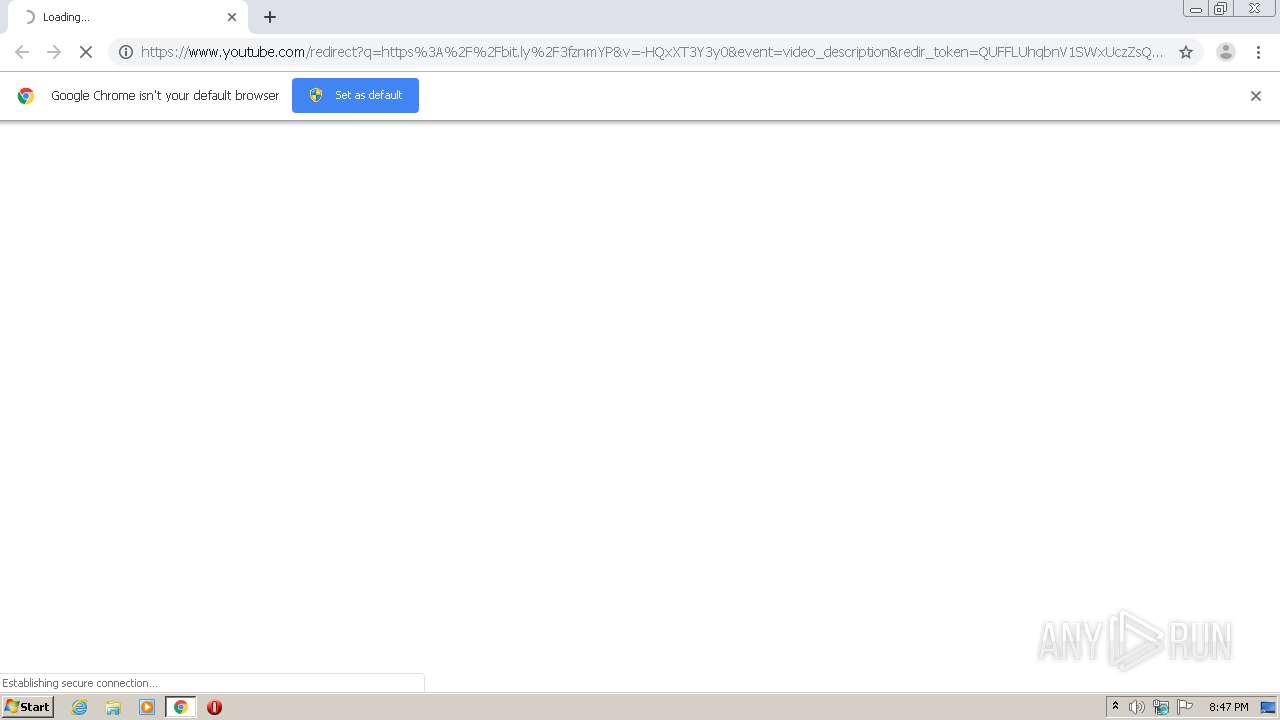
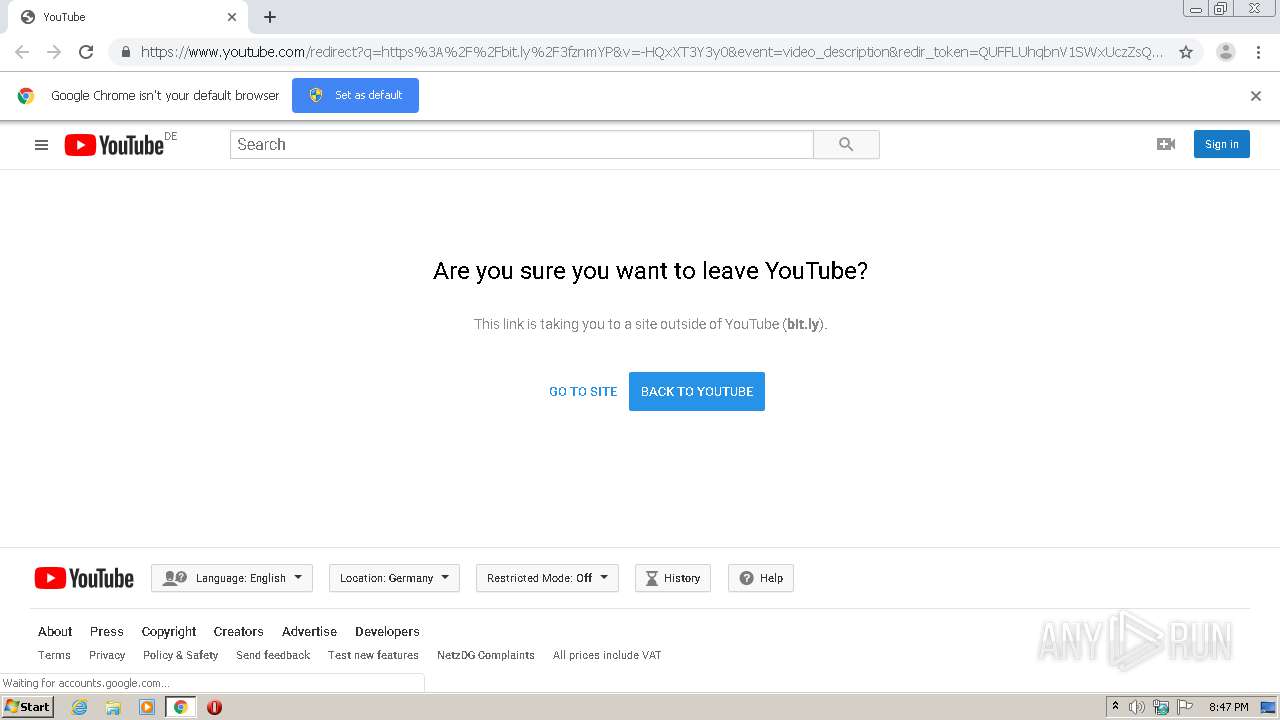
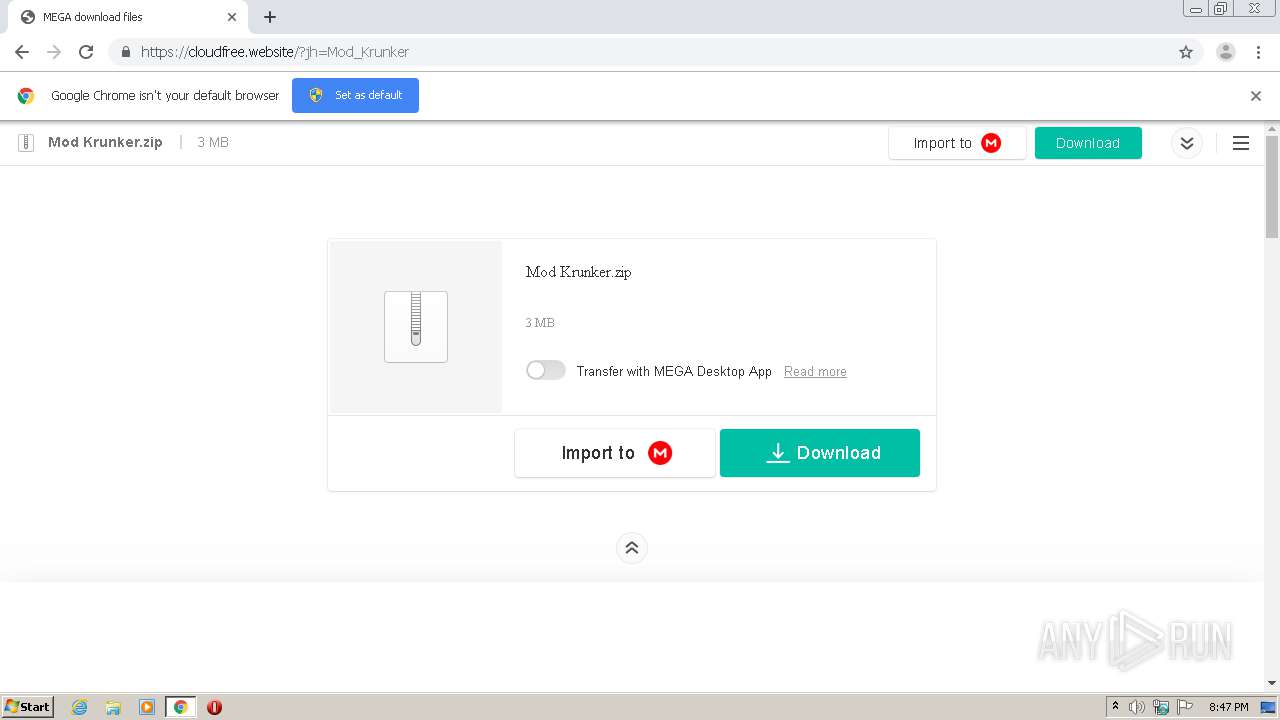
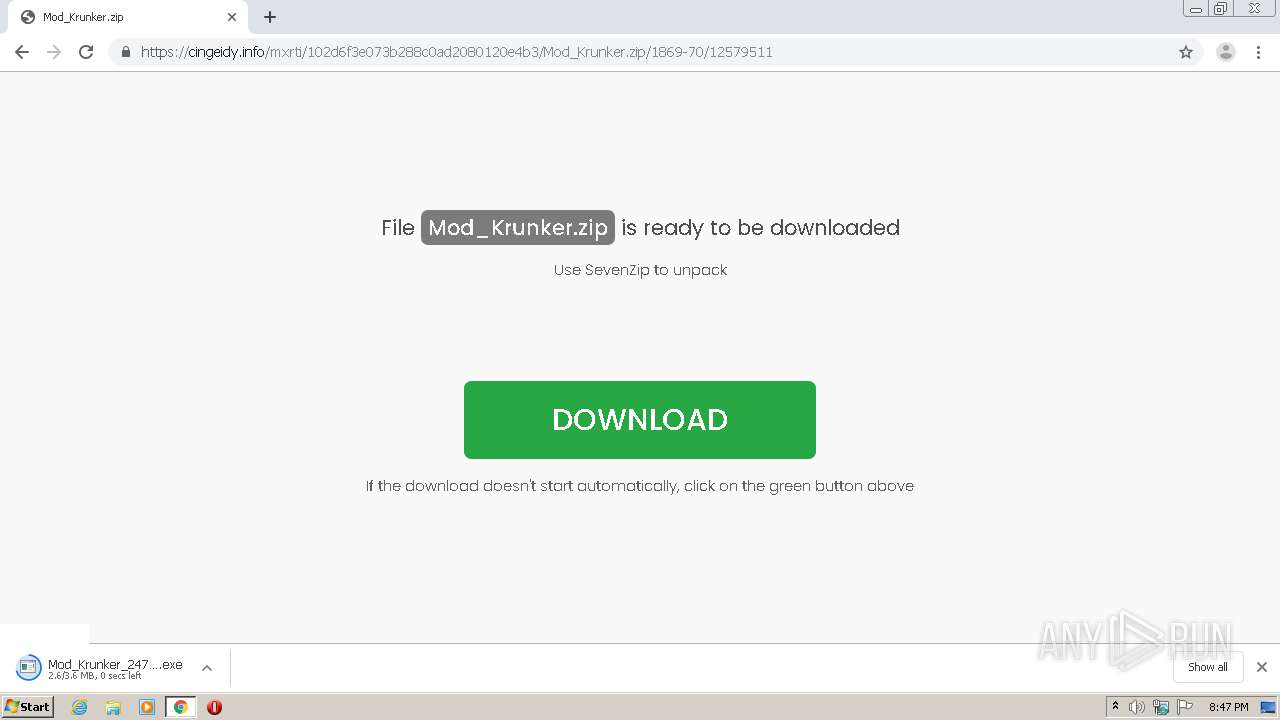
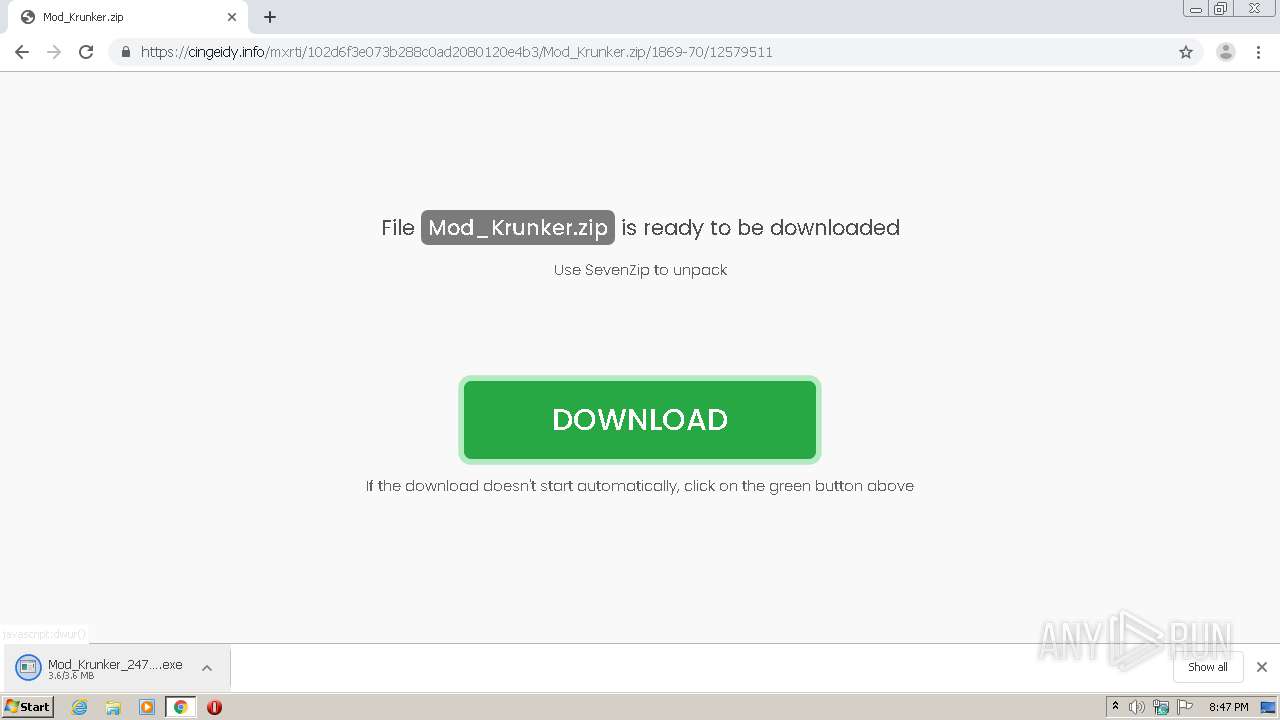
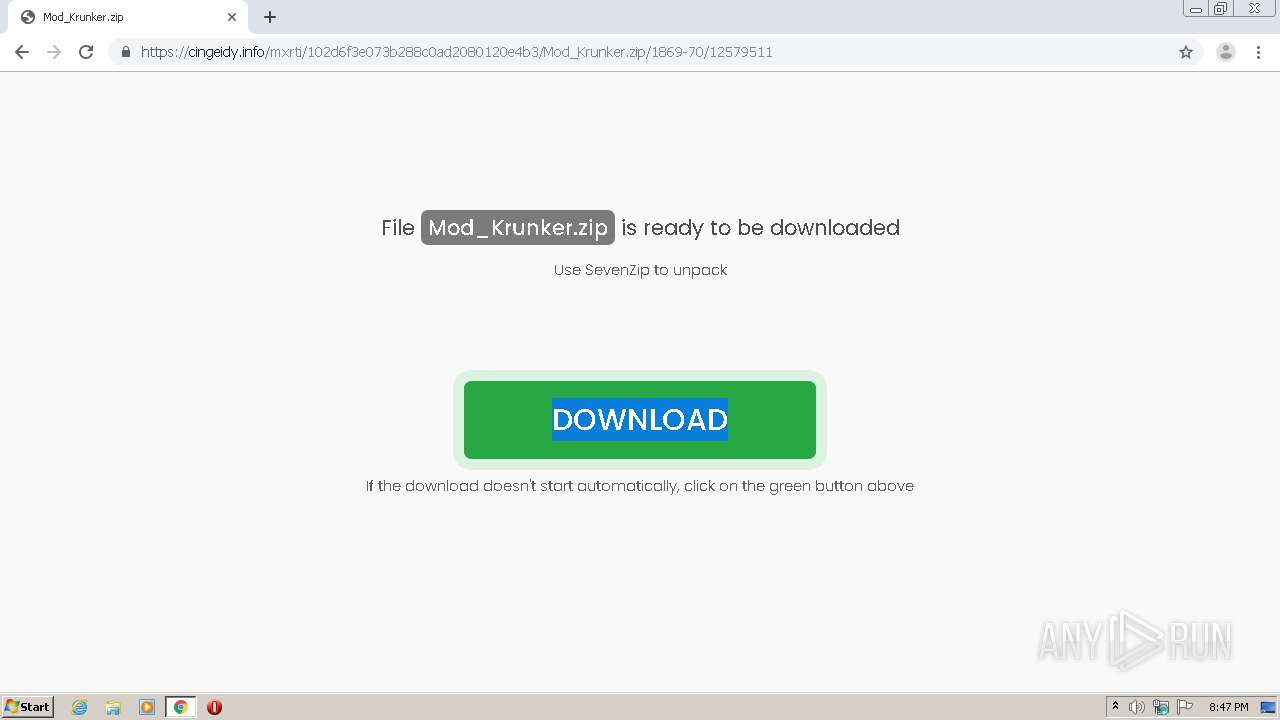
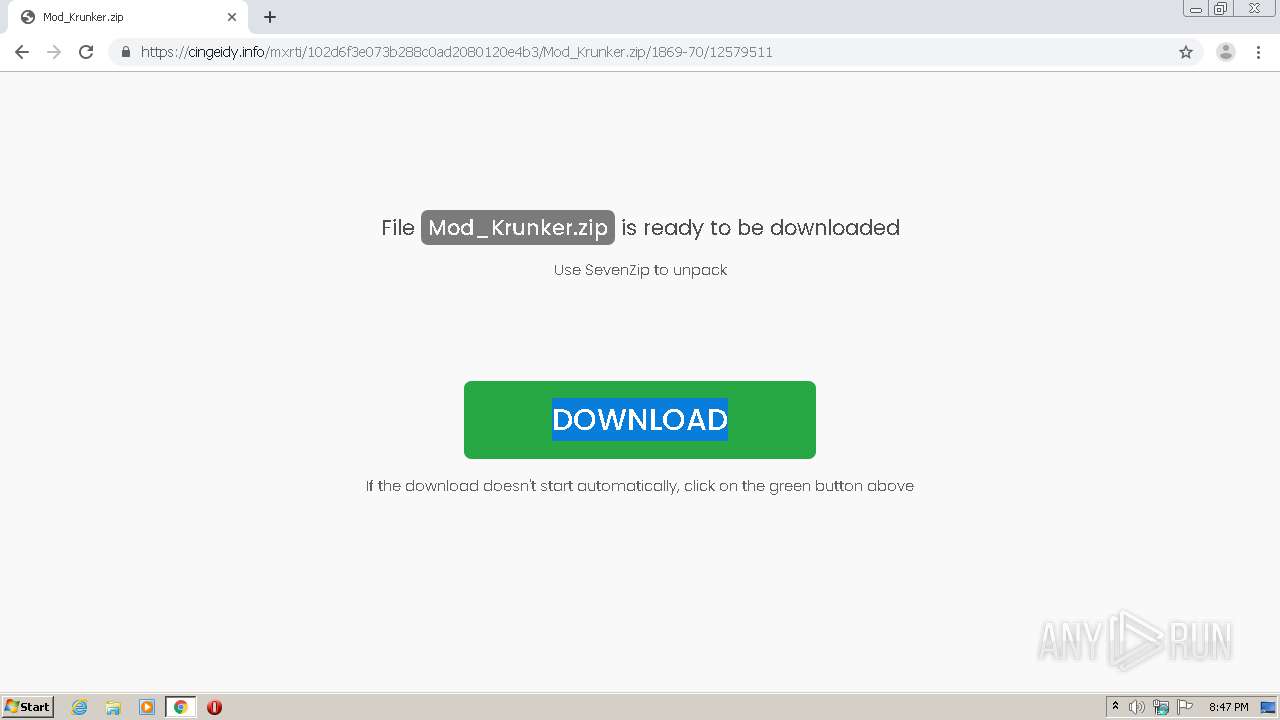
| URL: | https://www.youtube.com/redirect?q=https%3A%2F%2Fbit.ly%2F3fznmYP&v=-HQxXT3Y3y0&event=video_description&redir_token=QUFFLUhqbnV1SWxUczZsQzdKc2JPblpUZWdVZlFSSmdid3xBQ3Jtc0trYkw1MDdsRkJwWURYUGZ6MmU5dmRjX25VVTVzZVM0bWd0OHpBMjNYVUdDdDdQV3E4RWZBd2ZxRndXdk9rSThuTXVCLWVHWGxnaGRYSHE0WXJGOXJpWmw4dUtQVFRKVGVJUmpPUWg3bWJnY1piUmVzbw%3D%3D |
| Full analysis: | https://app.any.run/tasks/7a3bb321-ccc1-4a02-8f5d-c94b78867649 |
| Verdict: | Malicious activity |
| Analysis date: | July 31, 2020, 19:46:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | D366BF81F3EE931C3DEB1D576A6AB889 |
| SHA1: | 091DF46EF71C50A437373F82089B84E4554030C4 |
| SHA256: | D2B622F6EC2D47647F407F5926067C1AF1B5252189D1AEB9C31D1DE579B41EE8 |
| SSDEEP: | 6:2OLUxGKW5zsYy4DPl9RLqZUhR1pa43bixscxhKWgQMtk9eY7azfS:2jG1YYbDPloUh9y7xhNgO9eYT |
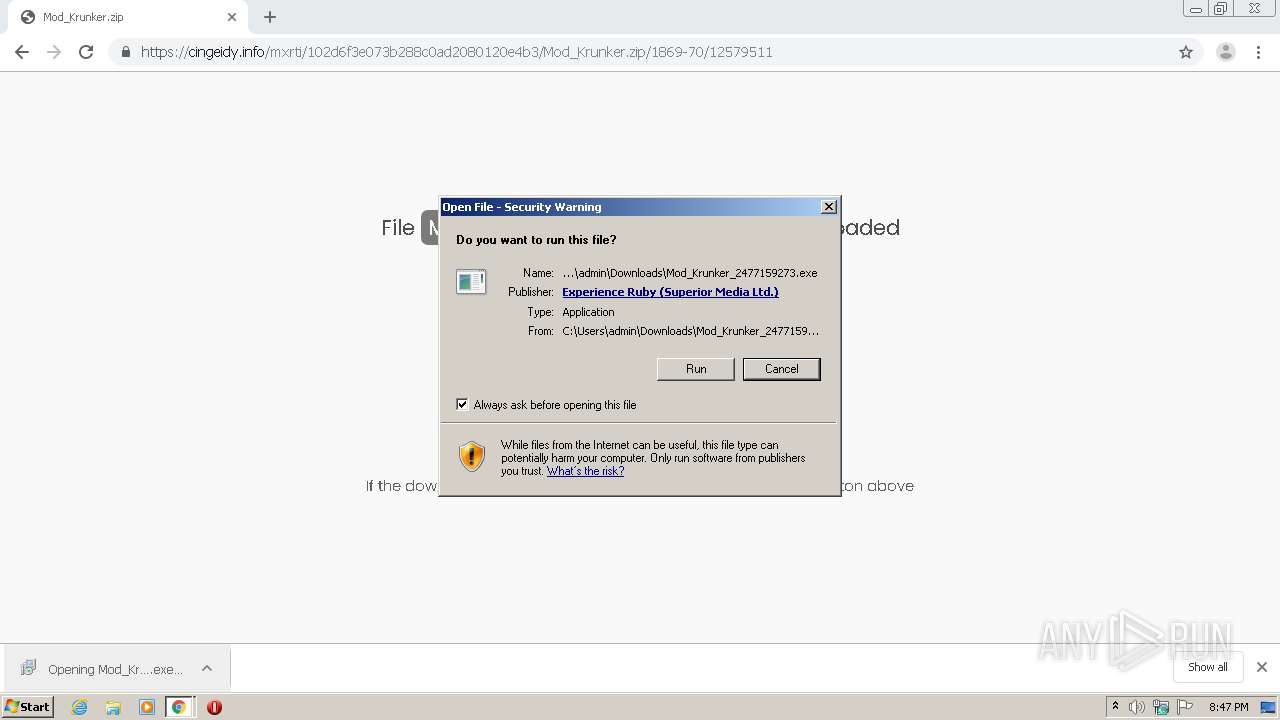
MALICIOUS
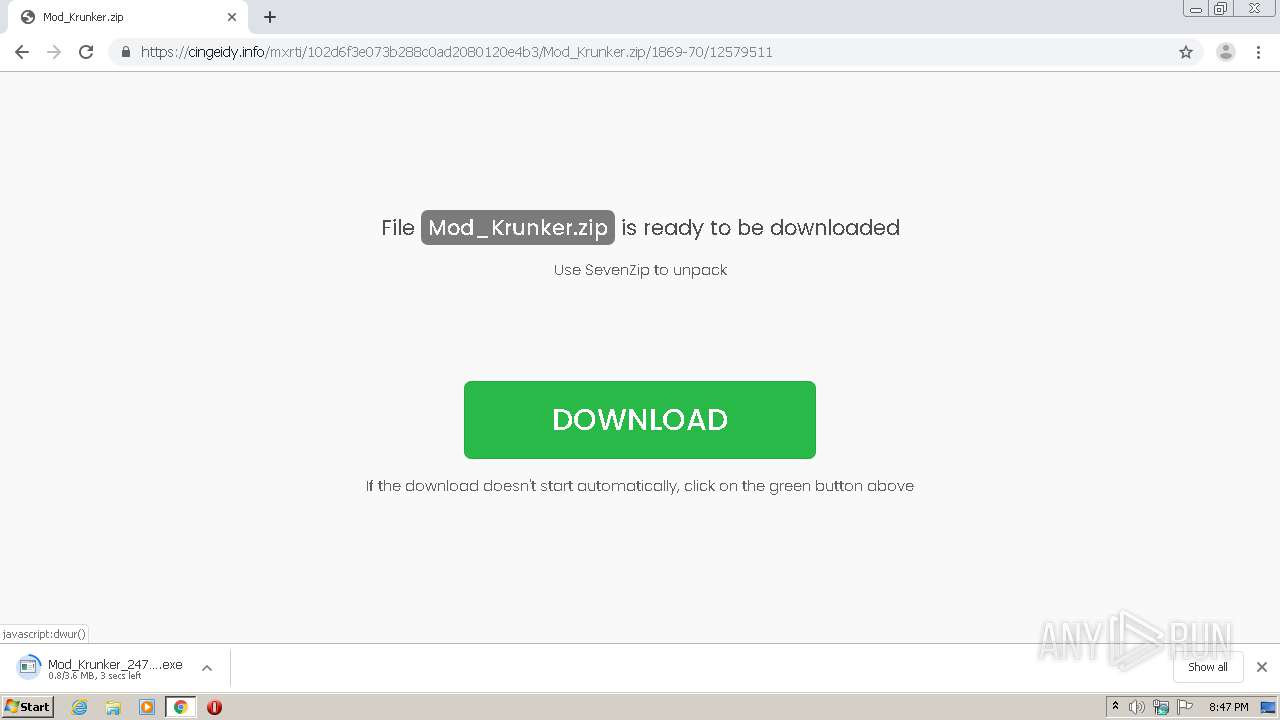
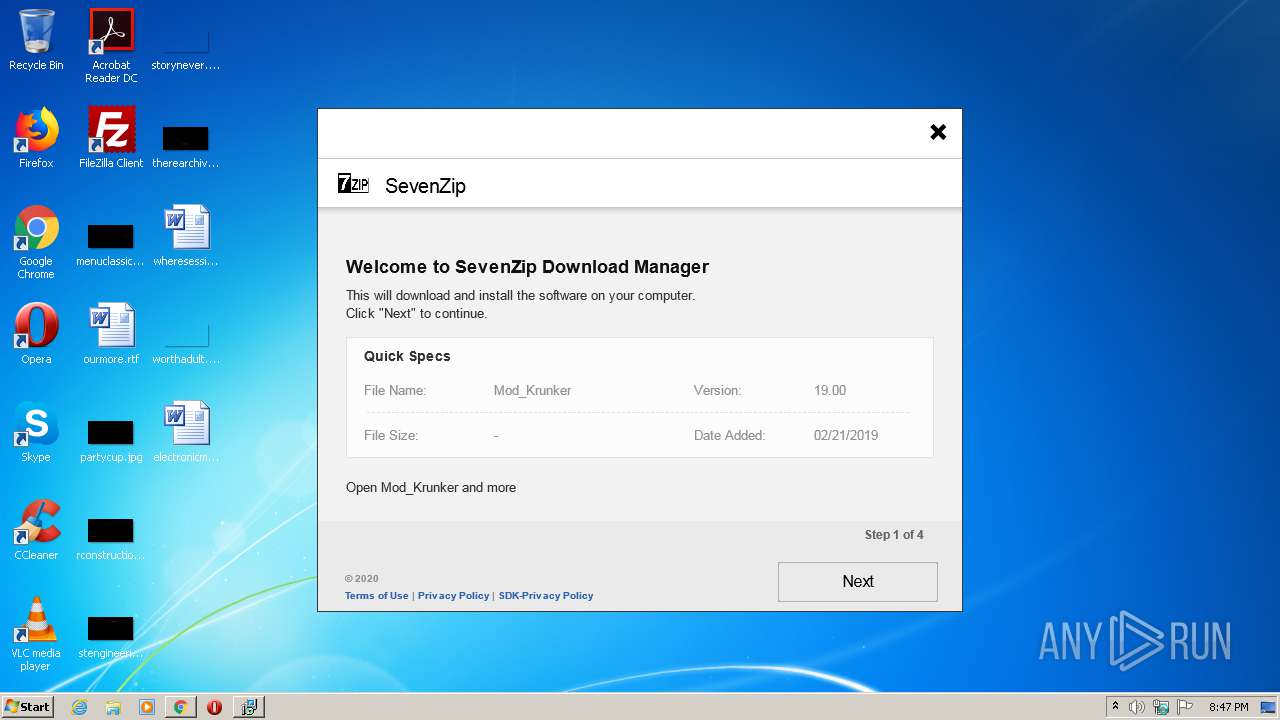
Loads dropped or rewritten executable
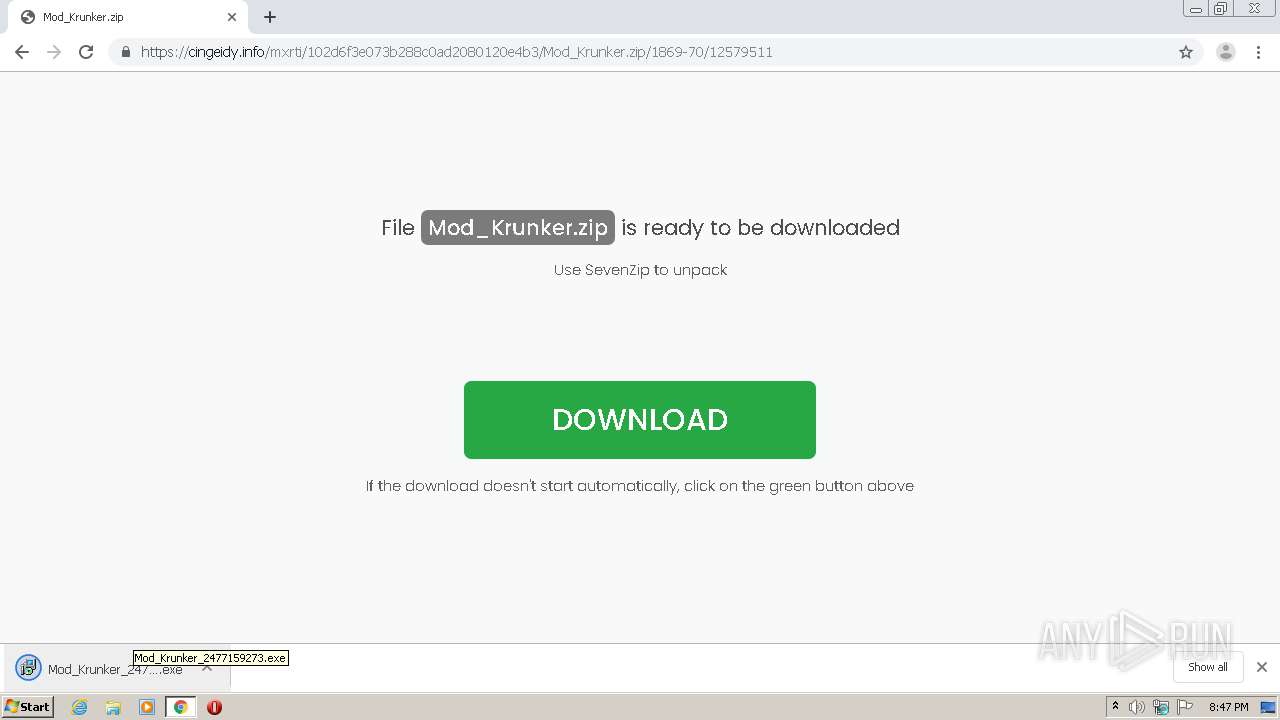
- Mod_Krunker_2477159273.exe (PID: 3200)
Actions looks like stealing of personal data
- Mod_Krunker_2477159273.exe (PID: 3200)
Application was dropped or rewritten from another process
- Mod_Krunker_2477159273.exe (PID: 1812)
- Mod_Krunker_2477159273.exe (PID: 3200)
SUSPICIOUS
Application launched itself
- Mod_Krunker_2477159273.exe (PID: 1812)
Cleans NTFS data-stream (Zone Identifier)
- Mod_Krunker_2477159273.exe (PID: 1812)
Executable content was dropped or overwritten
- chrome.exe (PID: 1724)
- chrome.exe (PID: 1496)
- Mod_Krunker_2477159273.exe (PID: 3200)
Reads Environment values
- Mod_Krunker_2477159273.exe (PID: 3200)
Reads internet explorer settings
- Mod_Krunker_2477159273.exe (PID: 3200)
INFO
Application launched itself
- chrome.exe (PID: 1724)
Reads the hosts file
- chrome.exe (PID: 1496)
- chrome.exe (PID: 1724)
Reads settings of System Certificates
- chrome.exe (PID: 1496)
Reads Internet Cache Settings
- chrome.exe (PID: 1724)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
66
Monitored processes
28
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1016,15921042826395965018,2790711063508149265,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=2759215902293476016 --mojo-platform-channel-handle=3152 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,15921042826395965018,2790711063508149265,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4323697183429086610 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2240 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1084 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,15921042826395965018,2790711063508149265,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15655821460192845263 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3908 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1156 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,15921042826395965018,2790711063508149265,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3715262734298065323 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3648 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,15921042826395965018,2790711063508149265,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=9225118844442946980 --mojo-platform-channel-handle=3836 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1472 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,15921042826395965018,2790711063508149265,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=9608774259782618112 --mojo-platform-channel-handle=4072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,15921042826395965018,2790711063508149265,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=2878540436220789373 --mojo-platform-channel-handle=1648 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1588 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,15921042826395965018,2790711063508149265,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7007091457136961516 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2248 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,15921042826395965018,2790711063508149265,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18119052087861113290 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2820 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,15921042826395965018,2790711063508149265,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=5433817390753267892 --mojo-platform-channel-handle=3172 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 326
Read events
1 145
Write events
176
Delete events
5
Modification events
| (PID) Process: | (1724) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1724) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1724) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1724) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1724) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2196) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1724-13240698427758875 |
Value: 259 | |||
| (PID) Process: | (1724) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1724) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1724) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1724) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
Executable files
6
Suspicious files
30
Text files
144
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFde2a0.TMP | — | |
MD5:— | SHA256:— | |||
| 1724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\21436cec-bd21-4581-8aae-483d11930ff6.tmp | — | |
MD5:— | SHA256:— | |||
| 1724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFde290.TMP | text | |
MD5:— | SHA256:— | |||
| 1724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFde290.TMP | text | |
MD5:— | SHA256:— | |||
| 1724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\000001.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
47
DNS requests
27
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1496 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEAy%2BK8lPT%2B%2Fr4u1gFxGeJoE%3D | US | der | 471 b | whitelisted |
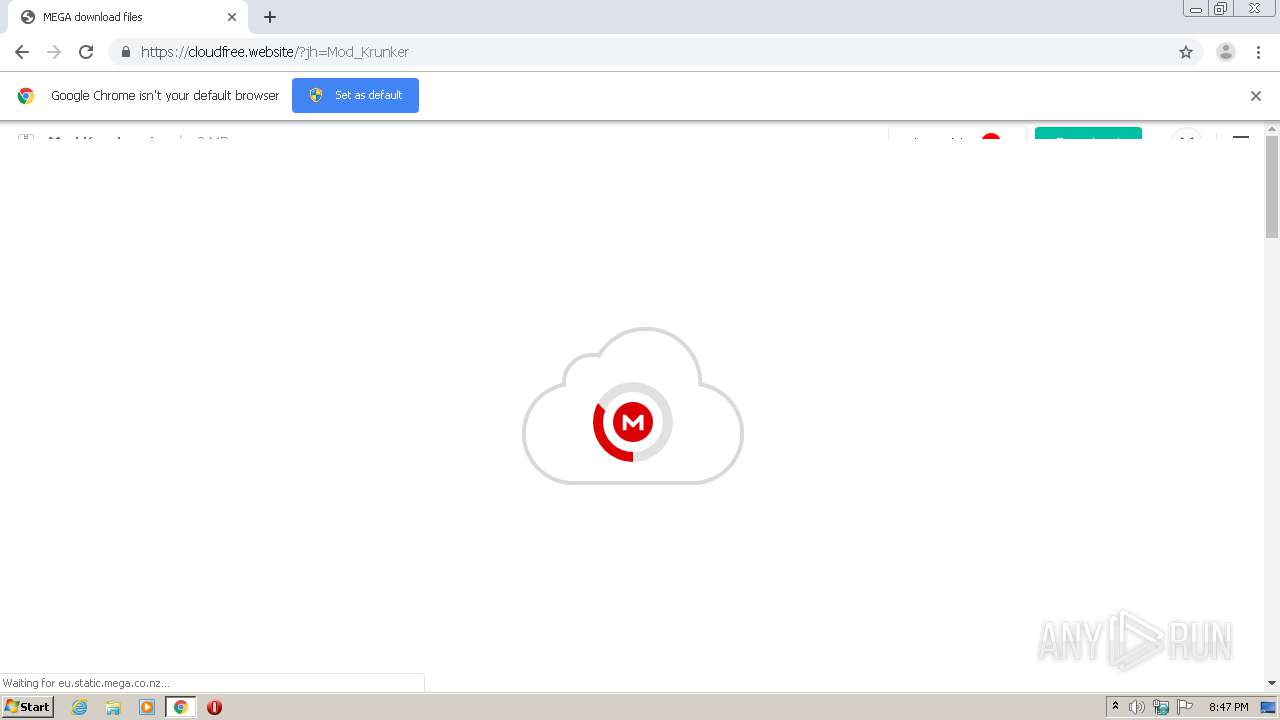
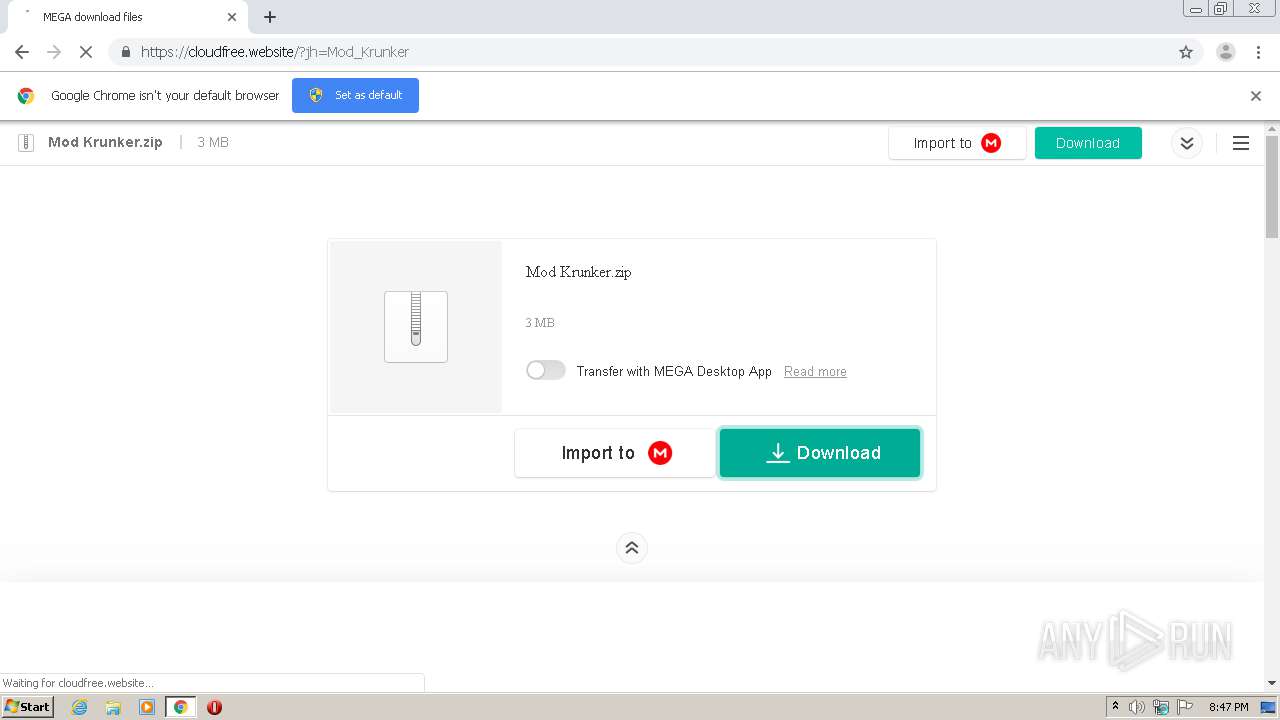
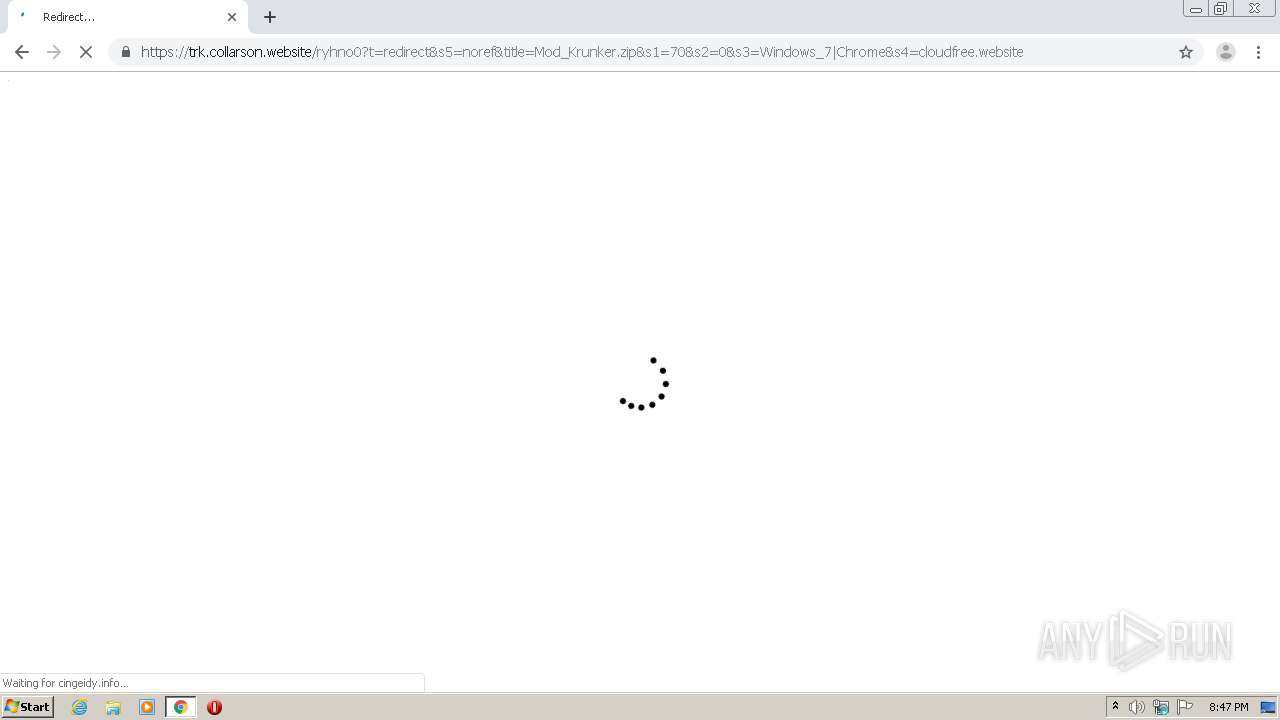
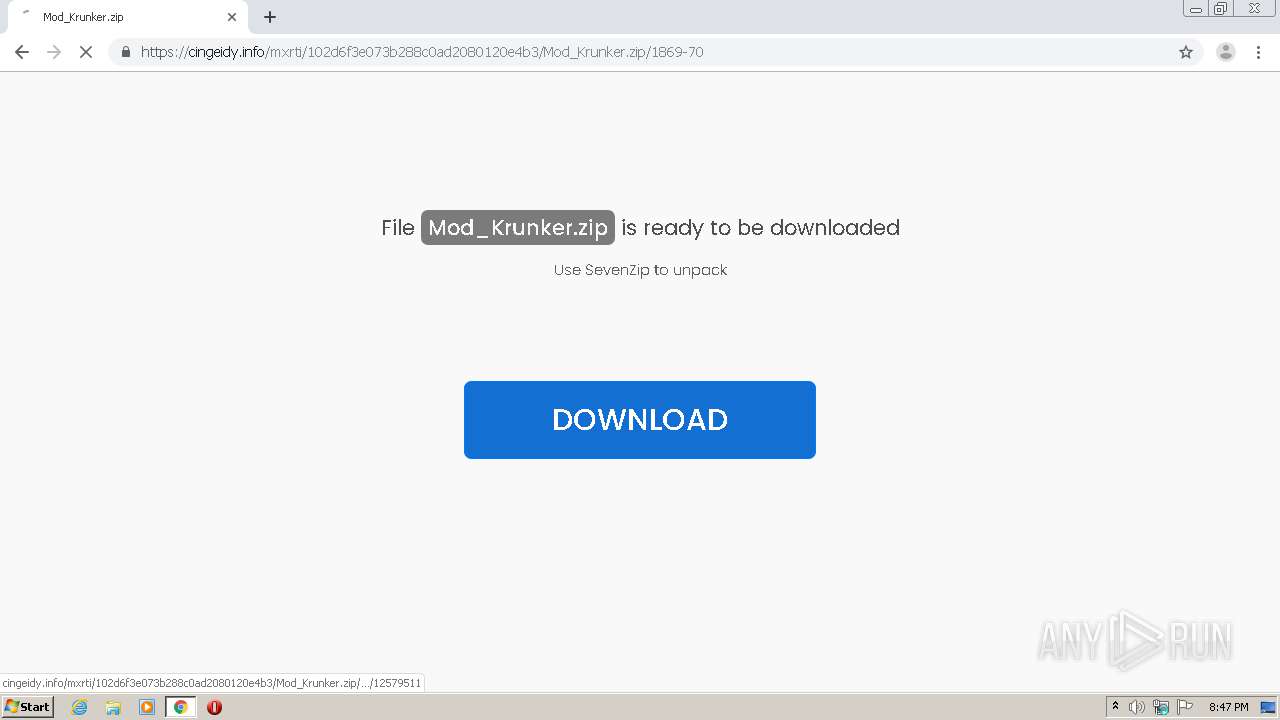
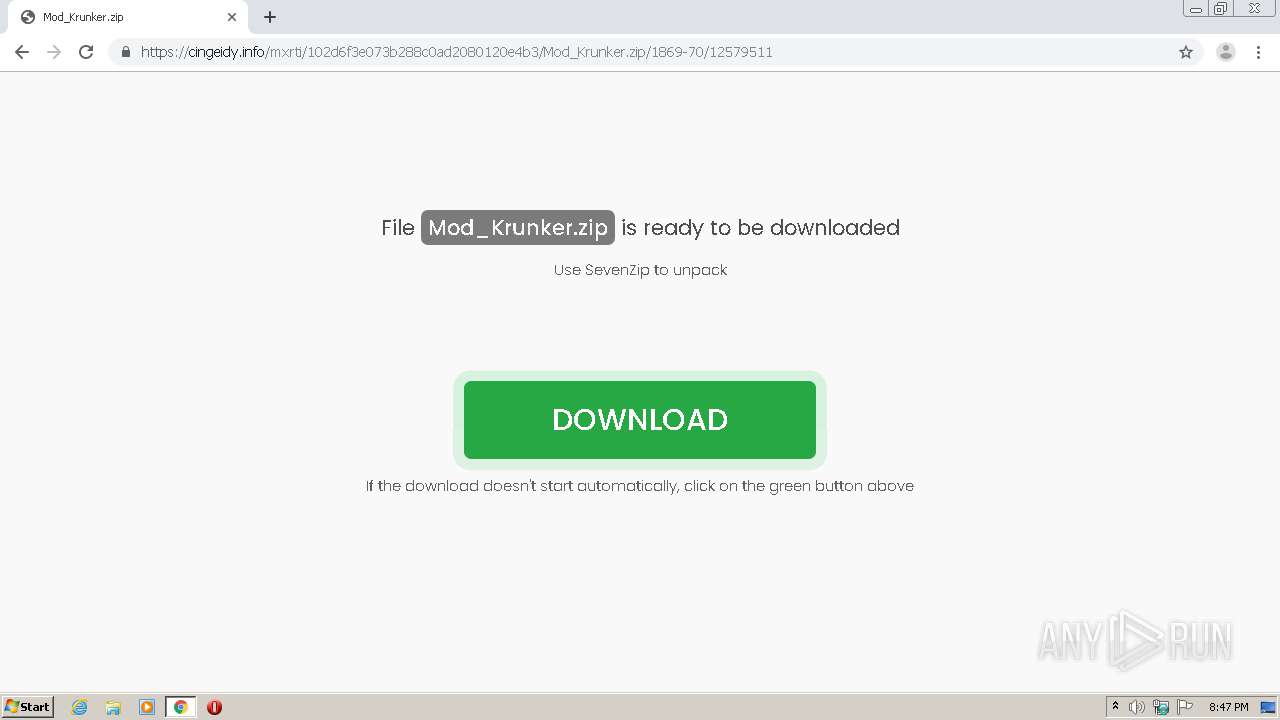
1496 | chrome.exe | GET | 302 | 52.210.174.128:80 | http://trk.sparkrainstorm.host/aff_c?source=1869-70&offer_id=194&aff_click_id=&aff_id=1869&aff_sub=70&aff_sub2=0&aff_sub3=Windows_7|Chrome&aff_sub4=cloudfree.website&aff_sub5=noref&aff_unique1=&aff_unique2=&aff_unique3=&name=Mod_Krunker.zip&url=&url_id=14 | IE | html | 367 b | shared |
3200 | Mod_Krunker_2477159273.exe | POST | 200 | 13.35.254.125:80 | http://db.sinayiv-vece.com/ | US | text | 1.19 Kb | whitelisted |
3200 | Mod_Krunker_2477159273.exe | POST | 200 | 13.35.254.25:80 | http://ftp.sinayiv-vece.com/ | US | — | — | whitelisted |
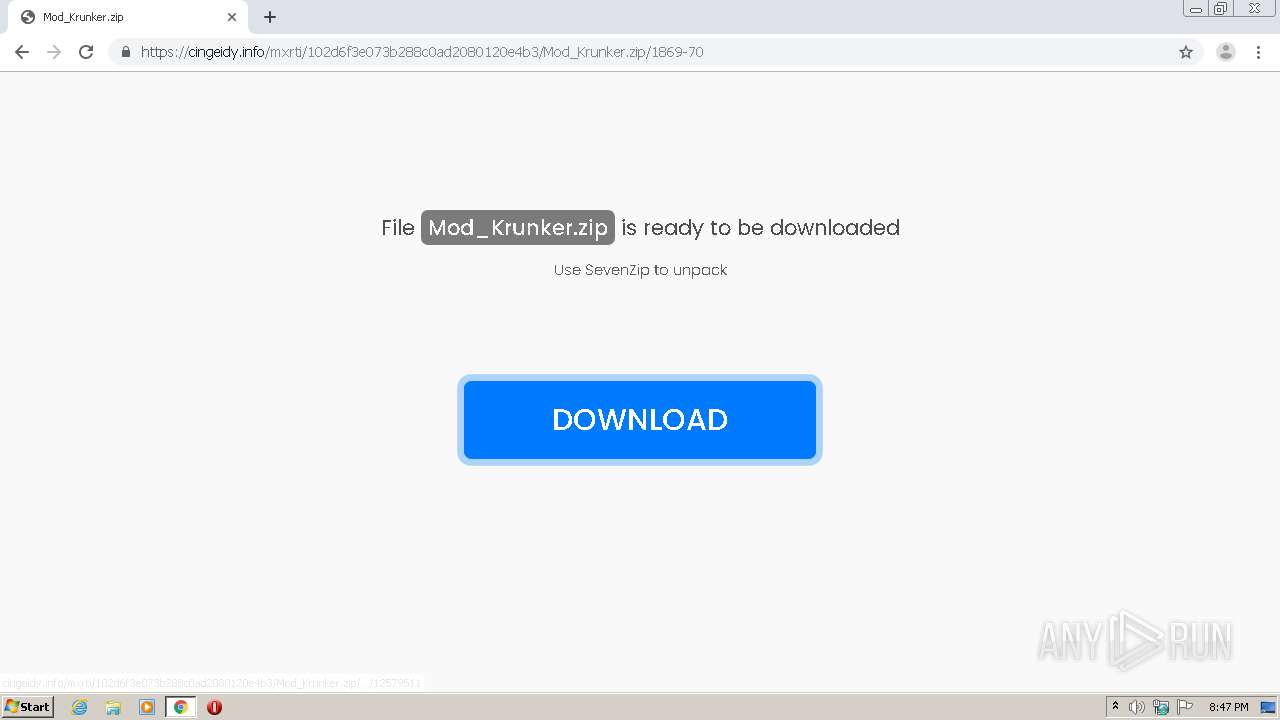
3200 | Mod_Krunker_2477159273.exe | GET | 200 | 46.21.100.252:80 | http://sevenzip.net/img/sevenzip.png | US | image | 12.7 Kb | malicious |
3200 | Mod_Krunker_2477159273.exe | POST | 200 | 13.35.254.25:80 | http://ftp.sinayiv-vece.com/ | US | — | — | whitelisted |
3200 | Mod_Krunker_2477159273.exe | POST | 200 | 143.204.201.64:80 | http://live.sinayiv-vece.com/ | US | binary | 861 Kb | shared |
1496 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
1496 | chrome.exe | GET | 302 | 52.210.174.128:80 | http://trk.sparkrainstorm.host/aff_r?offer_id=194&aff_id=1869&url=https%3A%2F%2Fcingeidy.info%2Fmxrti%2F102d6f3e073b288c0ad2080120e4b3%2FMod_Krunker.zip%2F1869-70&urlauth=293486538928460618899938824741 | IE | html | 266 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1496 | chrome.exe | 172.217.23.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1496 | chrome.exe | 216.58.212.174:443 | www.youtube.com | Google Inc. | US | whitelisted |
1496 | chrome.exe | 172.217.22.67:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
1496 | chrome.exe | 172.217.21.238:443 | www.youtube.com | Google Inc. | US | whitelisted |
1496 | chrome.exe | 216.58.212.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
1496 | chrome.exe | 216.58.212.142:443 | clients1.google.com | Google Inc. | US | whitelisted |
1496 | chrome.exe | 67.199.248.11:443 | bit.ly | Bitly Inc | US | shared |
1496 | chrome.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1496 | chrome.exe | 37.140.192.71:443 | cloudfree.website | Domain names registrar REG.RU, Ltd | RU | suspicious |
1496 | chrome.exe | 172.217.18.14:443 | www.youtube.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.youtube.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
fonts.gstatic.com |
| whitelisted |
s.ytimg.com |
| whitelisted |
clients1.google.com |
| whitelisted |
bit.ly |
| shared |
ocsp.digicert.com |
| whitelisted |
cloudfree.website |
| suspicious |
clients2.google.com |
| whitelisted |