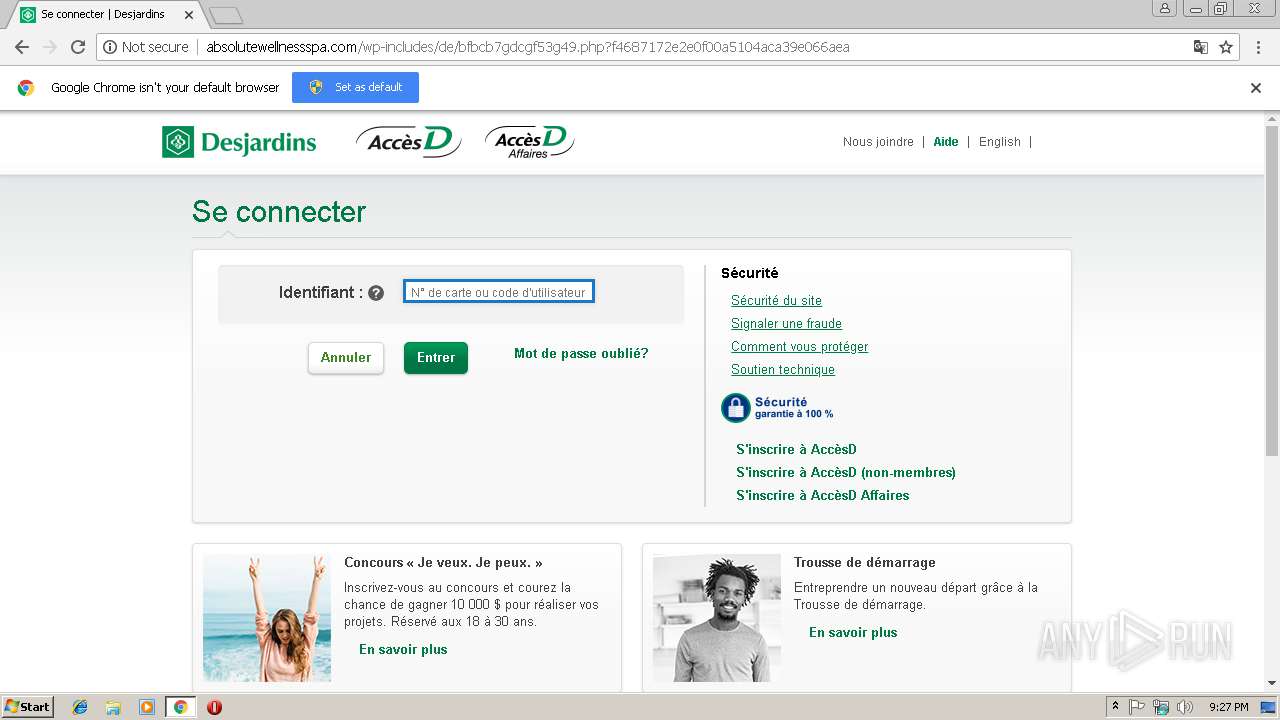
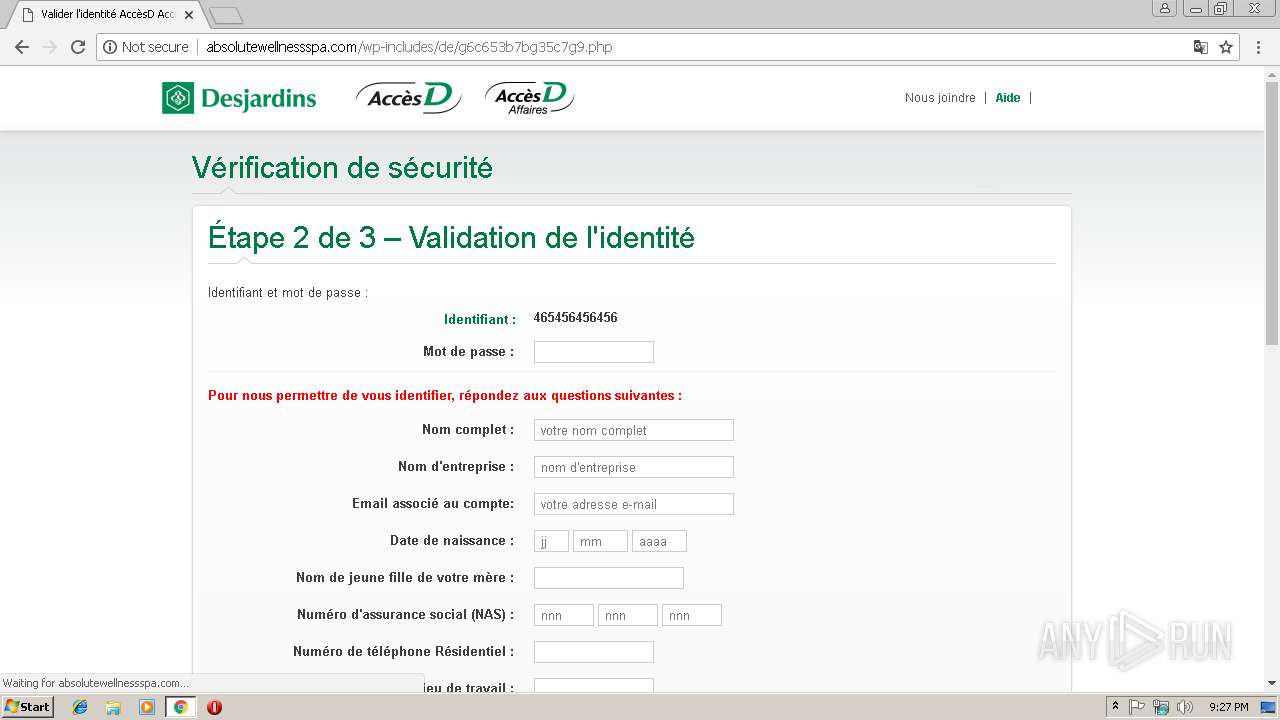
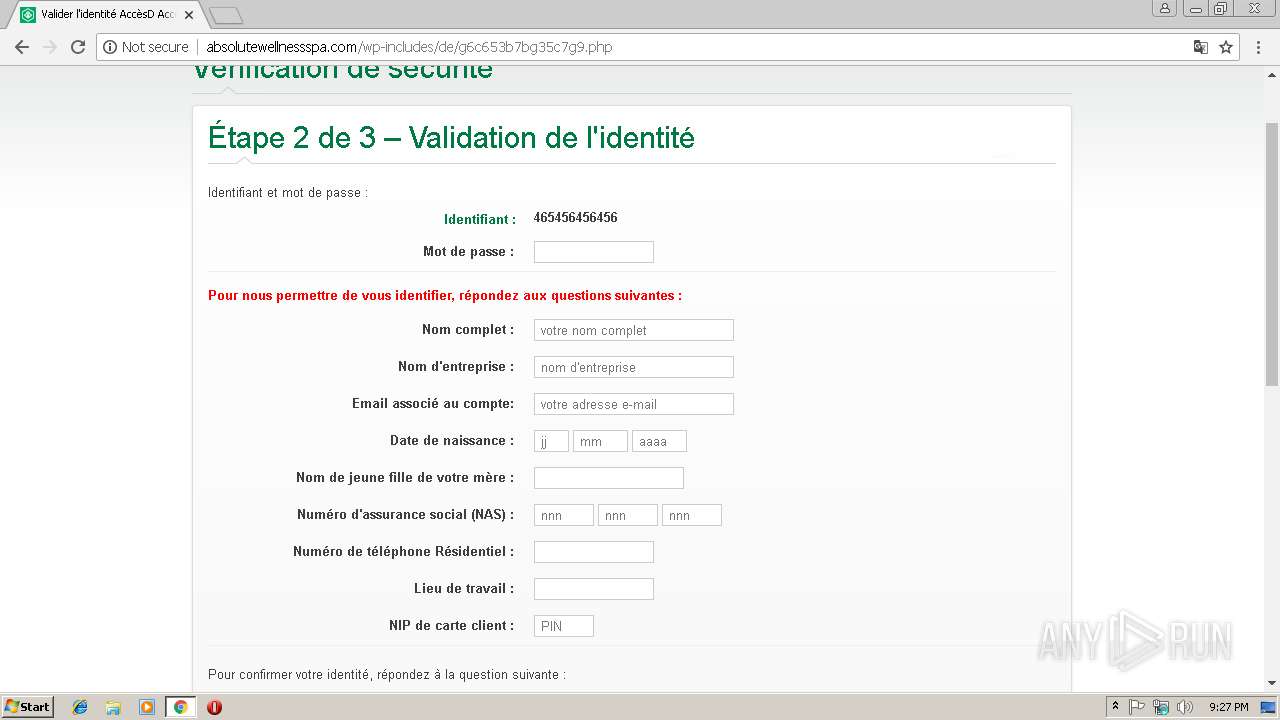
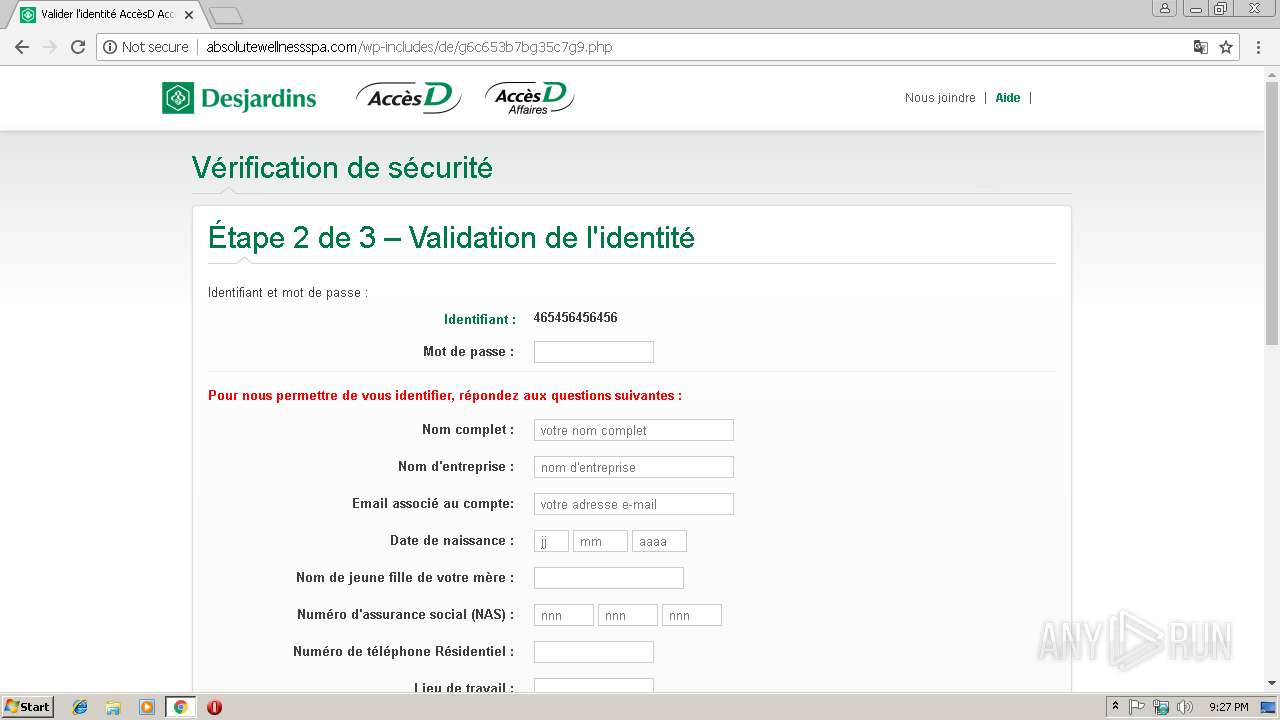
| URL: | http://2myevent.com/2myevent/segovia/IopElz21Anz/open.html |
| Full analysis: | https://app.any.run/tasks/dd70e525-6dd5-4db2-9b34-3ea3b5a8c161 |
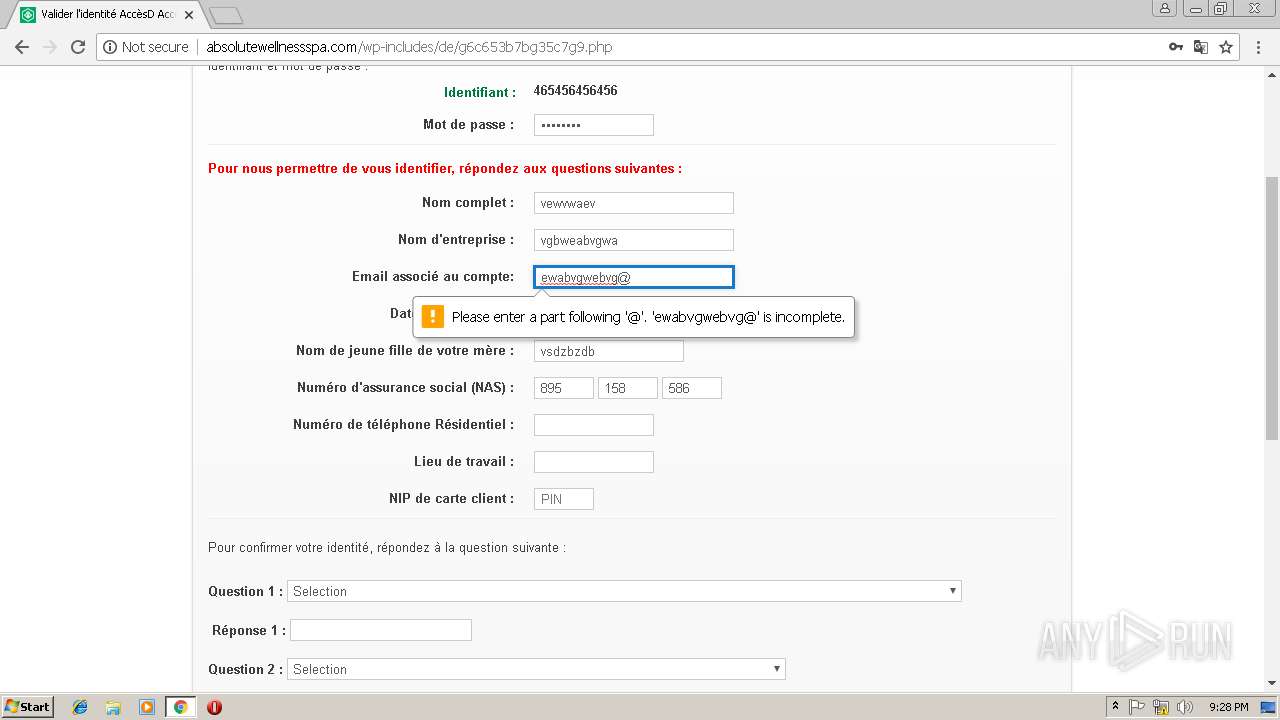
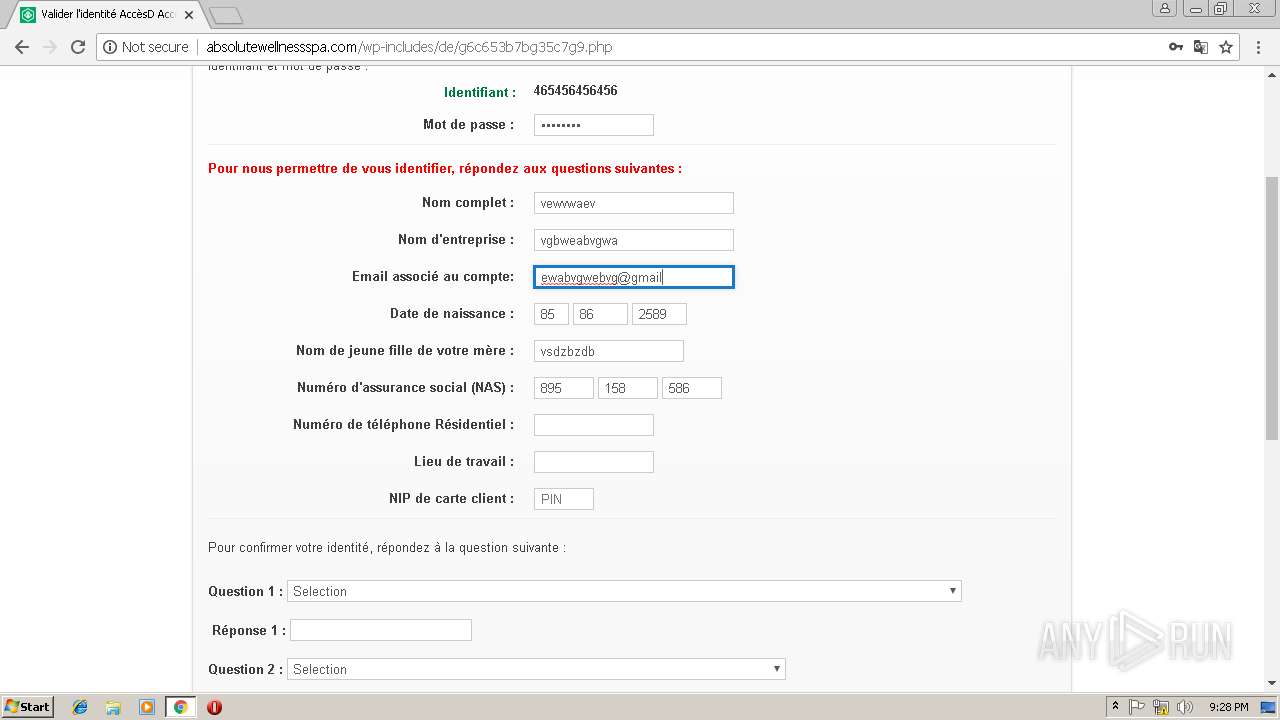
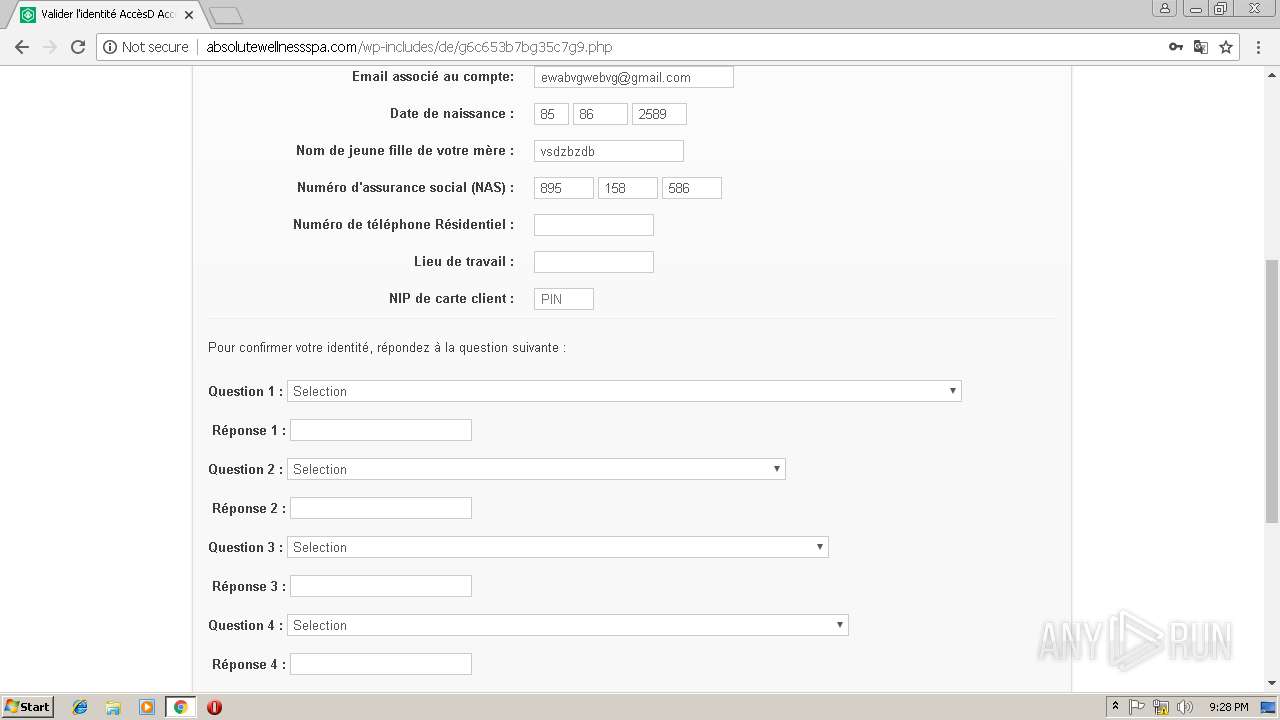
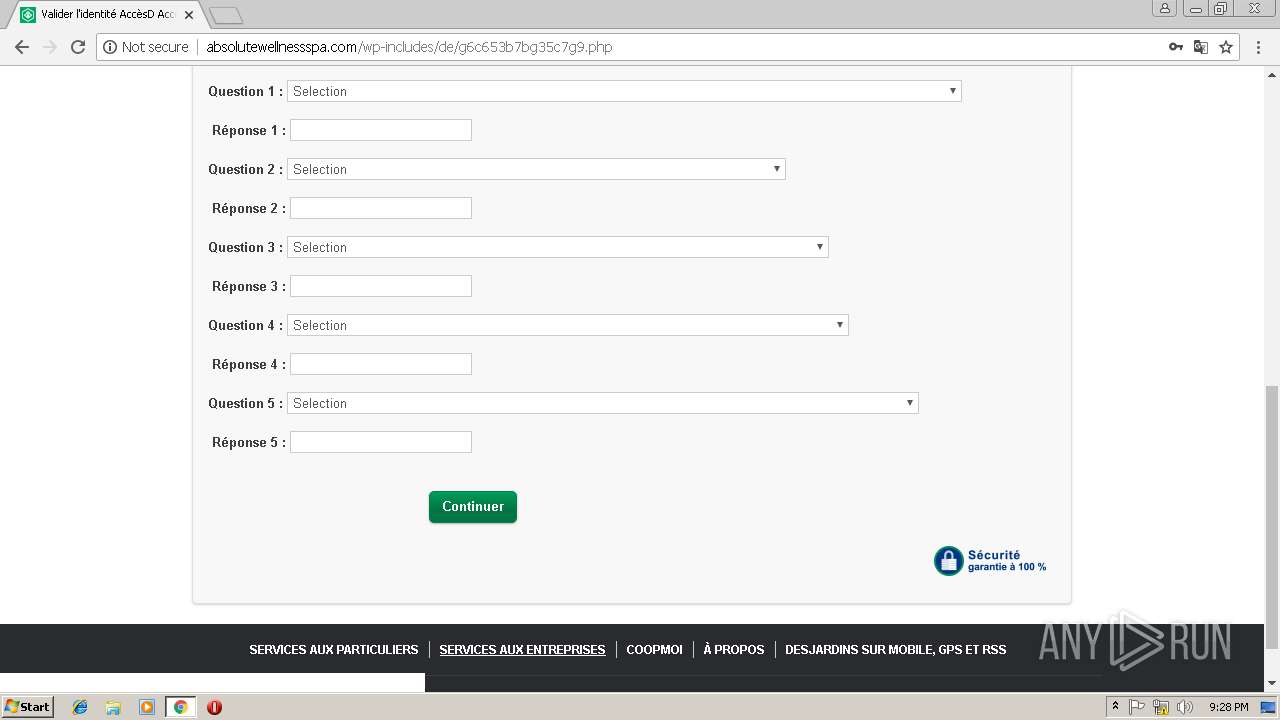
| Verdict: | Malicious activity |
| Analysis date: | February 18, 2019, 21:26:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 6617C068F40128FCD15A44A11B2DD089 |
| SHA1: | 952C09FBED2004B1F6A072A385D30B4858E432BB |
| SHA256: | D25A5C971793D73FA91C2B2C7EA8266CA560FF16F21ED9832E6B63E5CDD2A040 |
| SSDEEP: | 3:N1KIgKIMUAzKdpUkLiv/Qn:CnKUkKokLoQn |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 3492)
Reads settings of System Certificates
- chrome.exe (PID: 3492)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
38
Monitored processes
9
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6f6000b0,0x6f6000c0,0x6f6000cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=972,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=78792D34EF95173D8C123789476ED93D --mojo-platform-channel-handle=516 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=972,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=33FF2C0AC3CCF2B4F5A9F9DE1C426F58 --mojo-platform-channel-handle=992 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3220 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=972,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --service-pipe-token=587870EDE714DF2DF9DDF8B0C0206D68 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=587870EDE714DF2DF9DDF8B0C0206D68 --renderer-client-id=4 --mojo-platform-channel-handle=1900 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3496 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://2myevent.com/2myevent/segovia/IopElz21Anz/open.html | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3704 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=972,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=4EB112A7A8FED0249B6CC2950E5B67A8 --mojo-platform-channel-handle=2344 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=972,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=25046AF729A2DD3273DE0D6A6E19FAD0 --mojo-platform-channel-handle=3500 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3816 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=972,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --service-pipe-token=383A650325B0EAAD8BBC7BF9E5C4522C --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=383A650325B0EAAD8BBC7BF9E5C4522C --renderer-client-id=3 --mojo-platform-channel-handle=2064 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
519
Read events
471
Write events
45
Delete events
3
Modification events
| (PID) Process: | (3440) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3492-13194998818227250 |
Value: 259 | |||
| (PID) Process: | (3492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3492) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3492-13194998818227250 |
Value: 259 | |||
| (PID) Process: | (3492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
0
Suspicious files
17
Text files
77
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\6b01bbe3-bb4f-42c5-b8c7-1875e44c0003.tmp | — | |
MD5:— | SHA256:— | |||
| 3492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 3492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT~RF1992a1.TMP | — | |
MD5:— | SHA256:— | |||
| 3492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\00f16534-2c4e-4eef-9852-0fb60c94b805.tmp | — | |
MD5:— | SHA256:— | |||
| 3492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF199243.TMP | text | |
MD5:— | SHA256:— | |||
| 3492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
62
TCP/UDP connections
38
DNS requests
14
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
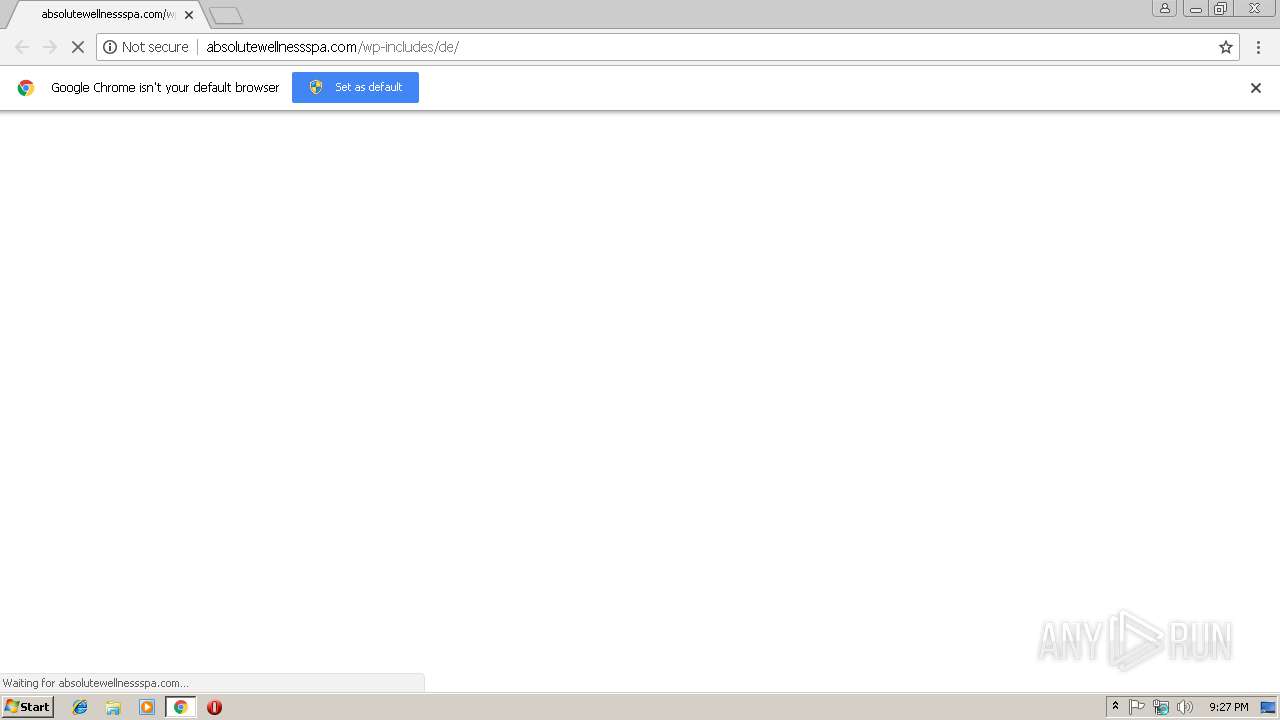
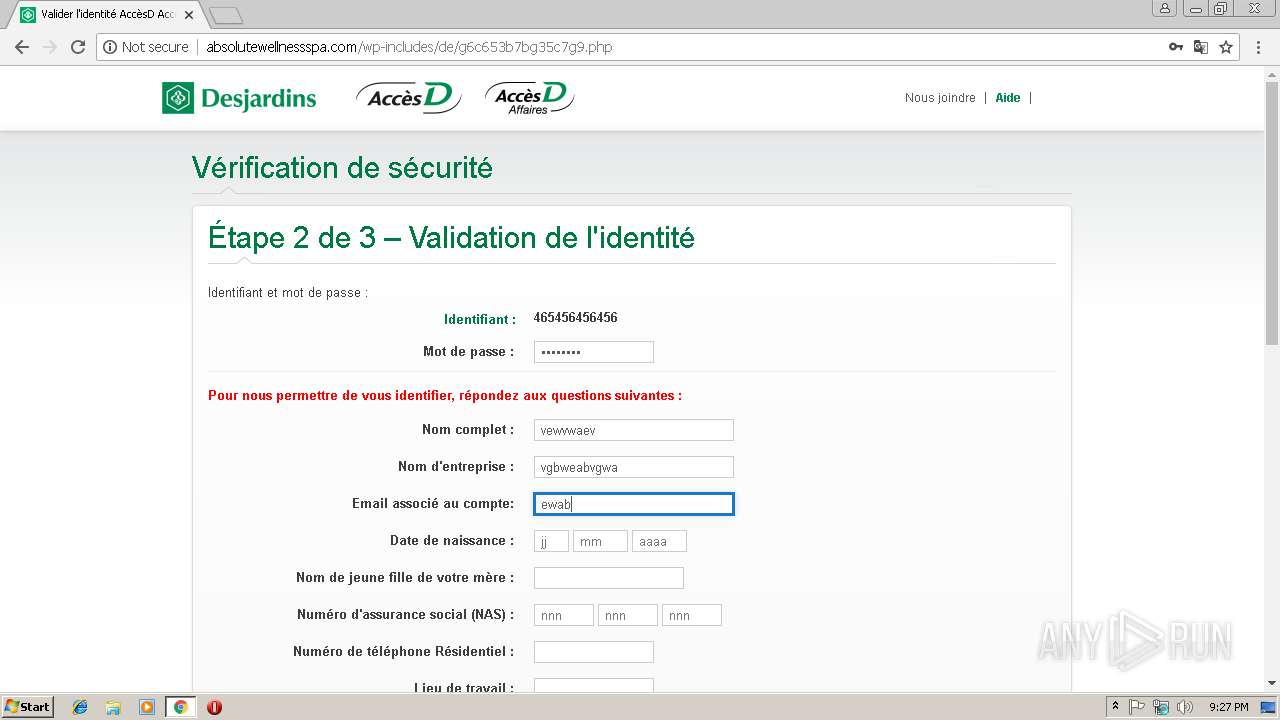
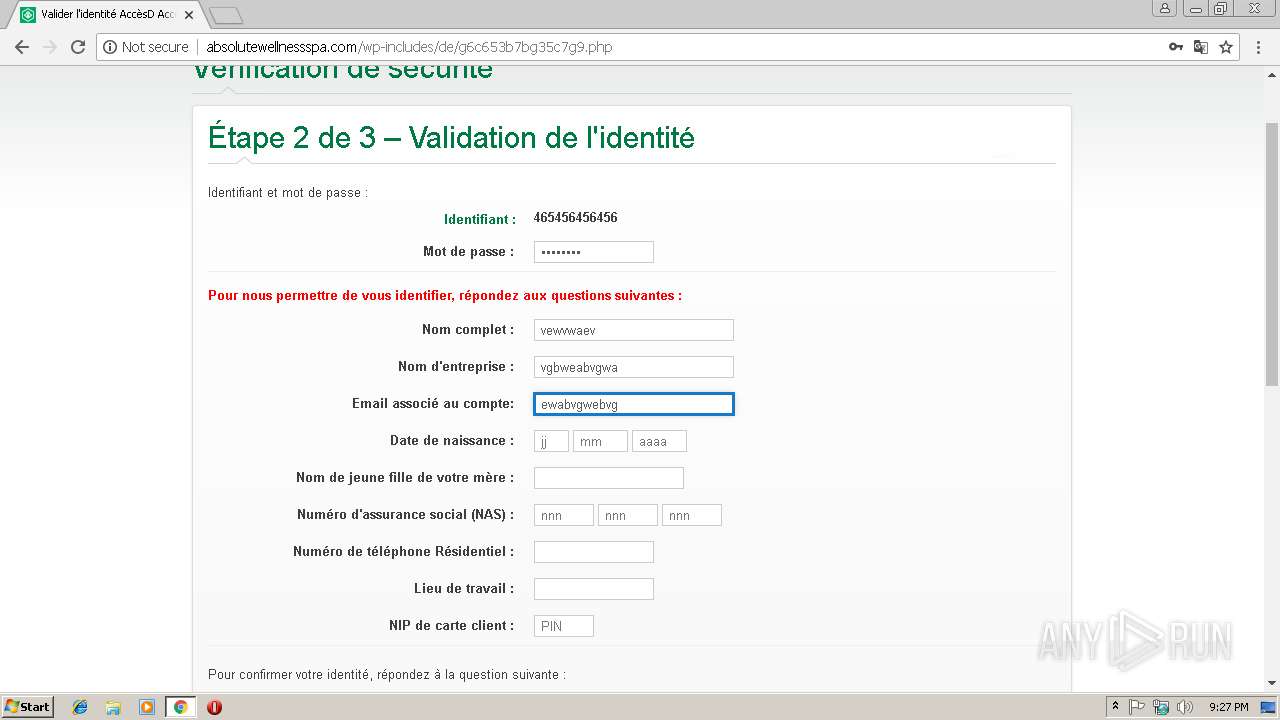
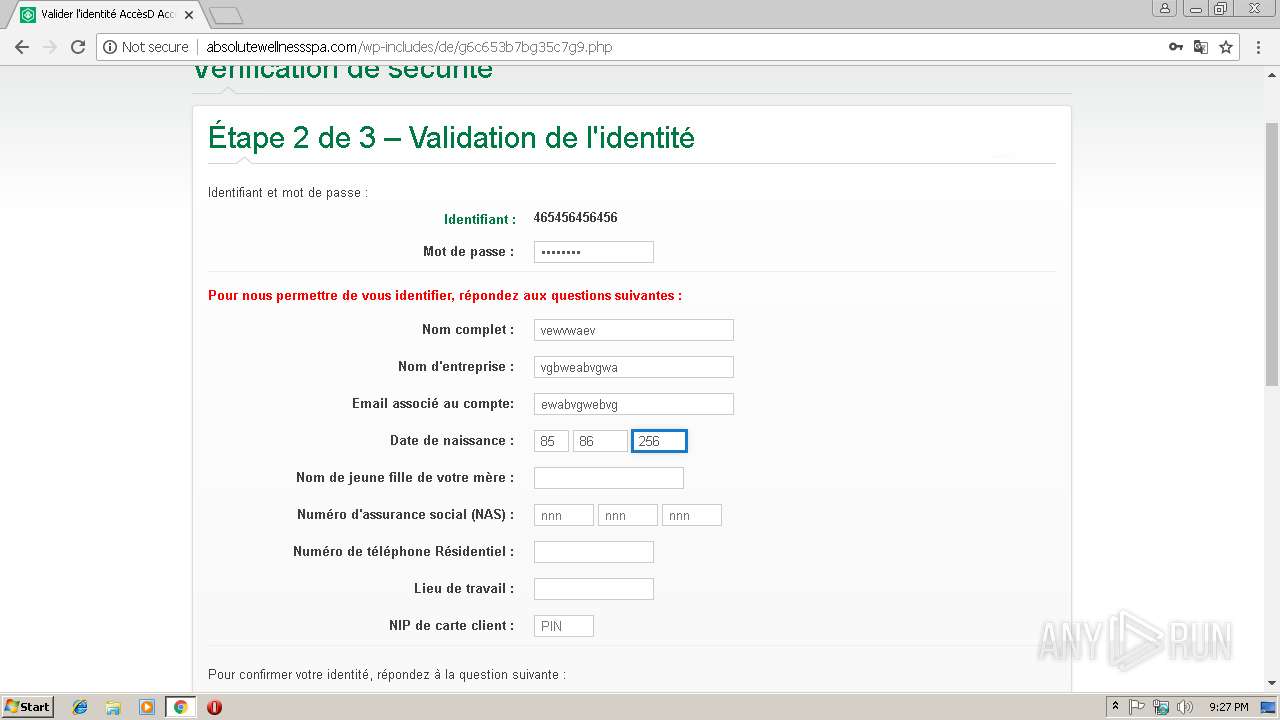
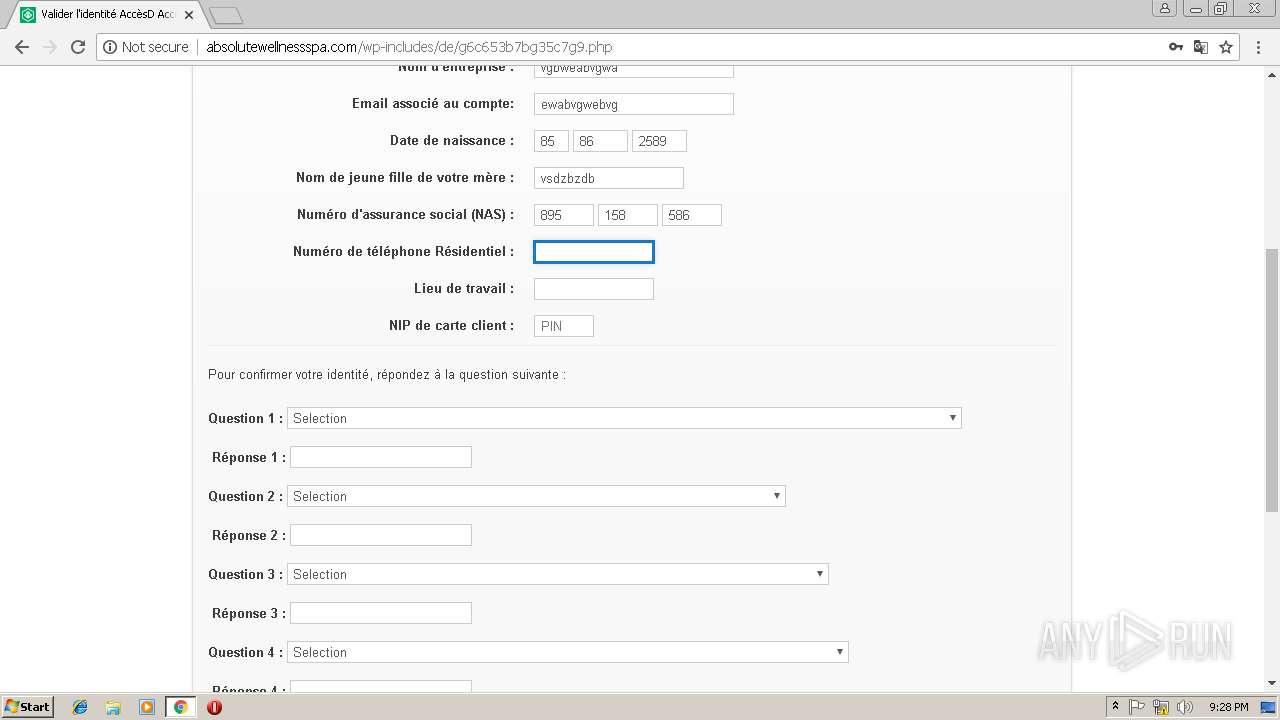
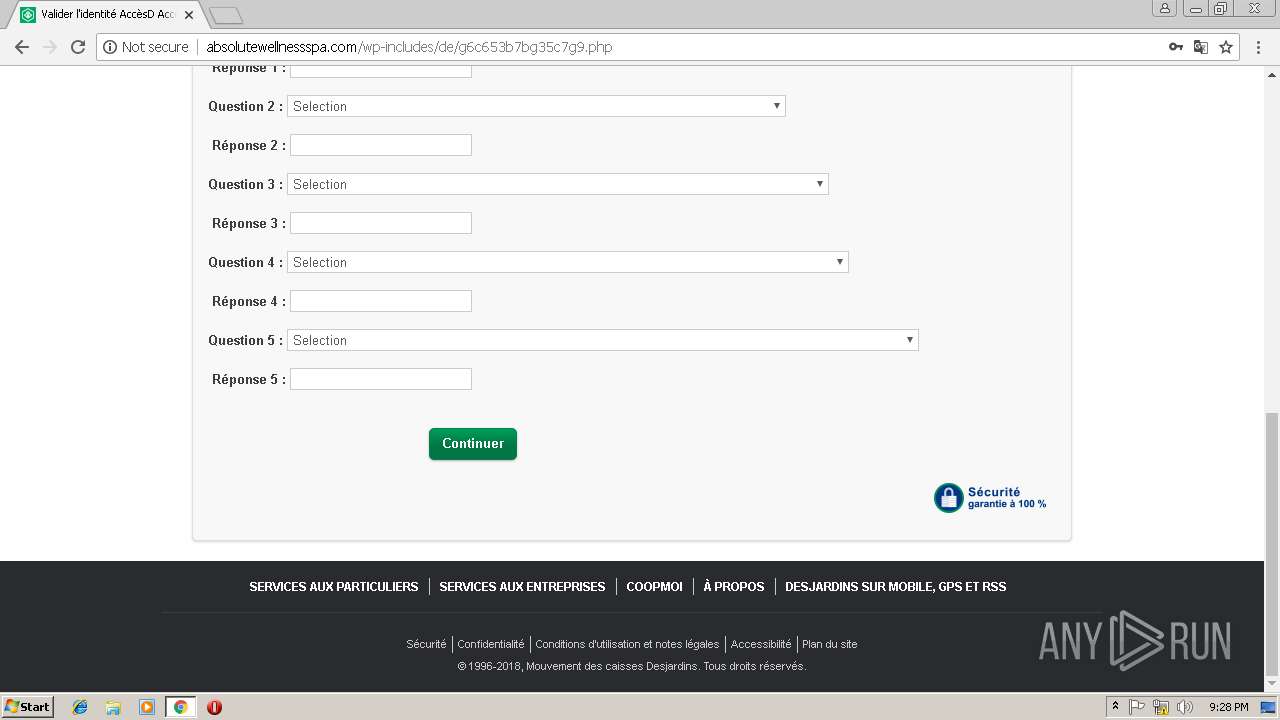
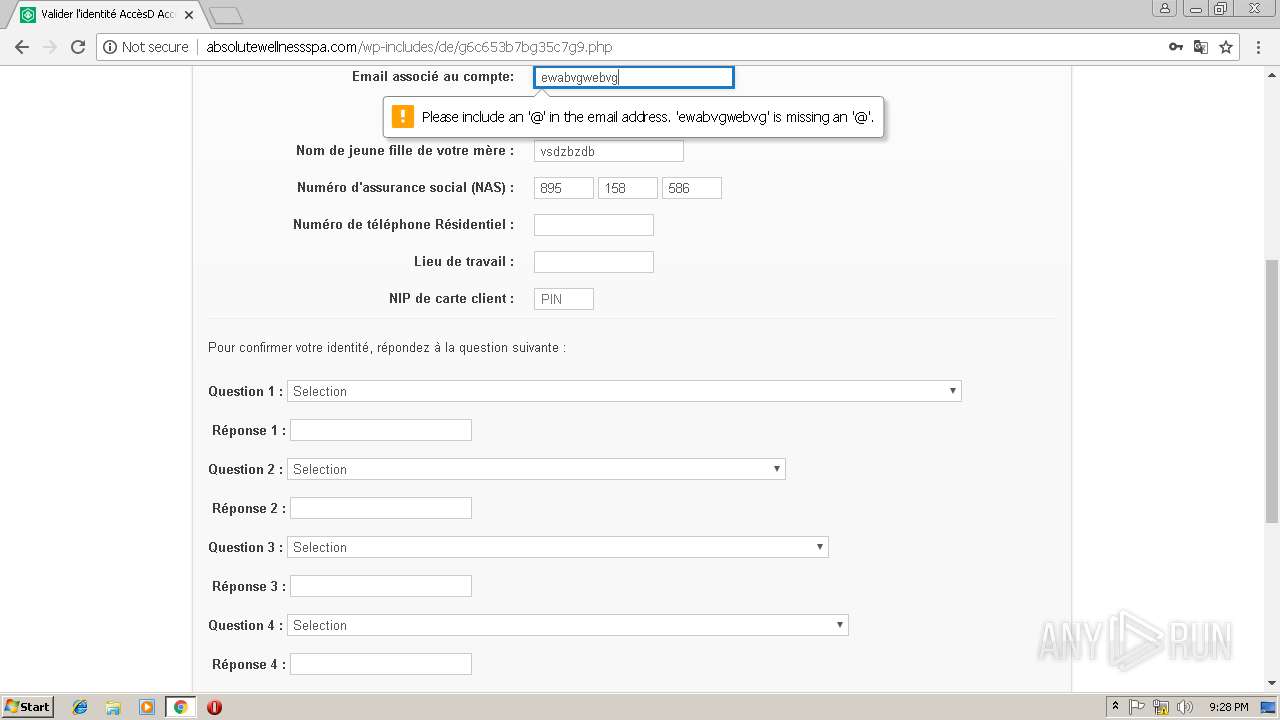
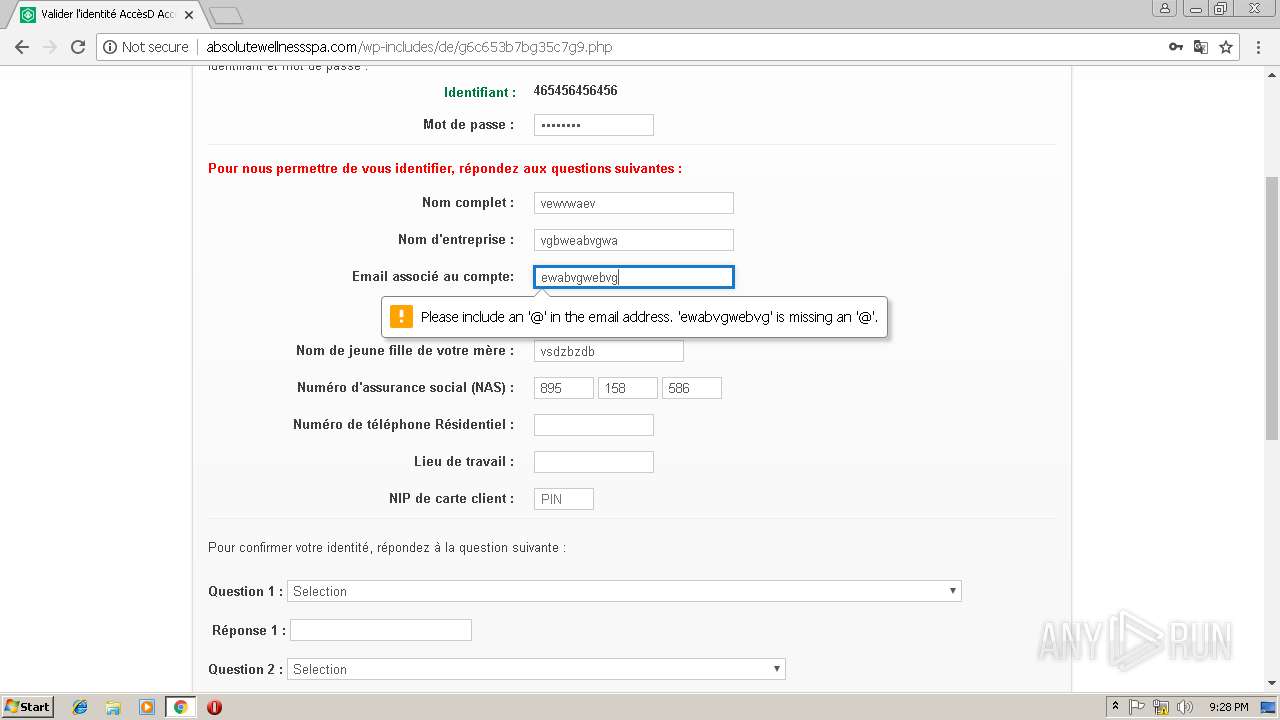
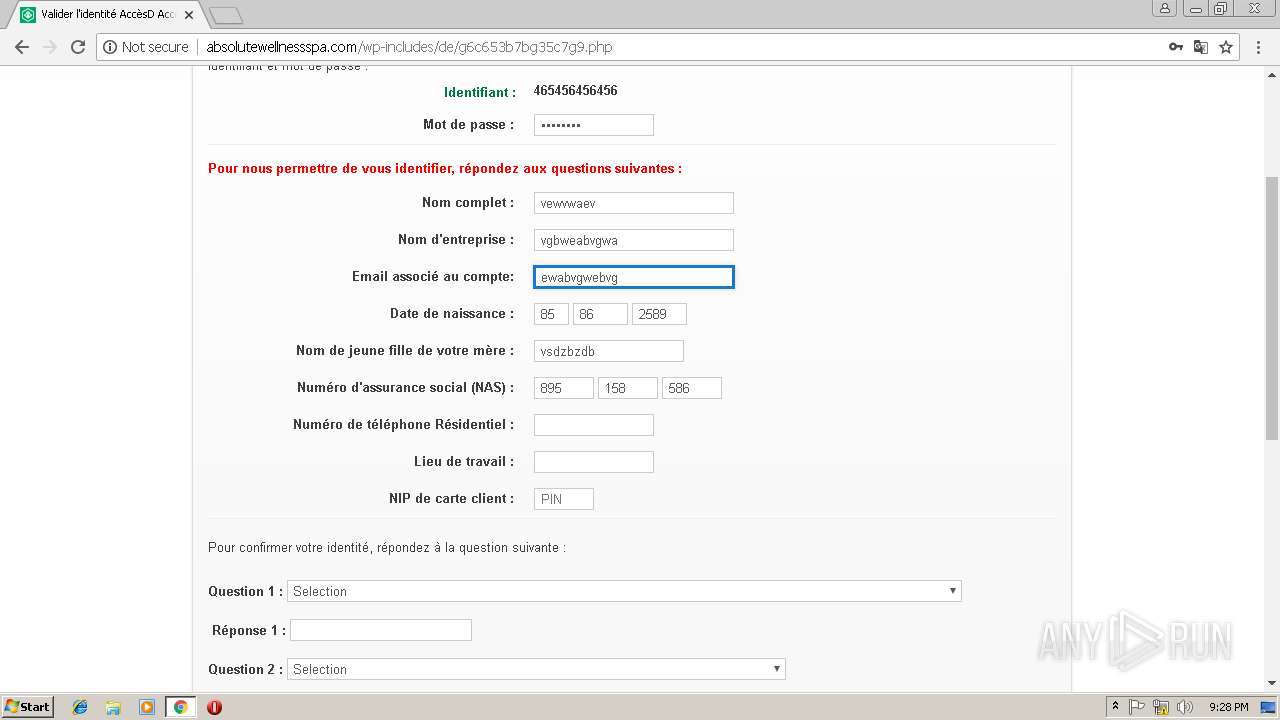
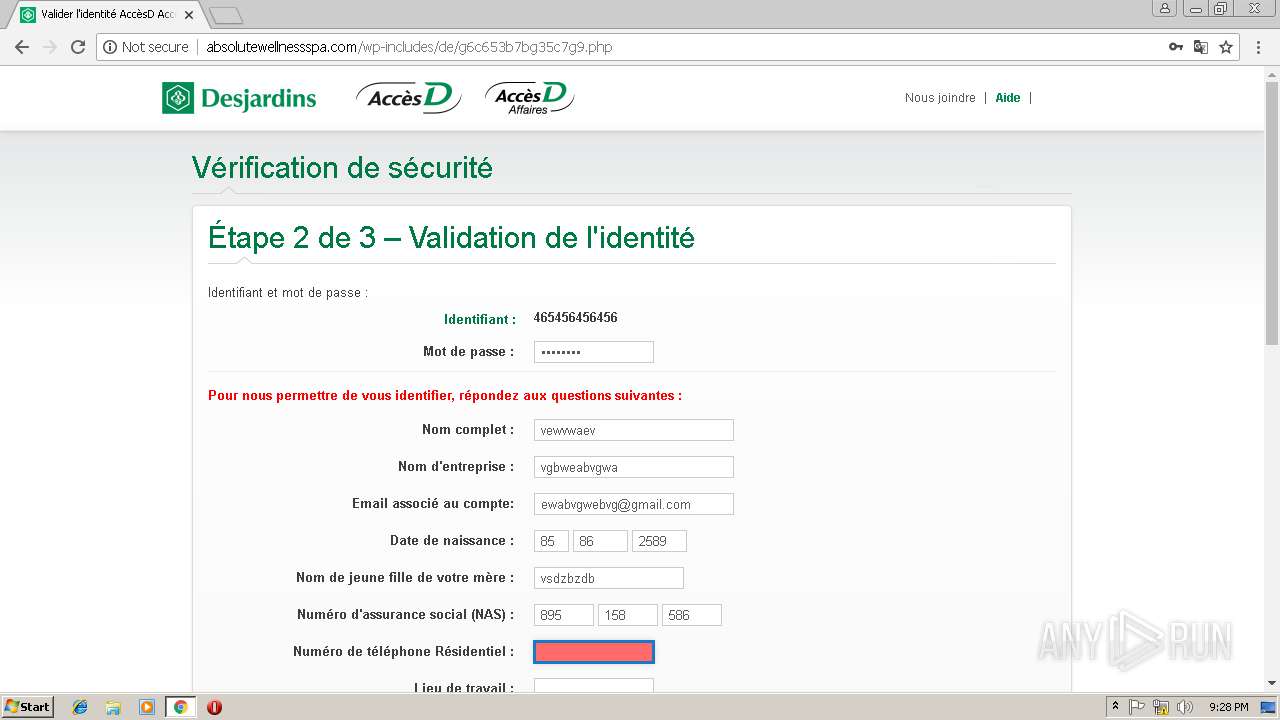
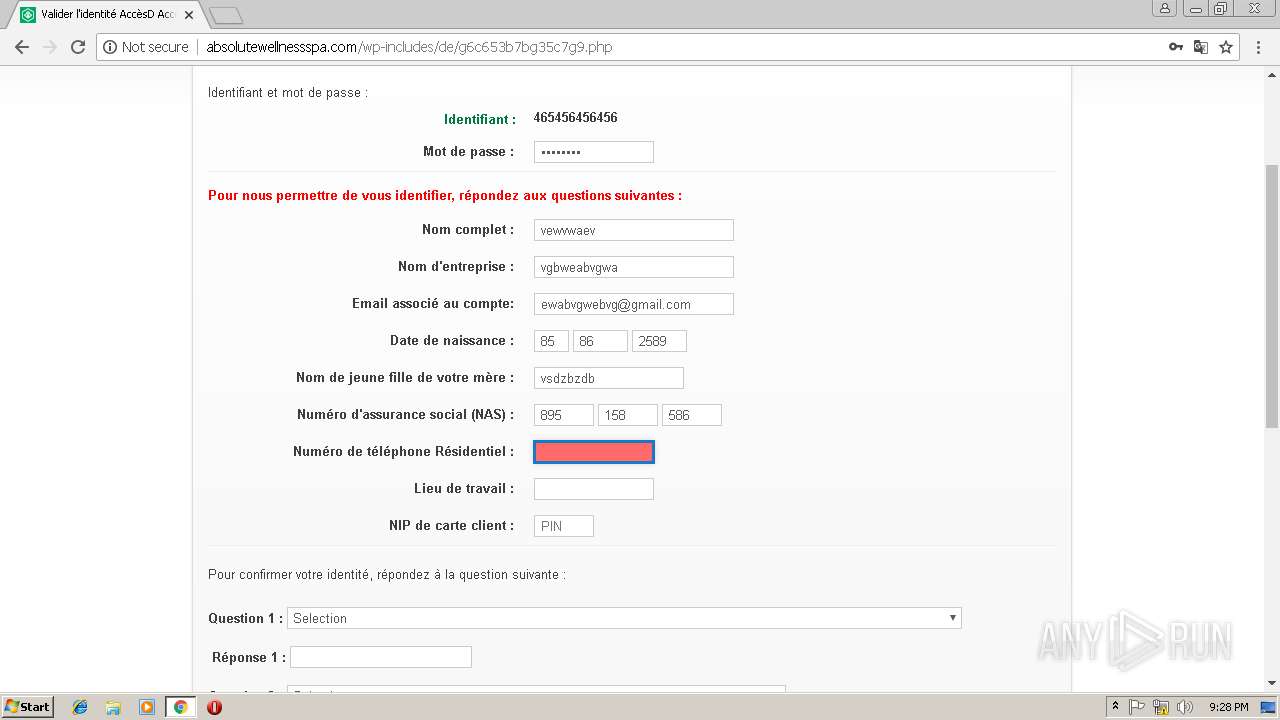
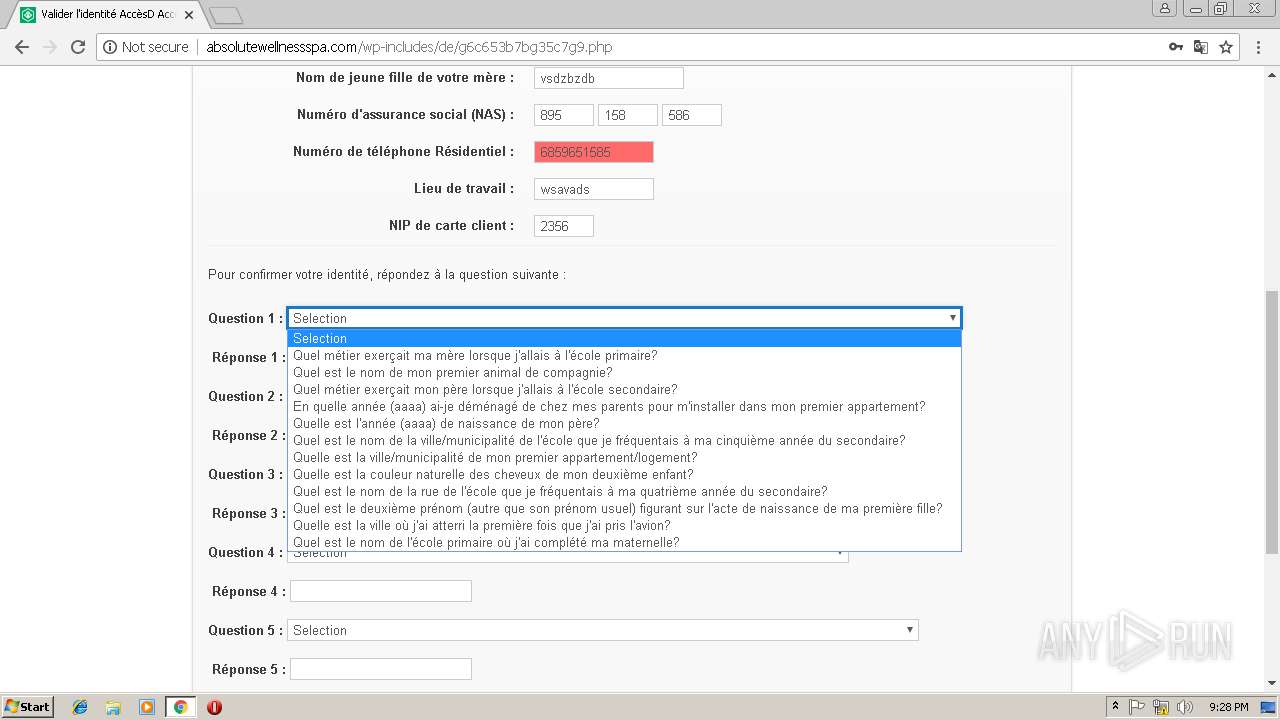
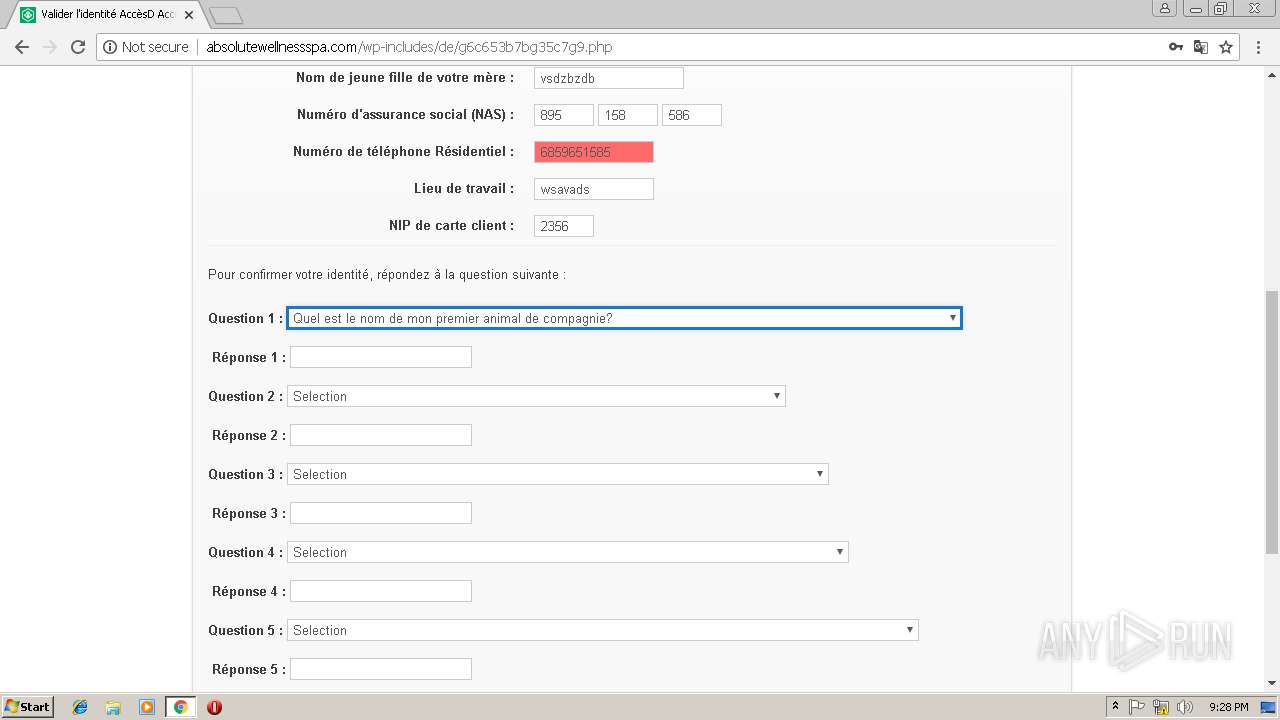
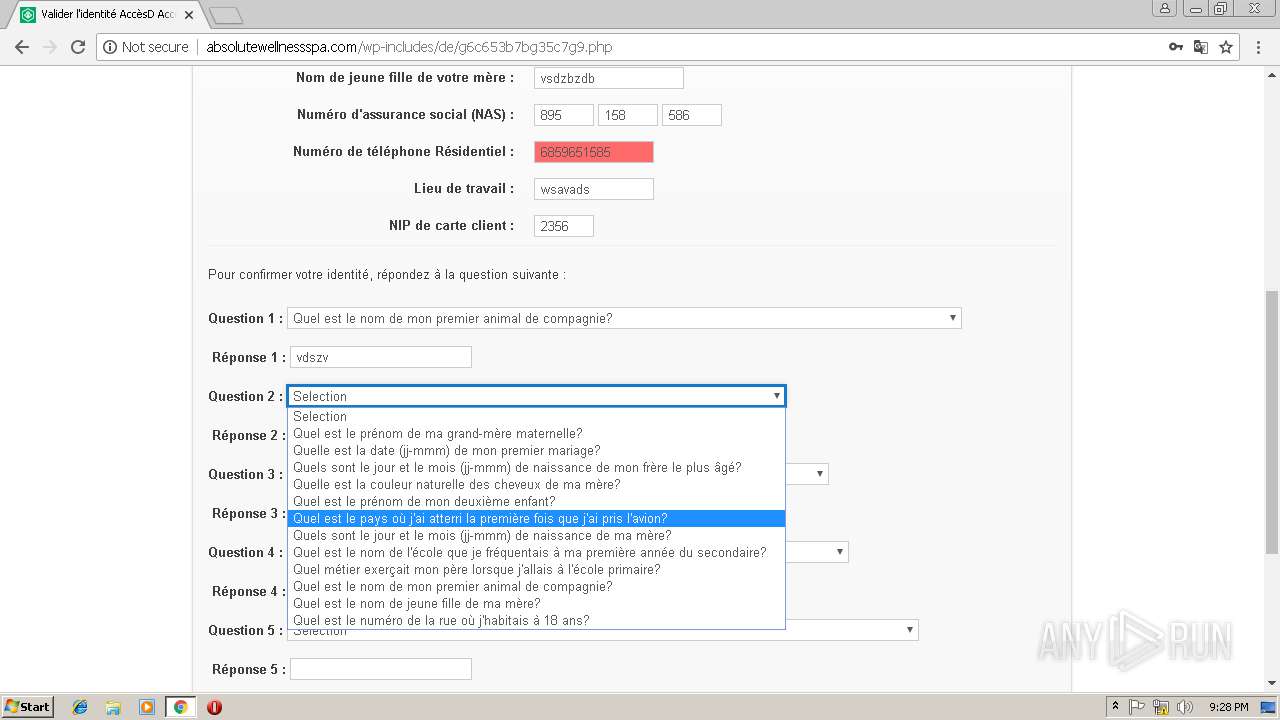
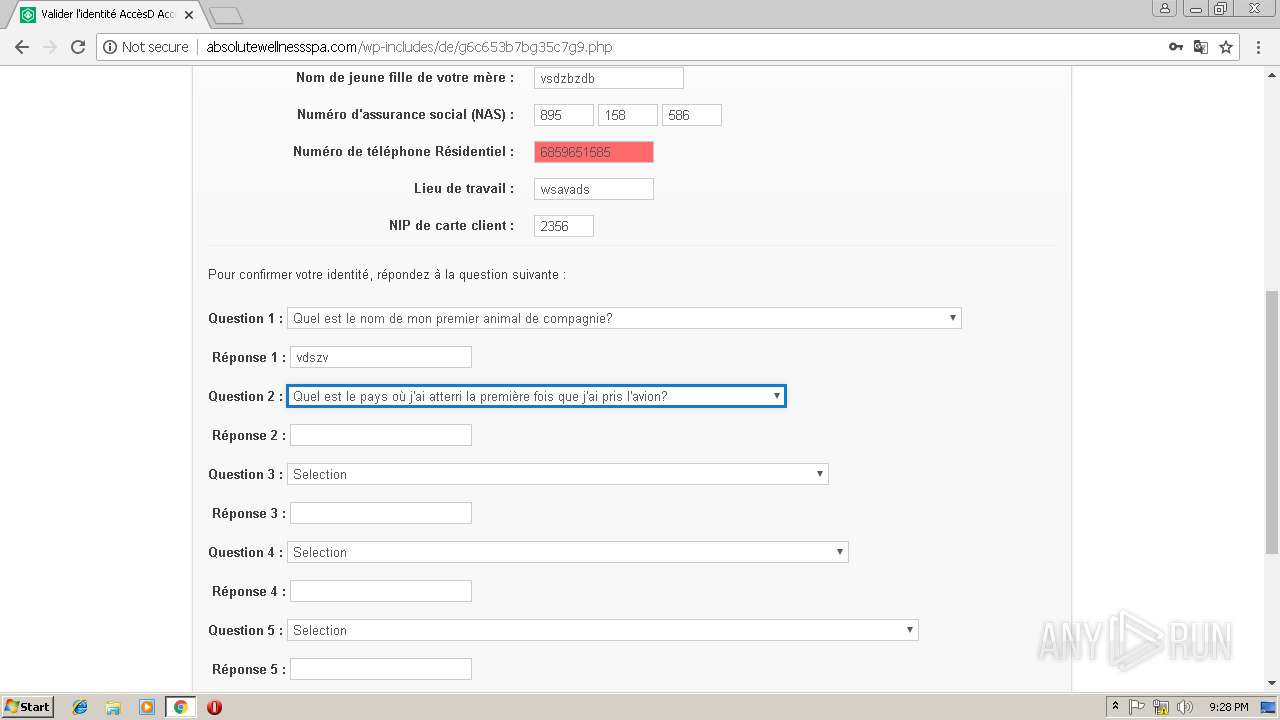
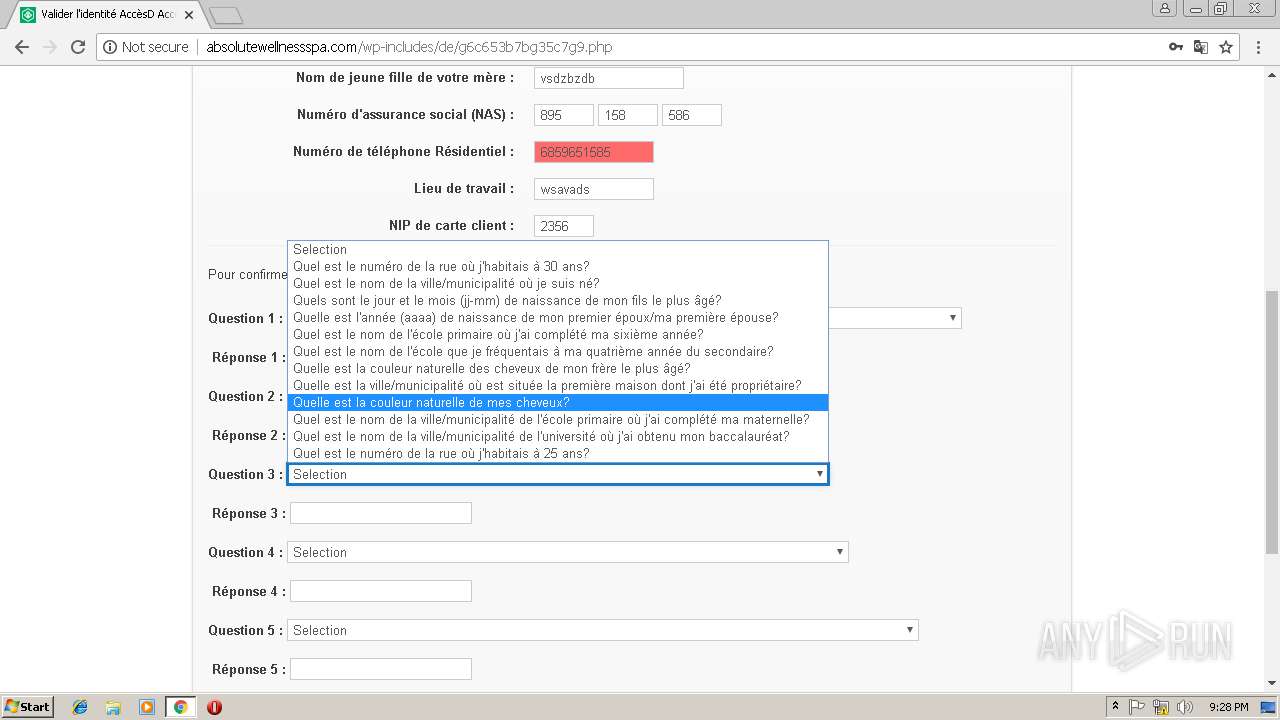
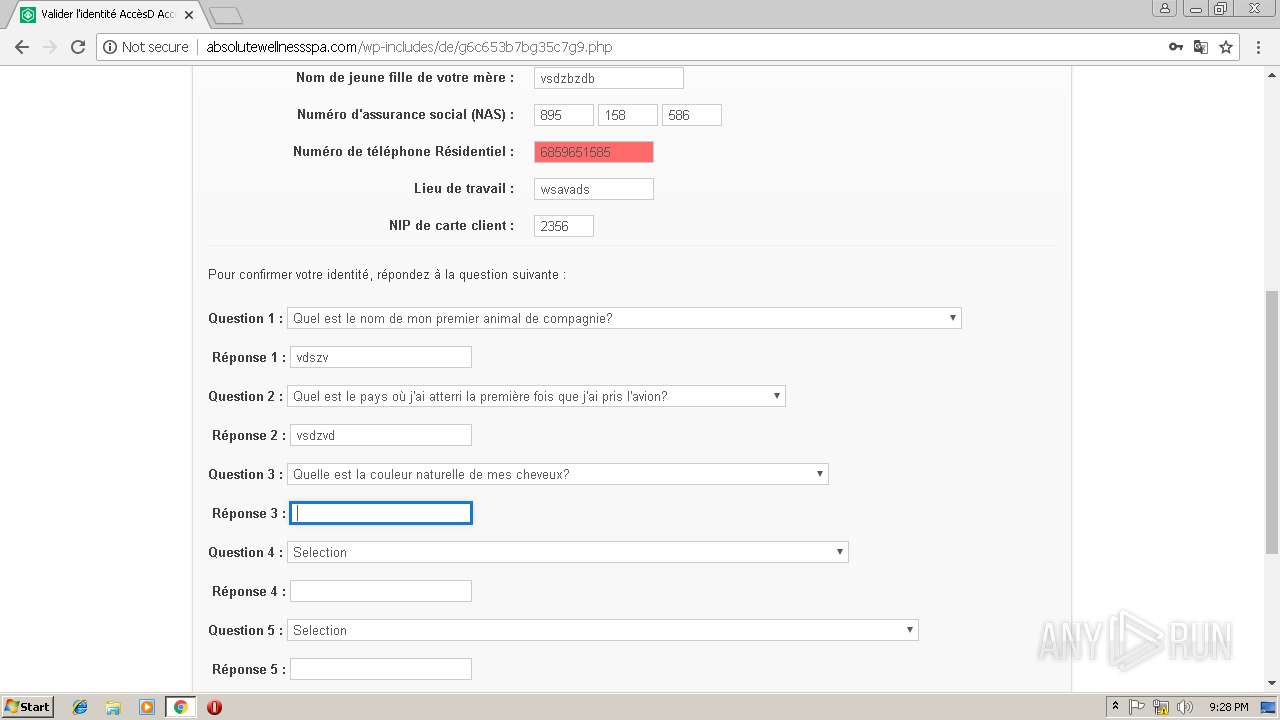
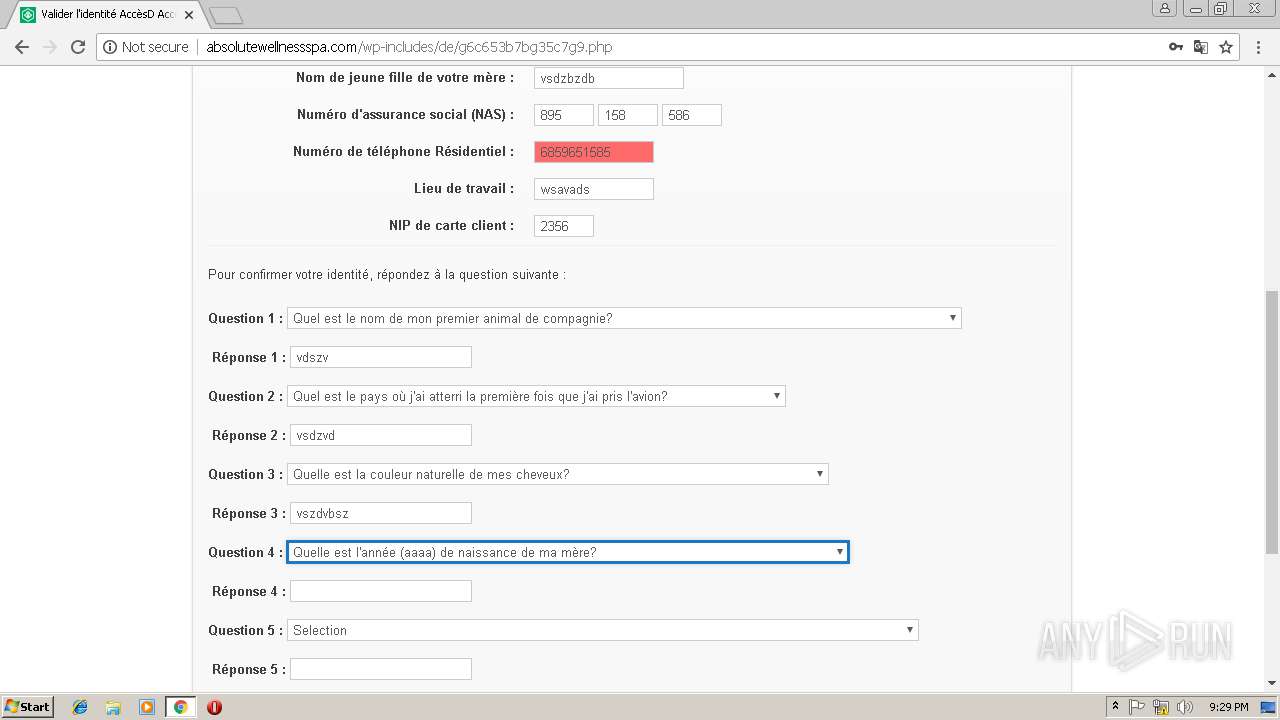
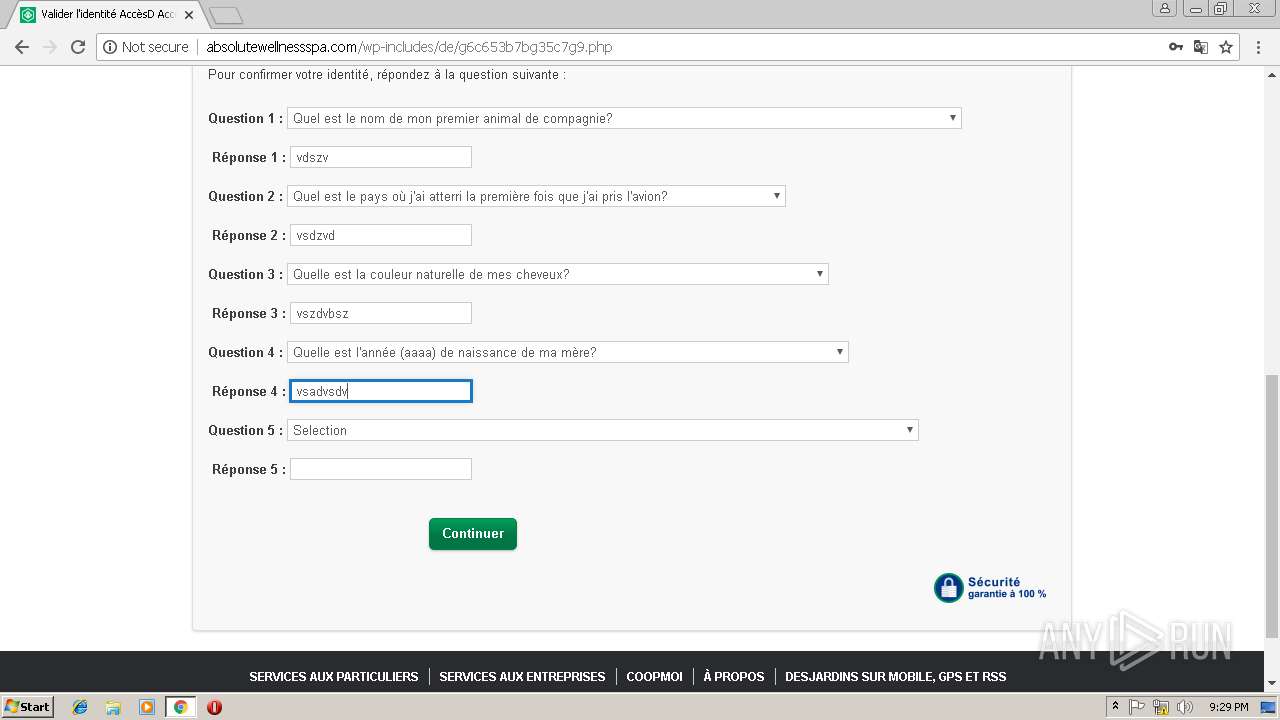
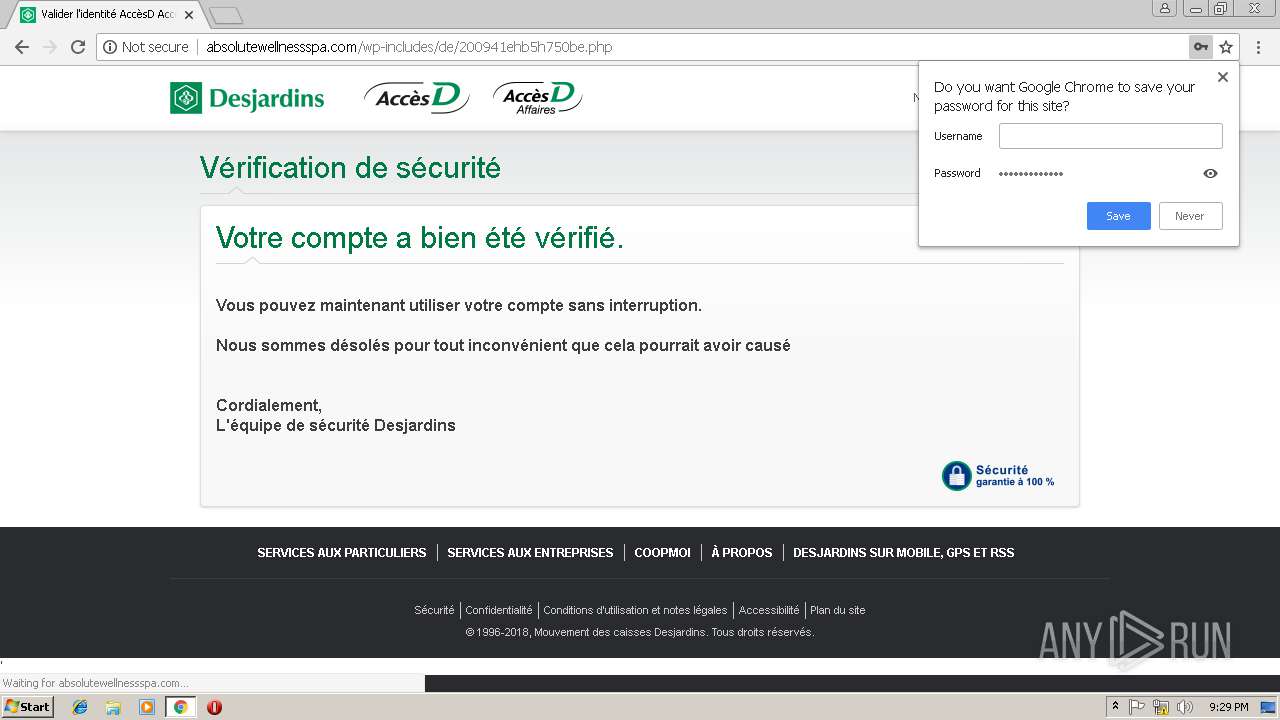
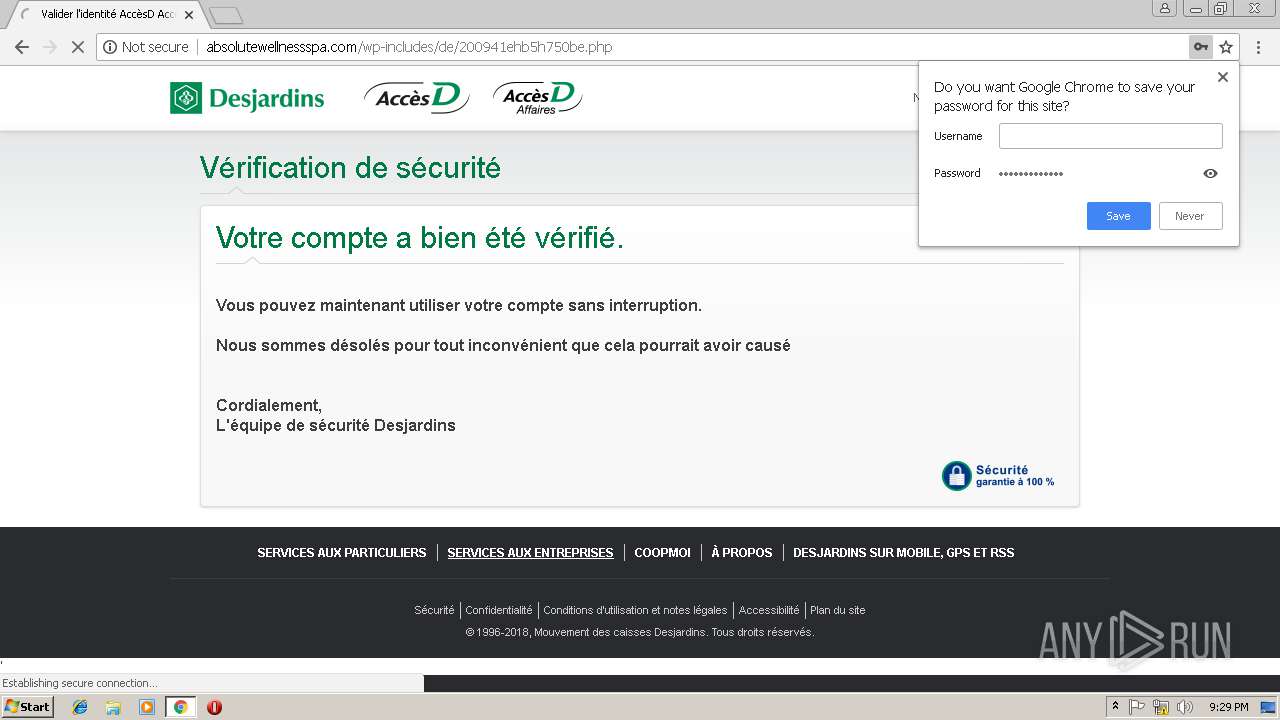
3492 | chrome.exe | GET | 200 | 45.40.180.129:80 | http://absolutewellnessspa.com/wp-includes/de/1b8d36hb3f2ggf85/fhg1242g2896chfg.css | US | — | — | malicious |
3492 | chrome.exe | GET | 200 | 45.40.180.129:80 | http://absolutewellnessspa.com/wp-includes/de/ | US | html | 271 b | malicious |
3492 | chrome.exe | GET | 200 | 45.40.180.129:80 | http://absolutewellnessspa.com/wp-includes/de/1b8d36hb3f2ggf85/4gccdb0062f134c5.css | US | text | 1.59 Kb | malicious |
3492 | chrome.exe | GET | 200 | 45.40.180.129:80 | http://absolutewellnessspa.com/wp-includes/de/1b8d36hb3f2ggf85/c8569g765981bb7b.js | US | text | 52.9 Kb | malicious |
3492 | chrome.exe | GET | 200 | 45.40.180.129:80 | http://absolutewellnessspa.com/wp-includes/de/1b8d36hb3f2ggf85/63cc9df4hefe82e4.js | US | text | 943 b | malicious |
3492 | chrome.exe | GET | 200 | 45.40.180.129:80 | http://absolutewellnessspa.com/wp-includes/de/1b8d36hb3f2ggf85/b3894d6fc50fb317.css | US | text | 1.52 Kb | malicious |
3492 | chrome.exe | GET | 200 | 45.40.180.129:80 | http://absolutewellnessspa.com/wp-includes/de/1b8d36hb3f2ggf85/h9f4hh72c108g00c.css | US | text | 21.6 Kb | malicious |
3492 | chrome.exe | GET | 404 | 45.40.180.129:80 | http://absolutewellnessspa.com/wp-includes/de/1b8d36hb3f2ggf85/info-poste-client.min.js | US | html | 76 b | malicious |
3492 | chrome.exe | GET | 200 | 50.116.74.12:80 | http://2myevent.com/2myevent/segovia/IopElz21Anz/open.html | US | html | 118 b | unknown |
3492 | chrome.exe | GET | 200 | 45.40.180.129:80 | http://absolutewellnessspa.com/wp-includes/de/1b8d36hb3f2ggf85/2869g29gc174f302.css | US | text | 15.9 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3492 | chrome.exe | 172.217.21.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3492 | chrome.exe | 172.217.22.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3492 | chrome.exe | 50.116.74.12:80 | 2myevent.com | CyrusOne LLC | US | unknown |
3492 | chrome.exe | 45.40.180.129:80 | absolutewellnessspa.com | GoDaddy.com, LLC | US | suspicious |
3492 | chrome.exe | 184.30.215.37:80 | ocsp.entrust.net | Akamai International B.V. | NL | whitelisted |
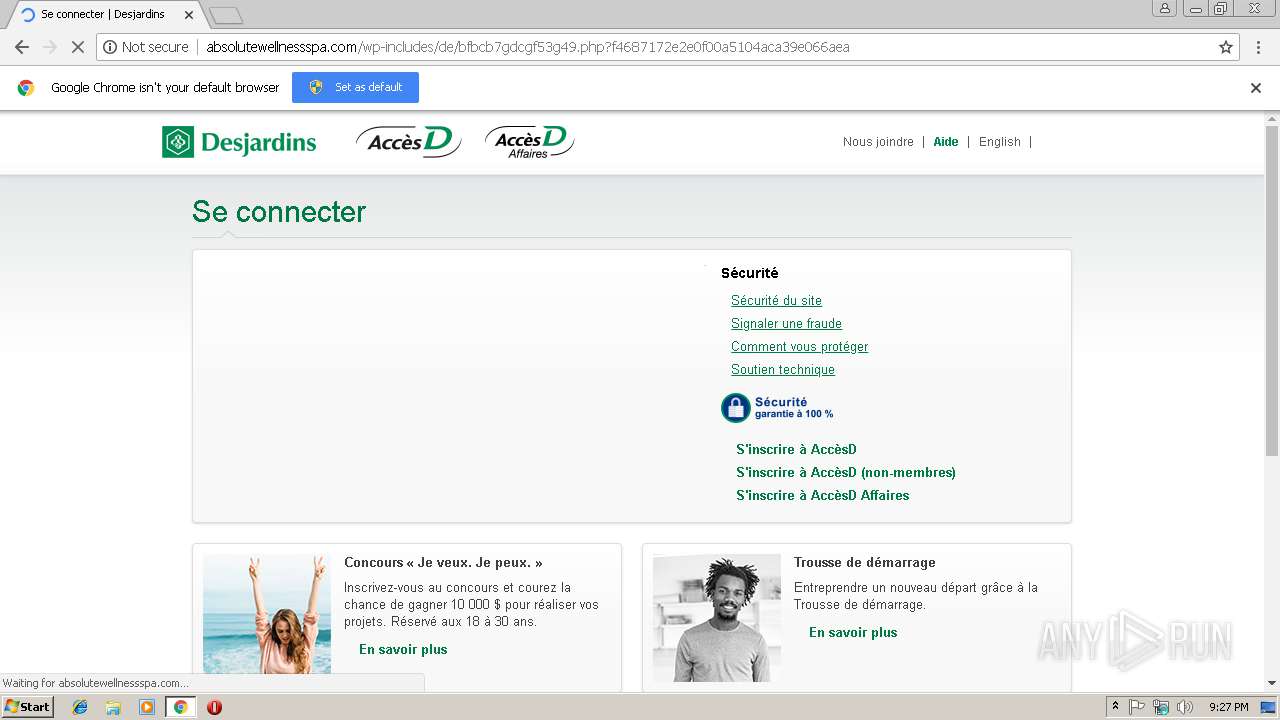
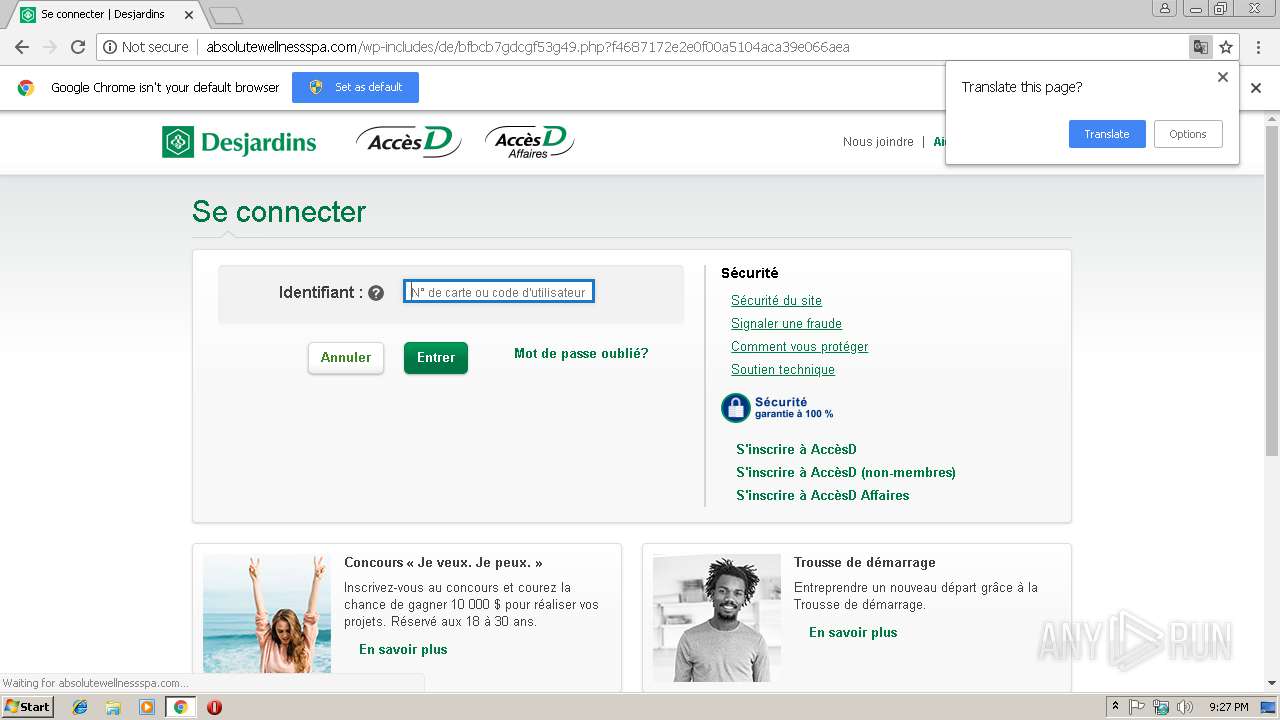
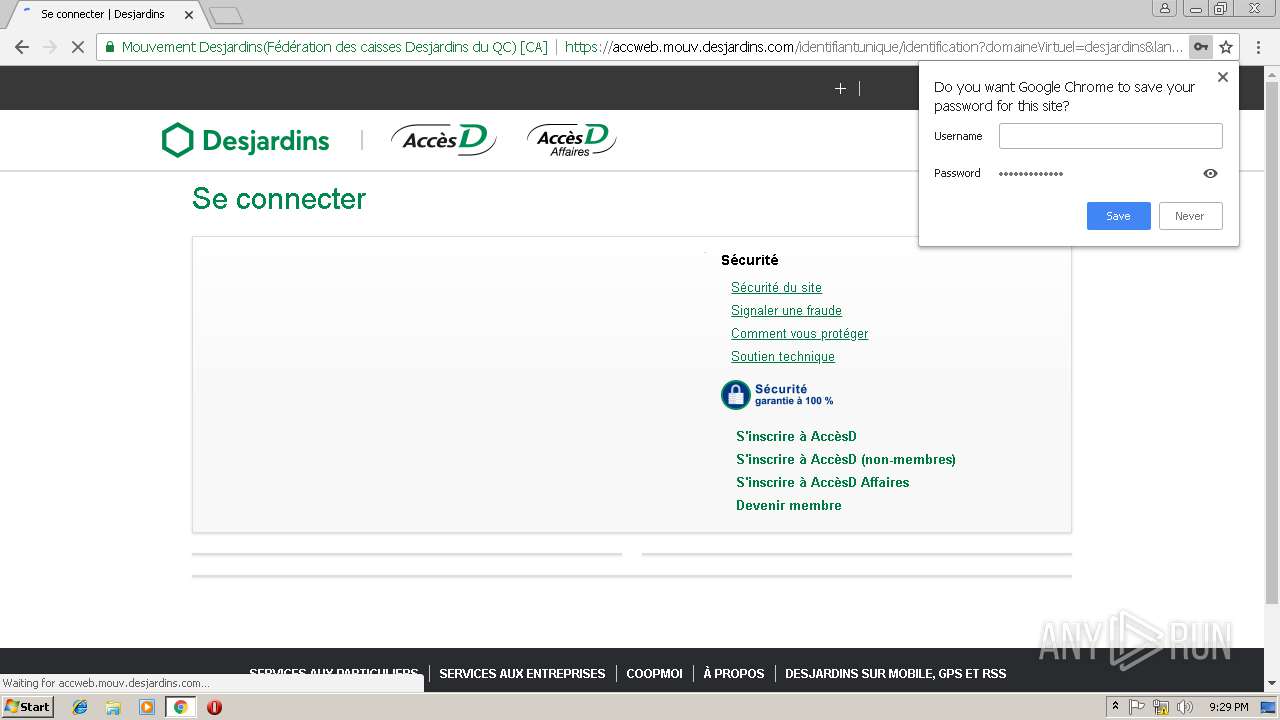
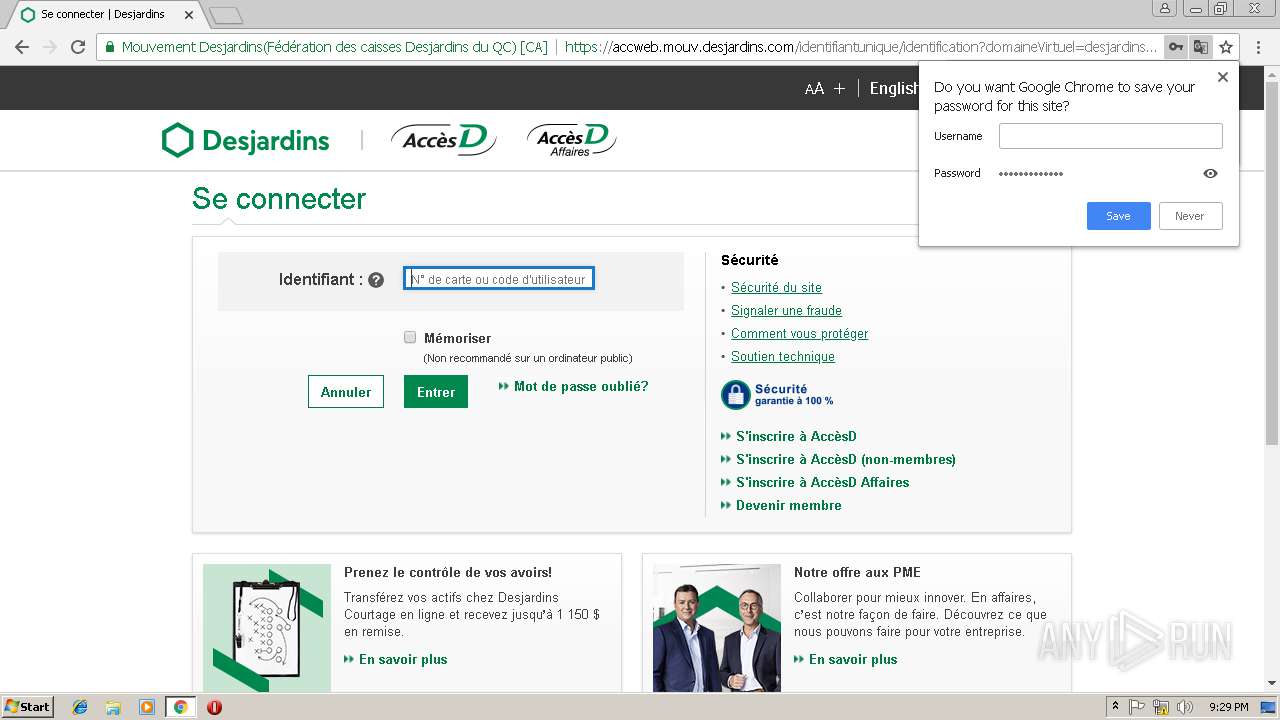
3492 | chrome.exe | 23.45.103.40:443 | accweb.mouv.desjardins.com | Akamai International B.V. | NL | whitelisted |
3492 | chrome.exe | 205.185.216.42:80 | www.download.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
3492 | chrome.exe | 216.58.206.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3492 | chrome.exe | 184.30.213.10:443 | www.desjardins.com | Akamai International B.V. | NL | whitelisted |
3492 | chrome.exe | 216.58.210.14:443 | clients1.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
2myevent.com |
| unknown |
accounts.google.com |
| shared |
absolutewellnessspa.com |
| malicious |
translate.googleapis.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
accweb.mouv.desjardins.com |
| suspicious |
www.download.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
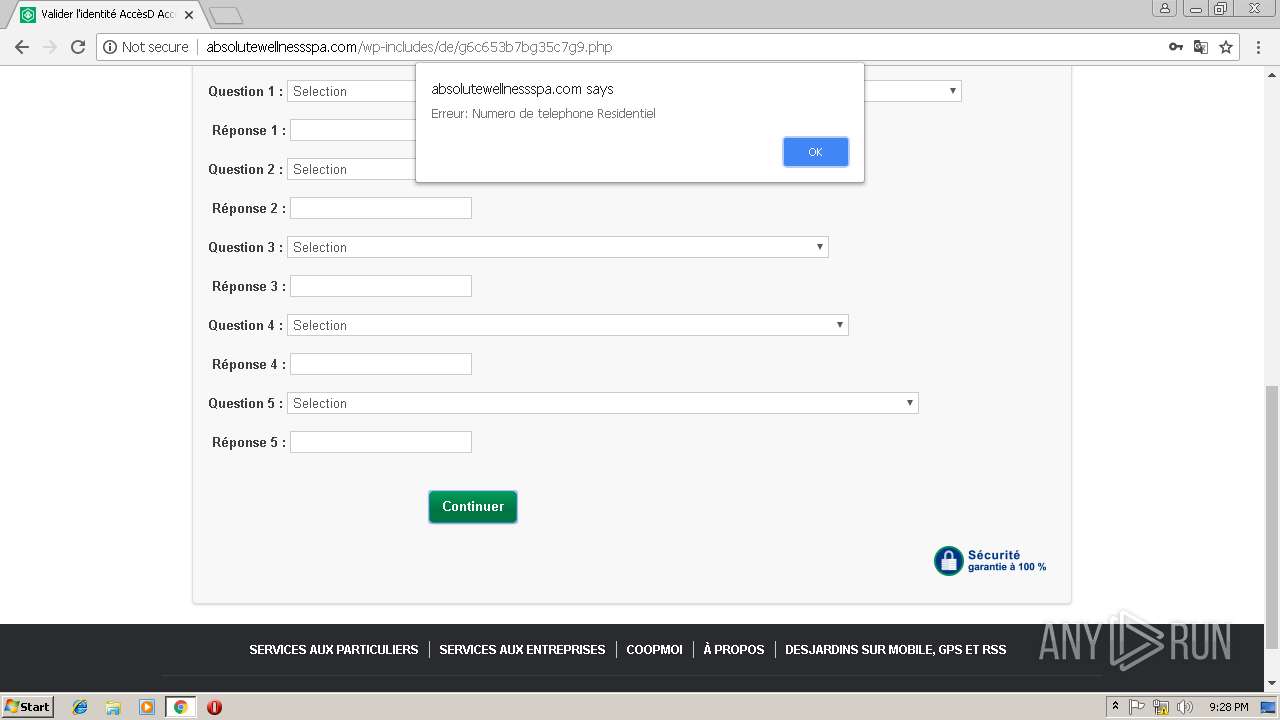
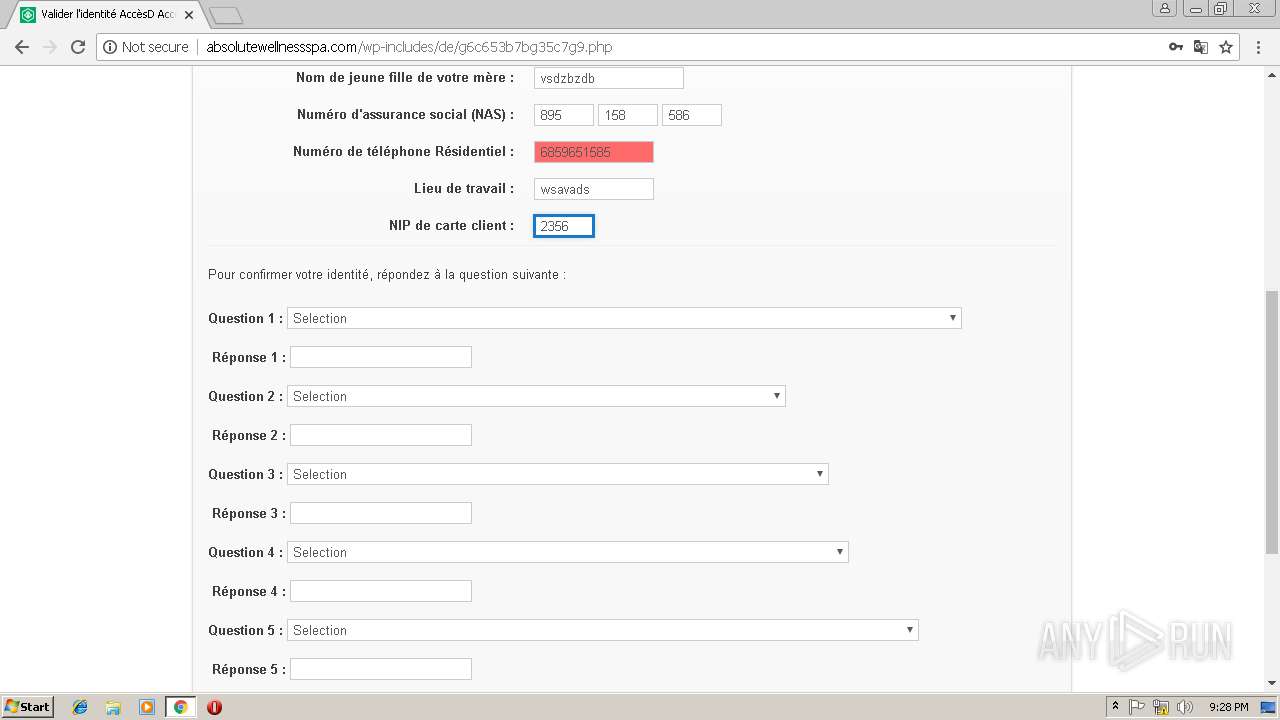
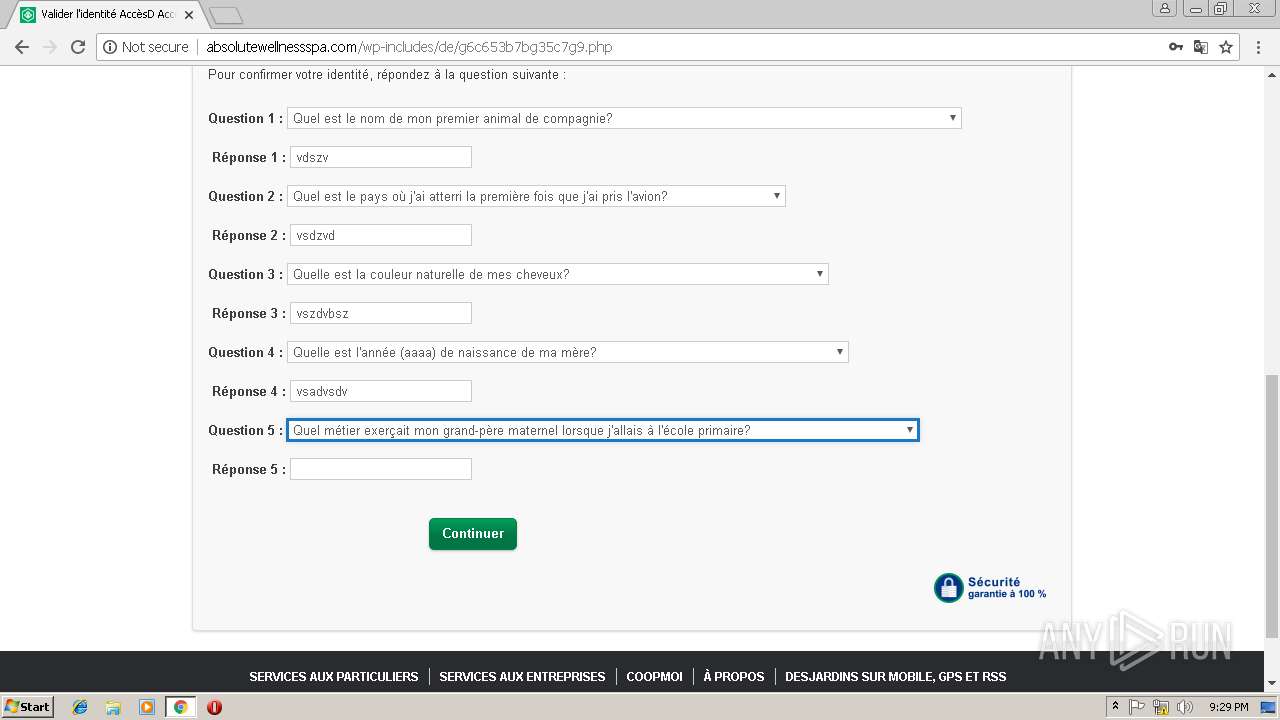
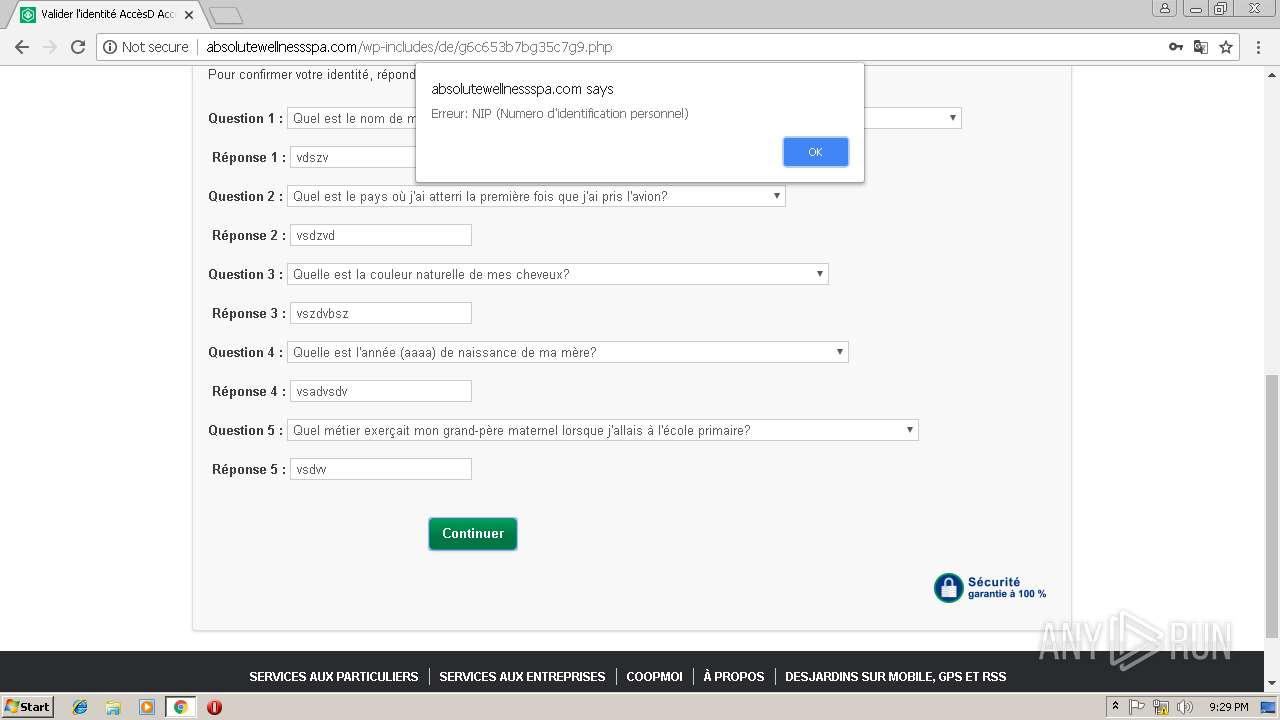
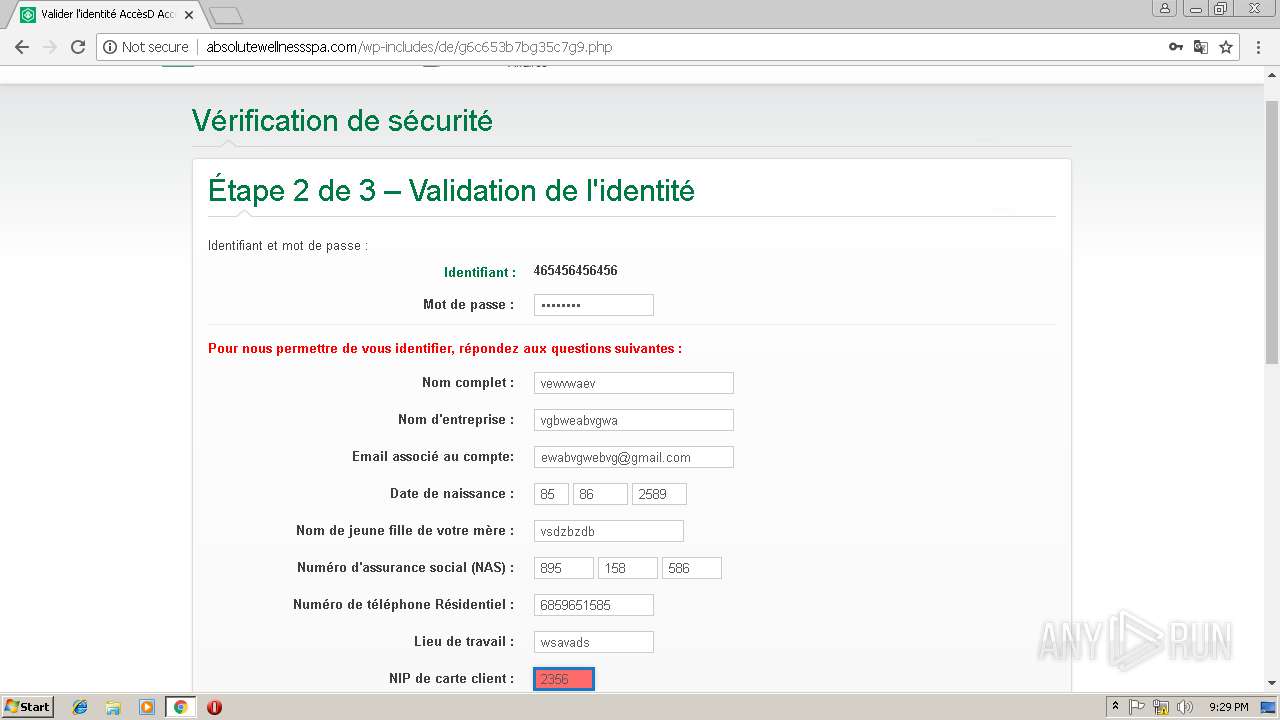
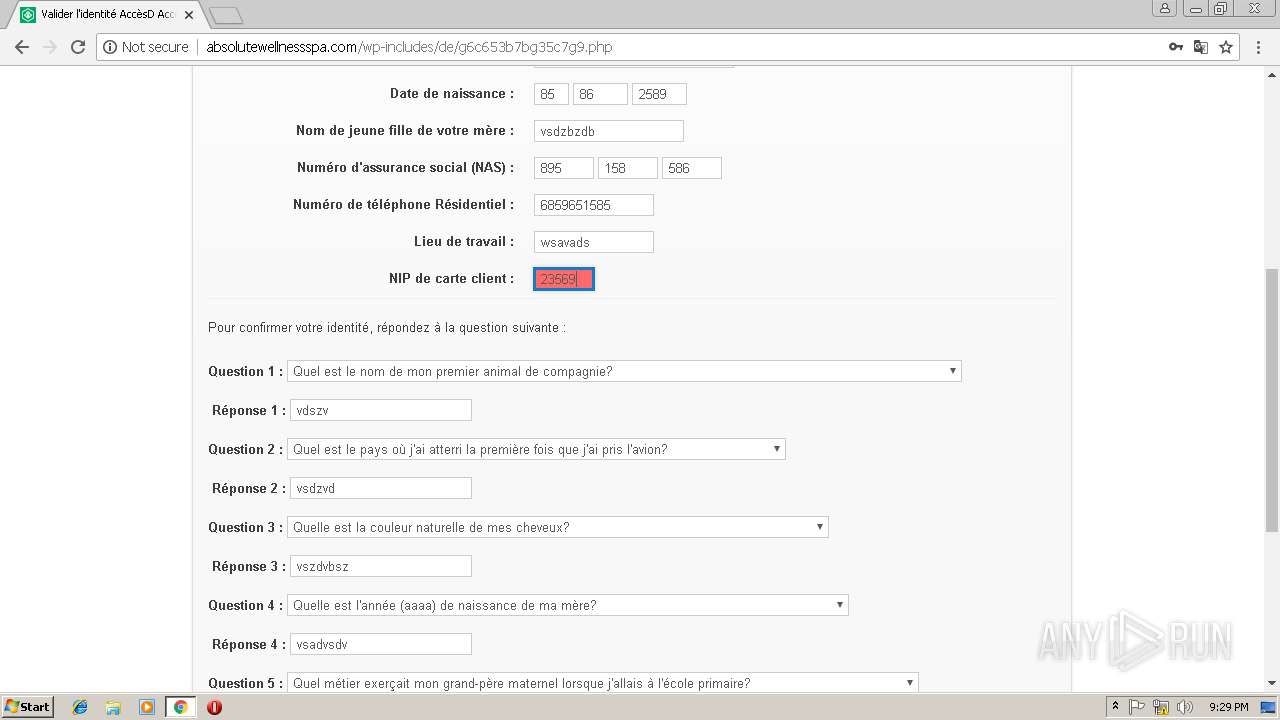
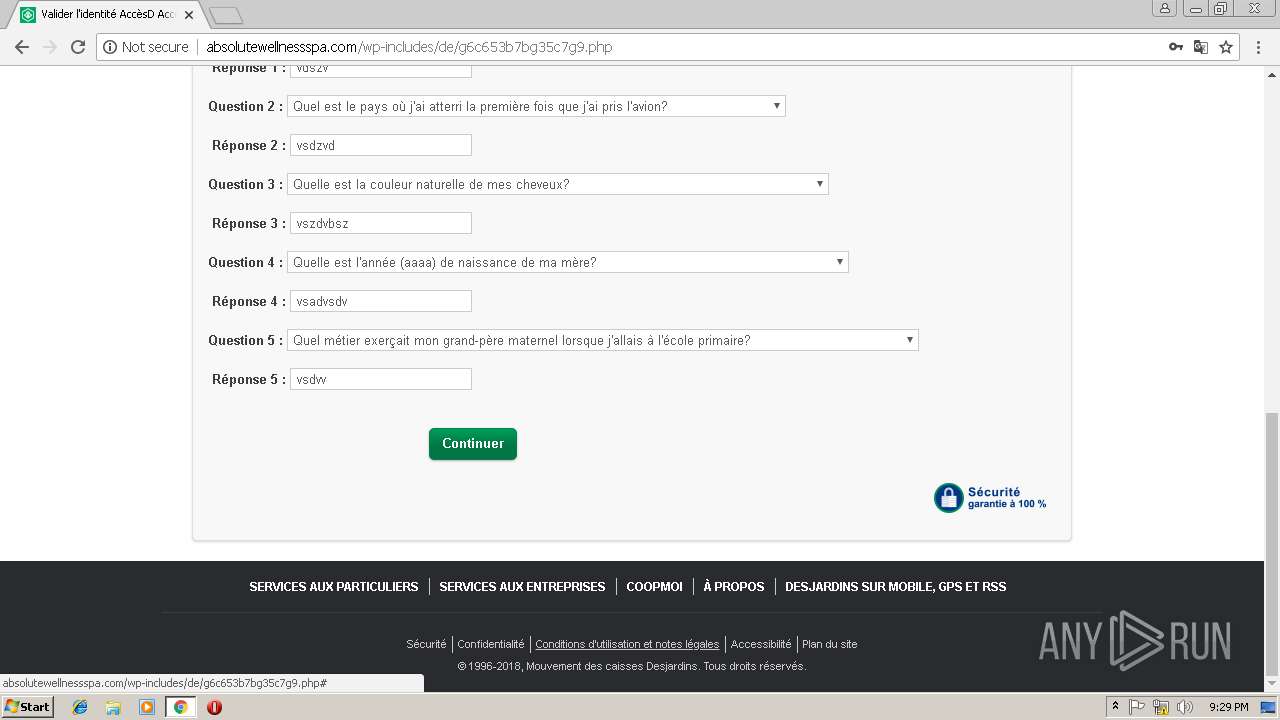
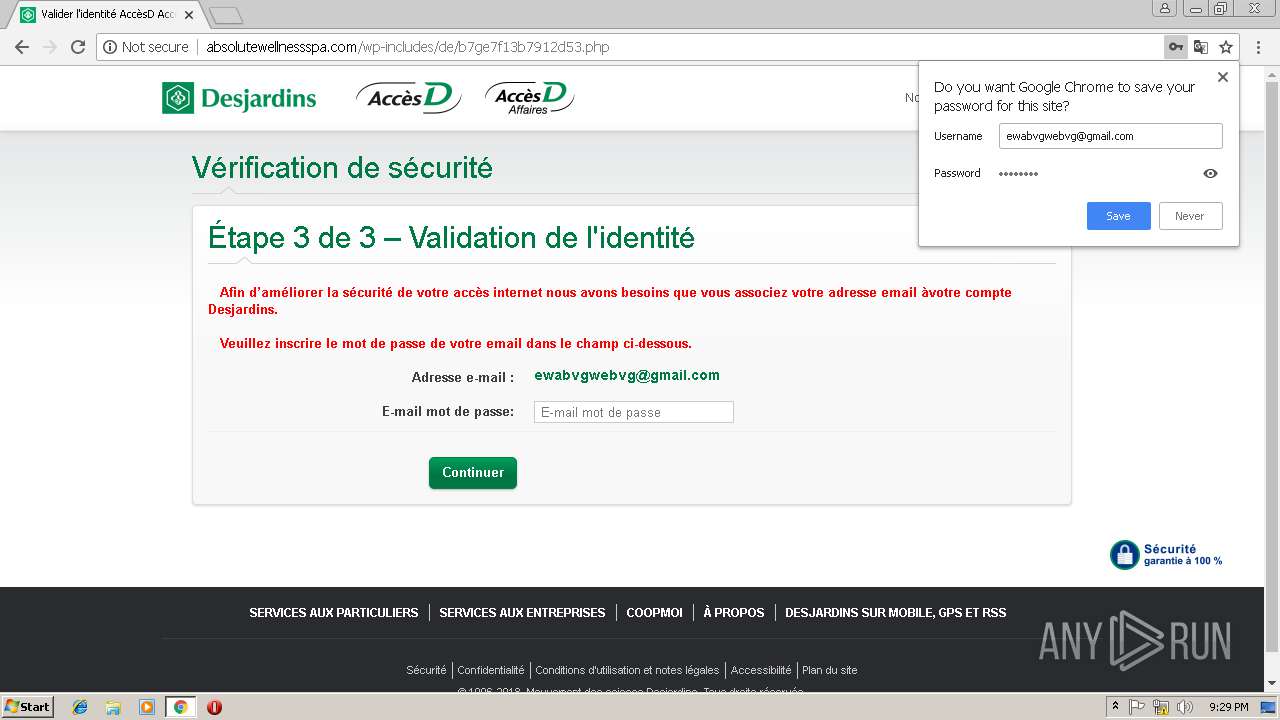
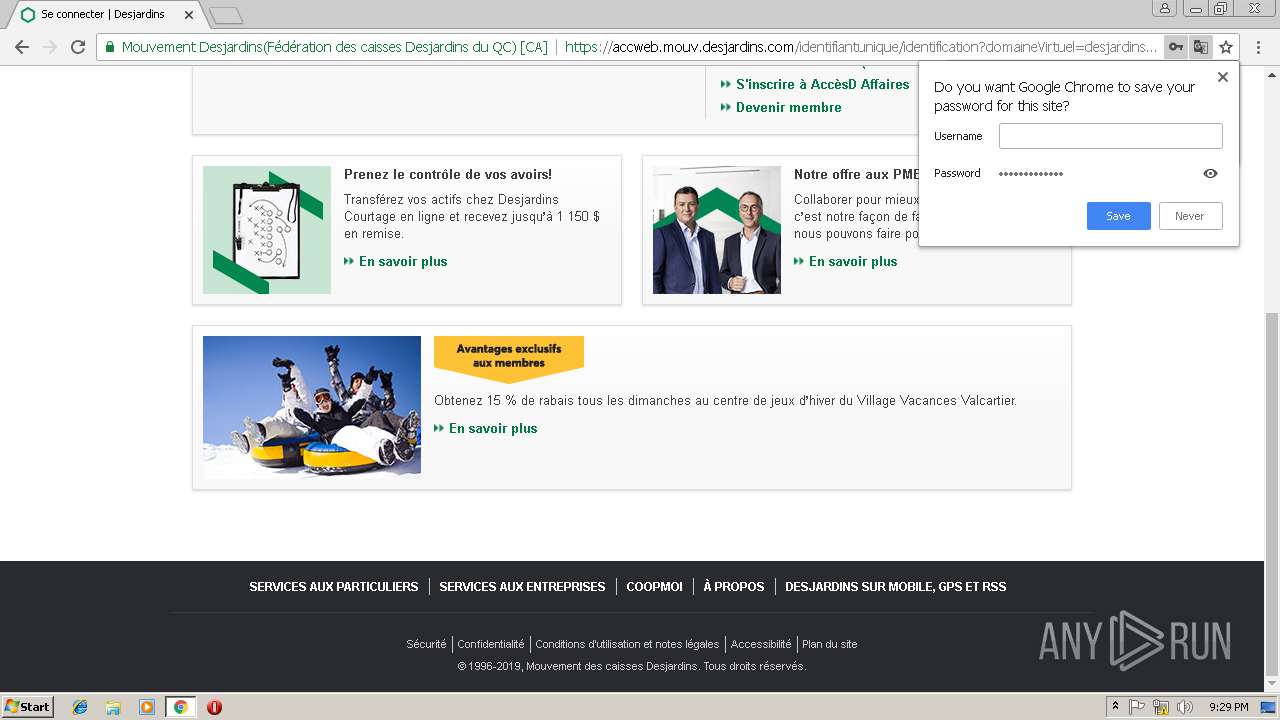
3492 | chrome.exe | A Network Trojan was detected | MALWARE [PTsecurity] Successful Desjardins Bank Phish |
3492 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains pass= in cleartext |
2 ETPRO signatures available at the full report