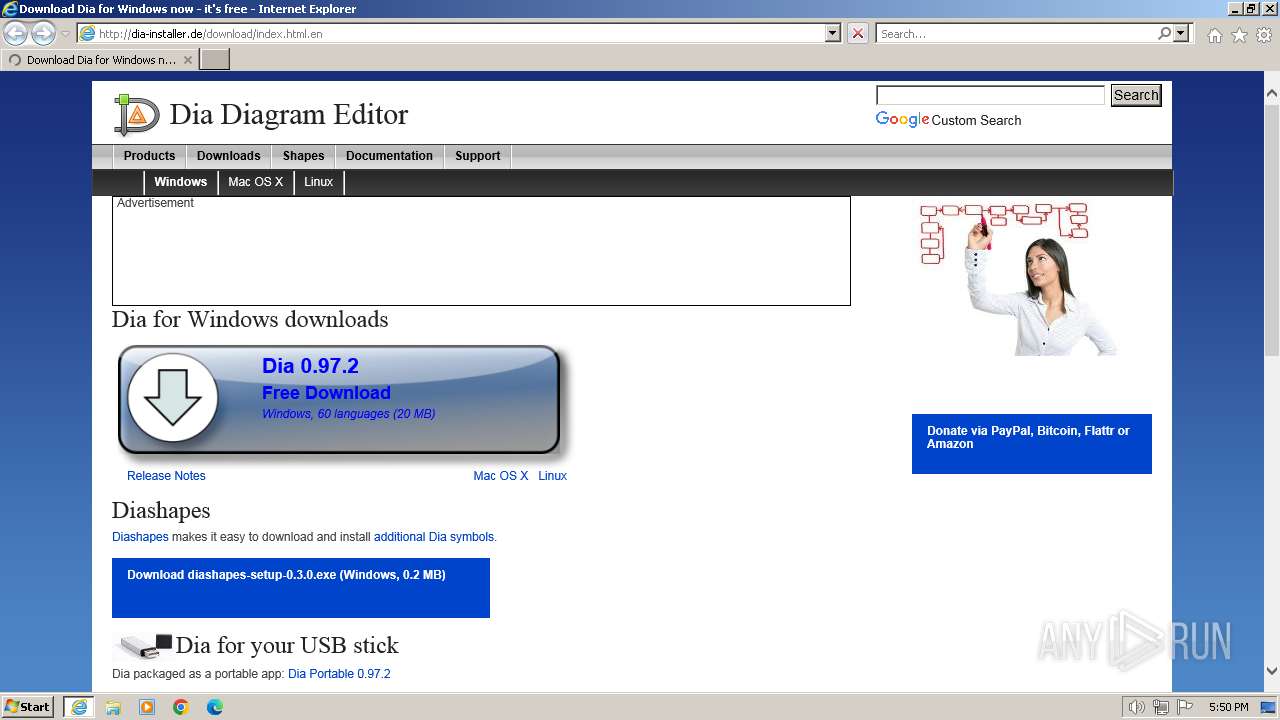
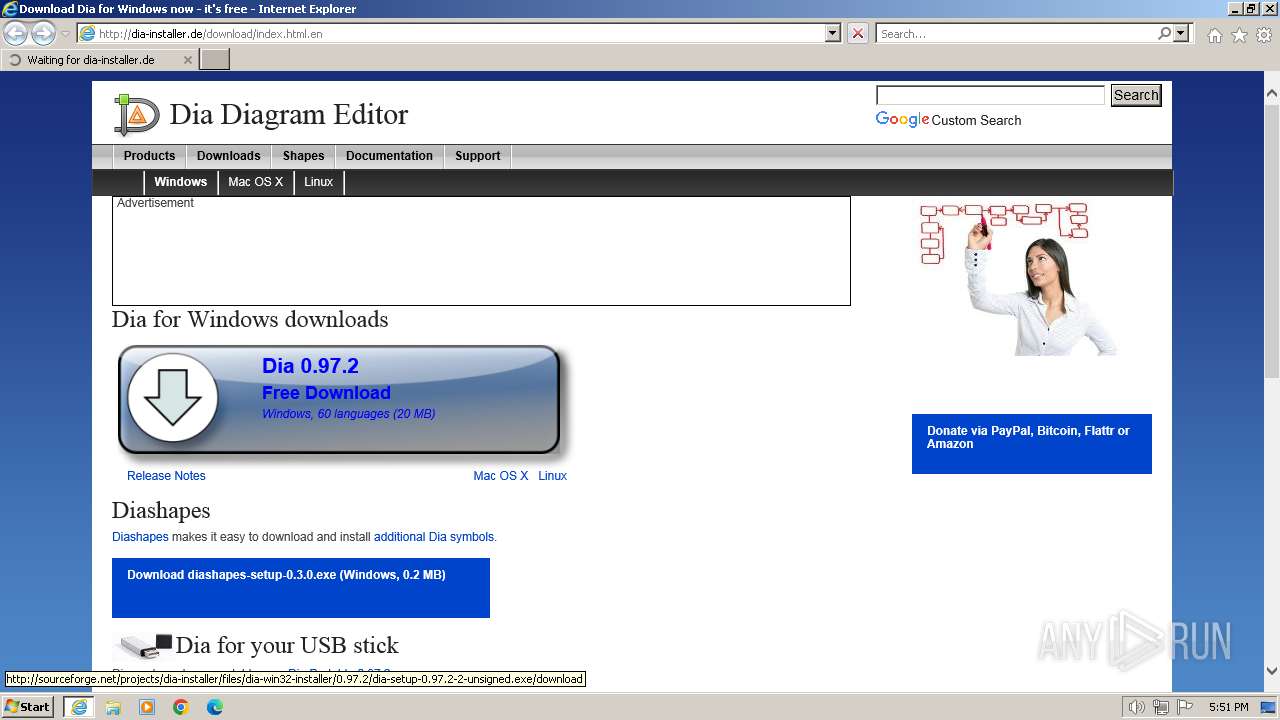
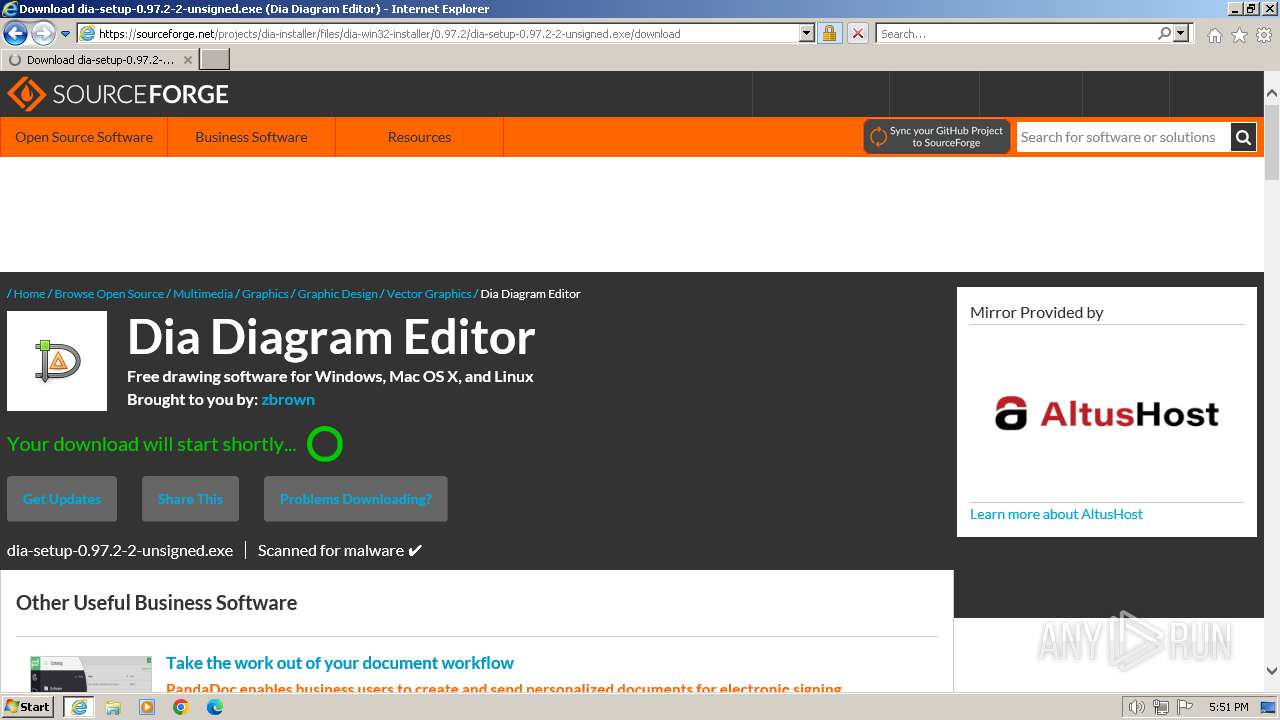
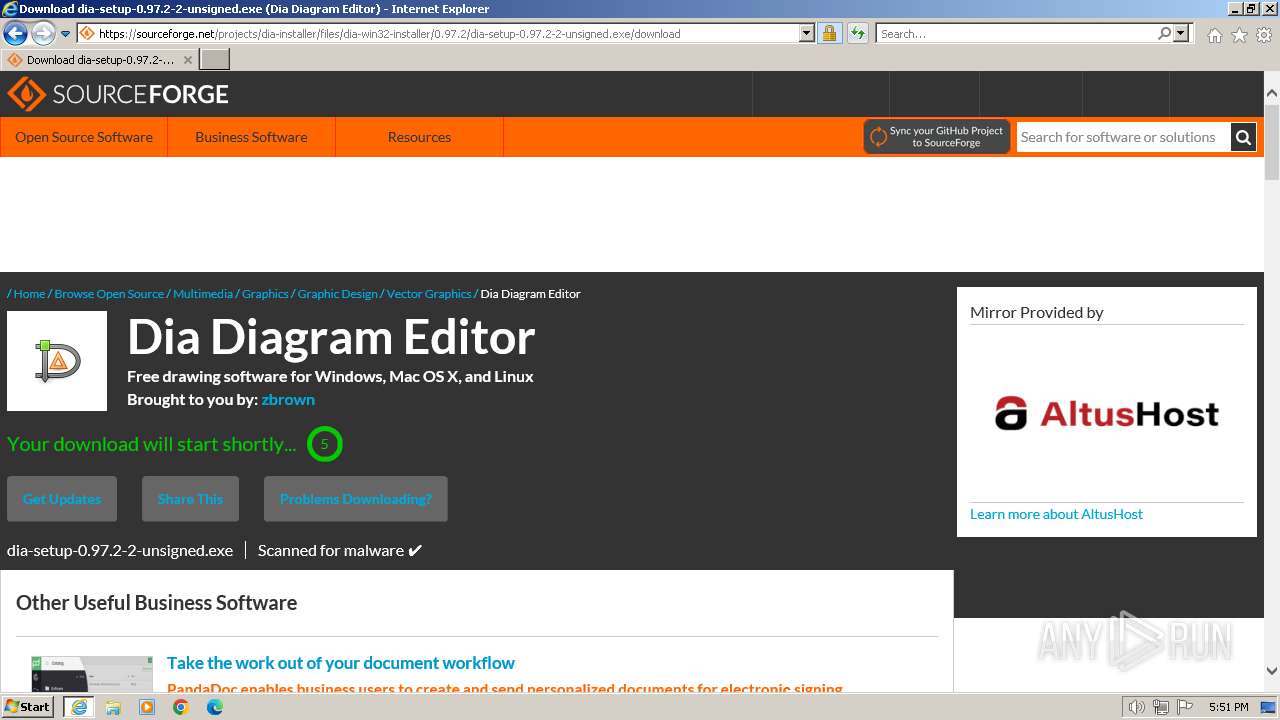
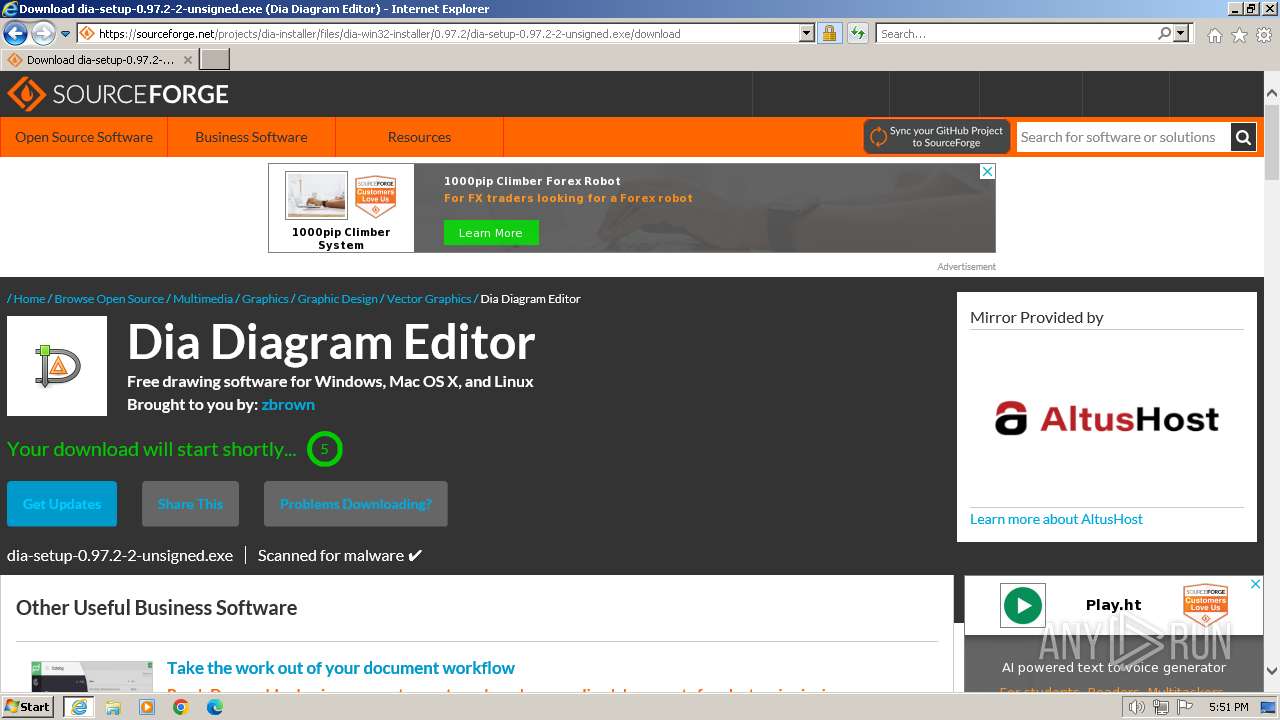
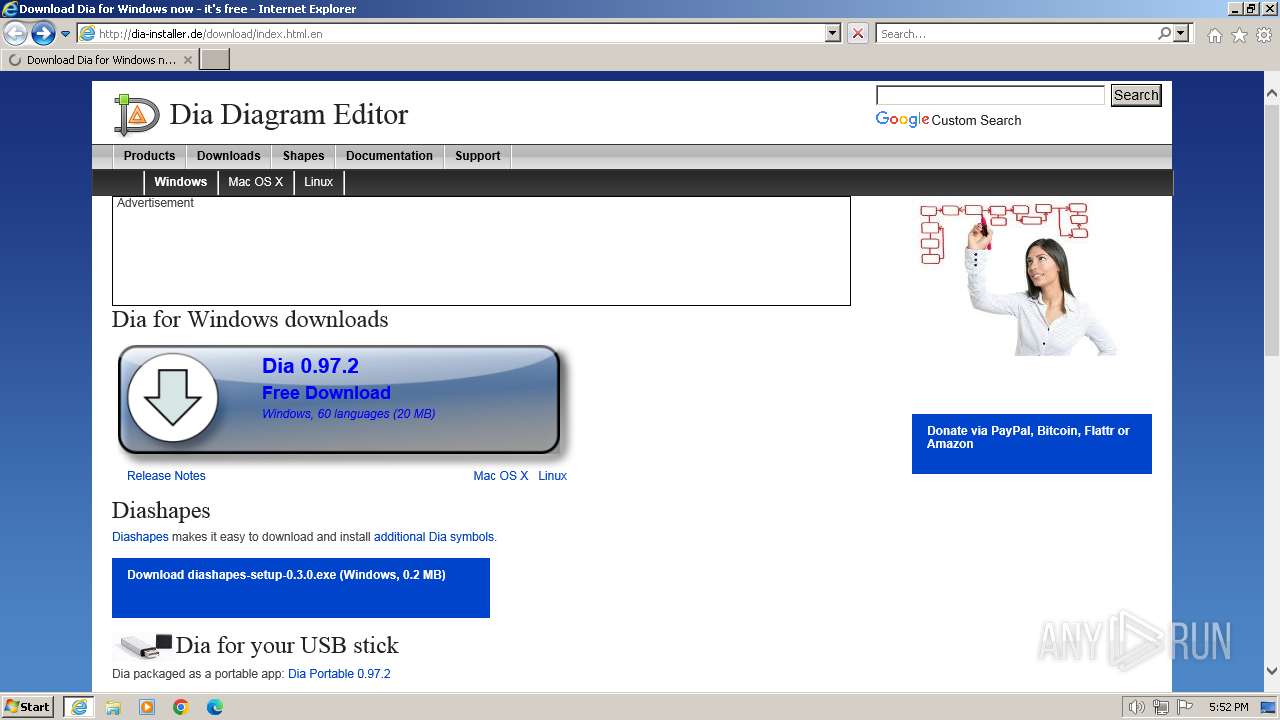
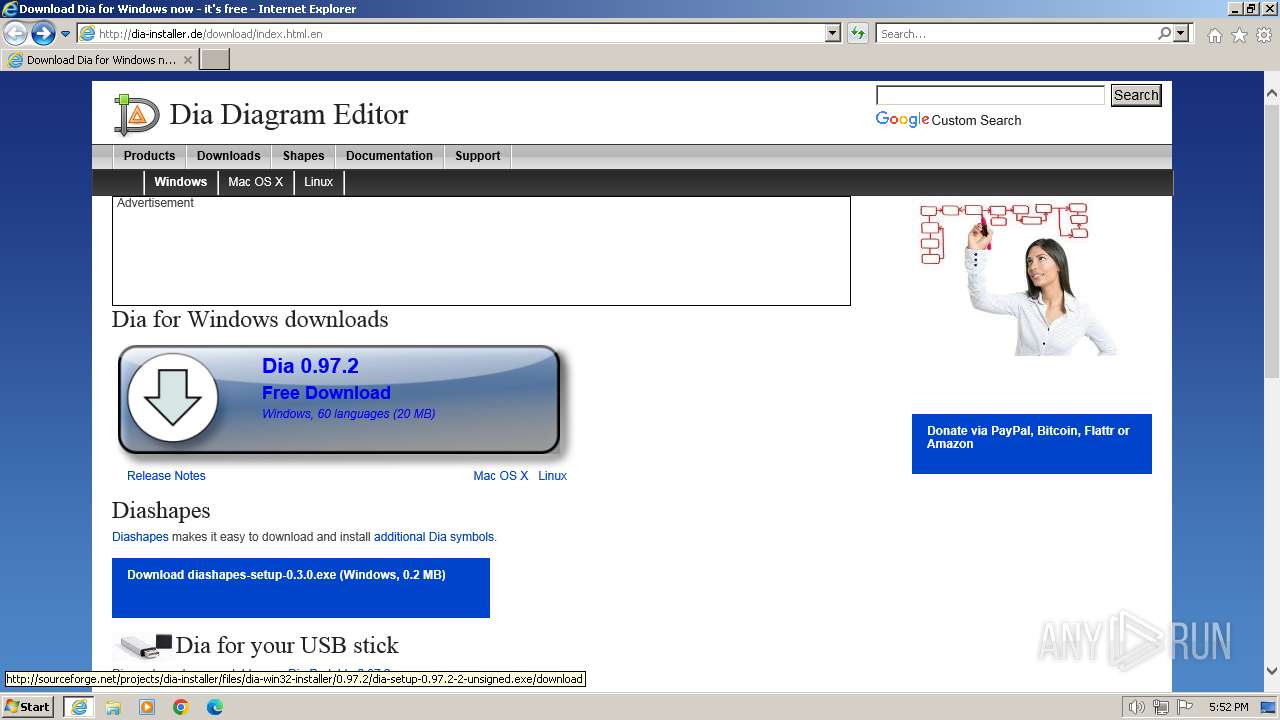
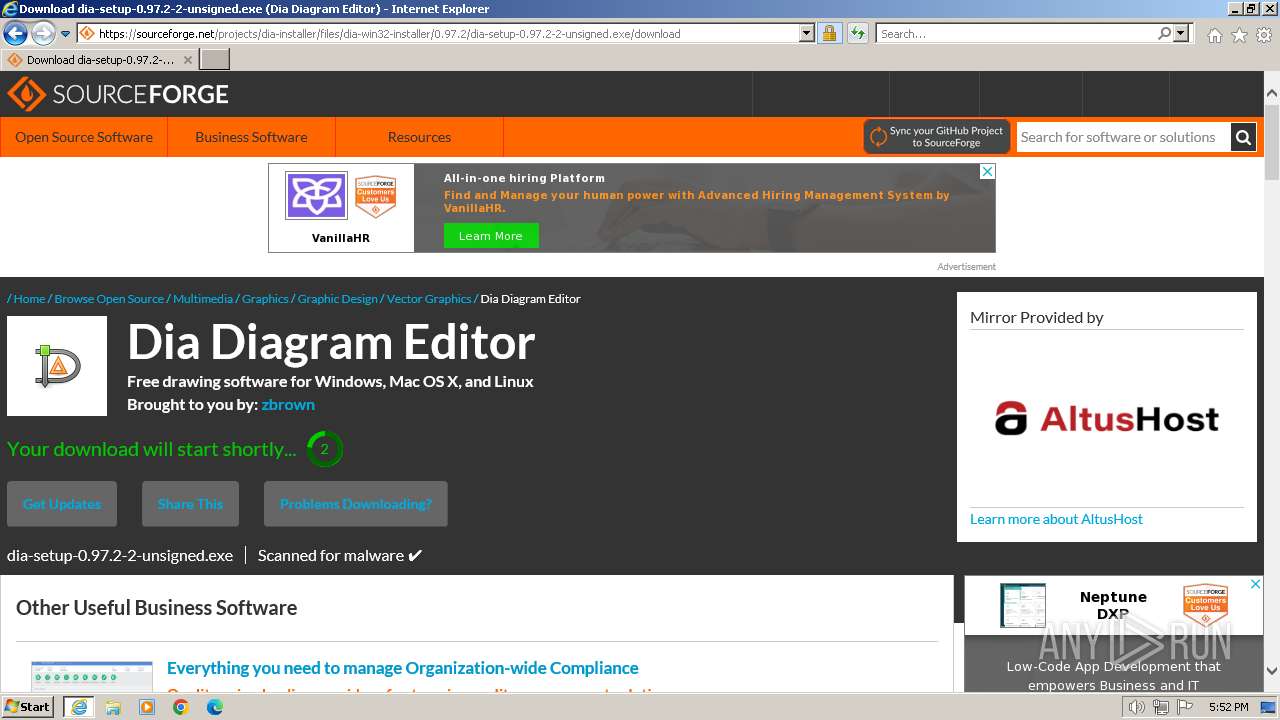
| URL: | http://dia-installer.de/download/index.html.en |
| Full analysis: | https://app.any.run/tasks/b3e679b4-fdf0-4b6d-a0fe-79eedc291938 |
| Verdict: | Malicious activity |
| Analysis date: | February 22, 2024, 17:50:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 47DAAC5FEC4AC7524EB396746BB57A45 |
| SHA1: | 3E7D237D0BE30069C7AFD112A781E4252855348C |
| SHA256: | D2DBFCBC49570C550B620ADEEED0F7CA74DE2CF1D350C4B854197C91CC713C35 |
| SSDEEP: | 3:N1KaMExiigXL2KB4KIcu:CaFETXL2KBWN |
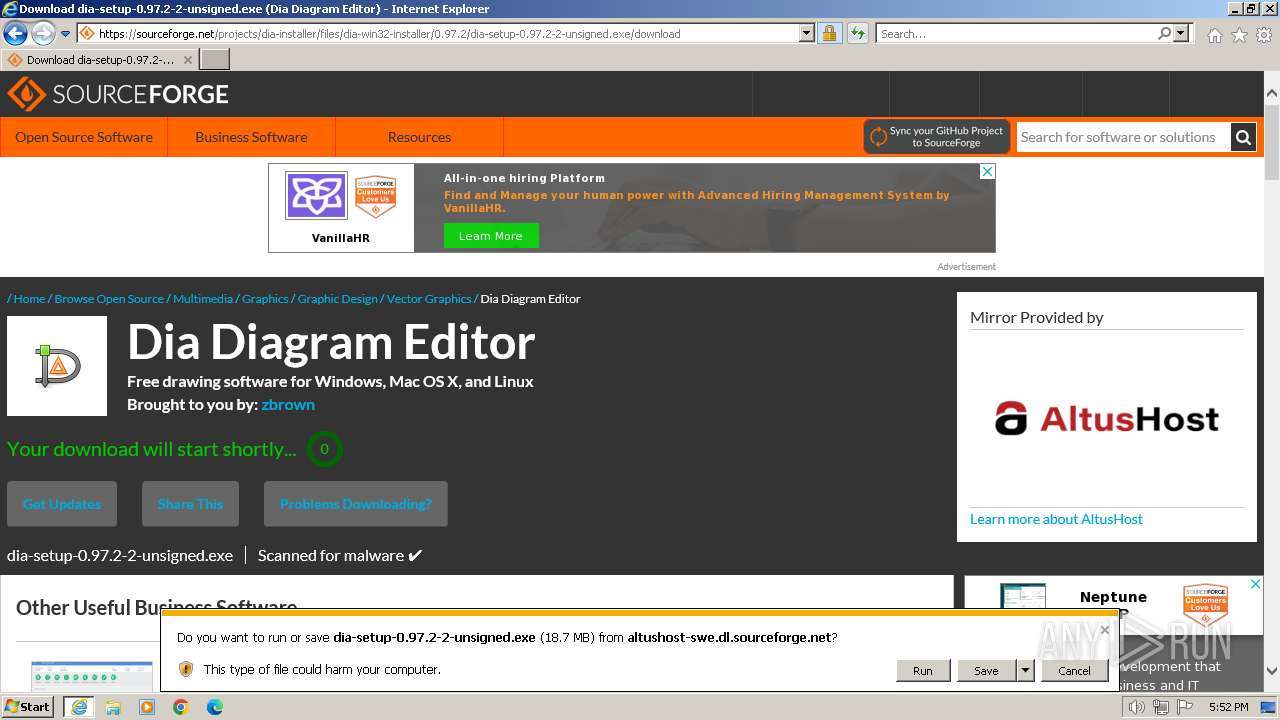
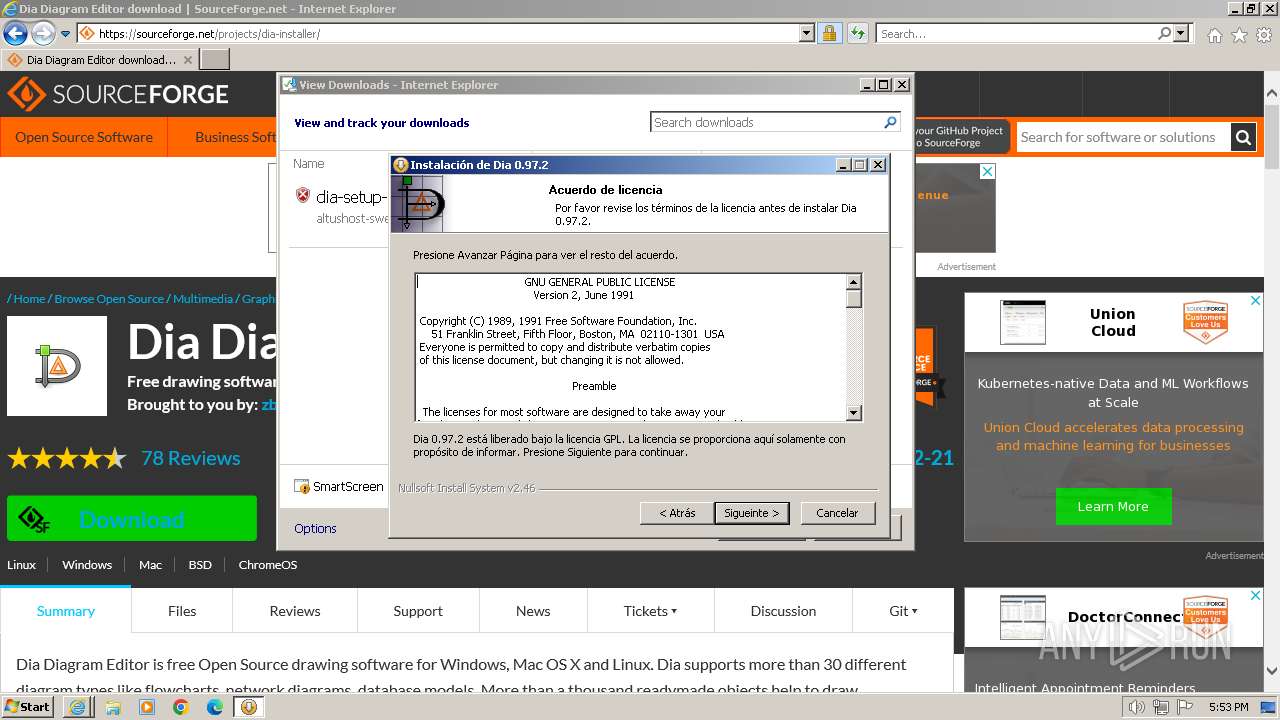
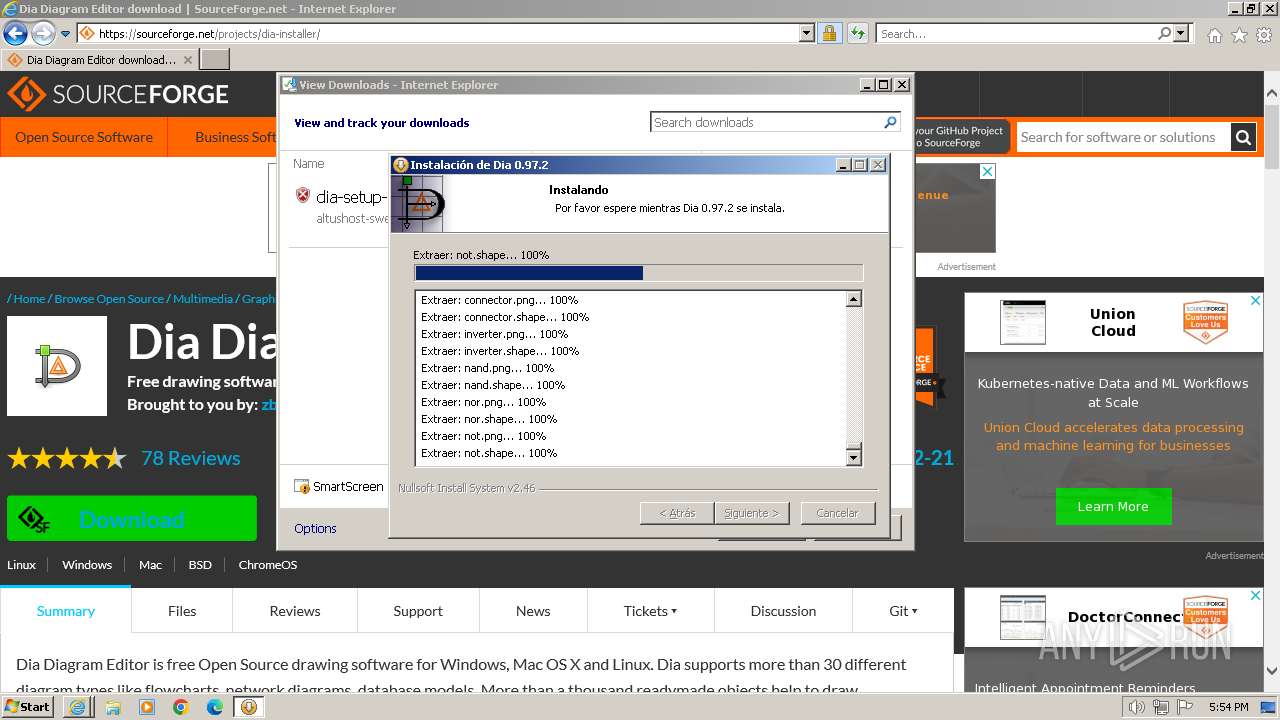
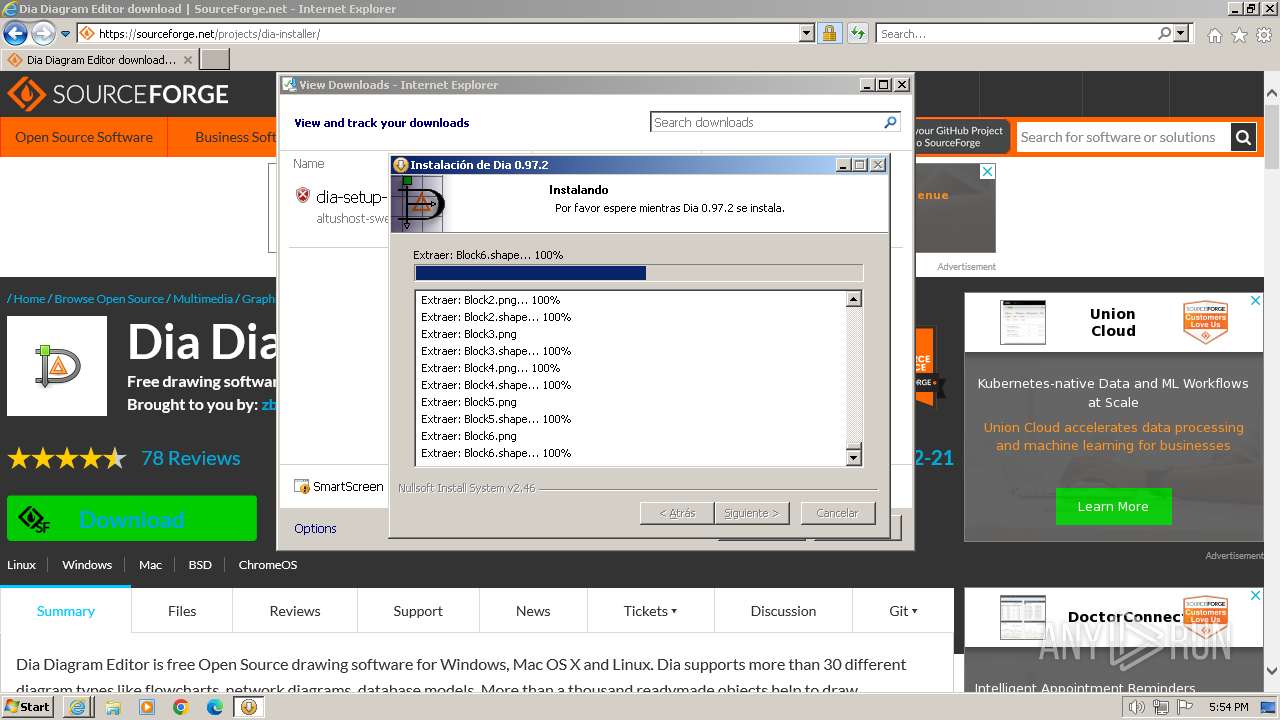
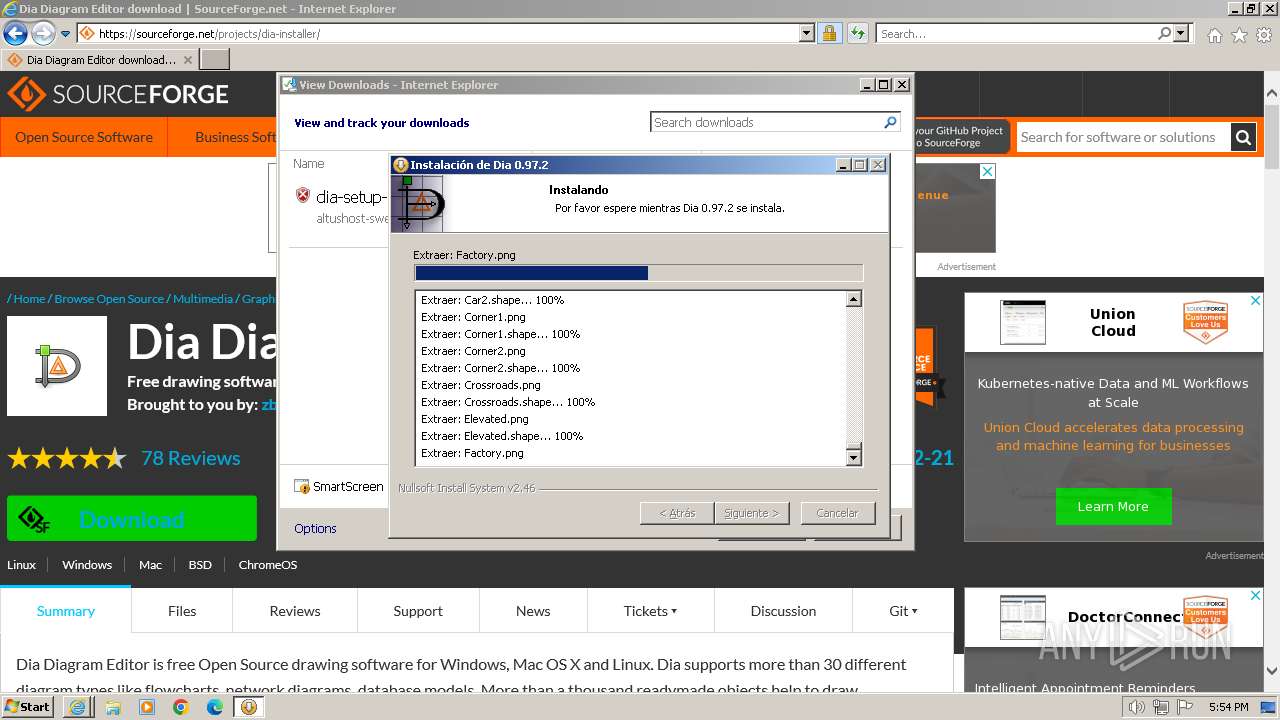
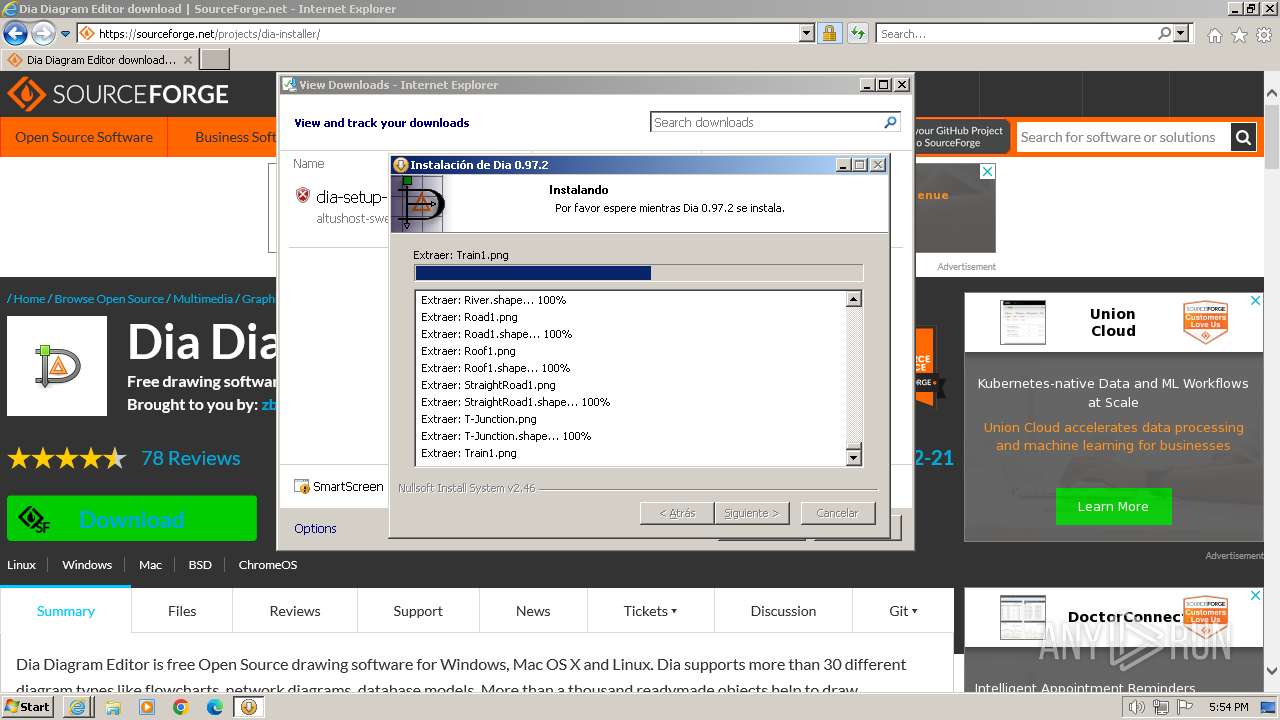
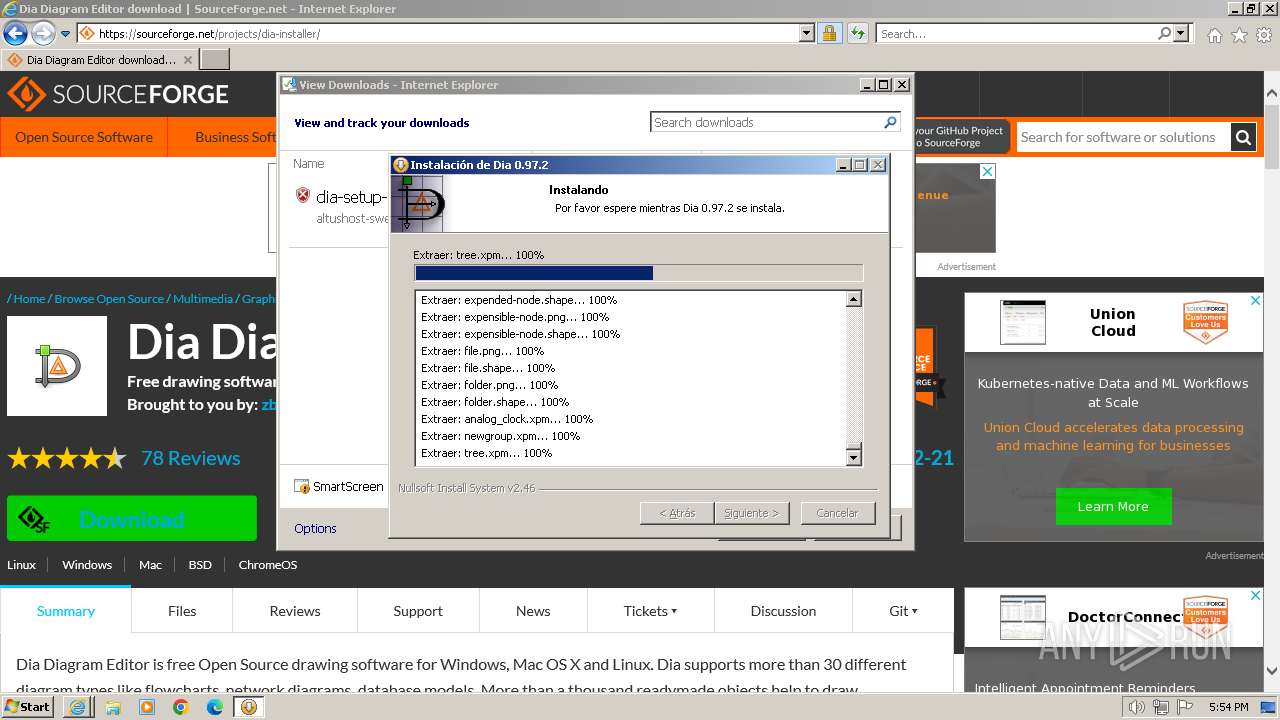
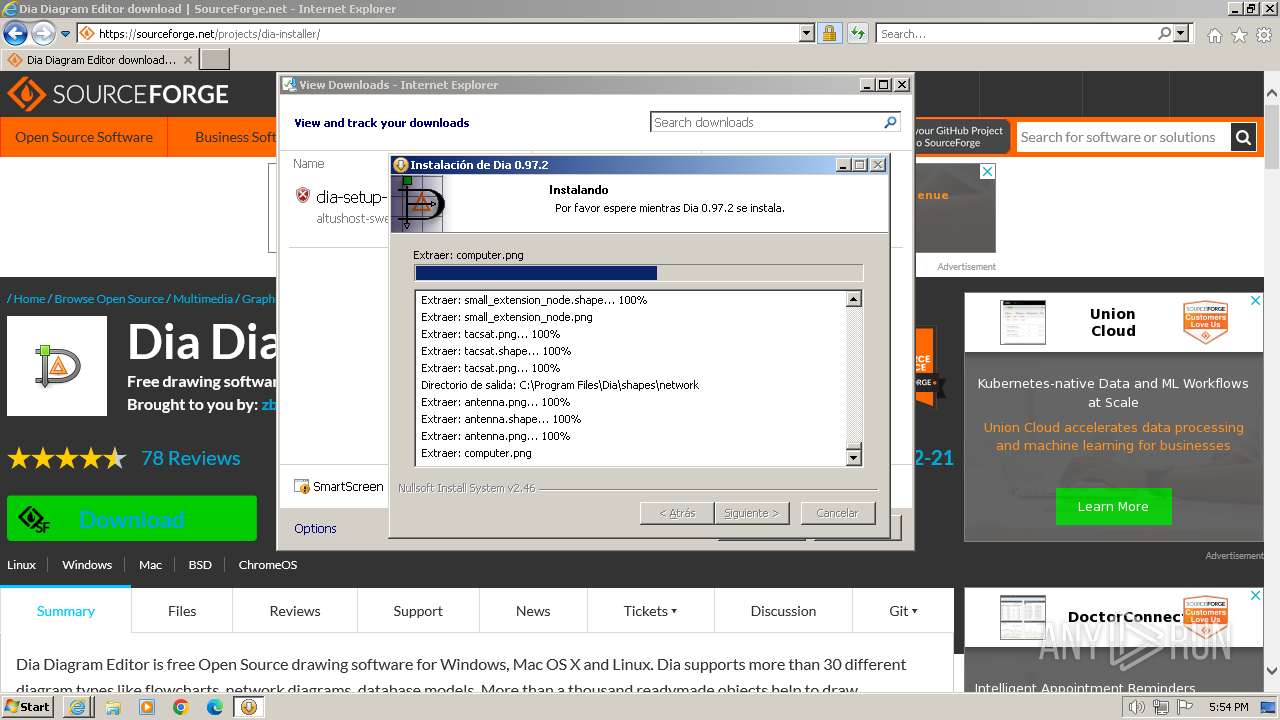
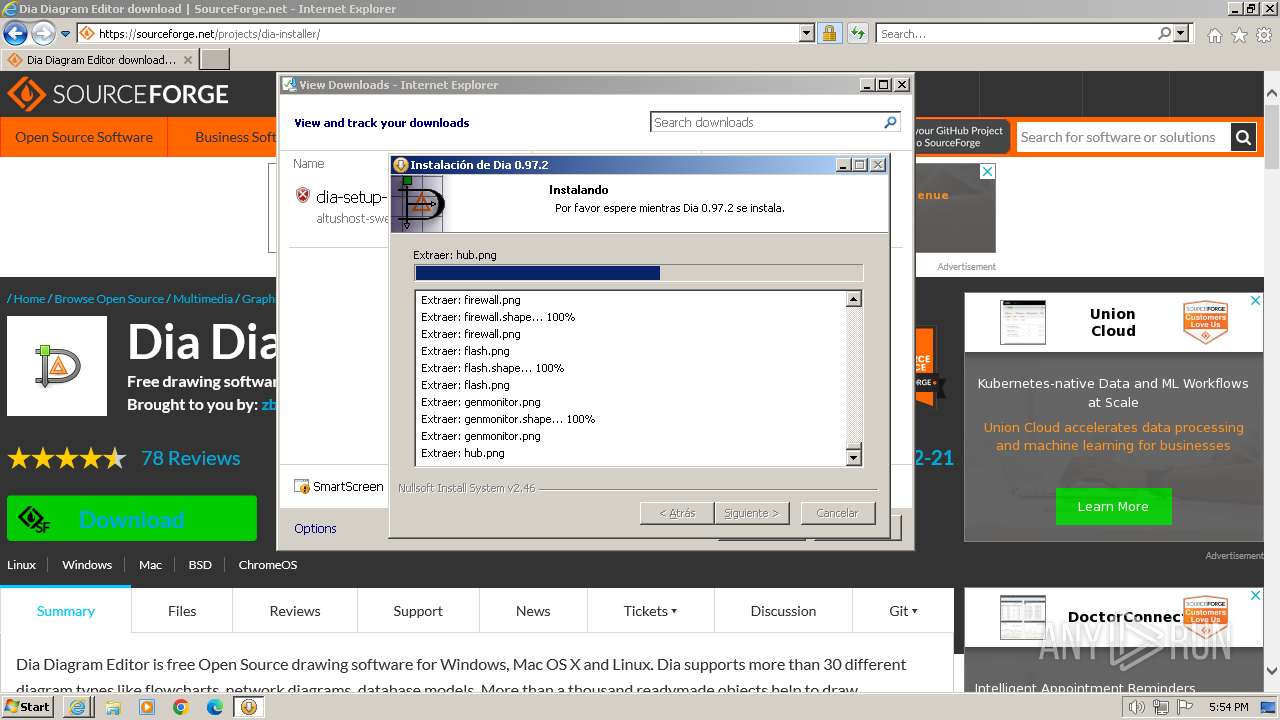
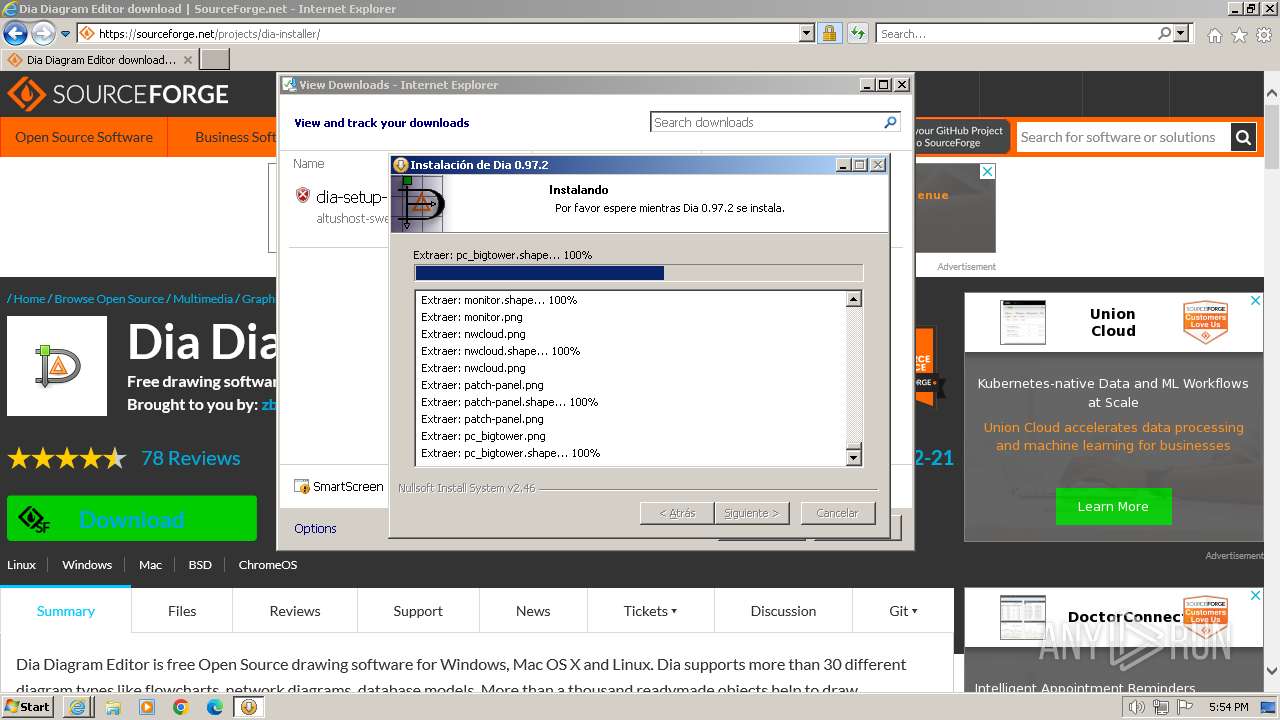
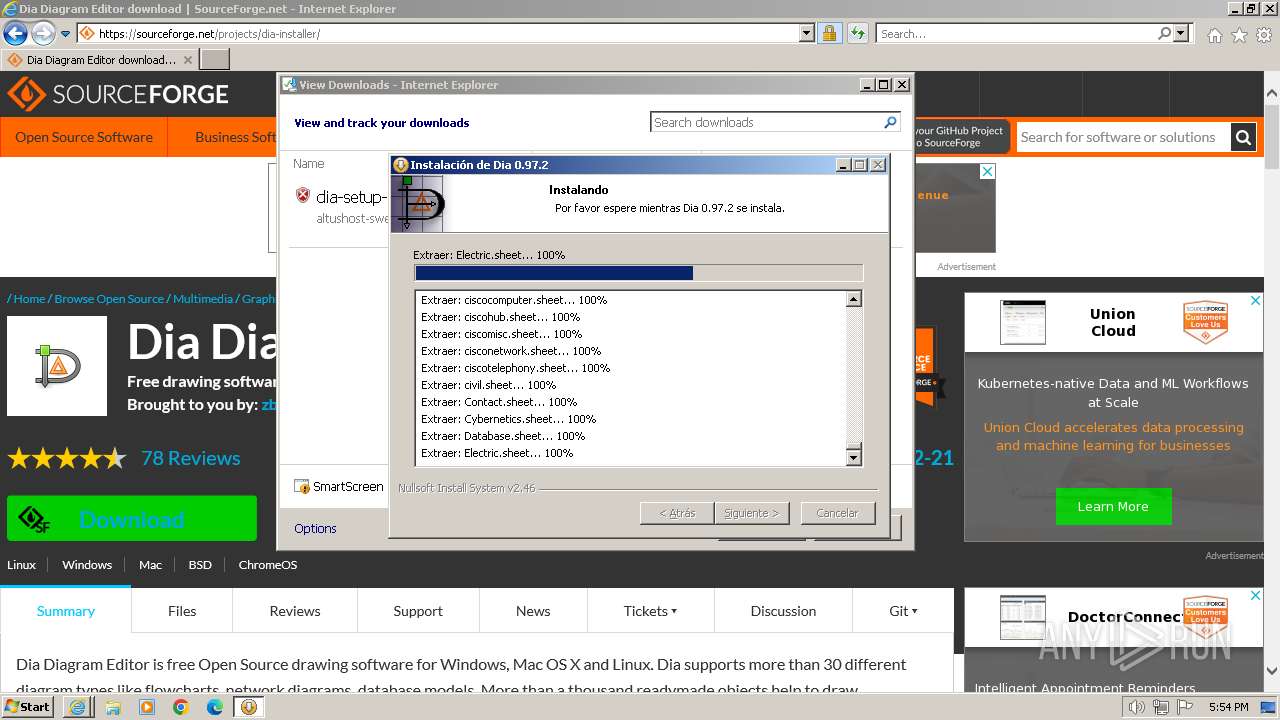
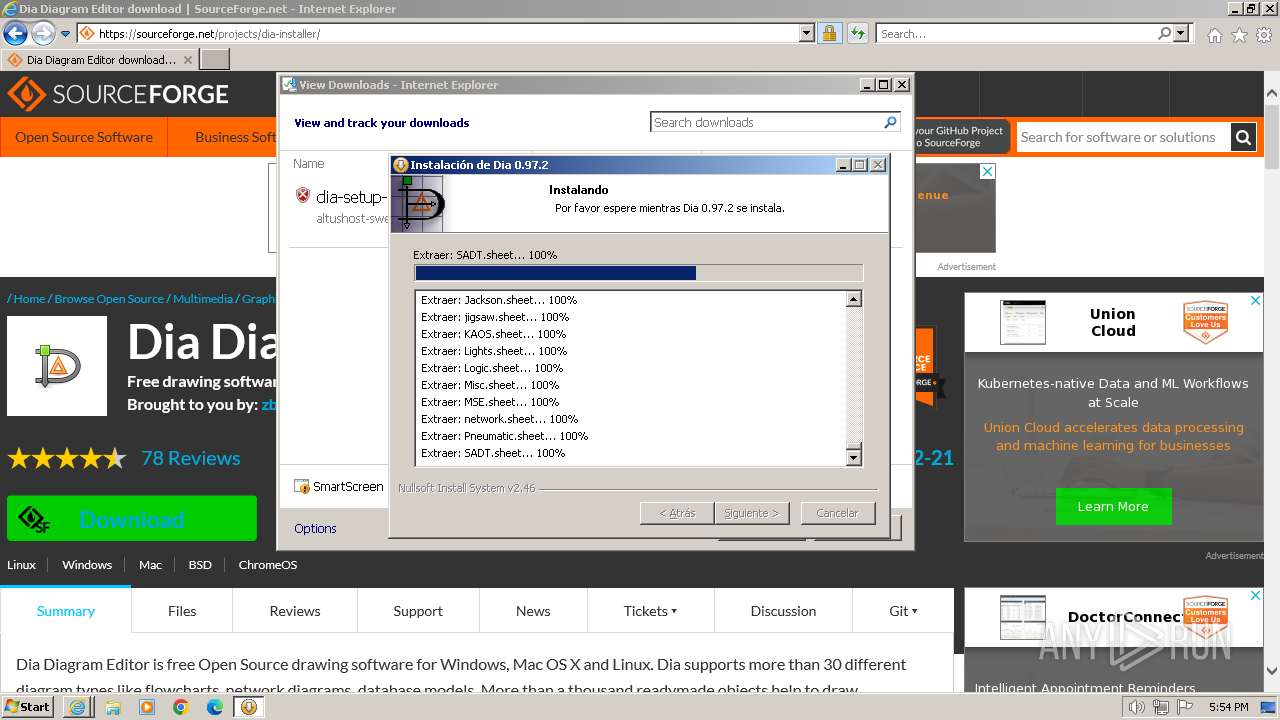
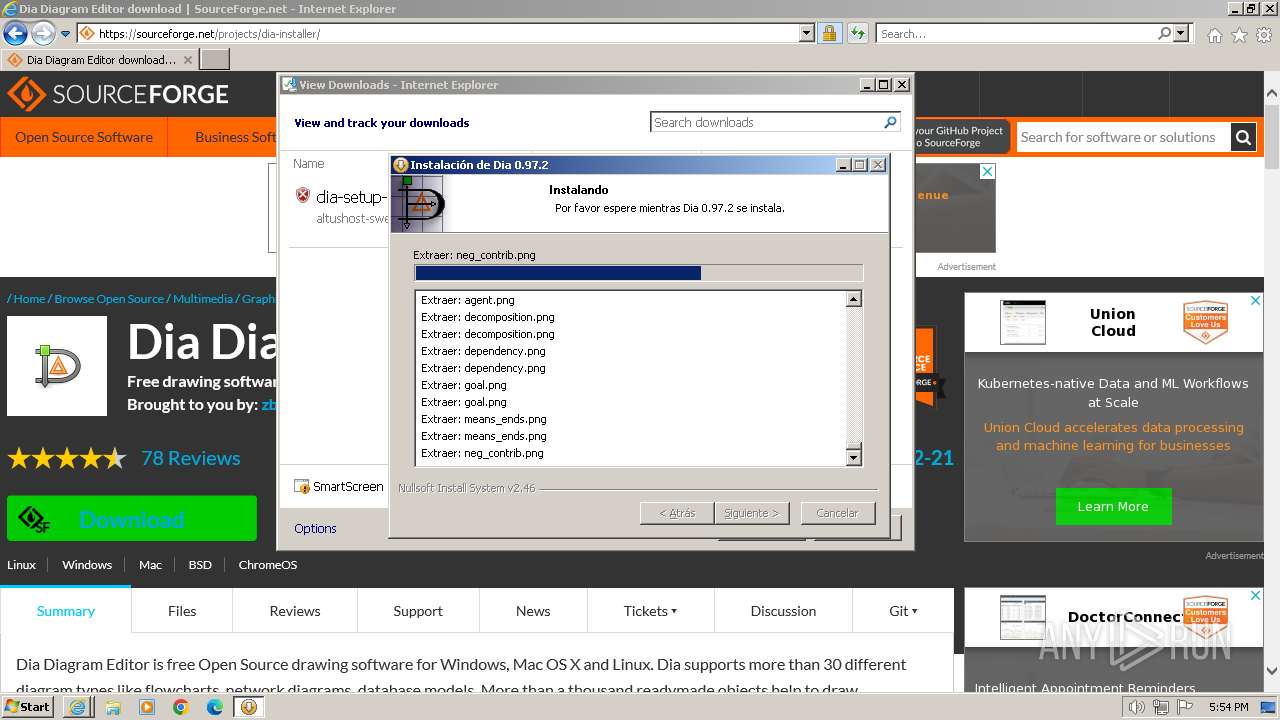
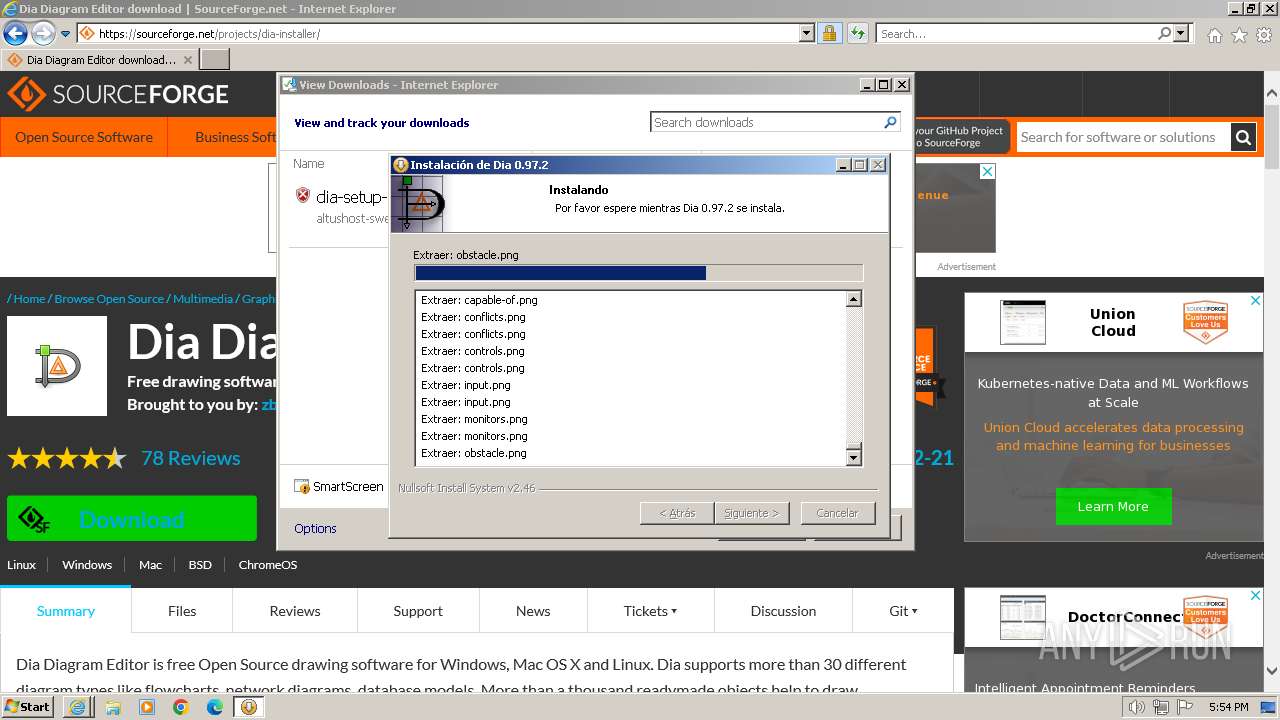
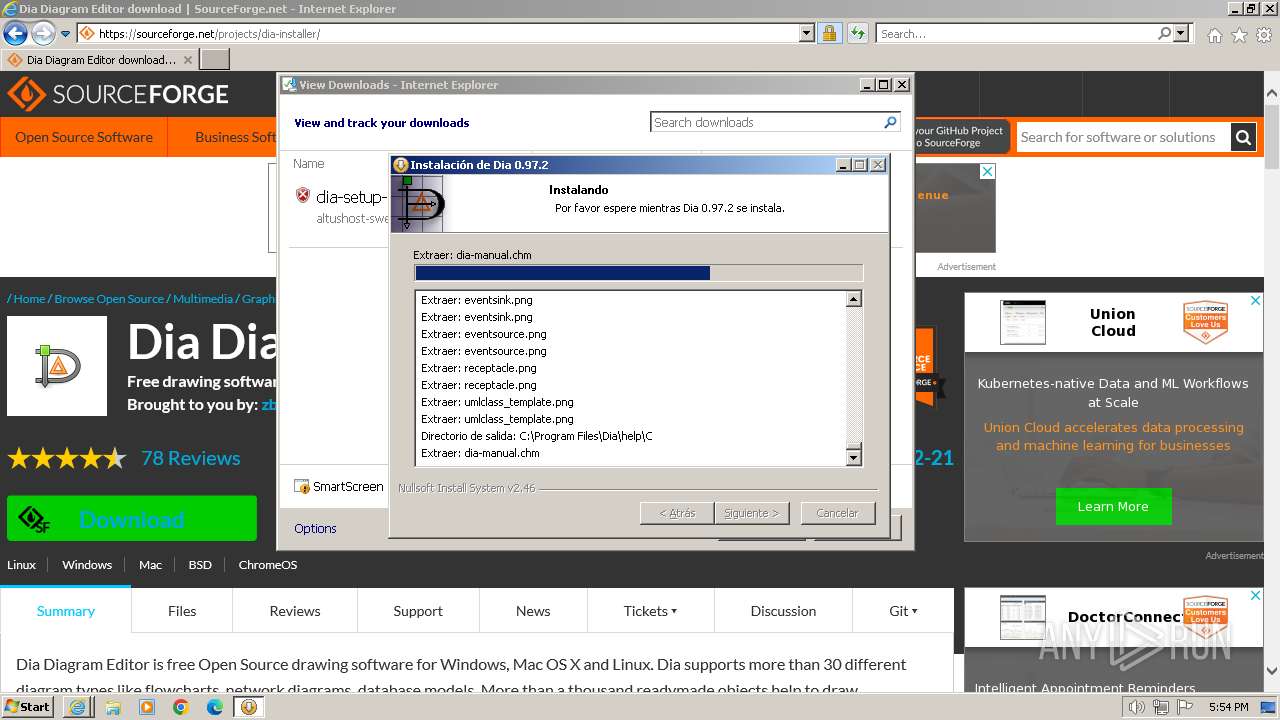
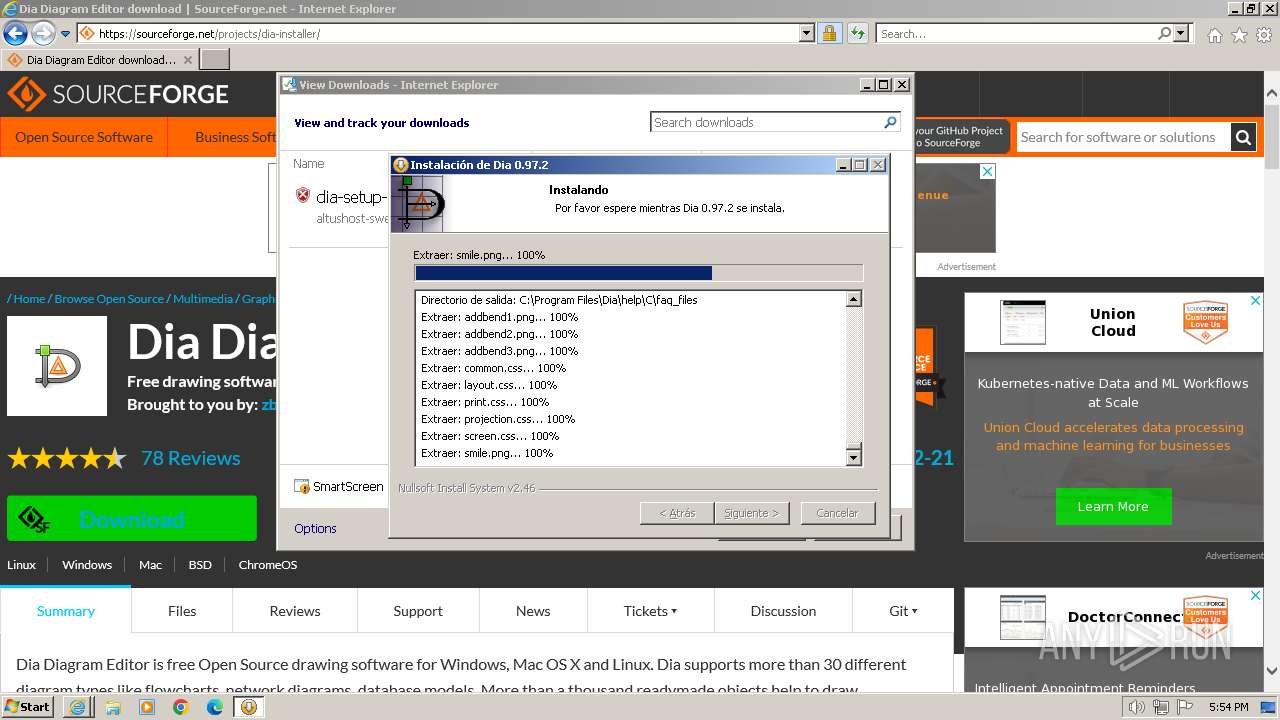
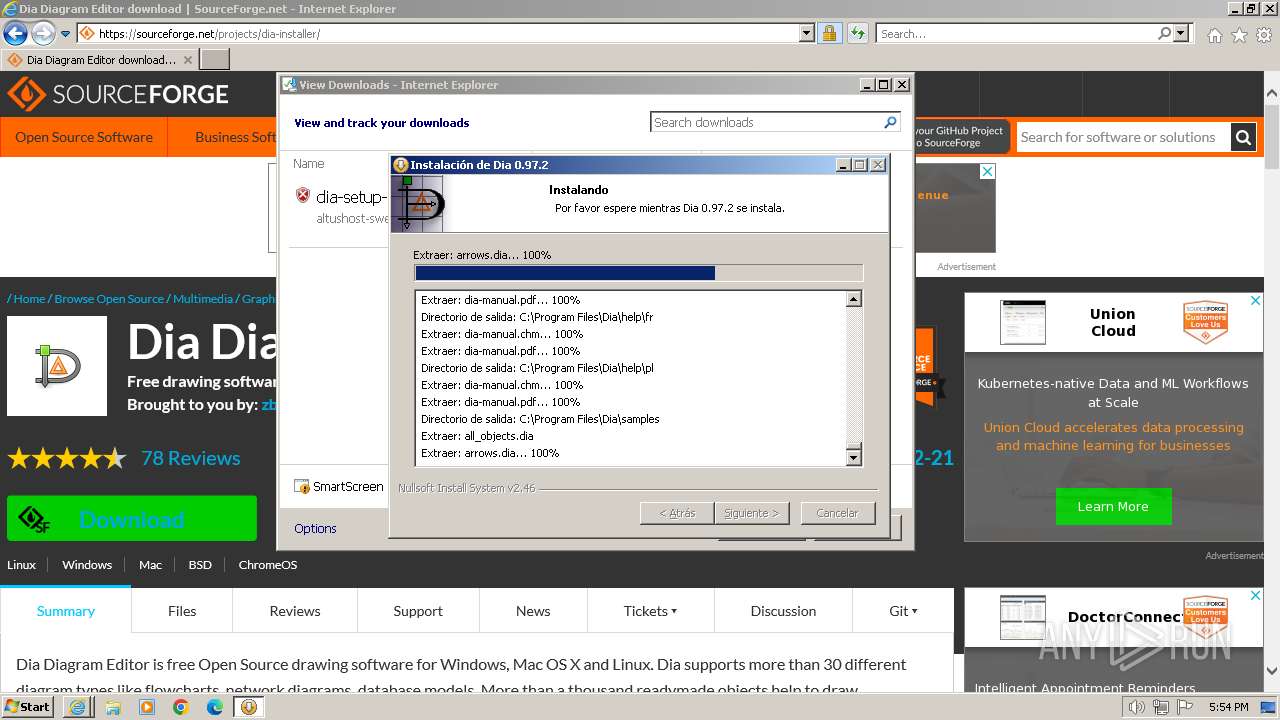
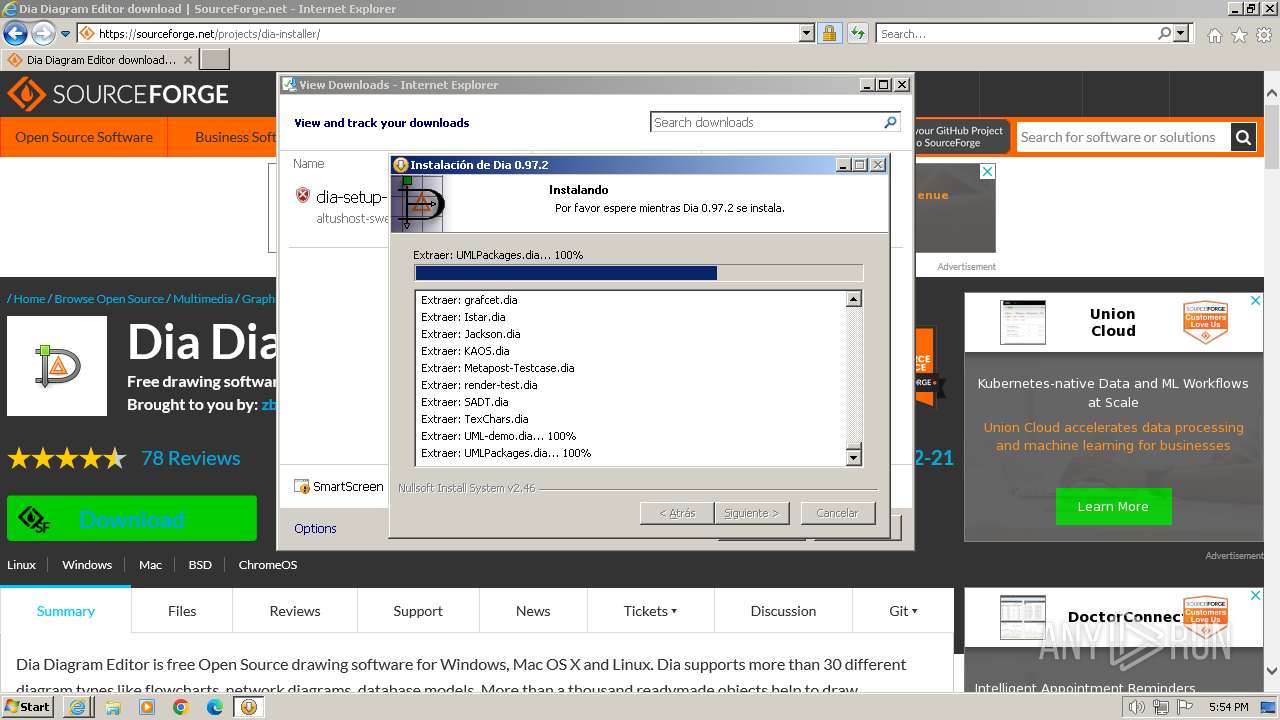
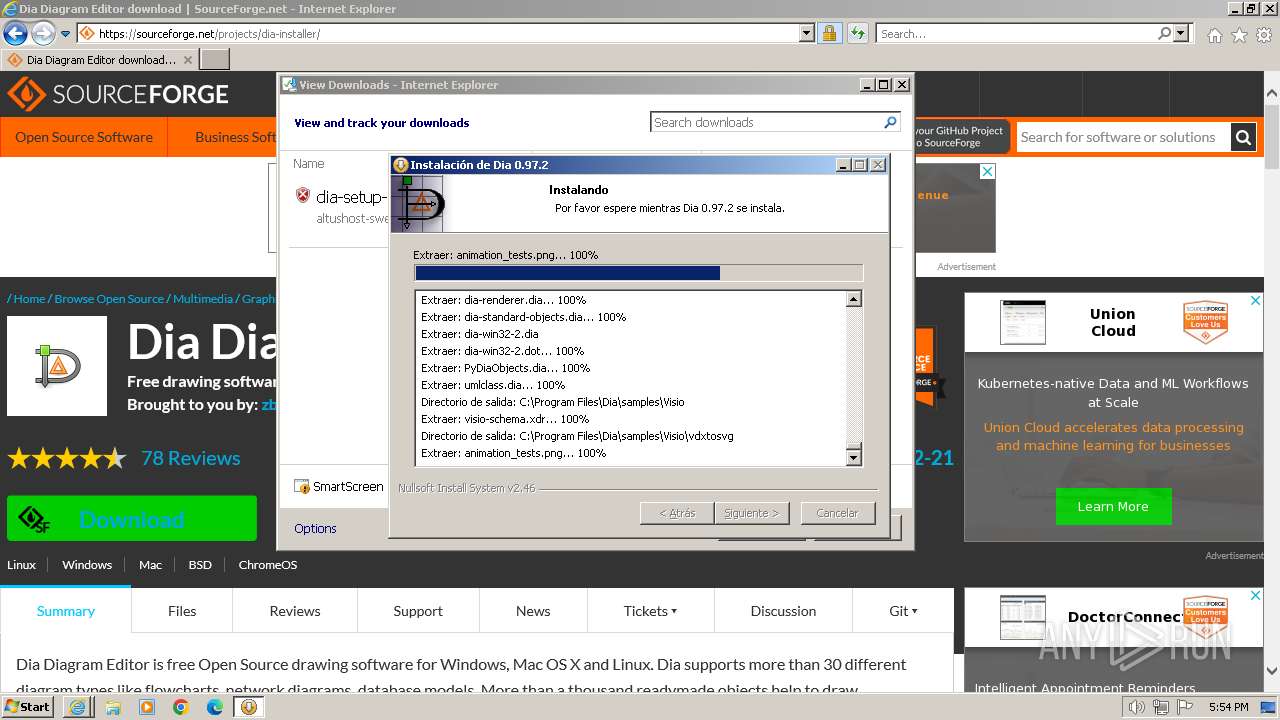
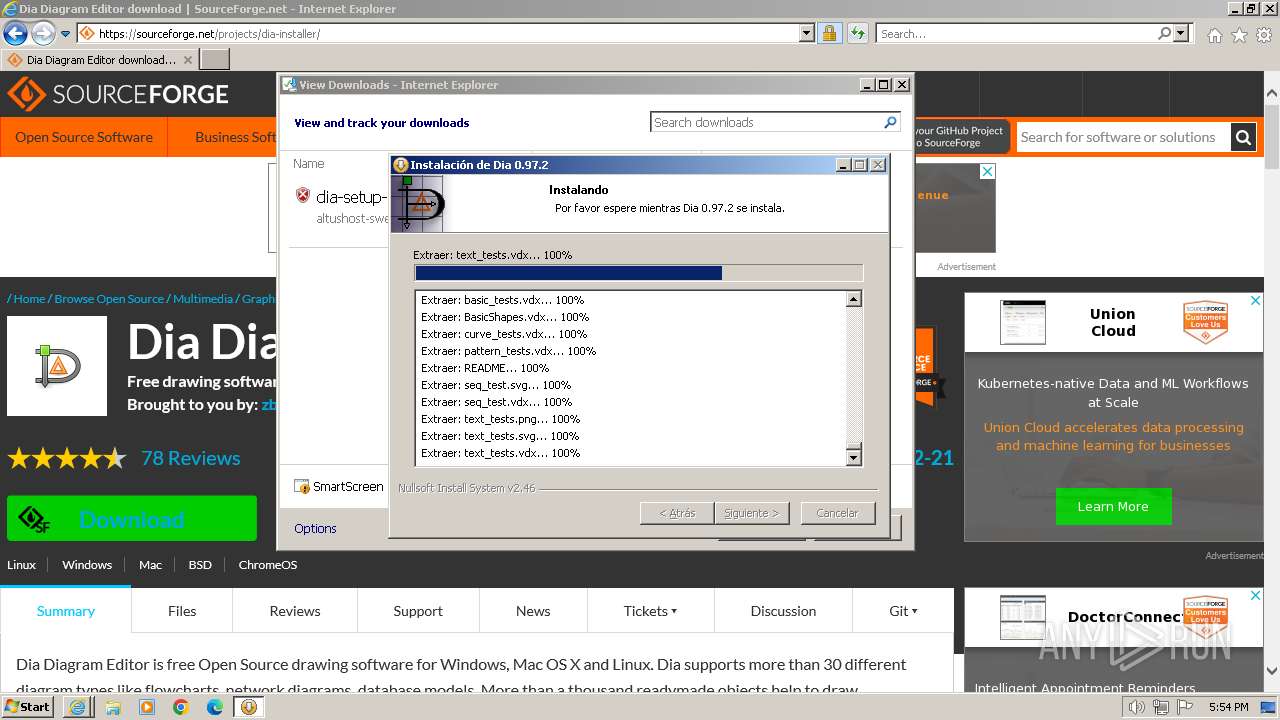
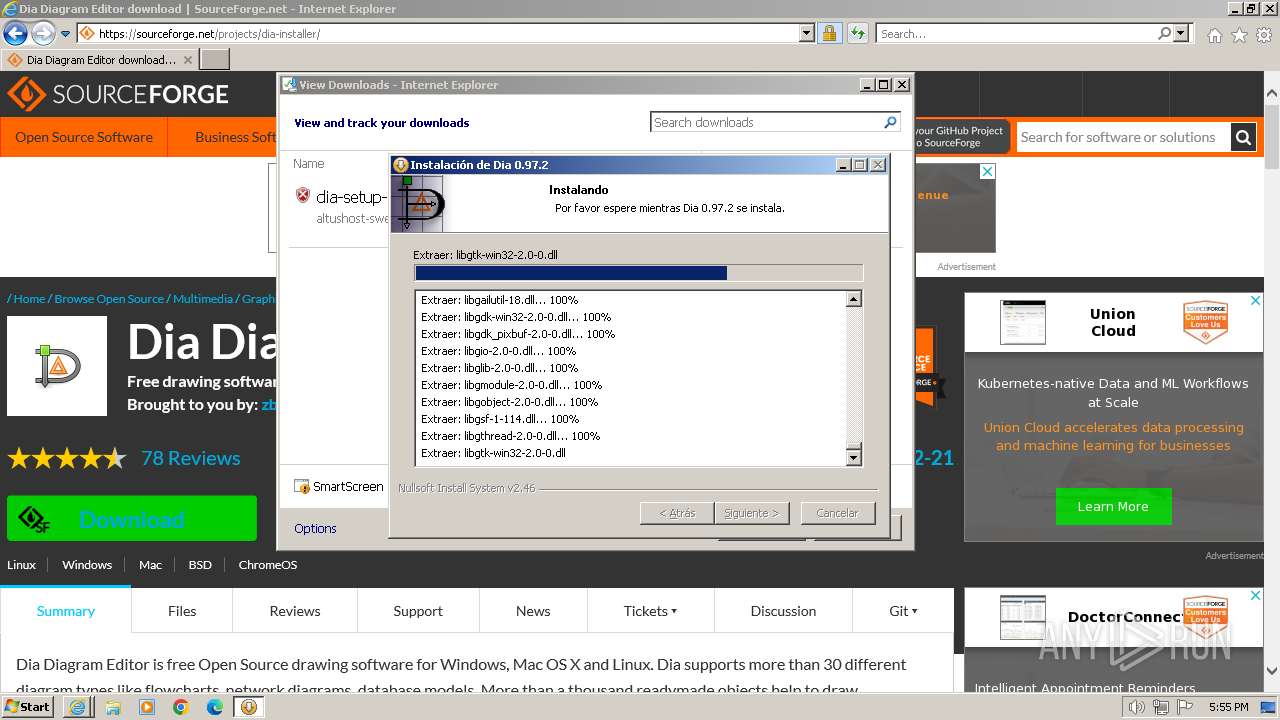
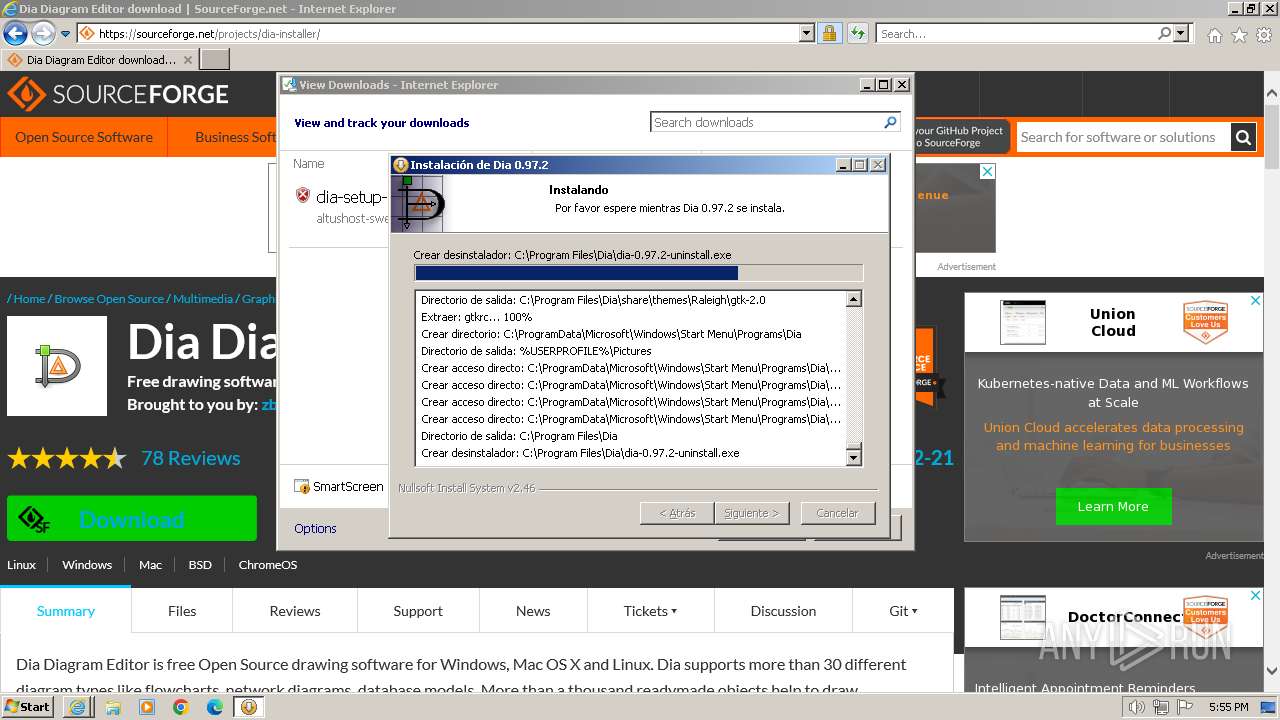
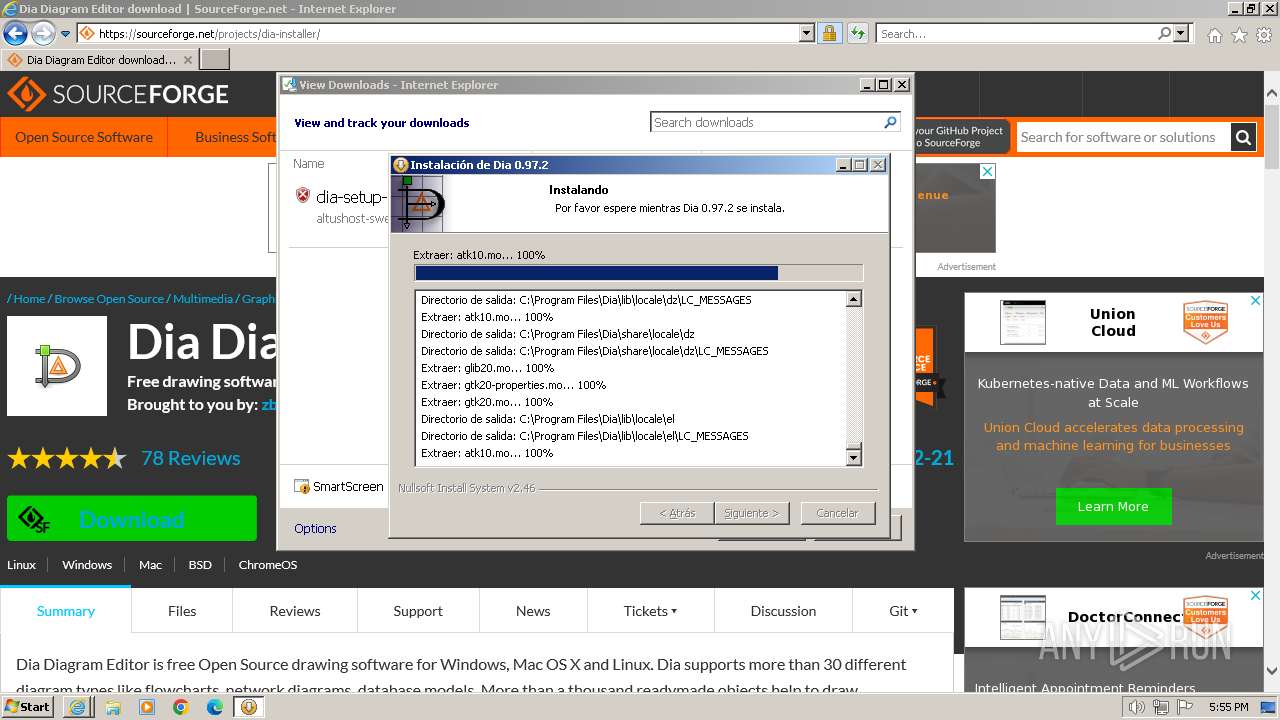
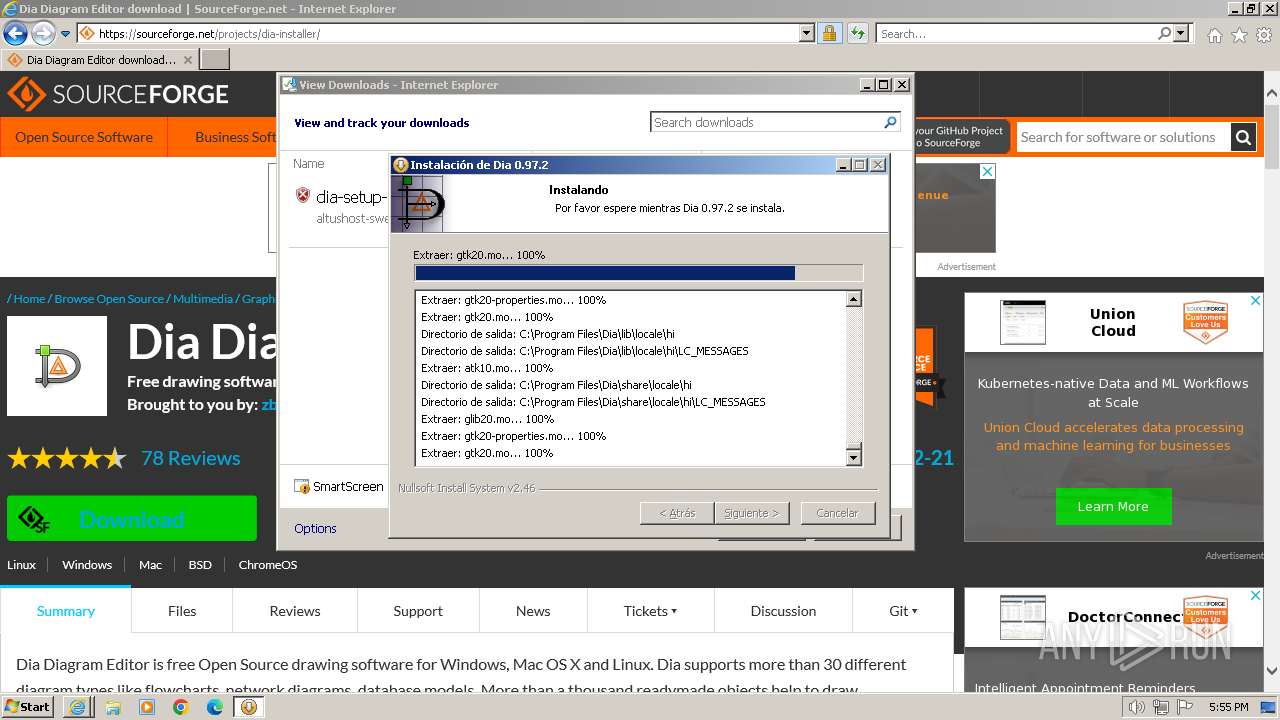
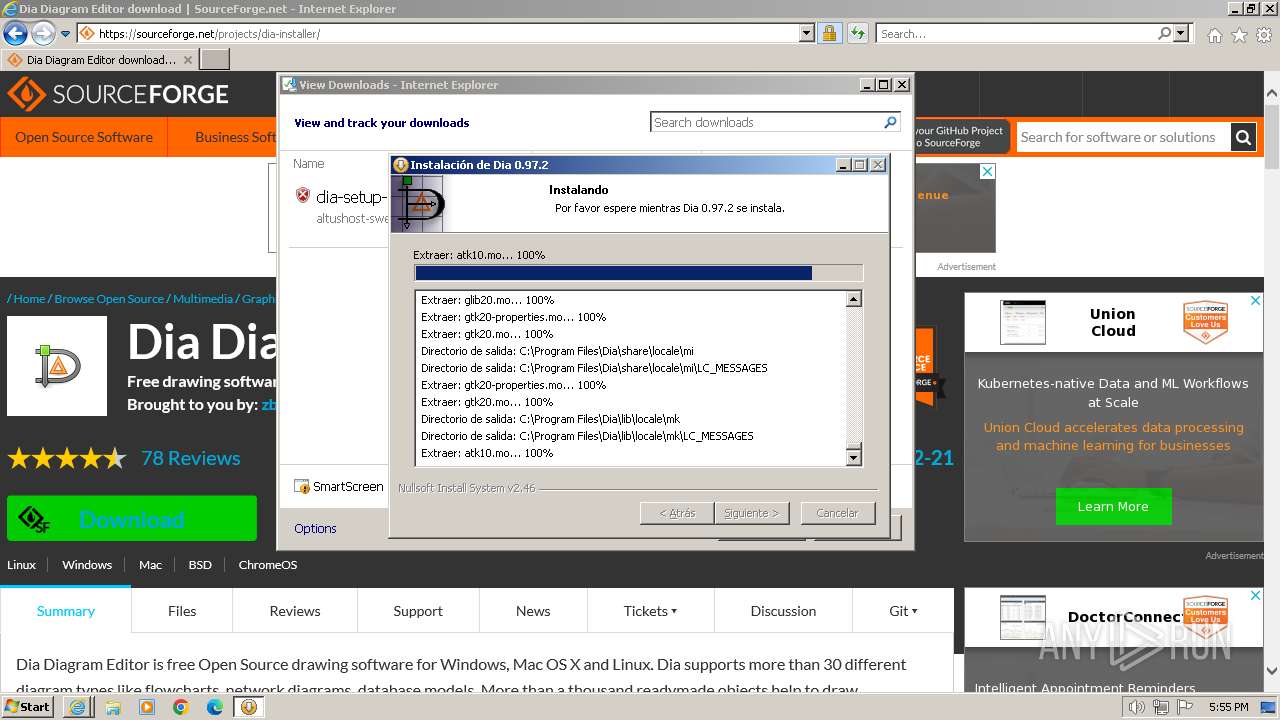
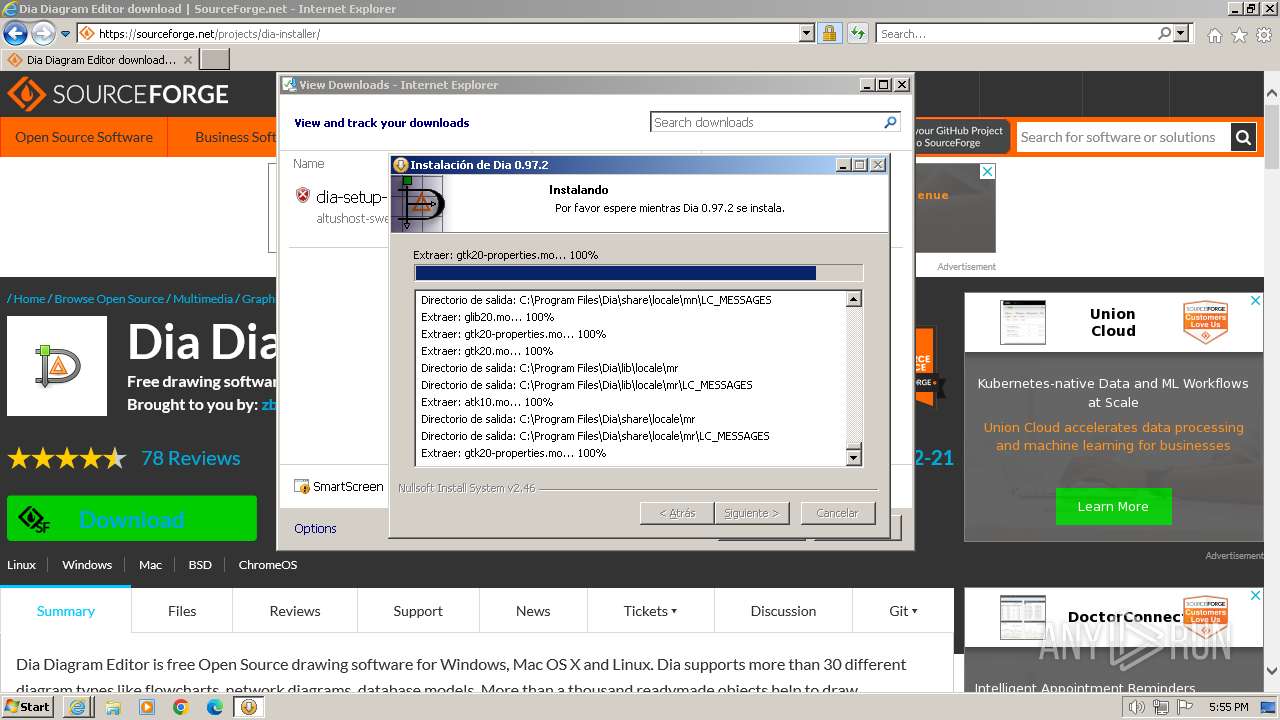
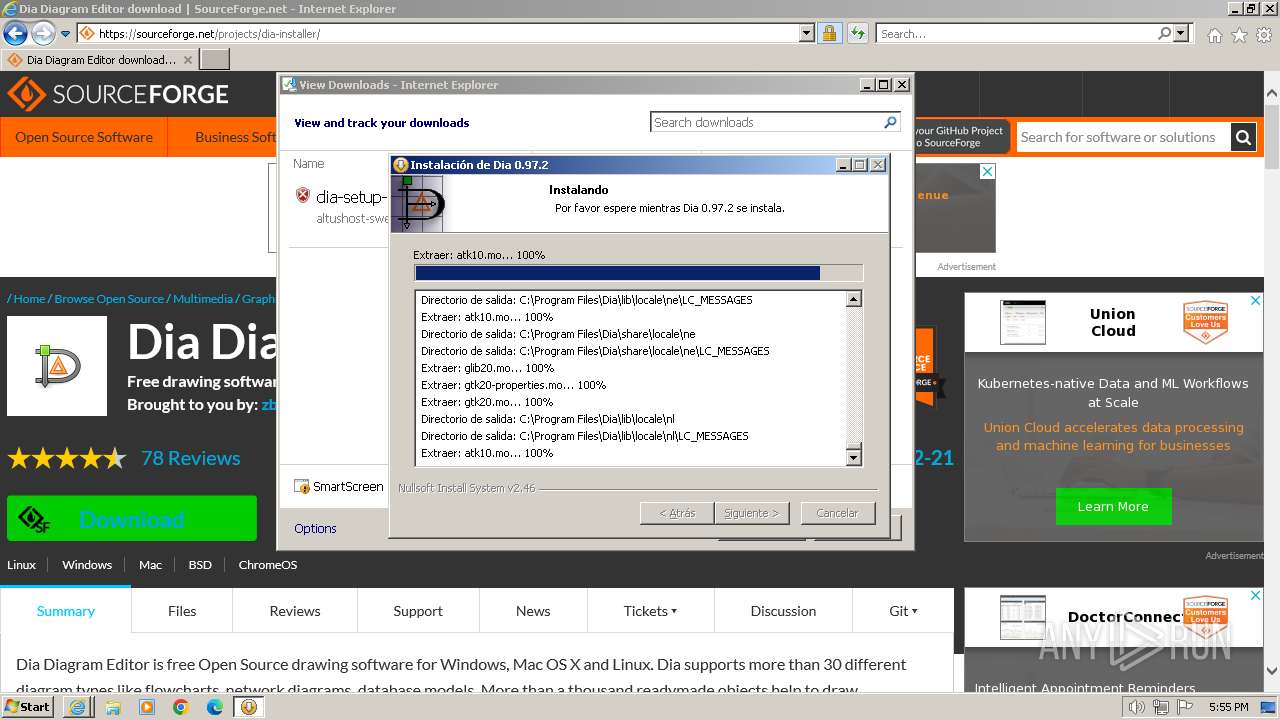
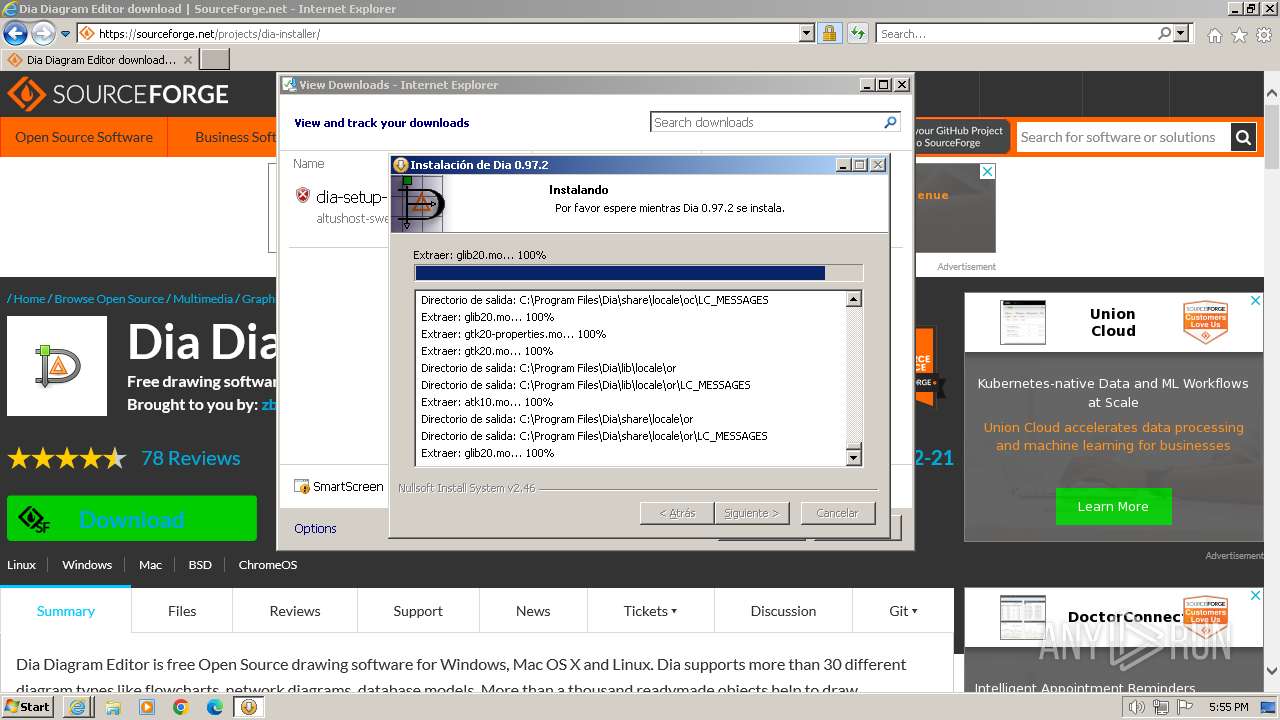
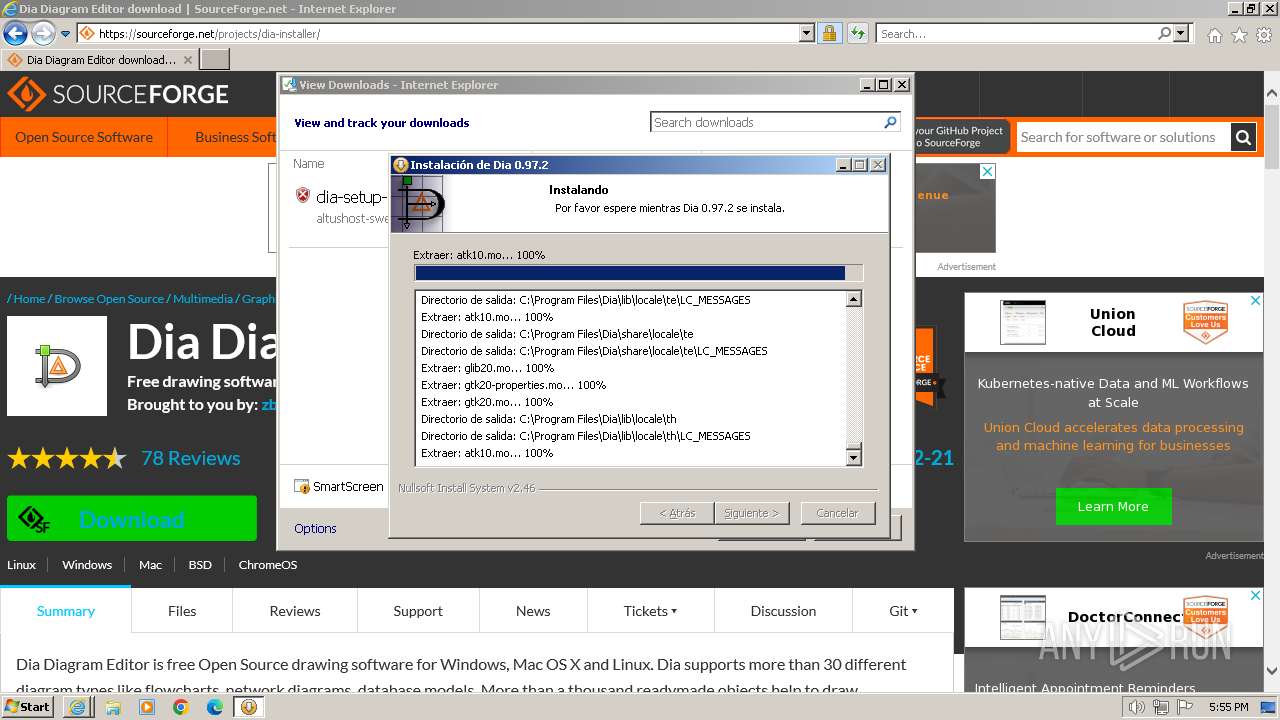
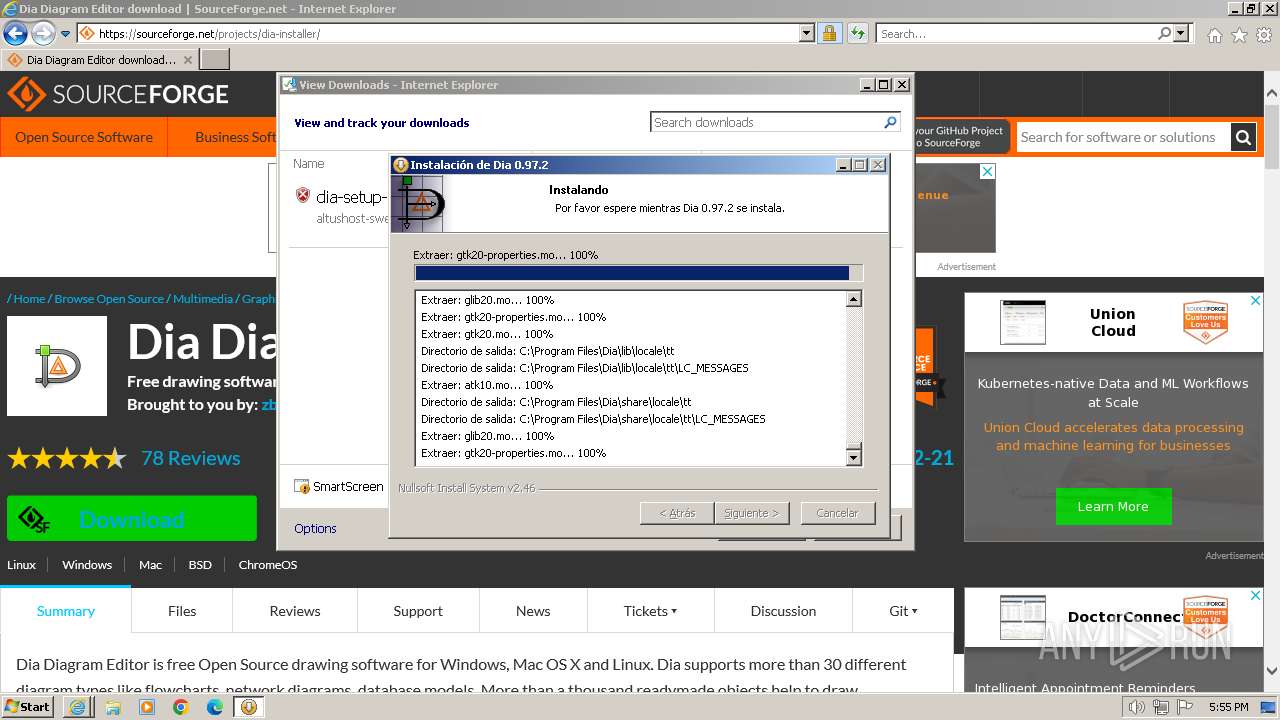
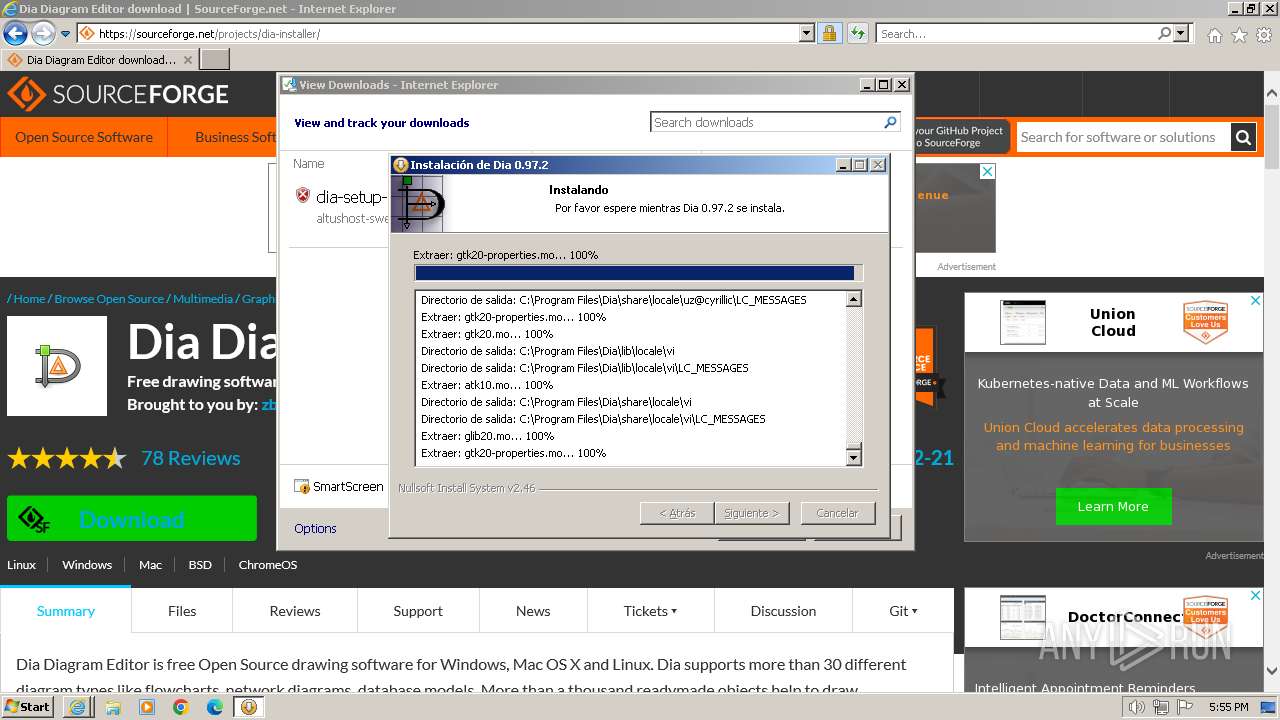
MALICIOUS
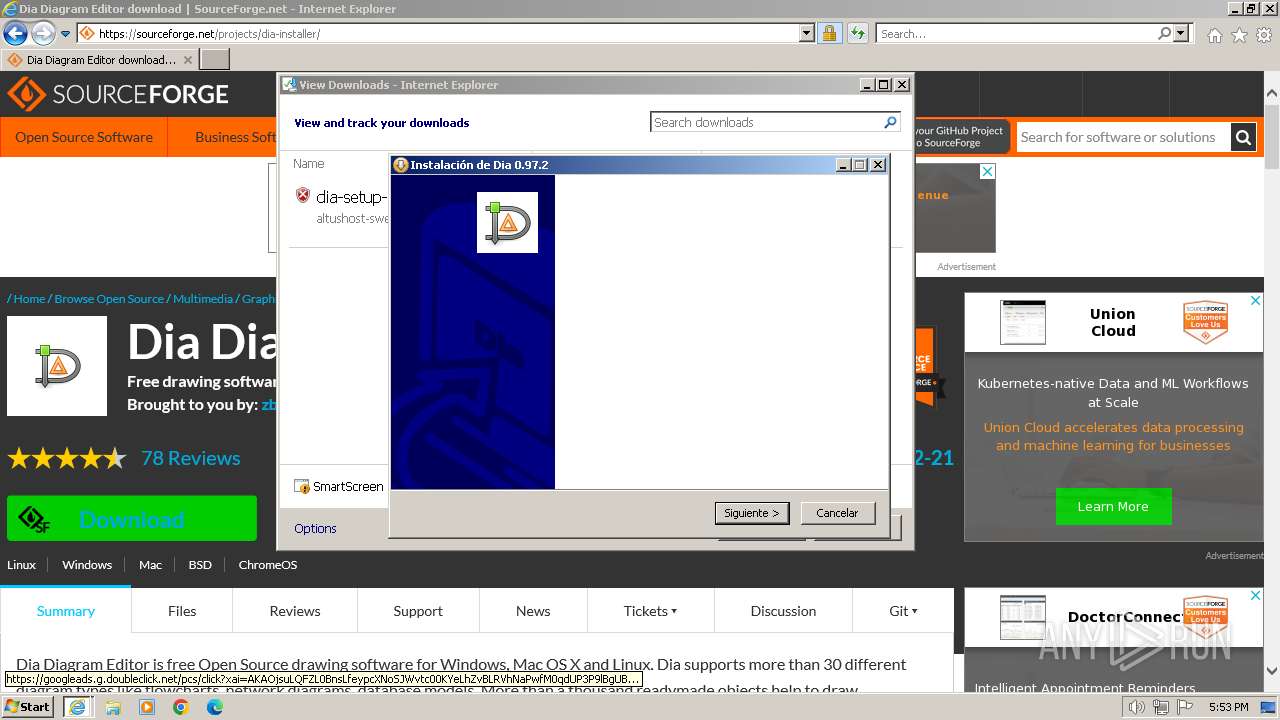
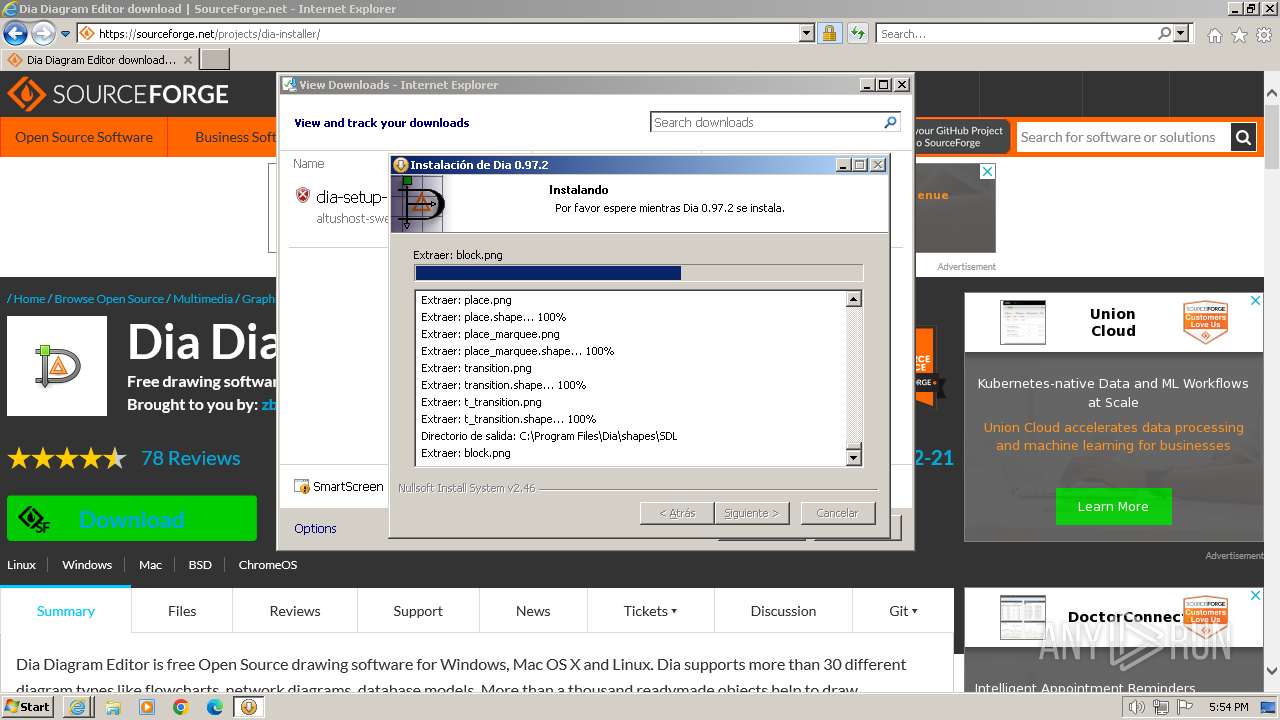
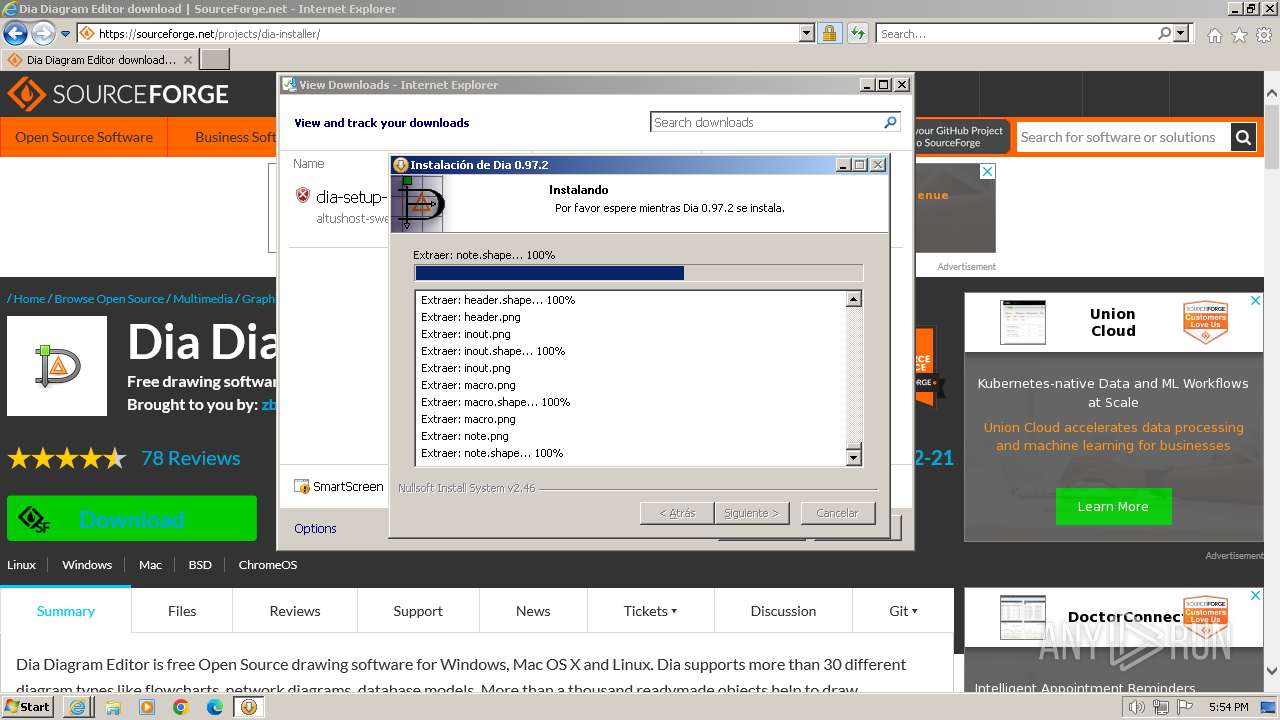
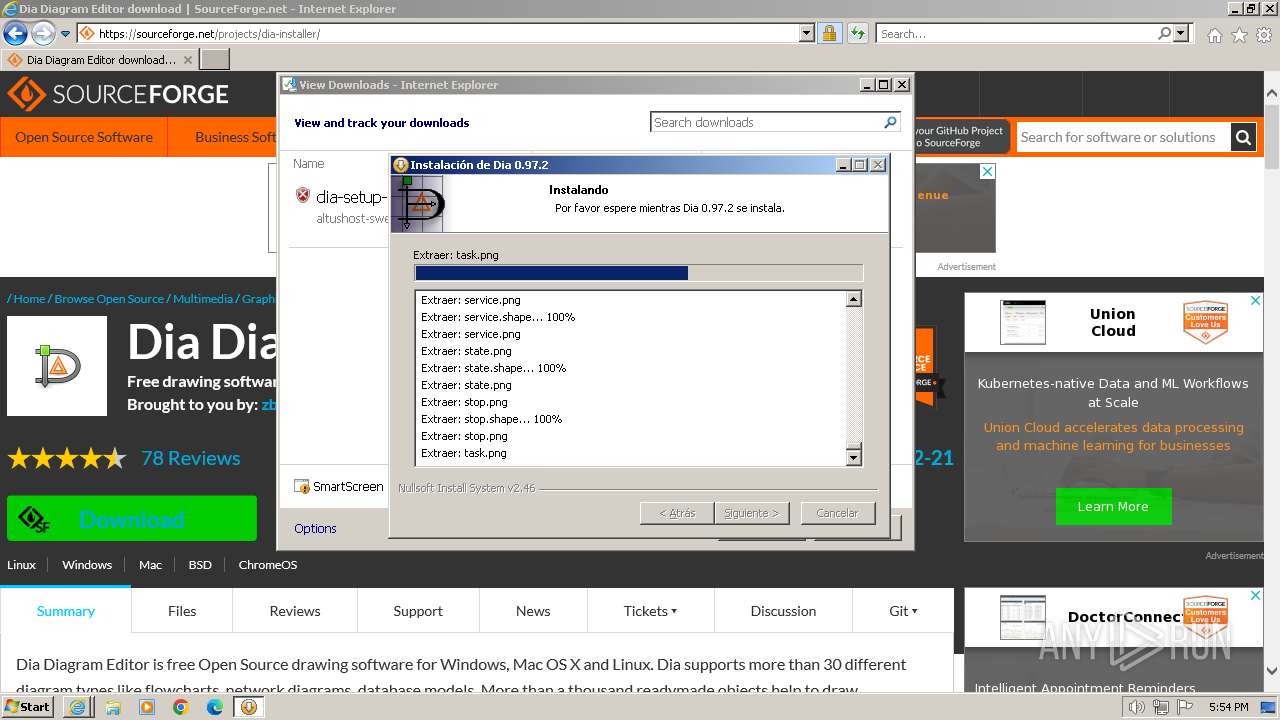
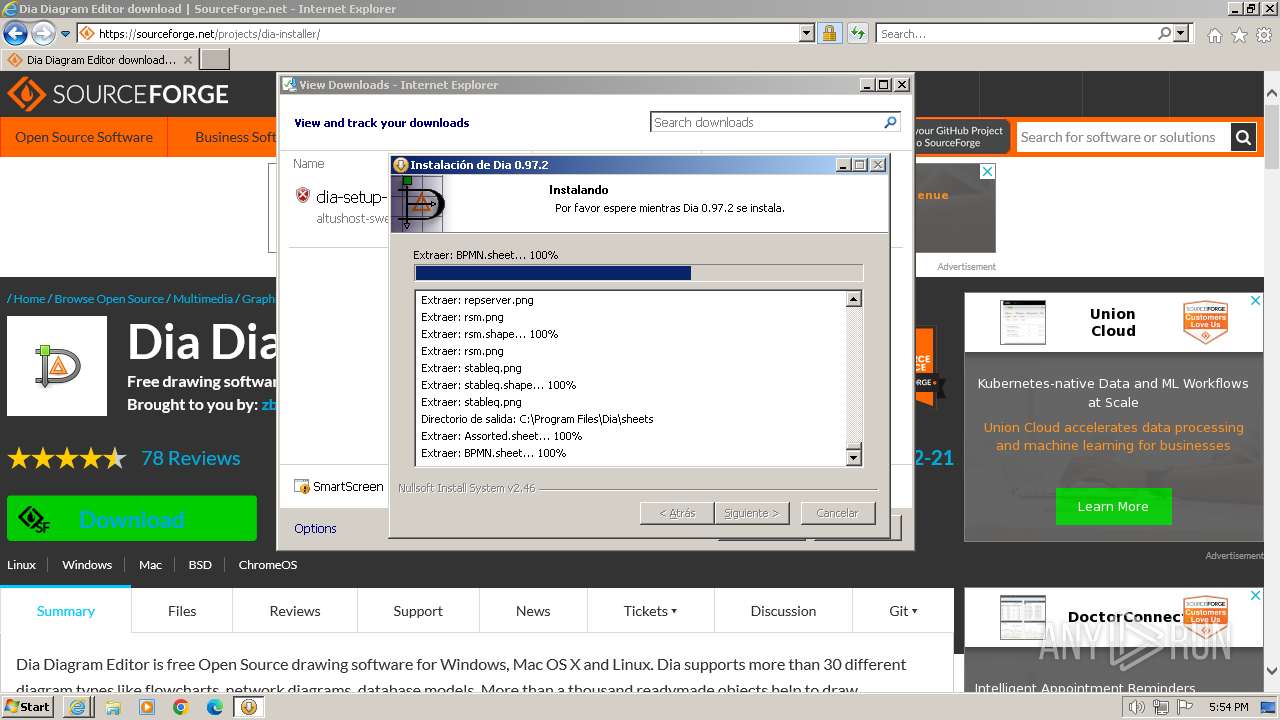
Drops the executable file immediately after the start
- dia-setup-0.97.2-2-unsigned.exe (PID: 2172)
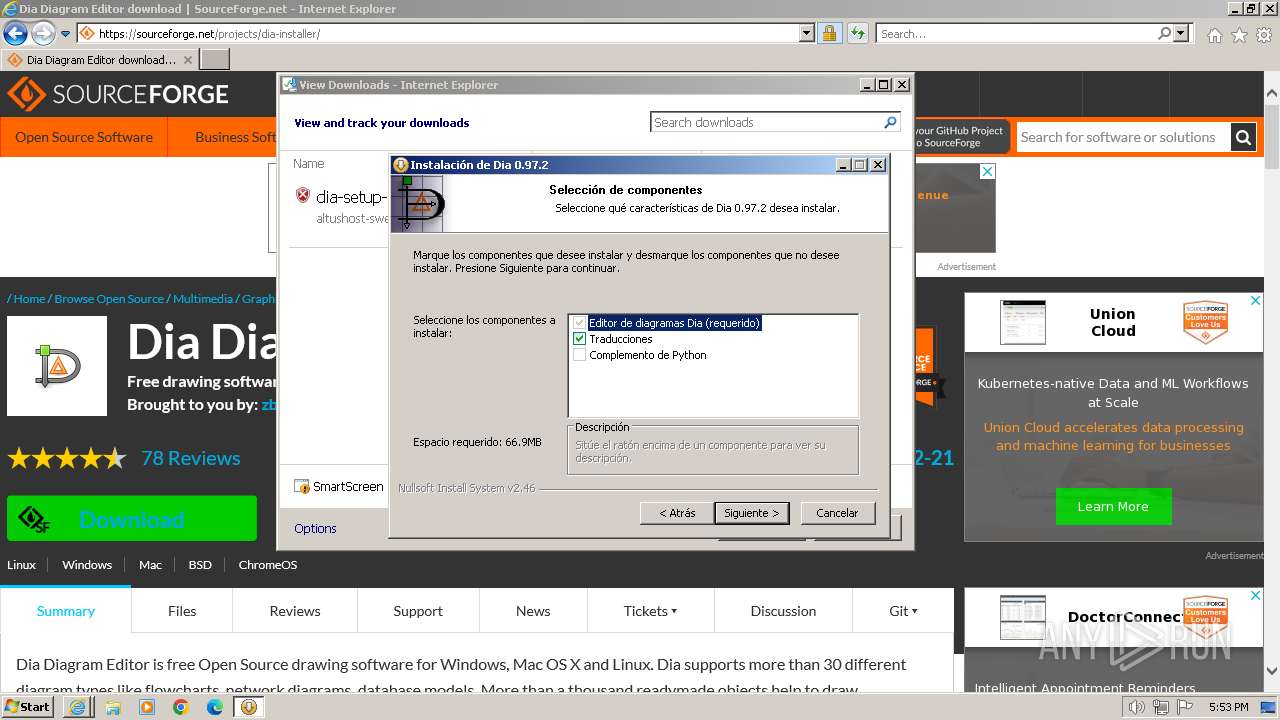
SUSPICIOUS
Executable content was dropped or overwritten
- dia-setup-0.97.2-2-unsigned.exe (PID: 2172)
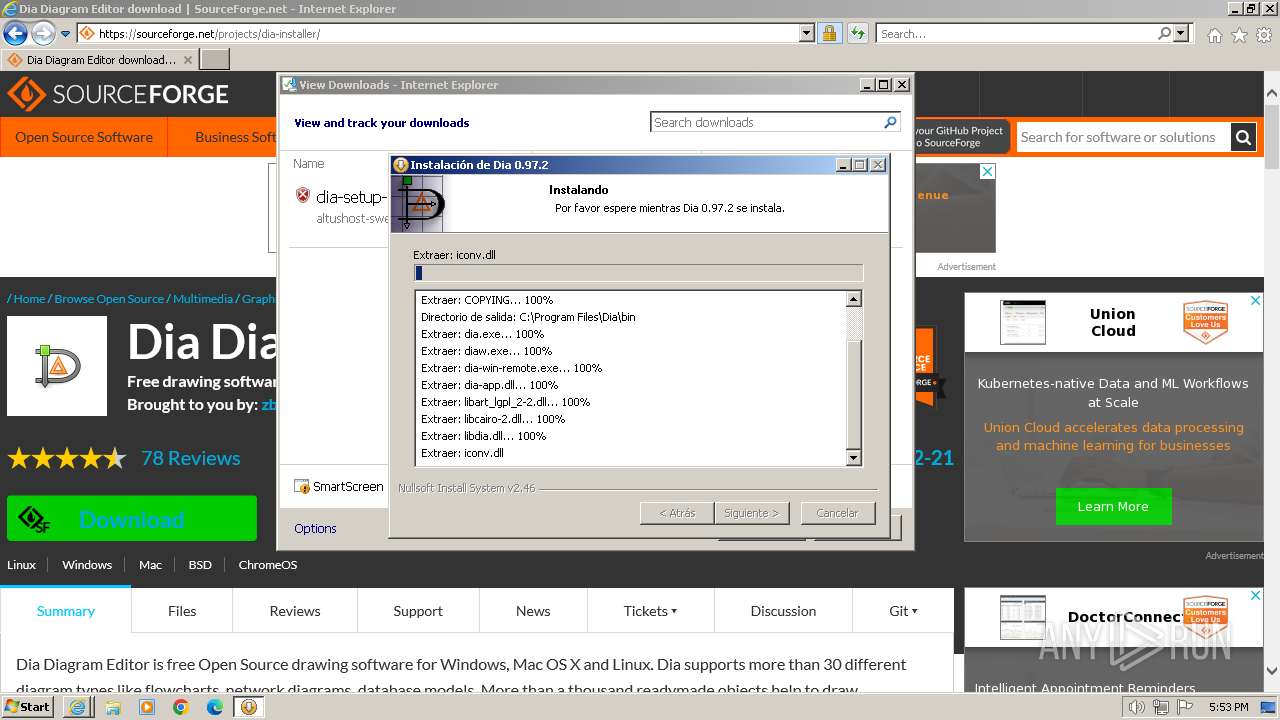
Starts CMD.EXE for commands execution
- ns12D6.tmp (PID: 2516)
Starts application with an unusual extension
- dia-setup-0.97.2-2-unsigned.exe (PID: 2172)
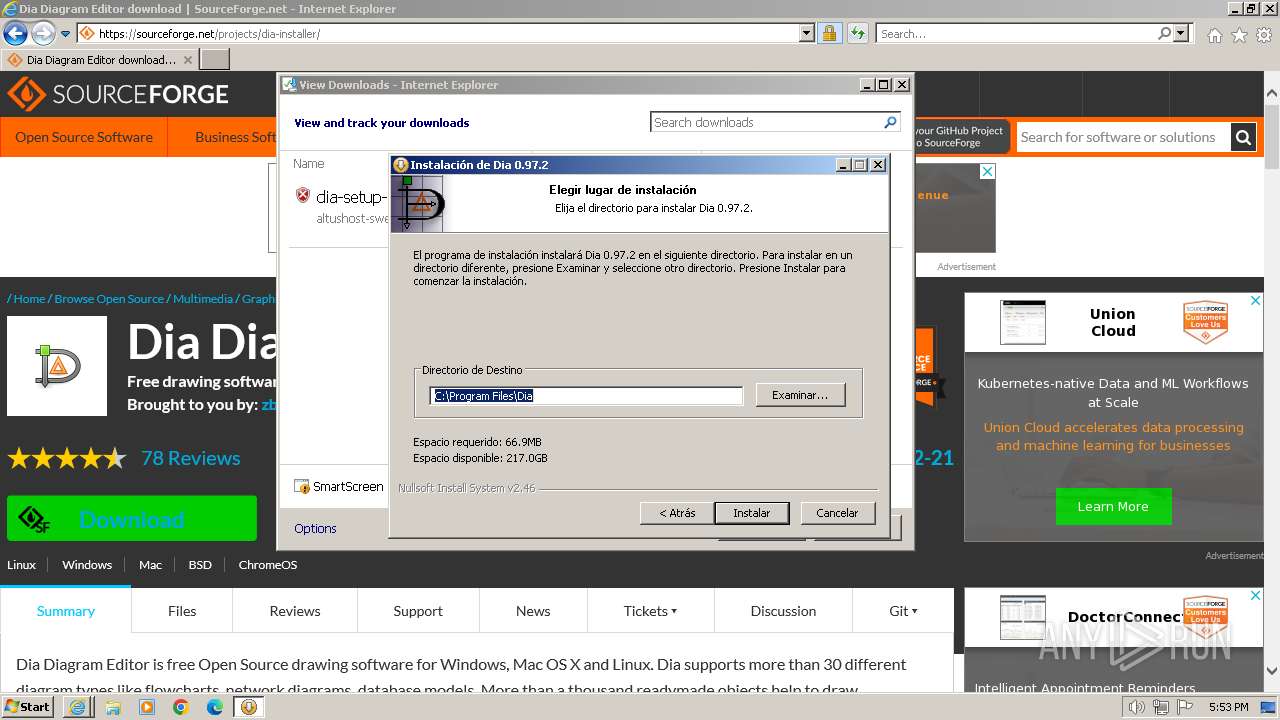
Creates a software uninstall entry
- dia-setup-0.97.2-2-unsigned.exe (PID: 2172)
Executing commands from a ".bat" file
- ns12D6.tmp (PID: 2516)
INFO
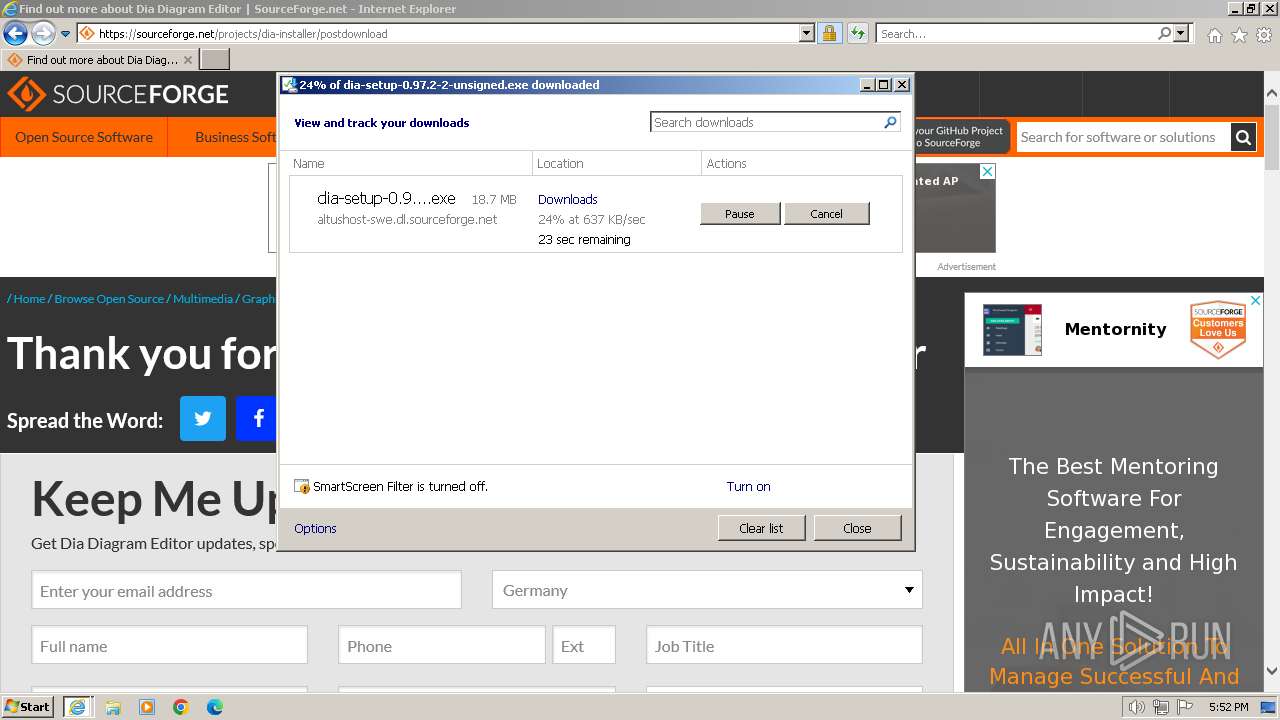
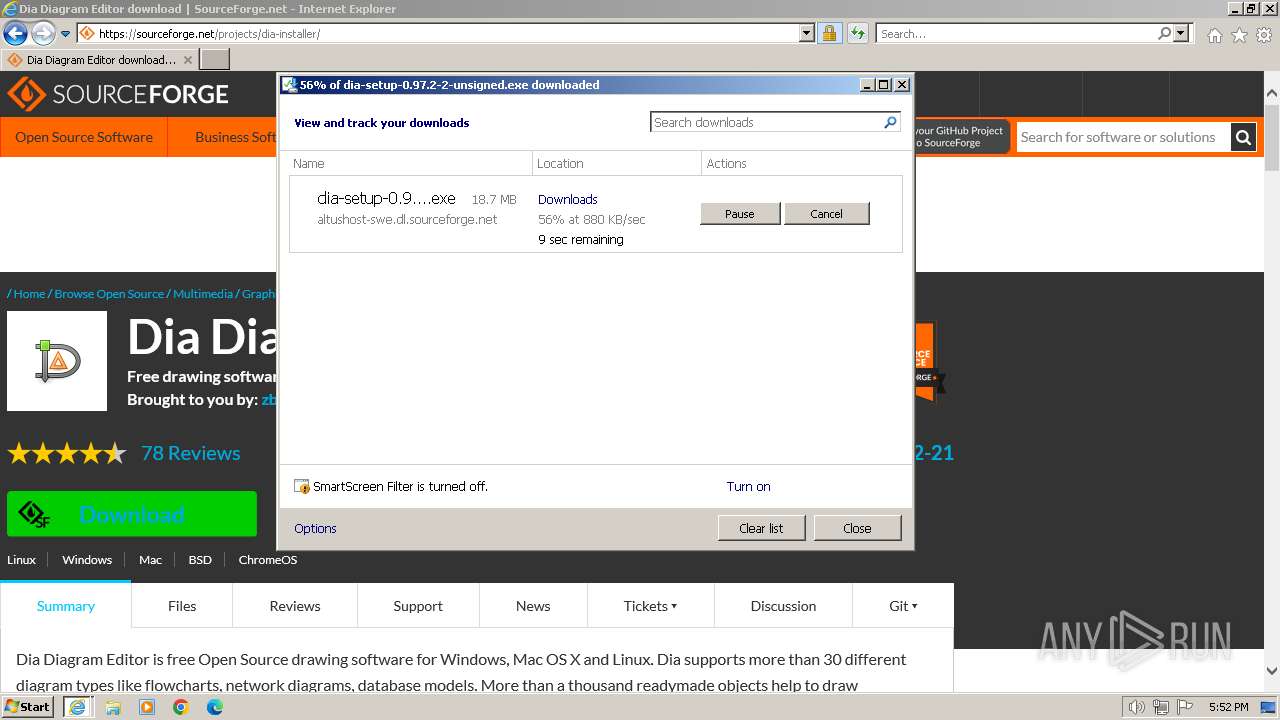
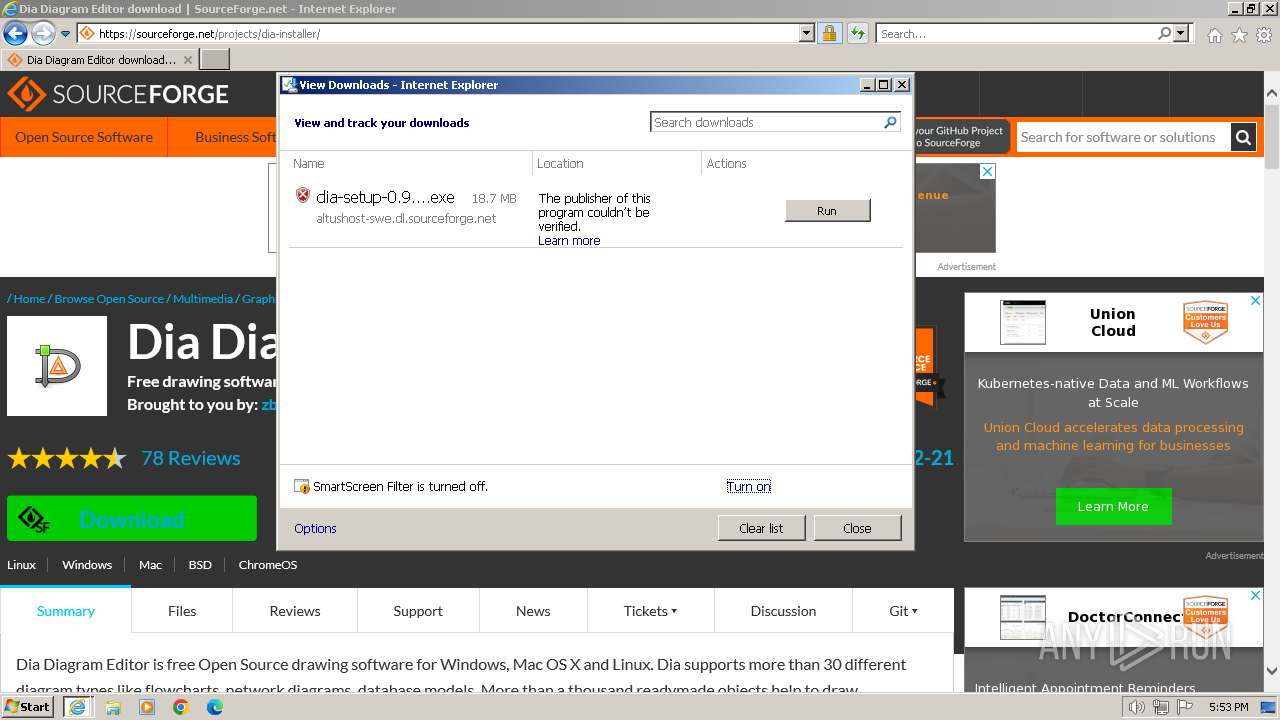
Application launched itself
- iexplore.exe (PID: 4052)
Modifies the phishing filter of IE
- iexplore.exe (PID: 4052)
Executable content was dropped or overwritten
- iexplore.exe (PID: 4052)
- iexplore.exe (PID: 3664)
Drops the executable file immediately after the start
- iexplore.exe (PID: 4052)
- iexplore.exe (PID: 3664)
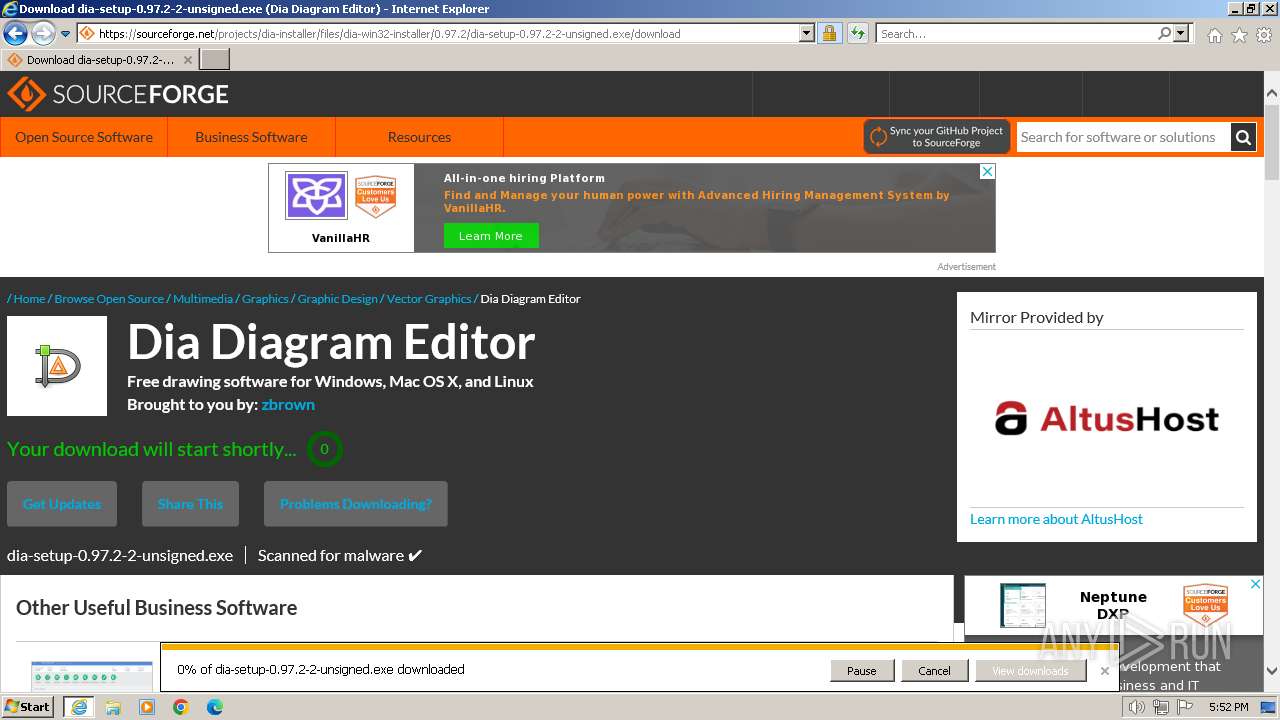
The process uses the downloaded file
- iexplore.exe (PID: 4052)
Reads the computer name
- dia-setup-0.97.2-2-unsigned.exe (PID: 2172)
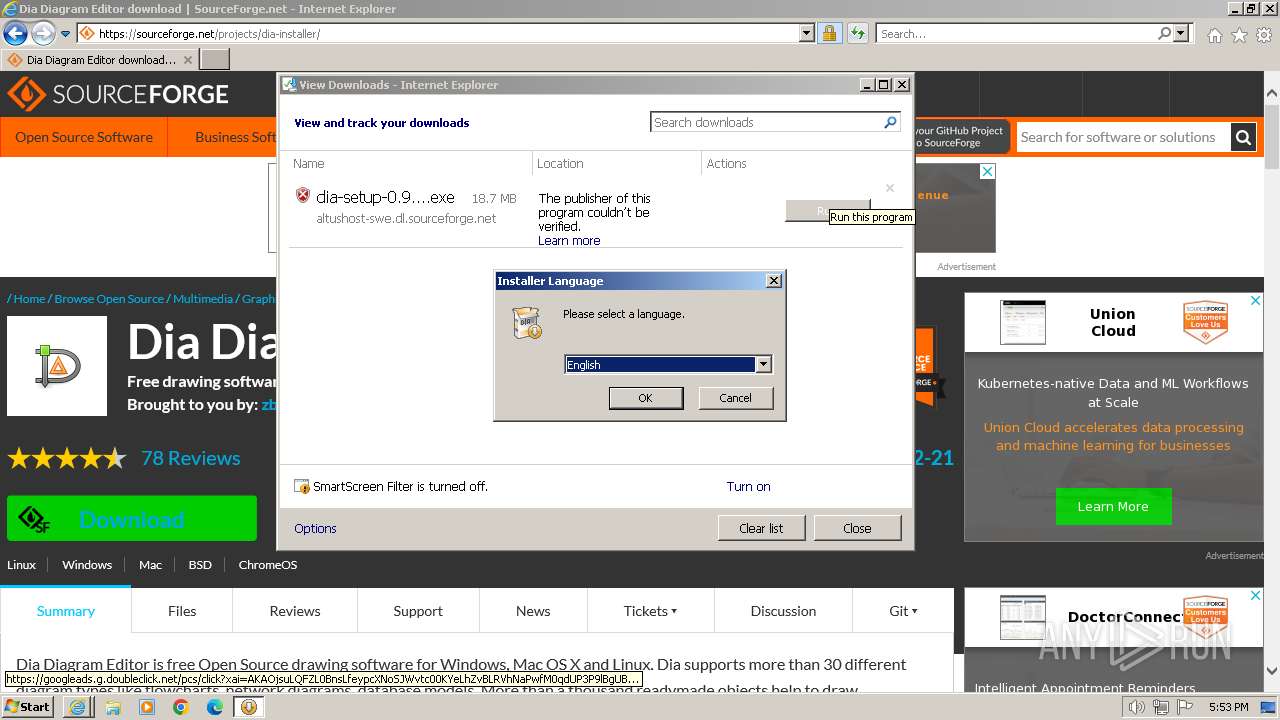
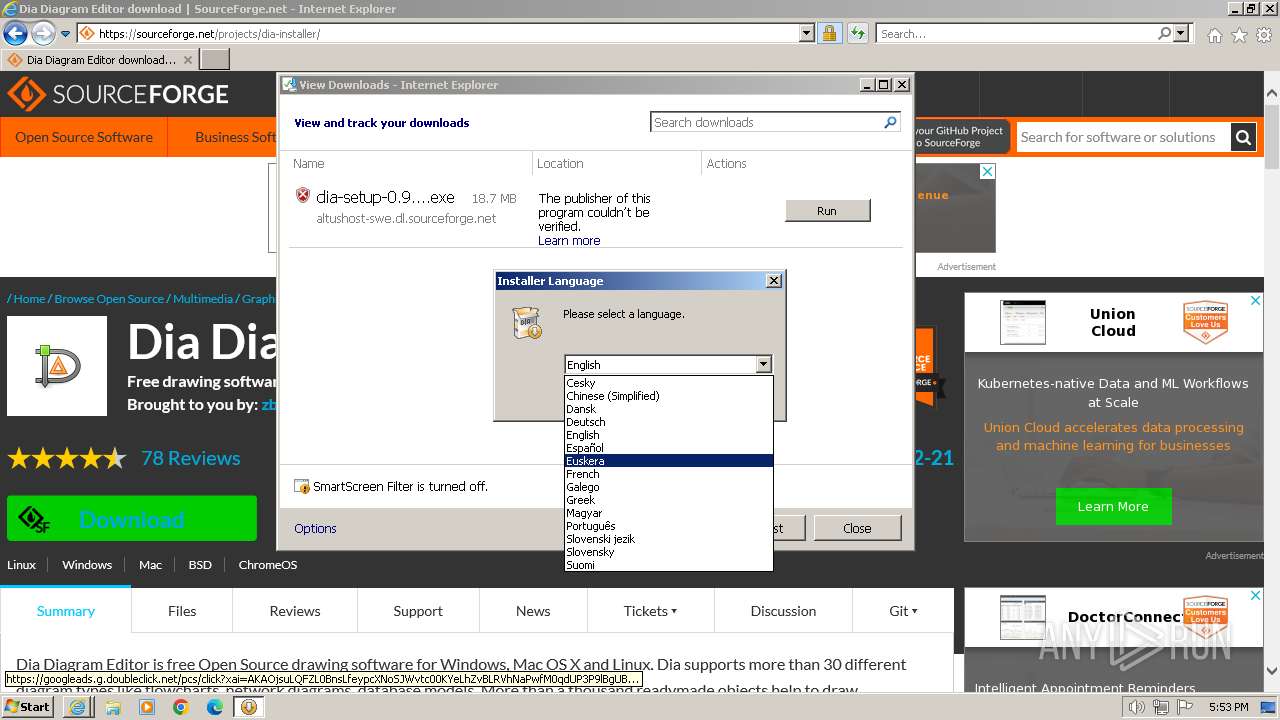
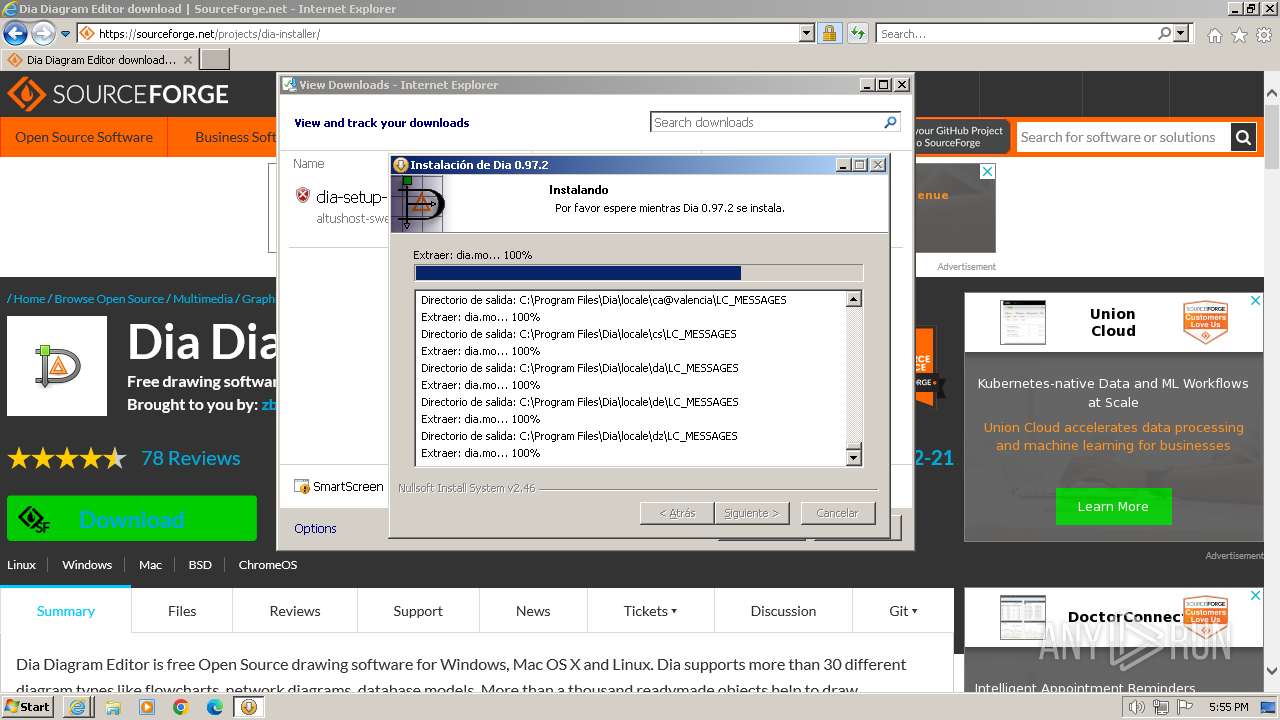
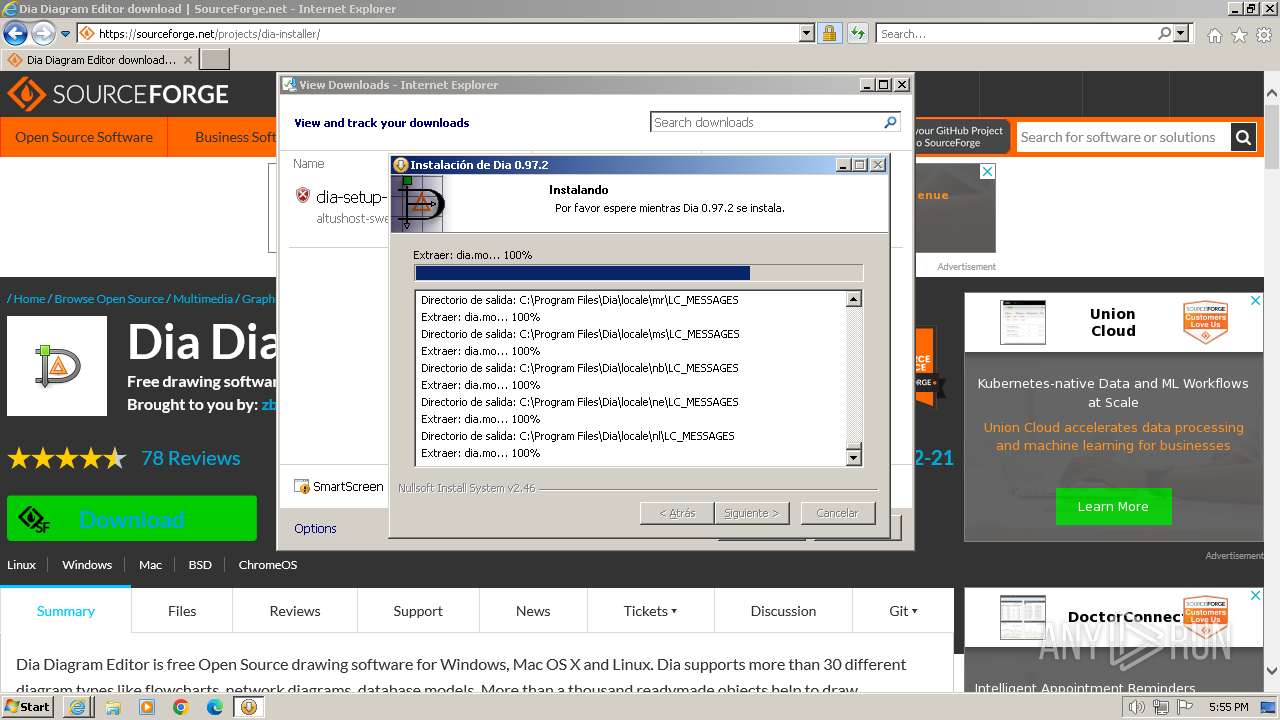
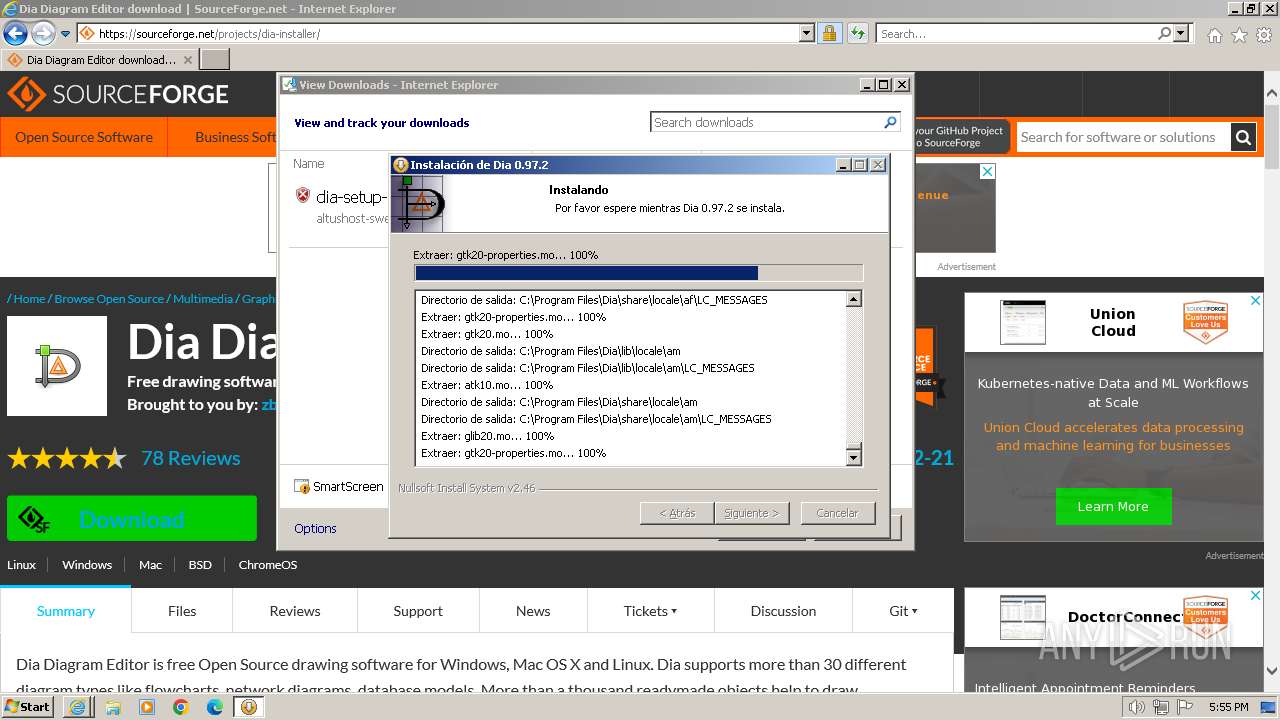
Checks supported languages
- dia-setup-0.97.2-2-unsigned.exe (PID: 2172)
- ns12D6.tmp (PID: 2516)
- gdk-pixbuf-query-loaders.exe (PID: 1020)
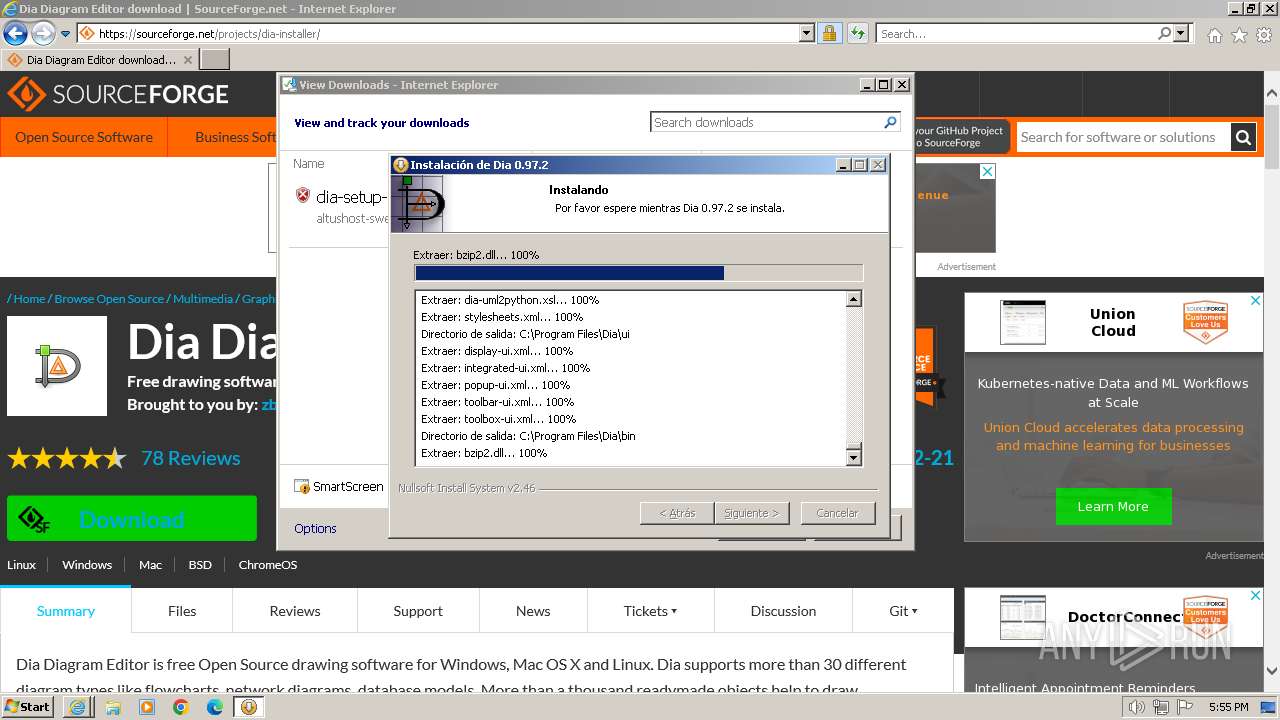
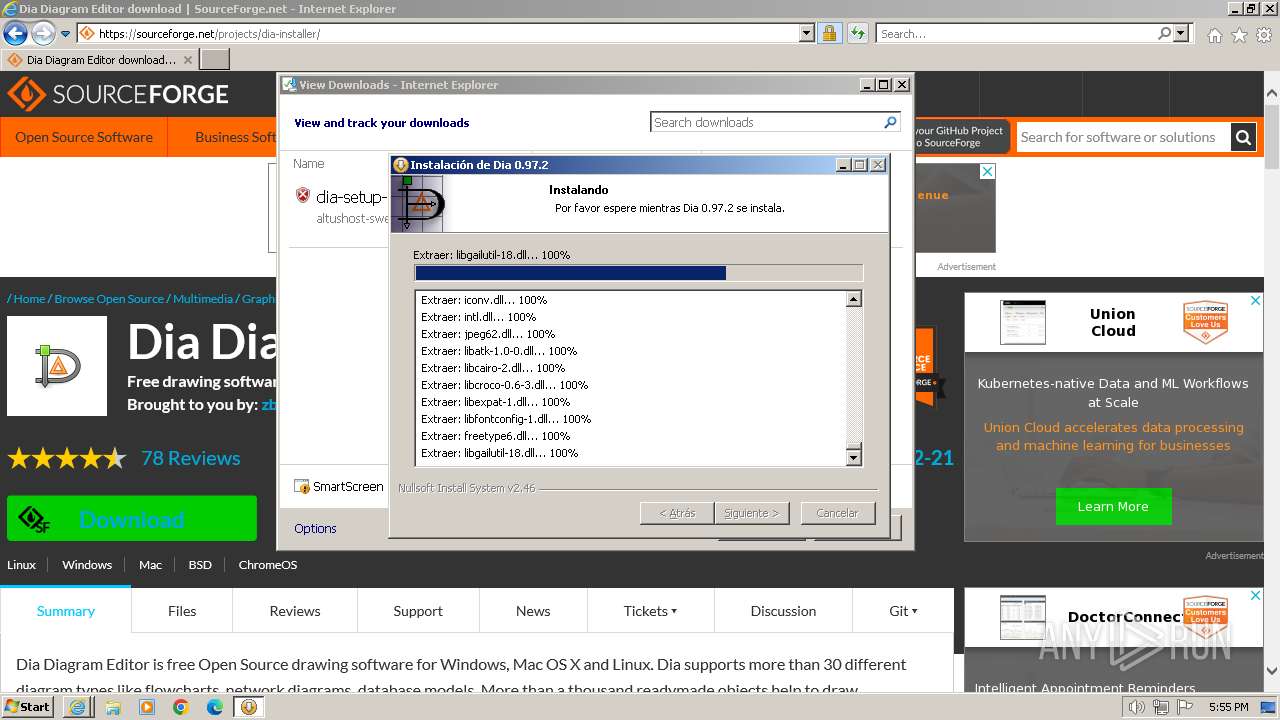
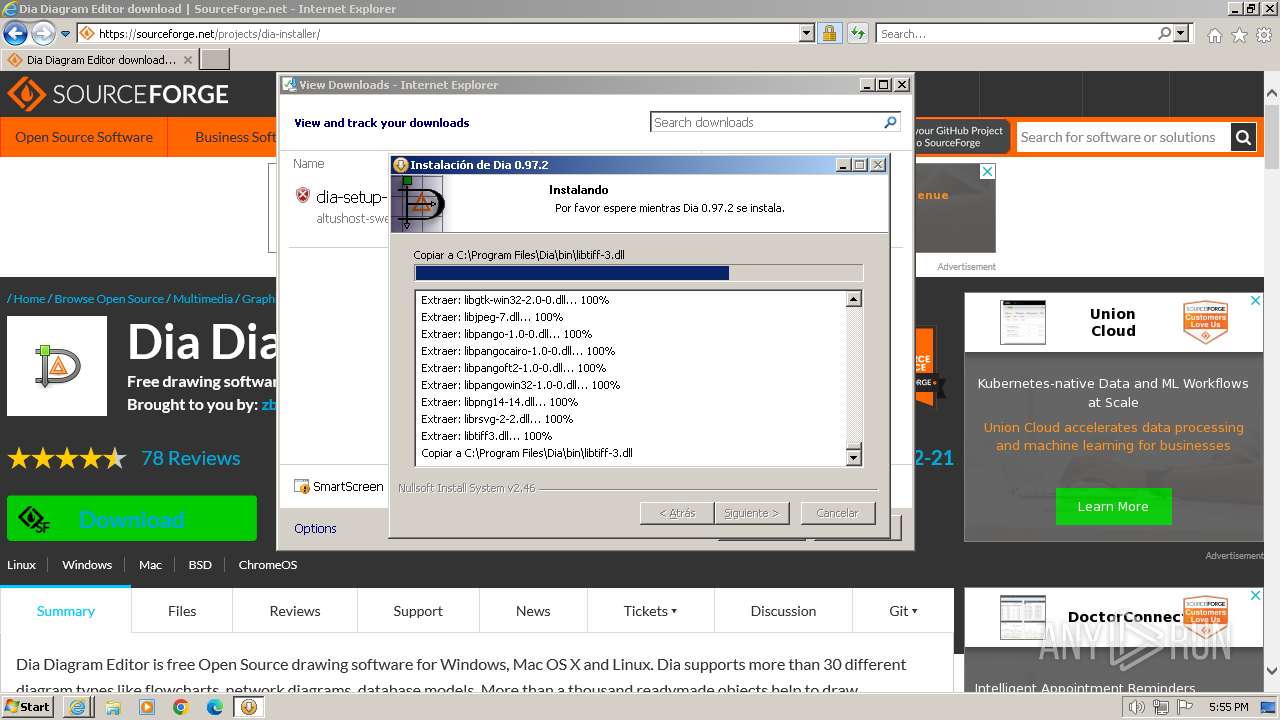
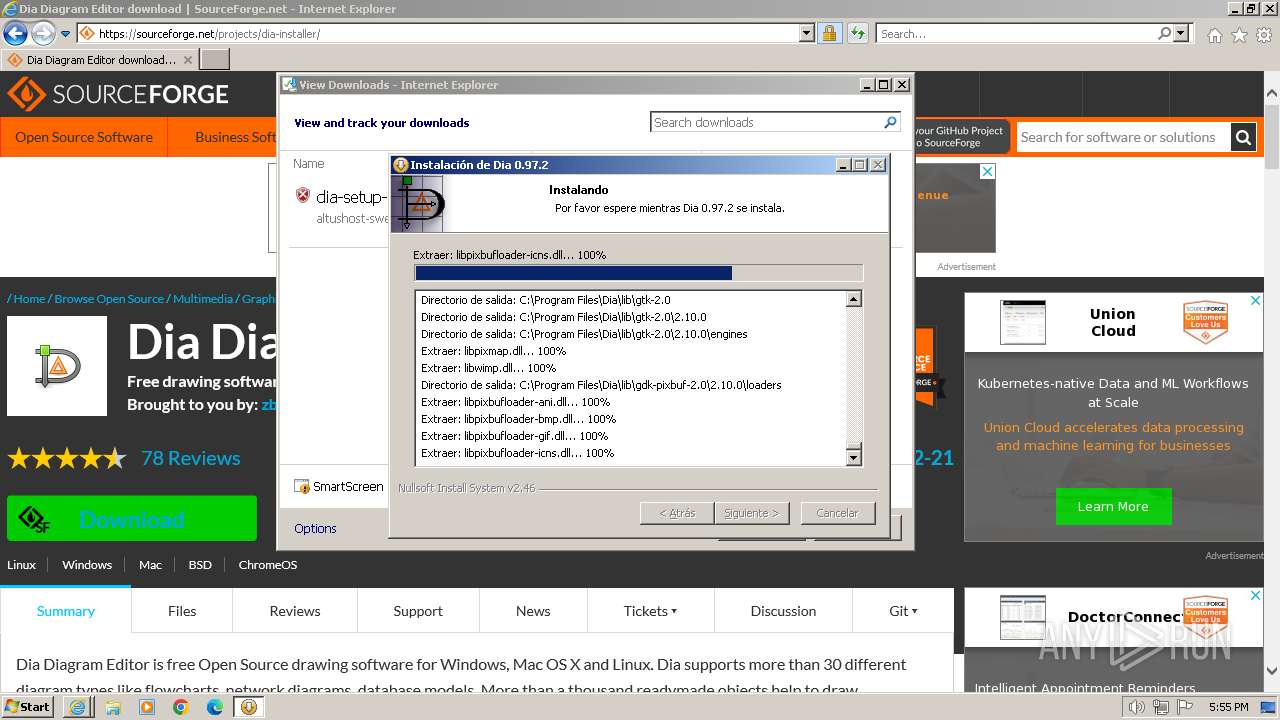
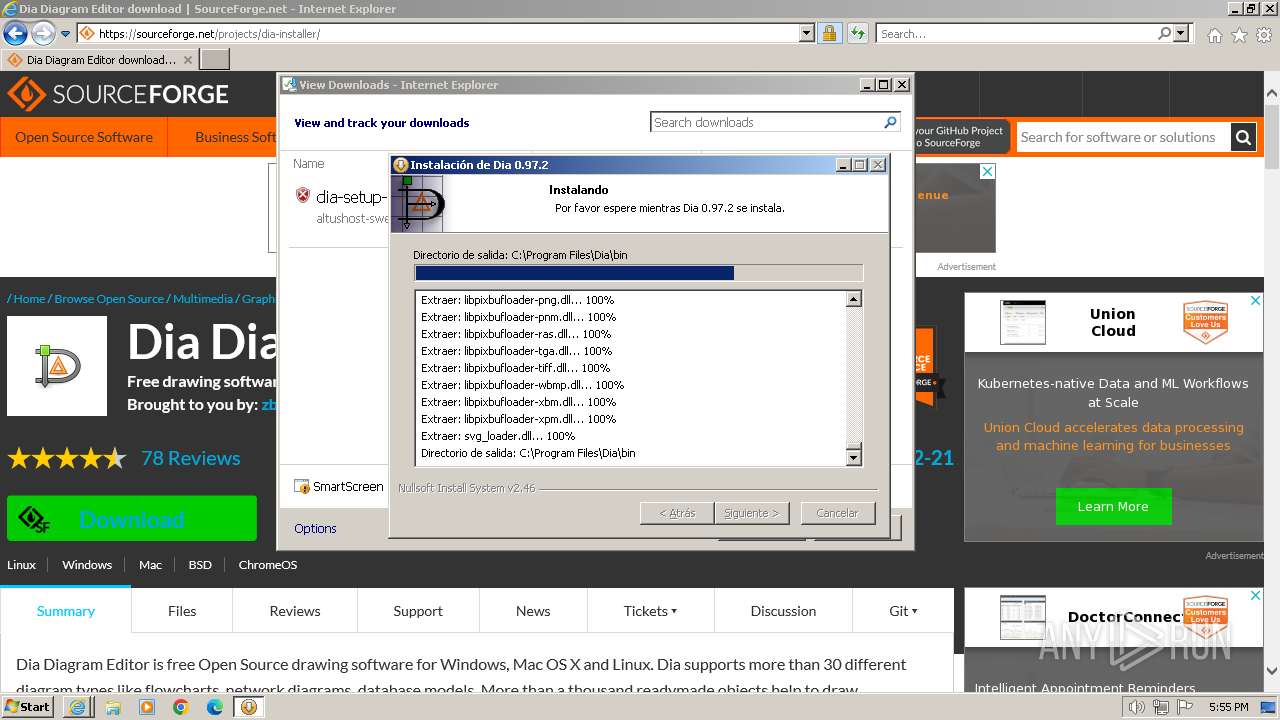
Creates files in the program directory
- dia-setup-0.97.2-2-unsigned.exe (PID: 2172)
- cmd.exe (PID: 1036)
Reads the machine GUID from the registry
- dia-setup-0.97.2-2-unsigned.exe (PID: 2172)
Create files in a temporary directory
- dia-setup-0.97.2-2-unsigned.exe (PID: 2172)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
52
Monitored processes
7
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
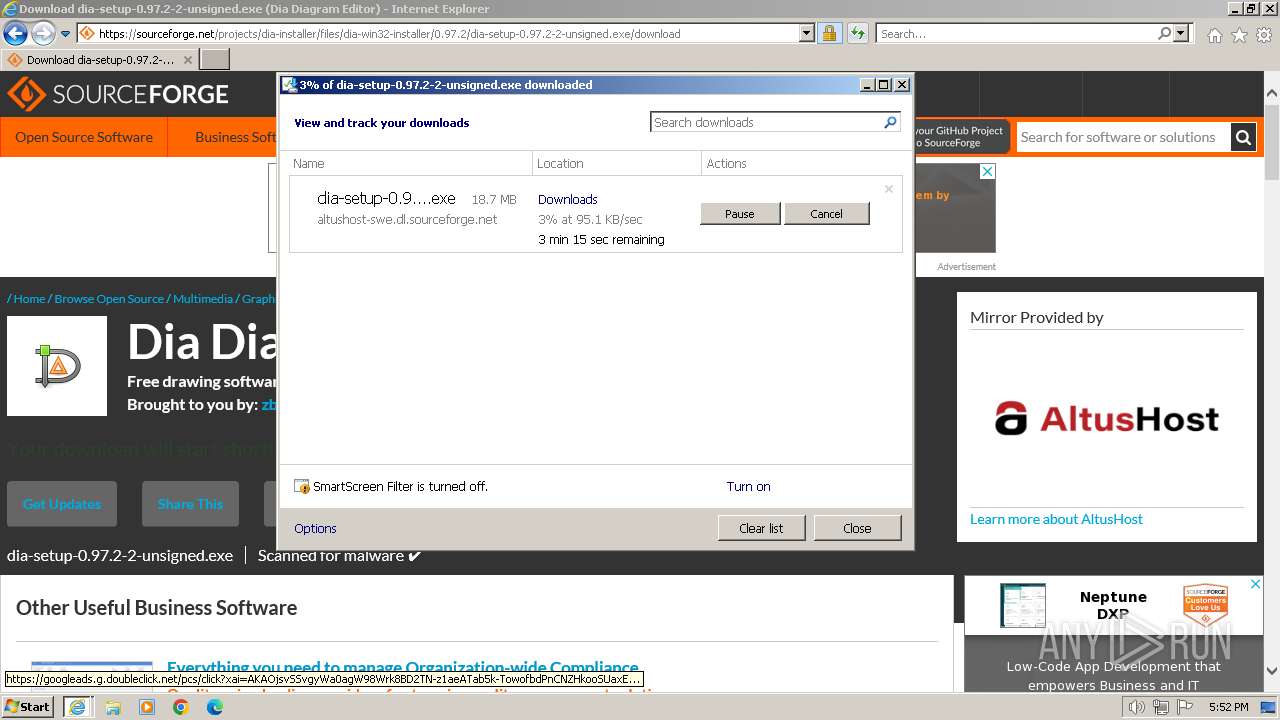
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1020 | .\gdk-pixbuf-query-loaders.exe | C:\Program Files\Dia\bin\gdk-pixbuf-query-loaders.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1036 | "C:\Windows\system32\cmd.exe" /c "C:\Program Files\Dia\bin\gdk-pixbuf-query-loaders.bat" | C:\Windows\System32\cmd.exe | — | ns12D6.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
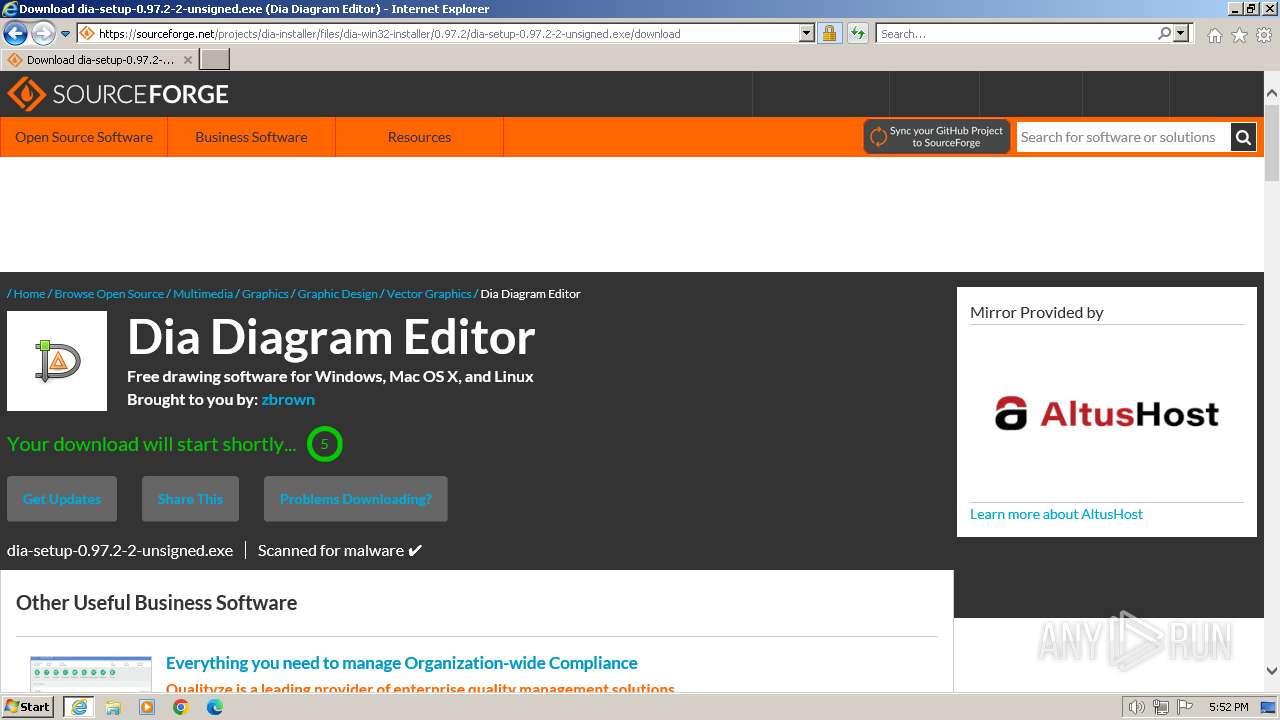
| 2172 | "C:\Users\admin\Downloads\dia-setup-0.97.2-2-unsigned.exe" | C:\Users\admin\Downloads\dia-setup-0.97.2-2-unsigned.exe | iexplore.exe | ||||||||||||
User: admin Company: The Dia Developers Integrity Level: HIGH Description: Dia for Windows Installer Exit code: 0 Version: 0.97.2.2 Modules
| |||||||||||||||
| 2516 | "C:\Users\admin\AppData\Local\Temp\nsu86A7.tmp\ns12D6.tmp" "C:\Windows\system32\cmd.exe" /c "C:\Program Files\Dia\bin\gdk-pixbuf-query-loaders.bat" | C:\Users\admin\AppData\Local\Temp\nsu86A7.tmp\ns12D6.tmp | — | dia-setup-0.97.2-2-unsigned.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2972 | "C:\Users\admin\Downloads\dia-setup-0.97.2-2-unsigned.exe" | C:\Users\admin\Downloads\dia-setup-0.97.2-2-unsigned.exe | — | iexplore.exe | |||||||||||
User: admin Company: The Dia Developers Integrity Level: MEDIUM Description: Dia for Windows Installer Exit code: 3221226540 Version: 0.97.2.2 Modules
| |||||||||||||||
| 3664 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:4052 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 4052 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://dia-installer.de/download/index.html.en" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
41 378
Read events
41 150
Write events
187
Delete events
41
Modification events
| (PID) Process: | (4052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (4052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (4052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31090103 | |||
| (PID) Process: | (4052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (4052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31090103 | |||
| (PID) Process: | (4052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (4052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
103
Suspicious files
1 197
Text files
1 178
Unknown types
77
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3664 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | binary | |
MD5:D31EBD06C7D8A076E34F7D42205DF43B | SHA256:8CE9B16DF7EB54779FC21F36C5B69B8B1287782067003D27FA3E8EFA209D4324 | |||
| 3664 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\index.html[1].htm | html | |
MD5:FD4D8629D27EB052F272A0F428FD94B7 | SHA256:DF2CE7053BE95100A24C035A3B538FF425C8F9BB353B9247B08FBFEB4D294FE1 | |||
| 3664 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\businesswoman[1].jpg | image | |
MD5:025301F9CCC3A9175392FB0A32D4481F | SHA256:B65005BFC01AE473882375FD4BE20E23201C85C5A1389894A7CF9311B0E2BF97 | |||
| 3664 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | binary | |
MD5:AC89A852C2AAA3D389B2D2DD312AD367 | SHA256:0B720E19270C672F9B6E0EC40B468AC49376807DE08A814573FE038779534F45 | |||
| 3664 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\jsapi[1].htm | html | |
MD5:894398A44E596D21C3DF5F131406ADA7 | SHA256:2554C2A9719ACECB146D0735EE2D06C63CC217C9DC104CFC509698D390DA6548 | |||
| 3664 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\poweredby_FFFFFF[1].gif | image | |
MD5:7759990FF12382CAB2E362E8DE465C92 | SHA256:F0E34E6156E006E95579F7FD649583A85175B331452C3CB0AAC883C472CEE0FE | |||
| 3664 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:04E1C0FB7C50EFAF86BA32AC99AF0CD4 | SHA256:59CD12F0B76CE31550E9068FED1DA5C917F8B4361EF4F3C62C9522473162705A | |||
| 3664 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:C9B4D4863732FB1E0D3392BC954B22AE | SHA256:61B79E17407D55AF0DACEB745F3C5D23AC28D27E776532B40D8B23A9C77D6F5F | |||
| 3664 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:FDE2AA4C740E700B53B0C616D82734DE | SHA256:D2165BFD176E75DF79087879C7FEB295D867000B166778BB1244FA8829C64104 | |||
| 3664 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\optimized[1].css | text | |
MD5:CD12A380C602FAA807BE25955BE321E6 | SHA256:37127AD0B5B388FB776A3B6D247E33D7804C23DEAE07D20FE1B32E02FE383300 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
50
TCP/UDP connections
158
DNS requests
52
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3664 | iexplore.exe | GET | 200 | 142.250.186.132:80 | http://www.google.com/images/poweredby_transparent/poweredby_FFFFFF.gif | US | image | 488 b | unknown |
3664 | iexplore.exe | GET | 301 | 142.250.186.132:80 | http://www.google.com/jsapi?key=ABQIAAAA_LC8bNVvrwDWlZeAUDd2TRQK9B8tGKDARuNlTGxOyQ6YZovAKhQaKXTVPtk1sEtjOo43jAxDQmHhKw | US | html | 328 b | unknown |
3664 | iexplore.exe | GET | 200 | 81.169.145.64:80 | http://static.dia-installer.de/images/dia.png | DE | image | 3.11 Kb | unknown |
3664 | iexplore.exe | GET | 200 | 142.250.181.226:80 | http://pagead2.googlesyndication.com/pagead/show_ads.js | US | text | 14.0 Kb | unknown |
3664 | iexplore.exe | GET | 200 | 81.169.145.64:80 | http://static.dia-installer.de/images/businesswoman.jpg | DE | image | 5.89 Kb | unknown |
3664 | iexplore.exe | GET | 304 | 23.48.23.61:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?29f261daf338db73 | DE | — | — | unknown |
3664 | iexplore.exe | GET | 304 | 23.48.23.61:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?09a5b2e51d609355 | DE | — | — | unknown |
3664 | iexplore.exe | GET | 304 | 23.48.23.61:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?2eca403b5c4f6283 | DE | — | — | unknown |
3664 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | binary | 471 b | unknown |
3664 | iexplore.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | binary | 1.41 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3664 | iexplore.exe | 81.169.145.64:80 | dia-installer.de | Strato AG | DE | unknown |
3664 | iexplore.exe | 142.250.186.132:80 | www.google.com | GOOGLE | US | whitelisted |
3664 | iexplore.exe | 142.250.184.238:443 | apis.google.com | GOOGLE | US | whitelisted |
3664 | iexplore.exe | 142.250.181.226:80 | pagead2.googlesyndication.com | GOOGLE | US | whitelisted |
3664 | iexplore.exe | 142.250.185.131:443 | www.gstatic.com | GOOGLE | US | whitelisted |
3664 | iexplore.exe | 23.48.23.61:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
3664 | iexplore.exe | 142.250.186.163:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dia-installer.de |
| unknown |
static.dia-installer.de |
| unknown |
www.google.com |
| whitelisted |
apis.google.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
connect.facebook.net |
| whitelisted |