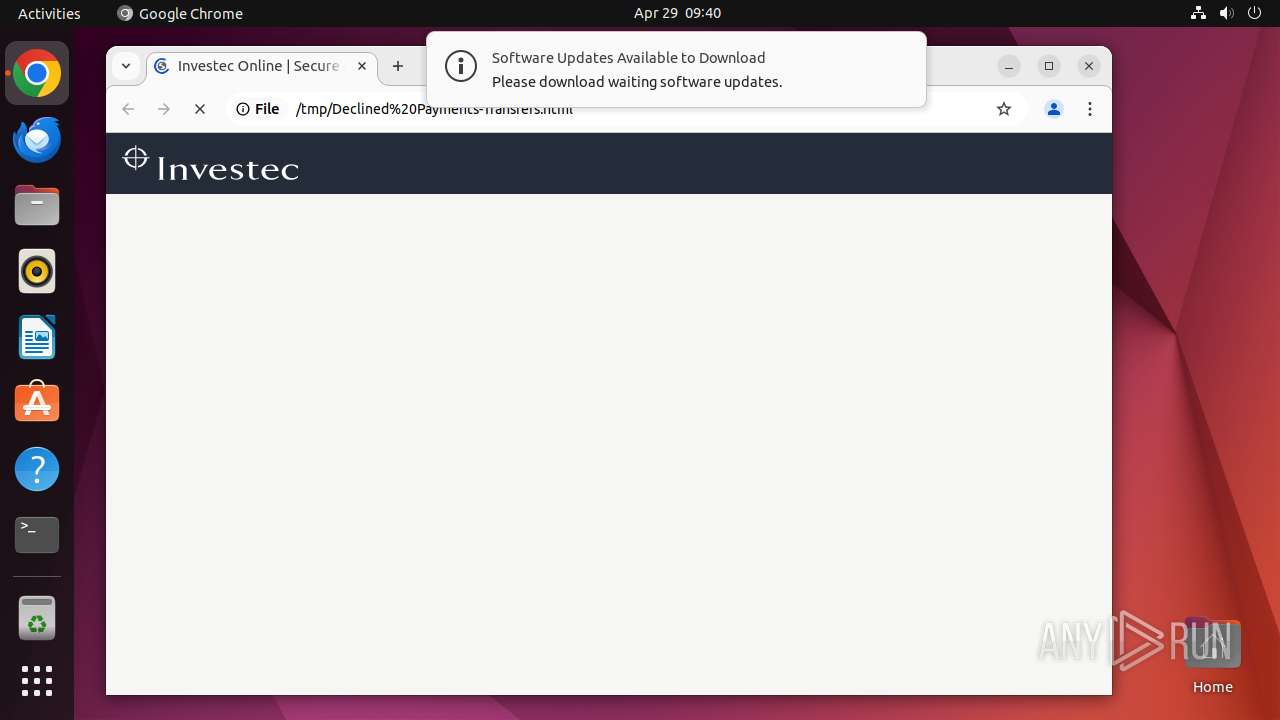
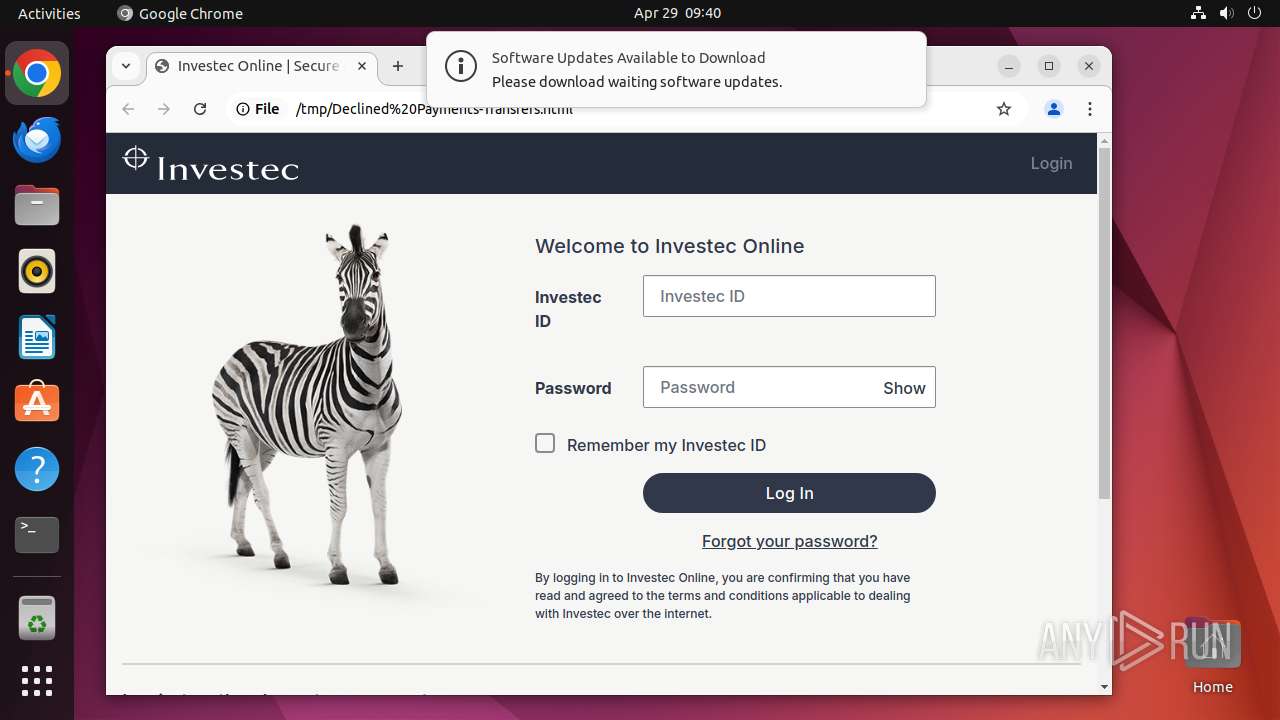
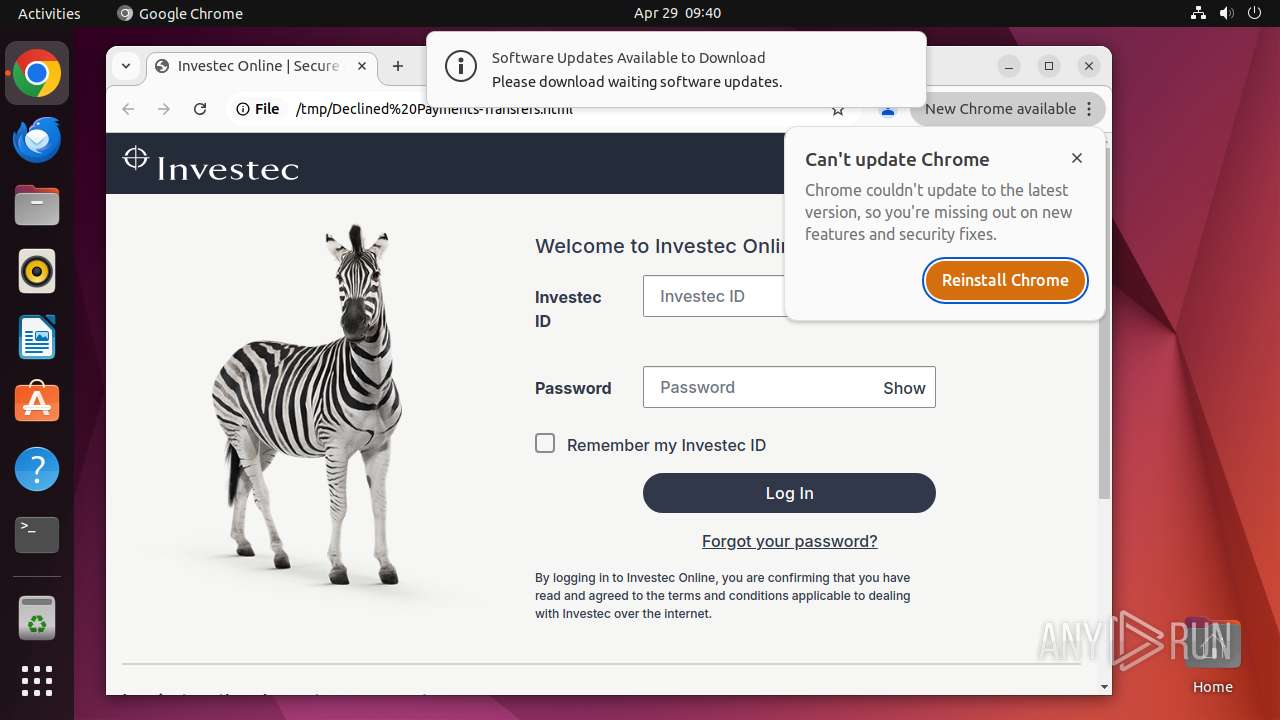
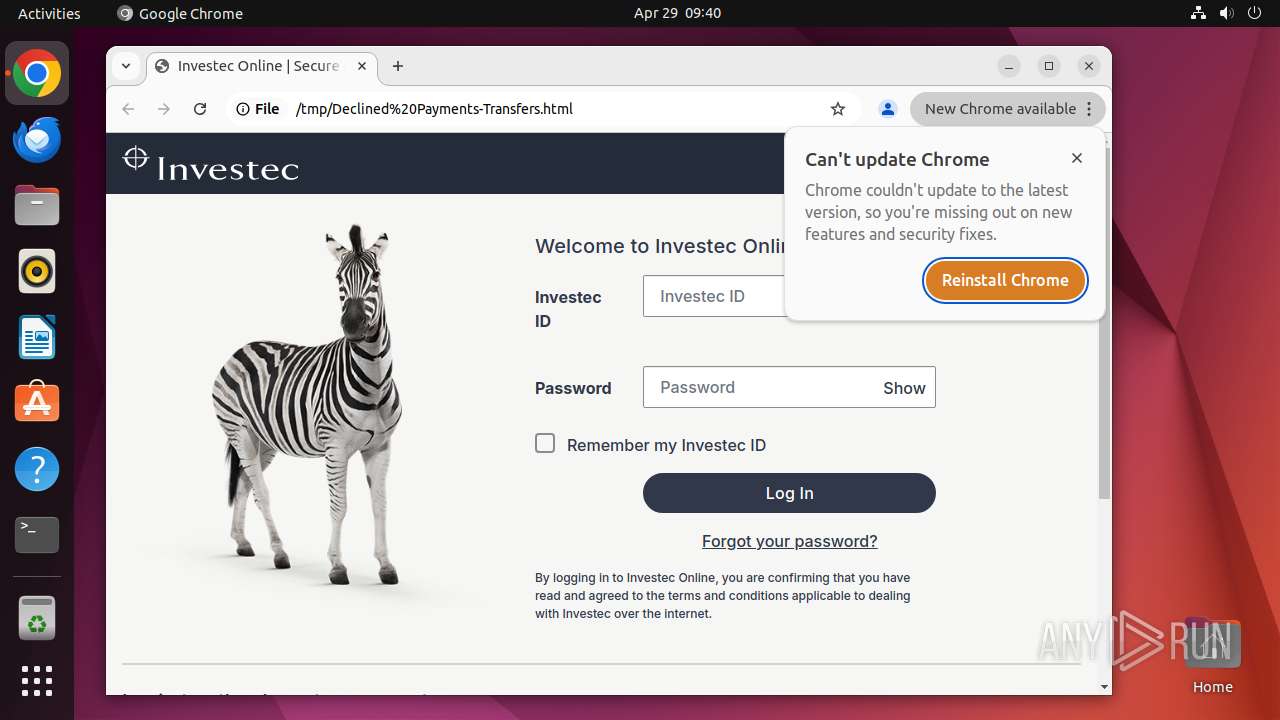
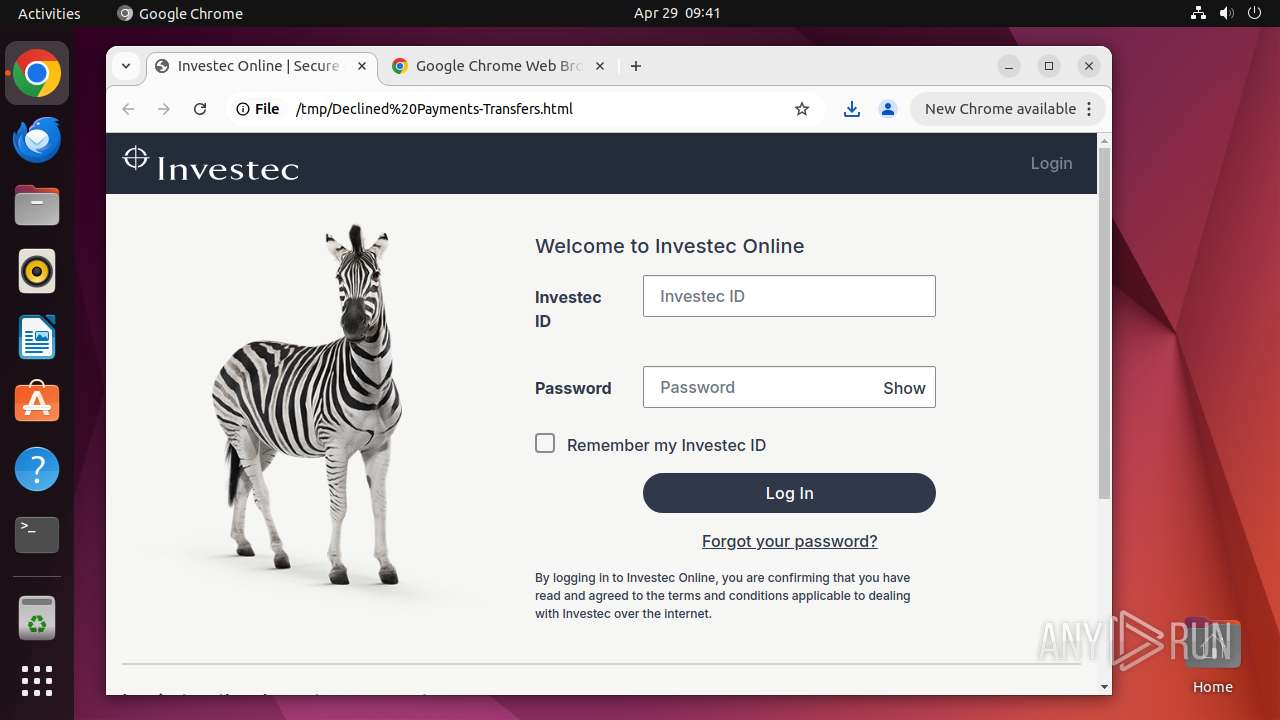
| File name: | Declined Payments-Transfers.html |
| Full analysis: | https://app.any.run/tasks/1cd8bc9d-00b4-45dc-8e3f-8f4e33fa70a0 |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 08:39:59 |
| OS: | Ubuntu 22.04.2 |
| Tags: | |
| MIME: | application/javascript |
| File info: | JavaScript source, Unicode text, UTF-8 text, with very long lines (65498), with no line terminators |
| MD5: | 4F6B23CB5F6203F7975E9C2D232EC439 |
| SHA1: | 8FEEC61ADB005A32AC34992D8E5AFE174A59111C |
| SHA256: | D2BD9ADBF722A8054EC69212212B53FCE391E305DFDDCEA6F652271664F6B903 |
| SSDEEP: | 1536:aPbI1loaXicG7lVFzjUXiup6PrGJlBL+CQ79773a:4sUaXiplVFjUXz6PrGlJYNe |
MALICIOUS
No malicious indicators.SUSPICIOUS
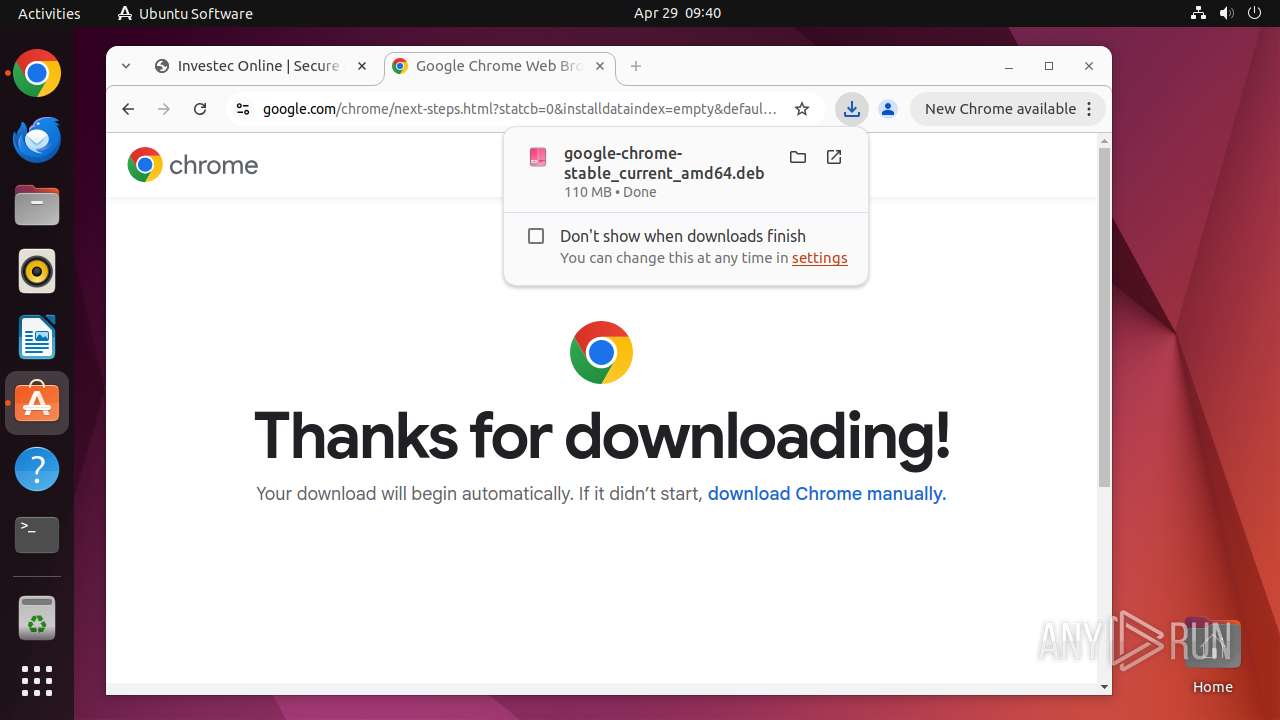
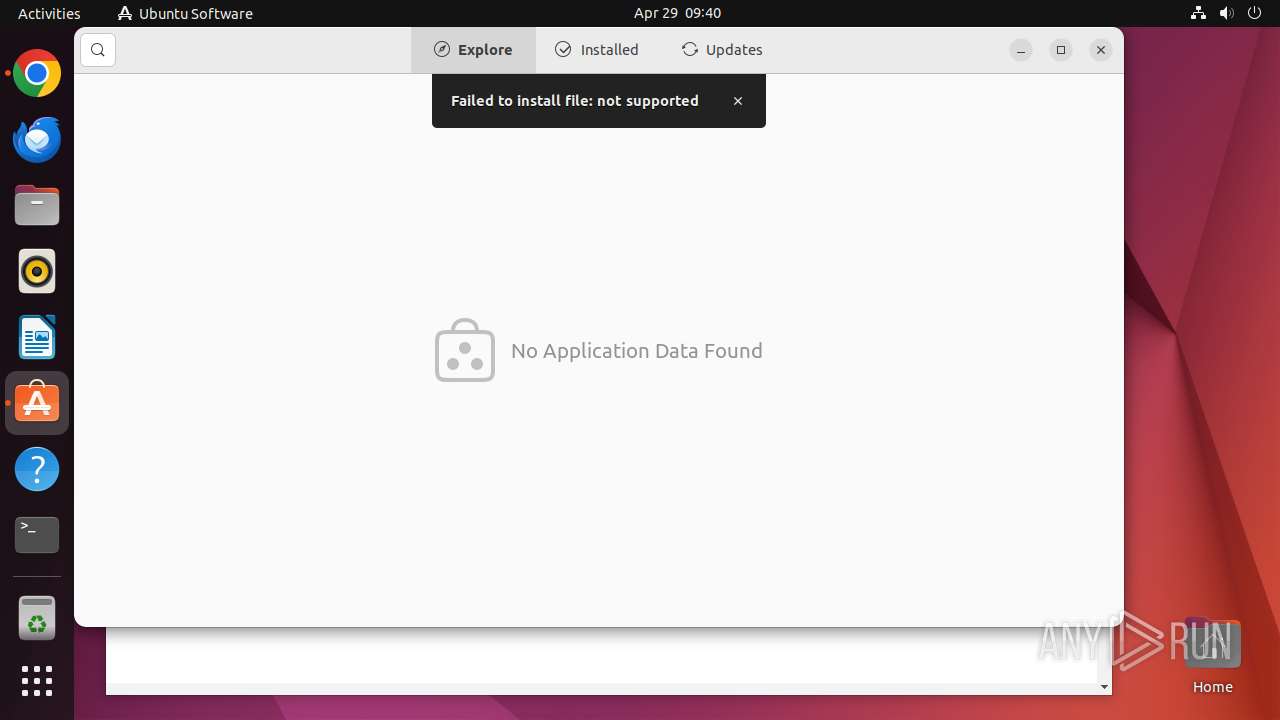
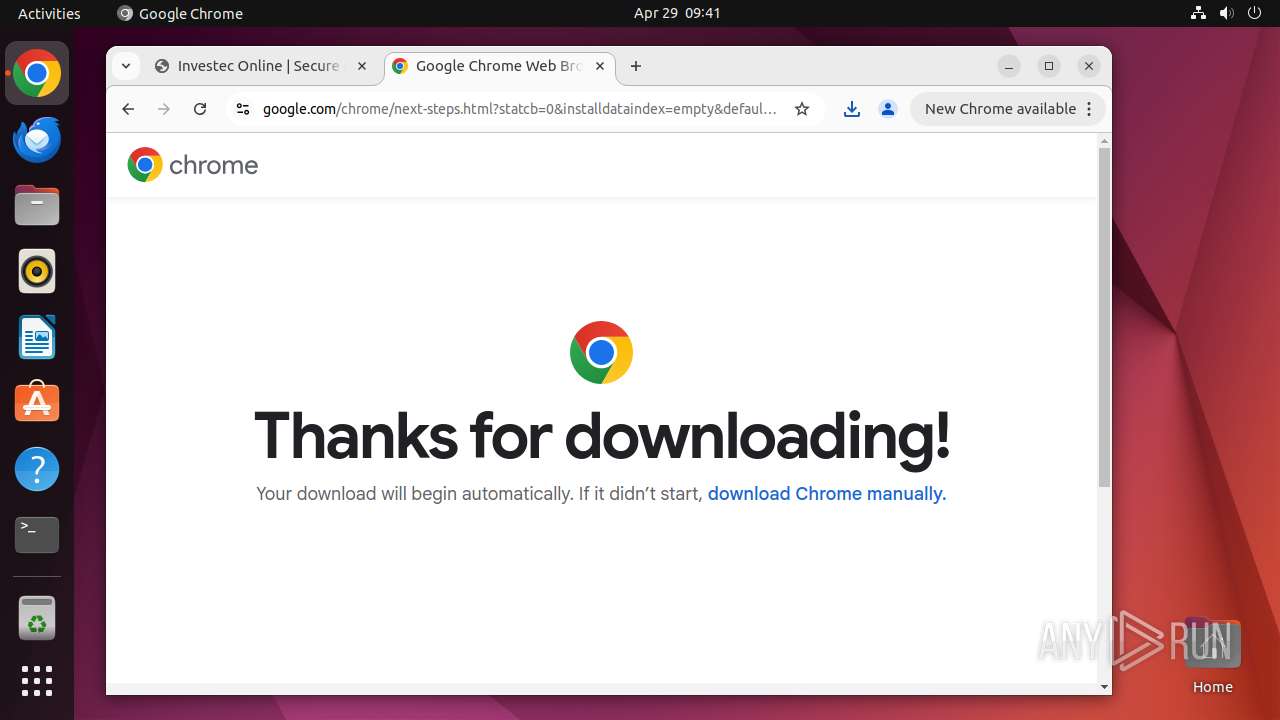
Executes commands using command-line interpreter
- chrome (PID: 40667)
- sudo (PID: 40664)
- gio (PID: 40954)
Checks for external IP
- systemd-resolved (PID: 445)
- chrome (PID: 40714)
Check the Environment Variables Related to System Identification (os-release)
- snapctl (PID: 41003)
- snapctl (PID: 40997)
- snap-store (PID: 40955)
Reads /proc/mounts (likely used to find writable filesystems)
- snap-store (PID: 40955)
INFO
Checks timezone
- chrome (PID: 40667)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
366
Monitored processes
147
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 445 | /lib/systemd/systemd-resolved | /usr/lib/systemd/systemd-resolved | systemd | |
User: systemd-resolve Integrity Level: UNKNOWN | ||||
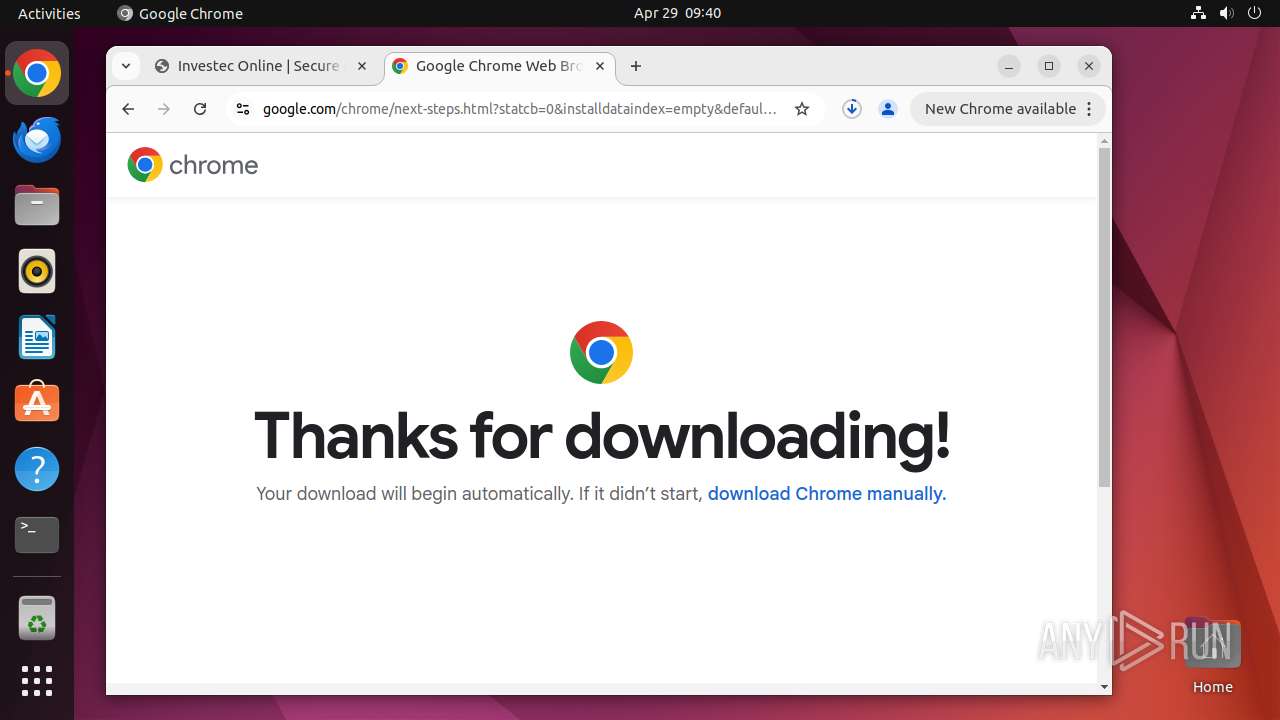
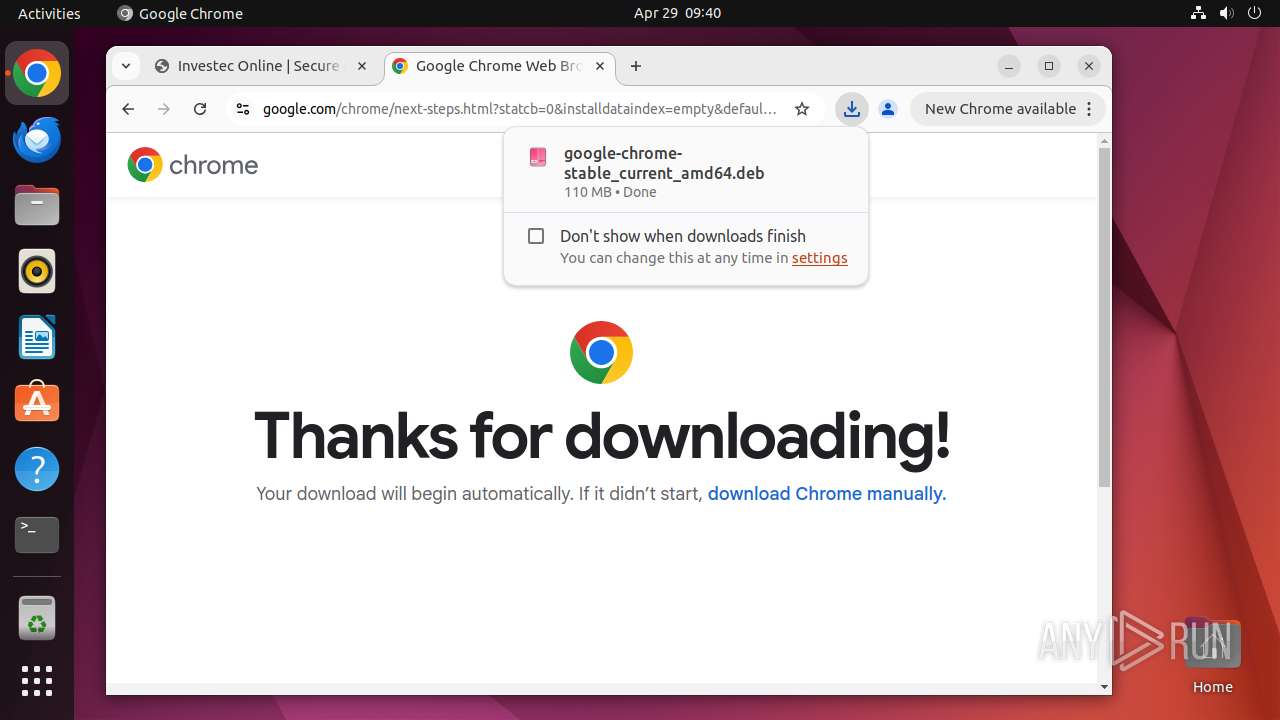
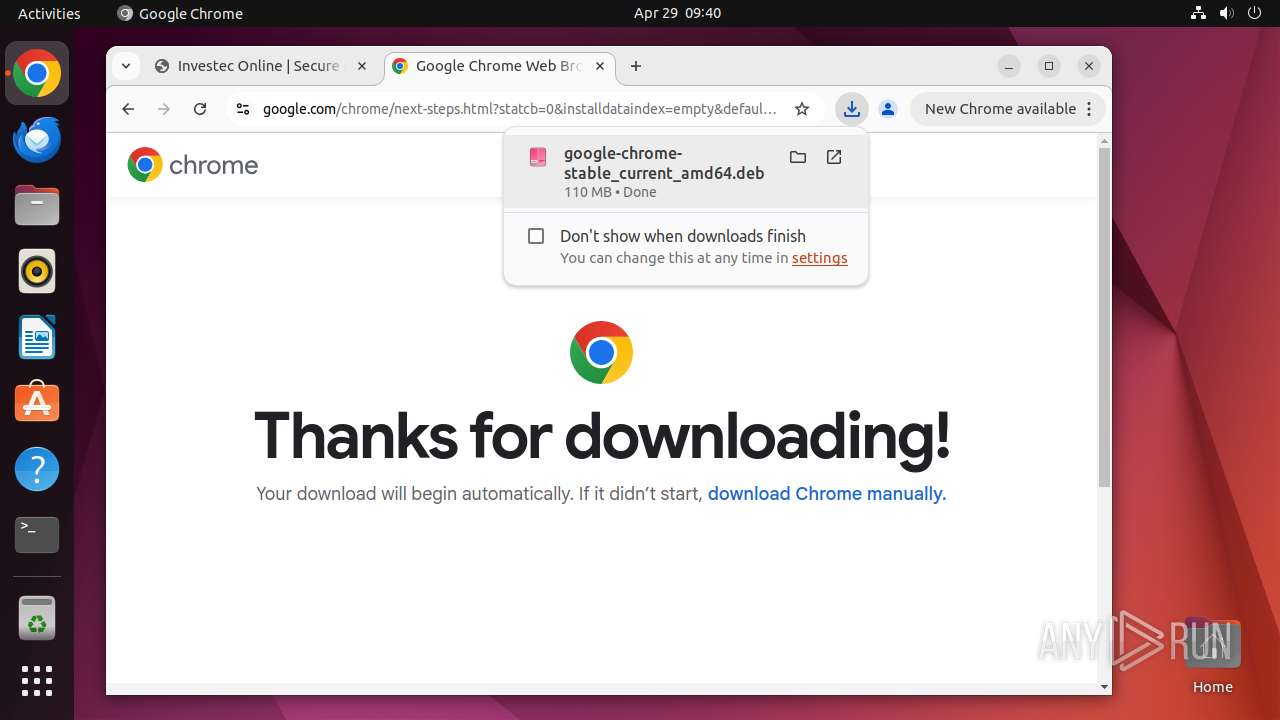
| 40663 | /bin/sh -c "DISPLAY=:0 sudo -iu user google-chrome \"/tmp/Declined Payments-Transfers\.html\" " | /usr/bin/dash | — | any-guest-agent |
User: user Integrity Level: UNKNOWN | ||||
| 40664 | sudo -iu user google-chrome "/tmp/Declined Payments-Transfers\.html" | /usr/bin/sudo | — | dash |
User: root Integrity Level: UNKNOWN | ||||
| 40665 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40666 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40667 | /usr/bin/google-chrome "/tmp/Declined Payments-Transfers\.html" | /opt/google/chrome/chrome | — | sudo |
User: user Integrity Level: UNKNOWN | ||||
| 40668 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40669 | readlink -f /usr/bin/google-chrome | /usr/bin/readlink | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40670 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40671 | mkdir -p /home/user/.local/share/applications | /usr/bin/mkdir | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
Executable files
12
Suspicious files
296
Text files
25
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 40667 | chrome | /home/user/.config/google-chrome/ShaderCache/data_3 | binary | |
MD5:— | SHA256:— | |||
| 40667 | chrome | /home/user/.config/google-chrome/ShaderCache/data_2 | binary | |
MD5:— | SHA256:— | |||
| 40667 | chrome | /home/user/.config/google-chrome/ShaderCache/data_0 | binary | |
MD5:— | SHA256:— | |||
| 40667 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_3 | binary | |
MD5:— | SHA256:— | |||
| 40667 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_2 | binary | |
MD5:— | SHA256:— | |||
| 40667 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_0 | binary | |
MD5:— | SHA256:— | |||
| 40711 | chrome | /home/user/.cache/mesa_shader_cache/index | binary | |
MD5:— | SHA256:— | |||
| 40804 | chrome | /home/user/.cache/mesa_shader_cache/index | binary | |
MD5:— | SHA256:— | |||
| 40667 | chrome | /home/user/.config/google-chrome/Default/History | binary | |
MD5:— | SHA256:— | |||
| 40667 | chrome | /home/user/.config/google-chrome/Default/DawnWebGPUCache/data_3 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
64
DNS requests
70
Threats
74
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 185.125.190.48:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
40714 | chrome | GET | 200 | 185.186.25.167:80 | http://185.186.25.167/plesk-site-preview/etc.com/https/185.186.25.167/index_files/styles.c993622b9e4bfbee.css | unknown | — | — | unknown |
40714 | chrome | GET | 200 | 185.186.25.167:80 | http://185.186.25.167/plesk-site-preview/etc.com/https/185.186.25.167/index_files/jquery.min.js | unknown | — | — | unknown |
40714 | chrome | GET | 200 | 185.186.25.167:80 | http://185.186.25.167/plesk-site-preview/etc.com/https/185.186.25.167/index_files/main.1ec89ebf36fc9acd.css | unknown | — | — | unknown |
40714 | chrome | GET | 200 | 185.186.25.167:80 | http://185.186.25.167/plesk-site-preview/etc.com/https/185.186.25.167/index_files/logo.svg | unknown | — | — | unknown |
40714 | chrome | GET | 200 | 185.186.25.167:80 | http://185.186.25.167/plesk-site-preview/etc.com/https/185.186.25.167/index_files/interface-search.svg | unknown | — | — | unknown |
40714 | chrome | GET | 200 | 185.186.25.167:80 | http://185.186.25.167/plesk-site-preview/etc.com/https/185.186.25.167/index_files/code.svg | unknown | — | — | unknown |
40714 | chrome | GET | 200 | 185.186.25.167:80 | http://185.186.25.167/plesk-site-preview/etc.com/https/185.186.25.167/index_files/interface-insights.svg | unknown | — | — | unknown |
40714 | chrome | GET | 200 | 185.186.25.167:80 | http://185.186.25.167/plesk-site-preview/etc.com/https/185.186.25.167/index_files/interface-favourite-default.svg | unknown | — | — | unknown |
40714 | chrome | GET | 200 | 185.186.25.167:80 | http://185.186.25.167/plesk-site-preview/etc.com/https/185.186.25.167/index_files/nav-profile-settings.svg | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 185.125.190.48:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | whitelisted |
— | — | 195.181.175.41:443 | odrs.gnome.org | Datacamp Limited | DE | whitelisted |
484 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 185.125.188.54:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
— | — | 185.125.188.55:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
512 | snapd | 185.125.188.55:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
512 | snapd | 185.125.188.59:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
40714 | chrome | 142.250.186.138:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
40714 | chrome | 142.250.185.195:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
40714 | chrome | 64.233.184.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
connectivity-check.ubuntu.com |
| whitelisted |
odrs.gnome.org |
| whitelisted |
google.com |
| whitelisted |
api.snapcraft.io |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
ipinfo.io |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
40714 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40714 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40714 | chrome | Device Retrieving External IP Address Detected | ET INFO Possible External IP Lookup Domain Observed in SNI (ipinfo. io) |
445 | systemd-resolved | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ipinfo .io) |
445 | systemd-resolved | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ipinfo .io) |
40714 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40714 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40714 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40714 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40714 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |