| File name: | rk_free_setup_301.exe |
| Full analysis: | https://app.any.run/tasks/dc736ec4-42f1-4a8e-9bb8-7201e7d39691 |
| Verdict: | Malicious activity |
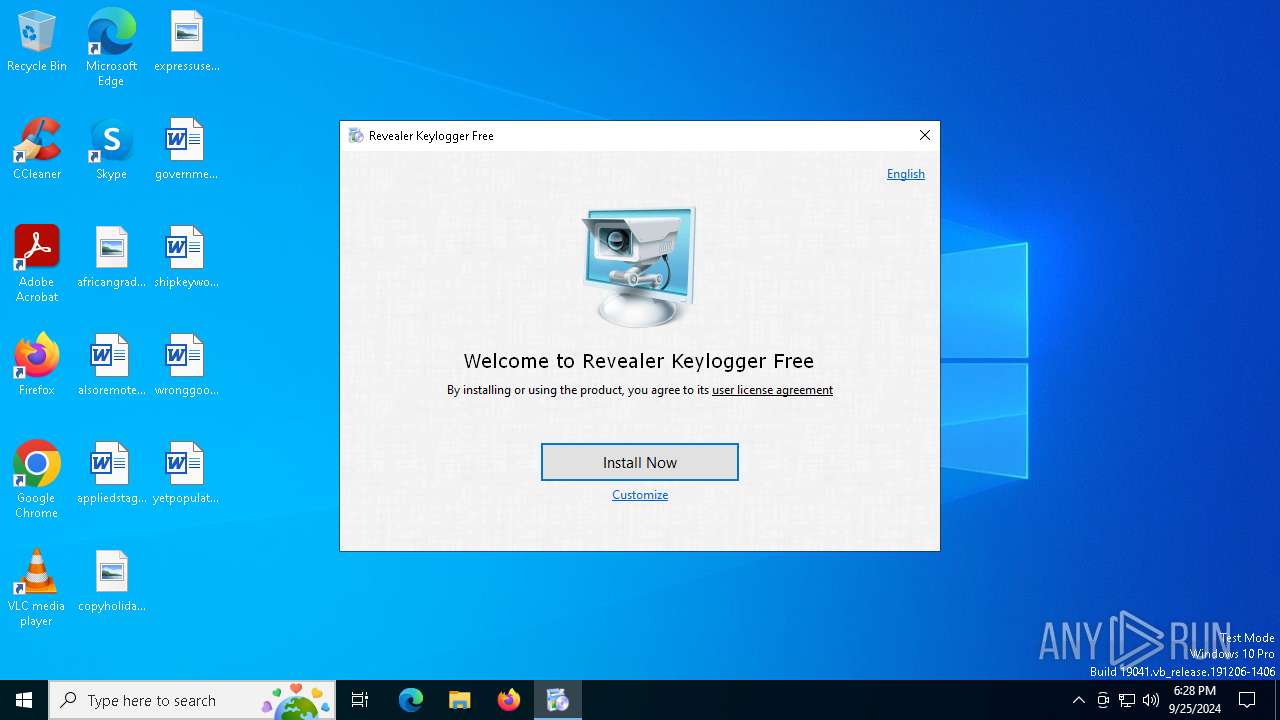
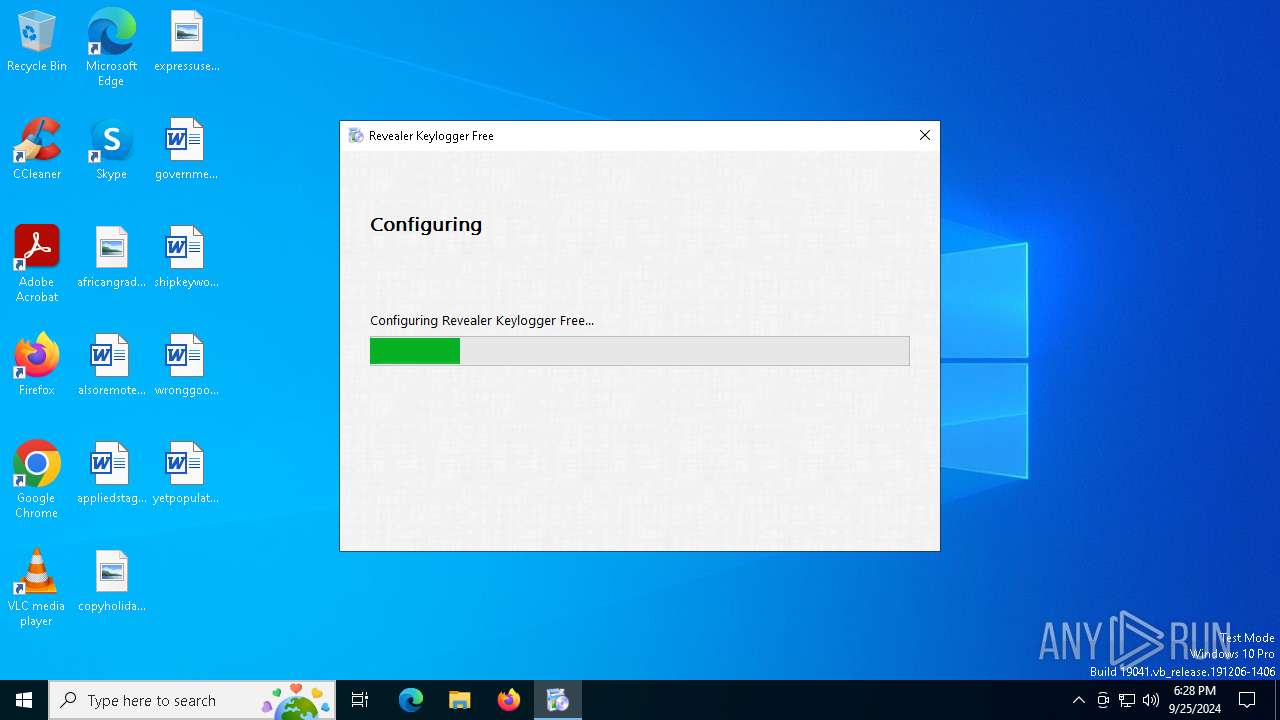
| Analysis date: | September 25, 2024, 18:28:06 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 3935C389ED8451DF43C021CBB8DCD740 |
| SHA1: | 10810B87D883C4A006F4499D973610B95C14C2B6 |
| SHA256: | D2AD1908D041D0B2B09D2FFB68D98881F0AFF30B9055C6670AA623587BA35224 |
| SSDEEP: | 49152:Gv/C1Im6vgkSY7pmXIeawosEbzDJUgyR0GXmvgkSY7pmXIwy:0/ZmK/ogH1OLW/n |
MALICIOUS
Modifies exclusions in Windows Defender
- rkfree_setup64.exe (PID: 1176)
Create files in the Startup directory
- rvlkl.exe (PID: 5208)
SUSPICIOUS
Reads security settings of Internet Explorer
- rk_free_setup_301.exe (PID: 2084)
- rkfree_setup64.exe (PID: 1176)
- rvlkl.exe (PID: 1236)
Executable content was dropped or overwritten
- rkfree_setup64.exe (PID: 1176)
- rk_free_setup_301.exe (PID: 2084)
Detected use of alternative data streams (AltDS)
- rkfree_setup64.exe (PID: 1176)
Reads the date of Windows installation
- rkfree_setup64.exe (PID: 1176)
INFO
Reads the computer name
- rk_free_setup_301.exe (PID: 2084)
