| File name: | pdr-setup-online.exe |
| Full analysis: | https://app.any.run/tasks/d85e1b61-8622-41f3-8c19-9b27302c255a |
| Verdict: | Malicious activity |
| Analysis date: | May 01, 2020, 08:36:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | F9DF3BBDCA146348C1A7B1081232F3D3 |
| SHA1: | AF82BBFEC52CA3A3D0DC3883235620C05FBDA773 |
| SHA256: | D2B60CC6D9B5EC2399CB3CAC87299ED4257B6C2F01EB85D80ACC43F651205562 |
| SSDEEP: | 49152:ct2E49kLDizsx/Zyum0+4zC43ecL6H8frrEIhkaXmb:ctu9kLezsRZyh0+TdvcfP3kaXQ |
MALICIOUS
Application was dropped or rewritten from another process
- OnlineInstall.exe (PID: 2464)
- experience.exe (PID: 3296)
- pdr-setup.exe (PID: 3024)
Loads dropped or rewritten executable
- experience.exe (PID: 3296)
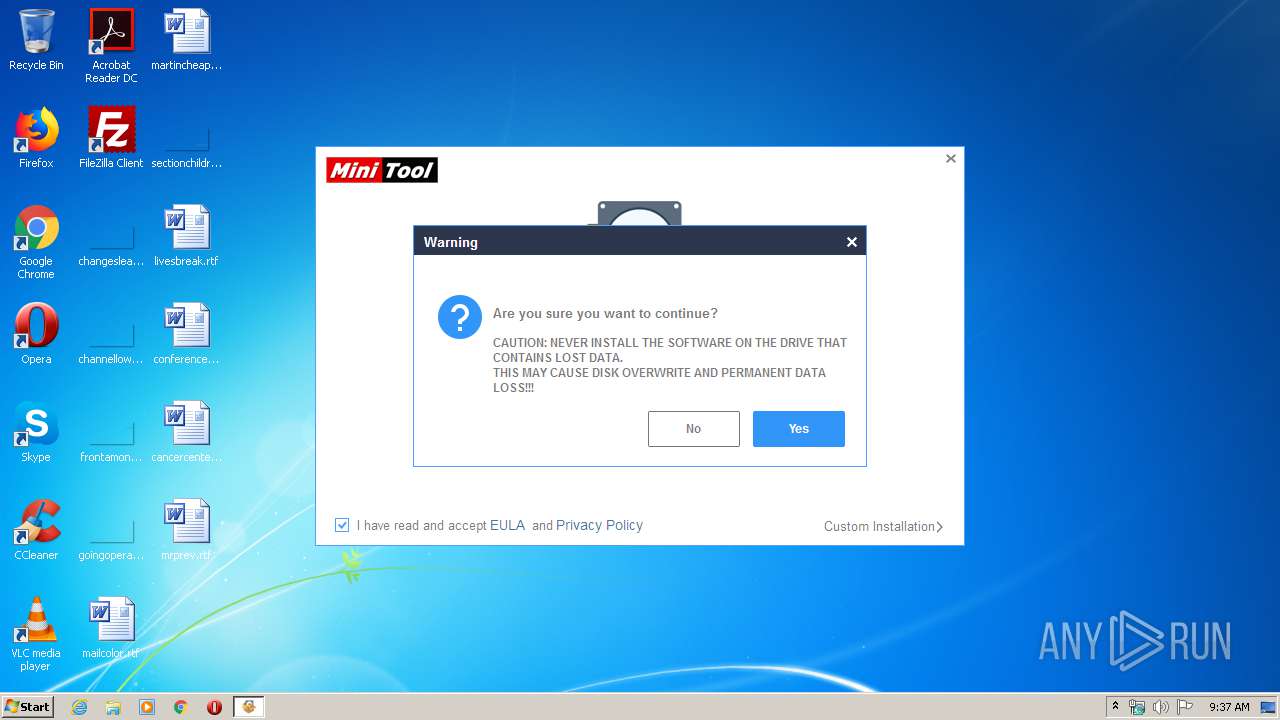
Changes settings of System certificates
- experience.exe (PID: 3296)
SUSPICIOUS
Application launched itself
- pdr-setup-online.exe (PID: 3508)
Executable content was dropped or overwritten
- pdr-setup-online.exe (PID: 3872)
- OnlineInstall.exe (PID: 2464)
- pdr-setup.tmp (PID: 2860)
- pdr-setup.exe (PID: 3024)
Reads Windows owner or organization settings
- pdr-setup.tmp (PID: 2860)
Reads the Windows organization settings
- pdr-setup.tmp (PID: 2860)
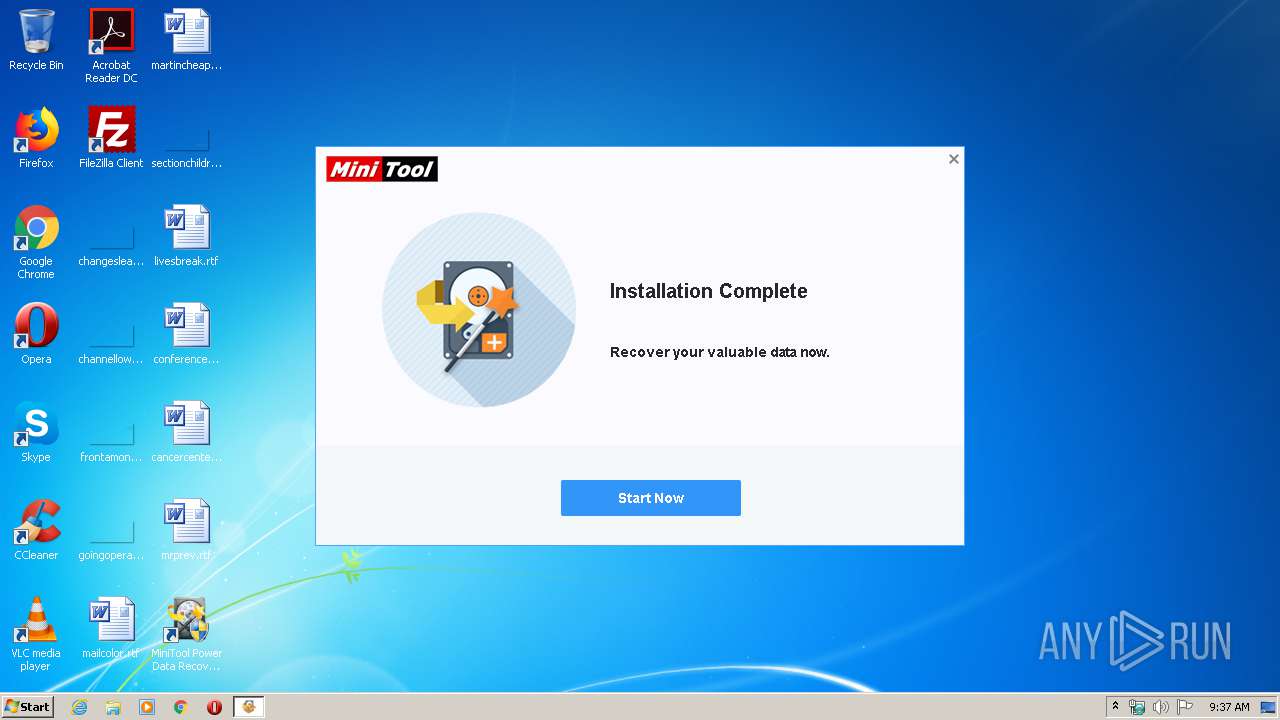
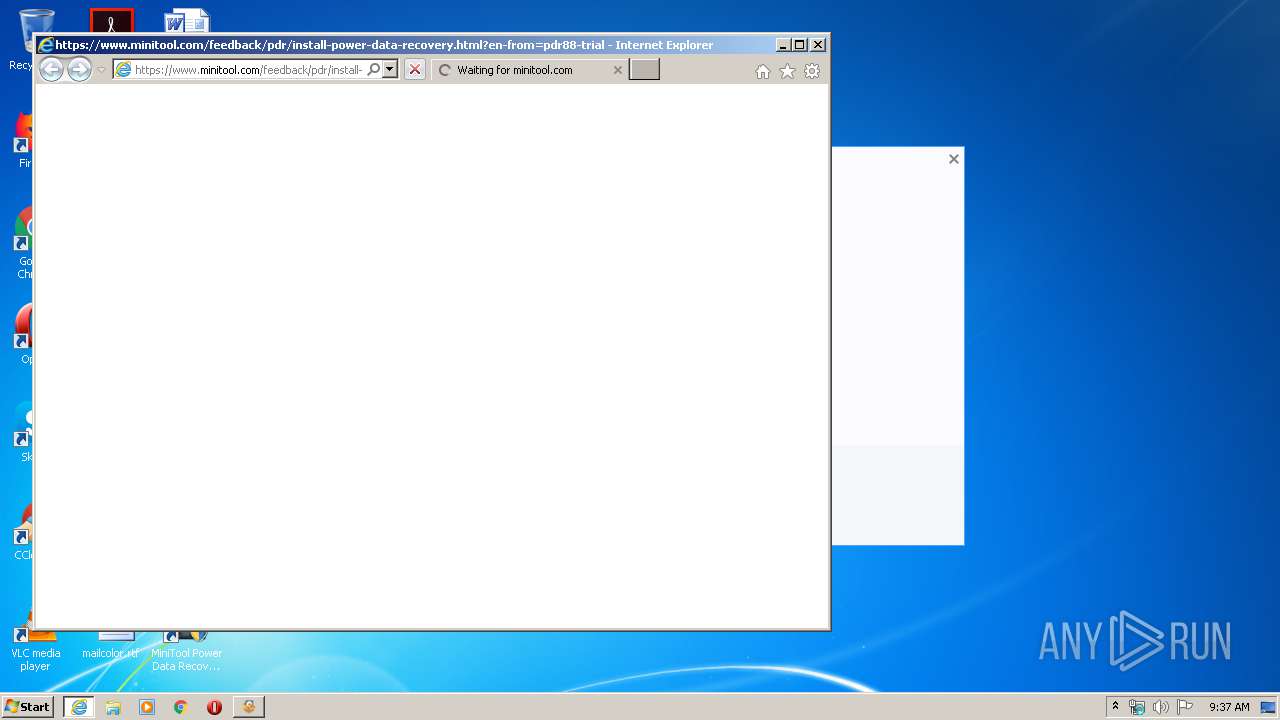
Starts Internet Explorer
- pdr-setup.tmp (PID: 2860)
Reads Internet Cache Settings
- experience.exe (PID: 3296)
Reads internet explorer settings
- experience.exe (PID: 3296)
Creates files in the user directory
- experience.exe (PID: 3296)
Adds / modifies Windows certificates
- experience.exe (PID: 3296)
INFO
Loads dropped or rewritten executable
- pdr-setup.tmp (PID: 2860)
Creates files in the program directory
- pdr-setup.tmp (PID: 2860)
Application launched itself
- iexplore.exe (PID: 1232)
Dropped object may contain Bitcoin addresses
- pdr-setup.tmp (PID: 2860)
Application was dropped or rewritten from another process
- pdr-setup.tmp (PID: 2860)
Creates a software uninstall entry
- pdr-setup.tmp (PID: 2860)
