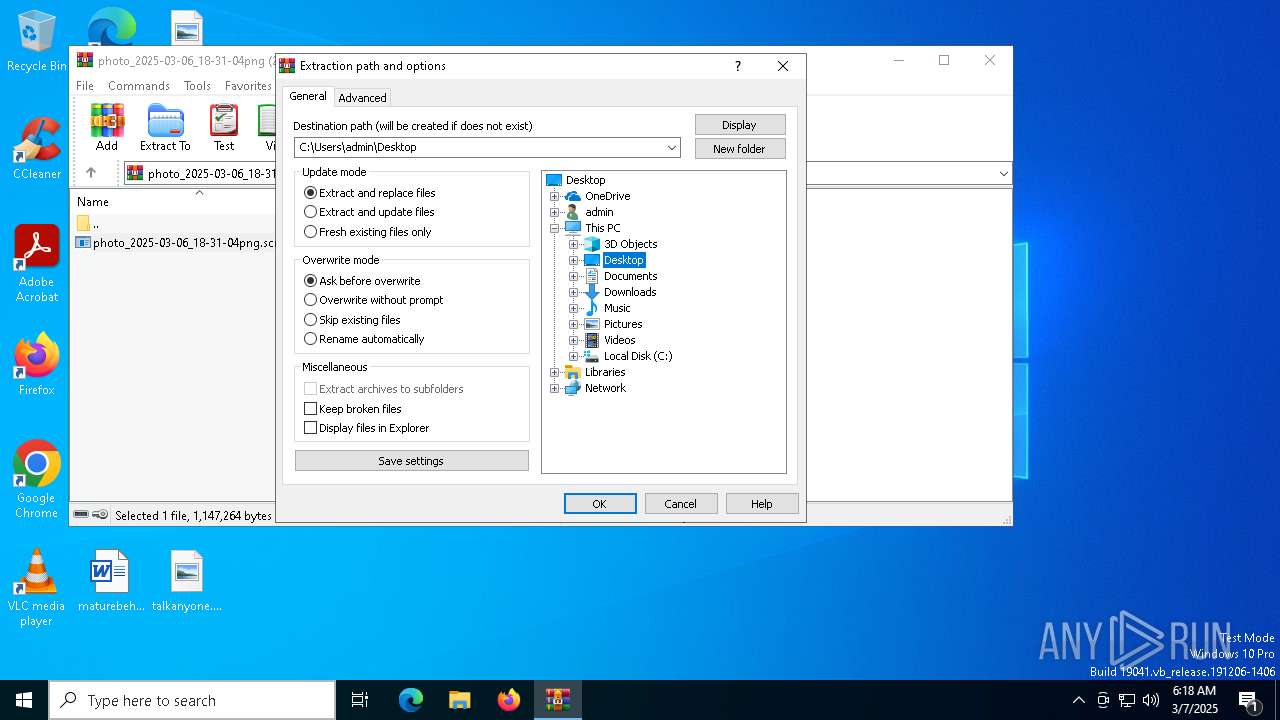
| 7192 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\photo_2025-03-06_18-31-04png (2).zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 7388 | C:\Users\admin\Desktop\photo_2025-03-06_18-31-04png.scr /p 393838 | C:\Users\admin\Desktop\photo_2025-03-06_18-31-04png.scr | rundll32.exe | ||||||||||||
User: admin Company: Zhuhai Kingsoft Office Software Co.,Ltd Integrity Level: MEDIUM Description: WPS Office service program for service such as login and Cloud storage Exit code: 0 Version: 12,1,0,18608 Modules
| |||||||||||||||
Total events
7 632
Read events
7 576
Write events
43
Delete events
13
Modification events
| (PID) Process: | (7192) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7192) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7192) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7192) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\photo_2025-03-06_18-31-04png (2).zip | |||
| (PID) Process: | (7192) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7192) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7192) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7192) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (8060) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (8060) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
3
Suspicious files
5
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5404 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\bdd98fab-372b-403d-a21e-9982cfb50622.down_data | — | |
MD5:— | SHA256:— | |||
| 5404 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\bdd98fab-372b-403d-a21e-9982cfb50622.6d828345-36e9-4c5e-8b15-2cb5135f4727.down_meta | binary | |
MD5:1CAE56899186BEC442FA4FEB3D1DFC57 | SHA256:8FAF094B59630F9C9F9B21099324568CF60BB3BA39EFC4E4BC88D45E7B65E46D | |||
| 7532 | photo_2025-03-06_18-31-04png.scr | C:\Users\Public\Downloads\1vs5scep.tmp | executable | |
MD5:D5A693EFDEF4E71D95267FAD4A247D8F | SHA256:DCE8404FFFA4C80799304F7E1A27B9602A86BD885771A58D0F10FD60DE9AC956 | |||
| 5404 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\MetaData\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:AE20CA69BD9582ADE90121EBEA114712 | SHA256:D4AEC9223CC30CFDBFB1526EA24A5A5D3E49AAC266701CF394C5D5EAEA7E84CC | |||
| 4608 | rundll32.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Themes\Custom.theme | text | |
MD5:1348E4E8FC451E8021F935F4B1376C95 | SHA256:CDF0440A375C4D4A180A358EA3C87448482622FBC71833BC797EC1410E54BB01 | |||
| 5404 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:38989CDC9B939CBF439472EC8FEBE5D7 | SHA256:0188CCDAB61284075618619F99DBB9FC9BA066DF5B1FF02EC5684476CABA0732 | |||
| 7192 | WinRAR.exe | C:\Users\admin\Desktop\photo_2025-03-06_18-31-04png.scr | executable | |
MD5:D5A693EFDEF4E71D95267FAD4A247D8F | SHA256:DCE8404FFFA4C80799304F7E1A27B9602A86BD885771A58D0F10FD60DE9AC956 | |||
| 7192 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa7192.5277\photo_2025-03-06_18-31-04png.scr | executable | |
MD5:D5A693EFDEF4E71D95267FAD4A247D8F | SHA256:DCE8404FFFA4C80799304F7E1A27B9602A86BD885771A58D0F10FD60DE9AC956 | |||
| 5404 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\d0b90063-7448-4e8a-87fa-9ab36f28b1a0.up_meta_secure | binary | |
MD5:EEE3DA6682FF385248A7B4ADFE6C9873 | SHA256:F2C5EA82C644E40DE039A75BE0128F219E78006E6DB186FF4623F8F7033DBC98 | |||
| 5404 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\d0b90063-7448-4e8a-87fa-9ab36f28b1a0.6d828345-36e9-4c5e-8b15-2cb5135f4727.down_meta | binary | |
MD5:1CAE56899186BEC442FA4FEB3D1DFC57 | SHA256:8FAF094B59630F9C9F9B21099324568CF60BB3BA39EFC4E4BC88D45E7B65E46D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
36
DNS requests
17
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5404 | BackgroundTransferHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | DE | binary | 313 b | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
7020 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
7340 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | DE | binary | 471 b | whitelisted |
7020 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
7532 | photo_2025-03-06_18-31-04png.scr | GET | 200 | 103.177.76.233:80 | http://103.177.76.233/1660392789.jpg | SG | image | 184 Kb | unknown |
8180 | 1vs5scep.tmp | GET | 200 | 103.177.76.233:80 | http://103.177.76.233/1660392789.jpg | SG | image | 184 Kb | unknown |
7388 | photo_2025-03-06_18-31-04png.scr | GET | 200 | 103.177.76.233:80 | http://103.177.76.233/1660392789.jpg | SG | image | 184 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.160.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
5164 | RUXIMICS.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2112 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7340 | backgroundTaskHost.exe | 20.223.36.55:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |