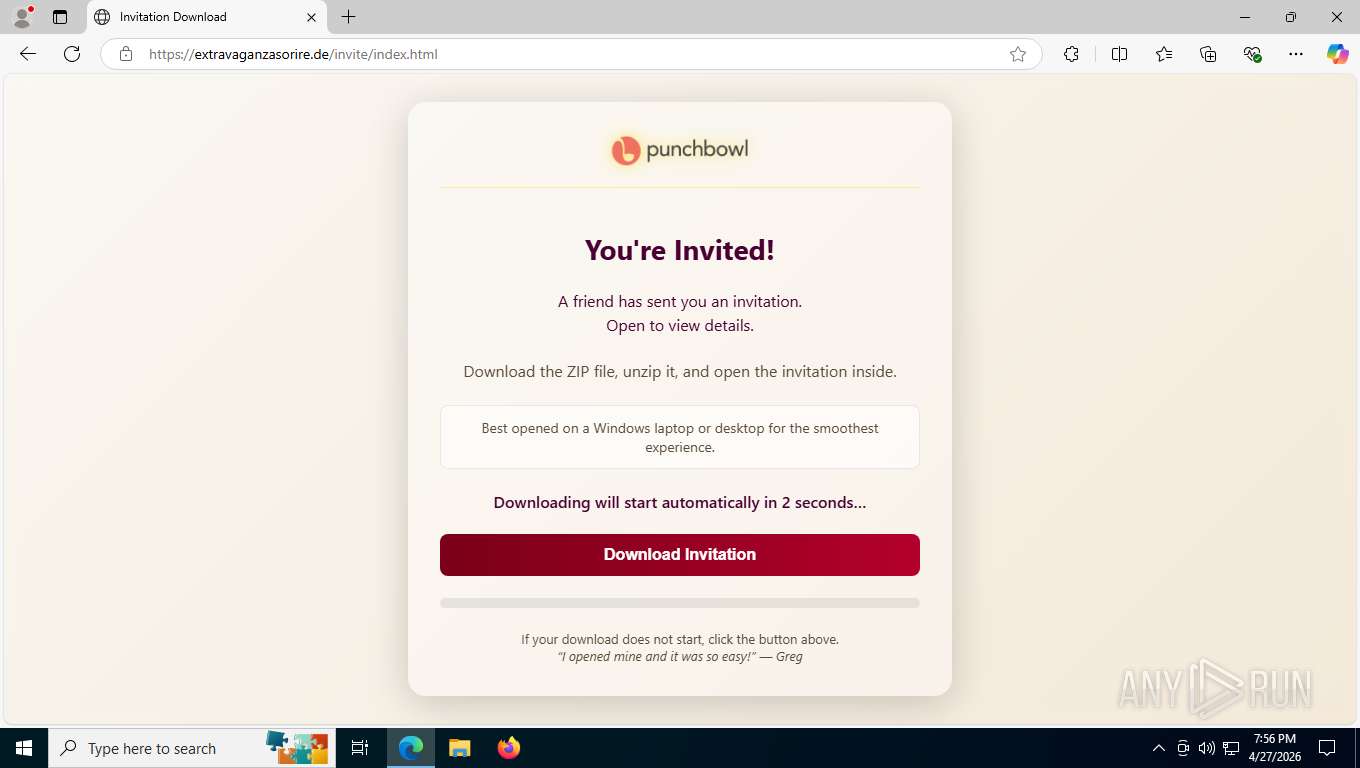
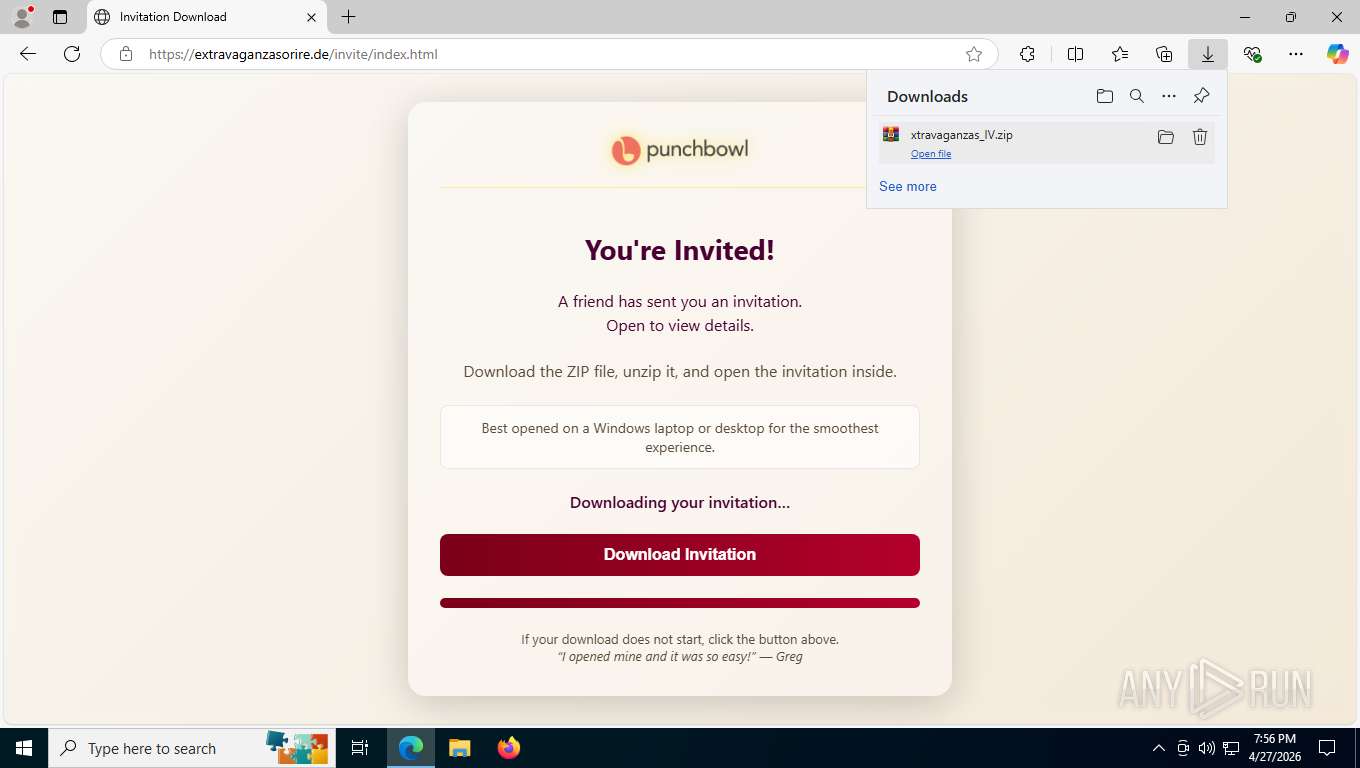
| URL: | https://extravaganzasorire.de/invite/index.html |
| Full analysis: | https://app.any.run/tasks/632cc946-781f-4124-845e-f2e53f11892e |
| Verdict: | Malicious activity |
| Analysis date: | April 27, 2026, 23:55:59 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
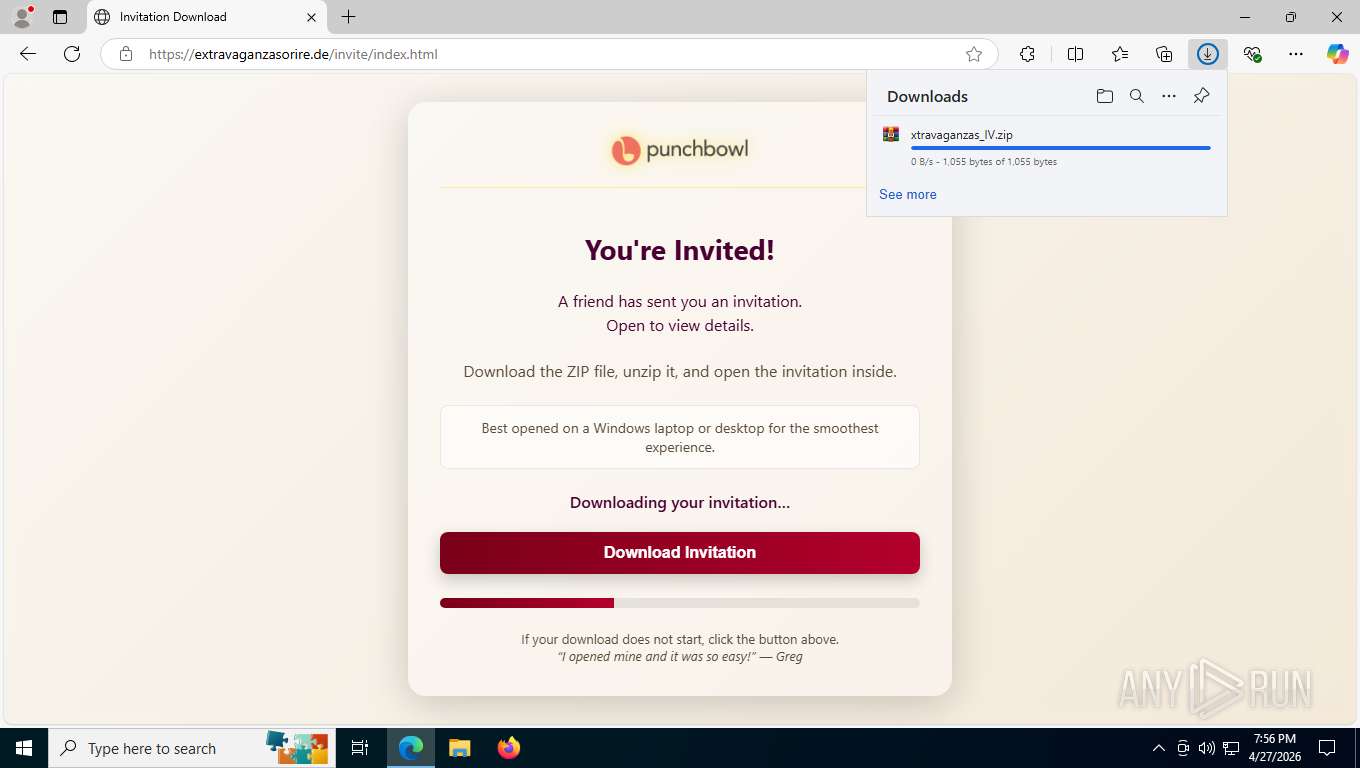
| MD5: | 4977EC55848121B74CA6A5A5D2393213 |
| SHA1: | D0EC8FDBFB47EE72026CF73C87519564631E38D2 |
| SHA256: | D2A6E31B35889E59402C0B250F91A66BC4A74285994FC04EF8D5EF7146E3D811 |
| SSDEEP: | 3:N89IC8EN2gML2d5G:2CC8EN2gK2DG |
MALICIOUS
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 9212)
- wscript.exe (PID: 8412)
Changes powershell execution policy (Bypass)
- wscript.exe (PID: 9212)
- wscript.exe (PID: 8412)
Gets TEMP folder path (SCRIPT)
- wscript.exe (PID: 9212)
- wscript.exe (PID: 8412)
Gets a file object corresponding to the file in a specified path (SCRIPT)
- wscript.exe (PID: 9212)
- wscript.exe (PID: 8412)
SCREENCONNECT has been detected
- rundll32.exe (PID: 5404)
- msiexec.exe (PID: 9000)
- rundll32.exe (PID: 9080)
SCREENCONNECT has been detected (SURICATA)
- ScreenConnect.ClientService.exe (PID: 9168)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 9212)
Deletes a file (SCRIPT)
- wscript.exe (PID: 9212)
SUSPICIOUS
Application launched itself
- wscript.exe (PID: 9116)
- wscript.exe (PID: 8752)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 9116)
- wscript.exe (PID: 8752)
Runs shell command (SCRIPT)
- wscript.exe (PID: 9116)
- wscript.exe (PID: 9212)
- wscript.exe (PID: 8752)
- wscript.exe (PID: 8412)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 9116)
- wscript.exe (PID: 9212)
- wscript.exe (PID: 8412)
- wscript.exe (PID: 8752)
The process bypasses the loading of PowerShell profile settings
- wscript.exe (PID: 9212)
- wscript.exe (PID: 8412)
Probably download files using WebClient
- wscript.exe (PID: 9212)
- wscript.exe (PID: 8412)
Bypass execution policy to execute commands
- powershell.exe (PID: 8308)
- powershell.exe (PID: 9048)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 9212)
- wscript.exe (PID: 8412)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 9000)
Uses RUNDLL32.EXE to run a file without a DLL extension
- rundll32.exe (PID: 5404)
- rundll32.exe (PID: 9080)
Screenconnect has been detected
- msiexec.exe (PID: 9000)
- ScreenConnect.ClientService.exe (PID: 9168)
- ScreenConnect.ClientService.exe (PID: 9168)
- rundll32.exe (PID: 9080)
The process creates files with name similar to system file names
- msiexec.exe (PID: 9000)
Creates/Modifies COM task schedule object
- msiexec.exe (PID: 9000)
Executable content was dropped or overwritten
- rundll32.exe (PID: 5404)
- rundll32.exe (PID: 9080)
Executes as Windows Service
- ScreenConnect.ClientService.exe (PID: 9168)
SCREENCONNECT mutex has been found
- ScreenConnect.ClientService.exe (PID: 9168)
Creates or modifies Windows services
- ScreenConnect.ClientService.exe (PID: 9168)
Potential Corporate Privacy Violation
- ScreenConnect.ClientService.exe (PID: 9168)
INFO
Reads Environment values
- identity_helper.exe (PID: 1652)
Application launched itself
- msedge.exe (PID: 7804)
Checks supported languages
- identity_helper.exe (PID: 1652)
- msiexec.exe (PID: 9000)
- msiexec.exe (PID: 9080)
- msiexec.exe (PID: 9140)
- ScreenConnect.ClientService.exe (PID: 9168)
- ScreenConnect.WindowsClient.exe (PID: 7984)
- ScreenConnect.WindowsClient.exe (PID: 3580)
- msiexec.exe (PID: 9128)
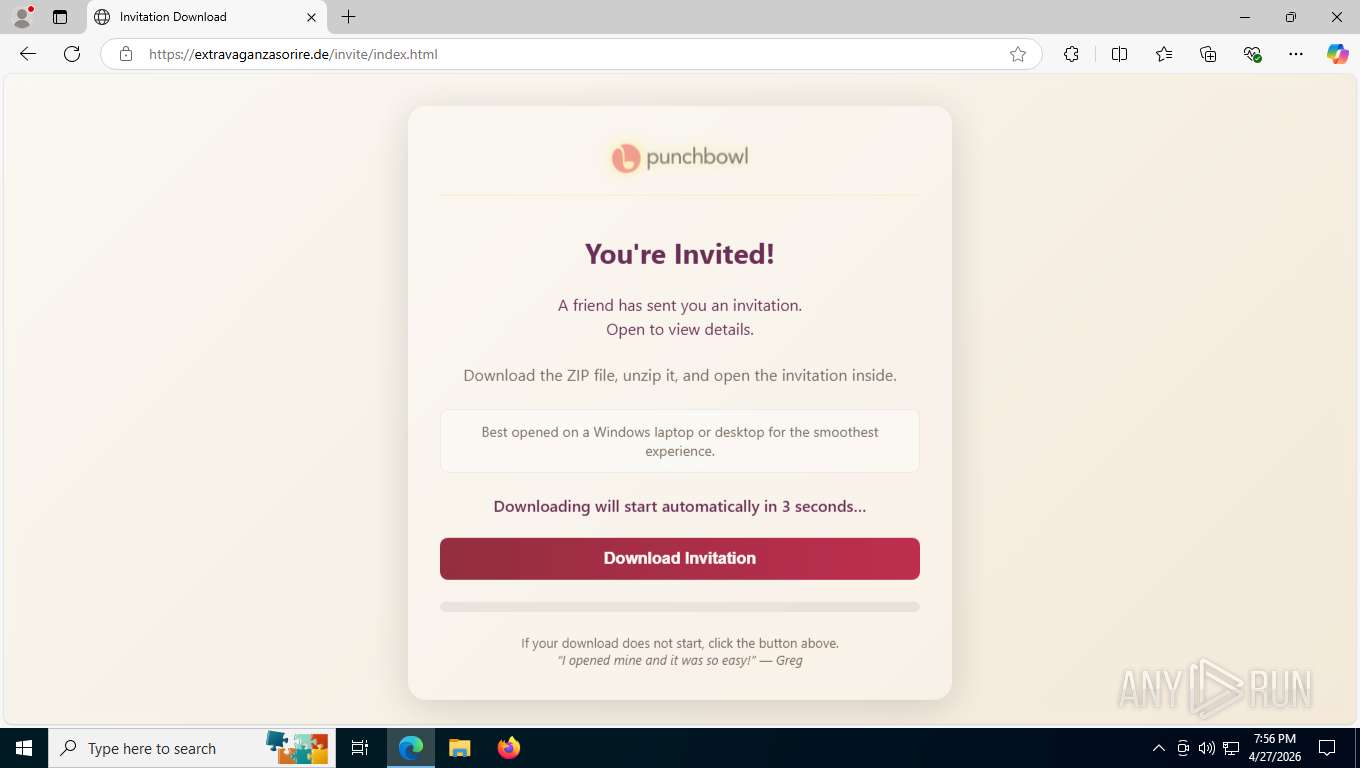
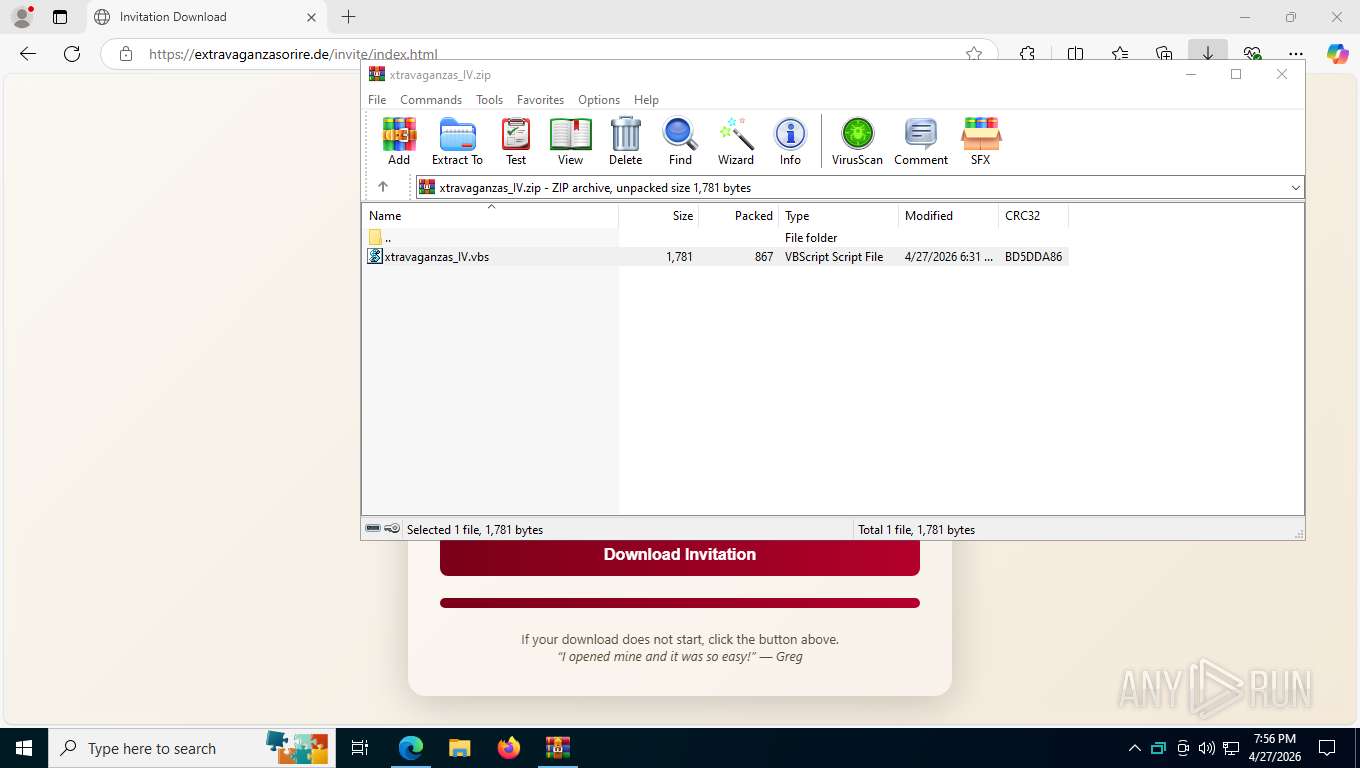
Launching a file from the Downloads directory
- msedge.exe (PID: 7804)
Reads the computer name
- identity_helper.exe (PID: 1652)
- msiexec.exe (PID: 9000)
- msiexec.exe (PID: 9080)
- msiexec.exe (PID: 9140)
- ScreenConnect.ClientService.exe (PID: 9168)
- ScreenConnect.WindowsClient.exe (PID: 7984)
- msiexec.exe (PID: 9128)
- ScreenConnect.WindowsClient.exe (PID: 3580)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 8956)
- ScreenConnect.ClientService.exe (PID: 9168)
- ScreenConnect.WindowsClient.exe (PID: 7984)
- ScreenConnect.WindowsClient.exe (PID: 3580)
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 8956)
CONNECTWISE has been detected
- msiexec.exe (PID: 9000)
- ScreenConnect.ClientService.exe (PID: 9168)
- ScreenConnect.WindowsClient.exe (PID: 7984)
- ScreenConnect.WindowsClient.exe (PID: 3580)
Reads the machine GUID from the registry
- msiexec.exe (PID: 9000)
- ScreenConnect.ClientService.exe (PID: 9168)
- ScreenConnect.WindowsClient.exe (PID: 7984)
- ScreenConnect.WindowsClient.exe (PID: 3580)
Creates files or folders in the user directory
- msiexec.exe (PID: 9000)
SCREENCONNECT has been detected
- msiexec.exe (PID: 9000)
- ScreenConnect.ClientService.exe (PID: 9168)
- ScreenConnect.ClientService.exe (PID: 9168)
- rundll32.exe (PID: 9080)
Executable content was dropped or overwritten
- msiexec.exe (PID: 9000)
Creates a software uninstall entry
- msiexec.exe (PID: 9000)
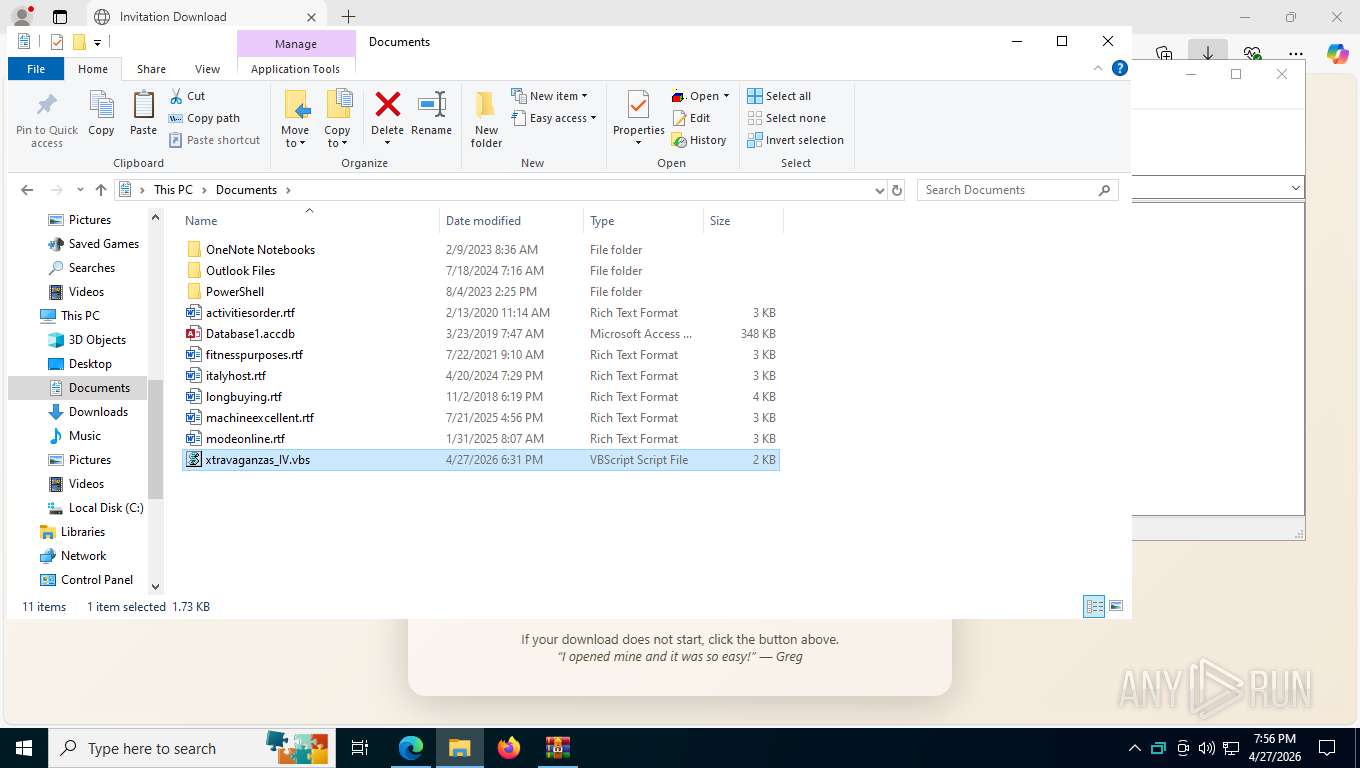
Manual execution by a user
- wscript.exe (PID: 8752)
Reads CPU info
- ScreenConnect.WindowsClient.exe (PID: 3580)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
185
Monitored processes
47
Malicious processes
9
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1180 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3400,i,14399494521543090688,5749311289286199955,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=3628 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1652 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6136,i,14399494521543090688,5749311289286199955,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=4072 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2316 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=10 --always-read-main-dll --field-trial-handle=4060,i,14399494521543090688,5749311289286199955,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5500 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3340 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x294,0x298,0x29c,0x28c,0x2a4,0x7ffe2392f208,0x7ffe2392f214,0x7ffe2392f220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3580 | "C:\Program Files (x86)\ScreenConnect Client (4540bdb08fe4a553)\ScreenConnect.WindowsClient.exe" "RunRole" "88677e52-df25-47f6-a949-26dcea849050" "System" | C:\Program Files (x86)\ScreenConnect Client (4540bdb08fe4a553)\ScreenConnect.WindowsClient.exe | — | ScreenConnect.ClientService.exe | |||||||||||