- rvlkl.exe (PID: 1236)
- rvlkl.exe (PID: 5208)
- rkfree_setup64.exe (PID: 1176)
Checks supported languages
- rk_free_setup_301.exe (PID: 2084)
- rkfree_setup64.exe (PID: 1176)
- rvlkl.exe (PID: 5208)
- rvlkl.exe (PID: 1236)
Process checks computer location settings
- rk_free_setup_301.exe (PID: 2084)
- rkfree_setup64.exe (PID: 1176)
Reads the machine GUID from the registry
- rkfree_setup64.exe (PID: 1176)
- rvlkl.exe (PID: 1236)
- rvlkl.exe (PID: 5208)
The process uses the downloaded file
- rkfree_setup64.exe (PID: 1176)
- rk_free_setup_301.exe (PID: 2084)
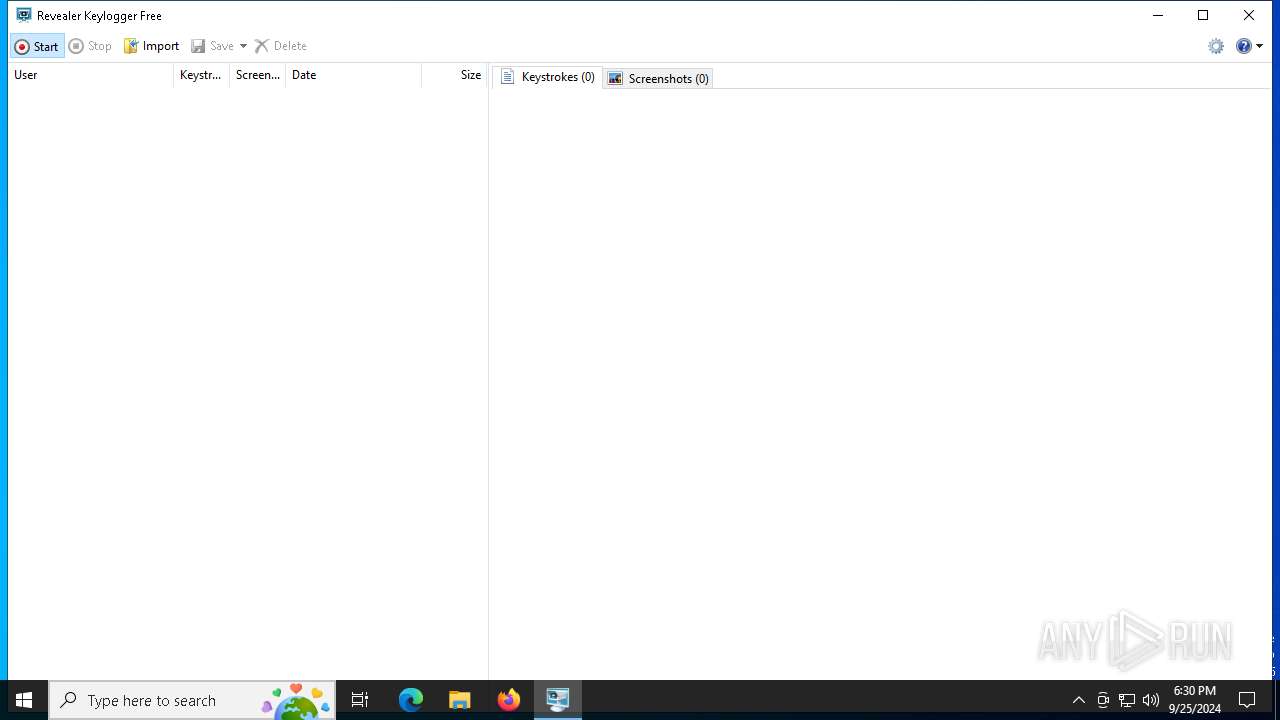
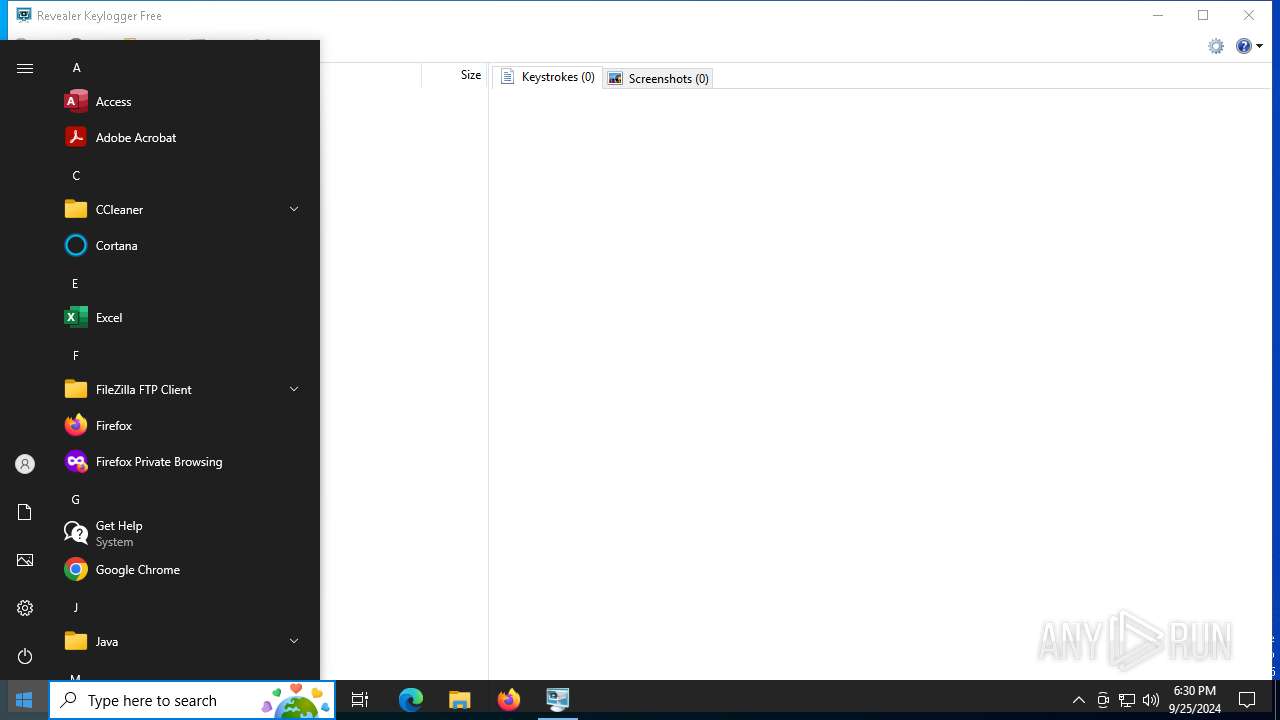
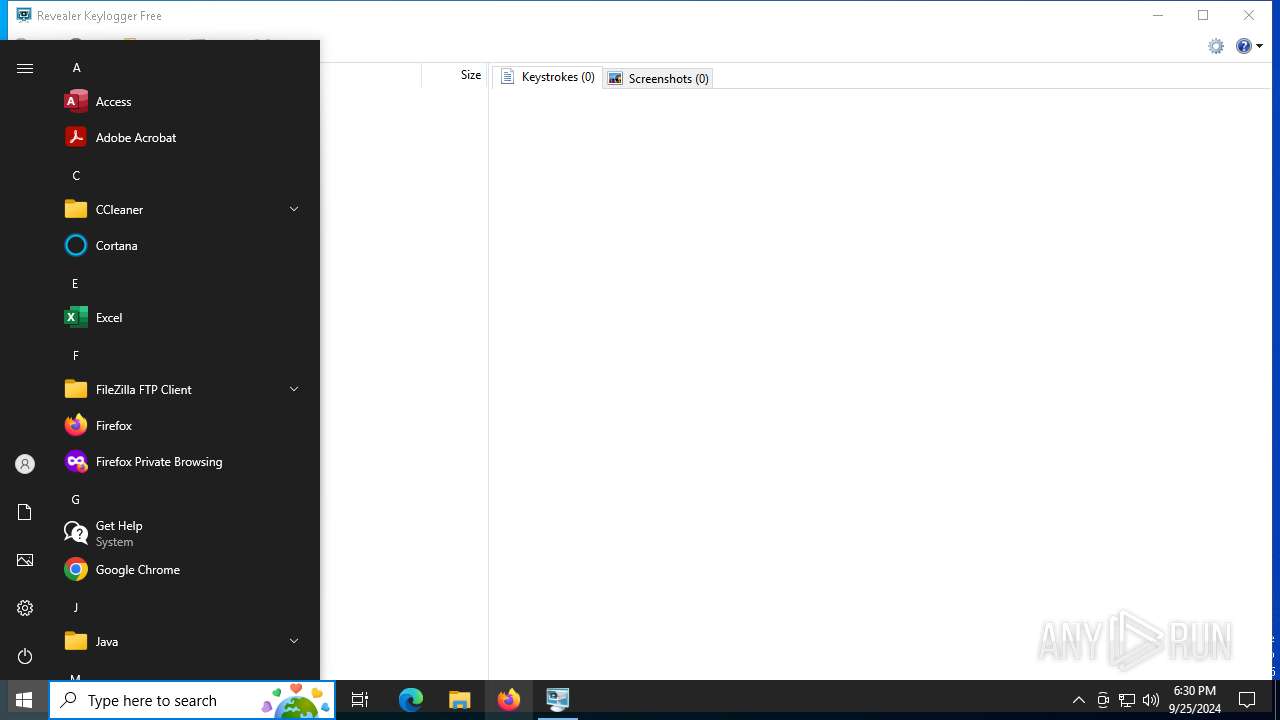
Manual execution by a user
- rvlkl.exe (PID: 1236)
- rvlkl.exe (PID: 6128)
Creates files in the program directory
- rvlkl.exe (PID: 5208)
- rvlkl.exe (PID: 1236)
- rkfree_setup64.exe (PID: 1176)
Create files in a temporary directory
- rk_free_setup_301.exe (PID: 2084)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:05:10 09:32:28+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.28 |
| CodeSize: | 105984 |
| InitializedDataSize: | 1758720 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xf7cf |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
146
Monitored processes
10
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 752 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1176 | "C:\Users\admin\AppData\Local\Temp\rkfree_setup\rkfree_setup64.exe" | C:\Users\admin\AppData\Local\Temp\rkfree_setup\rkfree_setup64.exe | rk_free_setup_301.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
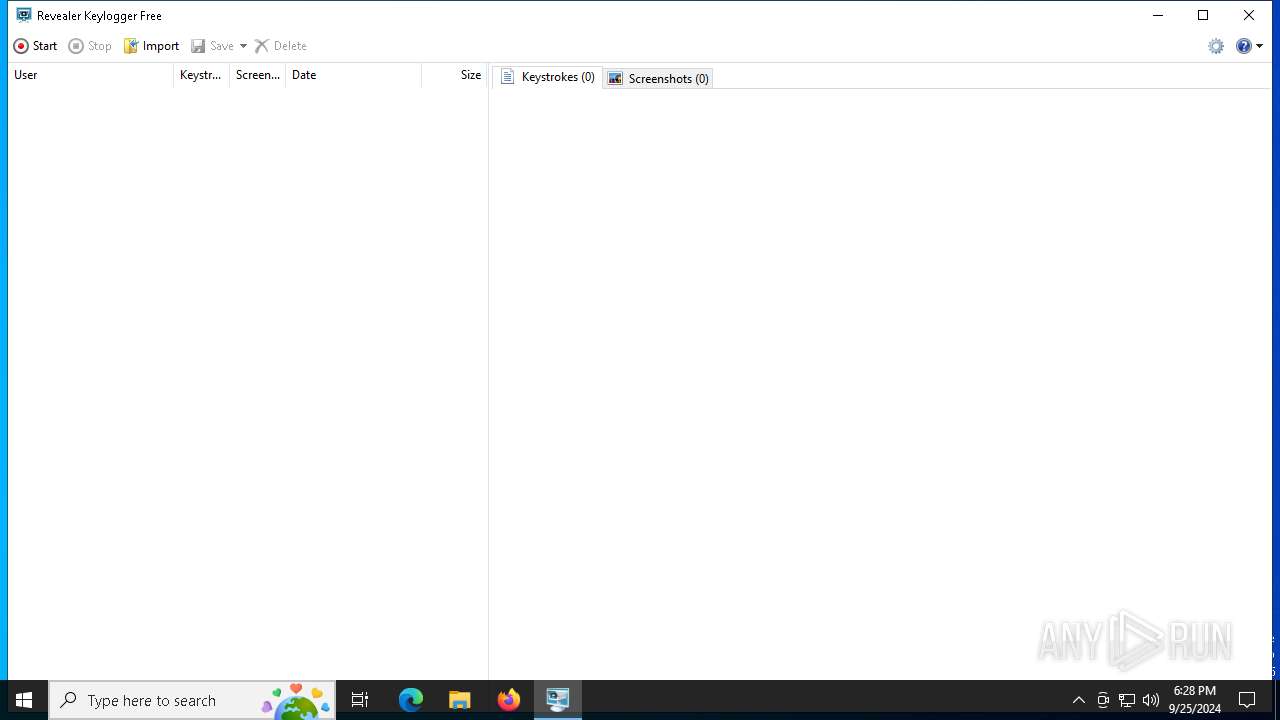
| 1236 | "C:\WINDOWS\system32\rvlkl.exe" | C:\Windows\System32\rvlkl.exe | explorer.exe | ||||||||||||
User: admin Company: Logixoft Integrity Level: HIGH Description: Revealer Free Version: 3.0.1.0 Modules
| |||||||||||||||
| 2084 | "C:\Users\admin\AppData\Local\Temp\rk_free_setup_301.exe" | C:\Users\admin\AppData\Local\Temp\rk_free_setup_301.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 4648 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5208 | "C:\WINDOWS\system32\rvlkl.exe" -install -lang 9 | C:\Windows\System32\rvlkl.exe | rkfree_setup64.exe | ||||||||||||
User: admin Company: Logixoft Integrity Level: HIGH Description: Revealer Free Exit code: 0 Version: 3.0.1.0 Modules
| |||||||||||||||
| 5900 | "C:\WINDOWS\system32\rvlkl.exe" -install -lang 9 | C:\Windows\System32\rvlkl.exe | — | rkfree_setup64.exe | |||||||||||
User: admin Company: Logixoft Integrity Level: HIGH Description: Revealer Free Exit code: 3221226540 Version: 3.0.1.0 Modules
| |||||||||||||||
| 6128 | "C:\WINDOWS\system32\rvlkl.exe" | C:\Windows\System32\rvlkl.exe | — | explorer.exe | |||||||||||
User: admin Company: Logixoft Integrity Level: MEDIUM Description: Revealer Free Exit code: 3221226540 Version: 3.0.1.0 Modules
| |||||||||||||||
| 6512 | "C:\Users\admin\AppData\Local\Temp\rk_free_setup_301.exe" | C:\Users\admin\AppData\Local\Temp\rk_free_setup_301.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 6760 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 836
Read events
1 832
Write events
2
Delete events
2
Modification events
| (PID) Process: | (1176) rkfree_setup64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | rvlkl |
Value: | |||
| (PID) Process: | (1176) rkfree_setup64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | rkfree |
Value: | |||
| (PID) Process: | (1176) rkfree_setup64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Defender\Exclusions\Paths |
| Operation: | write | Name: | C:\WINDOWS\system32\rvlkl.exe |
Value: 0 | |||
| (PID) Process: | (1176) rkfree_setup64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Defender\Exclusions\Processes |
| Operation: | write | Name: | C:\WINDOWS\system32\rvlkl.exe |
Value: 0 | |||
Executable files
3
Suspicious files
2
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1176 | rkfree_setup64.exe | C:\ProgramData\rvlkl\log.css | text | |
MD5:A35BD6E012B609D94A076699C5372657 | SHA256:6EF8CFC8307115A02E5B60AF549867DC79BDF3018EB95A9417E8E6C3632EABB5 | |||
| 5208 | rvlkl.exe | C:\ProgramData\rvlkl\conf_ | binary | |
MD5:6FBED2A2E0416D1C94E76905CEBF518D | SHA256:4240F55276638FAA4D186B992910CB991208A6C8E970E2A8AD41F6B37C5BB716 | |||
| 5208 | rvlkl.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\StartUp\rvlkl.lnk | binary | |
MD5:923E37273C76A85538F21FD7C36FBE70 | SHA256:5950FA4984E8E75576DCFDFA0D16AA3CA1D4EDBFFAFB181AF2842AF905B80C0D | |||
| 1236 | rvlkl.exe | C:\ProgramData\rvlkl\conf_ | text | |
MD5:E8433E7512D30AF4229E160FBA599A6A | SHA256:01709A396ECCA62E7C8A3284E5143F7C7C39BB15B73F6D0FB7CA2D29B43EF69F | |||
| 2084 | rk_free_setup_301.exe | C:\Users\admin\AppData\Local\Temp\rkfree_setup\rkfree_setup64.exe | executable | |
MD5:521F2A5C686F718E3CA2DCA5F4AF2B49 | SHA256:7444DC7F026376291DF6BC0BA8A1EF4A97B22B7EFA1FF446E8B7EE83814F0533 | |||
| 1176 | rkfree_setup64.exe | C:\Windows\System32\rvlkl.exe | executable | |
MD5:A96EC3A8236736C4153D8CC16C53DCA3 | SHA256:2C4147281974CE872B59BC994C378561AF209DA70875B60D8D213E563E605B87 | |||
| 5208 | rvlkl.exe | C:\ProgramData\rvlkl\conf | text | |
MD5:3A2A17F6EF47EA009788C4FA1E003E57 | SHA256:E125F4E866B633574ABD6B51EBF8F48DA282BB520281449331C97D071E59AD30 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
46
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
1224 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
5212 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1224 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6196 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6920 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5212 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5212 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5212 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6196 | svchost.exe | 40.126.32.133:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6196 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
browser.pipe.aria.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |