| File name: | Null_Removed.vbs |
| Full analysis: | https://app.any.run/tasks/5aa68788-dc81-4700-ae1c-2cf5697a7af7 |
| Verdict: | Malicious activity |
| Analysis date: | November 08, 2024, 14:36:14 |
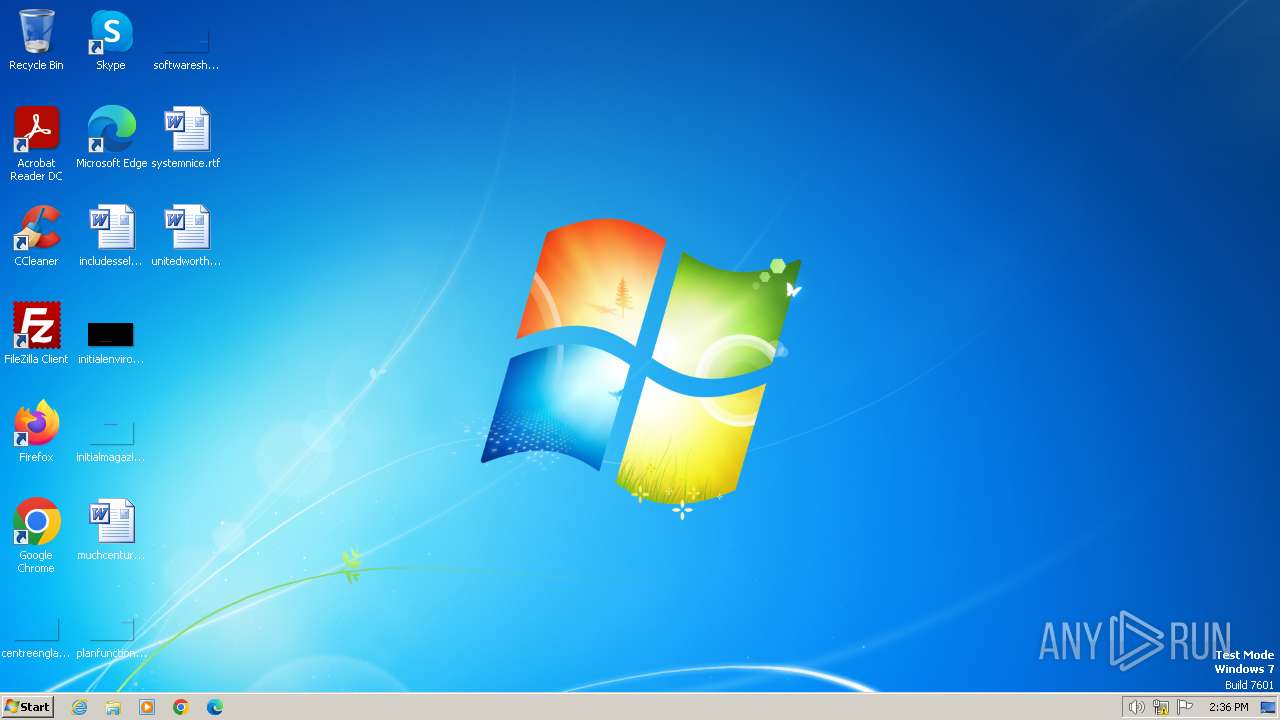
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines (65377), with CRLF line terminators |
| MD5: | AD290E9270BB6B178F79E813256296CF |
| SHA1: | 2DB39EDDFF35EF9D1B2A7CFFF20958C523E39998 |
| SHA256: | D27D37391A86874BFF7B8186CB45A61136F8130C0EC76D2144A8C285388F6756 |
| SSDEEP: | 1536:xaLTIwI9a1oWUdejoWXc+qeauBuMWAZUinpbmcxi/11BSl2TmRL0drLMQPt:xalI9AoWUd1zypWAZUOOP8Eb |
MALICIOUS
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 3024)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 3024)
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 3024)
Gets TEMP folder path (SCRIPT)
- wscript.exe (PID: 3024)
Accesses information about the status of the installed antivirus(Win32_AntivirusProduct) via WMI (SCRIPT)
- wscript.exe (PID: 3024)
SUSPICIOUS
Accesses OperatingSystem(Win32_OperatingSystem) via WMI (SCRIPT)
- wscript.exe (PID: 3024)
Executes WMI query (SCRIPT)
- wscript.exe (PID: 3024)
Accesses WMI object, sets custom ImpersonationLevel (SCRIPT)
- wscript.exe (PID: 3024)
Accesses operating system name via WMI (SCRIPT)
- wscript.exe (PID: 3024)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- wscript.exe (PID: 3024)
Accesses WMI object caption (SCRIPT)
- wscript.exe (PID: 3024)
INFO
Manual execution by a user
- explorer.exe (PID: 3660)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
36
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3024 | "C:\Windows\System32\WScript.exe" C:\Users\admin\AppData\Local\Temp\Null_Removed.vbs | C:\Windows\System32\wscript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3660 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
512
Read events
512
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
7
DNS requests
3
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2564 | svchost.exe | 239.255.255.250:3702 | — | — | — | whitelisted |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3024 | wscript.exe | 186.233.148.134:80 | beta.enerbras.com.br | Central Server Informatica Ltda | BR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
alhussain.pk |
| unknown |
beta.enerbras.com.br |
| unknown |