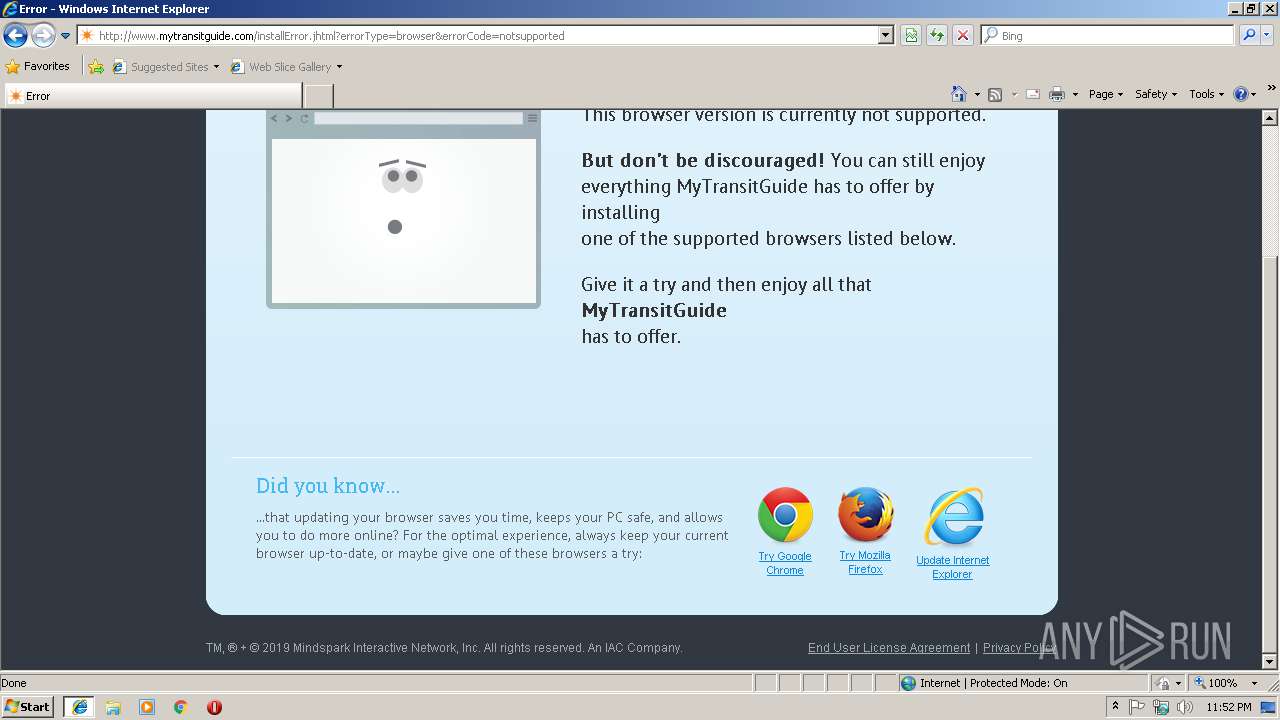
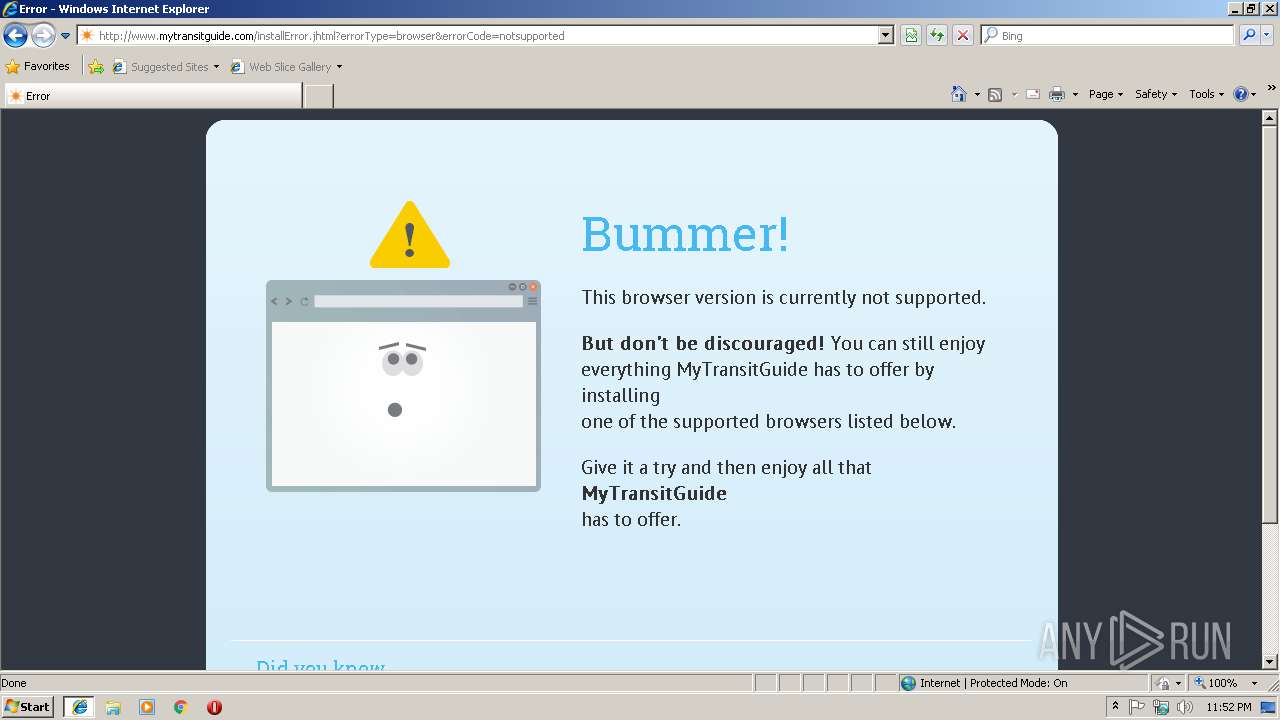
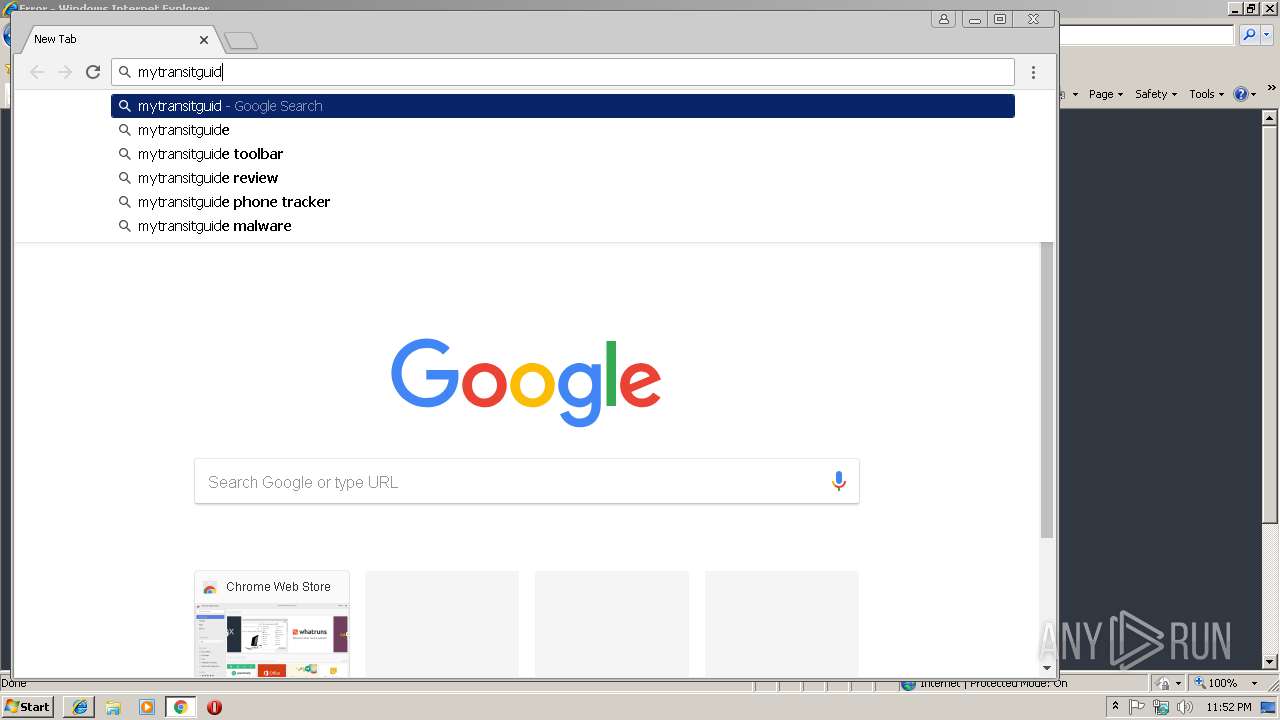
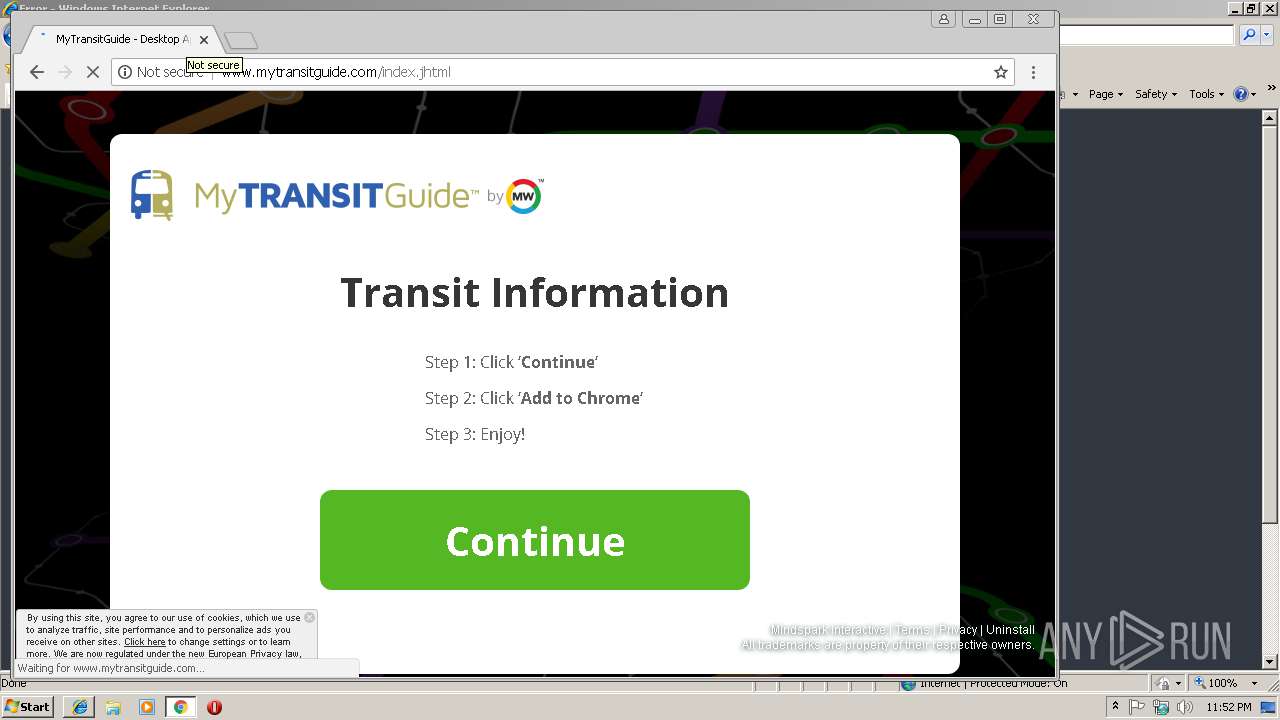
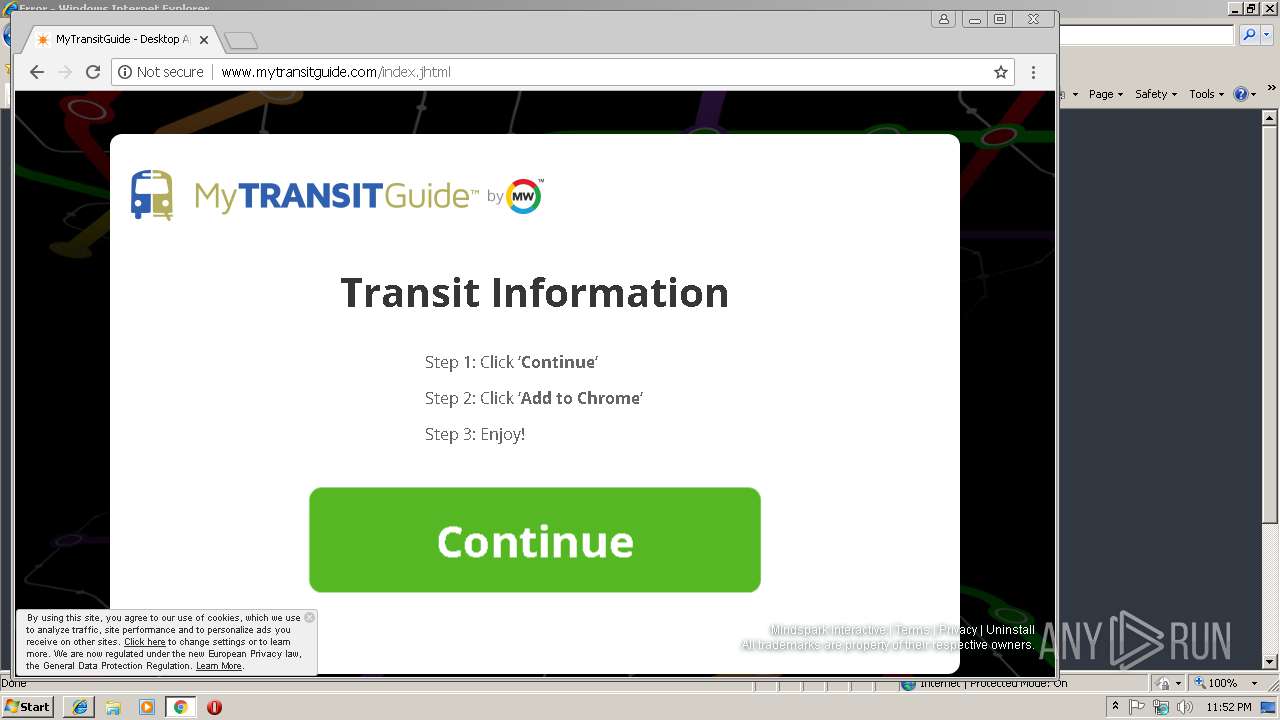
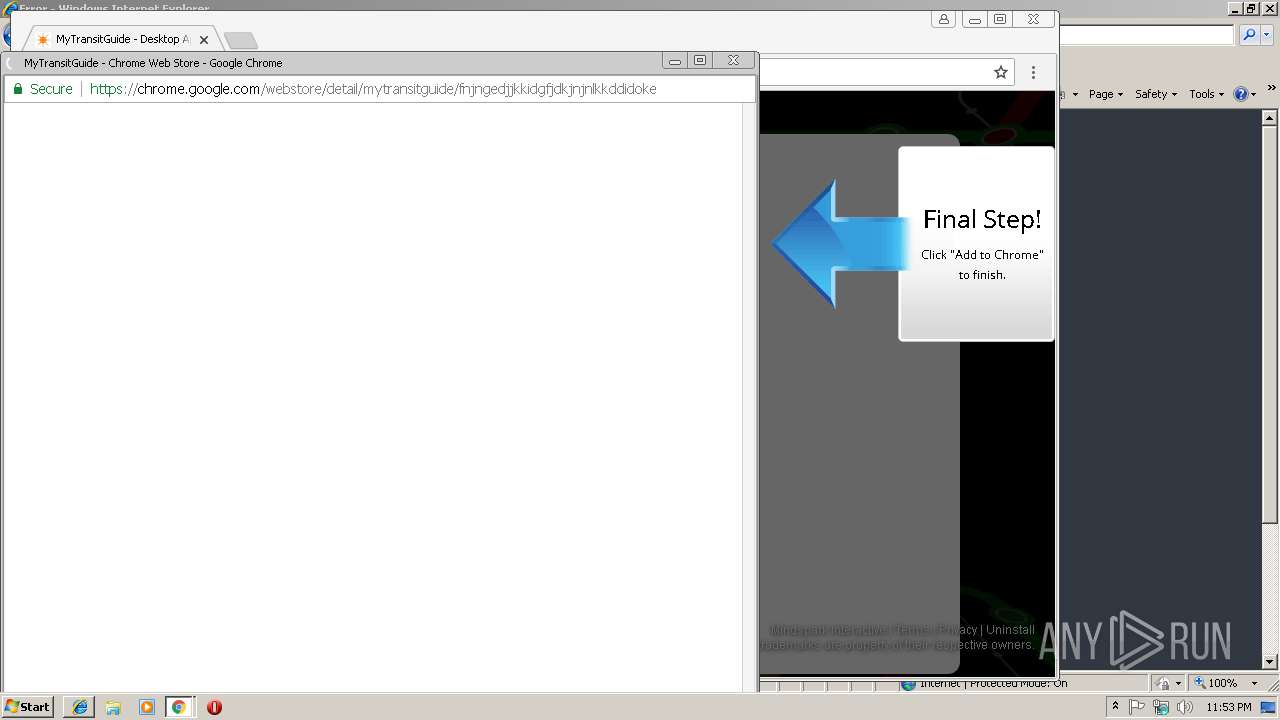
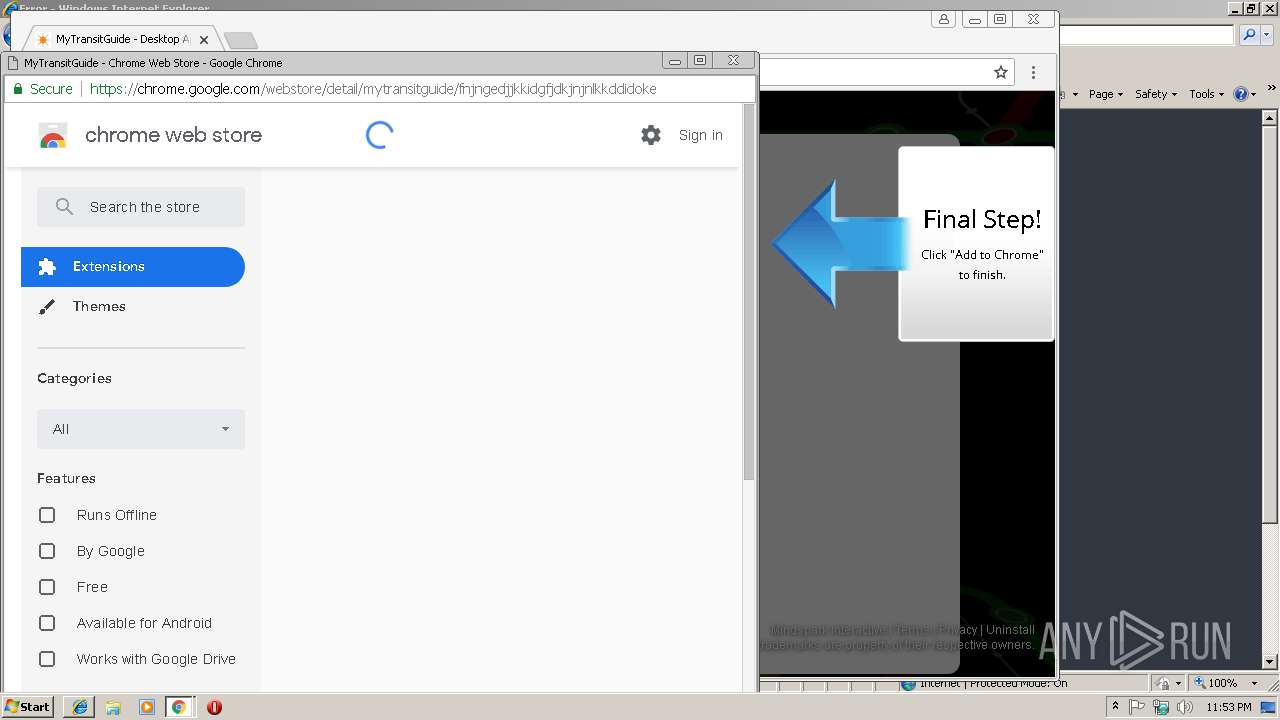
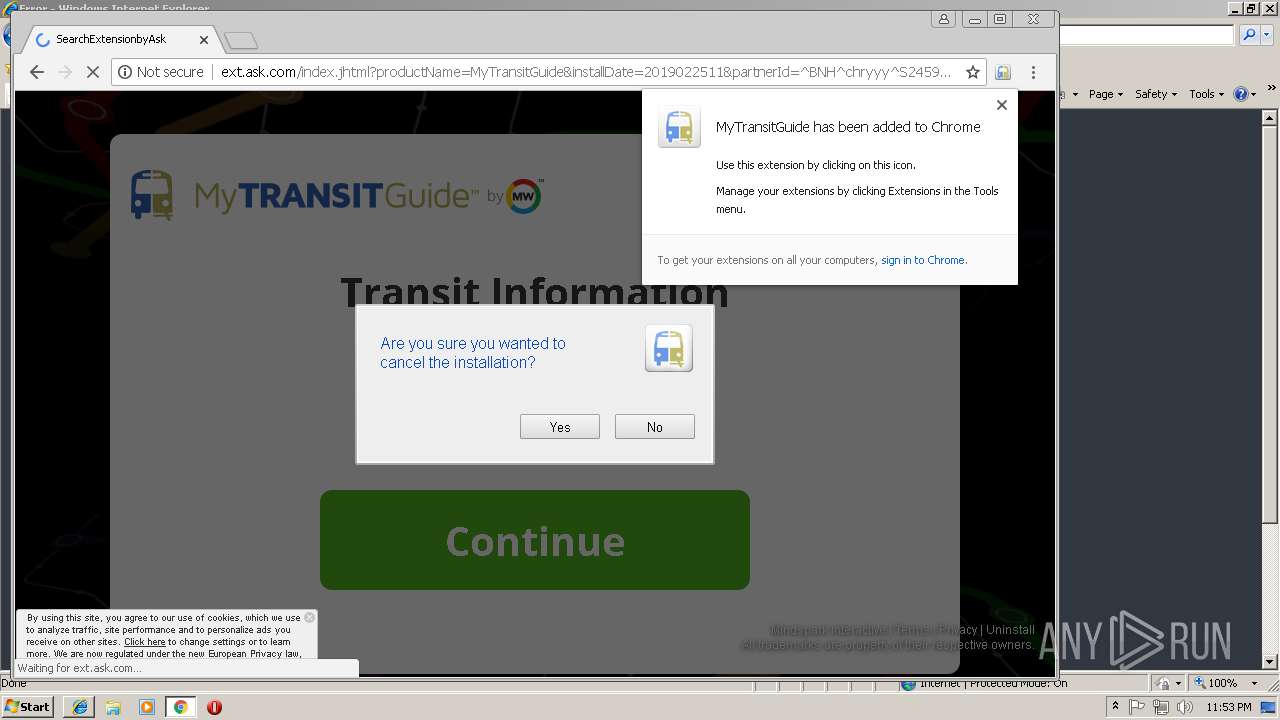
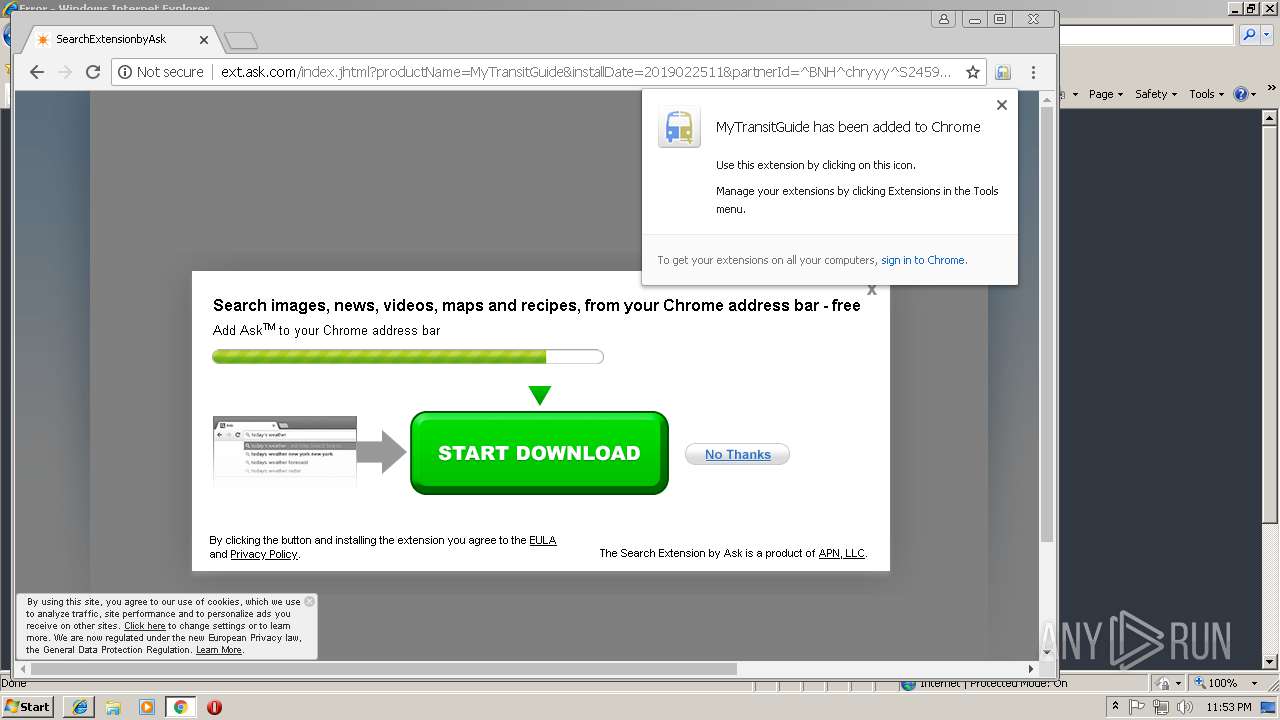
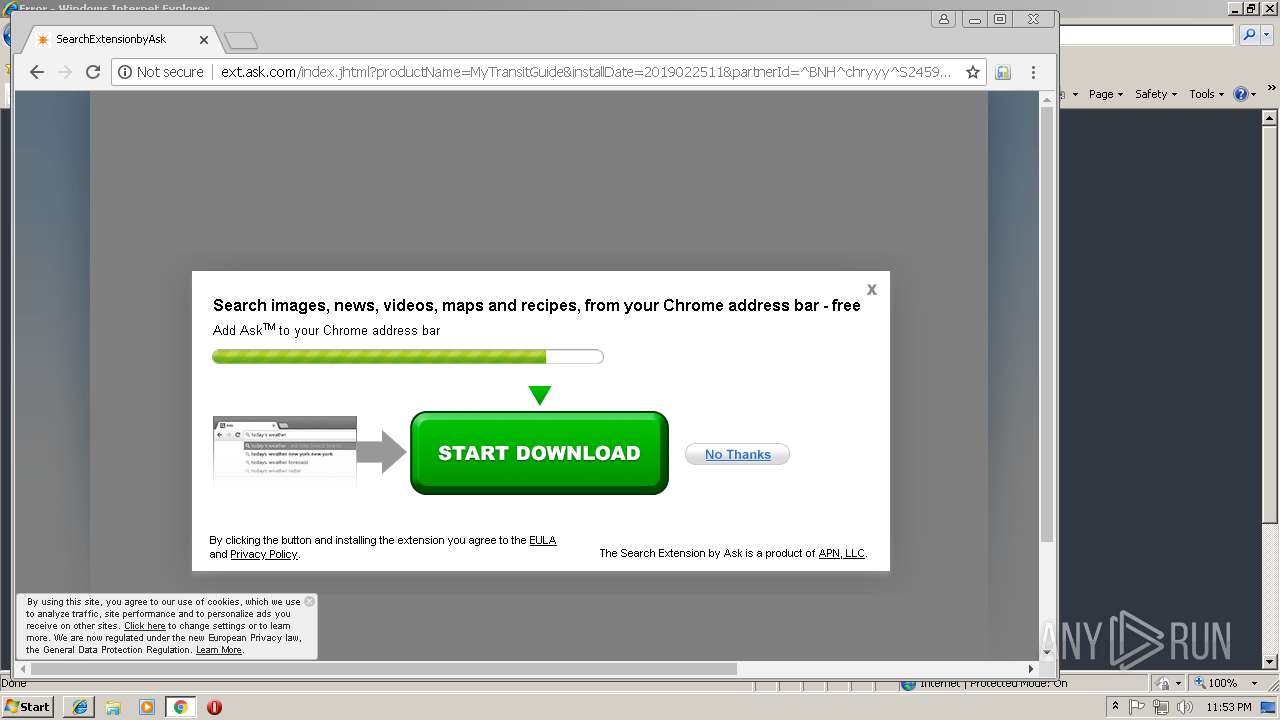
| URL: | http://mytransitguide.com |
| Full analysis: | https://app.any.run/tasks/5fbcf840-622e-4d80-b15c-21bba54e5112 |
| Verdict: | Malicious activity |
| Analysis date: | February 25, 2019, 23:52:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 98654ABFFFC8F95B3C38E571B3E79221 |
| SHA1: | 9E84B11FA9F08B85020095B01C5DC6E04F3E3263 |
| SHA256: | D2C9EB990B85AC8DFA144FDD2247F5CAFB98577C2625911198AE4ED8DF58B1F7 |
| SSDEEP: | 3:N1KT7LRJ2n:CDRs |
MALICIOUS
No malicious indicators.SUSPICIOUS
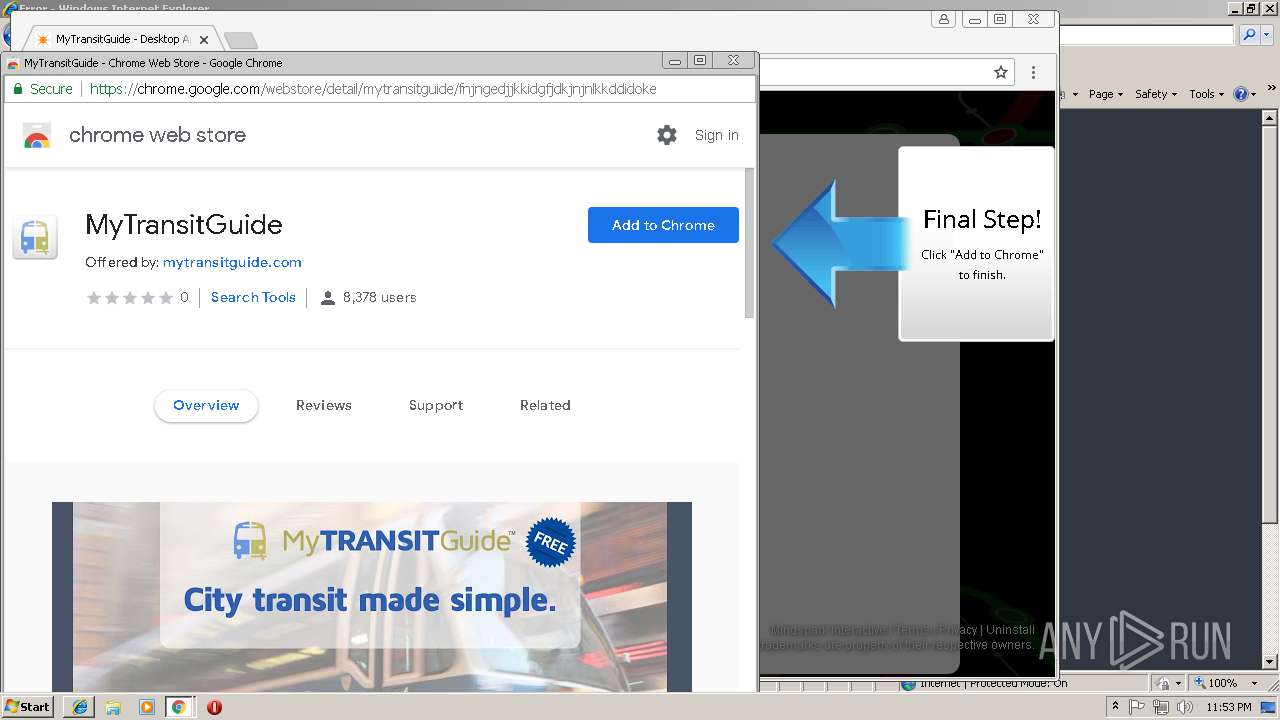
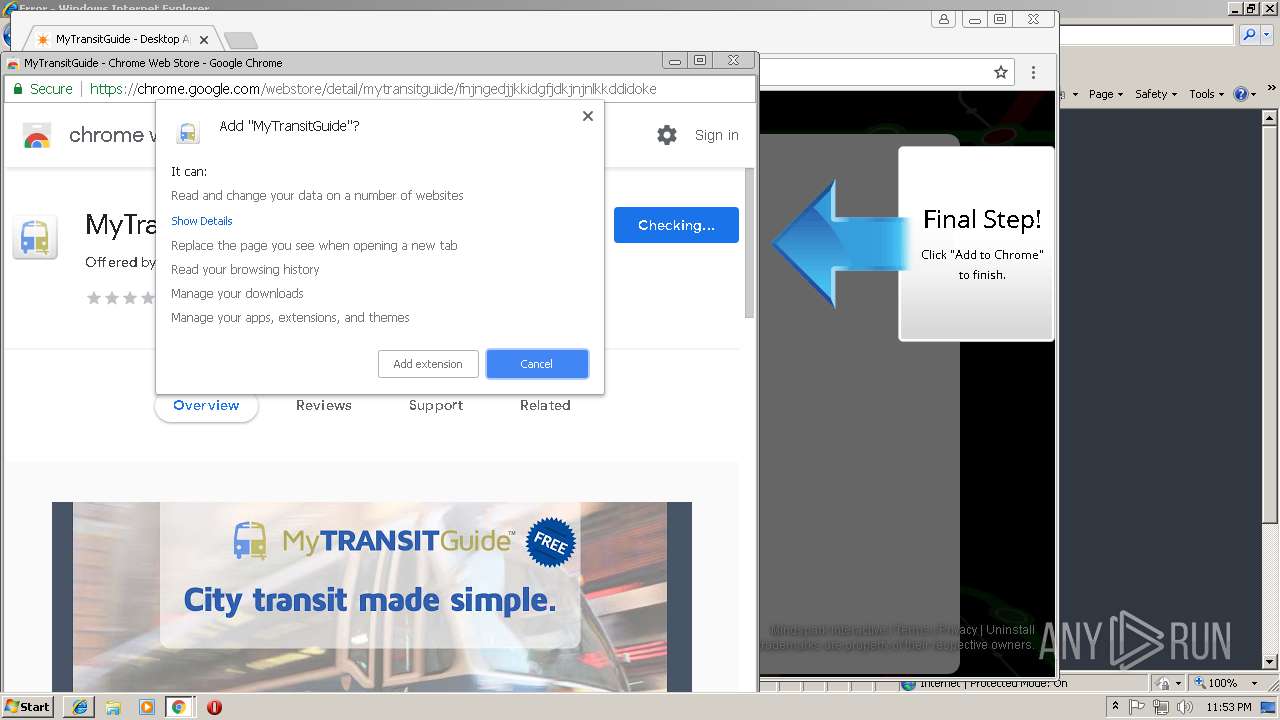
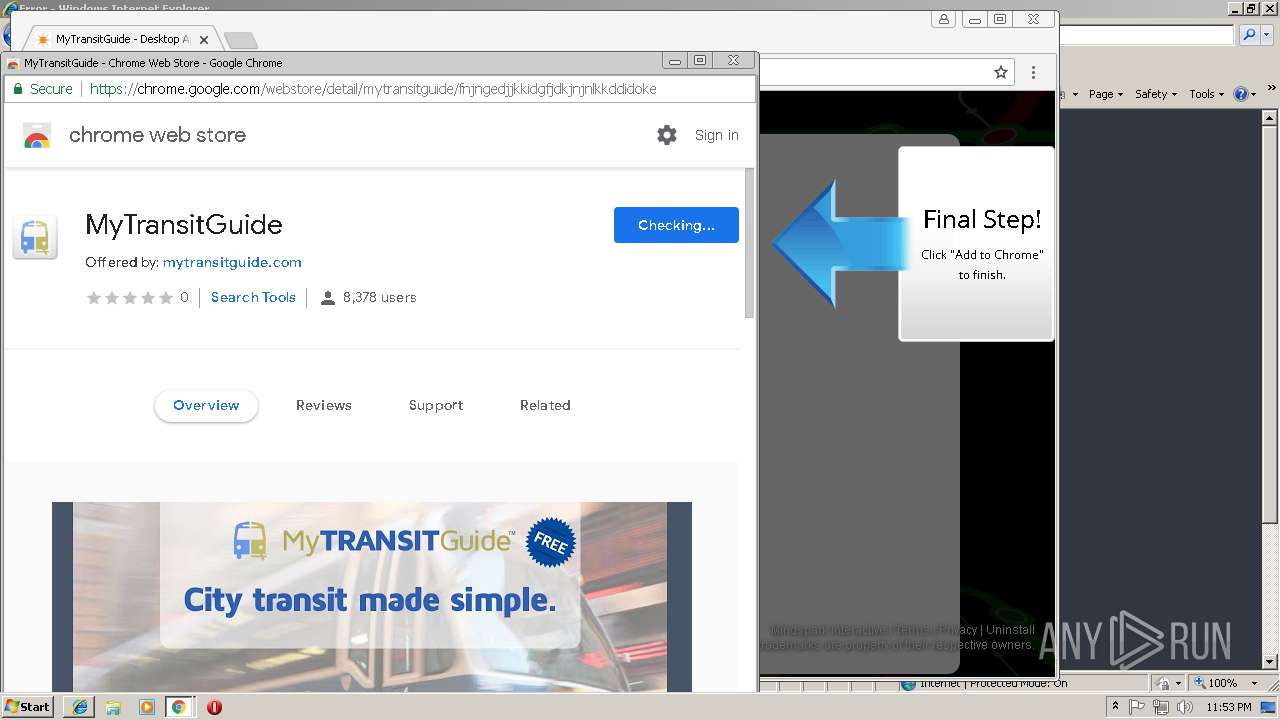
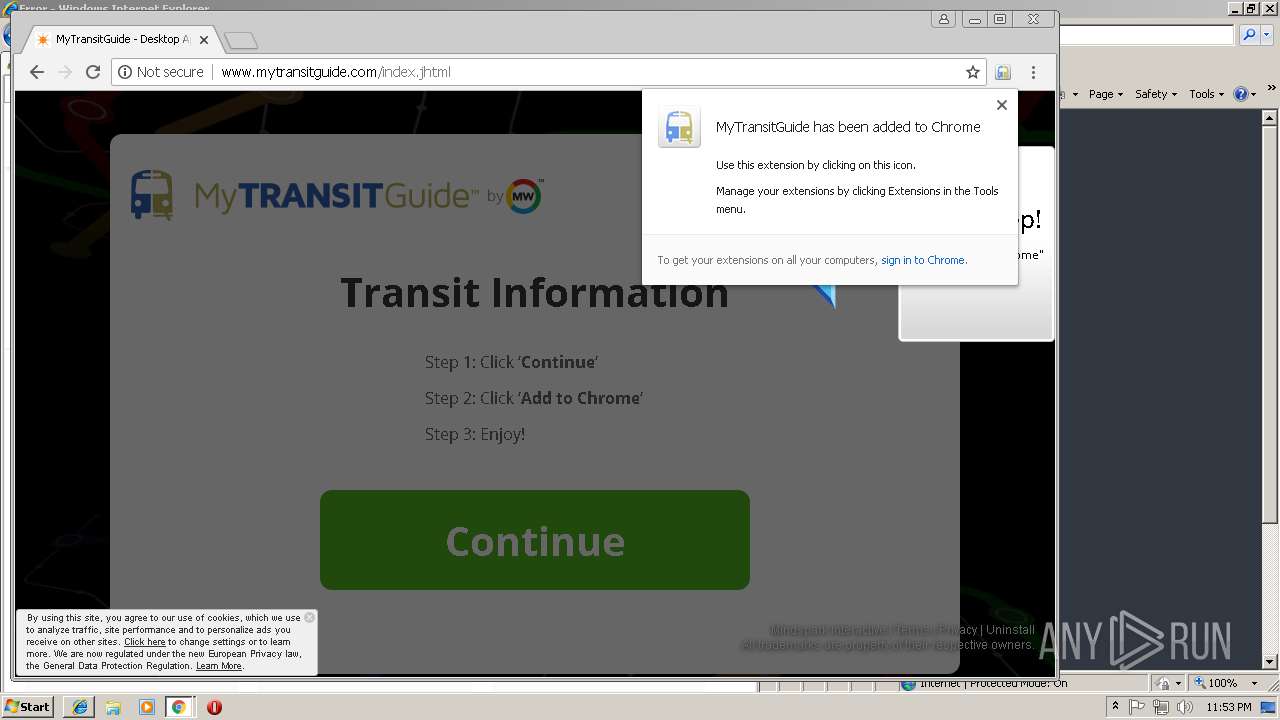
Modifies files in Chrome extension folder
- chrome.exe (PID: 3772)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3220)
- iexplore.exe (PID: 2860)
- chrome.exe (PID: 3772)
Creates files in the user directory
- iexplore.exe (PID: 3220)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3468)
- iexplore.exe (PID: 2860)
Changes internet zones settings
- iexplore.exe (PID: 2860)
Reads internet explorer settings
- iexplore.exe (PID: 3220)
Application launched itself
- iexplore.exe (PID: 2860)
- chrome.exe (PID: 3772)
Reads settings of System Certificates
- chrome.exe (PID: 3772)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
56
Monitored processes
26
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2024 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,11888443782932172974,12728857008823790944,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=15F797B4323A362DC02CD97D9D77FB28 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15F797B4323A362DC02CD97D9D77FB28 --renderer-client-id=22 --mojo-platform-channel-handle=4656 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 | |||||||||||||||
| 2164 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,11888443782932172974,12728857008823790944,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=FA30B148ED23055D993292B8280A6D9B --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=FA30B148ED23055D993292B8280A6D9B --renderer-client-id=11 --mojo-platform-channel-handle=4444 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,11888443782932172974,12728857008823790944,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=692DEE080692050B71A82A92993220A4 --mojo-platform-channel-handle=4780 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2228 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3768 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,11888443782932172974,12728857008823790944,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=A55383DEECDB2EA3445D83FA5D79DD26 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=A55383DEECDB2EA3445D83FA5D79DD26 --renderer-client-id=19 --mojo-platform-channel-handle=4372 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,11888443782932172974,12728857008823790944,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7938D43E3720D34AC0CD3E52A5977397 --mojo-platform-channel-handle=3920 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,11888443782932172974,12728857008823790944,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=969A2CAB02582AFD9536558B225BF54F --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=969A2CAB02582AFD9536558B225BF54F --renderer-client-id=10 --mojo-platform-channel-handle=4264 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,11888443782932172974,12728857008823790944,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8C1573B4FD0020B3BF3AA093C8299FD7 --mojo-platform-channel-handle=3652 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,11888443782932172974,12728857008823790944,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=0D9283320FEF0B63C35A304AB3B57D14 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=0D9283320FEF0B63C35A304AB3B57D14 --renderer-client-id=8 --mojo-platform-channel-handle=3736 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6b3300b0,0x6b3300c0,0x6b3300cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
678
Read events
560
Write events
112
Delete events
6
Modification events
| (PID) Process: | (2860) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2860) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2860) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2860) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2860) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2860) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2860) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {678E16C5-3958-11E9-BAD8-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2860) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2860) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (2860) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E307020001001900170034001C009901 | |||
Executable files
0
Suspicious files
65
Text files
97
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2860 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2860 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3220 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@mytransitguide[2].txt | — | |
MD5:— | SHA256:— | |||
| 3220 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\index[1].htm | — | |
MD5:— | SHA256:— | |||
| 3220 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\index[1].jhtml | — | |
MD5:— | SHA256:— | |||
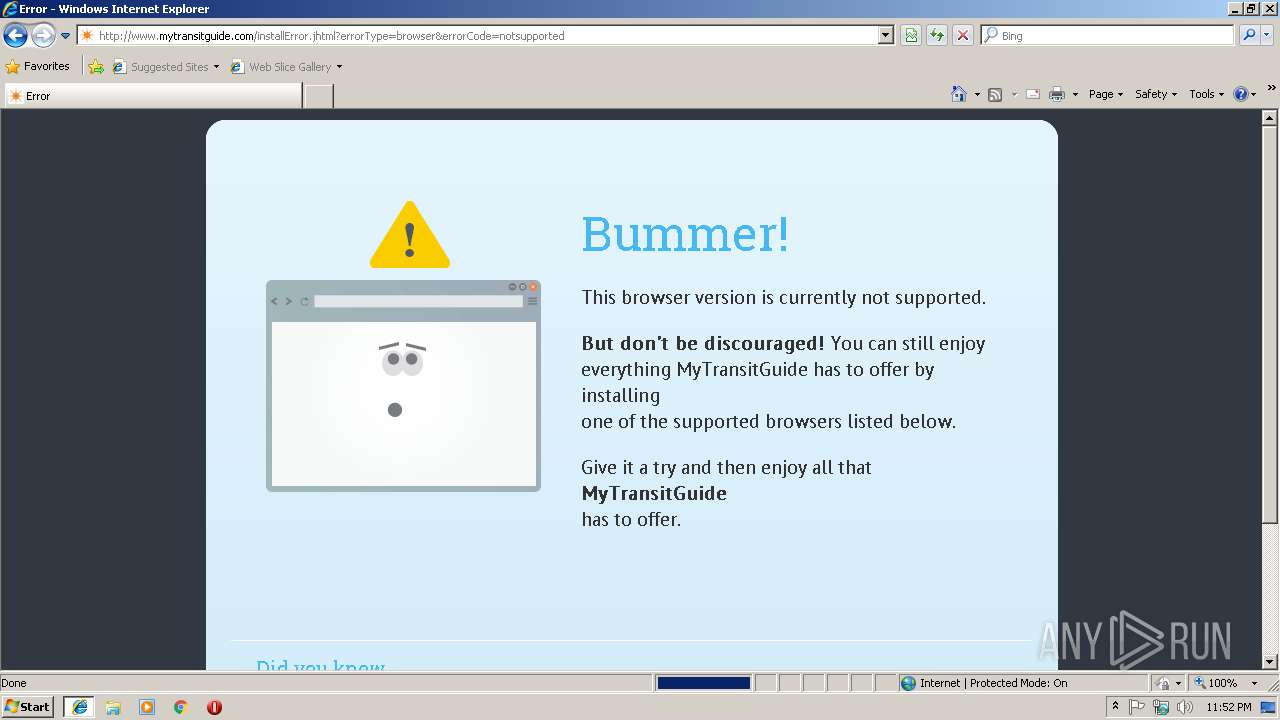
| 3220 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\installError[1].jhtml | — | |
MD5:— | SHA256:— | |||
| 3220 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@mytransitguide[1].txt | text | |
MD5:— | SHA256:— | |||
| 3220 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\installError[1].htm | html | |
MD5:— | SHA256:— | |||
| 3220 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\BWPPCY0O\365_icon_crx[1].png | image | |
MD5:— | SHA256:— | |||
| 3220 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\css[2].txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
74
TCP/UDP connections
108
DNS requests
73
Threats
89
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3772 | chrome.exe | GET | 301 | 74.113.235.138:80 | http://www.mytransitguide.com/ | IE | — | — | whitelisted |
3220 | iexplore.exe | GET | 301 | 74.113.235.138:80 | http://mytransitguide.com/ | IE | html | 238 b | whitelisted |
3220 | iexplore.exe | GET | 200 | 74.113.235.138:80 | http://www.mytransitguide.com/installError.jhtml?errorType=browser&errorCode=notsupported | IE | html | 20.0 Kb | whitelisted |
3220 | iexplore.exe | GET | 204 | 74.113.235.138:80 | http://www.mytransitguide.com/anemone.jhtml?anxuu=C9C04331-5D52-4345-8D20-82ECC8597495&anxa=CAPDownloadProcess&anxv=1.0.0&anxd=2011-06-01T04%3A00%3A00Z&anxsn=dubprdsndlbfe69.dub.jabodo.com&anxu=http%3A%2F%2Fwww.mytransitguide.com%2FinstallError.jhtml&anxl=en-US&anxlv=1551138750622&anxsq=3&errorCode=notsupported&errorType=browser&anxe=installErrorLanding&anxr=1110296211 | IE | compressed | 20.0 Kb | whitelisted |
3220 | iexplore.exe | GET | 200 | 172.217.18.170:80 | http://fonts.googleapis.com/css?family=PT+Sans | US | text | 164 b | whitelisted |
3220 | iexplore.exe | GET | 200 | 2.18.232.251:80 | http://ak.imgfarm.com/images/download/error/365_icon_crx.png | unknown | image | 5.46 Kb | whitelisted |
3772 | chrome.exe | GET | 301 | 74.113.235.138:80 | http://mytransitguide.com/ | IE | html | 238 b | whitelisted |
3220 | iexplore.exe | GET | 200 | 172.217.18.170:80 | http://fonts.googleapis.com/css?family=Roboto+Slab | US | text | 173 b | whitelisted |
3220 | iexplore.exe | GET | 301 | 74.113.235.138:80 | http://www.mytransitguide.com/ | IE | — | — | whitelisted |
3220 | iexplore.exe | GET | 204 | 74.113.235.138:80 | http://www.mytransitguide.com/anemone.jhtml?anxuu=C9C04331-5D52-4345-8D20-82ECC8597495&anxa=CAPDownloadProcess&anxv=1.0.0&anxd=2011-06-01T04%3A00%3A00Z&anxsn=dubprdsndlbfe69.dub.jabodo.com&anxu=http%3A%2F%2Fwww.mytransitguide.com%2FinstallError.jhtml&anxl=en-US&anxlv=1551138749827&anxrd=none&anxrp=-&anxrk=-&anxrm=-&anxrb=-&anxrc=-&anxrs=-&anxsq=1&anxi=DE24AF3F-F6E5-4917-B1BB-8BE950FDB07E&anxe=backFill&anxr=454497369 | IE | compressed | 20.0 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3220 | iexplore.exe | 172.217.18.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2860 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3220 | iexplore.exe | 172.217.22.67:80 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2860 | iexplore.exe | 74.113.235.138:80 | mytransitguide.com | Mindspark Interactive Network, Inc. | IE | malicious |
3220 | iexplore.exe | 2.18.232.251:443 | akz.imgfarm.com | Akamai International B.V. | — | whitelisted |
3772 | chrome.exe | 172.217.16.131:443 | www.google.de | Google Inc. | US | whitelisted |
3772 | chrome.exe | 172.217.21.234:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3772 | chrome.exe | 172.217.16.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3772 | chrome.exe | 172.217.21.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3772 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
mytransitguide.com |
| whitelisted |
www.mytransitguide.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
akz.imgfarm.com |
| whitelisted |
ak.imgfarm.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.google.de |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3772 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |