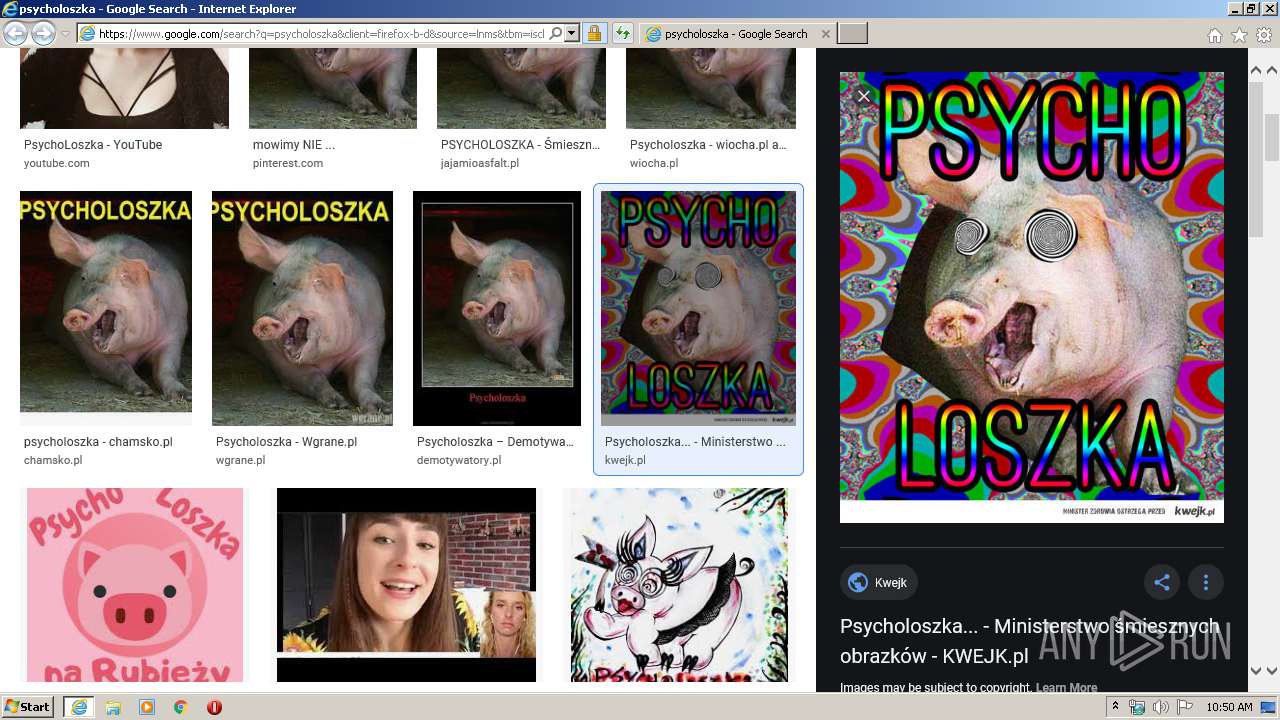
| URL: | https://www.google.com/search?q=psycholoszka&client=firefox-b-d&source=lnms&tbm=isch&sa=X&ved=2ahUKEwiX__7H17LnAhVSr4sKHT8BCa0Q_AUoAXoECAwQAw&biw=1920&bih=916#imgrc=e3RTNXOlNoVsYM |
| Full analysis: | https://app.any.run/tasks/fde953bf-68c8-47cf-9e32-26617d0bcc48 |
| Verdict: | Malicious activity |
| Analysis date: | February 02, 2020, 10:49:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 641837DC6047BFD3DA9EC3D8AF095A10 |
| SHA1: | EED7D65365F4B79C797E5EA0F7812F705130E356 |
| SHA256: | D2A7444AE27EC8CB983CB835C6944B9E3D71E06786E424DDDAB64441D564D537 |
| SSDEEP: | 3:N8DSLIwAEXGpUEWzGu2d6IUWAgbspNbBkiD68okAdSoAvUTjfz3t5zW5:2OLIwBGKqd6IU8uN1hobpAvKTs |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 2856)
Reads Internet Cache Settings
- iexplore.exe (PID: 3728)
- iexplore.exe (PID: 2856)
Reads internet explorer settings
- iexplore.exe (PID: 3728)
Creates files in the user directory
- iexplore.exe (PID: 3728)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 3728)
Changes internet zones settings
- iexplore.exe (PID: 2856)
Reads settings of System Certificates
- iexplore.exe (PID: 3728)
- iexplore.exe (PID: 2856)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2856)
Changes settings of System certificates
- iexplore.exe (PID: 2856)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2856 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.google.com/search?q=psycholoszka&client=firefox-b-d&source=lnms&tbm=isch&sa=X&ved=2ahUKEwiX__7H17LnAhVSr4sKHT8BCa0Q_AUoAXoECAwQAw&biw=1920&bih=916#imgrc=e3RTNXOlNoVsYM" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3728 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2856 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
5 994
Read events
770
Write events
3 507
Delete events
1 717
Modification events
| (PID) Process: | (2856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2631508322 | |||
| (PID) Process: | (2856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30792118 | |||
| (PID) Process: | (2856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
42
Text files
39
Unknown types
23
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3728 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab6D78.tmp | — | |
MD5:— | SHA256:— | |||
| 3728 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar6D79.tmp | — | |
MD5:— | SHA256:— | |||
| 3728 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\WQ37RWQU.txt | — | |
MD5:— | SHA256:— | |||
| 3728 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\0JMY1J0X.txt | — | |
MD5:— | SHA256:— | |||
| 3728 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\N1UZ7L2E.txt | — | |
MD5:— | SHA256:— | |||
| 3728 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\AJBSQM5A.txt | — | |
MD5:— | SHA256:— | |||
| 3728 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\0OOJWKXC.txt | — | |
MD5:— | SHA256:— | |||
| 3728 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\PGXAICWX.txt | text | |
MD5:— | SHA256:— | |||
| 3728 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\BE8B021F9E811DFC8C8A28572A17C05A_B6E508CB345B95F29F504E60D228C8C1 | der | |
MD5:— | SHA256:— | |||
| 3728 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\search[1].htm | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
42
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3728 | iexplore.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCiHCV1WIxifQgAAAAAKZcn | US | der | 472 b | whitelisted |
3728 | iexplore.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQC84yJU1UcYQAgAAAAAKZdB | US | der | 472 b | whitelisted |
3728 | iexplore.exe | GET | 200 | 2.16.186.27:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgPoOCSRXUCq6Lj8Q4rwFinCnw%3D%3D | unknown | der | 527 b | whitelisted |
3728 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAKDNYJlYx4BMp3nlQdiIwE%3D | US | der | 471 b | whitelisted |
3728 | iexplore.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCiHCV1WIxifQgAAAAAKZcn | US | der | 472 b | whitelisted |
3728 | iexplore.exe | GET | 200 | 2.16.186.27:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgOg7AEY9MuY7XQN3%2FM9%2BGwulw%3D%3D | unknown | der | 527 b | whitelisted |
3728 | iexplore.exe | GET | 200 | 2.16.186.35:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
3728 | iexplore.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCIN%2FMcJ72F4QIAAAAAVXz7 | US | der | 472 b | whitelisted |
3728 | iexplore.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQC84yJU1UcYQAgAAAAAKZdB | US | der | 472 b | whitelisted |
3728 | iexplore.exe | GET | 200 | 2.16.186.27:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgPoOCSRXUCq6Lj8Q4rwFinCnw%3D%3D | unknown | der | 527 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3728 | iexplore.exe | 172.217.23.99:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3728 | iexplore.exe | 172.217.21.206:443 | apis.google.com | Google Inc. | US | whitelisted |
3728 | iexplore.exe | 172.217.18.174:443 | play.google.com | Google Inc. | US | whitelisted |
3728 | iexplore.exe | 172.217.23.132:443 | www.google.com | Google Inc. | US | whitelisted |
3728 | iexplore.exe | 216.58.208.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3728 | iexplore.exe | 95.211.149.171:443 | img2.dmty.pl | LeaseWeb Netherlands B.V. | NL | unknown |
3728 | iexplore.exe | 172.217.23.99:443 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3728 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3728 | iexplore.exe | 172.217.23.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| malicious |
ocsp.pki.goog |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
encrypted-tbn0.gstatic.com |
| whitelisted |
play.google.com |
| whitelisted |
i1.kwejk.pl |
| unknown |
isrg.trustid.ocsp.identrust.com |
| whitelisted |