| File name: | Download File Instagram Data Extractor._841028.exe |
| Full analysis: | https://app.any.run/tasks/b90d000b-7d11-45af-8455-282d50c63137 |
| Verdict: | Malicious activity |
| Analysis date: | October 03, 2020, 16:34:17 |
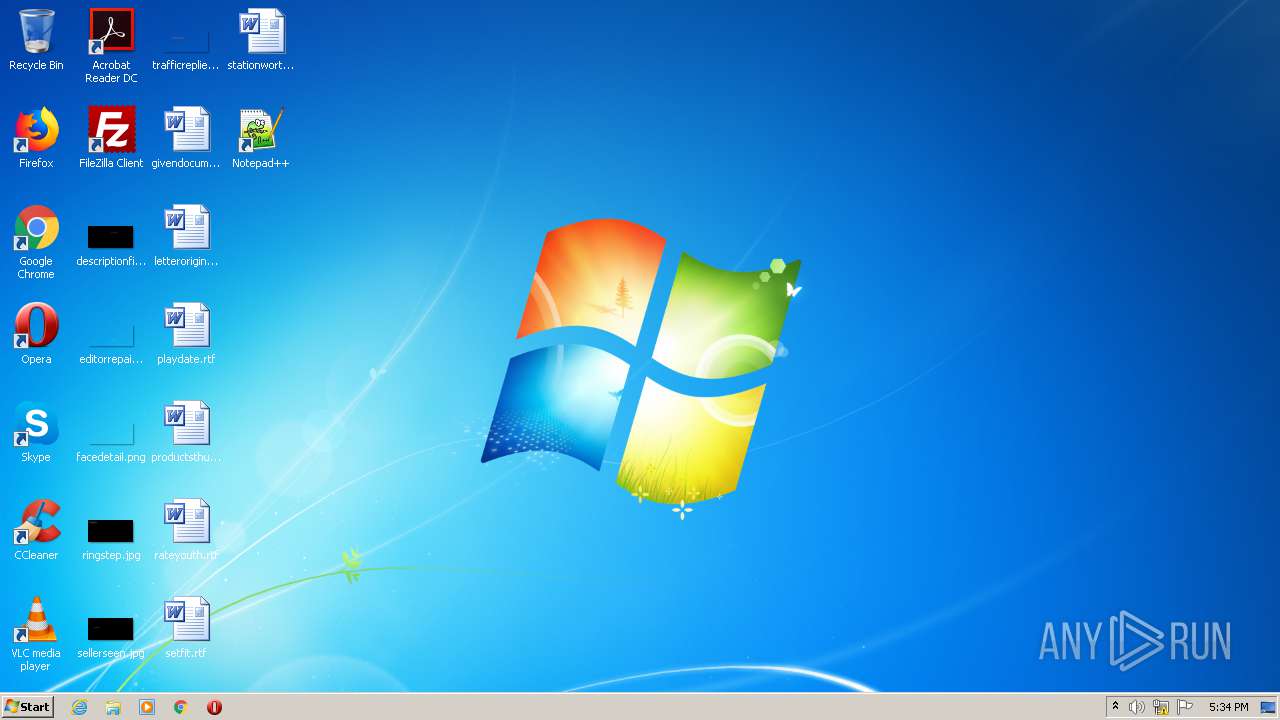
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | CCD1003162F51DF087E46D4F412B51A6 |
| SHA1: | 43C5722A6F30921620788F8BD52B3C60E42B26D4 |
| SHA256: | D29380831B7A5B62C0D56E0D2A7A196863FF1C3199434172EE199A36CB929312 |
| SSDEEP: | 24576:DM56iBSerDcK8AHqmn+WKStr9izQsEs8QoiiyhqDe0:DKZBSe3c5kAEB9gjoinQD5 |
MALICIOUS
Changes settings of System certificates
- Download File Instagram Data Extractor._841028.exe (PID: 996)
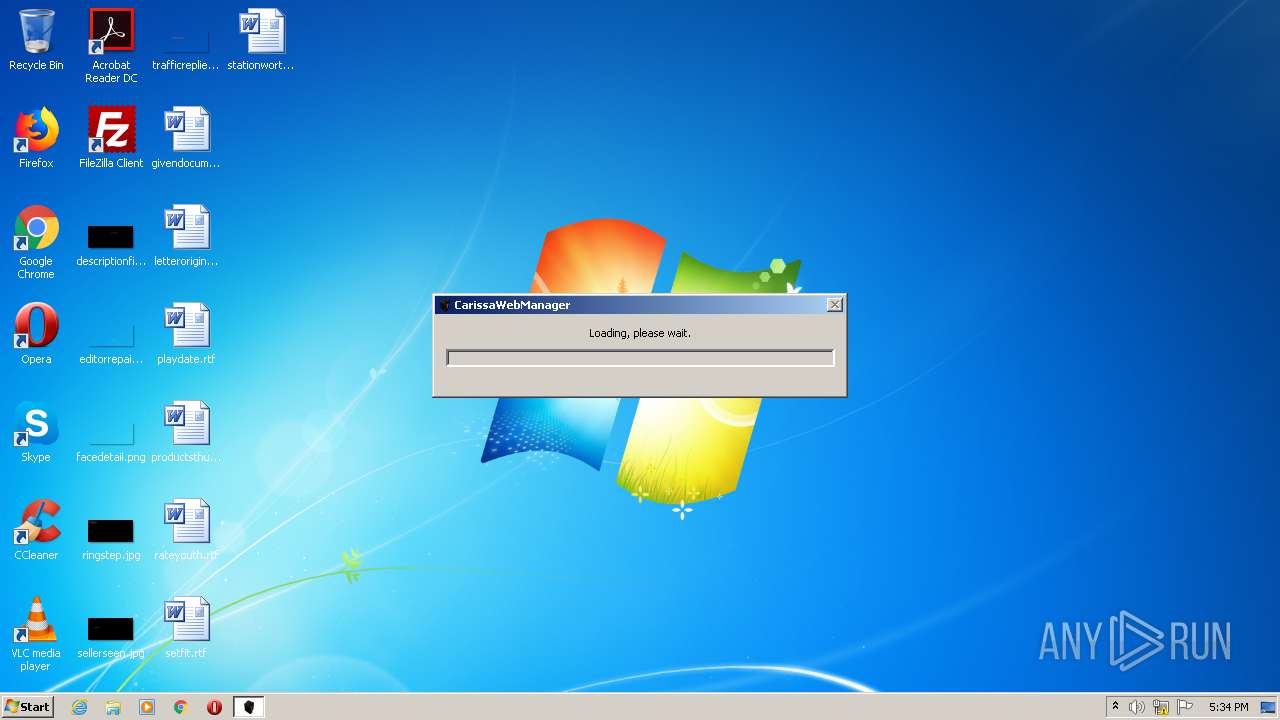
Application was dropped or rewritten from another process
- CarissauWeb.exe (PID: 292)
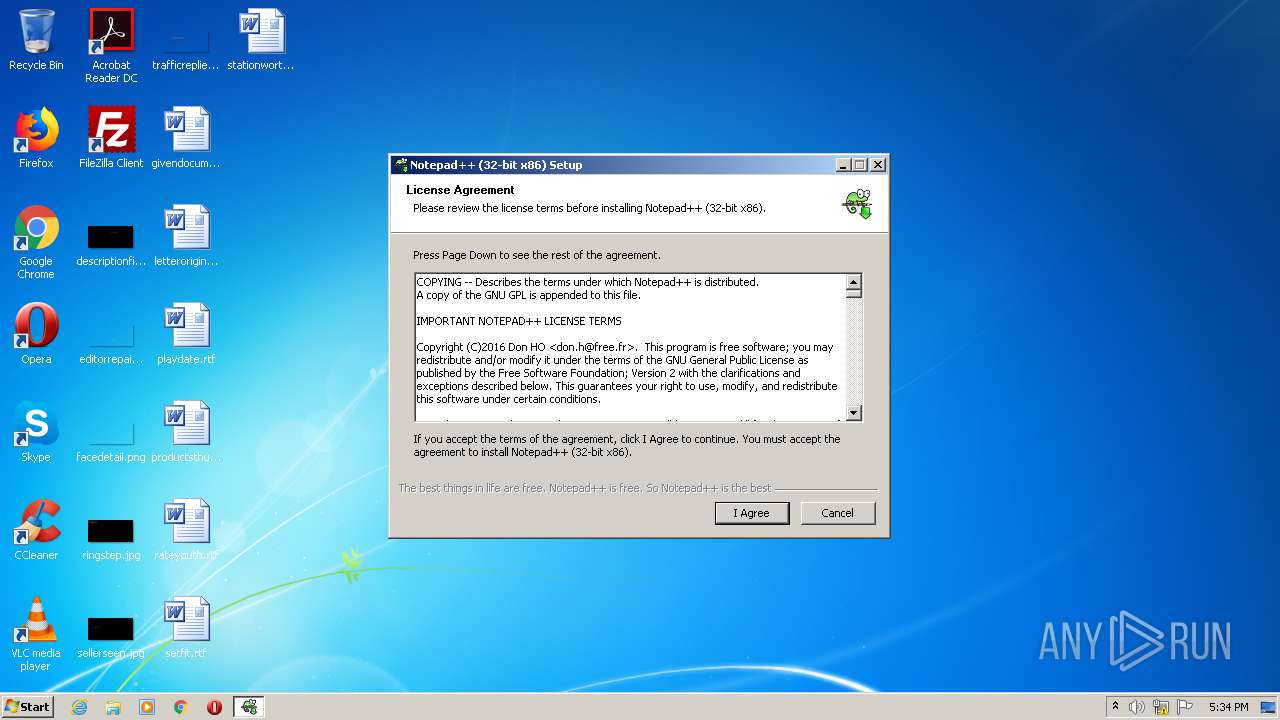
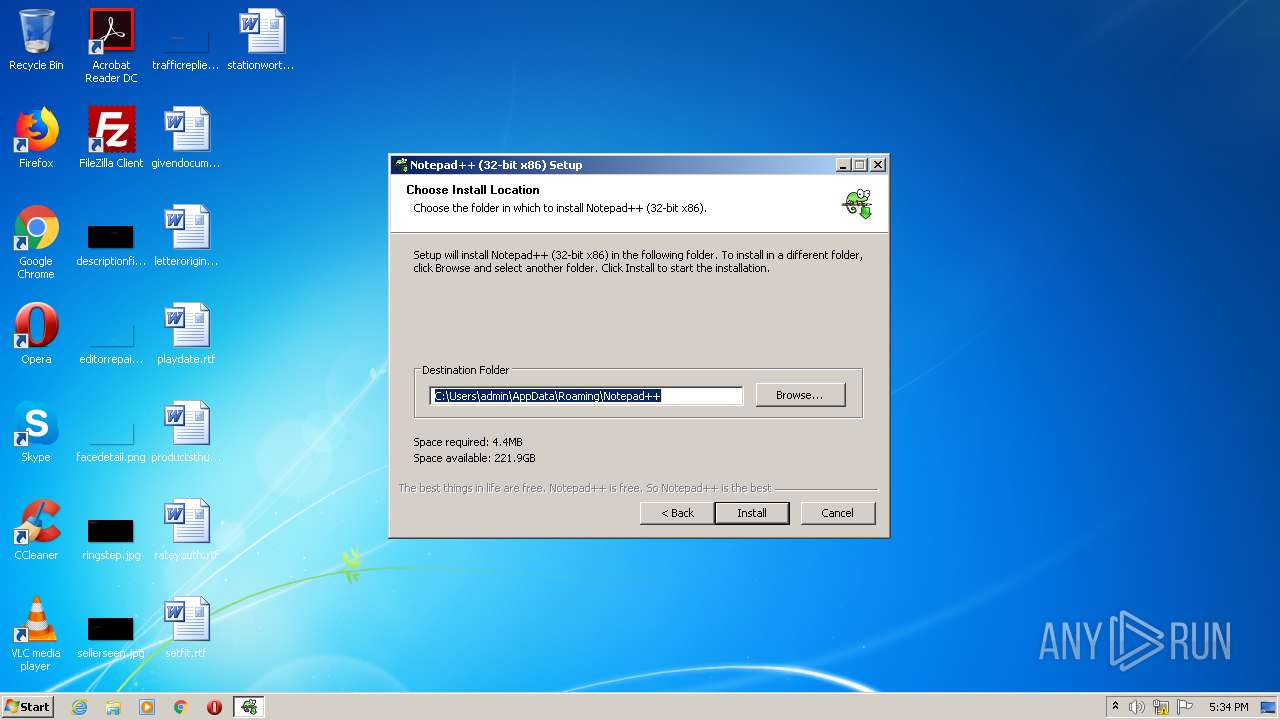
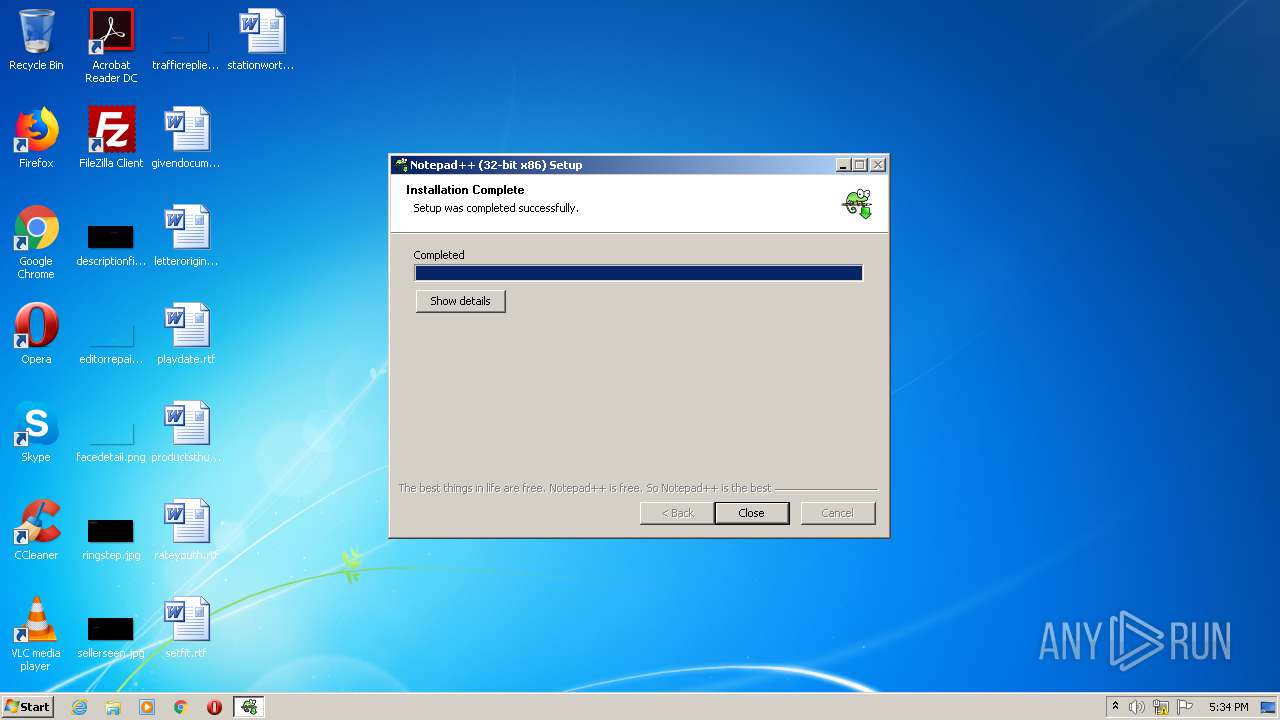
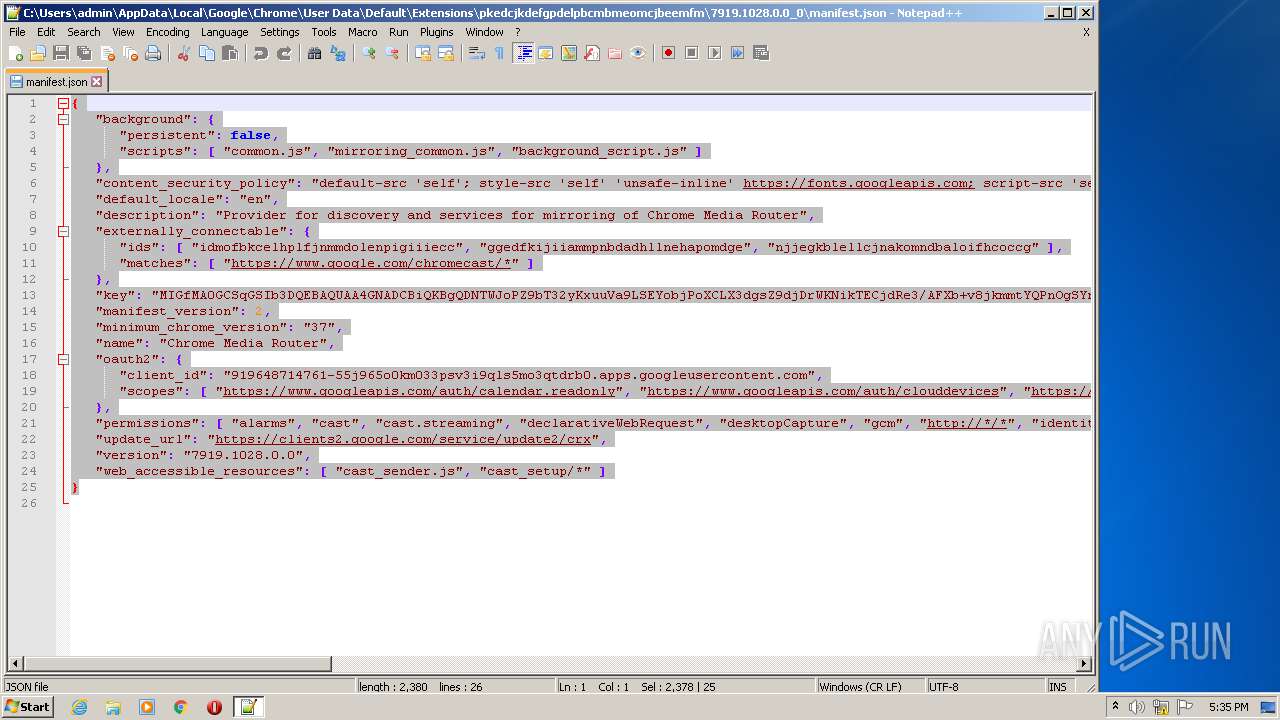
- notepad++.exe (PID: 276)
Loads dropped or rewritten executable
- notepad++.exe (PID: 276)
SUSPICIOUS
Adds / modifies Windows certificates
- Download File Instagram Data Extractor._841028.exe (PID: 996)
Creates files in the program directory
- Download File Instagram Data Extractor._841028.exe (PID: 996)
- Download File Instagram Data Extractor._841028.exe (PID: 2204)
Creates files in the user directory
- Download File Instagram Data Extractor._841028.exe (PID: 996)
- Download File Instagram Data Extractor._841028.exe (PID: 2204)
- CarissauWeb.exe (PID: 292)
Application launched itself
- Download File Instagram Data Extractor._841028.exe (PID: 2204)
Executable content was dropped or overwritten
- Download File Instagram Data Extractor._841028.exe (PID: 996)
- CarissauWeb.exe (PID: 292)
Reads Internet Cache Settings
- Download File Instagram Data Extractor._841028.exe (PID: 996)
Creates a software uninstall entry
- CarissauWeb.exe (PID: 292)
INFO
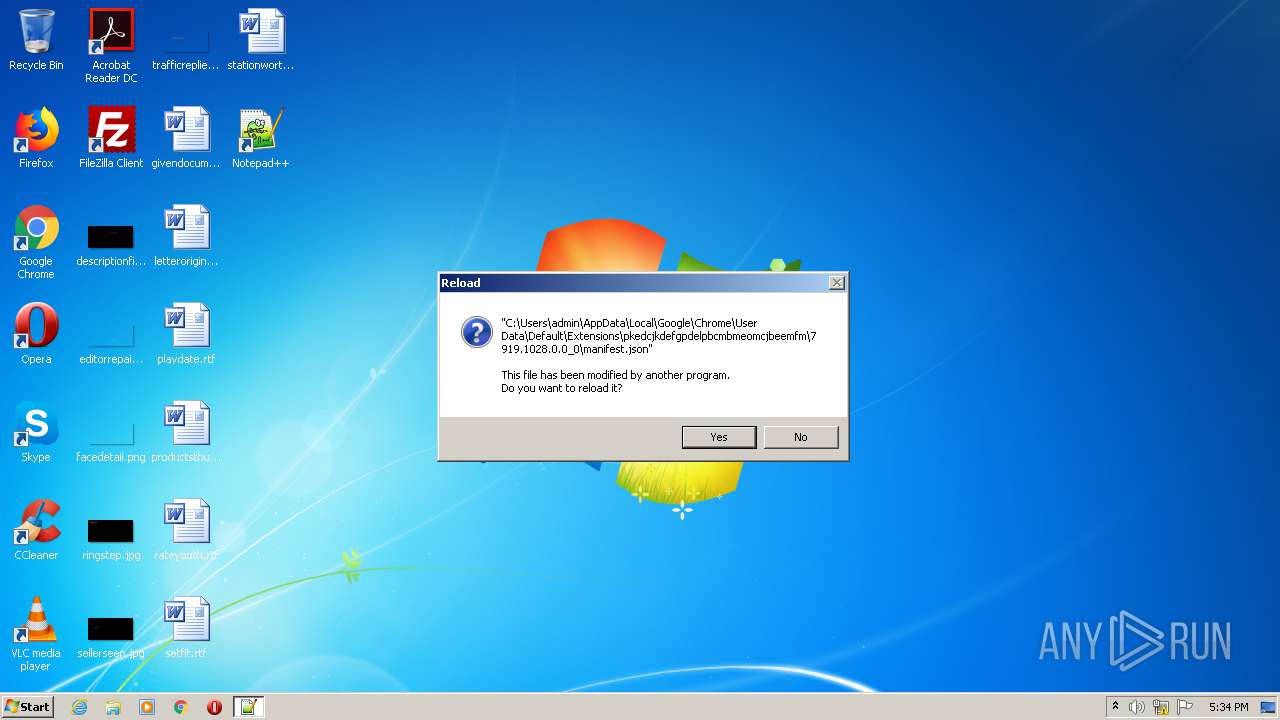
Manual execution by user
- notepad++.exe (PID: 276)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:09:22 16:24:31+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 320512 |
| InitializedDataSize: | 1411584 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x65d0 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.3.7 |
| ProductVersionNumber: | 1.0.3.7 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | Carissa Web Manager |
| FileVersion: | 1.0.3.7 |
| InternalName: | CarissaWebManager.exe |
| LegalCopyright: | Copyright 2020 |
| OriginalFileName: | CarissaWebManager.exe |
| ProductName: | CarissaWebManager |
| ProductVersion: | 1.0.3.7 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 22-Sep-2020 14:24:31 |
| Detected languages: |
|
| FileDescription: | Carissa Web Manager |
| FileVersion: | 1.0.3.7 |
| InternalName: | CarissaWebManager.exe |
| LegalCopyright: | Copyright 2020 |
| OriginalFilename: | CarissaWebManager.exe |
| ProductName: | CarissaWebManager |
| ProductVersion: | 1.0.3.7 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 22-Sep-2020 14:24:31 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0004E2C3 | 0x0004E400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.54378 |
.rdata | 0x00050000 | 0x0000EF74 | 0x0000F000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.09822 |
.data | 0x0005F000 | 0x00002118 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.96089 |
.gfids | 0x00062000 | 0x0000023C | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.49938 |
.tls | 0x00063000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.rsrc | 0x00064000 | 0x00144020 | 0x00144200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.74169 |
.reloc | 0x001A9000 | 0x00002E04 | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.58789 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.3298 | 822 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.86269 | 67624 | UNKNOWN | English - United States | RT_ICON |
3 | 3.09022 | 38056 | UNKNOWN | English - United States | RT_ICON |
4 | 3.08396 | 21640 | UNKNOWN | English - United States | RT_ICON |
5 | 3.01255 | 16936 | UNKNOWN | English - United States | RT_ICON |
6 | 3.21203 | 9640 | UNKNOWN | English - United States | RT_ICON |
7 | 3.26273 | 4264 | UNKNOWN | English - United States | RT_ICON |
8 | 3.46891 | 2440 | UNKNOWN | English - United States | RT_ICON |
9 | 3.54547 | 1128 | UNKNOWN | English - United States | RT_ICON |
107 | 3.01226 | 132 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
ole32.dll |
Total processes
42
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
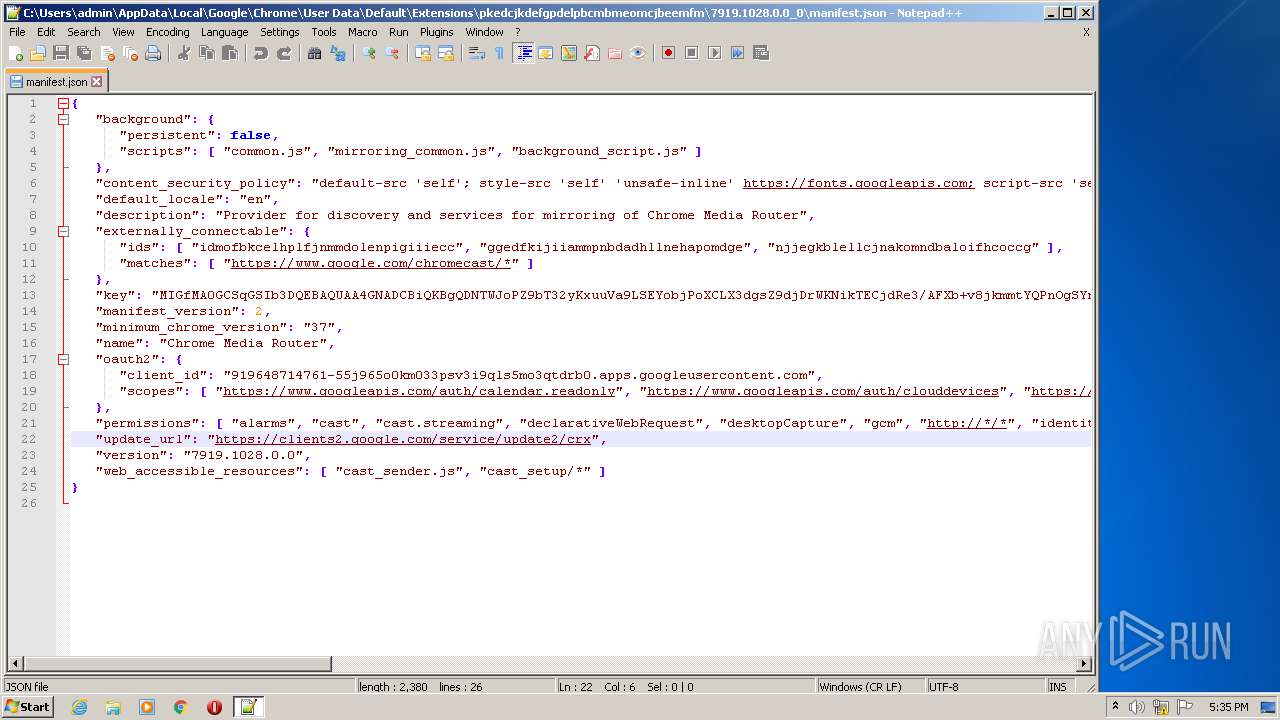
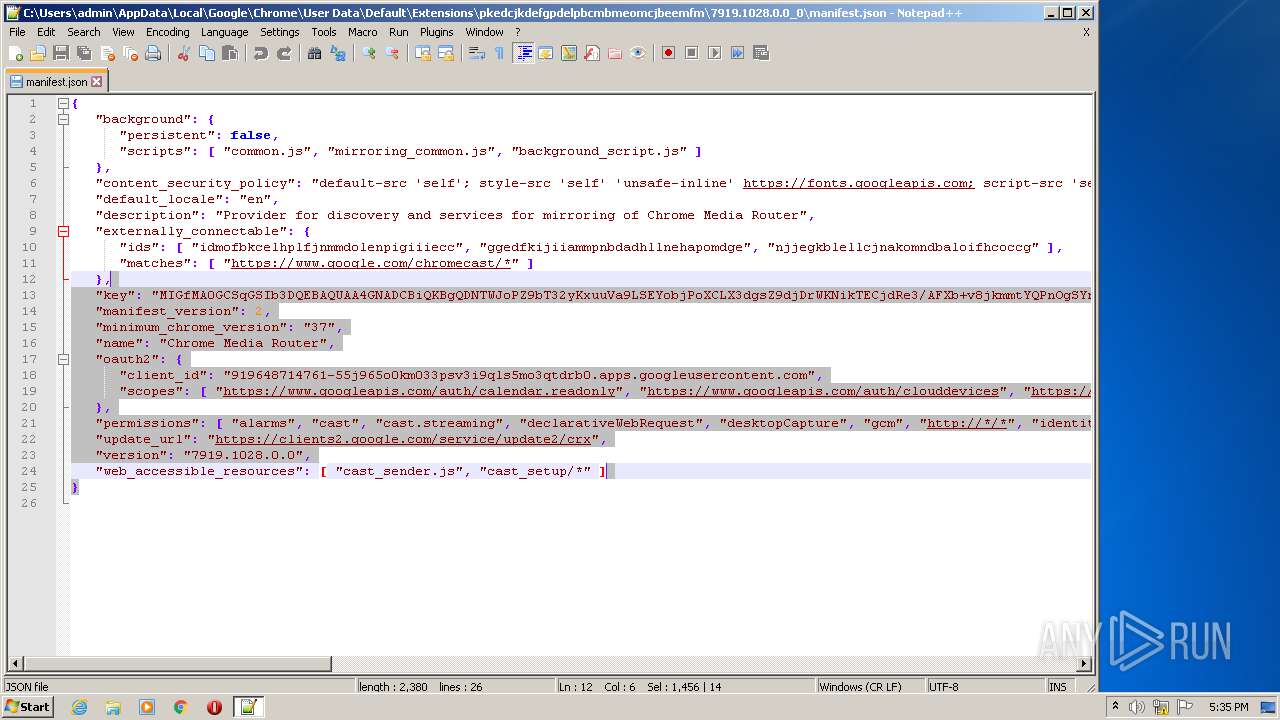
| 276 | "C:\Users\admin\AppData\Roaming\Notepad++\notepad++.exe" | C:\Users\admin\AppData\Roaming\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.8 Modules
| |||||||||||||||
| 292 | "C:\Program Files\CarissaWebtibManager\CarissauWeb.exe" 94081310027816 teT5NjWNdc8ztwzijO42A4zRm9mXPiW4/Zl7AUA7cQcdMeprNQ3LlqiGD2I1ALhY7nL9Gm1U+px2EfC1nJj3n+HNsq9d+3zrevlrZV+EvnZXQQbpFcuQJ+jWEAxXFfBhAt2LY3yH6SoNCiYflwXVeJaUgiX6a2VHxEjU3Jy5R0T8smm3obcflcC1qpnBJyODaeo4GjHI8PP+GjAjVl8KVmPRk8uXw9hxlIVxSGVDKxEsqzR3YG2tFPu9do/KuNUfNUUP8xChN7DM6UBnXbH2jw== | C:\Program Files\CarissaWebtibManager\CarissauWeb.exe | Download File Instagram Data Extractor._841028.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.8.0.0 Modules
| |||||||||||||||
| 996 | "C:\Users\admin\AppData\Local\Temp\Download File Instagram Data Extractor._841028.exe" -uac | C:\Users\admin\AppData\Local\Temp\Download File Instagram Data Extractor._841028.exe | Download File Instagram Data Extractor._841028.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Carissa Web Manager Exit code: 0 Version: 1.0.3.7 Modules
| |||||||||||||||
| 2204 | "C:\Users\admin\AppData\Local\Temp\Download File Instagram Data Extractor._841028.exe" | C:\Users\admin\AppData\Local\Temp\Download File Instagram Data Extractor._841028.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Carissa Web Manager Exit code: 0 Version: 1.0.3.7 Modules
| |||||||||||||||
Total events
782
Read events
746
Write events
36
Delete events
0
Modification events
| (PID) Process: | (2204) Download File Instagram Data Extractor._841028.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2204) Download File Instagram Data Extractor._841028.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (996) Download File Instagram Data Extractor._841028.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (996) Download File Instagram Data Extractor._841028.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (996) Download File Instagram Data Extractor._841028.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (996) Download File Instagram Data Extractor._841028.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (996) Download File Instagram Data Extractor._841028.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (996) Download File Instagram Data Extractor._841028.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (996) Download File Instagram Data Extractor._841028.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\D4DE20D05E66FC53FE1A50882C78DB2852CAE474 |
| Operation: | write | Name: | Blob |
Value: 040000000100000010000000ACB694A59C17E0D791529BB19706A6E40F0000000100000014000000CE0E658AA3E847E467A147B3049191093D055E6F030000000100000014000000D4DE20D05E66FC53FE1A50882C78DB2852CAE4741D0000000100000010000000918AD43A9475F78BB5243DE886D8103C140000000100000014000000E59D5930824758CCACFA085436867B3AB5044DF062000000010000002000000016AF57A9F676B0AB126095AA5EBADEF22AB31119D644AC95CD4B93DBF3F26AEB0B0000000100000030000000440069006700690043006500720074002000420061006C00740069006D006F0072006500200052006F006F007400000009000000010000003E000000303C06082B0601050507030106082B0601050507030406082B0601050507030206082B0601050507030306082B0601050507030906082B0601050507030853000000010000006200000030603020060A2B06010401B13E01640130123010060A2B0601040182373C0101030200C0301F06096086480186FD6C020130123010060A2B0601040182373C0101030200C0301B060567810C010130123010060A2B0601040182373C0101030200C019000000010000001000000068CB42B035EA773E52EF50ECF50EC52920000000010000007B030000308203773082025FA0030201020204020000B9300D06092A864886F70D0101050500305A310B300906035504061302494531123010060355040A130942616C74696D6F726531133011060355040B130A43796265725472757374312230200603550403131942616C74696D6F7265204379626572547275737420526F6F74301E170D3030303531323138343630305A170D3235303531323233353930305A305A310B300906035504061302494531123010060355040A130942616C74696D6F726531133011060355040B130A43796265725472757374312230200603550403131942616C74696D6F7265204379626572547275737420526F6F7430820122300D06092A864886F70D01010105000382010F003082010A0282010100A304BB22AB983D57E826729AB579D429E2E1E89580B1B0E35B8E2B299A64DFA15DEDB009056DDB282ECE62A262FEB488DA12EB38EB219DC0412B01527B8877D31C8FC7BAB988B56A09E773E81140A7D1CCCA628D2DE58F0BA650D2A850C328EAF5AB25878A9A961CA967B83F0CD5F7F952132FC21BD57070F08FC012CA06CB9AE1D9CA337A77D6F8ECB9F16844424813D2C0C2A4AE5E60FEB6A605FCB4DD075902D459189863F5A563E0900C7D5DB2067AF385EAEBD403AE5E843E5FFF15ED69BCF939367275CF77524DF3C9902CB93DE5C923533F1F2498215C079929BDC63AECE76E863A6B97746333BD681831F0788D76BFFC9E8E5D2A86A74D90DC271A390203010001A3453043301D0603551D0E04160414E59D5930824758CCACFA085436867B3AB5044DF030120603551D130101FF040830060101FF020103300E0603551D0F0101FF040403020106300D06092A864886F70D01010505000382010100850C5D8EE46F51684205A0DDBB4F27258403BDF764FD2DD730E3A41017EBDA2929B6793F76F6191323B8100AF958A4D46170BD04616A128A17D50ABDC5BC307CD6E90C258D86404FECCCA37E38C637114FEDDD68318E4CD2B30174EEBE755E07481A7F70FF165C84C07985B805FD7FBE6511A30FC002B4F852373904D5A9317A18BFA02AF41299F7A34582E33C5EF59D9EB5C89E7C2EC8A49E4E08144B6DFD706D6B1A63BD64E61FB7CEF0F29F2EBB1BB7F250887392C2E2E3168D9A3202AB8E18DDE91011EE7E35AB90AF3E30947AD0333DA7650FF5FC8E9E62CF47442C015DBB1DB532D247D2382ED0FE81DC326A1EB5EE3CD5FCE7811D19C32442EA6339A9 | |||
| (PID) Process: | (292) CarissauWeb.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\Notepad++ |
| Operation: | write | Name: | DisplayName |
Value: Notepad++ (32-bit x86) | |||
Executable files
4
Suspicious files
6
Text files
9
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 996 | Download File Instagram Data Extractor._841028.exe | C:\Users\admin\AppData\Local\Temp\CabE66E.tmp | — | |
MD5:— | SHA256:— | |||
| 996 | Download File Instagram Data Extractor._841028.exe | C:\Users\admin\AppData\Local\Temp\TarE66F.tmp | — | |
MD5:— | SHA256:— | |||
| 2204 | Download File Instagram Data Extractor._841028.exe | C:\Users\admin\AppData\Roaming\FLDR\Buffertemppho | binary | |
MD5:00A5033694B6E94D8078EF2535036E09 | SHA256:4DD388E61295C6B3F52937C142468B736B18D46EB878C28D15E202E84FD81C6F | |||
| 996 | Download File Instagram Data Extractor._841028.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\9FF67FB3141440EED32363089565AE60_F777CA2E0182A935A949E44ED00BB3DF | der | |
MD5:— | SHA256:— | |||
| 996 | Download File Instagram Data Extractor._841028.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\9FF67FB3141440EED32363089565AE60_F777CA2E0182A935A949E44ED00BB3DF | binary | |
MD5:— | SHA256:— | |||
| 292 | CarissauWeb.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Notepad++.lnk | lnk | |
MD5:— | SHA256:— | |||
| 292 | CarissauWeb.exe | C:\Users\admin\AppData\Roaming\Notepad++\uninstall.exe | executable | |
MD5:— | SHA256:— | |||
| 292 | CarissauWeb.exe | C:\Users\admin\Desktop\Notepad++.lnk | lnk | |
MD5:— | SHA256:— | |||
| 996 | Download File Instagram Data Extractor._841028.exe | C:\Program Files\CarissaWebtibManager\CarissauWeb.exe | executable | |
MD5:— | SHA256:— | |||
| 292 | CarissauWeb.exe | C:\Users\admin\AppData\Roaming\Notepad++\contextMenu.xml | xml | |
MD5:A7998766B85EE71FF1D82A1198988529 | SHA256:AA48A7C2EC3ED377C42C293F732807572F2EA305C9771B6EA210E7B92EF2C199 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
6
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1052 | svchost.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEA7yTSbUNi7CXXtef0luXqk%3D | US | der | 280 b | whitelisted |
996 | Download File Instagram Data Extractor._841028.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEAZvttjS1P9vd6CQxpwKkvE%3D | US | der | 278 b | whitelisted |
1052 | svchost.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
996 | Download File Instagram Data Extractor._841028.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
996 | Download File Instagram Data Extractor._841028.exe | 104.26.7.137:443 | silkysmoothtechnologies.com | Cloudflare Inc | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
silkysmoothtechnologies.com |
| suspicious |
ocsp.digicert.com |
| whitelisted |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: C:\Users\admin\AppData\Roaming\Notepad++\SciLexer.dll
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: error while getting certificate informations
|