| File name: | 02458426_1 |
| Full analysis: | https://app.any.run/tasks/02ca8fe0-2b50-480e-a15e-487618b310b6 |
| Verdict: | Malicious activity |
| Analysis date: | March 29, 2021, 06:57:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | CF767AE89F07D82DAA8C4EA369D0D9E9 |
| SHA1: | F02638FC9428E90F1EC2C3A917EC003A82544947 |
| SHA256: | D2D94766BC309C5C3D0142BCE3DF805D1EC2D80FB9E2CCA76C81F3E8DC037FE3 |
| SSDEEP: | 49152:OMG4iTX6+6M1Ikpv5aktO3+ZmP5yvcoeY3MeYC+fJn:Ol4mX6+6M1fpvrw+ZmhoeCWC+fJn |
MALICIOUS
Drops executable file immediately after starts
- 02458426_1.exe (PID: 2348)
Loads dropped or rewritten executable
- 02458426_1.exe (PID: 2348)
- KGPMService.exe (PID: 660)
- LoadNTDriver.exe (PID: 1460)
- KGPMService.exe (PID: 3196)
- KGPM_32.exe (PID: 3824)
Application was dropped or rewritten from another process
- LoadNTDriver.exe (PID: 1460)
- KGPMService.exe (PID: 660)
- KGPMService.exe (PID: 3196)
- KGPM_32.exe (PID: 3824)
SUSPICIOUS
Drops a file that was compiled in debug mode
- 02458426_1.exe (PID: 2348)
Creates files in the program directory
- 02458426_1.exe (PID: 2348)
Creates a directory in Program Files
- 02458426_1.exe (PID: 2348)
Drops a file with too old compile date
- 02458426_1.exe (PID: 2348)
Executable content was dropped or overwritten
- 02458426_1.exe (PID: 2348)
Creates files in the user directory
- 02458426_1.exe (PID: 2348)
Executed as Windows Service
- KGPMService.exe (PID: 3196)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:05 23:50:41+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23040 |
| InitializedDataSize: | 119808 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x30cb |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
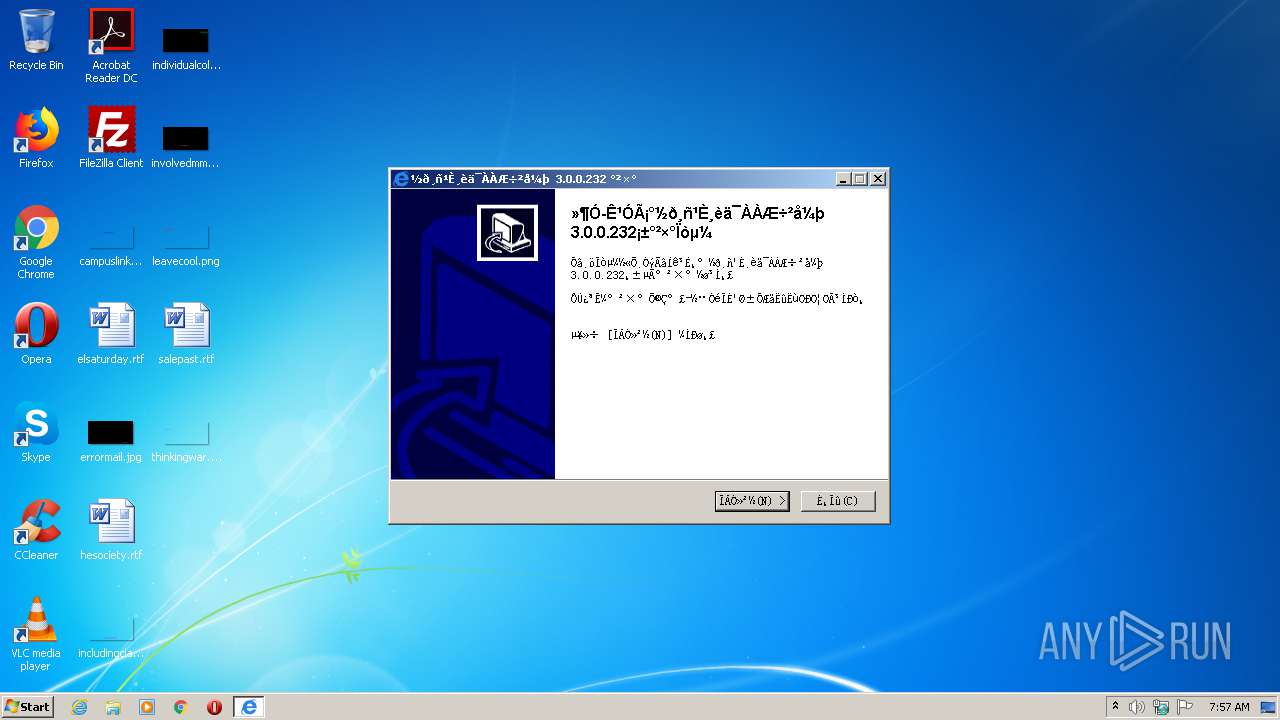
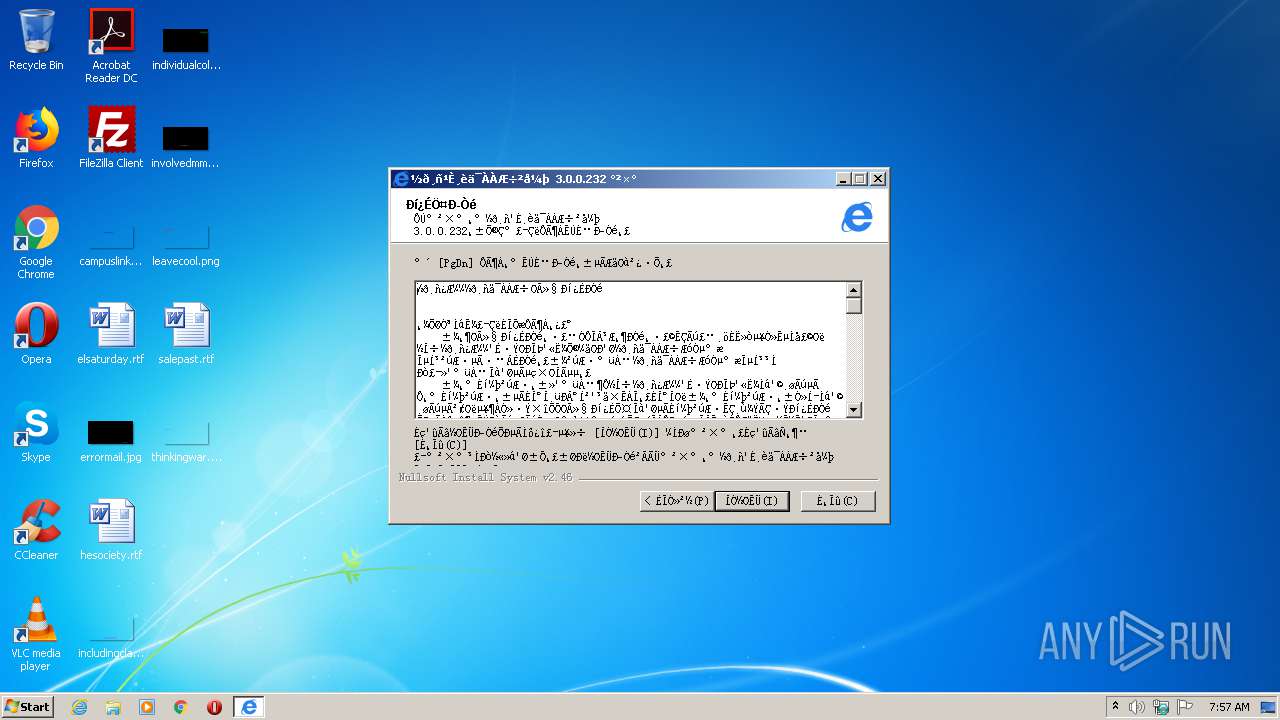
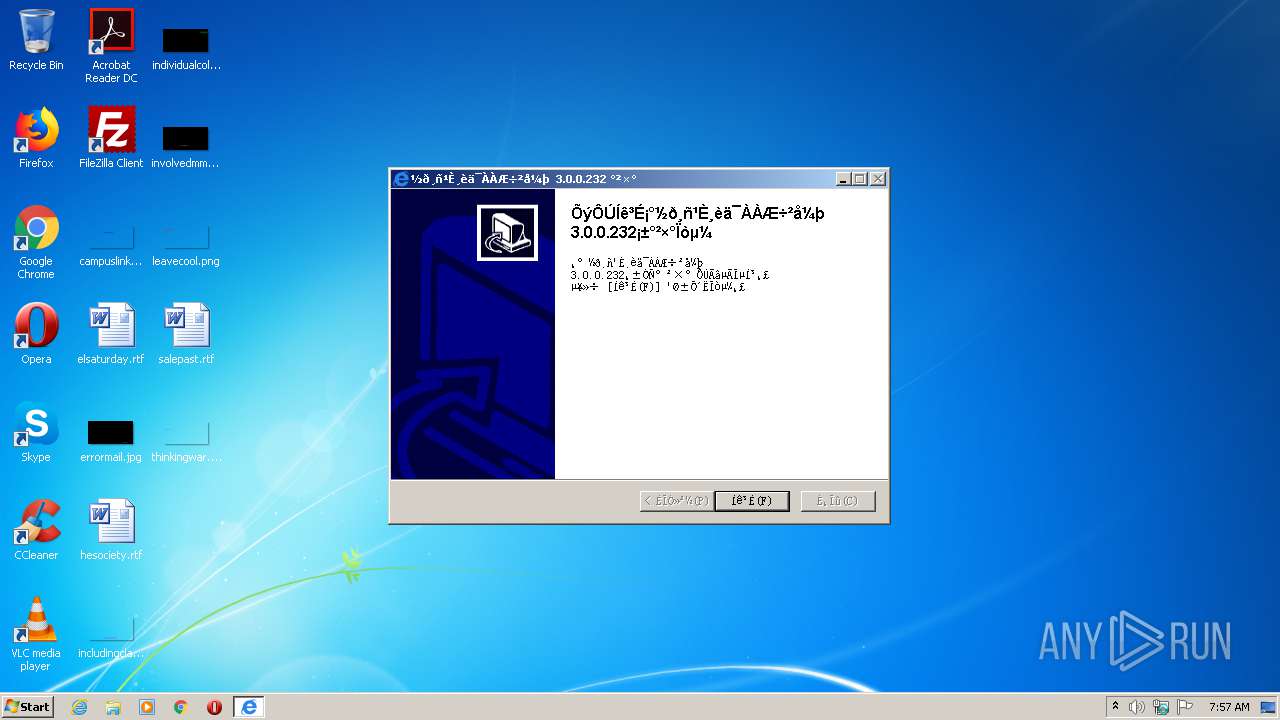
| FileVersionNumber: | 3.0.0.232 |
| ProductVersionNumber: | 3.0.0.232 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Windows, Chinese (Simplified) |
| CompanyName: | ${COMPANY_NAME} |
| FileDescription: | 金格谷歌浏览器插件 |
| FileVersion: | 3.0.0.232 |
| LegalCopyright: | 版权所有 (C) 2003-2021 江西金格科技股份有限公司。保留所有权利 |
| ProductName: | 金格谷歌浏览器插件 |
| ProductVersion: | 3.0.0.232 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2009 22:50:41 |
| Detected languages: |
|
| CompanyName: | ${COMPANY_NAME} |
| FileDescription: | 金格谷歌浏览器插件 |
| FileVersion: | 3.0.0.232 |
| LegalCopyright: | 版权所有 (C) 2003-2021 江西金格科技股份有限公司。保留所有权利 |
| ProductName: | 金格谷歌浏览器插件 |
| ProductVersion: | 3.0.0.232 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Dec-2009 22:50:41 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000058D2 | 0x00005A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4331 |
.rdata | 0x00007000 | 0x00001190 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.17976 |
.data | 0x00009000 | 0x0001AF78 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.6178 |
.ndata | 0x00024000 | 0x00012000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00036000 | 0x00017E88 | 0x00018000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.71191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21482 | 958 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.71171 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 4.90642 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 2.16829 | 3752 | UNKNOWN | English - United States | RT_ICON |
5 | 5.24617 | 2440 | UNKNOWN | English - United States | RT_ICON |
6 | 2.18425 | 2216 | UNKNOWN | English - United States | RT_ICON |
7 | 2.16706 | 1736 | UNKNOWN | English - United States | RT_ICON |
8 | 1.62721 | 1384 | UNKNOWN | English - United States | RT_ICON |
9 | 5.33528 | 1128 | UNKNOWN | English - United States | RT_ICON |
102 | 2.63447 | 160 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
45
Monitored processes
6
Malicious processes
2
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 660 | "C:\Program Files\KGChromePlugin\KGPMService.exe" -i | C:\Program Files\KGChromePlugin\KGPMService.exe | 02458426_1.exe | ||||||||||||
User: admin Company: 江西金格科技股份有限公司 Integrity Level: HIGH Description: KGPMService Exit code: 0 Version: 1.0.0.6 Modules
| |||||||||||||||
| 1456 | "C:\Users\admin\AppData\Local\Temp\02458426_1.exe" | C:\Users\admin\AppData\Local\Temp\02458426_1.exe | — | explorer.exe | |||||||||||
User: admin Company: ${COMPANY_NAME} Integrity Level: MEDIUM Description: 金格谷歌浏览器插件 Exit code: 3221226540 Version: 3.0.0.232 Modules
| |||||||||||||||
| 1460 | "C:\Program Files\KGChromePlugin\LoadNTDriver.exe" | C:\Program Files\KGChromePlugin\LoadNTDriver.exe | — | 02458426_1.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2348 | "C:\Users\admin\AppData\Local\Temp\02458426_1.exe" | C:\Users\admin\AppData\Local\Temp\02458426_1.exe | explorer.exe | ||||||||||||
User: admin Company: ${COMPANY_NAME} Integrity Level: HIGH Description: 金格谷歌浏览器插件 Exit code: 0 Version: 3.0.0.232 Modules
| |||||||||||||||
| 3196 | "C:\Program Files\KGChromePlugin\KGPMService.exe" | C:\Program Files\KGChromePlugin\KGPMService.exe | services.exe | ||||||||||||
User: SYSTEM Company: 江西金格科技股份有限公司 Integrity Level: SYSTEM Description: KGPMService Exit code: 0 Version: 1.0.0.6 Modules
| |||||||||||||||
| 3824 | "C:\Program Files\KGChromePlugin\X86\KGPM_32.exe" | C:\Program Files\KGChromePlugin\X86\KGPM_32.exe | KGPMService.exe | ||||||||||||
User: admin Company: 江西金格科技股份有限公司 Integrity Level: HIGH Description: 金格谷歌浏览器插件服务 Exit code: 0 Version: 1.0.0.22 Modules
| |||||||||||||||
Total events
344
Read events
339
Write events
5
Delete events
0
Modification events
| (PID) Process: | (2348) 02458426_1.exe | Key: | HKEY_CURRENT_USER\Software\KGChromePlugin |
| Operation: | write | Name: | (default) |
Value: C:\Program Files\KGChromePlugin | |||
| (PID) Process: | (2348) 02458426_1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2348) 02458426_1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
18
Suspicious files
0
Text files
6
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2348 | 02458426_1.exe | C:\Program Files\KGChromePlugin\KGChromePlugin_64.dll | executable | |
MD5:— | SHA256:— | |||
| 2348 | 02458426_1.exe | C:\Program Files\KGChromePlugin\KGChromePlugin_32.dll | executable | |
MD5:— | SHA256:— | |||
| 2348 | 02458426_1.exe | C:\Program Files\KGChromePlugin\WinExec.exe | executable | |
MD5:F633707216CA19E7748BBF485BC32898 | SHA256:C08410B2CA18AB7FD628533ADA13FC173640933FB94B791F1114DD78D4663DE8 | |||
| 2348 | 02458426_1.exe | C:\Program Files\KGChromePlugin\world.ico | image | |
MD5:51D641410B08F784E8D28E403BF84E43 | SHA256:DDE6E8A6B52744033A9CA0503E9CA76ED5320A8F7674533C3B3EFF1551C4868F | |||
| 2348 | 02458426_1.exe | C:\Program Files\KGChromePlugin\LoadNTDriver.exe | executable | |
MD5:155F058011702D8292E63F92E1B4DF9A | SHA256:F820EB89D734CEC157E3758AC95E521508CF61D86D35A791880F4941D116F12B | |||
| 2348 | 02458426_1.exe | C:\Program Files\KGChromePlugin\x64\KGPM_64.exe | executable | |
MD5:— | SHA256:— | |||
| 2348 | 02458426_1.exe | C:\Program Files\KGChromePlugin\x86\KGPM_32.exe | executable | |
MD5:— | SHA256:— | |||
| 2348 | 02458426_1.exe | C:\Users\admin\AppData\Local\Temp\nsy8713.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 2348 | 02458426_1.exe | C:\Program Files\KGChromePlugin\whitelist.lst | text | |
MD5:— | SHA256:— | |||
| 2348 | 02458426_1.exe | C:\Users\admin\AppData\Local\Temp\nsy8713.tmp\System.dll | executable | |
MD5:C17103AE9072A06DA581DEC998343FC1 | SHA256:DC58D8AD81CACB0C1ED72E33BFF8F23EA40B5252B5BB55D393A0903E6819AE2F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
KGPMService.exe | C:\Program Files\KGChromePlugin\KGPMService.exe |
KGPMService.exe | -i |
KGPMService.exe | KGSC InstallService |
KGPMService.exe | C:\Program Files\KGChromePlugin\KGPMService.exe |
KGPMService.exe | My Sample Service: Main: Entry |
KGPMService.exe | My Sample Service: ServiceMain: Entry |
KGPMService.exe | My Sample Service: ServiceMain: Performing Service Start Operations |
KGPMService.exe | My Sample Service: ServiceMain: Waiting for Worker Thread to complete |
KGPMService.exe | My Sample Service: ServiceWorkerThread: Entry |
KGPMService.exe | FindProcessByName
|