| File name: | Result.exe |
| Full analysis: | https://app.any.run/tasks/999ae2cf-4aee-42b0-aca2-15dd586e7bcd |
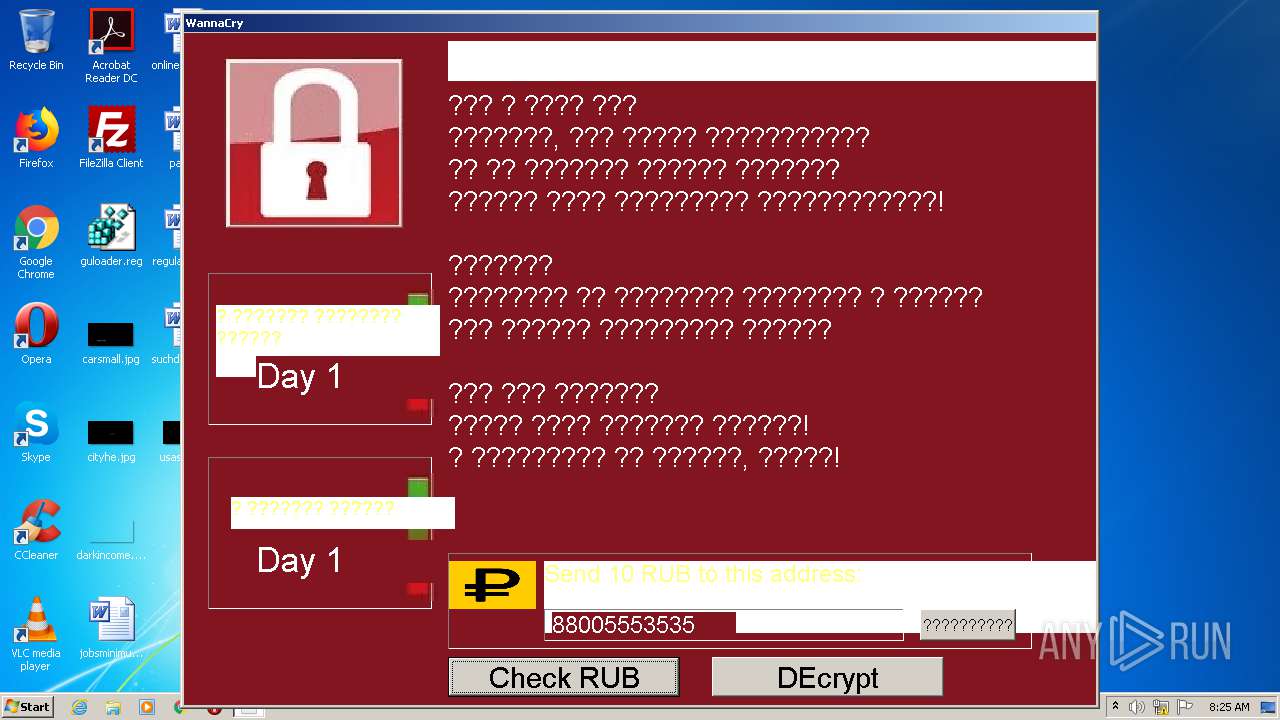
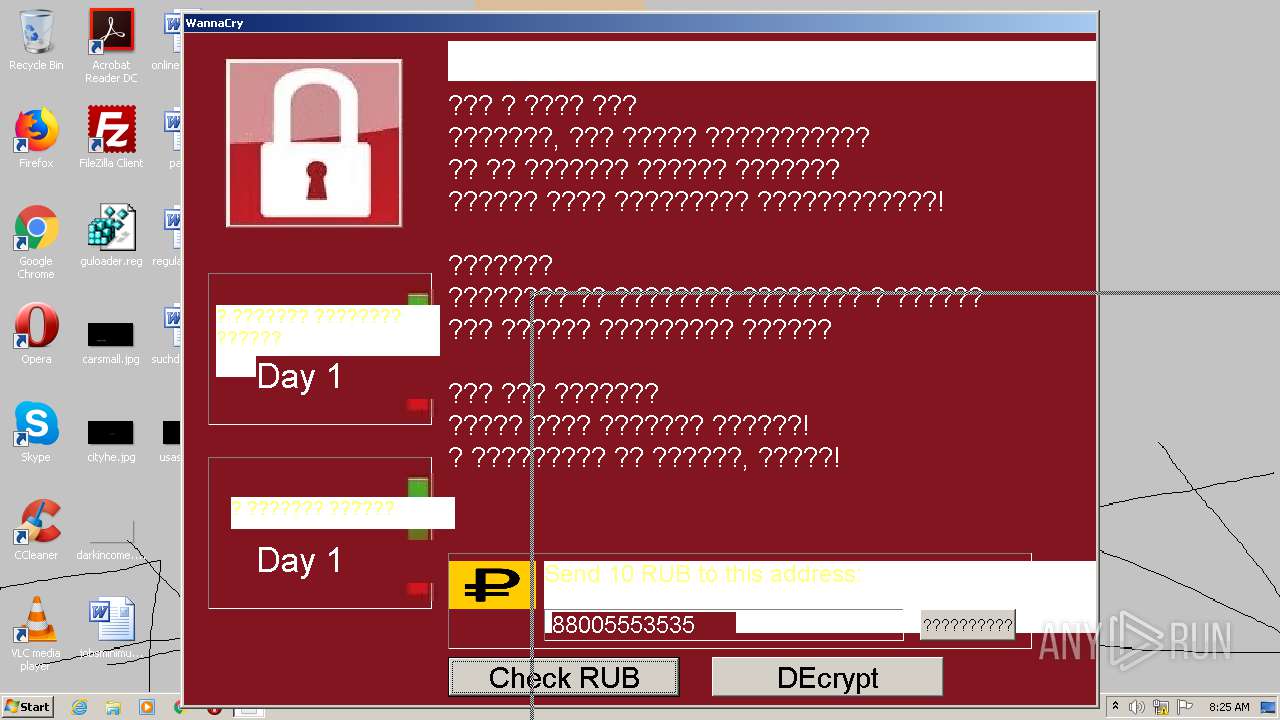
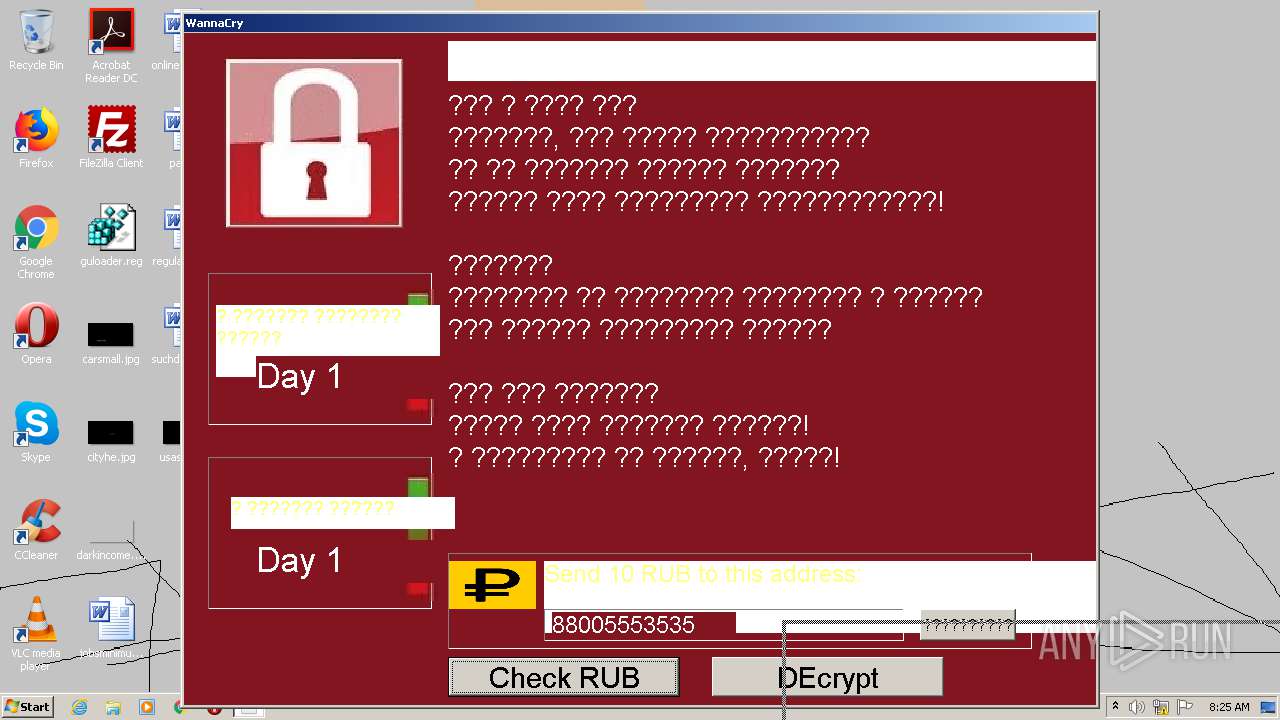
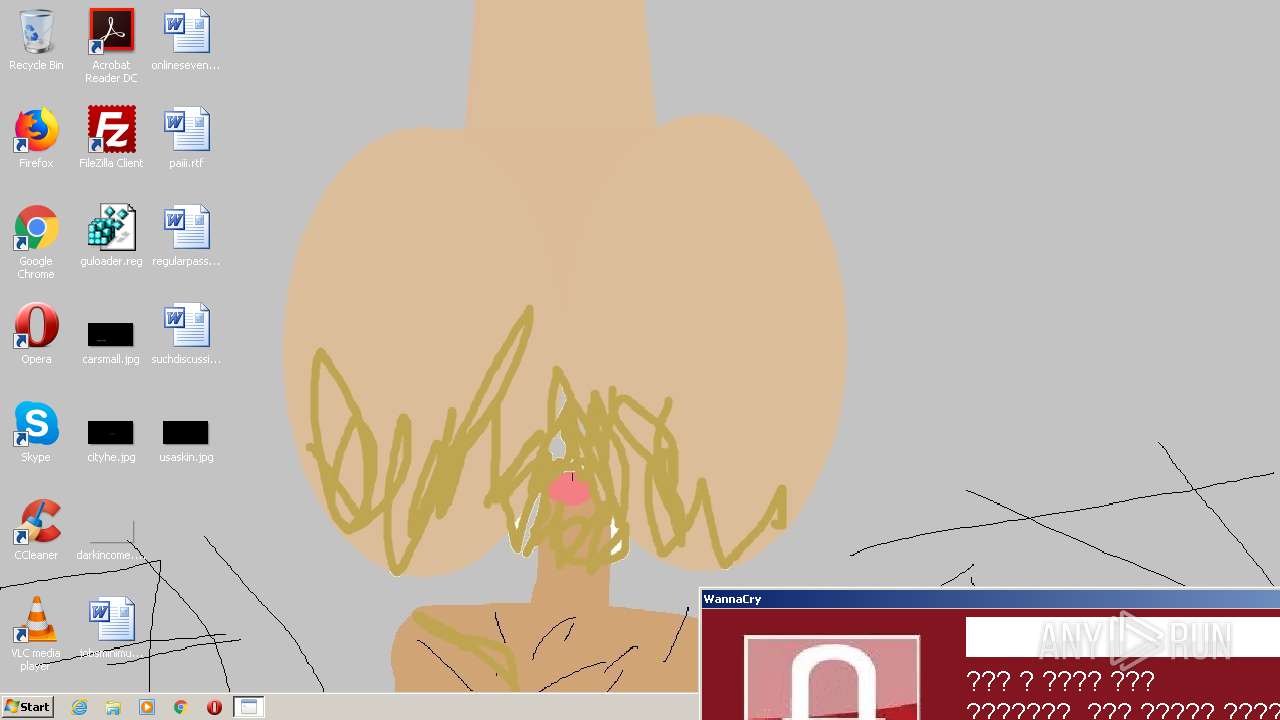
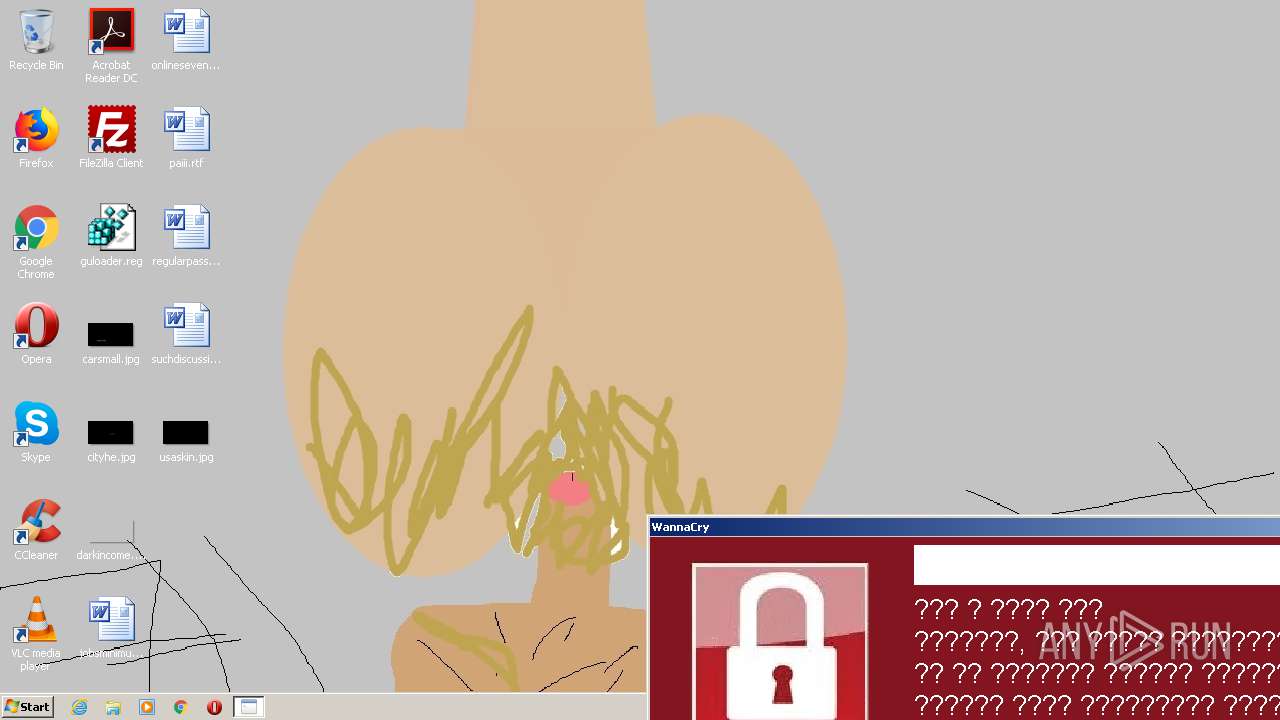
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2020, 08:25:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | A8E460F5084F8D4F6F9BD68E159F4606 |
| SHA1: | 14263F14F9DF330817791F4F6173C6273162B020 |
| SHA256: | D297E77C023AEF46E9FBA5D0190BBBB4DA6838C846CED00EA32E038EAF57329E |
| SSDEEP: | 98304:hqB4rJ4v8kvT7GdoV0EEgzMNscEz9JpRyG:84r+0kvT7tVnEGMNscEL |
MALICIOUS
Drops executable file immediately after starts
- Result.exe (PID: 2444)
- build.exe (PID: 1980)
- Desktop.exe (PID: 2228)
- WannaLol.exe (PID: 3316)
Application was dropped or rewritten from another process
- build.exe (PID: 1980)
- Desktop.exe (PID: 2228)
- vidzet.exe (PID: 924)
- WannaLol.exe (PID: 3316)
Loads dropped or rewritten executable
- WannaLol.exe (PID: 3316)
- vidzet.exe (PID: 924)
SUSPICIOUS
Executable content was dropped or overwritten
- Result.exe (PID: 2444)
- Desktop.exe (PID: 2228)
- build.exe (PID: 1980)
- WannaLol.exe (PID: 3316)
Drops a file with too old compile date
- build.exe (PID: 1980)
- WannaLol.exe (PID: 3316)
Drops a file that was compiled in debug mode
- Desktop.exe (PID: 2228)
- Result.exe (PID: 2444)
- WannaLol.exe (PID: 3316)
Drops a file with a compile date too recent
- Desktop.exe (PID: 2228)
Reads Environment values
- vidzet.exe (PID: 924)
INFO
Dropped object may contain Bitcoin addresses
- WannaLol.exe (PID: 3316)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (53.2) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (17.5) |
| .scr | | | Windows screen saver (16.1) |
| .exe | | | Win32 Executable (generic) (5.5) |
| .exe | | | Win16/32 Executable Delphi generic (2.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 5120 |
| InitializedDataSize: | 3495424 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x20cc |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x000013B8 | 0x00001400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.34099 |
DATA | 0x00003000 | 0x0000007C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.11763 |
BSS | 0x00004000 | 0x00000695 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00005000 | 0x00000302 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.47732 |
.tls | 0x00006000 | 0x00000004 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00007000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.199108 |
.reloc | 0x00008000 | 0x000001C8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 5.7833 |
.rsrc | 0x00009000 | 0x00354A70 | 0x00354C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 7.91224 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
A1 | 7.96432 | 3021501 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
A2 | 7.32039 | 470183 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
B1 | 2.9477 | 9 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
B2 | 3.02717 | 11 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
C1 | 0 | 1 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
C2 | 0 | 1 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
D1 | 0 | 1 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
D2 | 0 | 1 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
DVCLAL | 4 | 16 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
E1 | 0 | 1 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
kernel32.dll |
shell32.dll |
shfolder.dll |
Total processes
37
Monitored processes
5
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 924 | "C:\Users\admin\AppData\Local\Temp\RarSFX1\vidzet.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX1\vidzet.exe | Desktop.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4294967295 Modules
| |||||||||||||||
| 1980 | "C:\Users\admin\AppData\Local\Temp\build.exe" | C:\Users\admin\AppData\Local\Temp\build.exe | Result.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2228 | "C:\Users\admin\AppData\Local\Temp\Desktop.exe" | C:\Users\admin\AppData\Local\Temp\Desktop.exe | Result.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2444 | "C:\Users\admin\AppData\Local\Temp\Result.exe" | C:\Users\admin\AppData\Local\Temp\Result.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3316 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\WannaLol.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\WannaLol.exe | build.exe | ||||||||||||
User: admin Company: Todes Integrity Level: MEDIUM Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
1 178
Read events
1 136
Write events
42
Delete events
0
Modification events
| (PID) Process: | (2444) Result.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2444) Result.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2228) Desktop.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2228) Desktop.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1980) build.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1980) build.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (924) vidzet.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\vidzet_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (924) vidzet.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\vidzet_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (924) vidzet.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\vidzet_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (924) vidzet.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\vidzet_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
9
Suspicious files
1
Text files
6
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3316 | WannaLol.exe | C:\Users\admin\AppData\Local\Temp\PSE11\93A066E5CB4B9B4F98D1FE20DFCC21E8\php.ini | — | |
MD5:— | SHA256:— | |||
| 2228 | Desktop.exe | C:\Users\admin\AppData\Local\Temp\RarSFX1\vidzet.sb | text | |
MD5:— | SHA256:— | |||
| 924 | vidzet.exe | C:\Users\admin\AppData\Local\Temp\tmp7CE.tmp | image | |
MD5:— | SHA256:— | |||
| 2228 | Desktop.exe | C:\Users\admin\AppData\Local\Temp\RarSFX1\vidzet.exe | executable | |
MD5:— | SHA256:— | |||
| 1980 | build.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\WannaLol.exe | executable | |
MD5:— | SHA256:— | |||
| 924 | vidzet.exe | C:\Users\admin\AppData\Local\Temp\tmp7CF.tmp | image | |
MD5:— | SHA256:— | |||
| 2444 | Result.exe | C:\Users\admin\AppData\Local\Temp\Desktop.exe | executable | |
MD5:— | SHA256:— | |||
| 2228 | Desktop.exe | C:\Users\admin\AppData\Local\Temp\RarSFX1\vidzet.pdb | pdb | |
MD5:— | SHA256:— | |||
| 1980 | build.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\msvcr71.dll | executable | |
MD5:5776A4EF7F492636C052AE64B35BF4CE | SHA256:42DED6072E28ED5394B0A832A0559B8E618490764F2490DBEDCF7E5479537573 | |||
| 2228 | Desktop.exe | C:\Users\admin\AppData\Local\Temp\RarSFX1\SmallBasicLibrary.dll | executable | |
MD5:249B207E3FE4CD1DF5242EAE28404F52 | SHA256:4EA0823AA7A754719E751BA044468428BC7BC428A434F634AB6D405F6CCFAEEF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
924 | vidzet.exe | 87.240.185.168:443 | sun9-69.userapi.com | VKontakte Ltd | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
sun9-69.userapi.com |
| whitelisted |