User: SYSTEM Company: ScreenConnect Software Integrity Level: SYSTEM Description: ScreenConnect Client Exit code: 0 Version: 26.1.24.9579 Modules
| |||||||||||||||
| 3996 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2128,i,14399494521543090688,5749311289286199955,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=2744 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4324 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2324,i,14399494521543090688,5749311289286199955,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=2344 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 5404 | rundll32.exe "C:\WINDOWS\Installer\MSI7DB7.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_949828 2 ScreenConnect.InstallerActions!ScreenConnect.ClientInstallerActions.FixupServiceArguments | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5616 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6480,i,14399494521543090688,5749311289286199955,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6472 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
21 426
Read events
21 313
Write events
104
Delete events
9
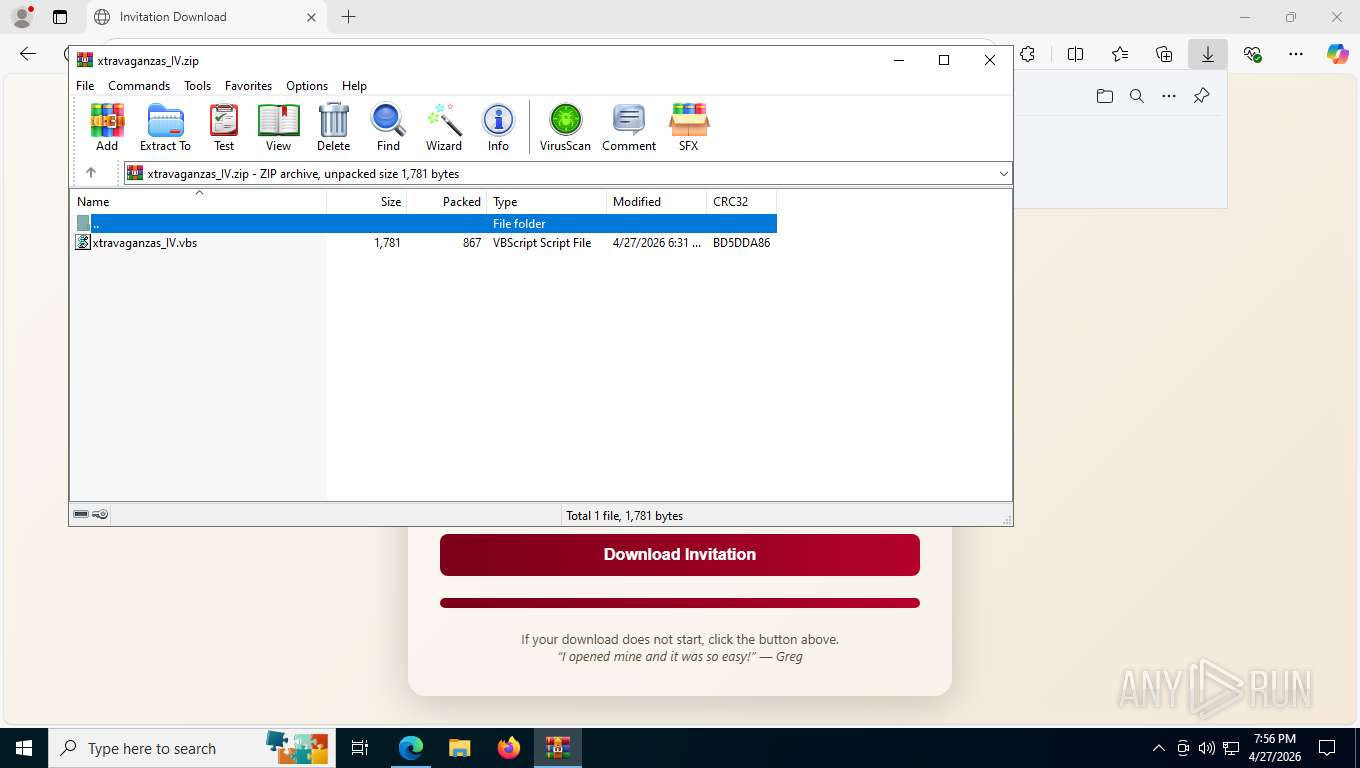
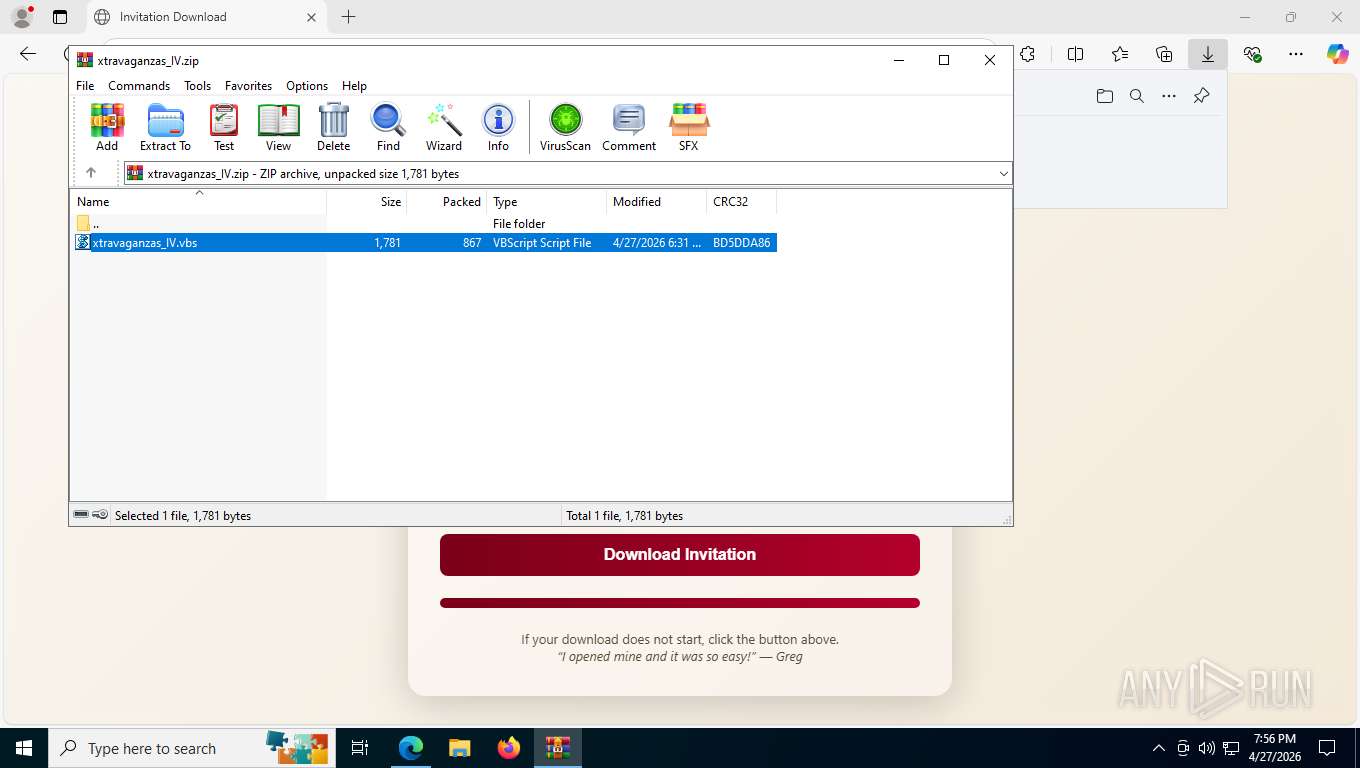
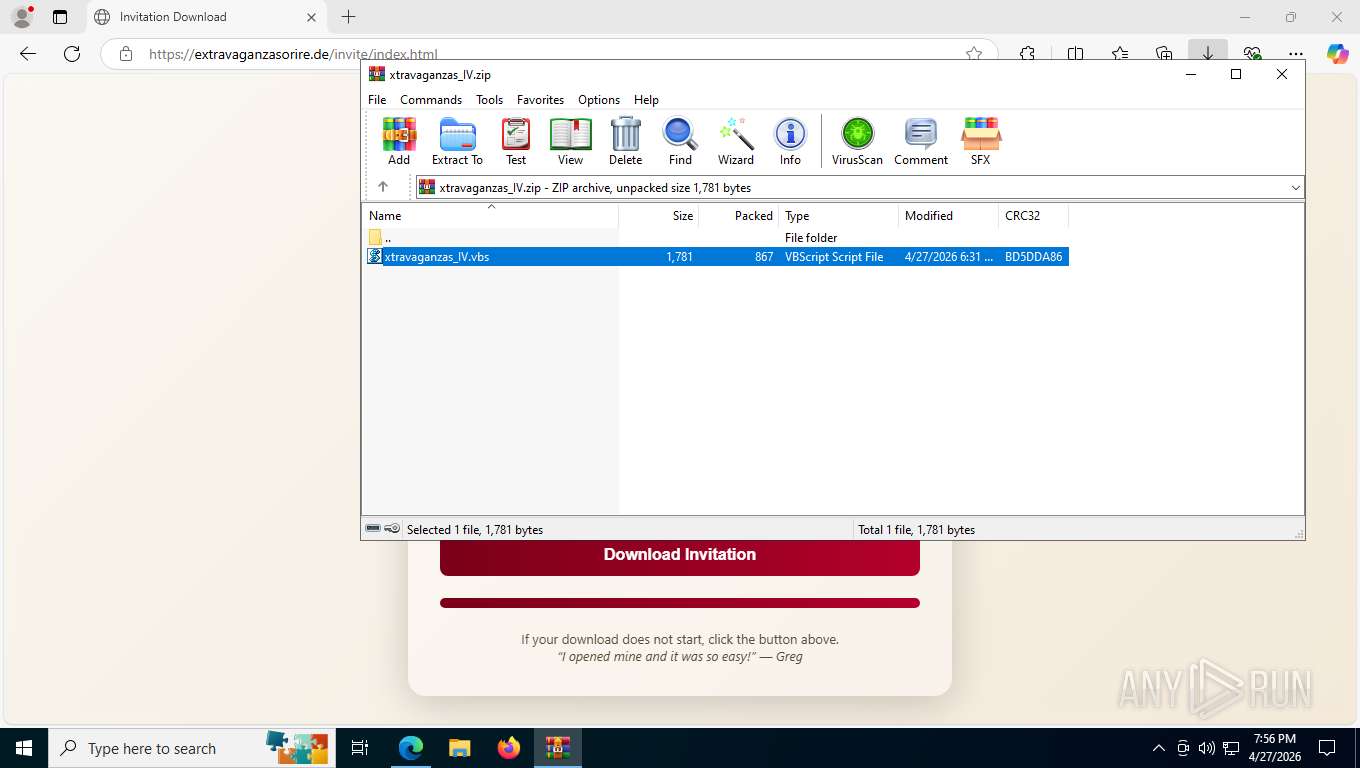
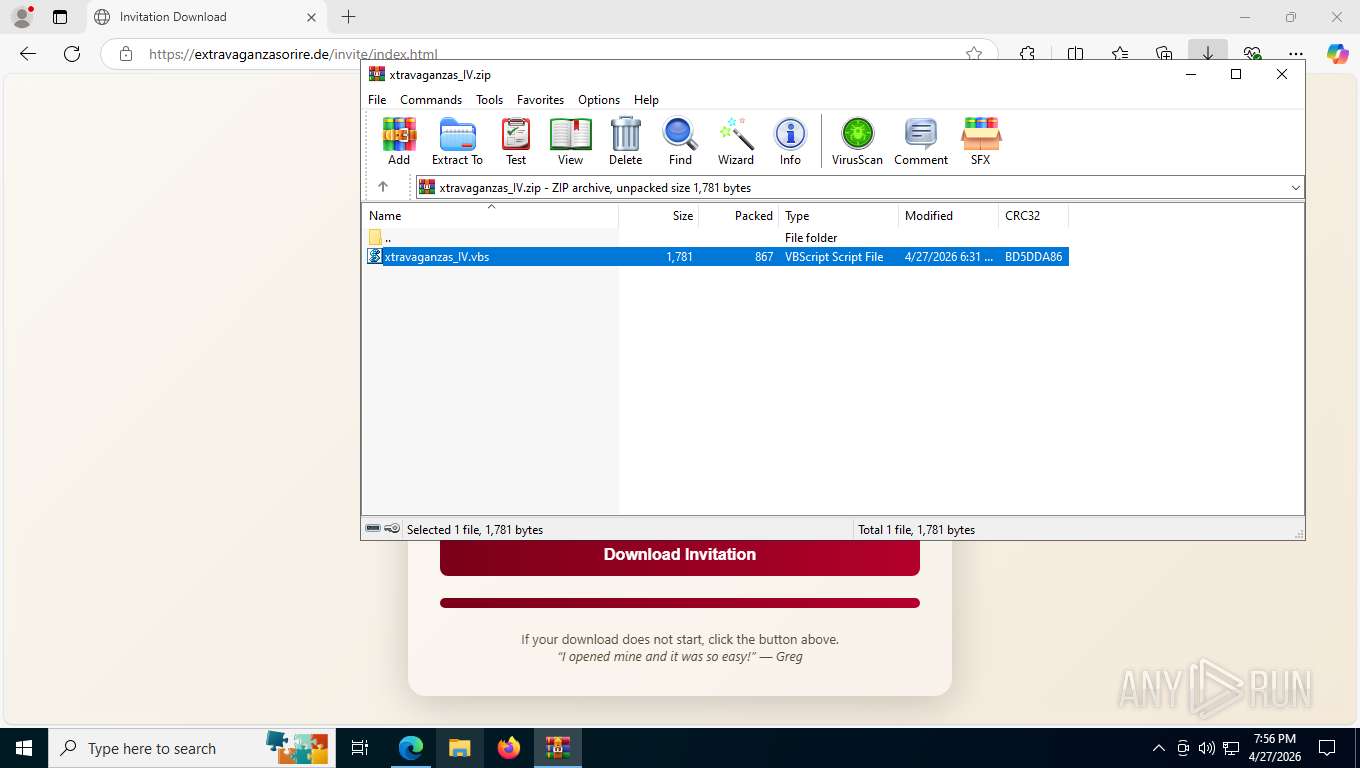
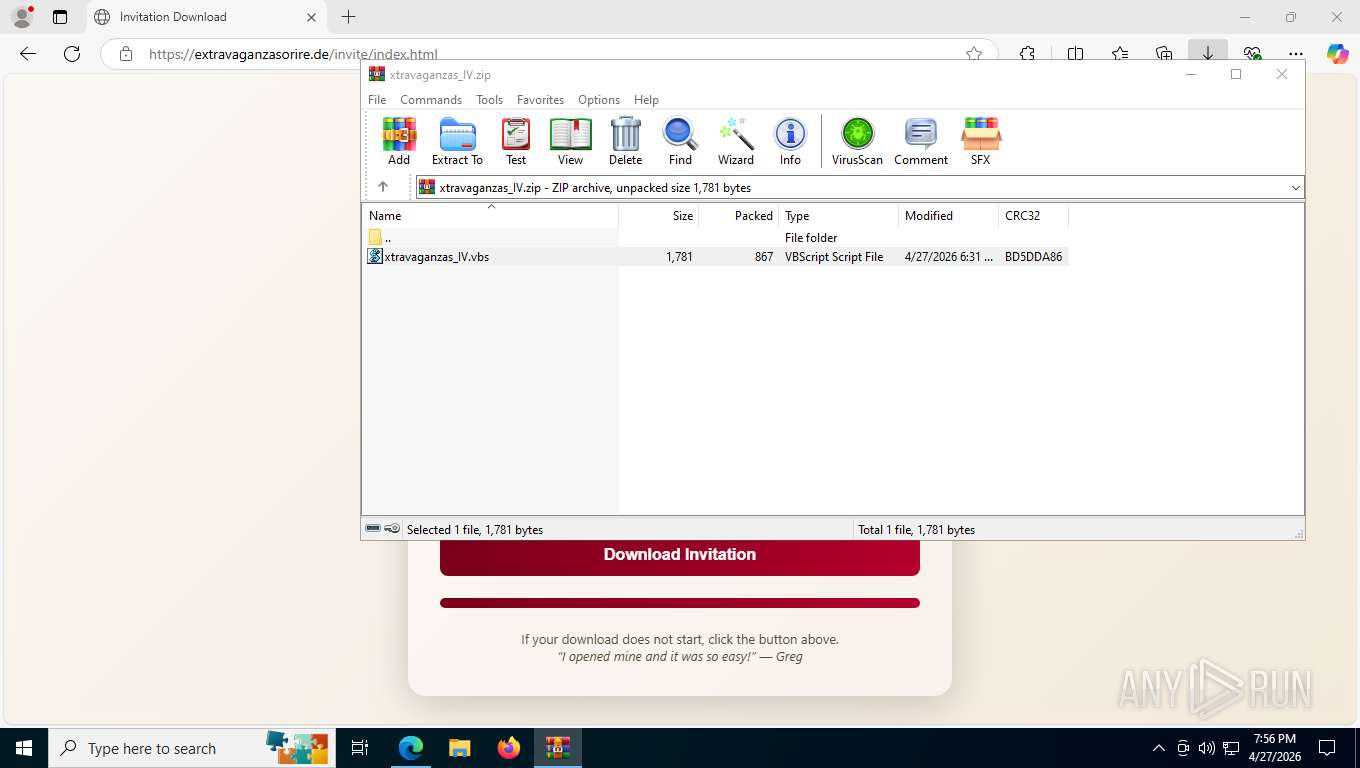
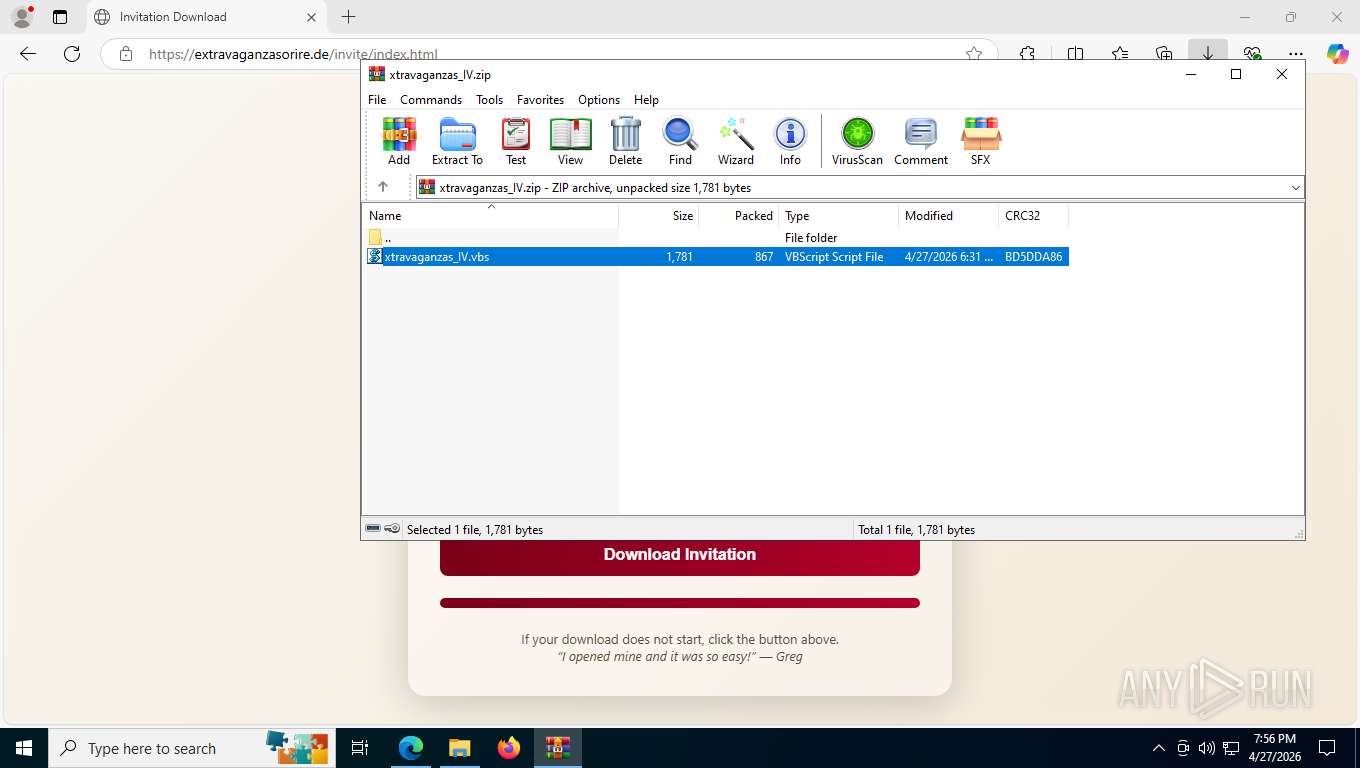
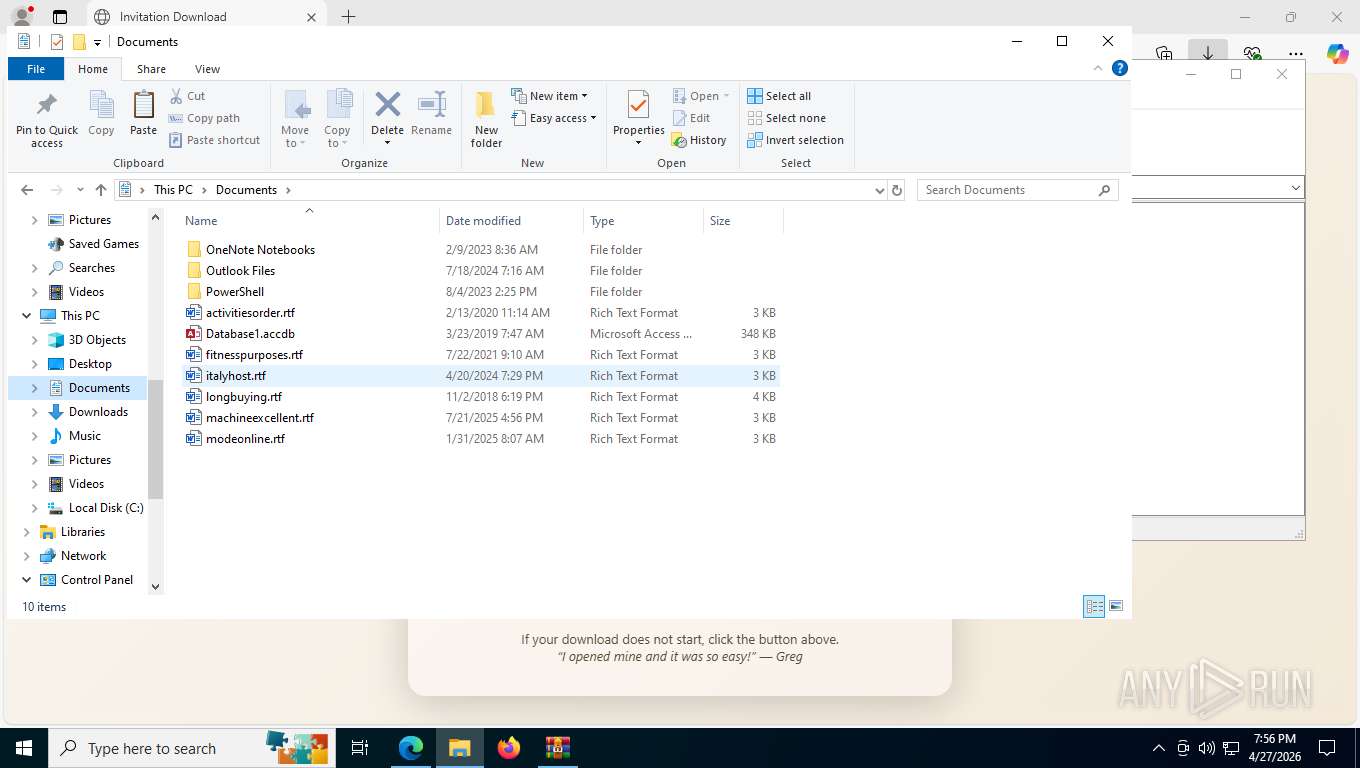
Modification events
| (PID) Process: | (8956) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3d\52C64B7E |
| Operation: | write | Name: | @C:\WINDOWS\System32\wshext.dll,-4802 |
Value: VBScript Script File | |||
| (PID) Process: | (8956) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (8956) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (8956) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Downloads\chromium_build 1.zip | |||
| (PID) Process: | (8956) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\xtravaganzas_IV.zip | |||
| (PID) Process: | (8956) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (8956) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (8956) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (8956) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (8956) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.vbs\OpenWithProgids |
| Operation: | write | Name: | VBSFile |
Value: | |||
Executable files
31
Suspicious files
77
Text files
251
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7804 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RFdffad.TMP | — | |
MD5:— | SHA256:— | |||
| 7804 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFdffbd.TMP | — | |
MD5:— | SHA256:— | |||
| 7804 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7804 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFdffbd.TMP | — | |
MD5:— | SHA256:— | |||
| 7804 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7804 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RFdffbd.TMP | — | |
MD5:— | SHA256:— | |||
| 7804 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7804 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFdffbd.TMP | — | |
MD5:— | SHA256:— | |||
| 7804 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7804 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RFdfffc.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
84
TCP/UDP connections
68
DNS requests
66
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6472 | msedge.exe | OPTIONS | 200 | 35.190.80.1:443 | https://a.nel.cloudflare.com/report/v4?s=74sYEfeZESc3EmgbwNJlpAZRFtd%2BuzaGVSE6n6bjKJrBoDAuNNzy9BfIHVChqBFVPG0rbs70y8m5zH%2FyzB9mzpyc99J0j0S5Y6s0spW4pGiMANJukxty7QNjaSXv2GVYdyIAGOCzYN4%3D | US | — | — | unknown |
6472 | msedge.exe | GET | 302 | 188.114.96.3:443 | https://extravaganzasorire.de/favicon.ico | US | — | — | unknown |
6472 | msedge.exe | GET | 302 | 188.114.96.3:443 | https://extravaganzasorire.de/favicon.ico | US | — | — | unknown |
— | — | GET | 200 | 162.159.142.9:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | US | binary | 312 b | whitelisted |
— | — | GET | 200 | 131.253.33.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ3L3%2F%2Fa6ADK8NraY2GXzVaYrHG4AQUb6t%2B2v%2BXQ3LsO2d33oJhNYhHQoUCEzMAAAAGb6JMMcOVb6sAAAAAAAY%3D | US | binary | 922 b | whitelisted |
6472 | msedge.exe | GET | 403 | 188.114.96.3:443 | https://extravaganzasorire.de/invite/index.html | US | html | 5.88 Kb | unknown |
6472 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=67&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1777334166&lafgdate=0 | US | text | 4.45 Kb | whitelisted |
6472 | msedge.exe | GET | 304 | 150.171.27.11:443 | https://edge.microsoft.com/abusiveadblocking/api/v1/blocklist | US | — | — | whitelisted |
6472 | msedge.exe | GET | 403 | 188.114.96.3:443 | https://extravaganzasorire.de/invite/index.html | US | html | 5.69 Kb | unknown |
6472 | msedge.exe | GET | 200 | 104.18.23.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | US | text | 25 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
5276 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 48.192.1.65:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
680 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 2.16.204.141:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 162.159.142.9:80 | ocsp.digicert.com | CLOUDFLARENET | US | whitelisted |
— | — | 131.253.33.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
6472 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6472 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
activation-v2.sls.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
extravaganzasorire.de |
| unknown |
api.edgeoffer.microsoft.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
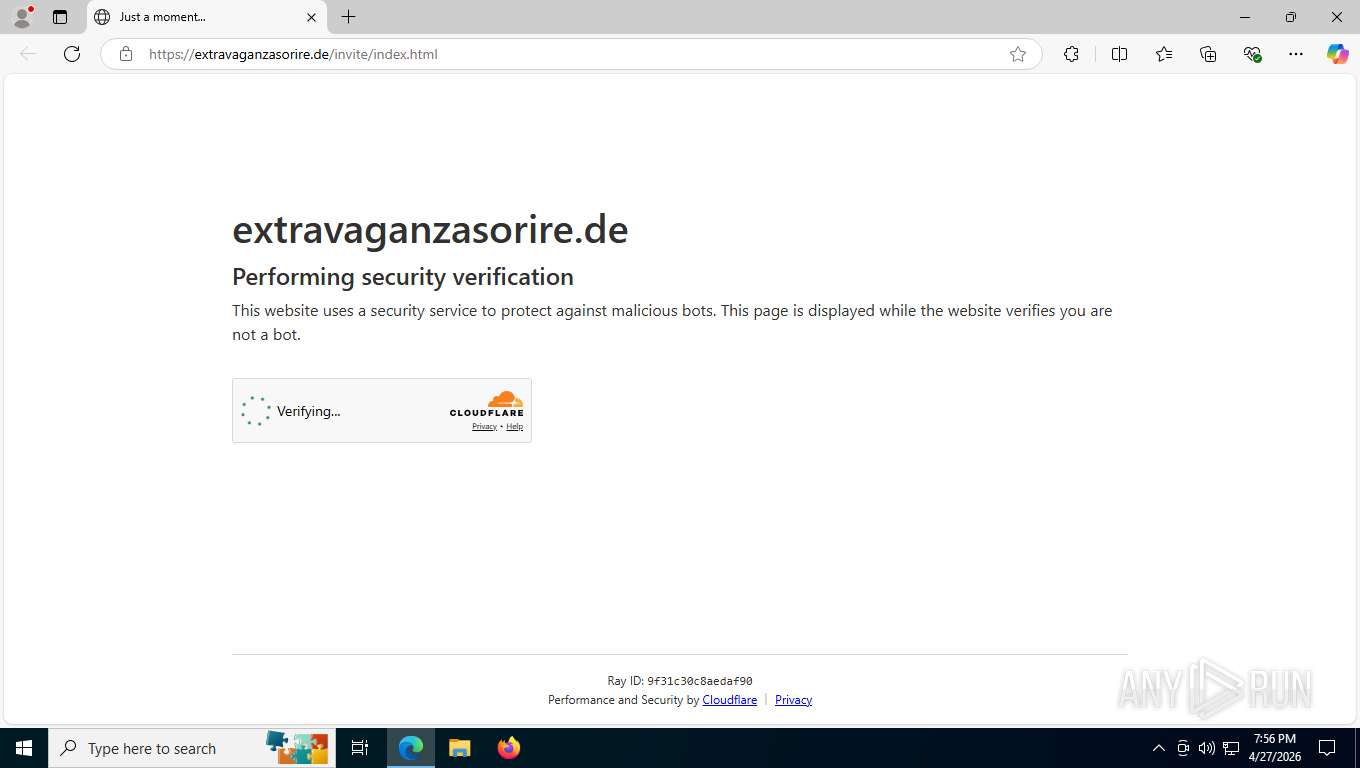
6472 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
6472 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
6472 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
6472 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
6472 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
6472 | msedge.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Challenge-Platform Page Request to cdn-cgi |
680 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
6472 | msedge.exe | Misc activity | INFO [ANY.RUN] Possible short link service (u .to) |
6472 | msedge.exe | Misc activity | INFO [ANY.RUN] Possible short link service (u .to) |
6472 | msedge.exe | Misc activity | ET INFO URL Shortener Service Domain in DNS Lookup (u .to) |