Reads Internet Cache Settings
- iexplore.exe (PID: 1232)
- iexplore.exe (PID: 3844)
Creates files in the user directory
- iexplore.exe (PID: 3844)
Reads internet explorer settings
- iexplore.exe (PID: 3844)
Reads settings of System Certificates
- iexplore.exe (PID: 3844)
- experience.exe (PID: 3296)
Changes internet zones settings
- iexplore.exe (PID: 1232)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3844)
Changes settings of System certificates
- iexplore.exe (PID: 3844)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:12:31 01:38:38+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 89600 |
| InitializedDataSize: | 393216 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1638f |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 8.7.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | Russian |
| CharacterSet: | Unicode |
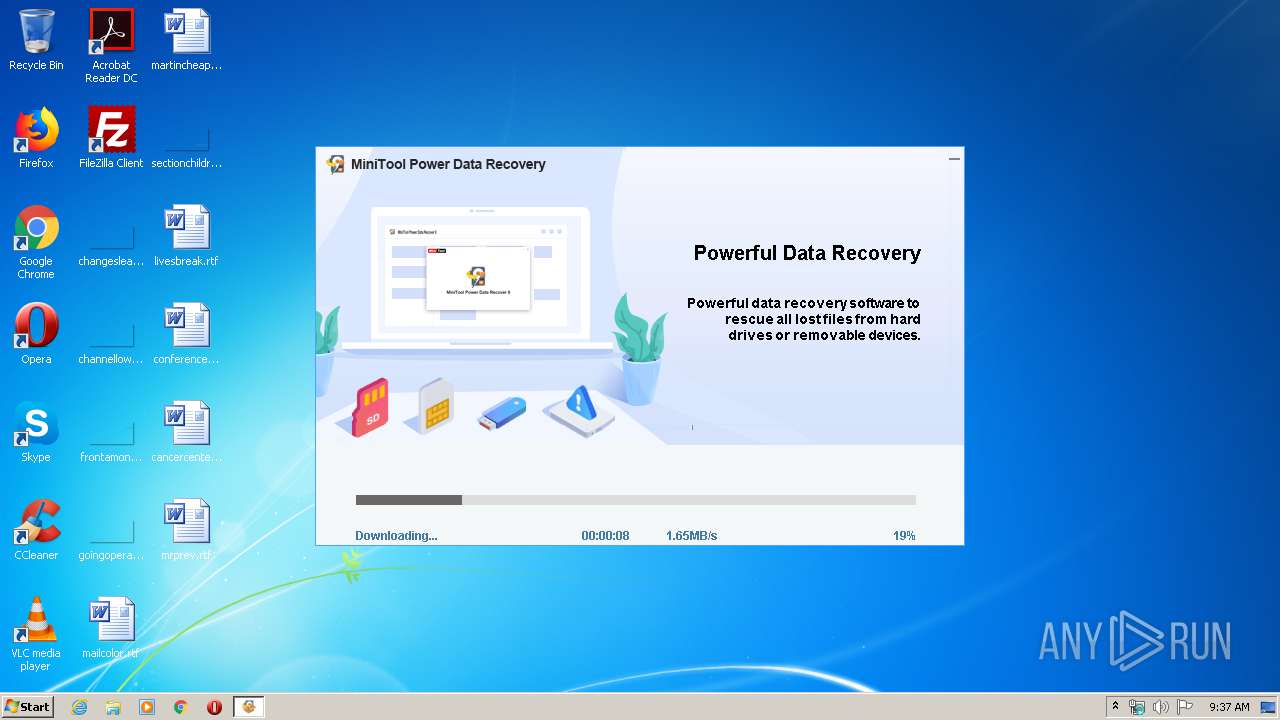
| CompanyName: | MiniTool Software Limited |
| FileDescription: | MiniTool Power Data Recovery Trial Edition Setup |
| LegalCopyright: | Copyright © 2006-2020 MiniTool Software Limited. All rights reserved. |
| ProductName: | MiniTool Power Data Recovery Trial Edition |
| FileVersion: | 0.0.0.0 |
| ProductVersion: | 8.7 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 31-Dec-2012 00:38:38 |
| Detected languages: |
|
| CompanyName: | MiniTool Software Limited |
| FileDescription: | MiniTool Power Data Recovery Trial Edition Setup |
| LegalCopyright: | Copyright © 2006-2020 MiniTool Software Limited. All rights reserved. |
| ProductName: | MiniTool Power Data Recovery Trial Edition |
| FileVersion: | 0.0.0.0 |
| ProductVersion: | 8.7 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0060 |
| Pages in file: | 0x0001 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000060 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 31-Dec-2012 00:38:38 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00015CFE | 0x00015E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.6445 |
.rdata | 0x00017000 | 0x00003982 | 0x00003A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.70129 |
.data | 0x0001B000 | 0x00004C8C | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.35632 |
.rsrc | 0x00020000 | 0x0005BB54 | 0x0005BC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.16692 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.23138 | 838 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 2.60602 | 744 | Latin 1 / Western European | Russian - Russia | RT_ICON |
3 | 2.63074 | 488 | Latin 1 / Western European | Russian - Russia | RT_ICON |
4 | 2.3817 | 296 | Latin 1 / Western European | Russian - Russia | RT_ICON |
50 | 4.05839 | 270376 | Latin 1 / Western European | Russian - Russia | RT_ICON |
51 | 4.26382 | 67624 | Latin 1 / Western European | Russian - Russia | RT_ICON |
52 | 4.47254 | 16936 | Latin 1 / Western European | Russian - Russia | RT_ICON |
53 | 4.62026 | 9640 | Latin 1 / Western European | Russian - Russia | RT_ICON |
54 | 4.95303 | 4264 | Latin 1 / Western European | Russian - Russia | RT_ICON |
55 | 5.21168 | 1128 | Latin 1 / Western European | Russian - Russia | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
MSVCRT.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
48
Monitored processes
8
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
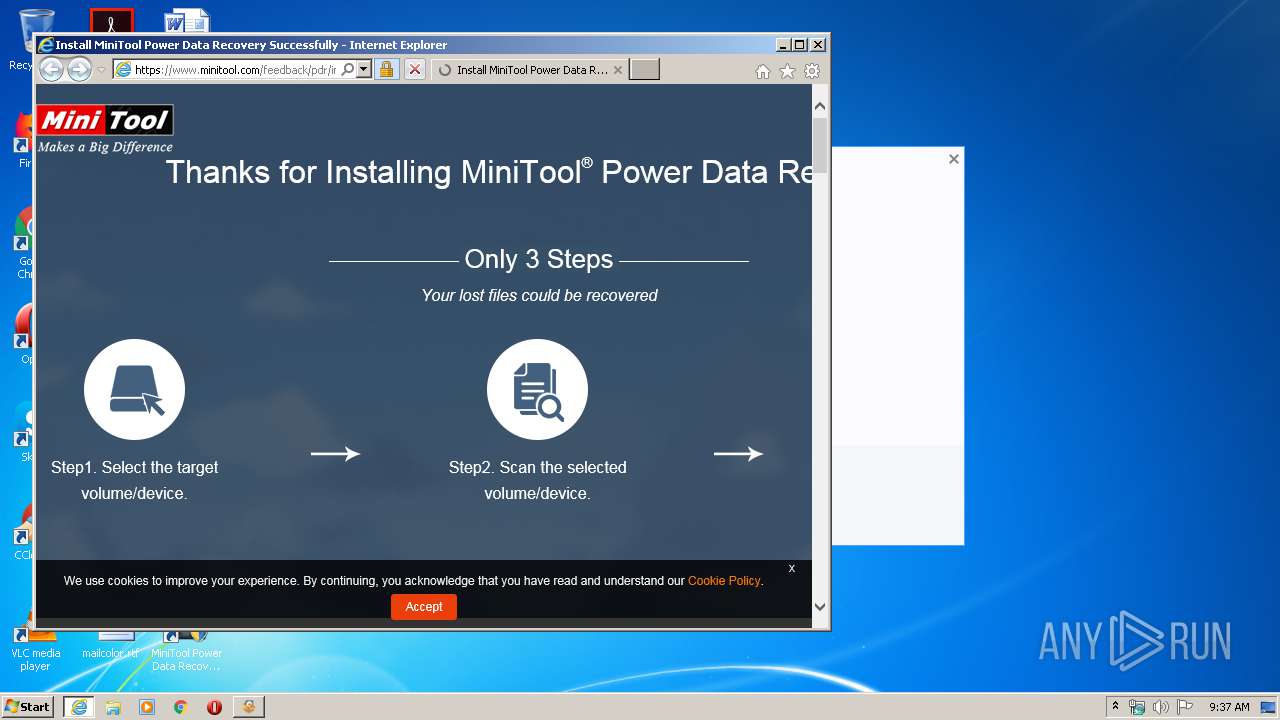
| 1232 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.minitool.com/feedback/pdr/install-power-data-recovery.html?en-from=pdr88-trial | C:\Program Files\Internet Explorer\iexplore.exe | pdr-setup.tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2464 | "C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\Trial-Release\OnlineInstall.exe" | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\Trial-Release\OnlineInstall.exe | pdr-setup-online.exe | ||||||||||||
User: admin Company: MiniTool Software Limited Integrity Level: HIGH Description: MiniTool Power Data Recovery Setup Exit code: 0 Version: 8.7.0.0 Modules
| |||||||||||||||
| 2860 | "C:\Users\admin\AppData\Local\Temp\is-0V3SH.tmp\pdr-setup.tmp" /SL5="$1D01FA,16558114,301056,C:\Users\admin\Downloads\pdr-setup.exe" /progress="C:\Users\admin\AppData\Local\Temp\progress.txt" /VERYSILENT /LOG="C:\Program Files\MiniTool PowerDataRecovery\Innosetuplog.txt" /NORESTART /DIR="C:\Program Files\MiniTool PowerDataRecovery" /LANG=english /agreeImprove=1 /online | C:\Users\admin\AppData\Local\Temp\is-0V3SH.tmp\pdr-setup.tmp | pdr-setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3024 | "C:\Users\admin\Downloads\pdr-setup.exe" /progress="C:\Users\admin\AppData\Local\Temp\progress.txt" /VERYSILENT /LOG="C:\Program Files\MiniTool PowerDataRecovery\Innosetuplog.txt" /NORESTART /DIR="C:\Program Files\MiniTool PowerDataRecovery" /LANG=english /agreeImprove=1 /online | C:\Users\admin\Downloads\pdr-setup.exe | OnlineInstall.exe | ||||||||||||
User: admin Company: MiniTool Software Limited Integrity Level: HIGH Description: MiniTool Power Data Recovery Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 3296 | "C:\Program Files\MiniTool PowerDataRecovery\experience.exe" http://tracking.minitool.com/pdr/installation.php?en-from=pdr88-trial | C:\Program Files\MiniTool PowerDataRecovery\experience.exe | pdr-setup.tmp | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3508 | "C:\Users\admin\AppData\Local\Temp\pdr-setup-online.exe" | C:\Users\admin\AppData\Local\Temp\pdr-setup-online.exe | — | explorer.exe | |||||||||||
User: admin Company: MiniTool Software Limited Integrity Level: MEDIUM Description: MiniTool Power Data Recovery Trial Edition Setup Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 3844 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1232 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3872 | "C:\Users\admin\AppData\Local\Temp\pdr-setup-online.exe" -sfxelevation | C:\Users\admin\AppData\Local\Temp\pdr-setup-online.exe | pdr-setup-online.exe | ||||||||||||
User: admin Company: MiniTool Software Limited Integrity Level: HIGH Description: MiniTool Power Data Recovery Trial Edition Setup Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
Total events
4 481
Read events
2 083
Write events
2 392
Delete events
6
Modification events
| (PID) Process: | (3508) pdr-setup-online.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3508) pdr-setup-online.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3872) pdr-setup-online.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3872) pdr-setup-online.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2464) OnlineInstall.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Compatibility Assistant\Persisted |
| Operation: | write | Name: | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\Trial-Release\OnlineInstall.exe |
Value: 1 | |||
| (PID) Process: | (2860) pdr-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 2C0B0000BA7A0FC2931FD601 | |||
| (PID) Process: | (2860) pdr-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 882A6D5F6C88EE5886DB987F224784CEA7C026C4A087E13D65853352D880282E | |||
| (PID) Process: | (2860) pdr-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2464) OnlineInstall.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2464) OnlineInstall.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
36
Suspicious files
96
Text files
132
Unknown types
75
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3872 | pdr-setup-online.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\Trial-Release\skin_anima\Check_Selected.png | image | |
MD5:6D116DCCAAC5056D7D1F4A593D5AC0DB | SHA256:0946EFEE104652F084C6FB2F271B06FCDFB50DE893D64CD4287CC8E64DECED92 | |||
| 3872 | pdr-setup-online.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\Trial-Release\skin_anima\Close_Pre.png | image | |
MD5:D68A848882BBFF4430F4BEE8435AA113 | SHA256:1821FDFF02AB26FD09A3E04FD21C740994AFD5AC80F1D5775B79D7F10290EB0D | |||
| 3872 | pdr-setup-online.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\Trial-Release\skin_anima\Check_Nomal.png | image | |
MD5:A544F7599747B3B04CDD4BEB2C27C603 | SHA256:DCE573C01333549B06149934C4B5E81FC75BE62DBBBE7E4F4806B029C6E9567A | |||
| 3872 | pdr-setup-online.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\Trial-Release\skin_anima\CloseUI.xml | xml | |
MD5:CC22DD8A2510B12D40BBD18D4F323EBD | SHA256:AECC5AE6AF21AB31221D47CCC42E8973BA5FB5D0F590F8DBE24E4EF81AD0C7E2 | |||
| 3872 | pdr-setup-online.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\Trial-Release\skin_anima\DownloadUI.xml | xml | |
MD5:— | SHA256:— | |||
| 3872 | pdr-setup-online.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\Trial-Release\skin_anima\Config.ini | text | |
MD5:— | SHA256:— | |||
| 3872 | pdr-setup-online.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\Trial-Release\skin_anima\Download_Pic1.png | image | |
MD5:— | SHA256:— | |||
| 3872 | pdr-setup-online.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\Trial-Release\skin_anima\Close_Selected.png | image | |
MD5:A92D5384258CB858E13377E09AD3B40A | SHA256:9FCF6087956D95E1122D42AA8FCD2CB413501D123DCA7E48377DB942640AC27E | |||
| 3872 | pdr-setup-online.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\Trial-Release\skin_anima\Download_Pic4.png | image | |
MD5:— | SHA256:— | |||
| 3872 | pdr-setup-online.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\Trial-Release\skin_anima\Close_Nomal.png | image | |
MD5:99FCFF2ACA703823E083CB90A3192146 | SHA256:CBE96210DC6C28E21625C01DB80E510152EECBF4DDBC75A30FEEEFB9FFA318EF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
47
TCP/UDP connections
83
DNS requests
36
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3844 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBReAhtobFzTvhaRmVeJ38QUchY9AwQUu69%2BAj36pvE8hI6t7jiY7NkyMtQCECsuburZdTZsFIpu26N8jAc%3D | US | der | 727 b | whitelisted |
3844 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCECdm7lbrSfOOq9dwovyE3iI%3D | US | der | 471 b | whitelisted |
3844 | iexplore.exe | GET | 200 | 13.225.78.95:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
3844 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCECdm7lbrSfOOq9dwovyE3iI%3D | US | der | 471 b | whitelisted |
3844 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
3296 | experience.exe | GET | 200 | 50.87.234.221:80 | http://tracking.minitool.com/pdr/installation.php?en-from=pdr88-trial | US | html | 501 b | suspicious |
3844 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
3844 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
3844 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBReAhtobFzTvhaRmVeJ38QUchY9AwQUu69%2BAj36pvE8hI6t7jiY7NkyMtQCECsuburZdTZsFIpu26N8jAc%3D | US | der | 727 b | whitelisted |
3296 | experience.exe | GET | 200 | 172.217.22.35:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDE9U%2B0StibRggAAAAAOMpn | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2464 | OnlineInstall.exe | 104.20.145.70:443 | www.minitool.com | Cloudflare Inc | US | shared |
3296 | experience.exe | 172.217.21.206:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
3296 | experience.exe | 50.87.234.221:80 | tracking.minitool.com | Unified Layer | US | suspicious |
3844 | iexplore.exe | 104.20.144.70:443 | www.minitool.com | Cloudflare Inc | US | suspicious |
3296 | experience.exe | 173.194.76.155:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
— | — | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3296 | experience.exe | 172.217.22.35:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3296 | experience.exe | 172.217.23.99:443 | www.google.nl | Google Inc. | US | whitelisted |
3844 | iexplore.exe | 151.139.128.14:80 | ocsp.usertrust.com | Highwinds Network Group, Inc. | US | suspicious |
3296 | experience.exe | 172.217.16.132:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.minitool.com |
| suspicious |
cdn2.minitool.com |
| suspicious |
tracking.minitool.com |
| suspicious |
www.google-analytics.com |
| whitelisted |
stats.g.doubleclick.net |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
www.google.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |