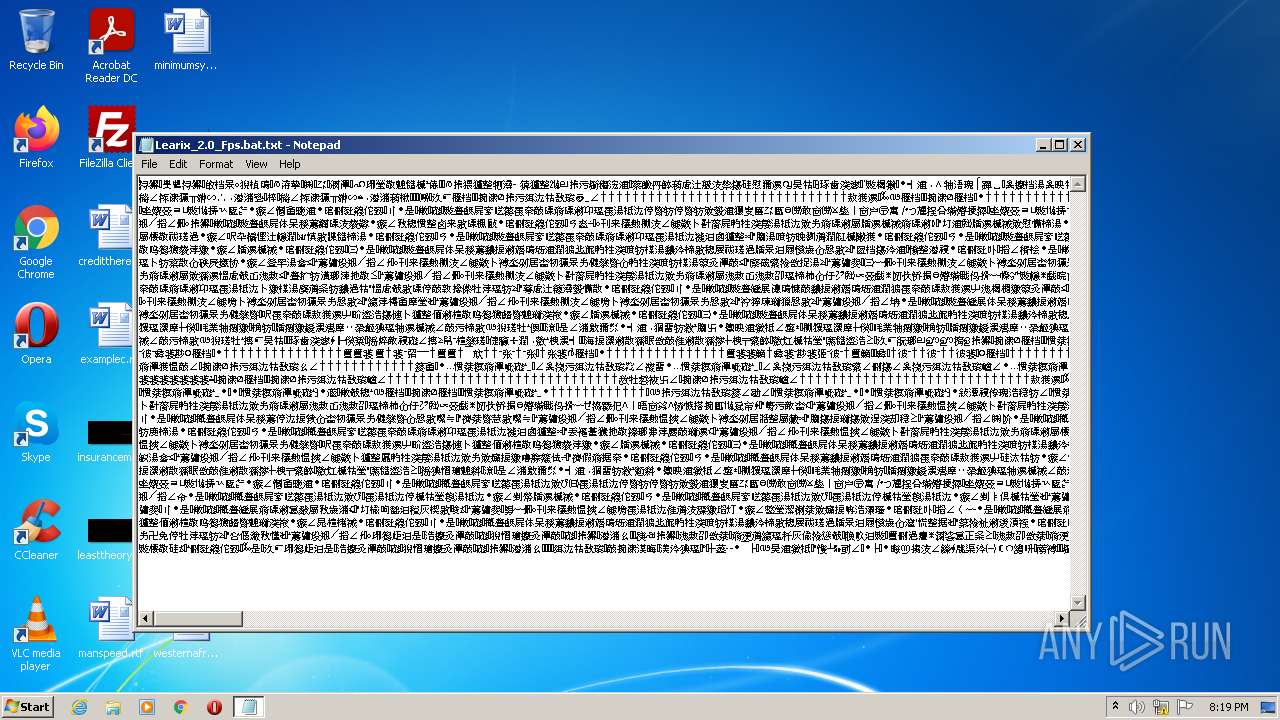
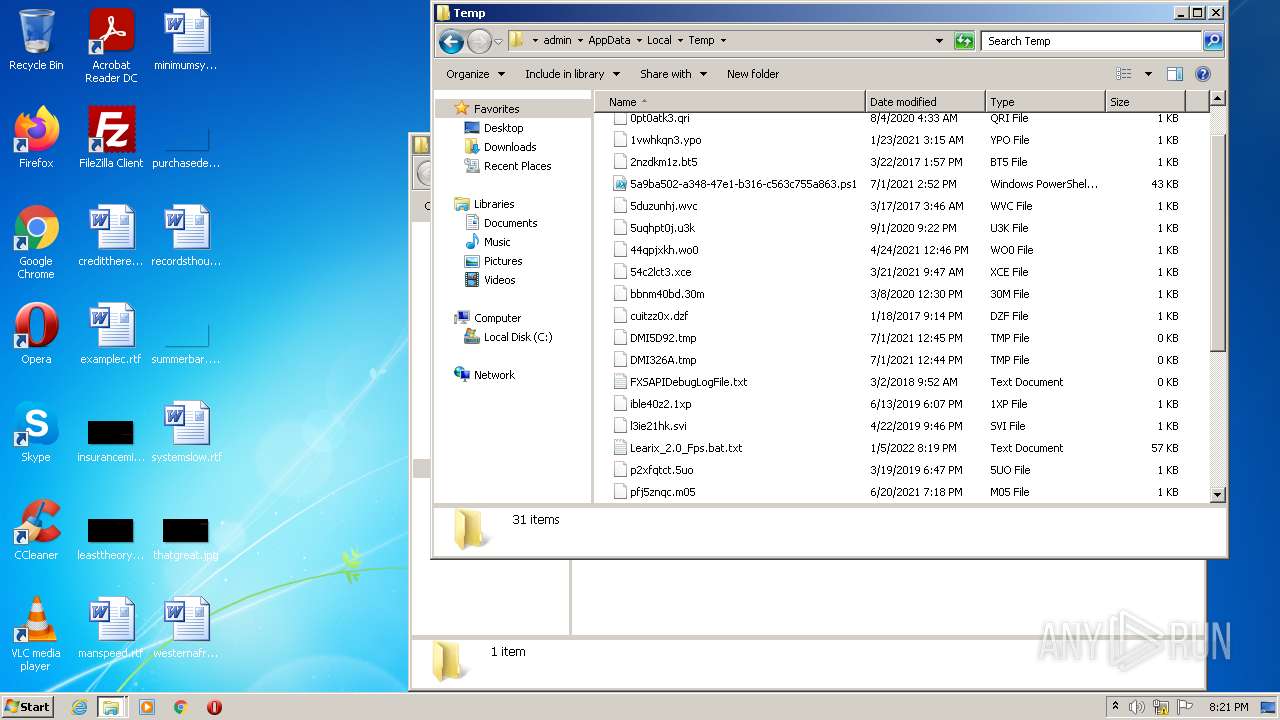
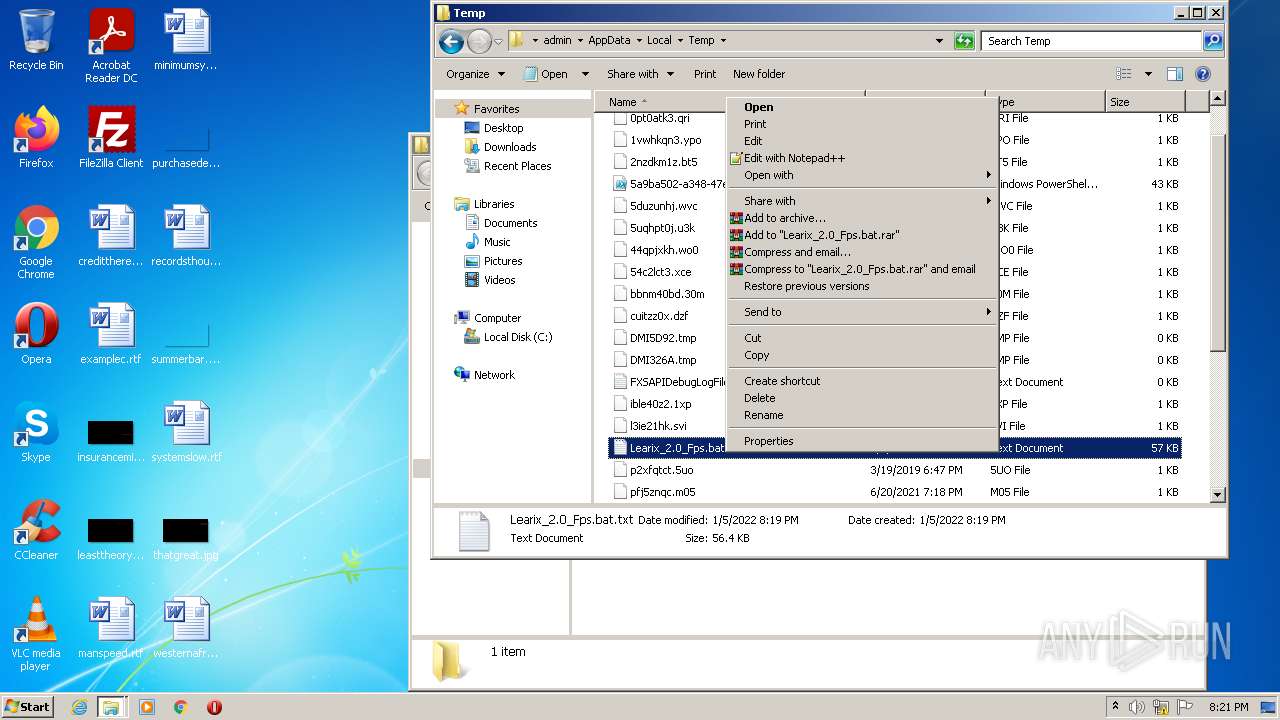
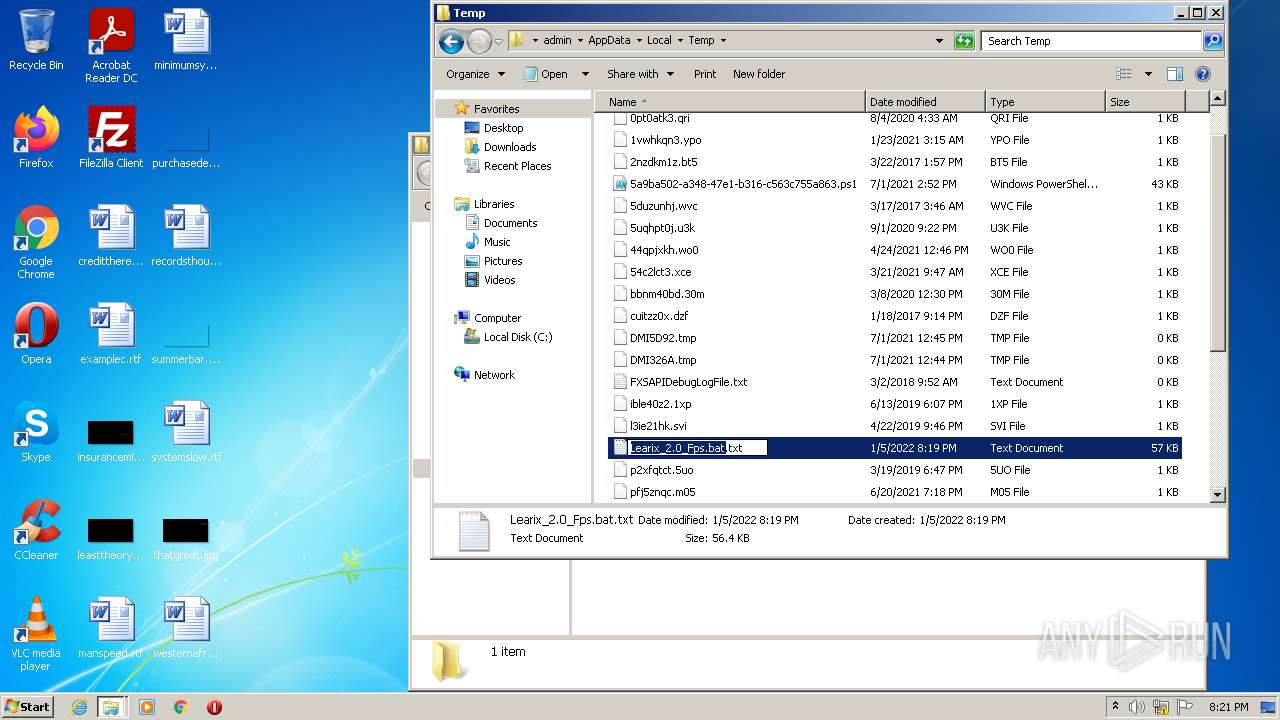
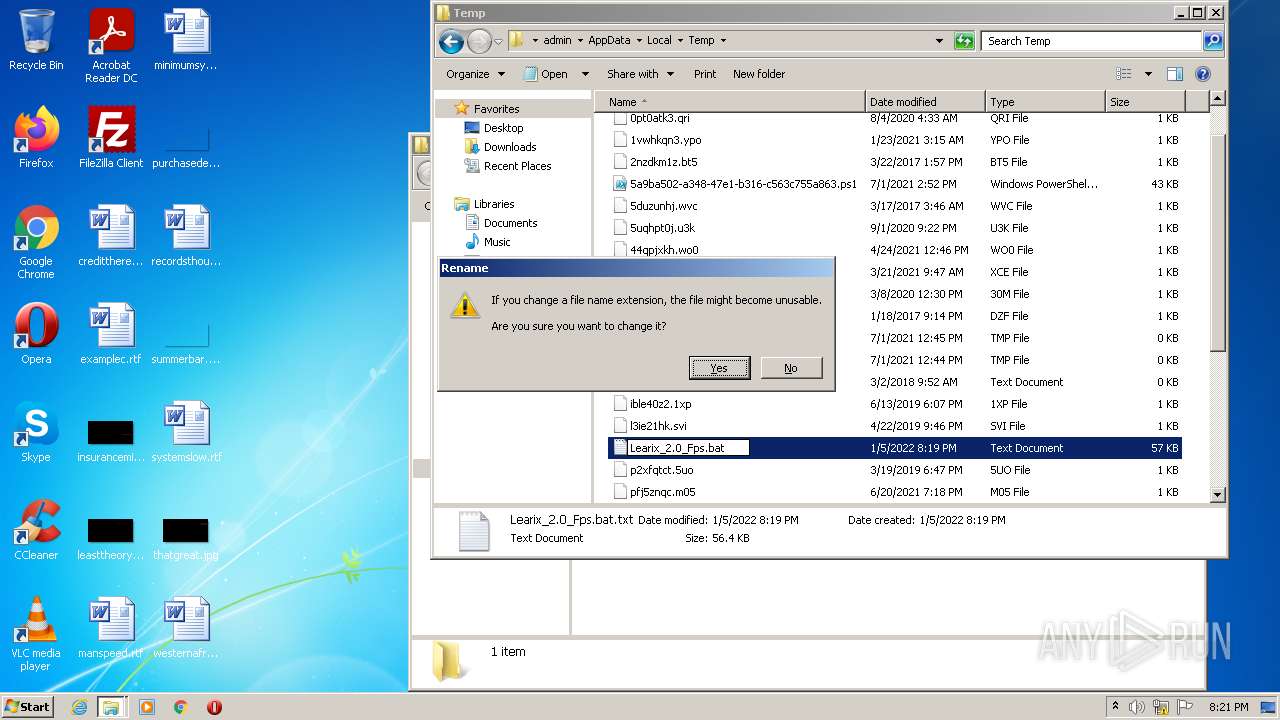
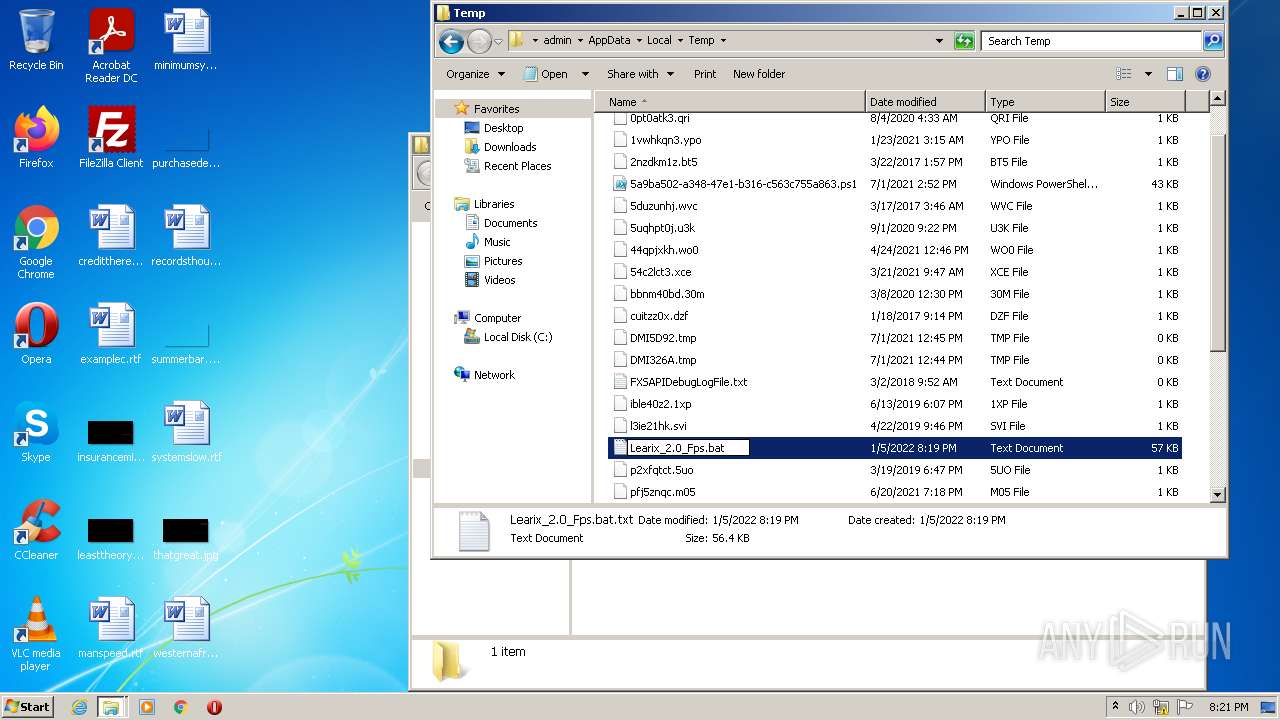
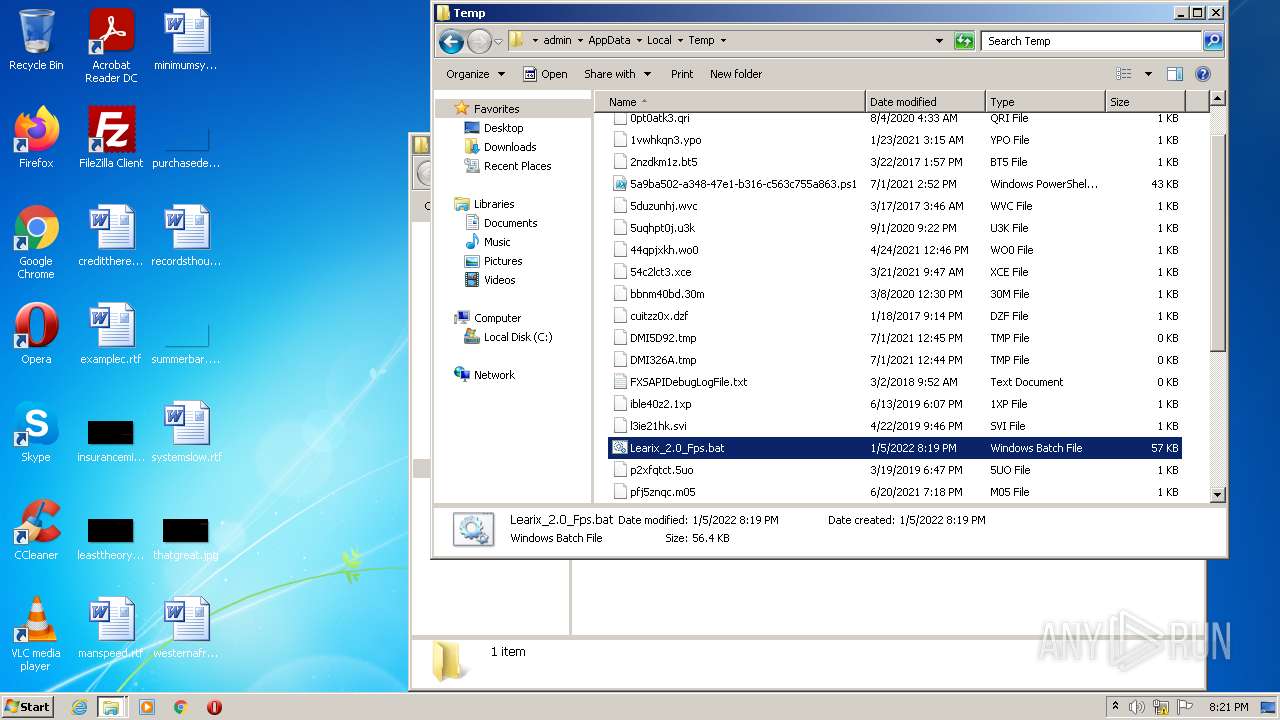
| File name: | Learix_2.0_Fps.bat |
| Full analysis: | https://app.any.run/tasks/605b5d76-2d0b-498f-9e04-28984f64a59d |
| Verdict: | Malicious activity |
| Analysis date: | January 05, 2022, 20:19:22 |
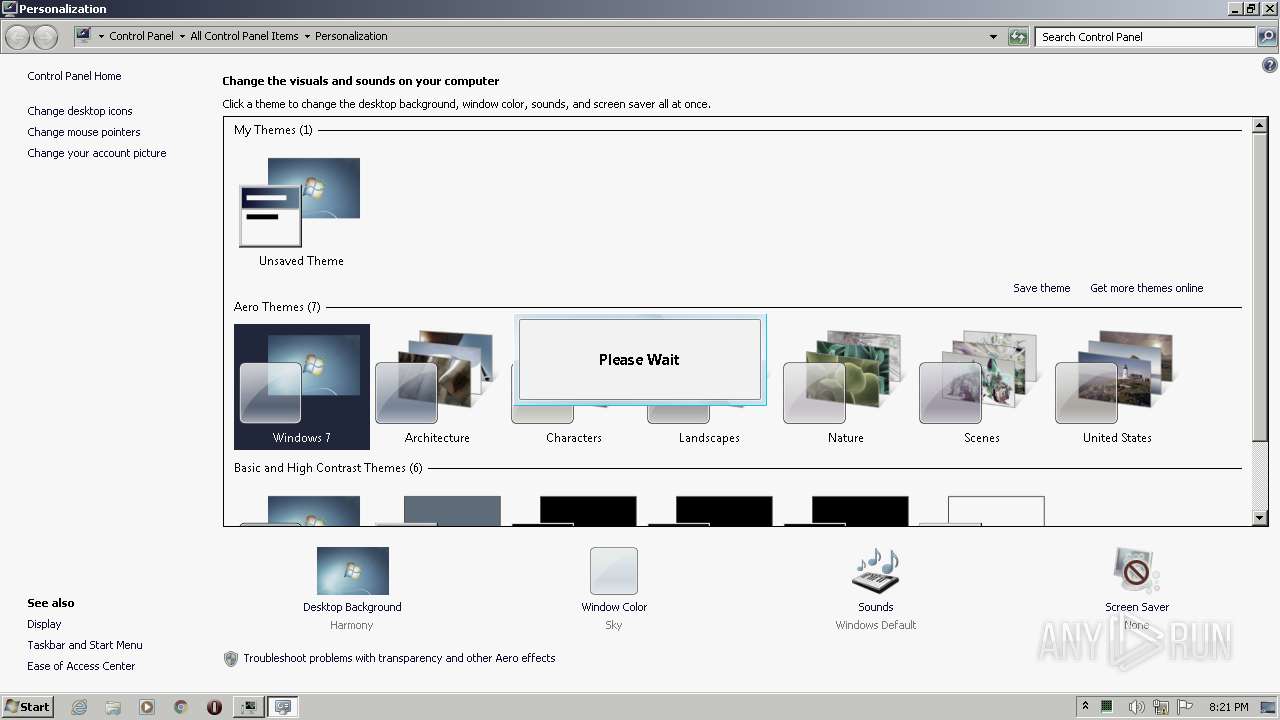
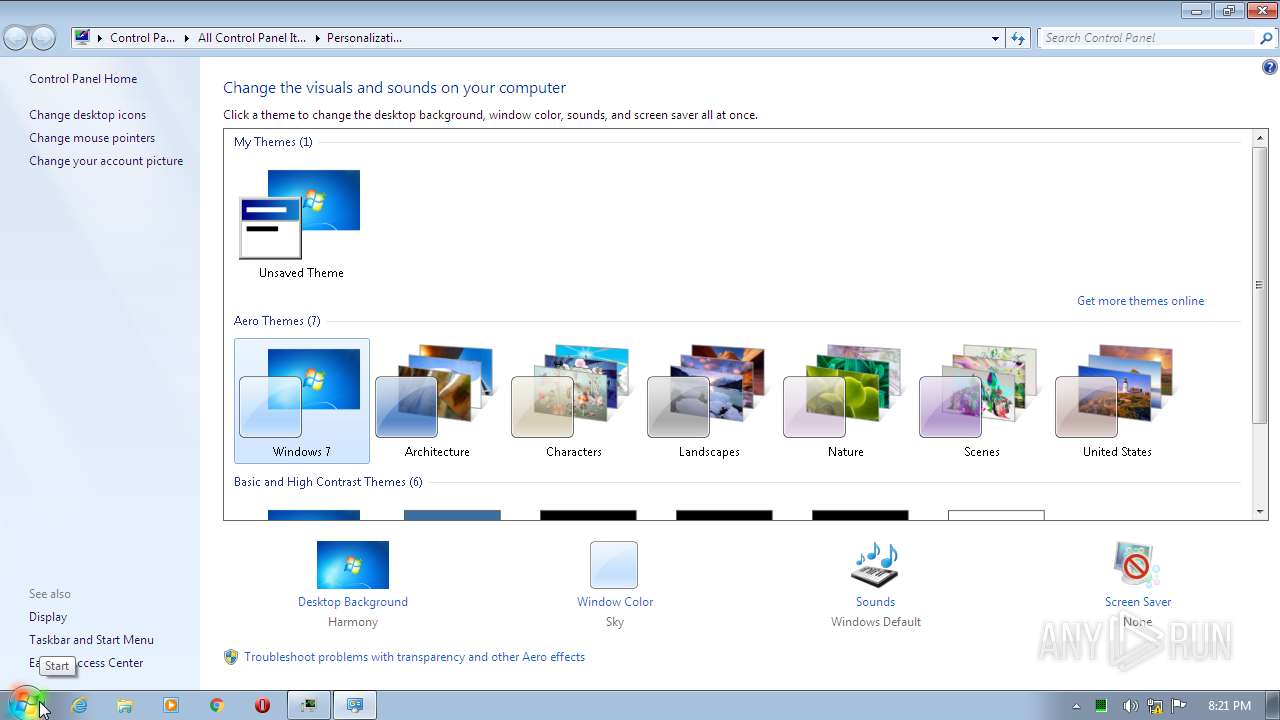
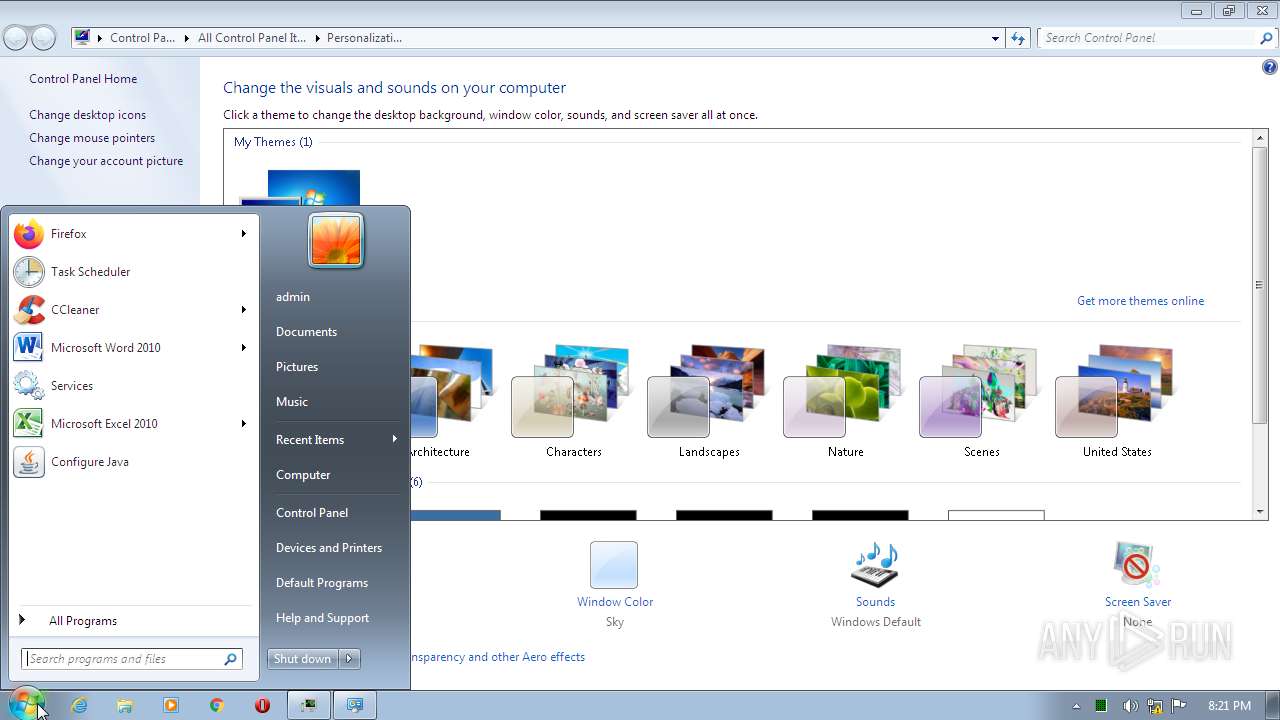
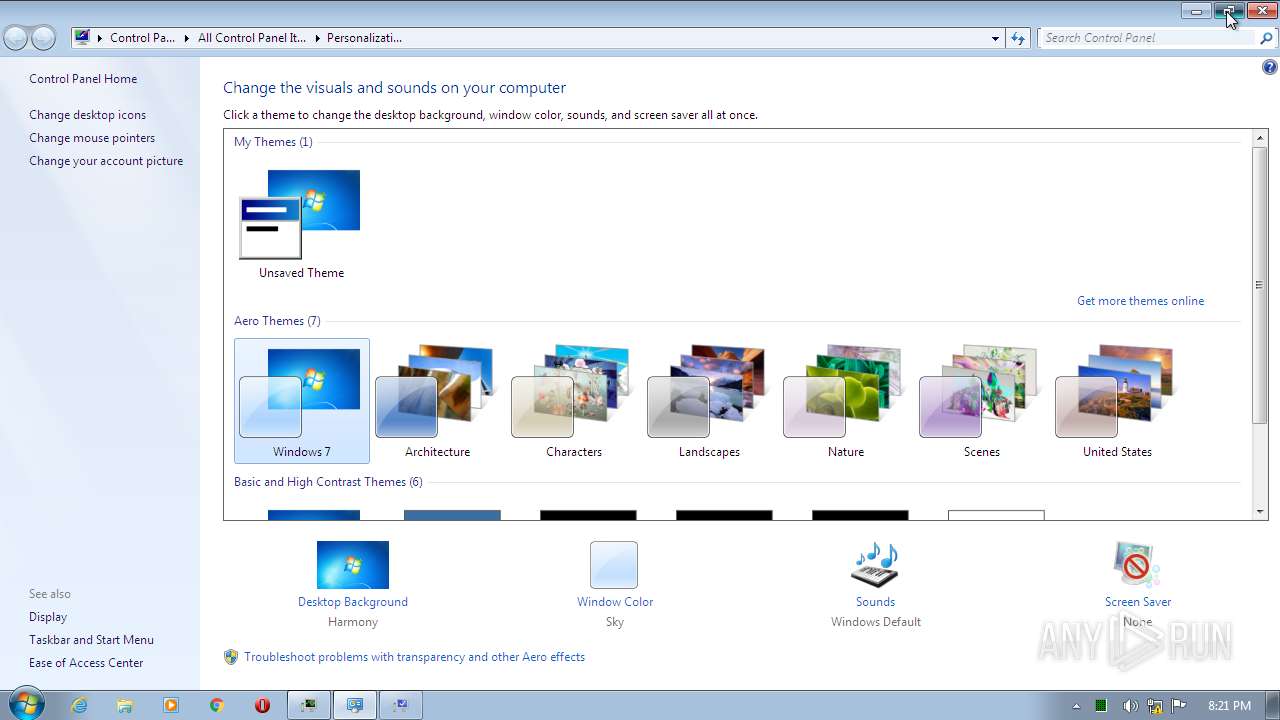
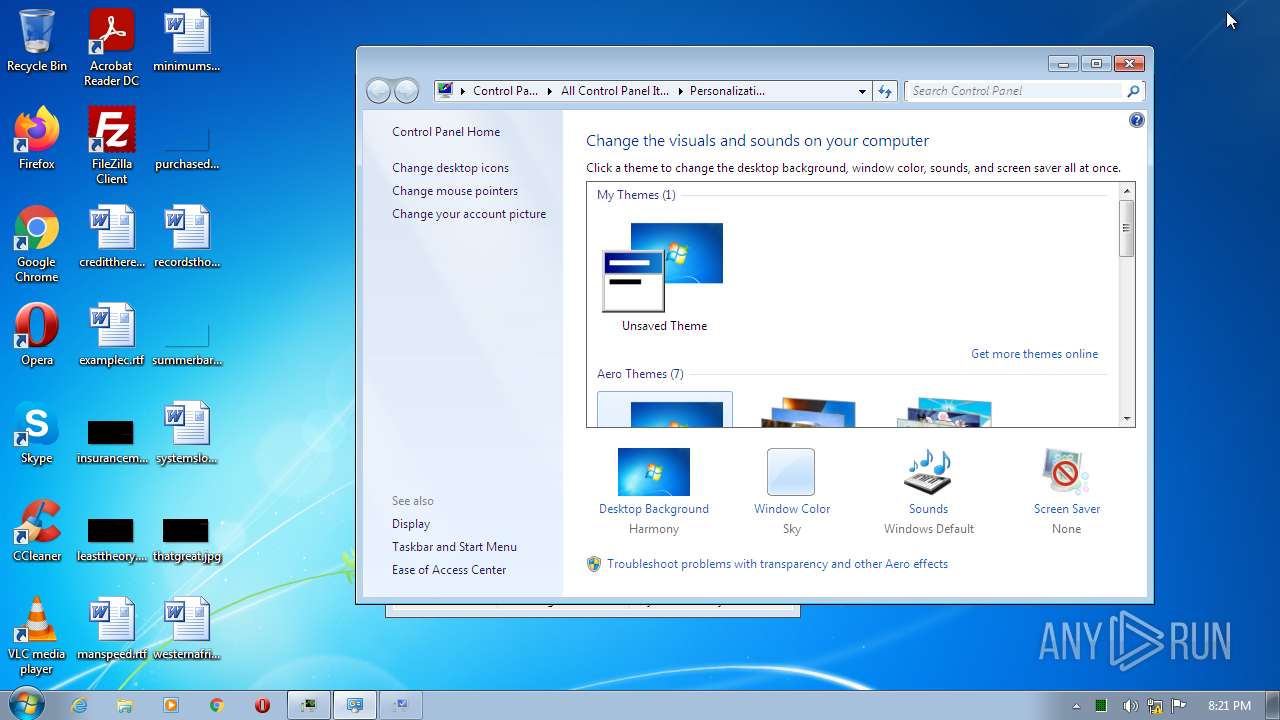
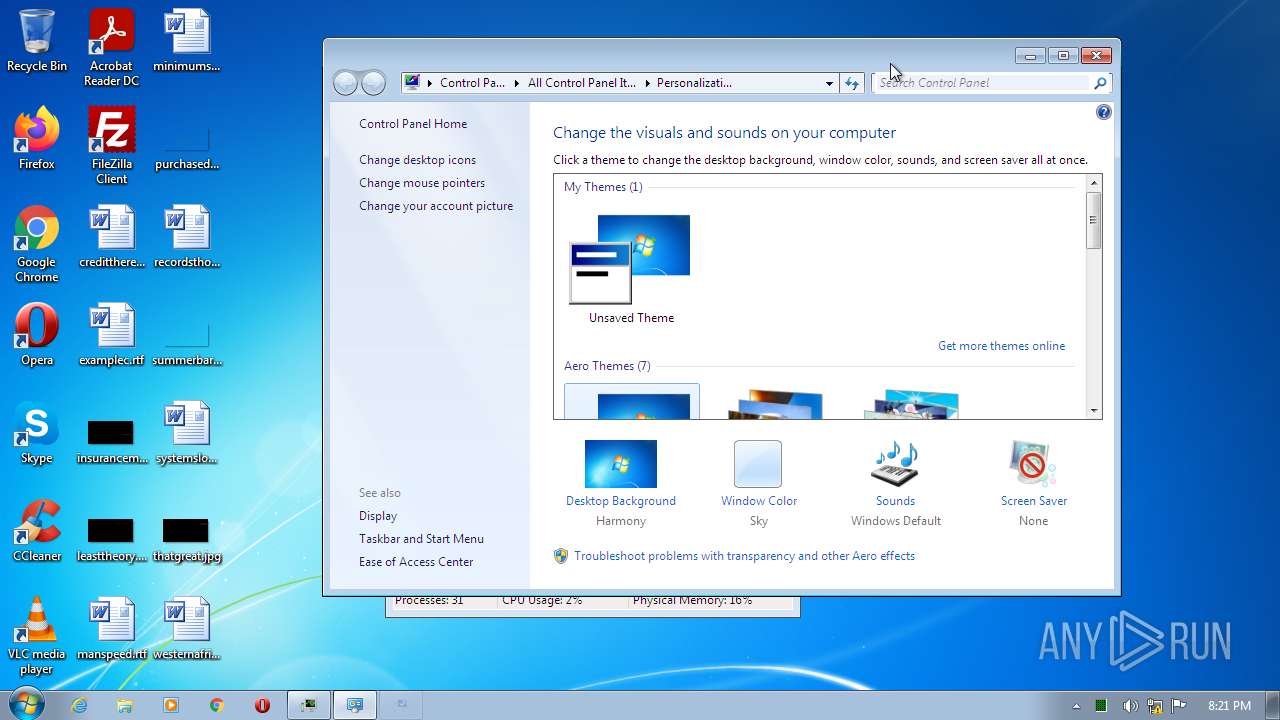
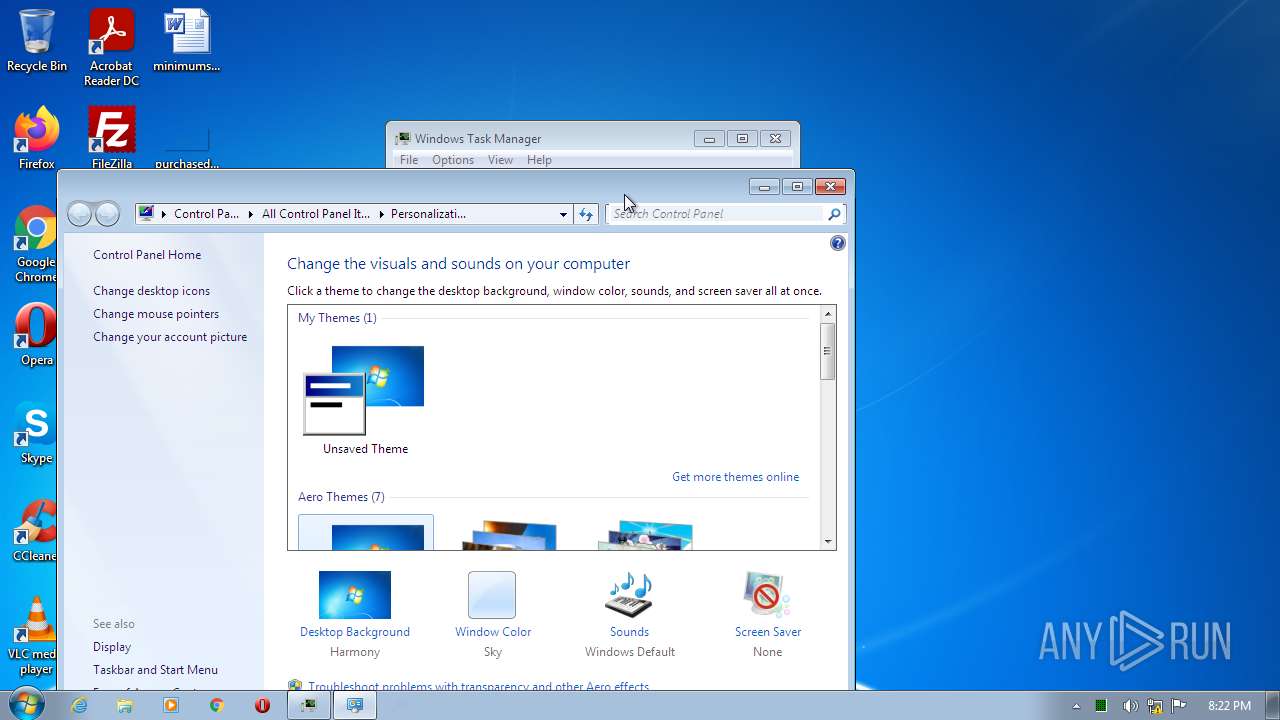
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | Little-endian UTF-16 Unicode text, with very long lines, with no line terminators |
| MD5: | 00C34BD8BD72D2EFDD70FE6737687246 |
| SHA1: | 165C93DB4EF01A071281C7B334A8BD940D53D45F |
| SHA256: | D26FA7E729BCB29CA402AAB21D59C17C9C3C1123C3261E93DC71A65579AF4986 |
| SSDEEP: | 1536:qW5X449tht1MF+VZKQ9u+7XGq2D3Kutht1MF+Vqz:qkI49tht1MF+VZBYMXNu3Kutht1MF+V0 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- cmd.exe (PID: 3156)
- mode.com (PID: 2104)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3156)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 4056)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1864)
INFO
Checks supported languages
- NOTEPAD.EXE (PID: 2288)
- verclsid.exe (PID: 1200)
- reg.exe (PID: 1520)
- taskmgr.exe (PID: 3812)
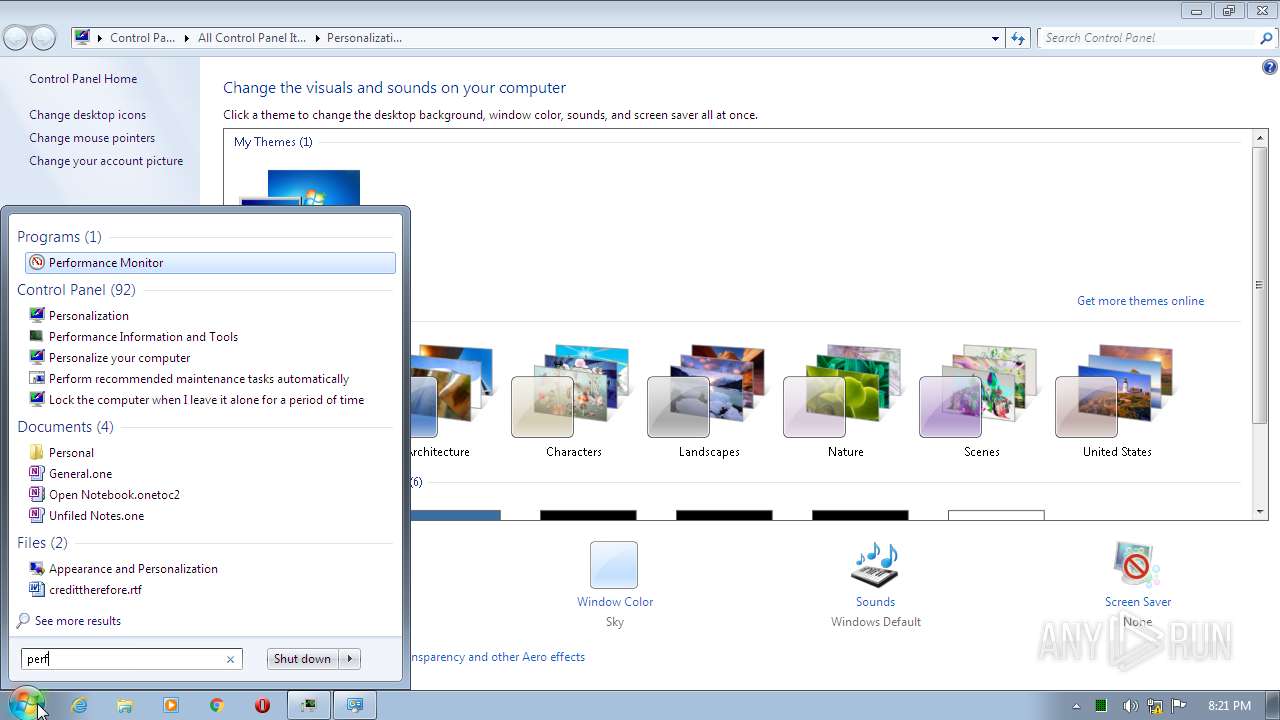
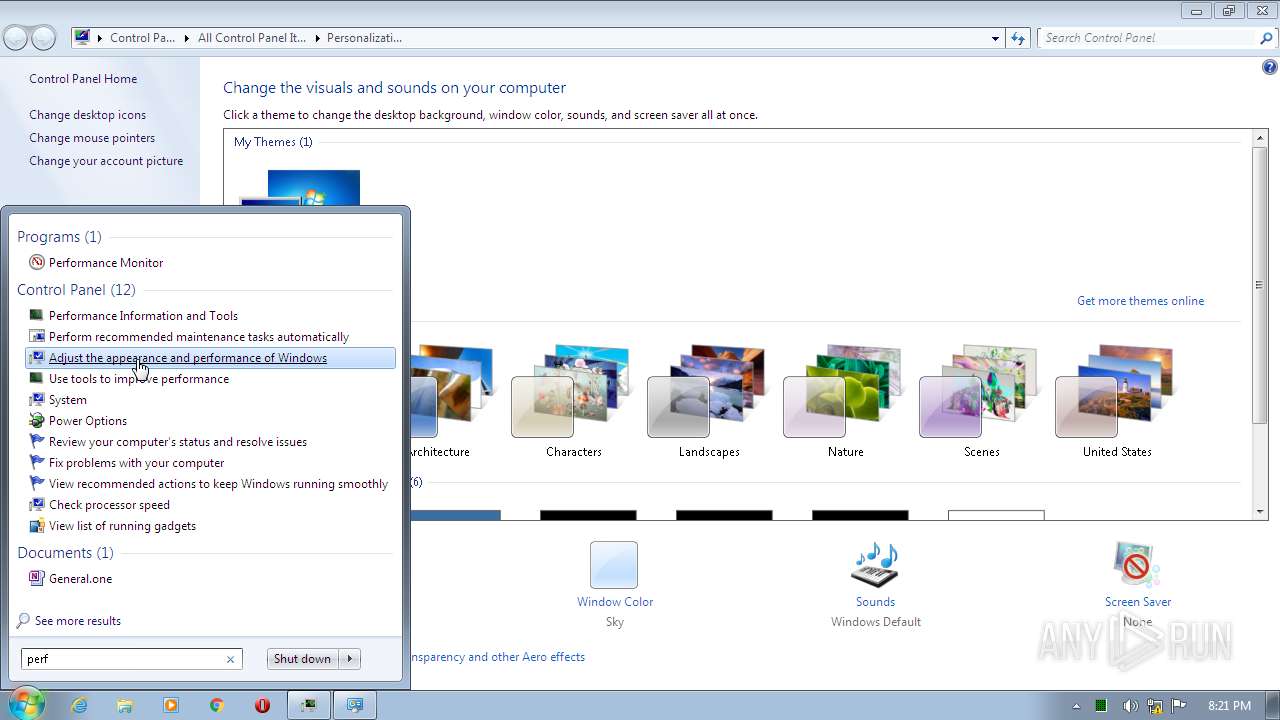
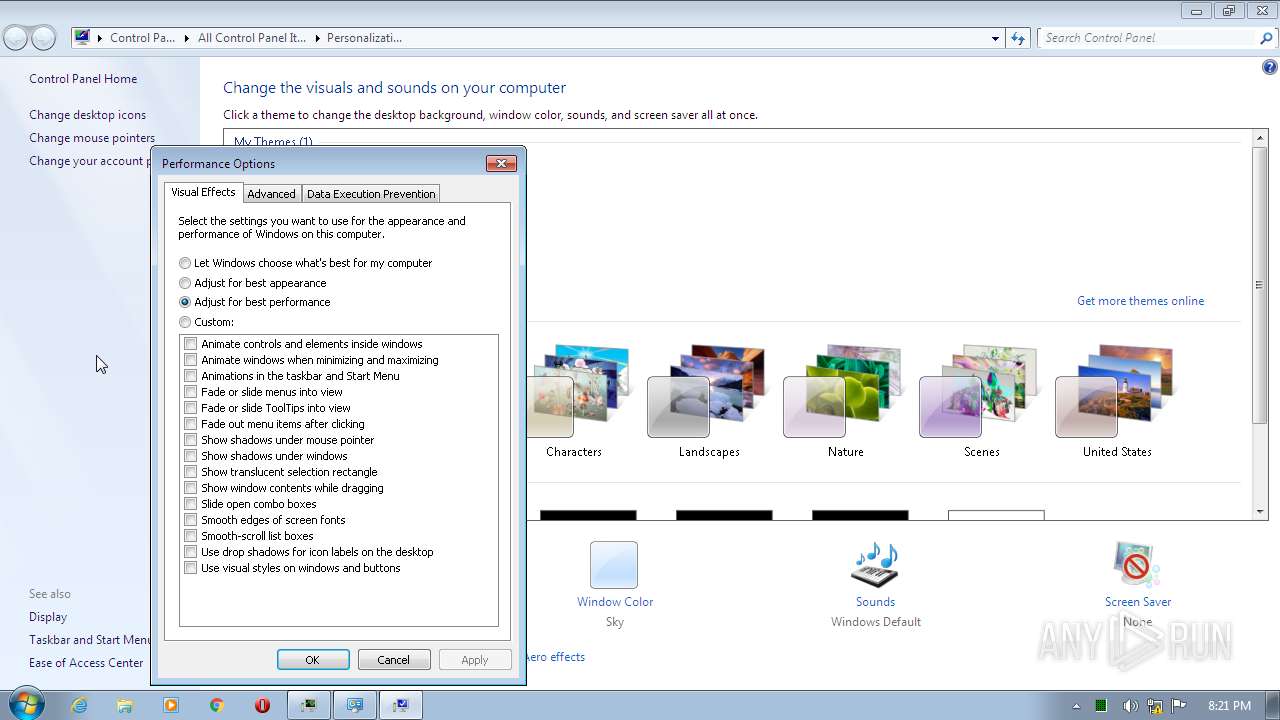
- SystemPropertiesPerformance.exe (PID: 1480)
- chrome.exe (PID: 1864)
- chrome.exe (PID: 2460)
- chrome.exe (PID: 4072)
- chrome.exe (PID: 2916)
- chrome.exe (PID: 3748)
- iexplore.exe (PID: 4056)
- chrome.exe (PID: 3764)
- chrome.exe (PID: 2496)
- chrome.exe (PID: 3812)
- chrome.exe (PID: 2260)
- chrome.exe (PID: 3860)
- chrome.exe (PID: 1992)
- chrome.exe (PID: 4036)
- chrome.exe (PID: 3036)
- chrome.exe (PID: 1116)
- chrome.exe (PID: 2900)
- chrome.exe (PID: 612)
- iexplore.exe (PID: 392)
- chrome.exe (PID: 3932)
- chrome.exe (PID: 1288)
- chrome.exe (PID: 1512)
- chrome.exe (PID: 2088)
- chrome.exe (PID: 496)
- chrome.exe (PID: 3216)
- chrome.exe (PID: 2144)
- chrome.exe (PID: 2040)
- chrome.exe (PID: 3044)
- chrome.exe (PID: 2908)
- chrome.exe (PID: 1852)
Reads the computer name
- iexplore.exe (PID: 392)
- taskmgr.exe (PID: 3812)
- iexplore.exe (PID: 4056)
- SystemPropertiesPerformance.exe (PID: 1480)
- chrome.exe (PID: 1864)
- chrome.exe (PID: 4072)
- chrome.exe (PID: 2916)
- chrome.exe (PID: 3812)
- chrome.exe (PID: 3932)
- chrome.exe (PID: 1512)
- chrome.exe (PID: 1852)
- chrome.exe (PID: 3044)
Reads the date of Windows installation
- iexplore.exe (PID: 392)
- chrome.exe (PID: 3044)
Changes internet zones settings
- iexplore.exe (PID: 392)
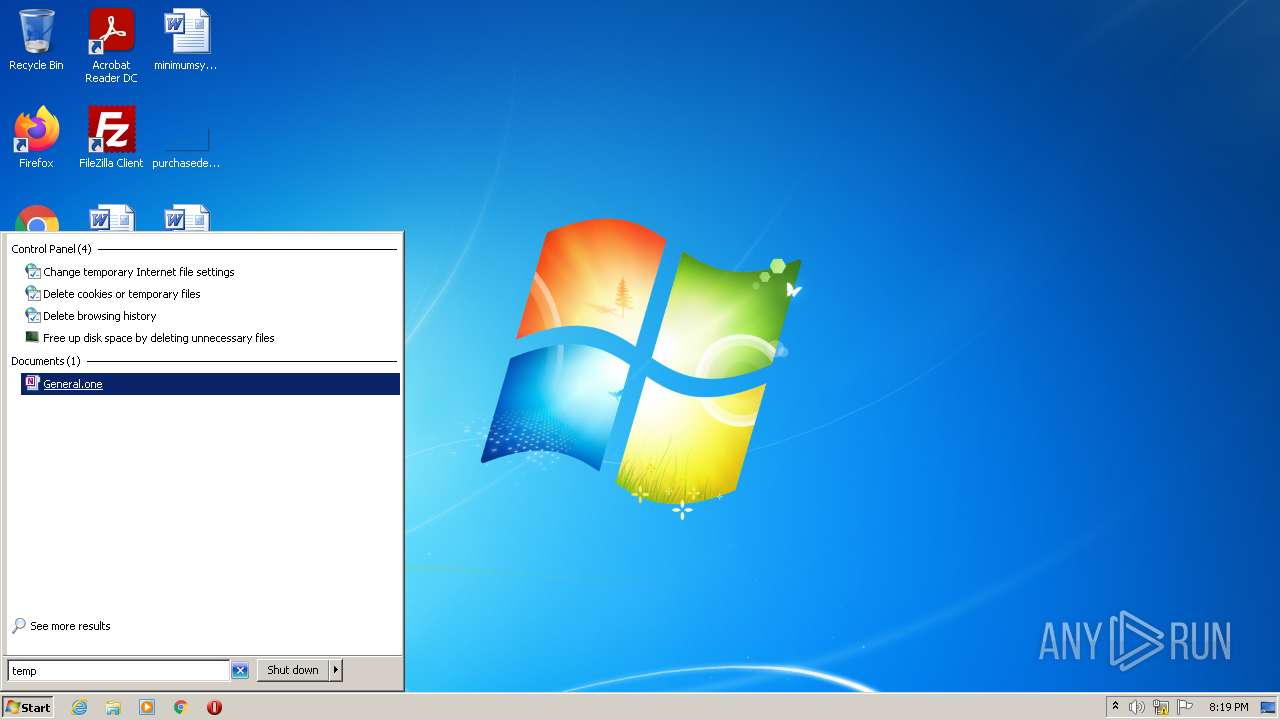
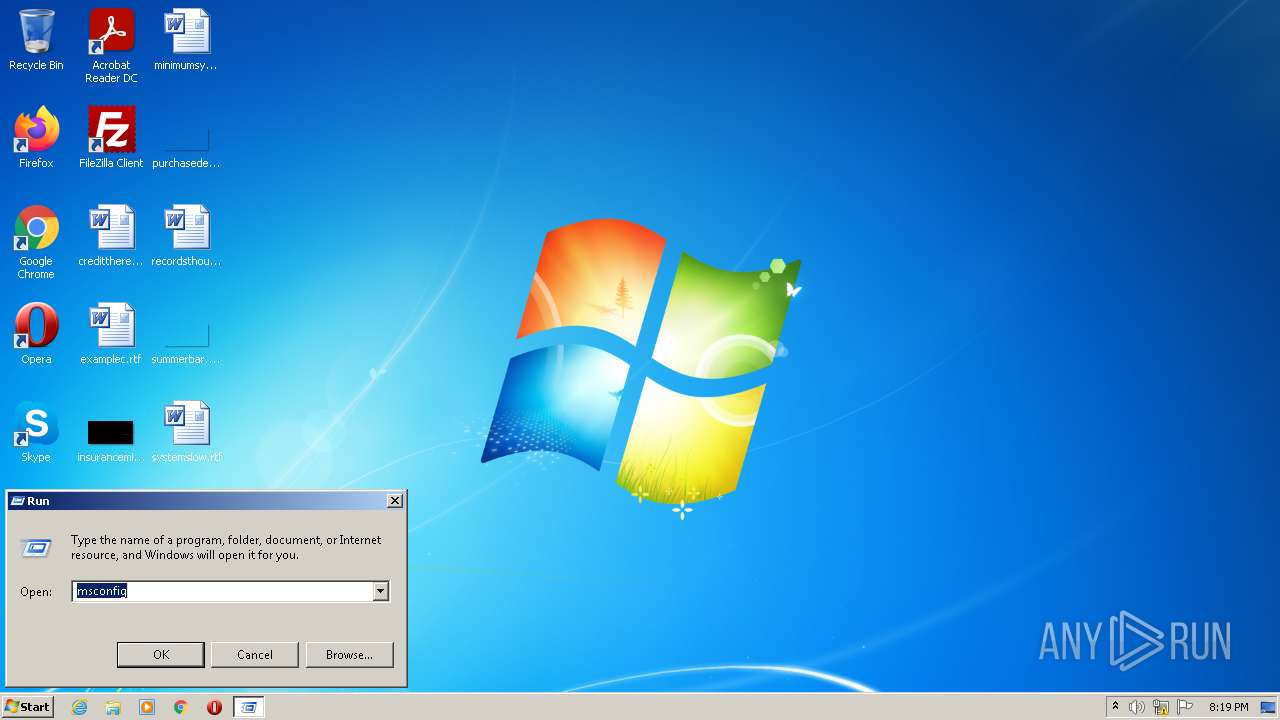
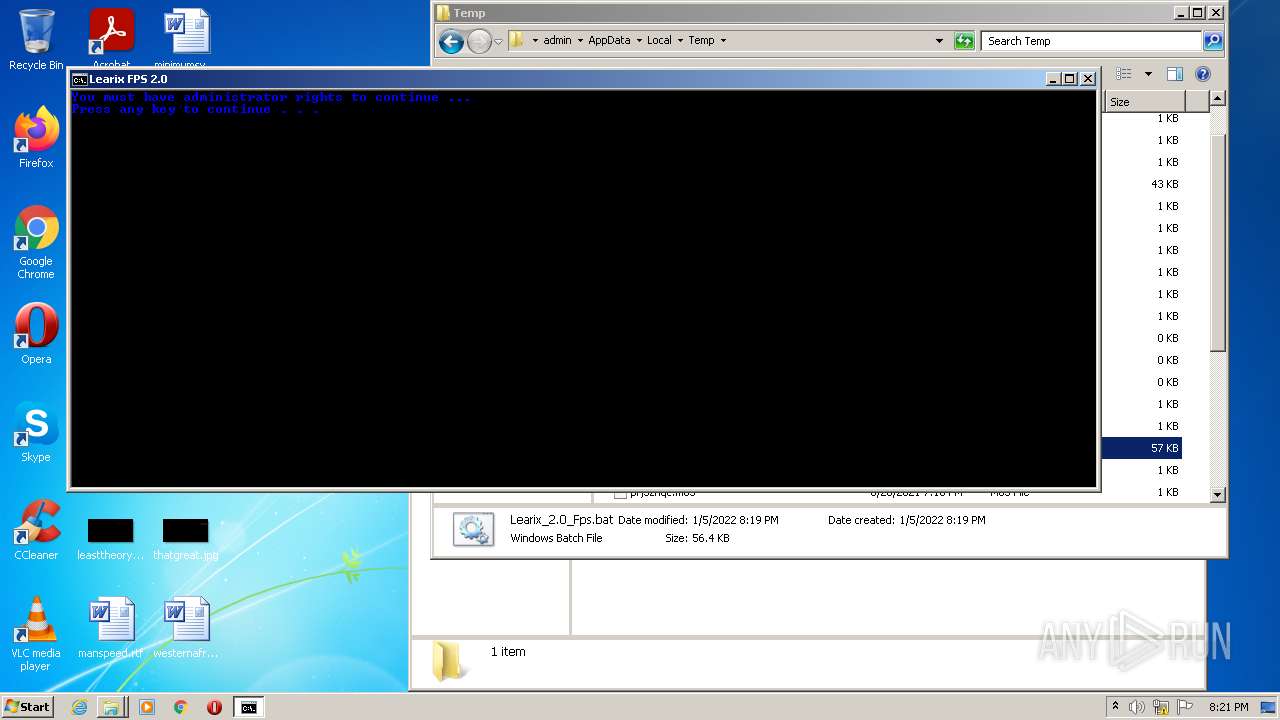
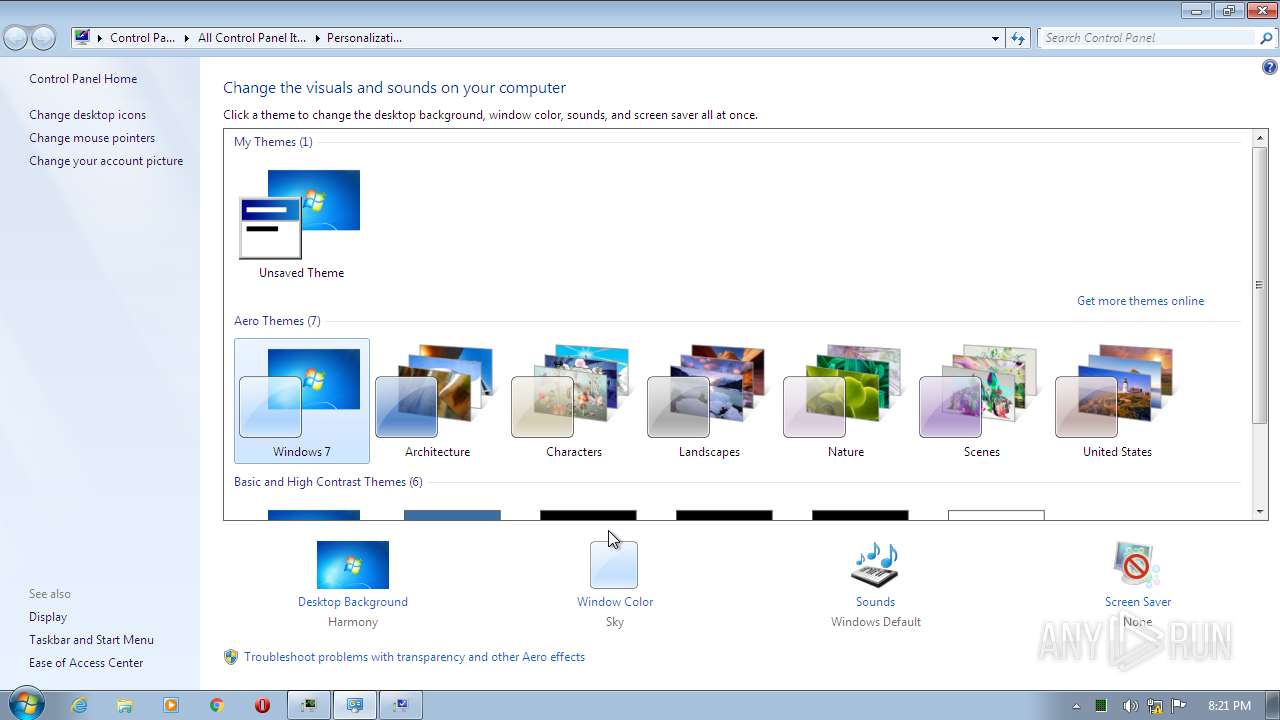
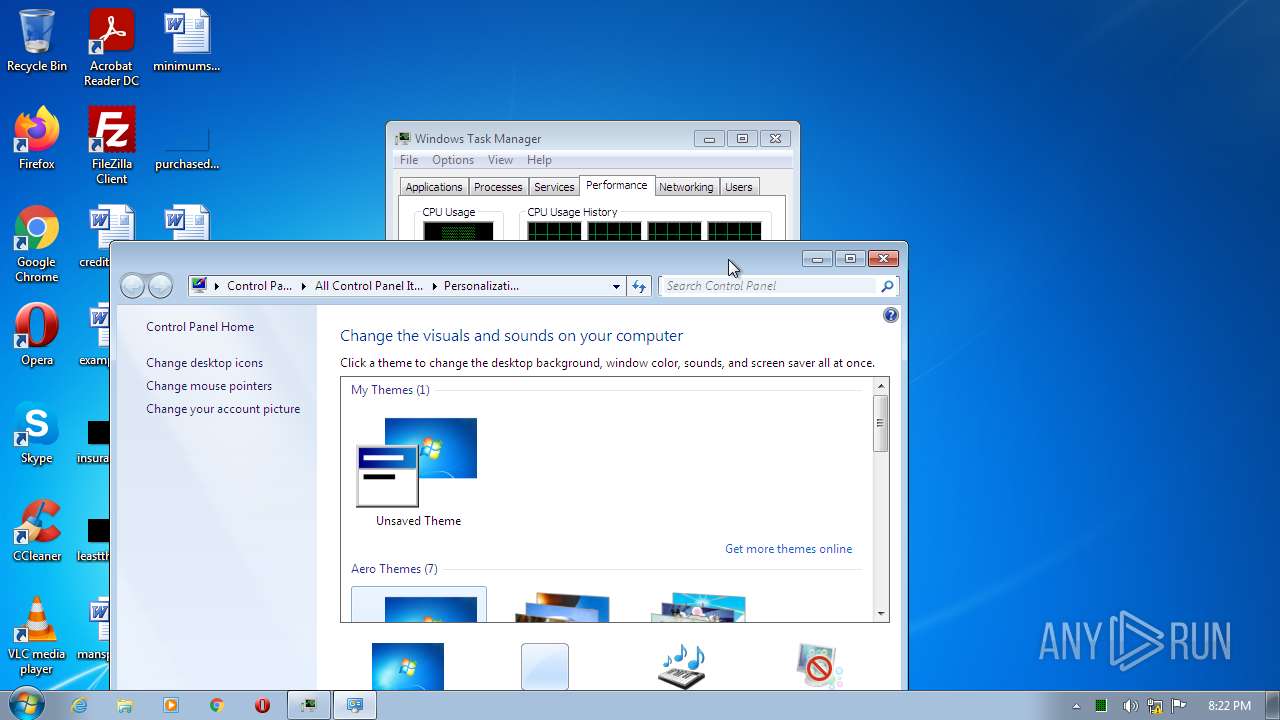
Manual execution by user
- verclsid.exe (PID: 1200)
- cmd.exe (PID: 3156)
- taskmgr.exe (PID: 3812)
- SystemPropertiesPerformance.exe (PID: 2480)
- SystemPropertiesPerformance.exe (PID: 1480)
- chrome.exe (PID: 1864)
- iexplore.exe (PID: 392)
Application launched itself
- chrome.exe (PID: 1864)
- iexplore.exe (PID: 392)
Reads the hosts file
- chrome.exe (PID: 1864)
- chrome.exe (PID: 2916)
Reads settings of System Certificates
- chrome.exe (PID: 2916)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .txt | | | Text - UTF-16 (LE) encoded (66.6) |
|---|---|---|
| .mp3 | | | MP3 audio (33.3) |
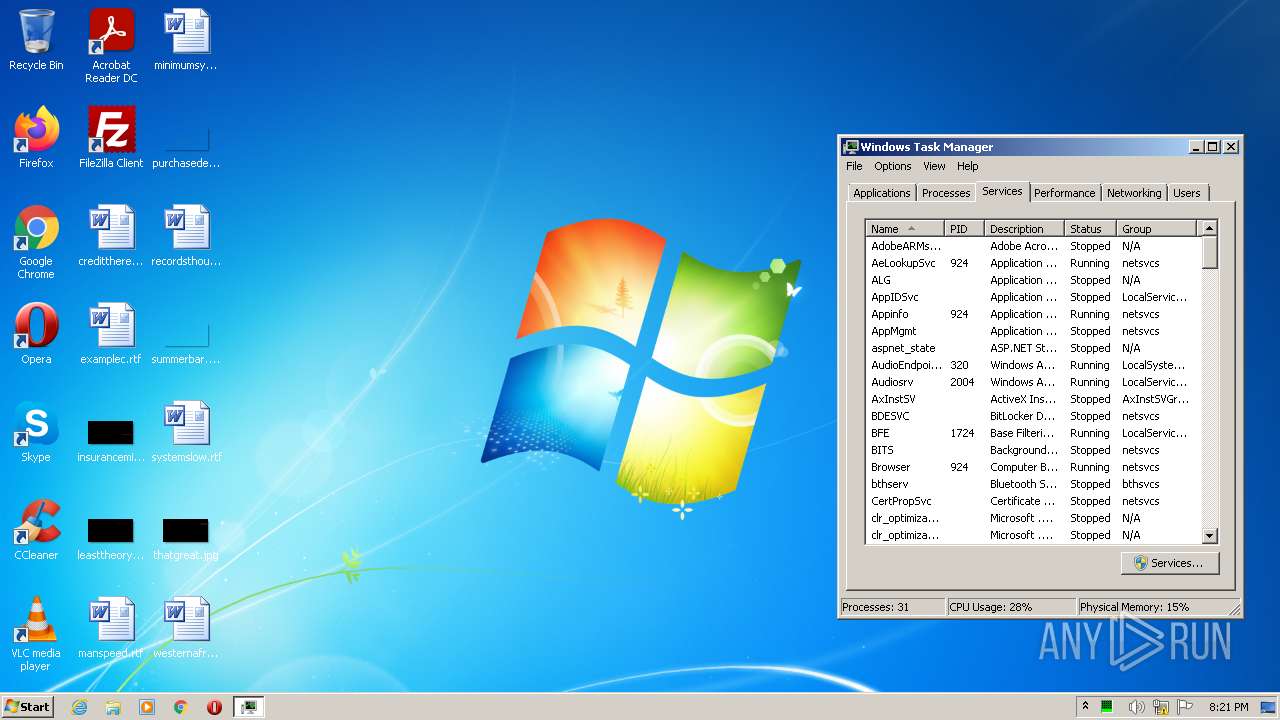
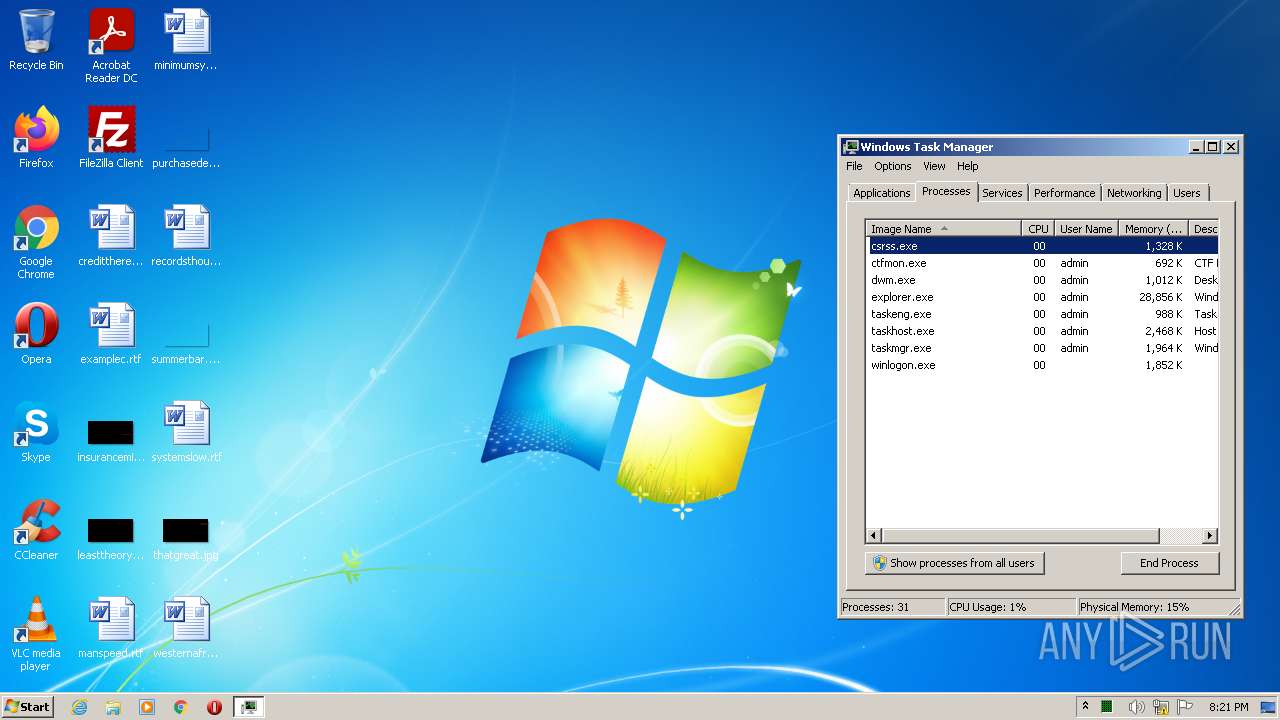
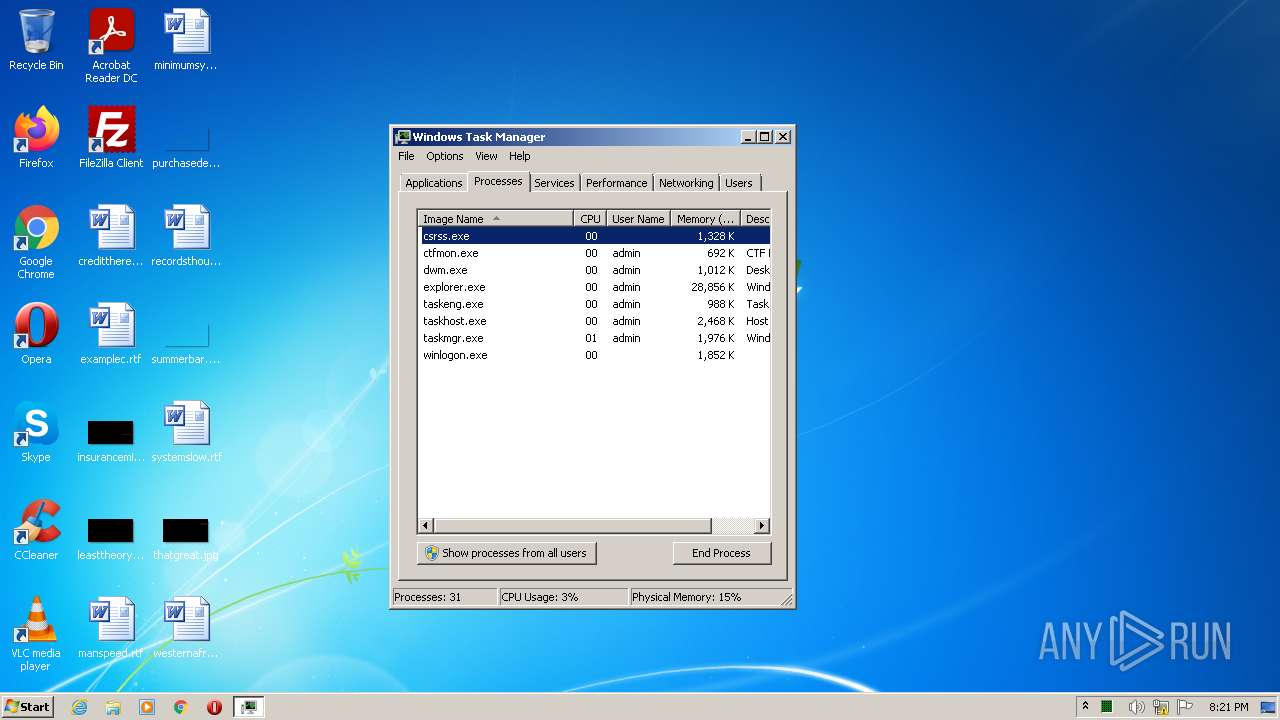
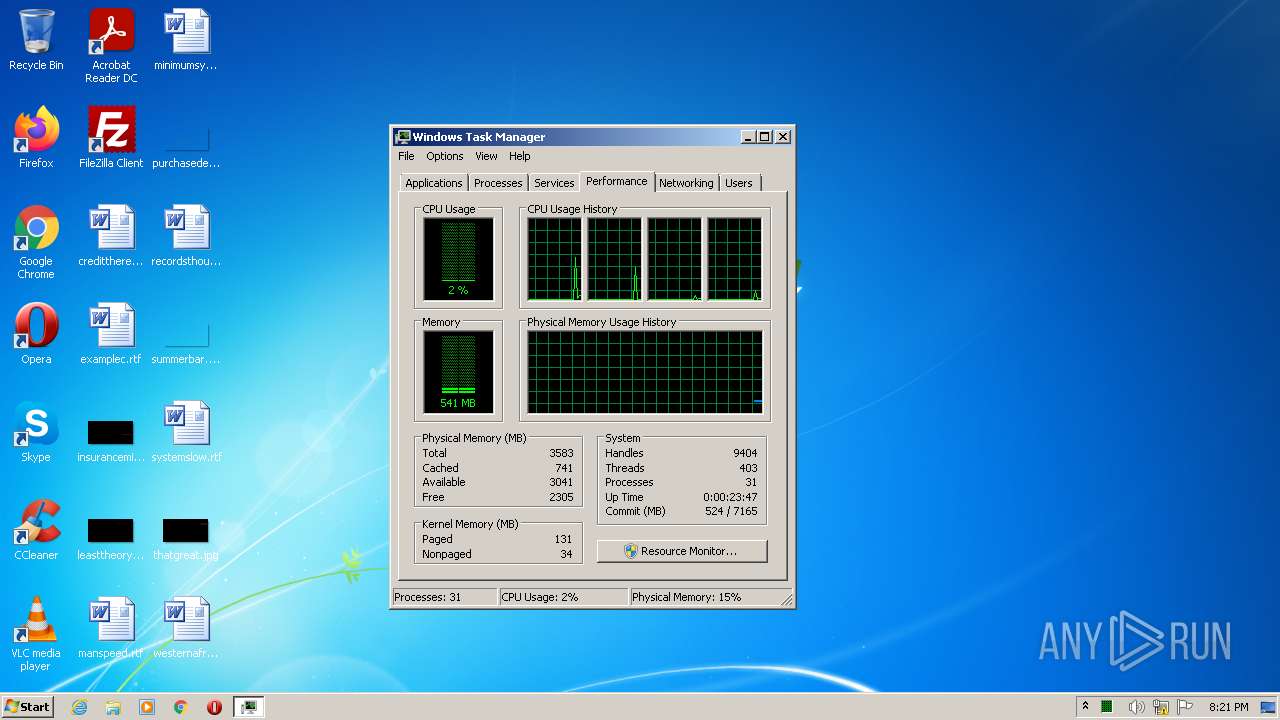
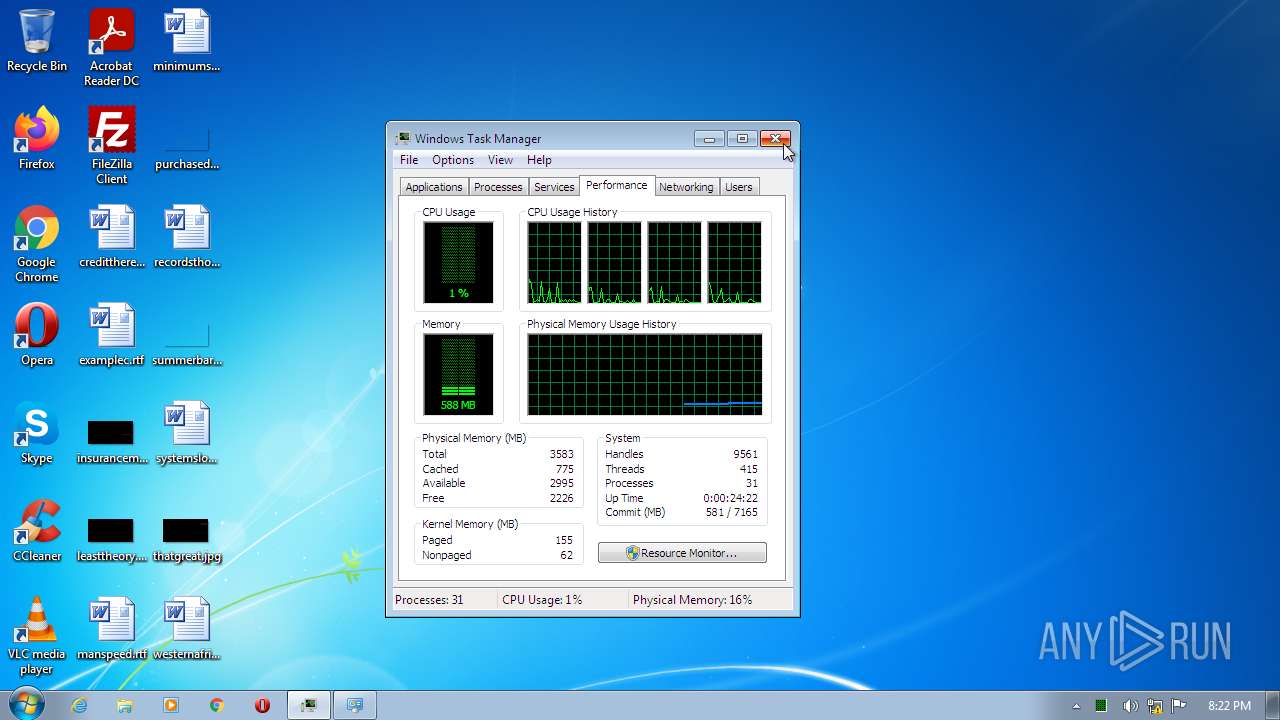
Total processes
81
Monitored processes
37
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
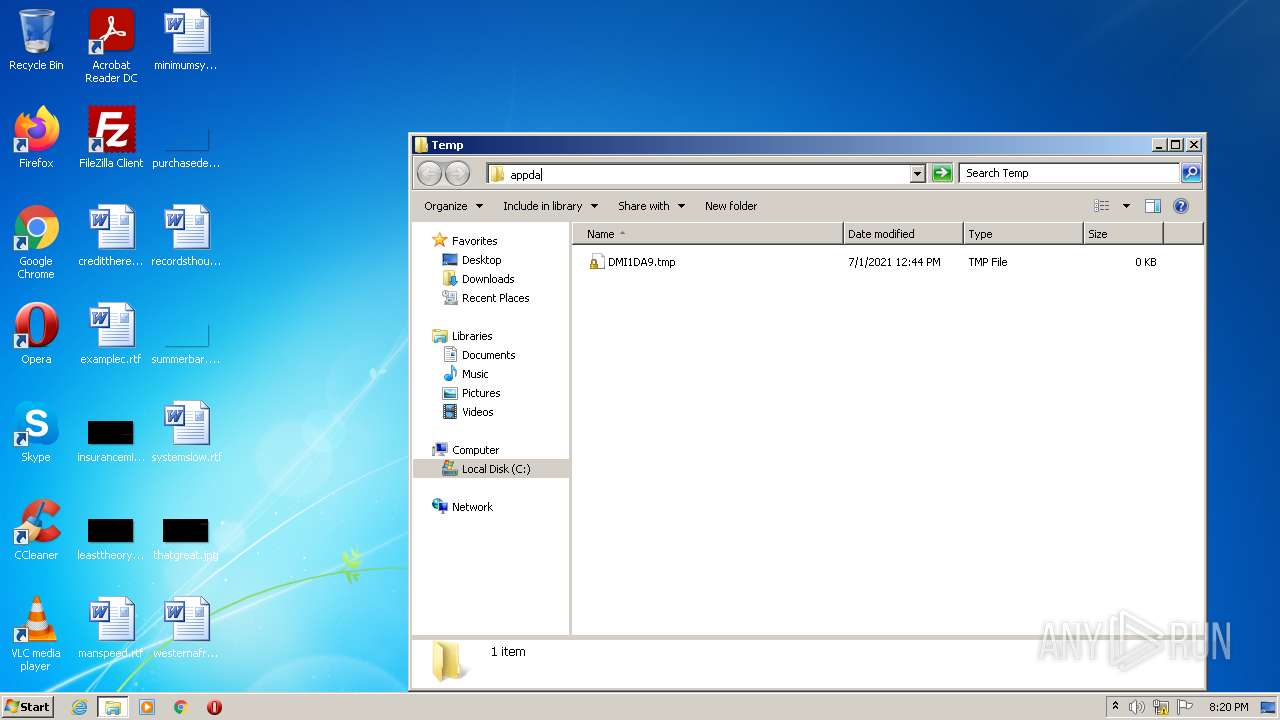
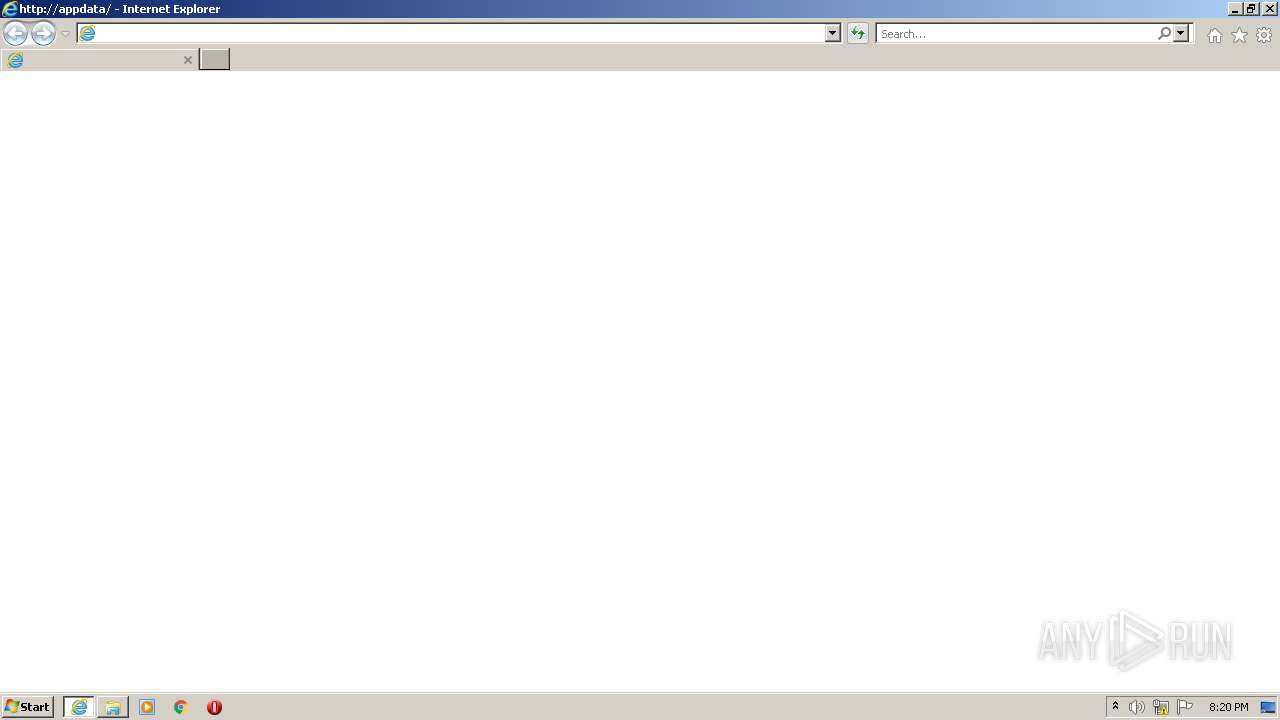
| 392 | "C:\Program Files\Internet Explorer\iexplore.exe" http://appdata/ | C:\Program Files\Internet Explorer\iexplore.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1064,16281818395584084323,9216034564667728565,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=4032 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 612 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1064,16281818395584084323,9216034564667728565,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3488 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1064,16281818395584084323,9216034564667728565,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2564 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1200 | "C:\Windows\system32\verclsid.exe" /S /C {0B2C9183-C9FA-4C53-AE21-C900B0C39965} /I {0C733A8A-2A1C-11CE-ADE5-00AA0044773D} /X 0x401 | C:\Windows\system32\verclsid.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Extension CLSID Verification Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1288 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1064,16281818395584084323,9216034564667728565,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2396 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
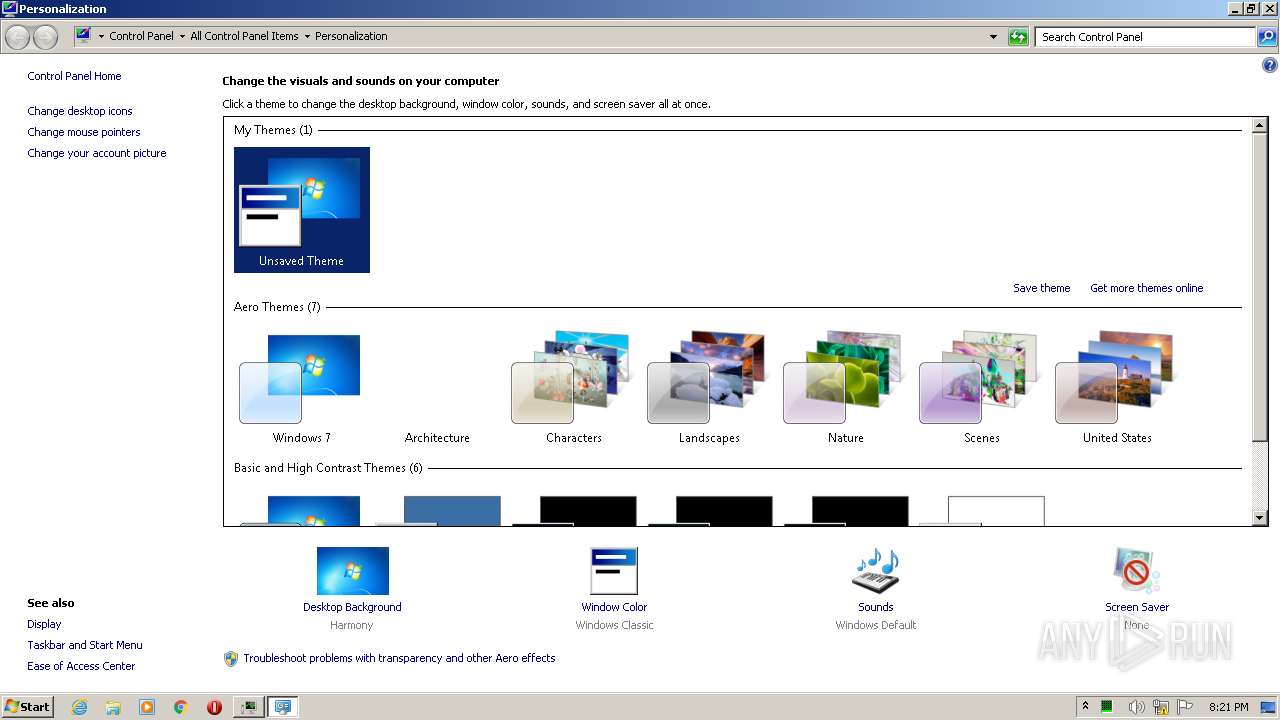
| 1480 | "C:\Windows\system32\SystemPropertiesPerformance.exe" | C:\Windows\system32\SystemPropertiesPerformance.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change Computer Performance Settings Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1512 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --field-trial-handle=1064,16281818395584084323,9216034564667728565,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=audio --mojo-platform-channel-handle=3984 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1520 | Reg.exe query "HKU\S-1-5-19\Environment" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1064,16281818395584084323,9216034564667728565,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3860 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
16 498
Read events
16 314
Write events
181
Delete events
3
Modification events
| (PID) Process: | (392) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (392) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (392) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30933617 | |||
| (PID) Process: | (392) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (392) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30933617 | |||
| (PID) Process: | (392) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (392) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (392) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (392) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (392) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
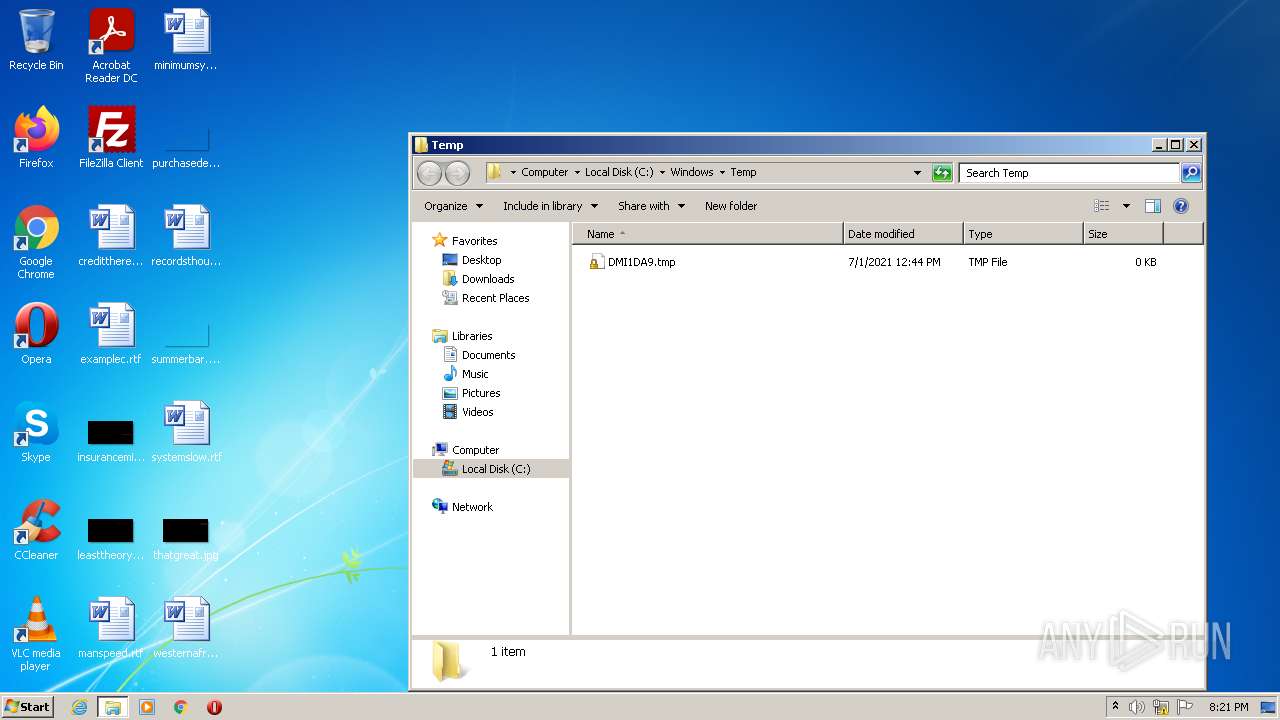
Executable files
0
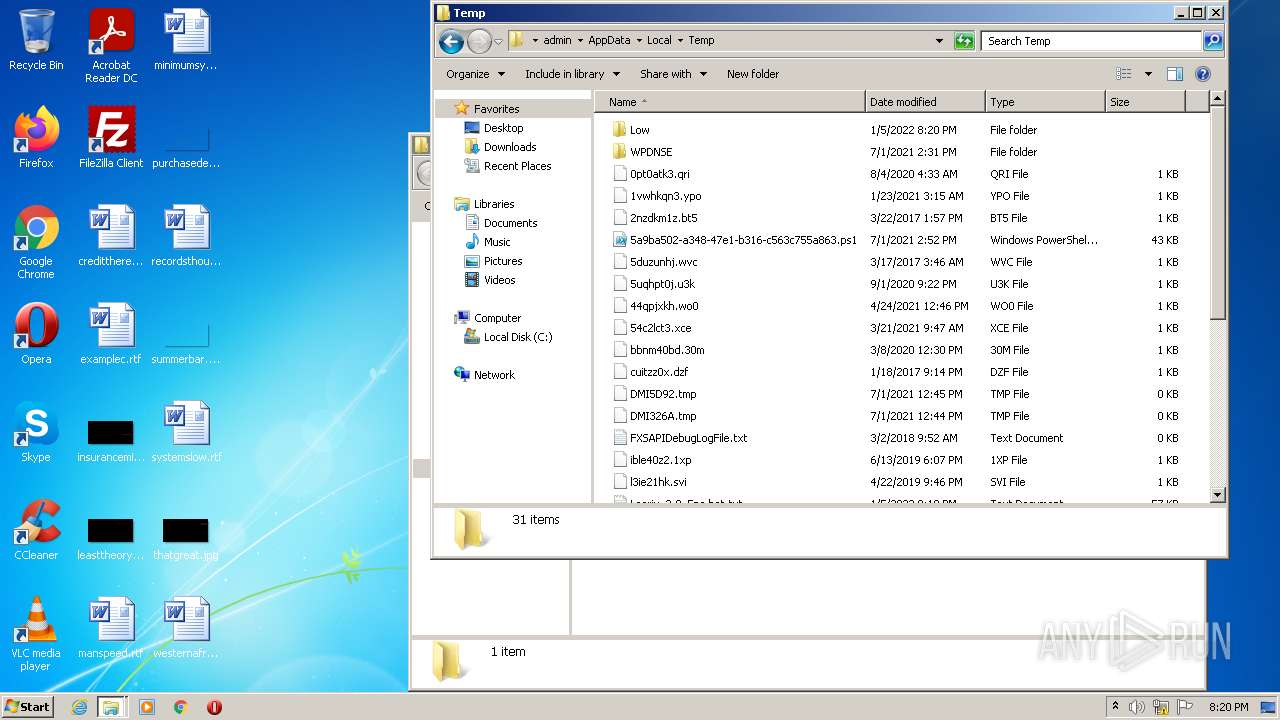
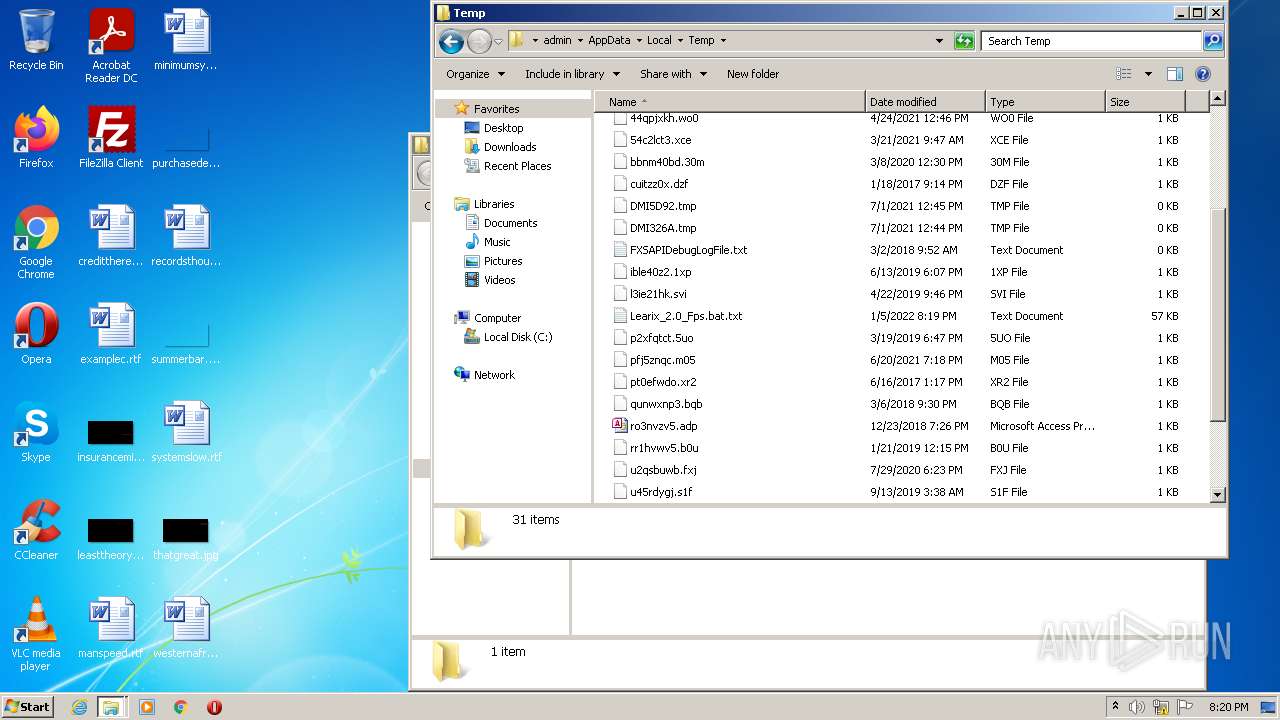
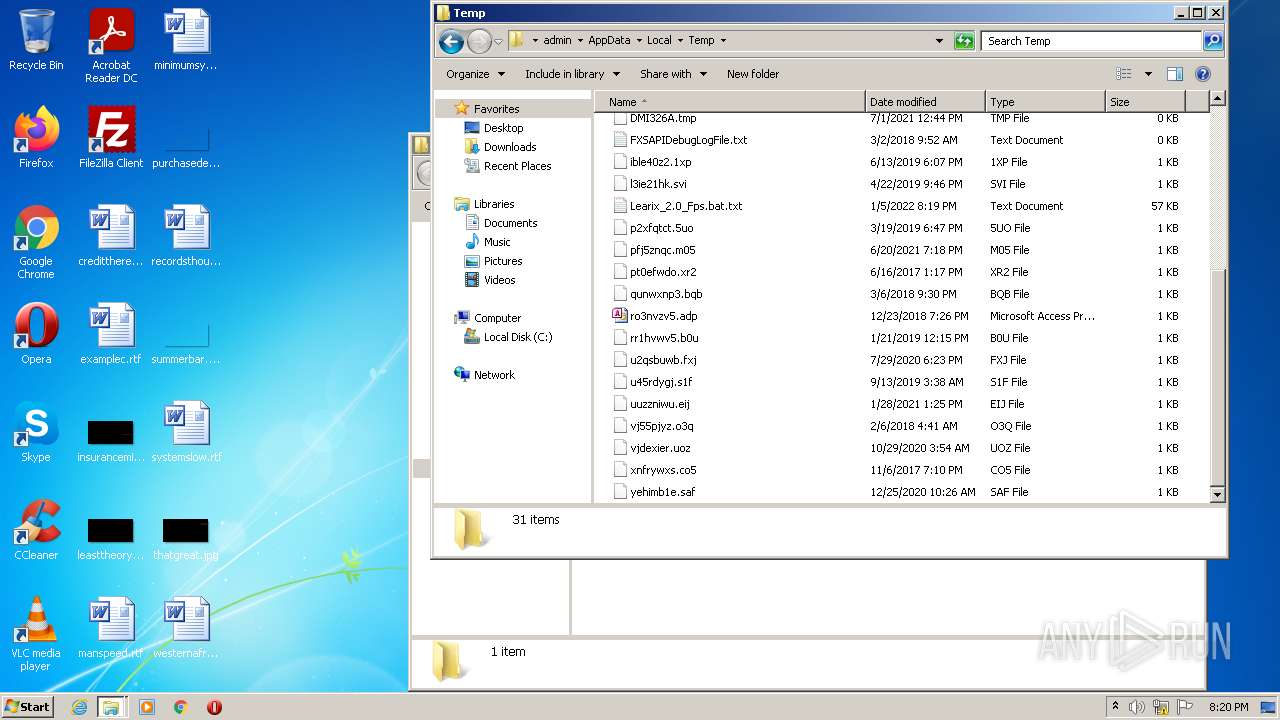
Suspicious files
223
Text files
118
Unknown types
16
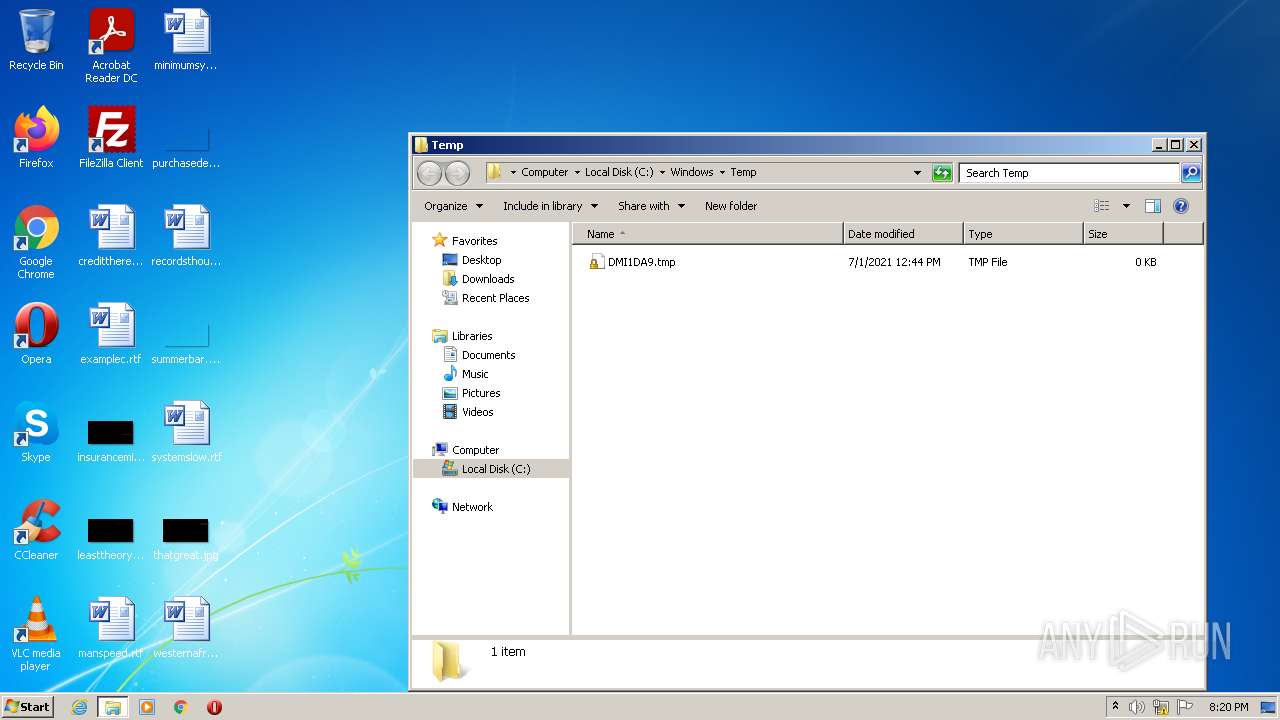
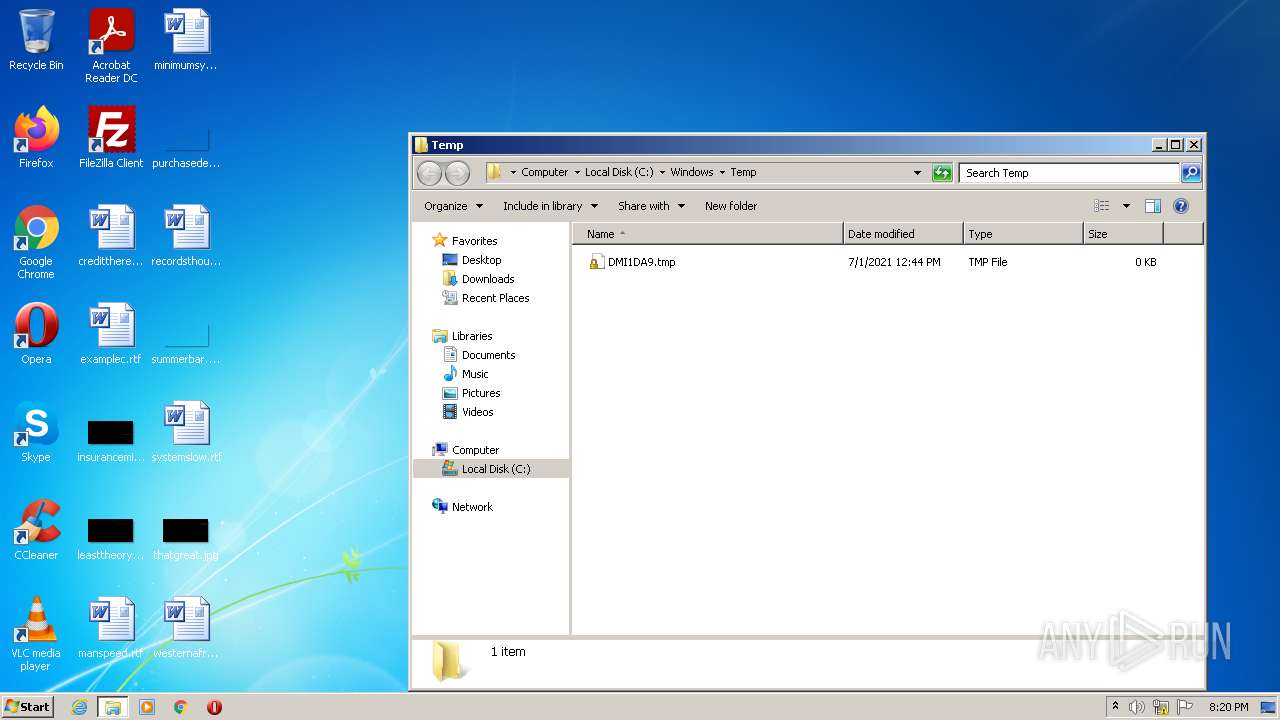
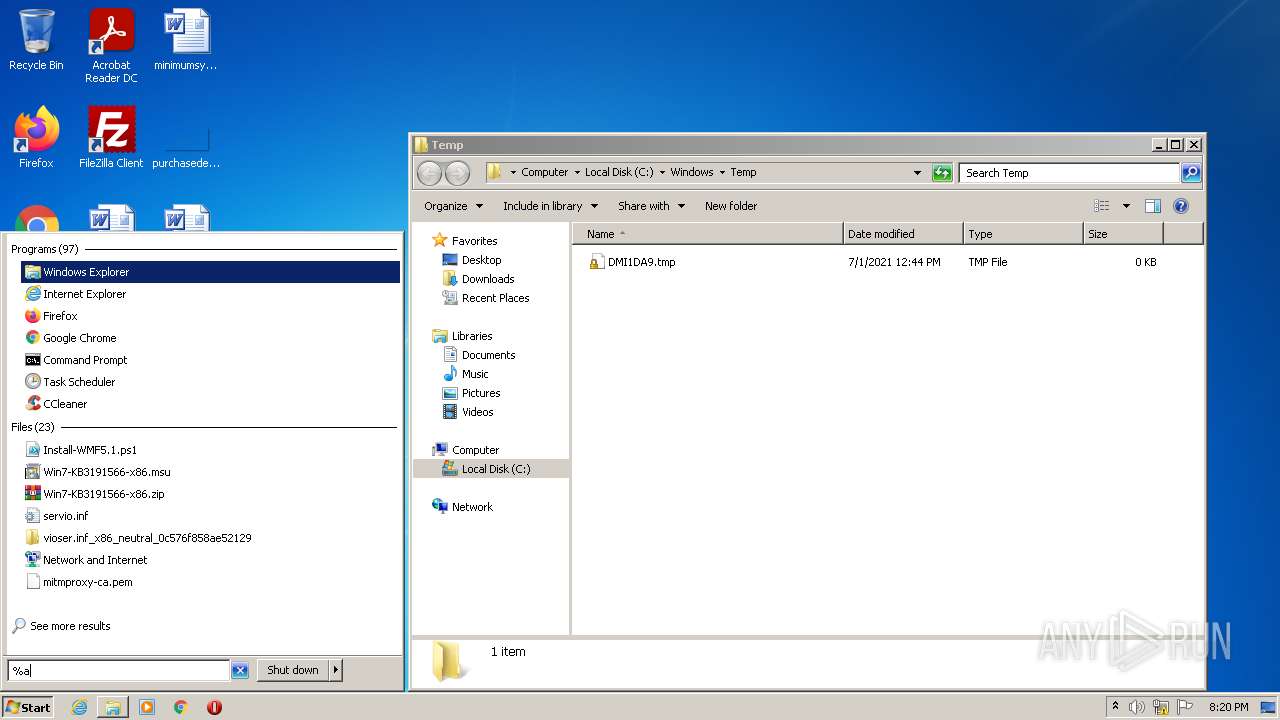
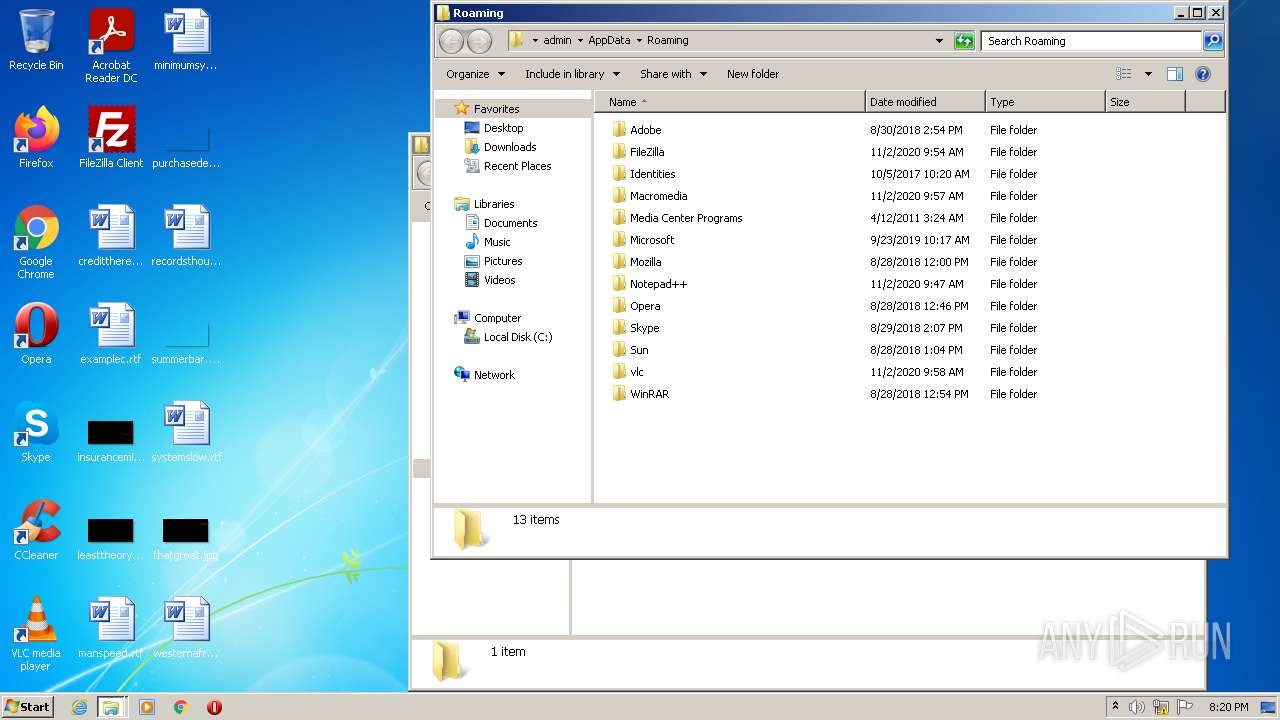
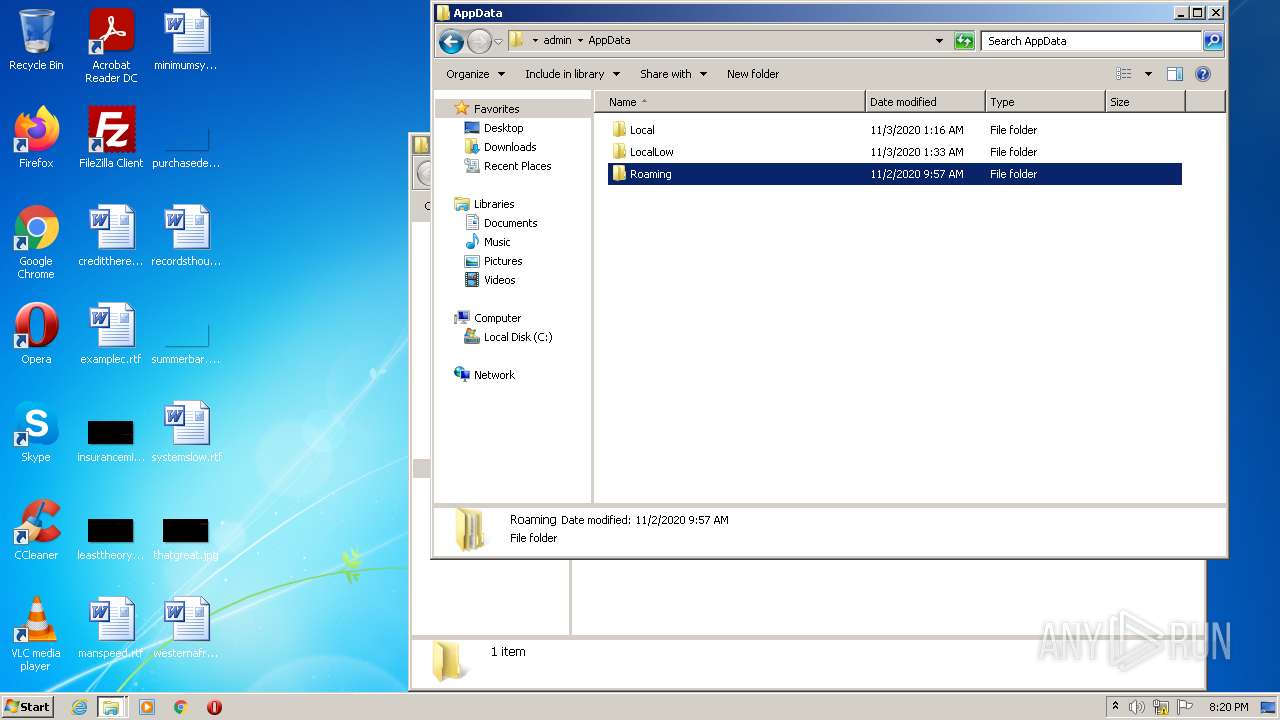
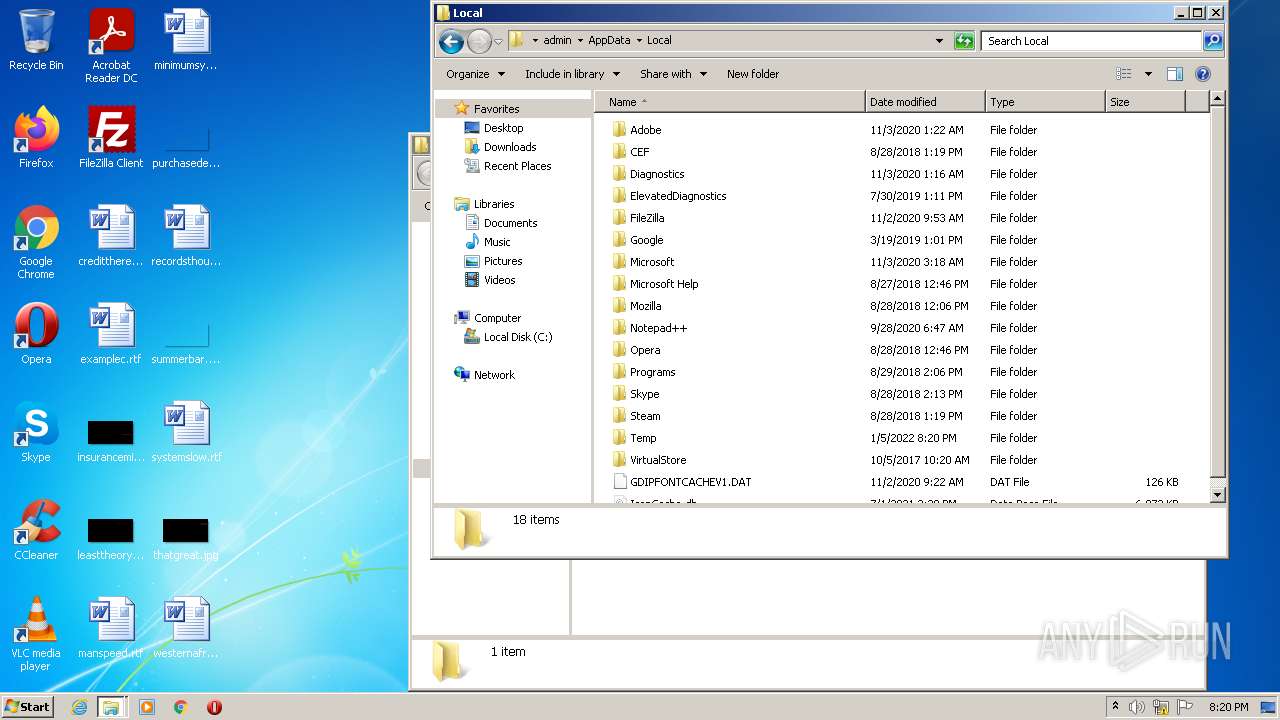
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61D5FDFA-748.pma | — | |
MD5:— | SHA256:— | |||
| 392 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{E0245469-6E64-11EC-A20C-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 392 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{E024546B-6E64-11EC-A20C-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 392 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\RecoveryStore.{42C873D0-1D90-11EB-BA2C-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 392 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFA158FE0085470166.TMP | gmc | |
MD5:— | SHA256:— | |||
| 392 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF86E301F7C46F8F5F.TMP | gmc | |
MD5:— | SHA256:— | |||
| 2916 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\index | binary | |
MD5:— | SHA256:— | |||
| 392 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF1B017F0845DAE3B8.TMP | gmc | |
MD5:— | SHA256:— | |||
| 392 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\{E024546C-6E64-11EC-A20C-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 392 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF66DB6A234570E3E3.TMP | gmc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
66
DNS requests
56
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
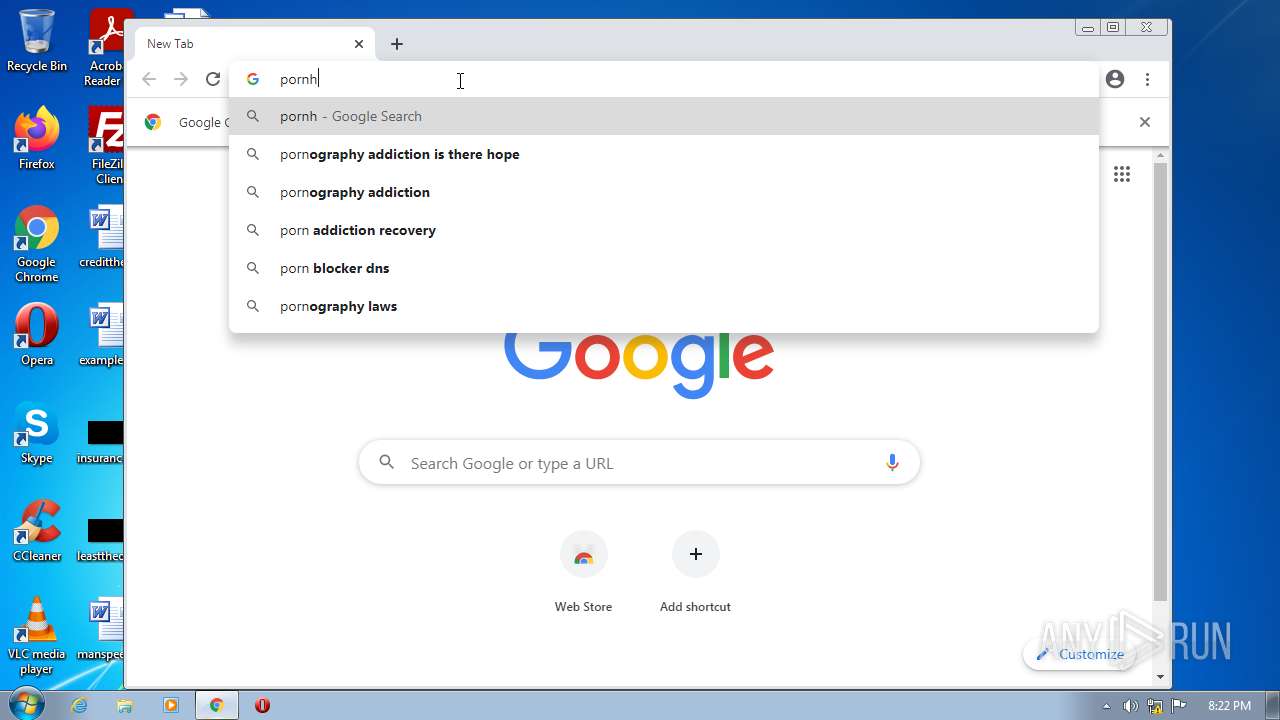
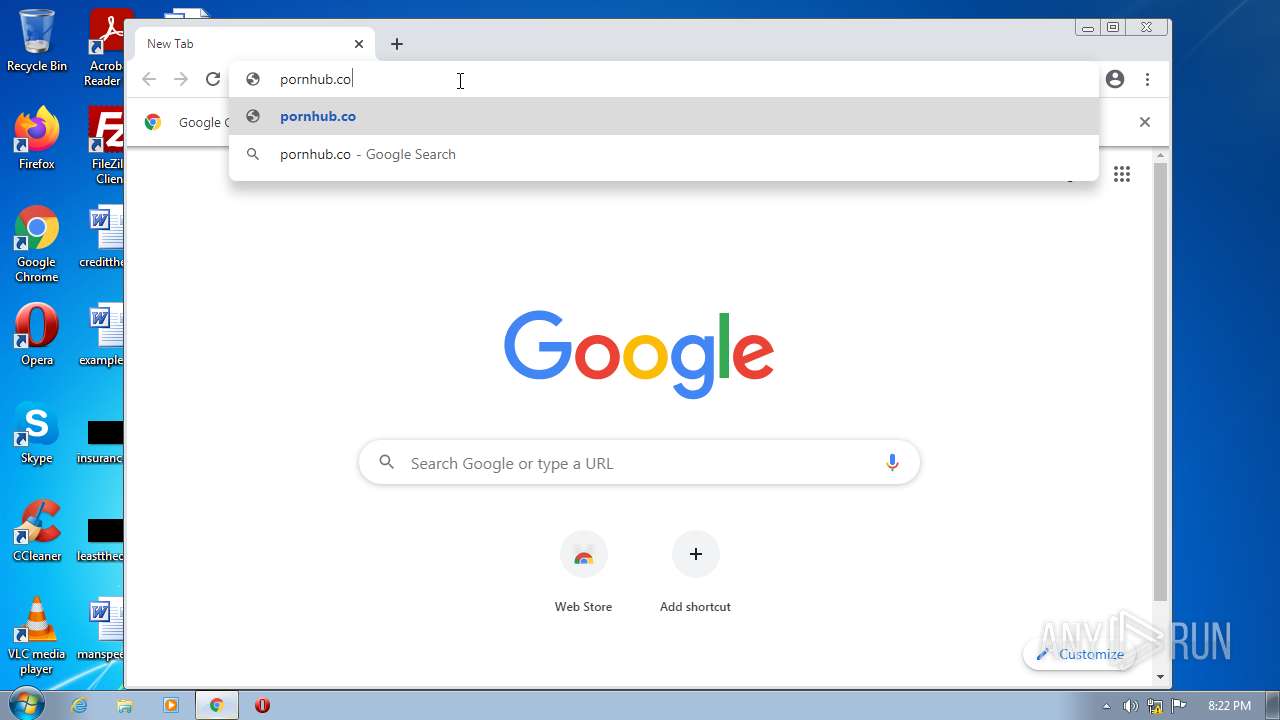
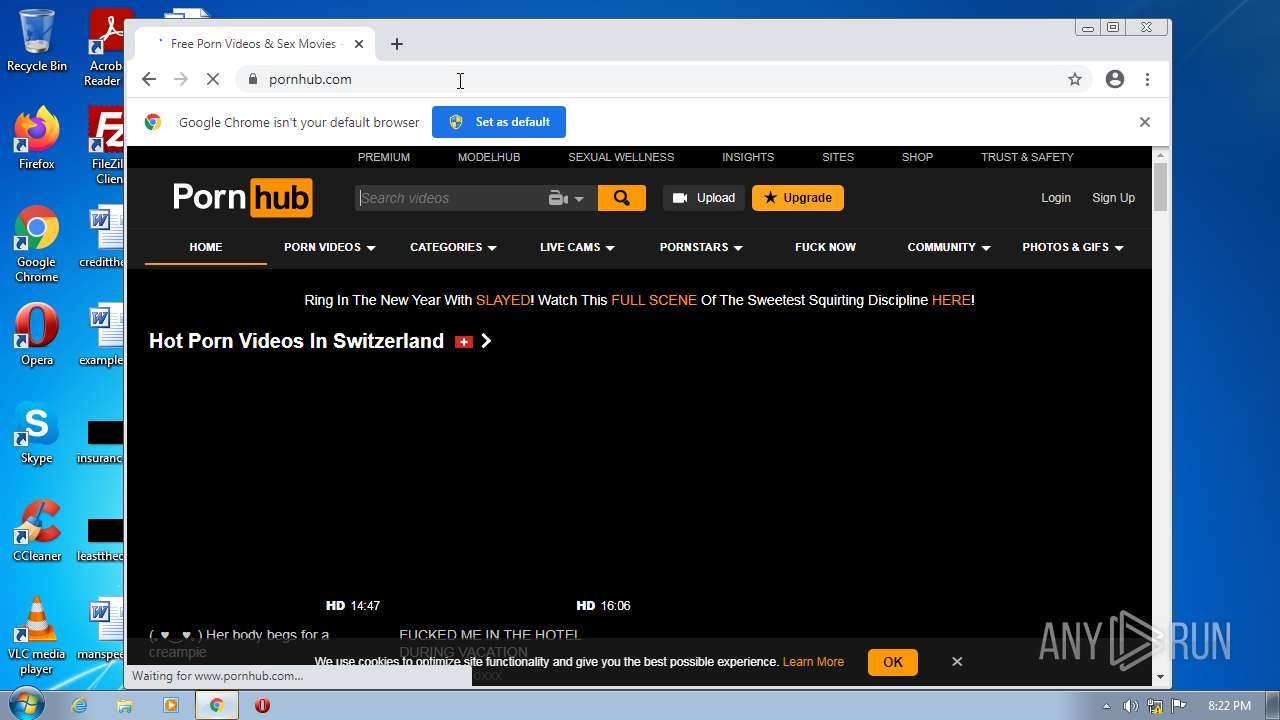
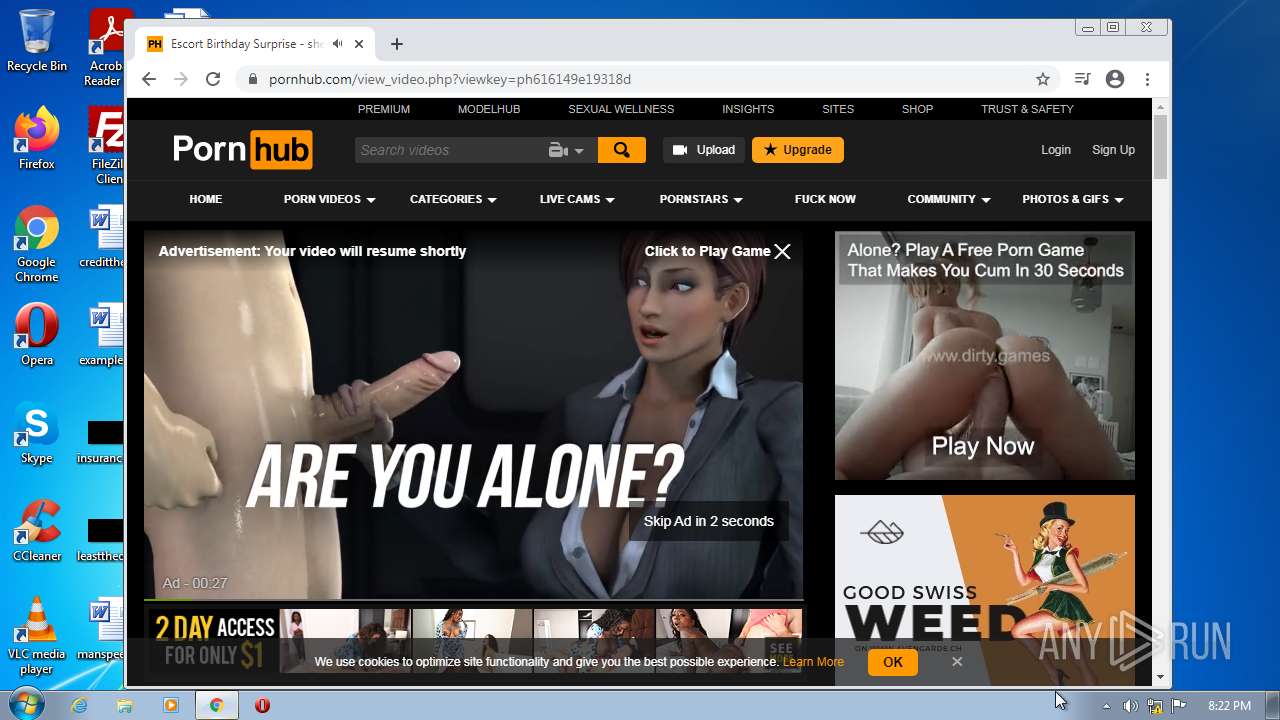
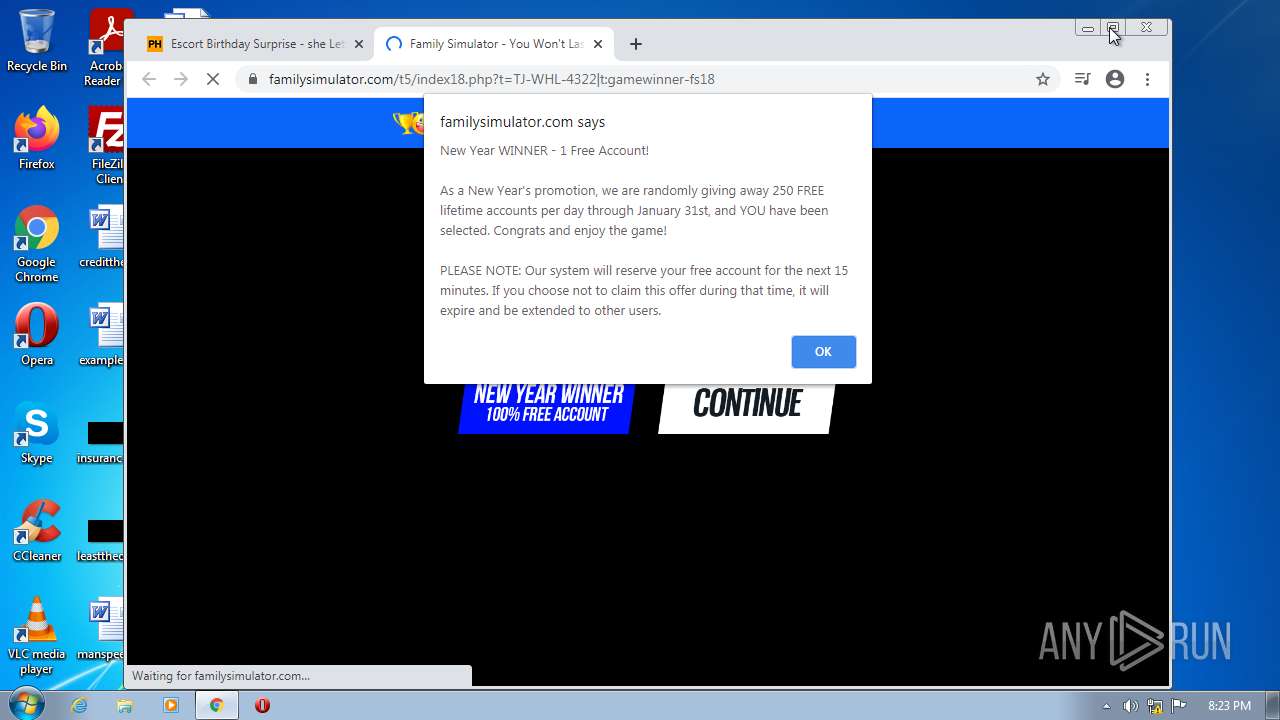
2916 | chrome.exe | GET | 301 | 66.254.114.41:80 | http://pornhub.com/ | US | — | — | whitelisted |
2916 | chrome.exe | GET | 302 | 142.250.186.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 554 b | whitelisted |
2916 | chrome.exe | GET | 200 | 74.125.108.201:80 | http://r4---sn-1gi7znek.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=e_&mip=85.203.45.7&mm=28&mn=sn-1gi7znek&ms=nvh&mt=1641413777&mv=m&mvi=4&pl=24&rmhost=r2---sn-1gi7znek.gvt1.com&shardbypass=yes | US | crx | 242 Kb | whitelisted |
2916 | chrome.exe | GET | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | text | 37 b | whitelisted |
2916 | chrome.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?fa6ffdf6c34f8b3e | US | compressed | 59.9 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2916 | chrome.exe | 216.58.212.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
2916 | chrome.exe | 142.250.185.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2916 | chrome.exe | 142.250.186.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2916 | chrome.exe | 66.254.114.41:80 | pornhub.com | Reflected Networks, Inc. | US | malicious |
2916 | chrome.exe | 142.250.185.78:443 | apis.google.com | Google Inc. | US | whitelisted |
2916 | chrome.exe | 142.250.186.110:443 | encrypted-tbn0.gstatic.com | Google Inc. | US | whitelisted |
2916 | chrome.exe | 66.254.114.41:443 | pornhub.com | Reflected Networks, Inc. | US | malicious |
2916 | chrome.exe | 205.185.208.79:443 | static.trafficjunky.com | Highwinds Network Group, Inc. | US | unknown |
2916 | chrome.exe | 205.185.208.142:443 | di.phncdn.com | Highwinds Network Group, Inc. | US | suspicious |
2916 | chrome.exe | 8.247.219.125:443 | ai.phncdn.com | Level 3 Communications, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
encrypted-tbn0.gstatic.com |
| whitelisted |
pornhub.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2916 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |