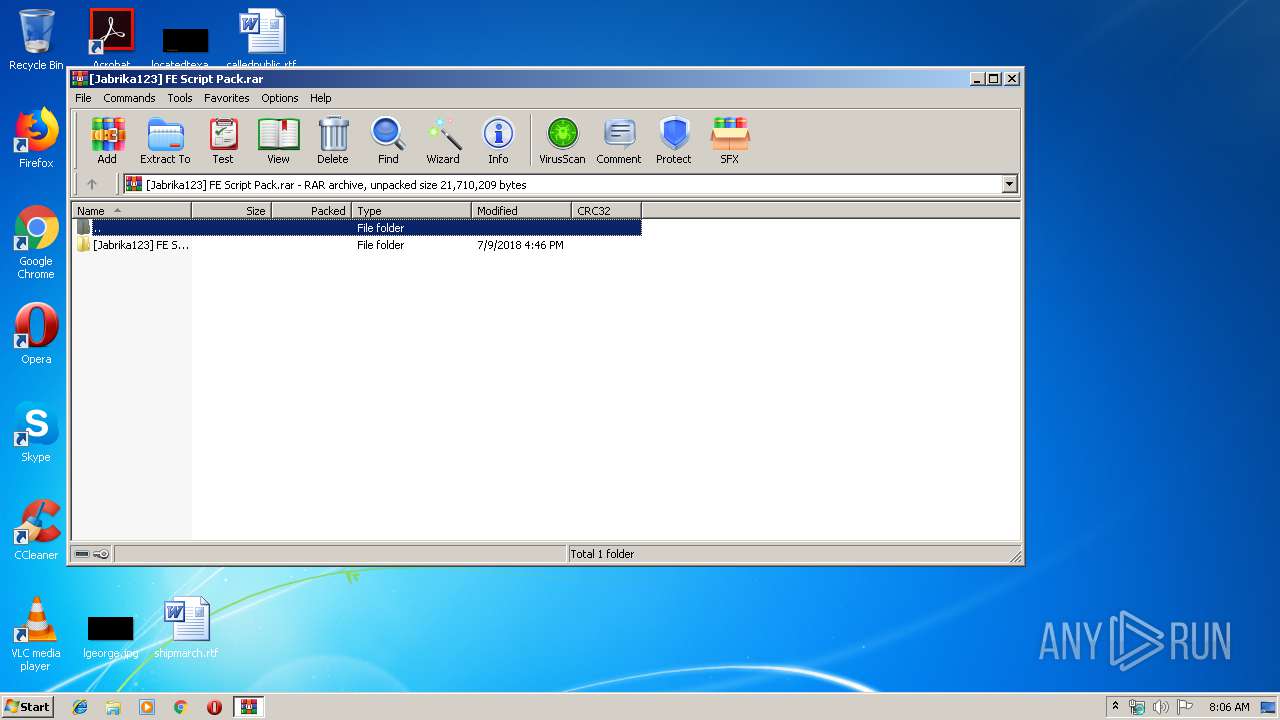
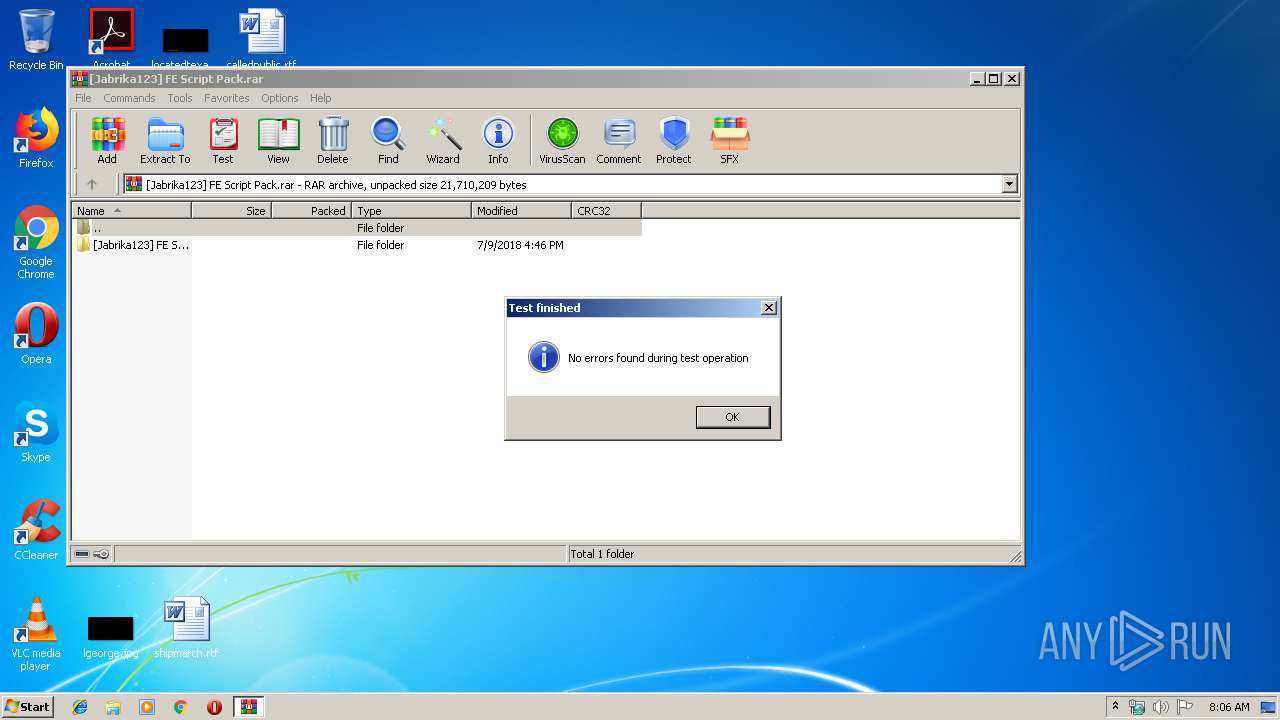
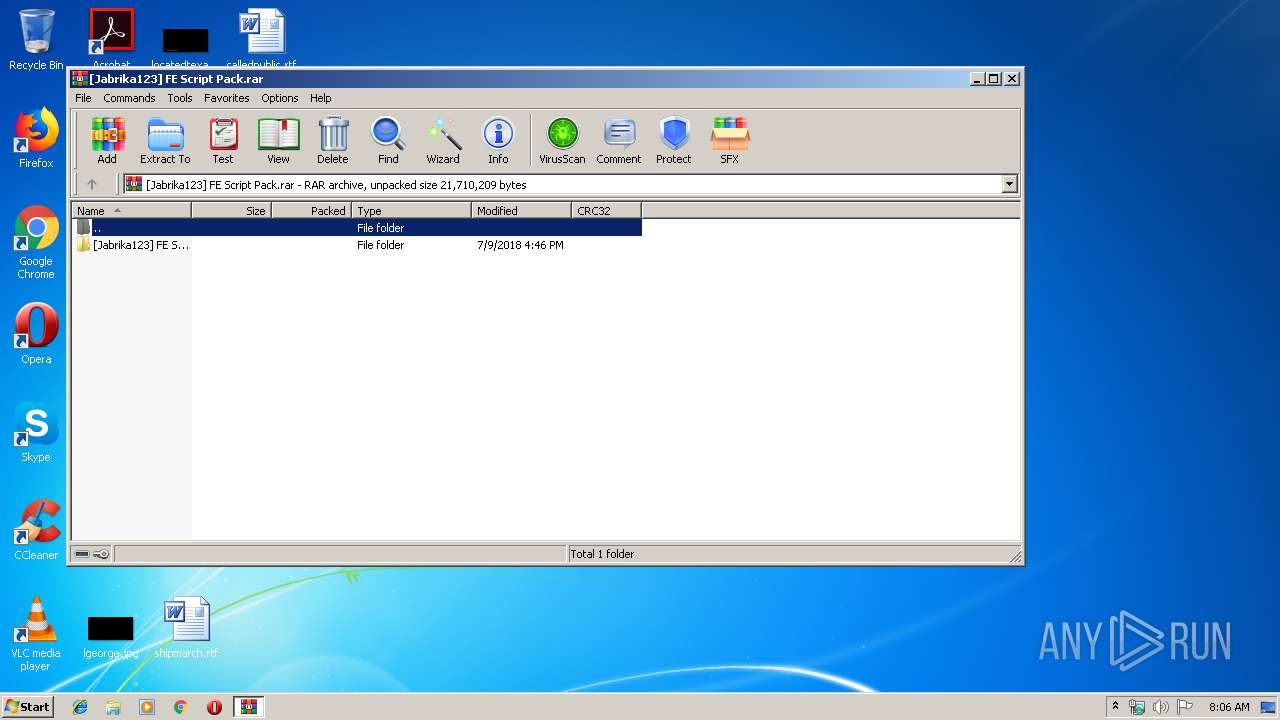
| File name: | [Jabrika123] FE Script Pack.rar |
| Full analysis: | https://app.any.run/tasks/f408b338-800b-44c4-8ab0-c24be0974988 |
| Verdict: | Suspicious activity |
| Analysis date: | December 16, 2019, 08:05:42 |
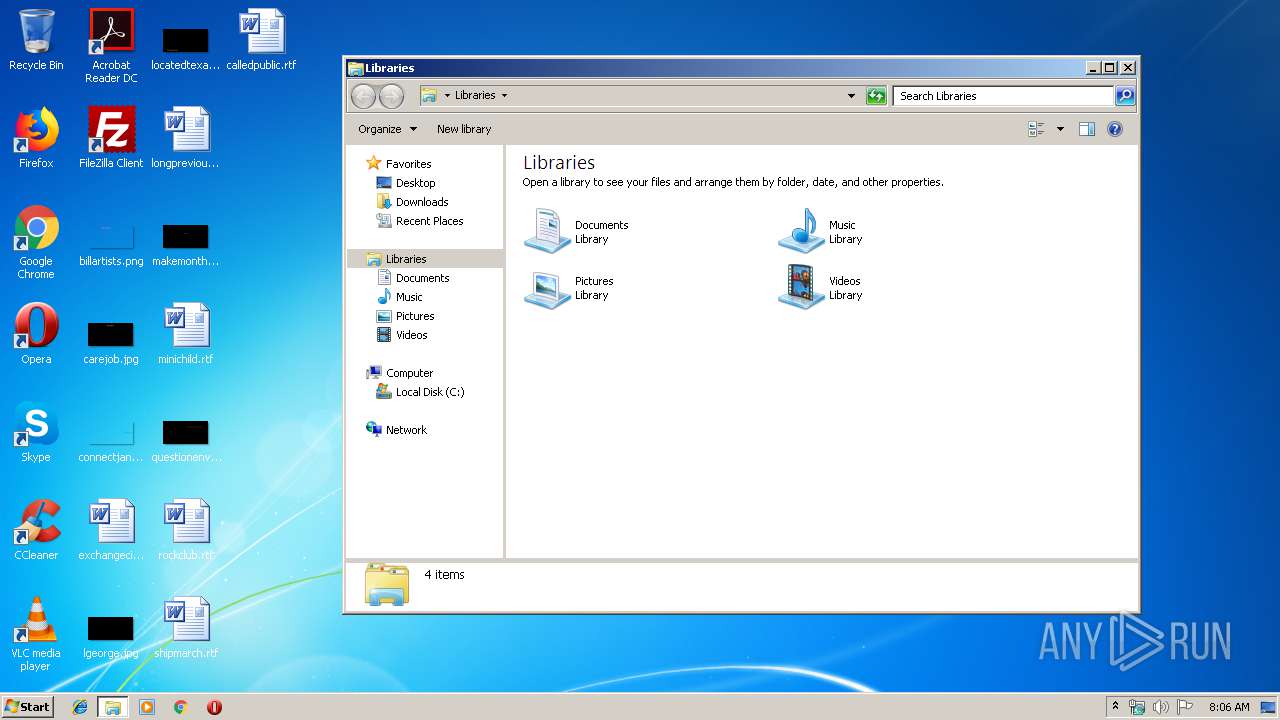
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 4B4C550CDEE8F739047747B9EDB55677 |
| SHA1: | E3237AC666C8D25842C6901982B384F06831E4A1 |
| SHA256: | D27013349981D1B0376630F760E8914B9CE0332A794BA716DA25ACE6F99EF7C5 |
| SSDEEP: | 49152:kbw91Og1BKjIVoVg37Nw1iuAMAzfWMmGDbFWcL5pYlvcSyyvGM5dj3:kbw6g7XVt7NwkgpMdEwpYlvDvGk3 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
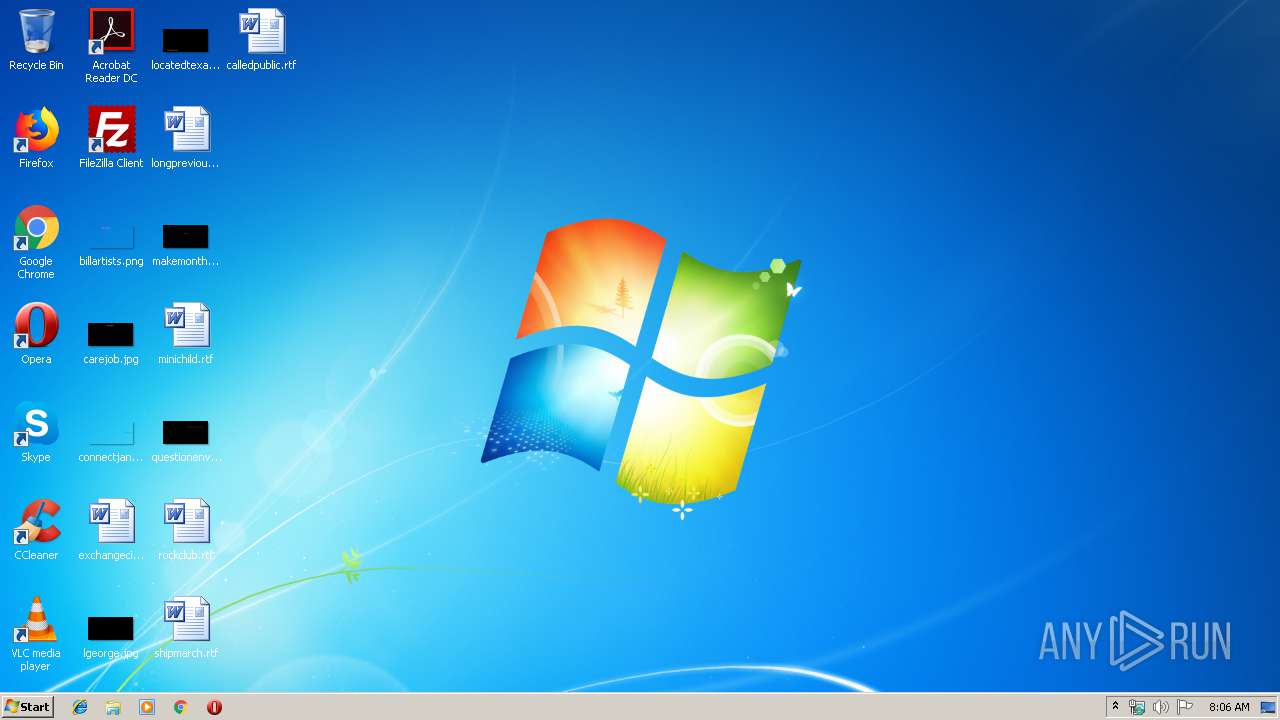
Manual execution by user
- chrome.exe (PID: 2328)
- explorer.exe (PID: 492)
Application launched itself
- chrome.exe (PID: 2328)
Changes settings of System certificates
- chrome.exe (PID: 3680)
Reads the hosts file
- chrome.exe (PID: 2328)
- chrome.exe (PID: 3680)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
73
Monitored processes
36
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,9447303748843514115,12046072740220007238,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16486901117943333528 --mojo-platform-channel-handle=5440 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 460 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1016,9447303748843514115,12046072740220007238,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=15504351009258073904 --mojo-platform-channel-handle=4956 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 492 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3428 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,9447303748843514115,12046072740220007238,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12903062986324228693 --mojo-platform-channel-handle=4500 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 656 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,9447303748843514115,12046072740220007238,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15106838369856033095 --mojo-platform-channel-handle=3464 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 892 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,9447303748843514115,12046072740220007238,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3841054181337137092 --mojo-platform-channel-handle=4520 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,9447303748843514115,12046072740220007238,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18250486009035346858 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2428 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1044 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,9447303748843514115,12046072740220007238,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6415400407631386613 --mojo-platform-channel-handle=3692 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,9447303748843514115,12046072740220007238,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12631882053329214336 --mojo-platform-channel-handle=3452 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
699
Read events
601
Write events
94
Delete events
4
Modification events
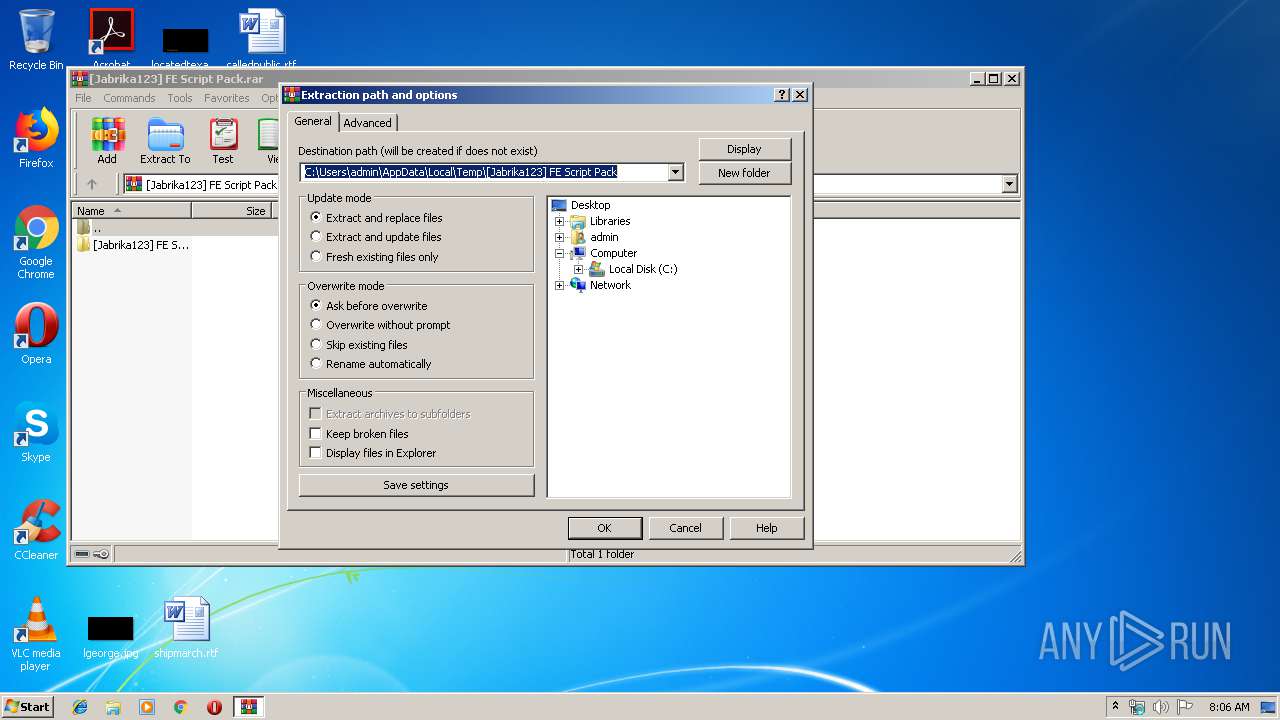
| (PID) Process: | (2512) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2512) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2512) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2512) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\[Jabrika123] FE Script Pack.rar | |||
| (PID) Process: | (2512) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2512) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2512) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2512) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2512) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\[Jabrika123] FE Script Pack | |||
| (PID) Process: | (2512) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
0
Suspicious files
52
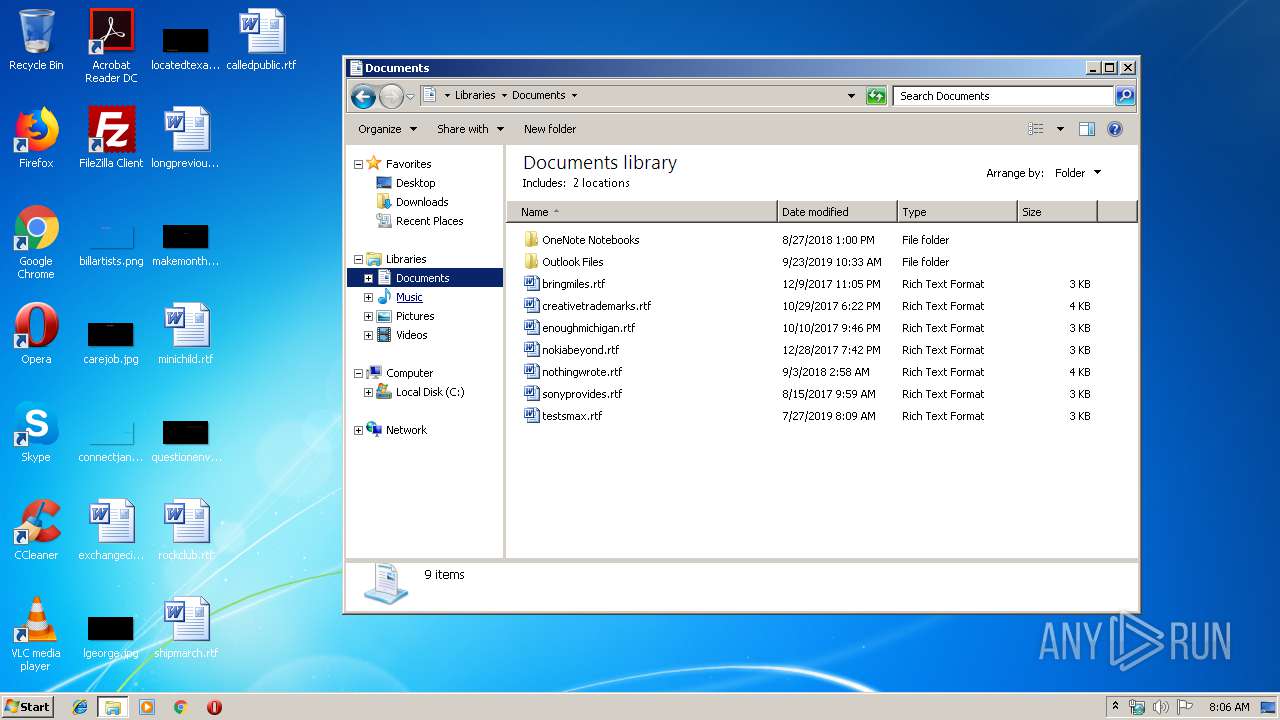
Text files
706
Unknown types
13
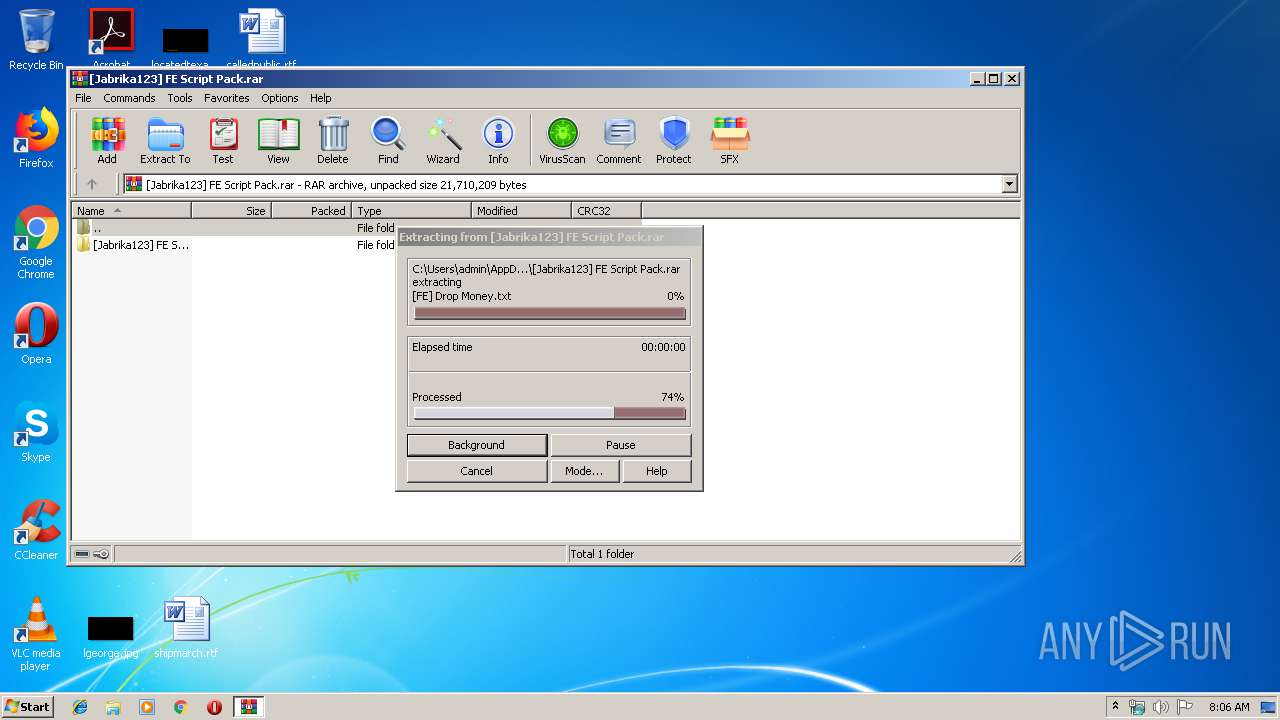
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2512 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\[Jabrika123] FE Script Pack\[Jabrika123] FE Script Pack\Extras\Favorite Non-FE Scripts\Maps\CkBackup Beach Map.txt | text | |
MD5:— | SHA256:— | |||
| 2512 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\[Jabrika123] FE Script Pack\[Jabrika123] FE Script Pack\Extras\Bypasses\Bypassed Audios [Favorites].txt | text | |
MD5:— | SHA256:— | |||
| 2512 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\[Jabrika123] FE Script Pack\[Jabrika123] FE Script Pack\Extras\Favorite Non-FE Scripts\Maps\Fist Town House.txt | text | |
MD5:— | SHA256:— | |||
| 2512 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\[Jabrika123] FE Script Pack\[Jabrika123] FE Script Pack\Extras\Favorite Non-FE Scripts\Maps\Cloud Atmosphere.txt | text | |
MD5:— | SHA256:— | |||
| 2512 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\[Jabrika123] FE Script Pack\[Jabrika123] FE Script Pack\Extras\Bypasses\Bypassed Audios.txt | text | |
MD5:— | SHA256:— | |||
| 2512 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\[Jabrika123] FE Script Pack\[Jabrika123] FE Script Pack\Extras\Favorite Non-FE Scripts\Maps\Grave Map.txt | text | |
MD5:— | SHA256:— | |||
| 2512 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\[Jabrika123] FE Script Pack\[Jabrika123] FE Script Pack\Extras\Favorite Non-FE Scripts\Maps\Memories.txt | text | |
MD5:— | SHA256:— | |||
| 2512 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\[Jabrika123] FE Script Pack\[Jabrika123] FE Script Pack\Extras\Bypasses\Decals-TShirts Bypassing Discord Servers.txt | text | |
MD5:— | SHA256:— | |||
| 2512 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\[Jabrika123] FE Script Pack\[Jabrika123] FE Script Pack\Extras\Favorite Non-FE Scripts\Maps\Clockwork Arena.txt | text | |
MD5:— | SHA256:— | |||
| 2512 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\[Jabrika123] FE Script Pack\[Jabrika123] FE Script Pack\Extras\Bypasses\Guest Bypass.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
56
DNS requests
35
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
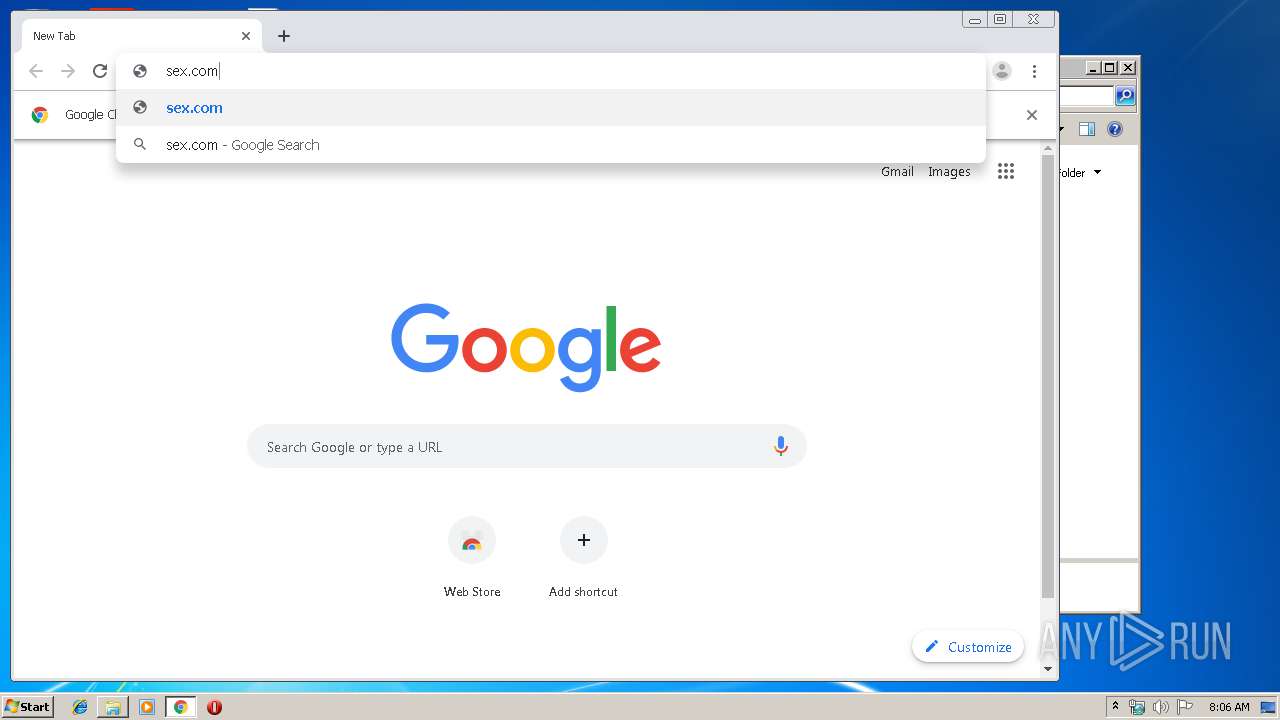
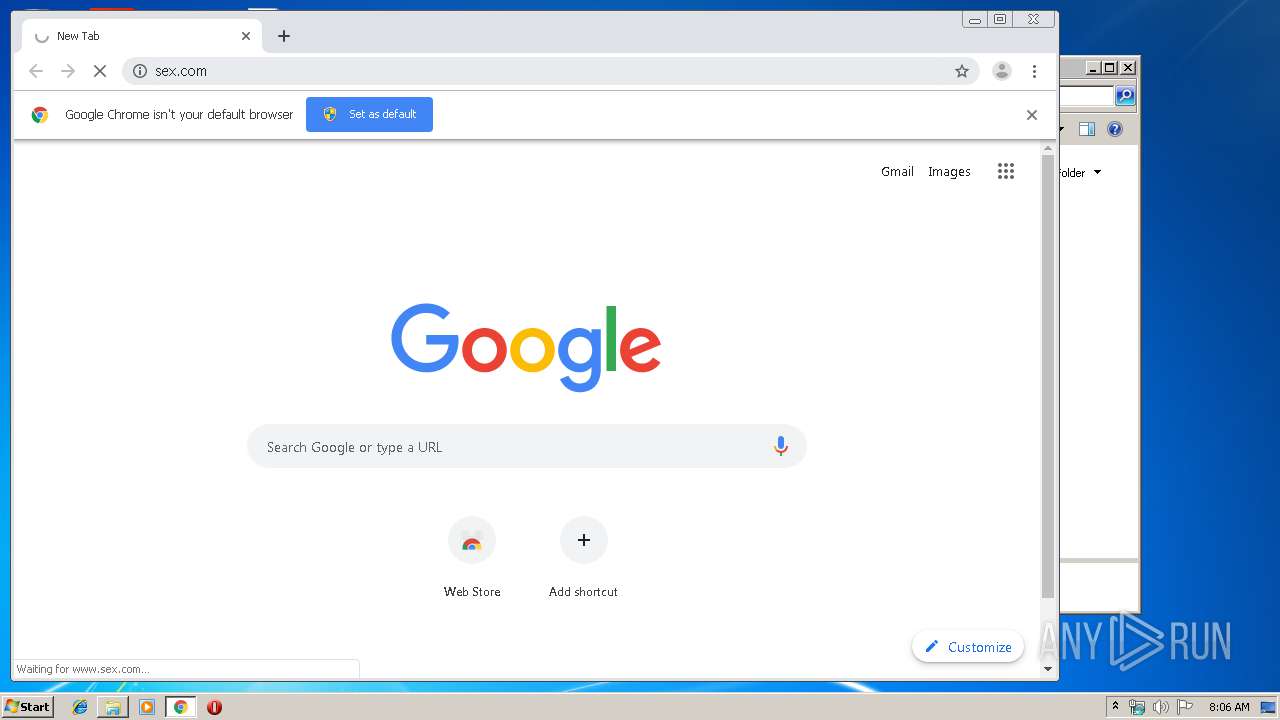
3680 | chrome.exe | GET | 301 | 206.125.164.82:80 | http://sex.com/ | CA | — | — | suspicious |
3680 | chrome.exe | GET | — | 188.121.36.237:80 | http://certificates.godaddy.com/repository/gdig2.crt | NL | — | — | whitelisted |
3680 | chrome.exe | GET | 302 | 172.217.18.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 514 b | whitelisted |
3680 | chrome.exe | GET | 200 | 8.253.207.121:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.4 Kb | whitelisted |
3680 | chrome.exe | GET | 200 | 8.253.207.121:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.4 Kb | whitelisted |
3680 | chrome.exe | GET | 200 | 8.253.207.121:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.4 Kb | whitelisted |
3680 | chrome.exe | GET | 302 | 172.217.18.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 509 b | whitelisted |
3680 | chrome.exe | GET | 200 | 8.253.207.121:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/47BEABC922EAE80E78783462A79F45C254FDE68B.crt | US | der | 969 b | whitelisted |
3680 | chrome.exe | GET | 200 | 173.194.129.232:80 | http://r3---sn-q0c7rn76.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=81.17.242.238&mm=28&mn=sn-q0c7rn76&ms=nvh&mt=1576483154&mv=u&mvi=2&pl=20&shardbypass=yes | US | crx | 862 Kb | whitelisted |
3680 | chrome.exe | GET | 200 | 91.199.212.52:80 | http://crt.usertrust.com/USERTrustRSAAddTrustCA.crt | GB | der | 1.37 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3680 | chrome.exe | 172.217.18.109:443 | accounts.google.com | Google Inc. | US | suspicious |
3680 | chrome.exe | 172.217.22.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3680 | chrome.exe | 216.58.207.74:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3680 | chrome.exe | 216.58.207.35:443 | www.google.com.ua | Google Inc. | US | whitelisted |
3680 | chrome.exe | 172.217.18.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3680 | chrome.exe | 172.217.22.35:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3680 | chrome.exe | 172.217.23.110:443 | apis.google.com | Google Inc. | US | whitelisted |
3680 | chrome.exe | 216.58.210.14:443 | ogs.google.com | Google Inc. | US | whitelisted |
3680 | chrome.exe | 216.58.205.228:443 | www.google.com | Google Inc. | US | whitelisted |
3680 | chrome.exe | 172.217.16.131:443 | www.google.ie | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
www.google.com |
| malicious |
www.google.ie |
| whitelisted |