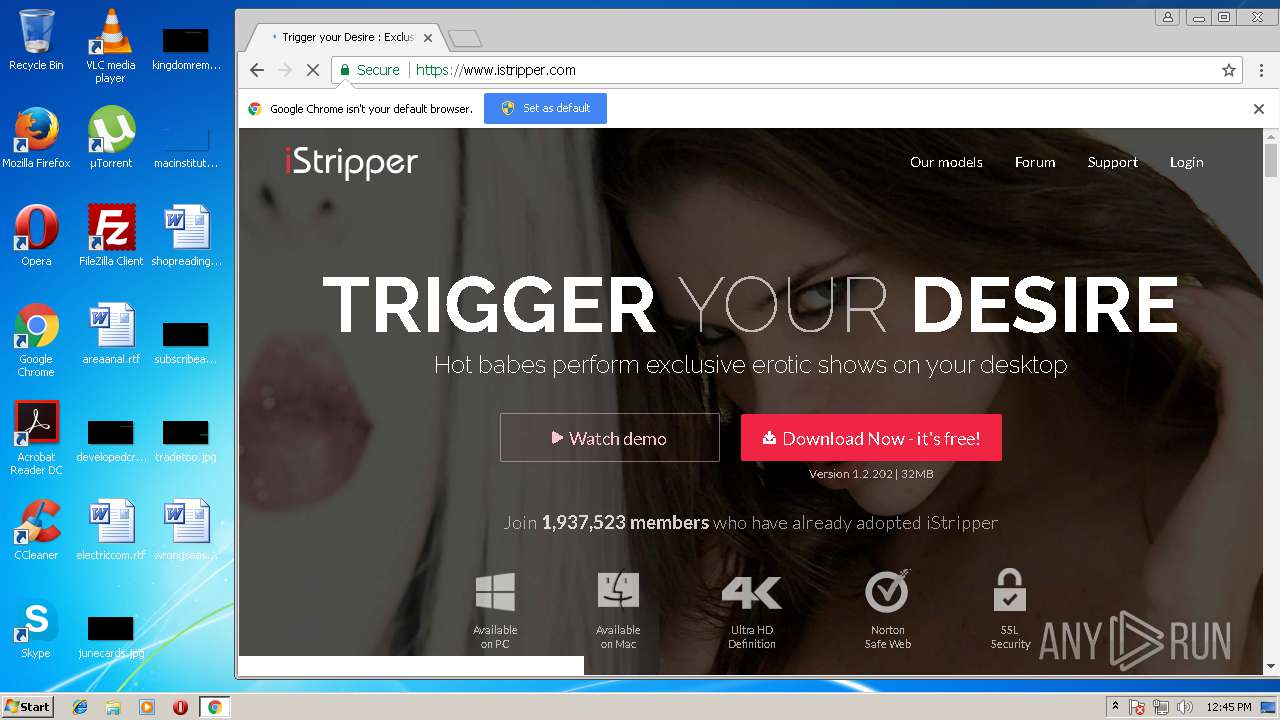
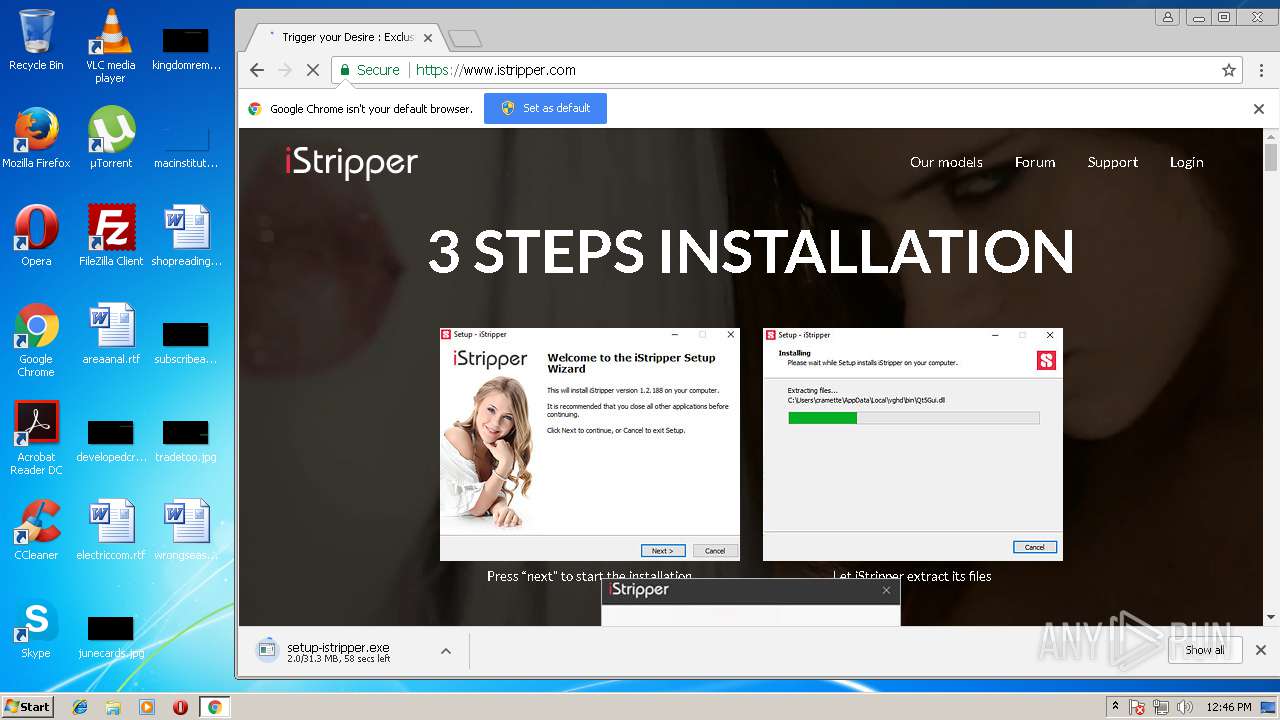
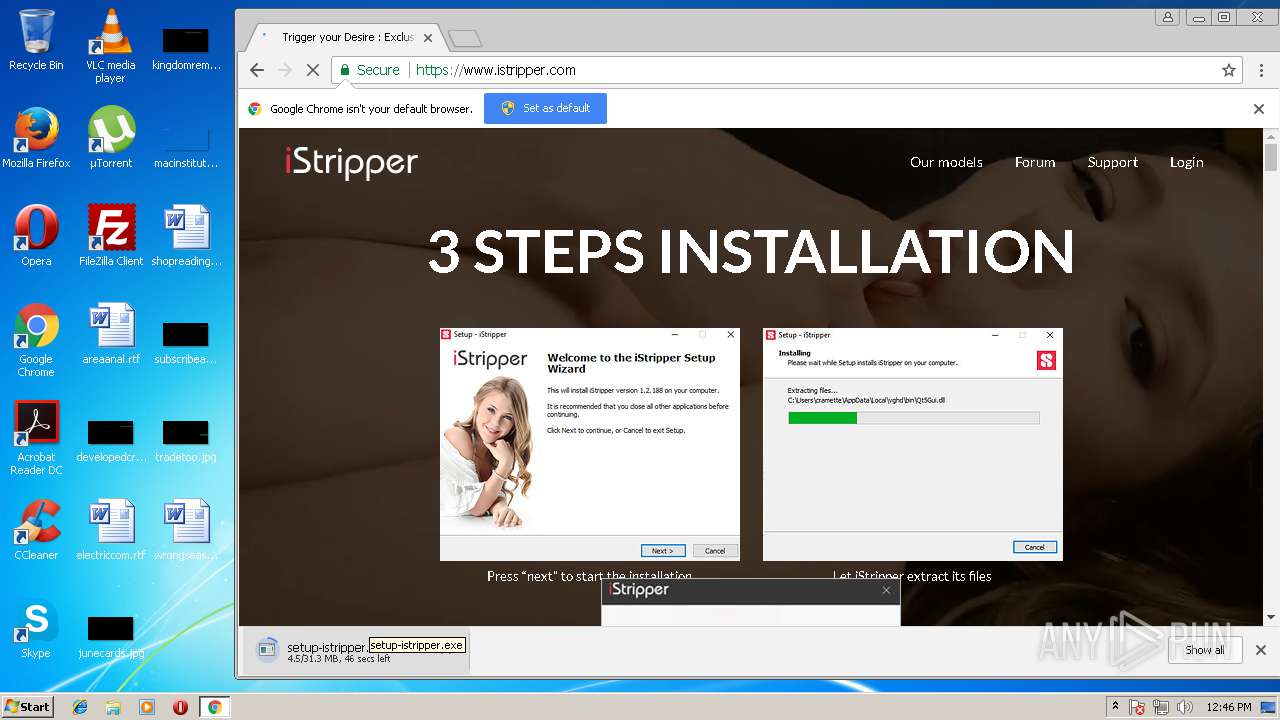
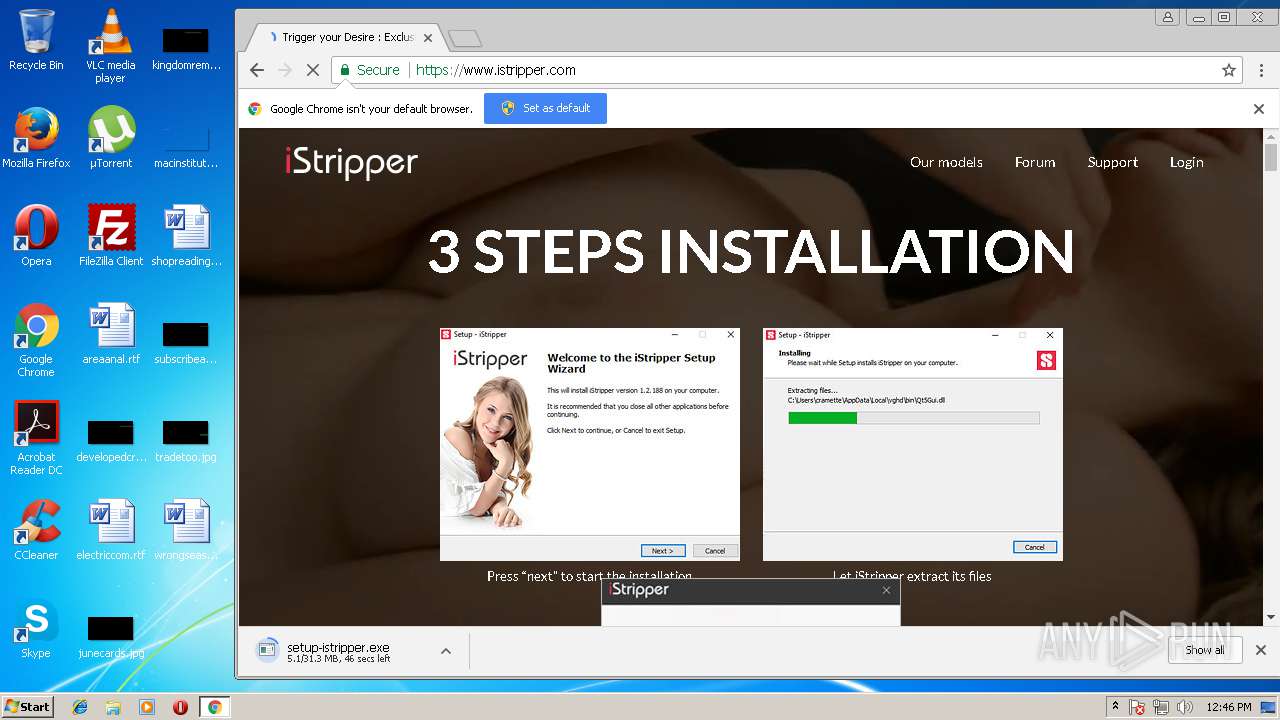
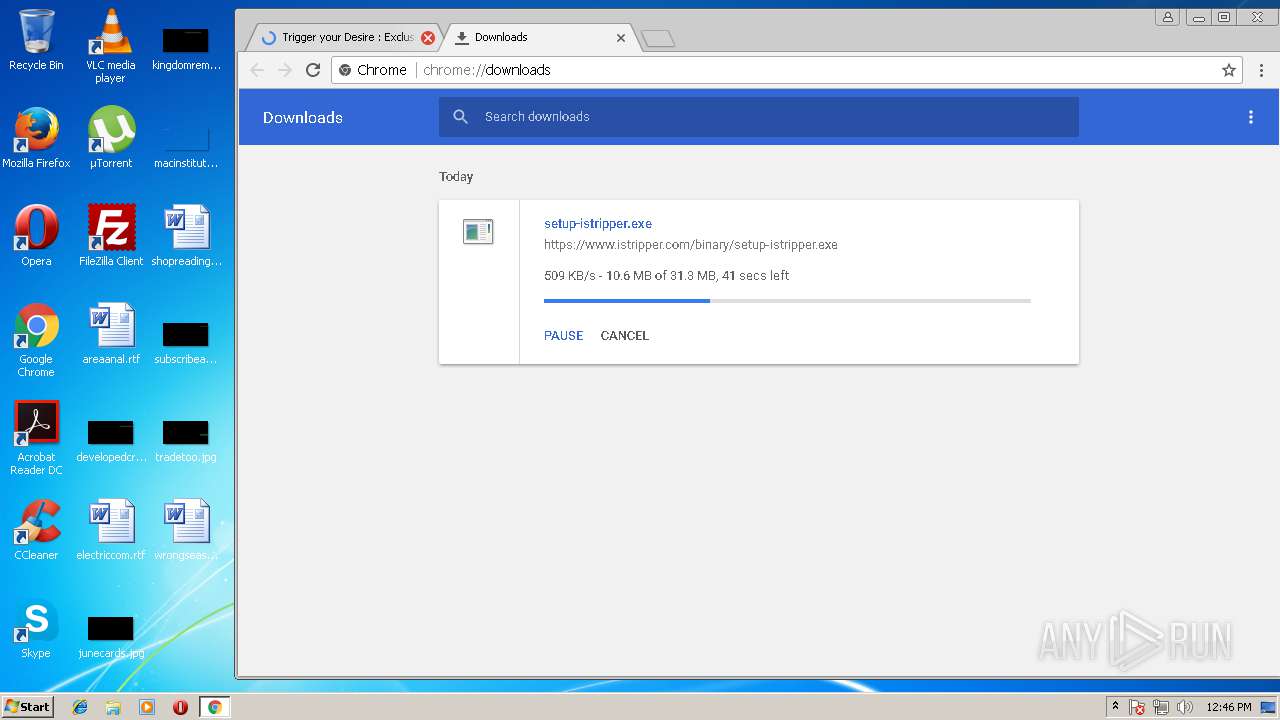
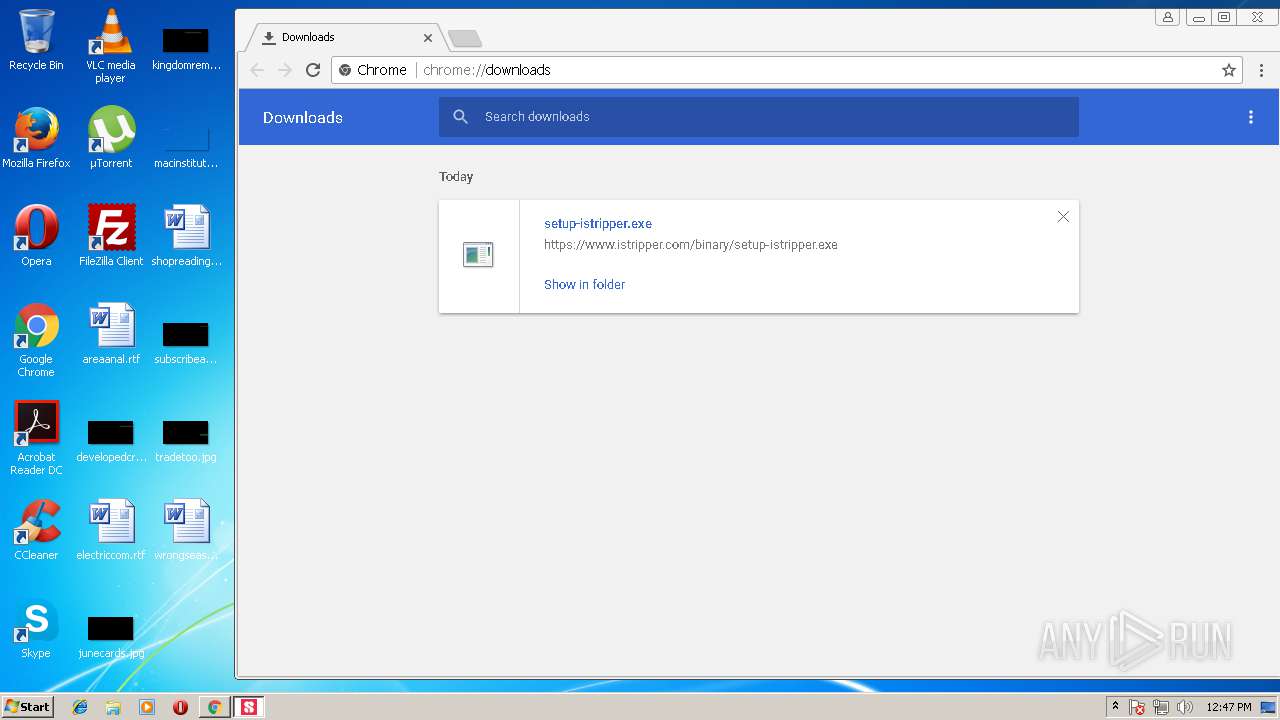
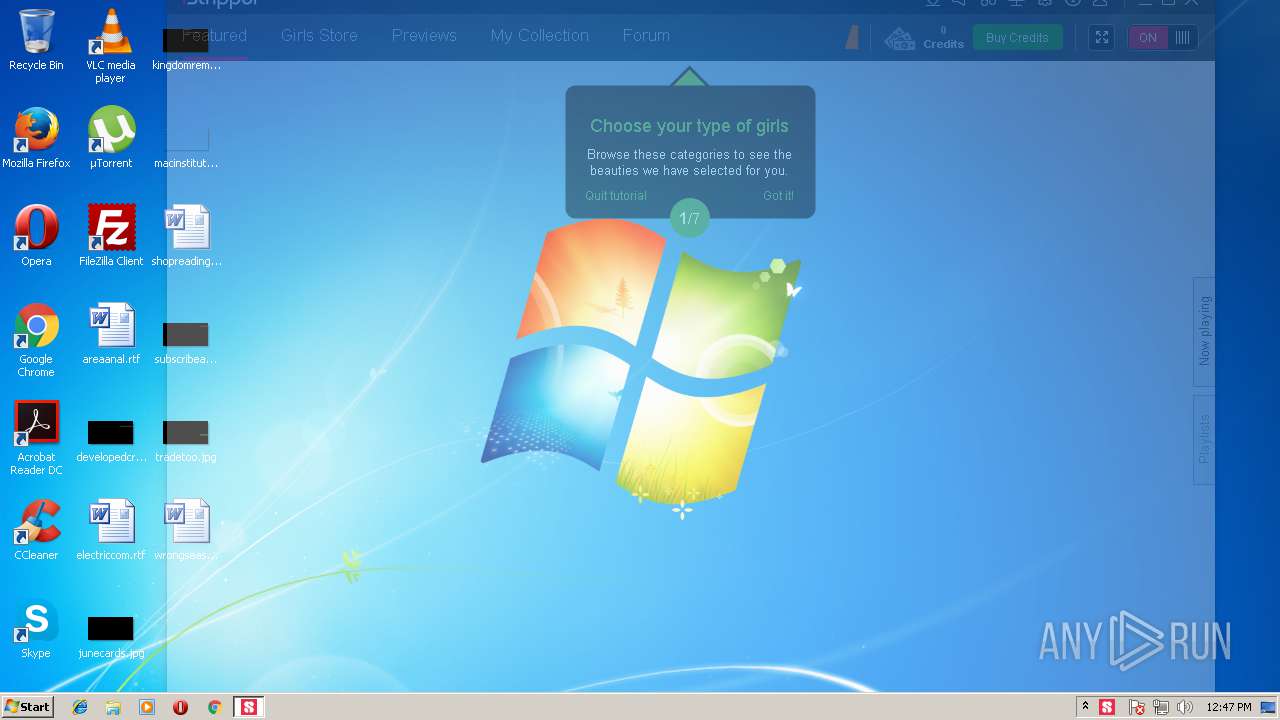
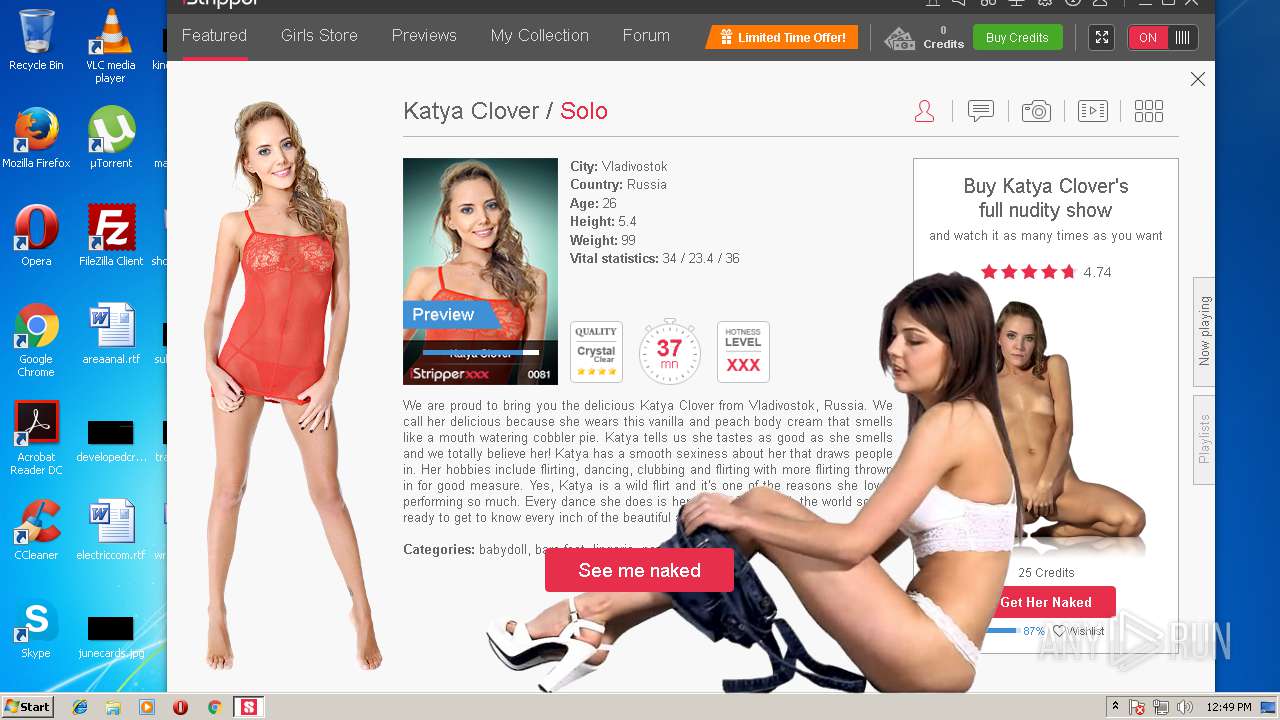
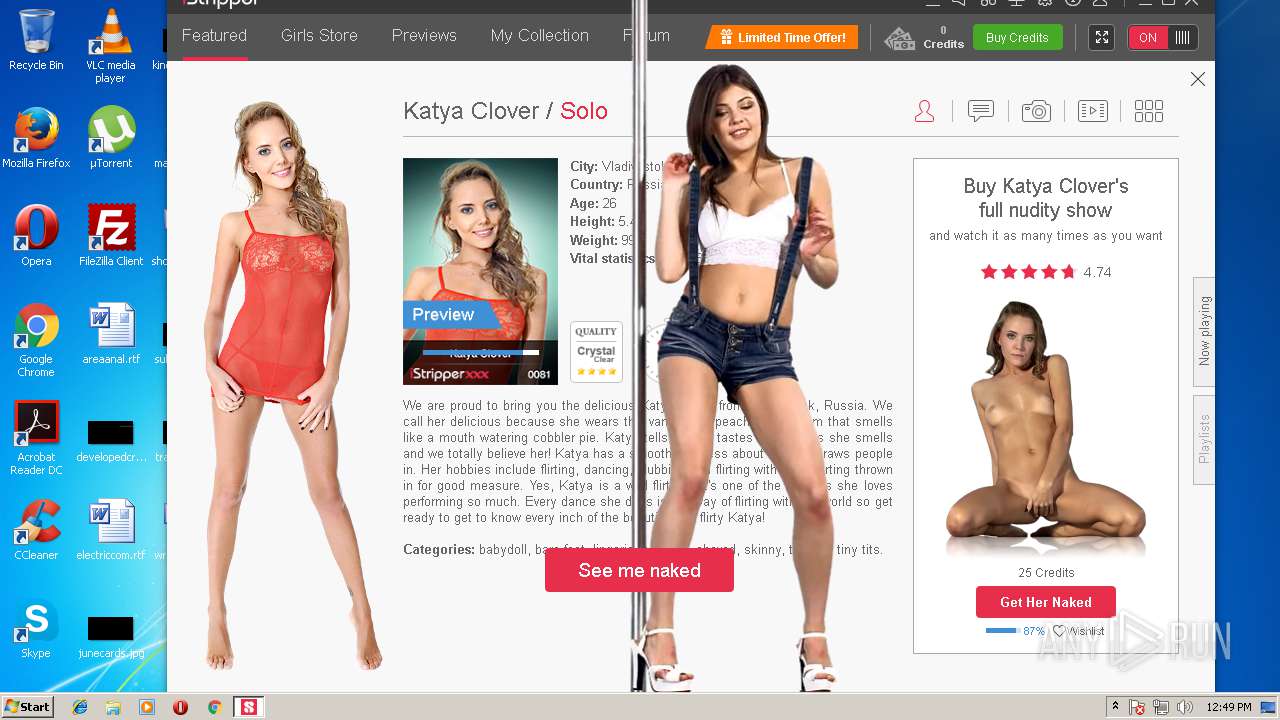
| URL: | http://www.istripper.com/ |
| Full analysis: | https://app.any.run/tasks/624c806b-4633-4a7d-ad8f-8785fafe6833 |
| Verdict: | Malicious activity |
| Analysis date: | July 15, 2018, 11:45:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 06DDB4252E4D818A116ABEF93A69FDC3 |
| SHA1: | A8E02DDCBA4CB3F999FAB10E604F5B94797C30B1 |
| SHA256: | D24D07881C47DAE428D583BAEF449B9B1AF26565C74577E113863BD88EE93E17 |
| SSDEEP: | 3:N1KJS4hBiG:Cc4R |
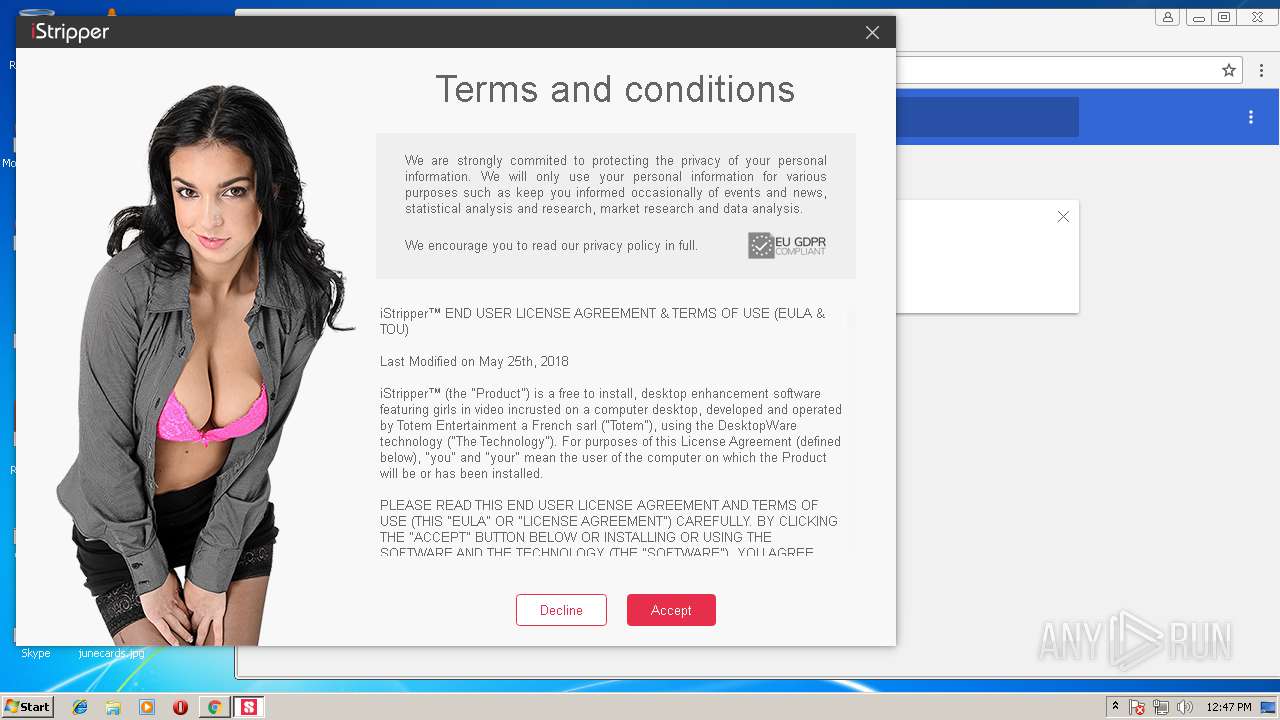
MALICIOUS
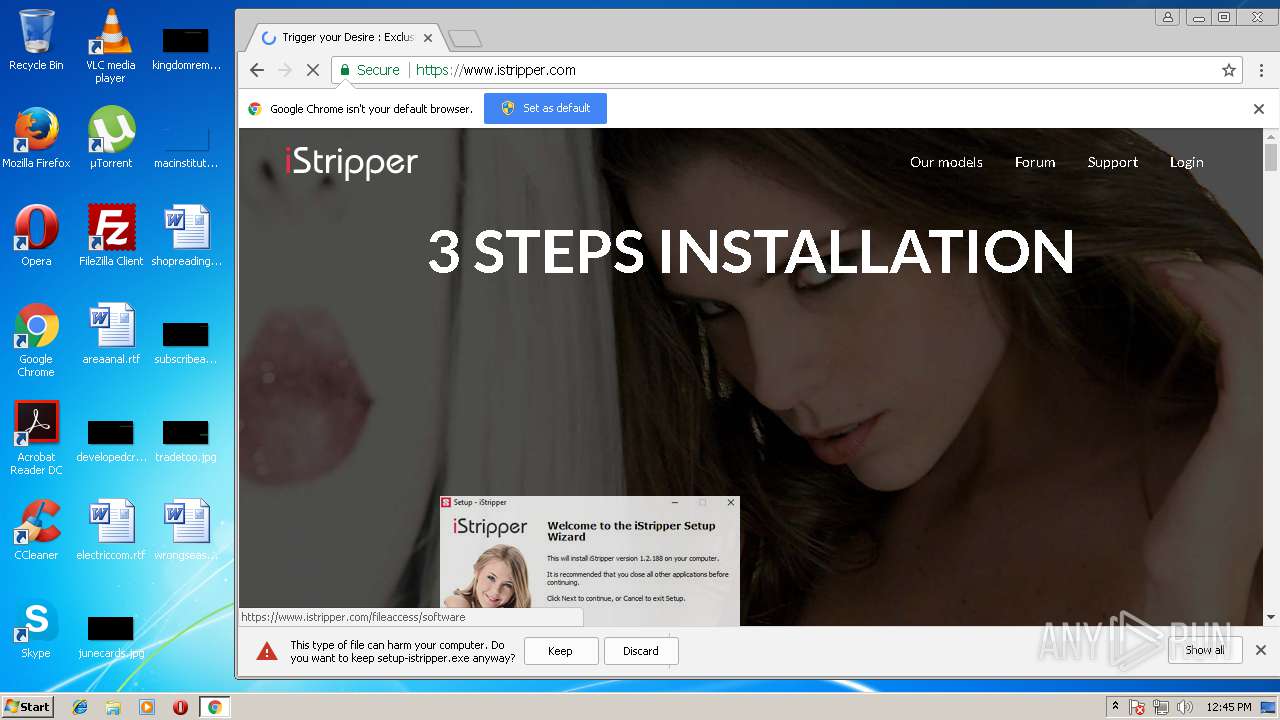
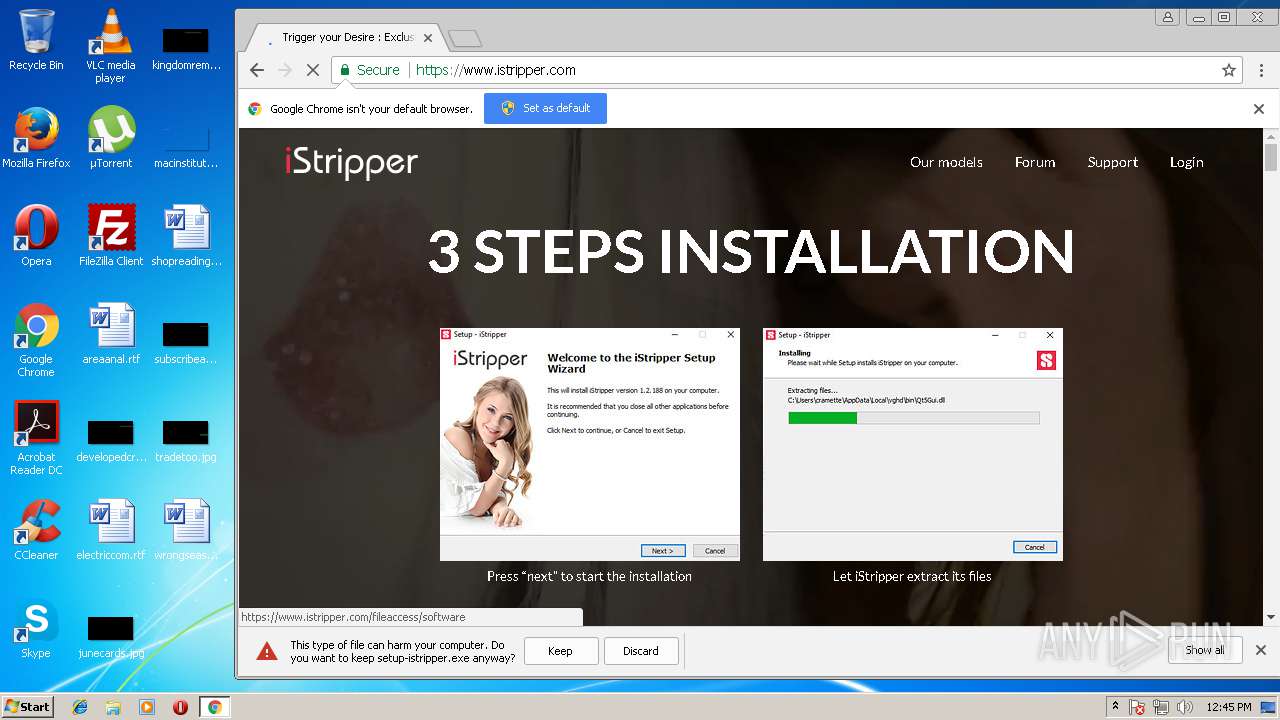
Application was dropped or rewritten from another process
- setup-istripper.exe (PID: 1600)
- vghd.exe (PID: 2580)
Writes to a start menu file
- setup-istripper.tmp (PID: 996)
Loads dropped or rewritten executable
- vghd.exe (PID: 2580)
SUSPICIOUS
Application launched itself
- software_reporter_tool.exe (PID: 3340)
Cleans NTFS data-stream (Zone Identifier)
- chrome.exe (PID: 3028)
Reads Windows owner settings
- setup-istripper.tmp (PID: 996)
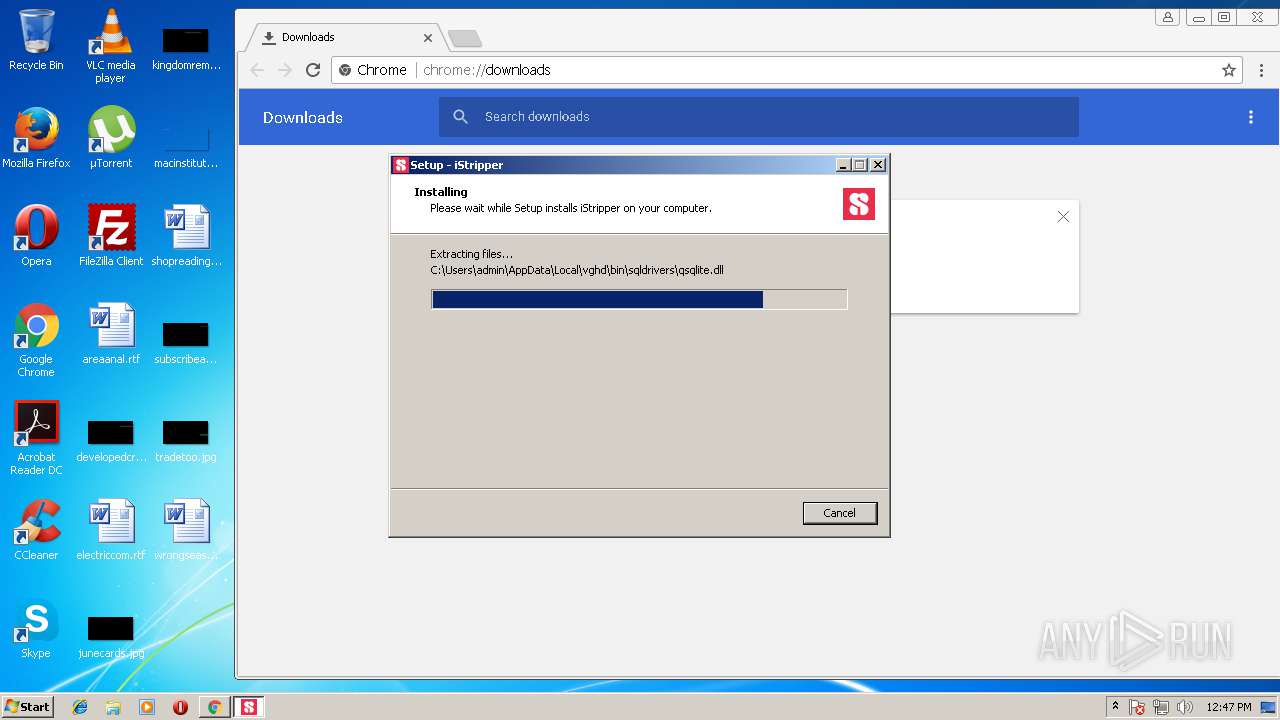
Executable content was dropped or overwritten
- setup-istripper.exe (PID: 1600)
- setup-istripper.tmp (PID: 996)
- chrome.exe (PID: 3028)
Reads the Windows organization settings
- setup-istripper.tmp (PID: 996)
Creates files in the user directory
- setup-istripper.tmp (PID: 996)
Reads Internet Cache Settings
- vghd.exe (PID: 2580)
Reads the BIOS version
- vghd.exe (PID: 2580)
INFO
Creates files in the user directory
- iexplore.exe (PID: 1992)
- FlashUtil32_27_0_0_187_ActiveX.exe (PID: 4000)
- chrome.exe (PID: 3028)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1744)
Reads Internet Cache Settings
- iexplore.exe (PID: 1992)
Changes internet zones settings
- iexplore.exe (PID: 1744)
Changes settings of System certificates
- iexplore.exe (PID: 1744)
Dropped object may contain URL's
- iexplore.exe (PID: 1744)
- chrome.exe (PID: 3028)
- iexplore.exe (PID: 1992)
- vghd.exe (PID: 2580)
- setup-istripper.tmp (PID: 996)
Reads internet explorer settings
- iexplore.exe (PID: 1992)
Application launched itself
- chrome.exe (PID: 3028)
Loads the Task Scheduler COM API
- software_reporter_tool.exe (PID: 3340)
Application was dropped or rewritten from another process
- setup-istripper.tmp (PID: 996)
Loads dropped or rewritten executable
- setup-istripper.tmp (PID: 996)
Dropped object may contain Bitcoin addresses
- setup-istripper.tmp (PID: 996)
Creates a software uninstall entry
- setup-istripper.tmp (PID: 996)
Reads Microsoft Office registry keys
- vghd.exe (PID: 2580)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
52
Monitored processes
20
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1604,17956891563902135478,17695451054721032693,131072 --lang=en-US --no-sandbox --service-request-channel-token=497B584B40541E17ECDBA8C9C71F6EB6 --mojo-platform-channel-handle=1612 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
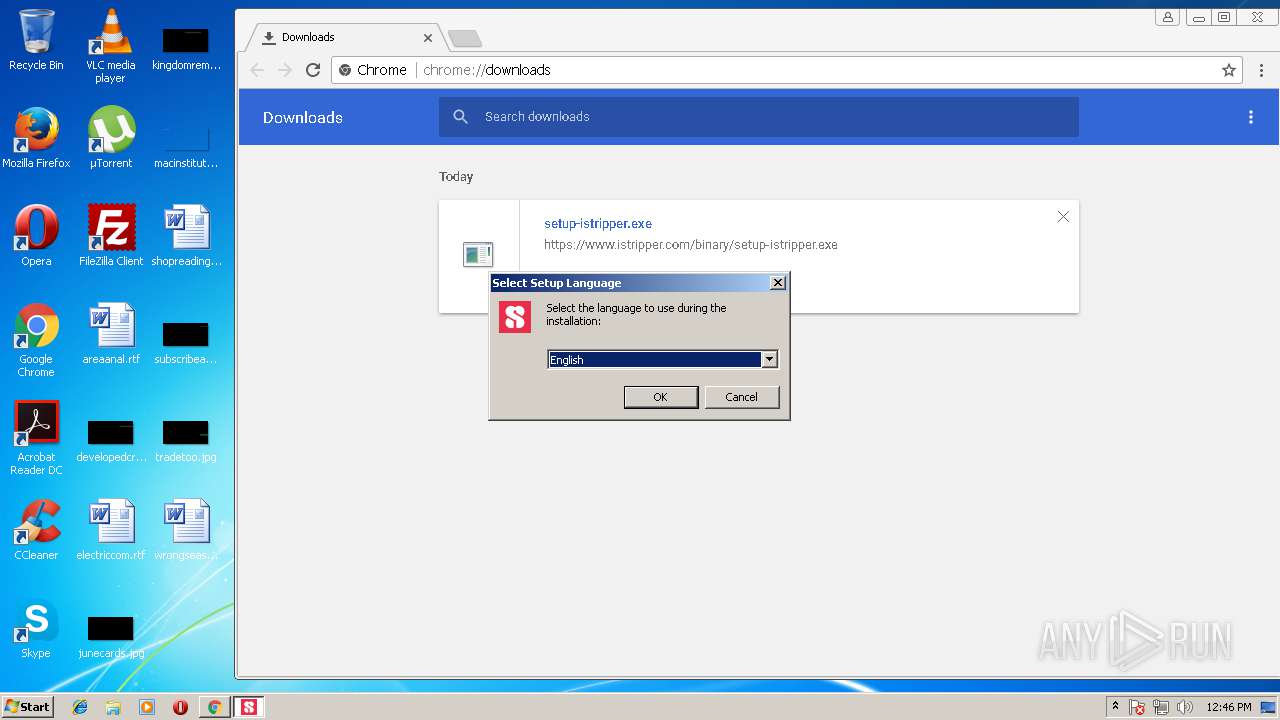
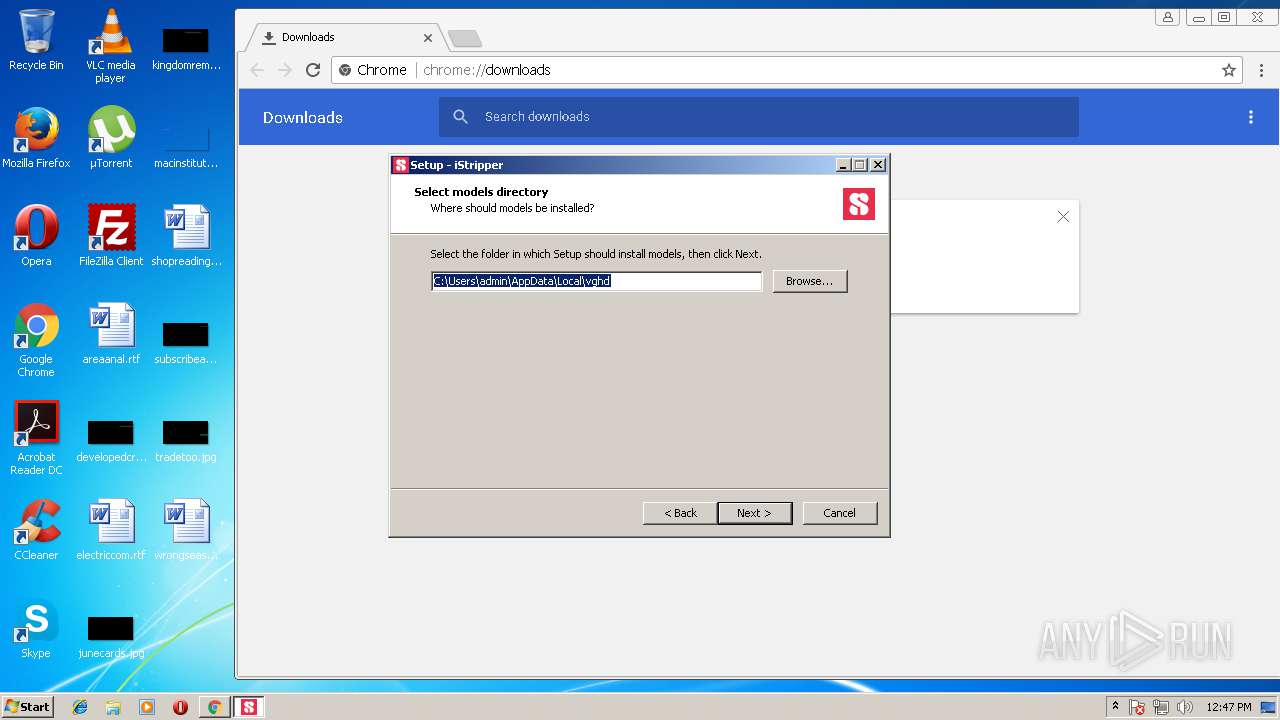
| 996 | "C:\Users\admin\AppData\Local\Temp\is-K9ER5.tmp\setup-istripper.tmp" /SL5="$110236,32320140,136704,C:\Users\admin\Downloads\setup-istripper.exe" | C:\Users\admin\AppData\Local\Temp\is-K9ER5.tmp\setup-istripper.tmp | setup-istripper.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1604,17956891563902135478,17695451054721032693,131072 --service-pipe-token=08B7437955FE89755DD5B20FBFDC498B --lang=en-US --disable-client-side-phishing-detection --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=08B7437955FE89755DD5B20FBFDC498B --renderer-client-id=9 --mojo-platform-channel-handle=4052 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
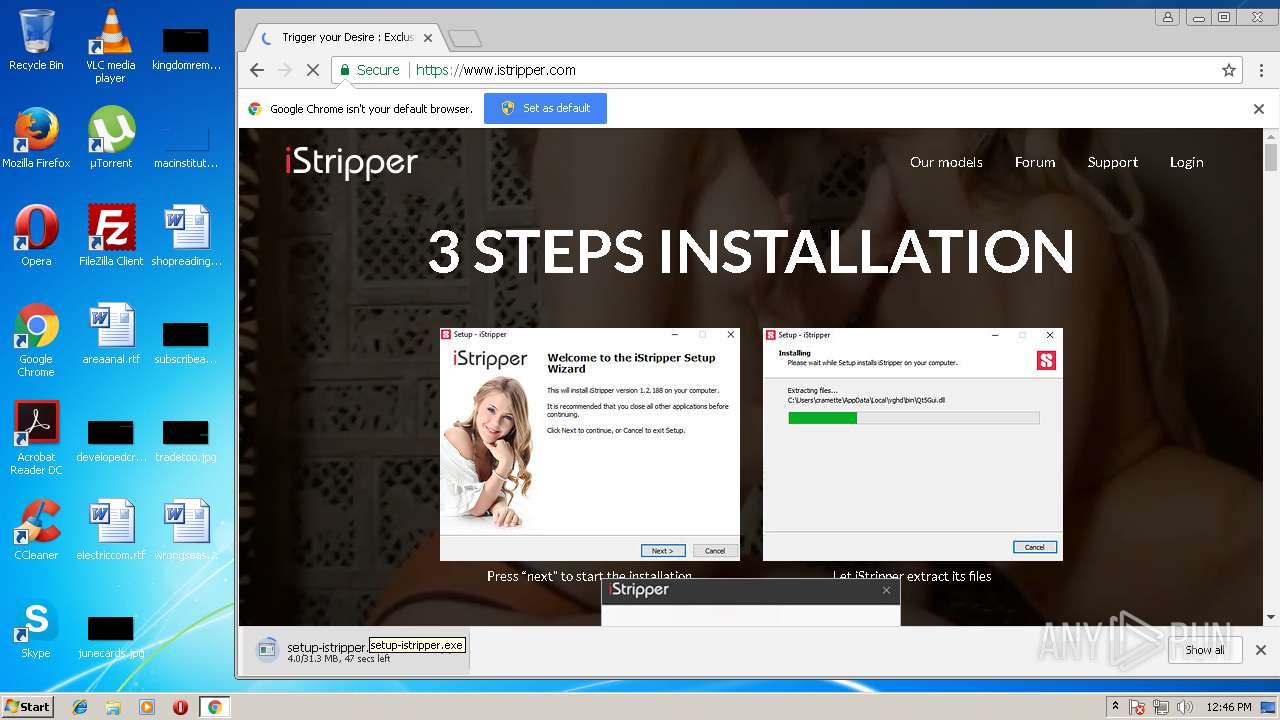
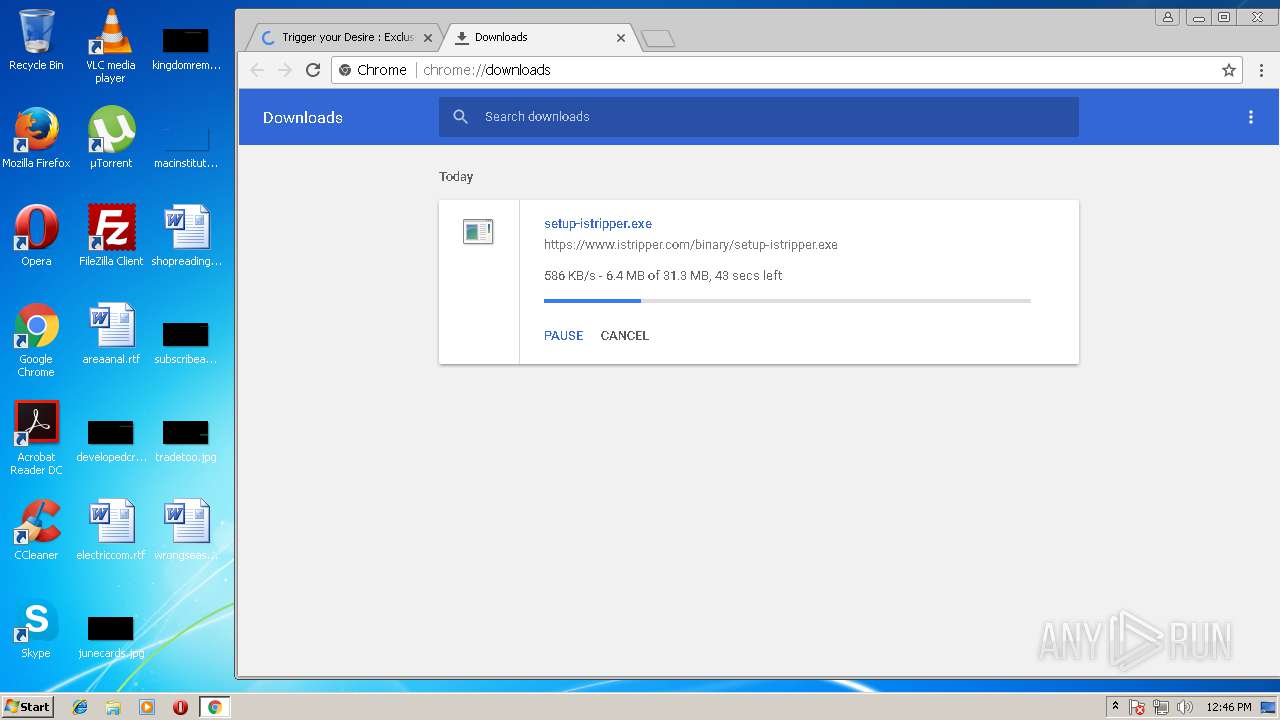
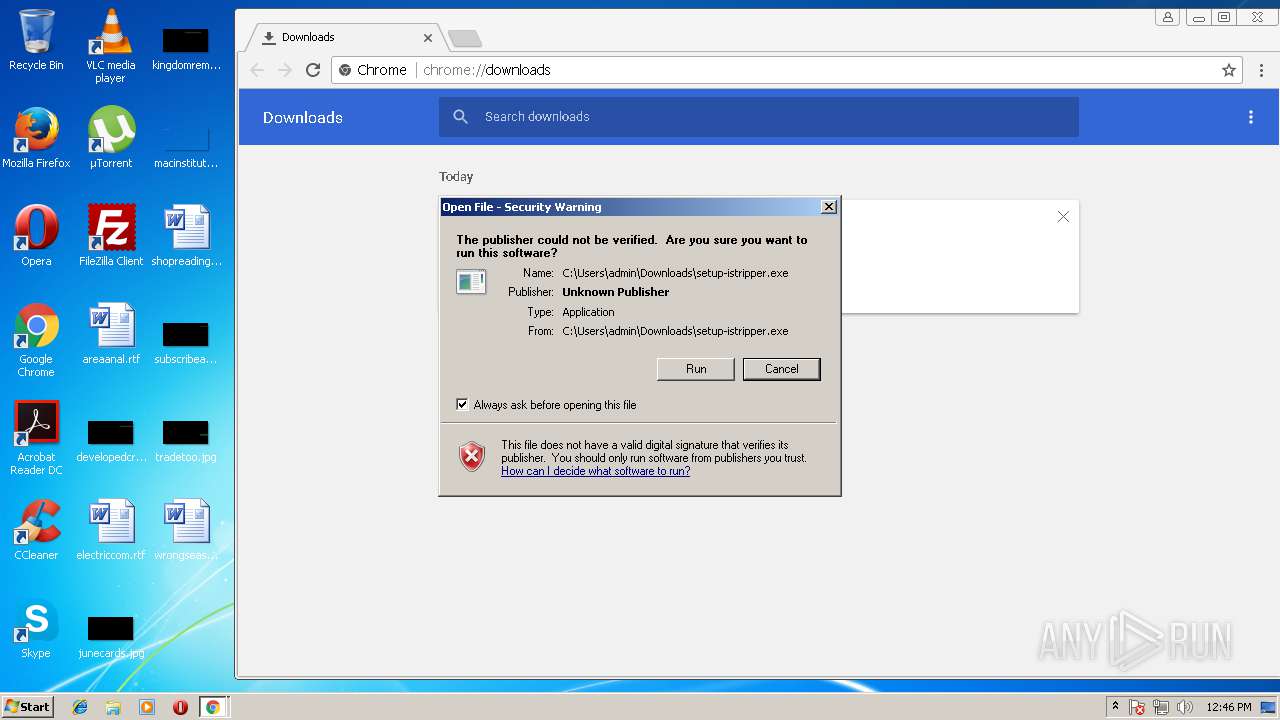
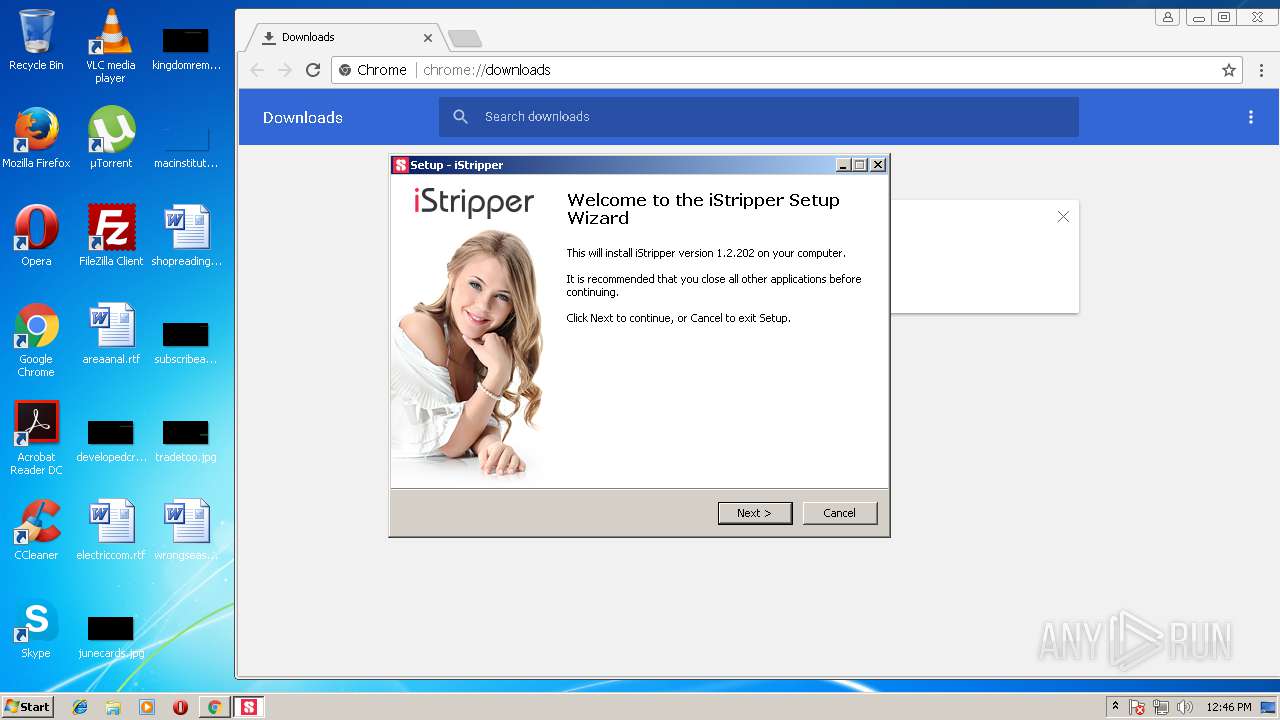
| 1600 | "C:\Users\admin\Downloads\setup-istripper.exe" | C:\Users\admin\Downloads\setup-istripper.exe | chrome.exe | ||||||||||||
User: admin Company: Totem Entertainment Integrity Level: MEDIUM Description: DesktopWare Installer Exit code: 0 Version: 1.2.2.2 Modules
| |||||||||||||||
| 1744 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1992 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1744 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2580 | "C:\Users\admin\AppData\Local\vghd\bin\vghd.exe" -fromSetup | C:\Users\admin\AppData\Local\vghd\bin\vghd.exe | setup-istripper.tmp | ||||||||||||
User: admin Company: Totem Entertainment Integrity Level: MEDIUM Description: DesktopWare / iStripper Exit code: 0 Version: 1.2.2.02 Modules
| |||||||||||||||
| 2704 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1604,17956891563902135478,17695451054721032693,131072 --service-pipe-token=D2AAA4059B36B4CB8BE88FB3CE0CDA43 --lang=en-US --extension-process --disable-client-side-phishing-detection --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=D2AAA4059B36B4CB8BE88FB3CE0CDA43 --renderer-client-id=2 --mojo-platform-channel-handle=1768 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
| 2740 | "c:\users\admin\appdata\local\google\chrome\user data\swreporter\23.129.0\software_reporter_tool.exe" --crash-handler "--database=c:\users\admin\appdata\local\Google\Software Reporter Tool" --url=https://clients2.google.com/cr/report --annotation=plat=Win32 --annotation=prod=ChromeFoil --annotation=ver=23.129.0 --initial-client-data=0xe4,0xec,0xf0,0xe8,0xf4,0xdec42c,0xdec43c,0xdec44c | c:\users\admin\appdata\local\google\chrome\user data\swreporter\23.129.0\software_reporter_tool.exe | — | software_reporter_tool.exe | |||||||||||
User: admin Company: Google Integrity Level: MEDIUM Description: Software Reporter Tool Exit code: 0 Version: 23.129.0 Modules
| |||||||||||||||
| 2900 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1604,17956891563902135478,17695451054721032693,131072 --service-pipe-token=AF070B77018413DCCC0B1341C5104C10 --lang=en-US --disable-client-side-phishing-detection --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=AF070B77018413DCCC0B1341C5104C10 --renderer-client-id=5 --mojo-platform-channel-handle=3236 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
Total events
2 674
Read events
2 105
Write events
544
Delete events
25
Modification events
| (PID) Process: | (1744) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1744) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1744) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1744) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (1744) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1744) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000070000000010000000000000000000000000000000000000000000000400C35B347C7D301000000000000000000000000020000001700000000000000FE80000000000000D45917EAB3ED3D860B000000000000001700000000000000FE80000000000000D45917EAB3ED3D860B000000000000001C00000000000000000000000000000000000000000000000000000000000000170000000000000000000000000000000000FFFFC0A8640B000000000000000002000000C0A801640000000000000000000000000000000000000000000000000C00000C37D0000010A73800D8703600000000000000000000000000000000000000000000000000000000000000000000000000000000000000000081F800009000230090002300380023000000000000702C000A00000000000000F8412C00 | |||
| (PID) Process: | (1744) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {9428F537-8824-11E8-B27F-5254004AAD21} |
Value: 0 | |||
| (PID) Process: | (1744) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (1744) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 5 | |||
| (PID) Process: | (1744) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E207070000000F000B002D0021006001 | |||
Executable files
73
Suspicious files
211
Text files
518
Unknown types
93
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1744 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\2LKO8ICX\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 1744 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1992 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@istripper[1].txt | — | |
MD5:— | SHA256:— | |||
| 1992 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab8E47.tmp | — | |
MD5:— | SHA256:— | |||
| 1992 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar8E48.tmp | — | |
MD5:— | SHA256:— | |||
| 1992 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab8E59.tmp | — | |
MD5:— | SHA256:— | |||
| 1992 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar8E5A.tmp | — | |
MD5:— | SHA256:— | |||
| 1992 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab8EC8.tmp | — | |
MD5:— | SHA256:— | |||
| 1992 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar8EC9.tmp | — | |
MD5:— | SHA256:— | |||
| 1992 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\WF2FXMJU\istripper_com[1].txt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
101
TCP/UDP connections
98
DNS requests
37
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1744 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
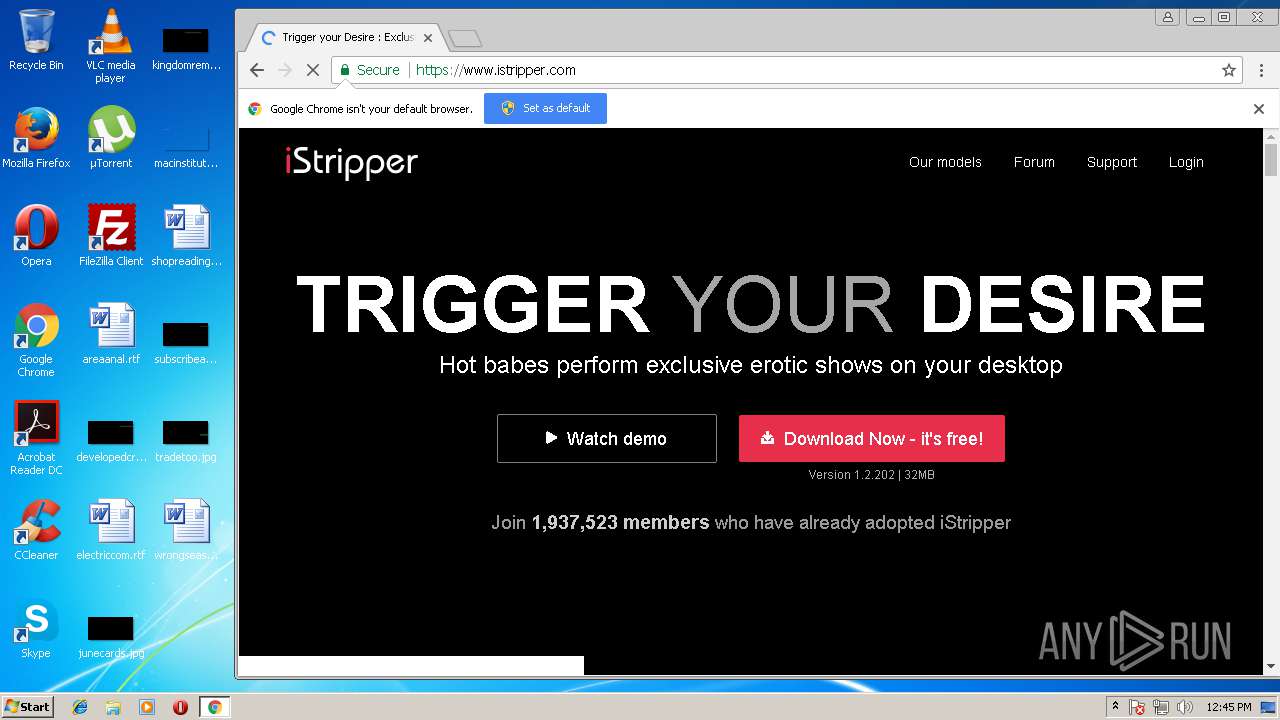
1992 | iexplore.exe | GET | 301 | 130.185.144.4:80 | http://www.istripper.com/ | GB | — | — | suspicious |
1992 | iexplore.exe | GET | 200 | 192.35.177.64:80 | http://apps.identrust.com/roots/dstrootcax3.p7c | US | cat | 893 b | shared |
3028 | chrome.exe | GET | 304 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | — | — | whitelisted |
1992 | iexplore.exe | GET | 304 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | — | — | whitelisted |
3028 | chrome.exe | GET | 304 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | — | — | whitelisted |
3028 | chrome.exe | GET | 304 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | — | — | whitelisted |
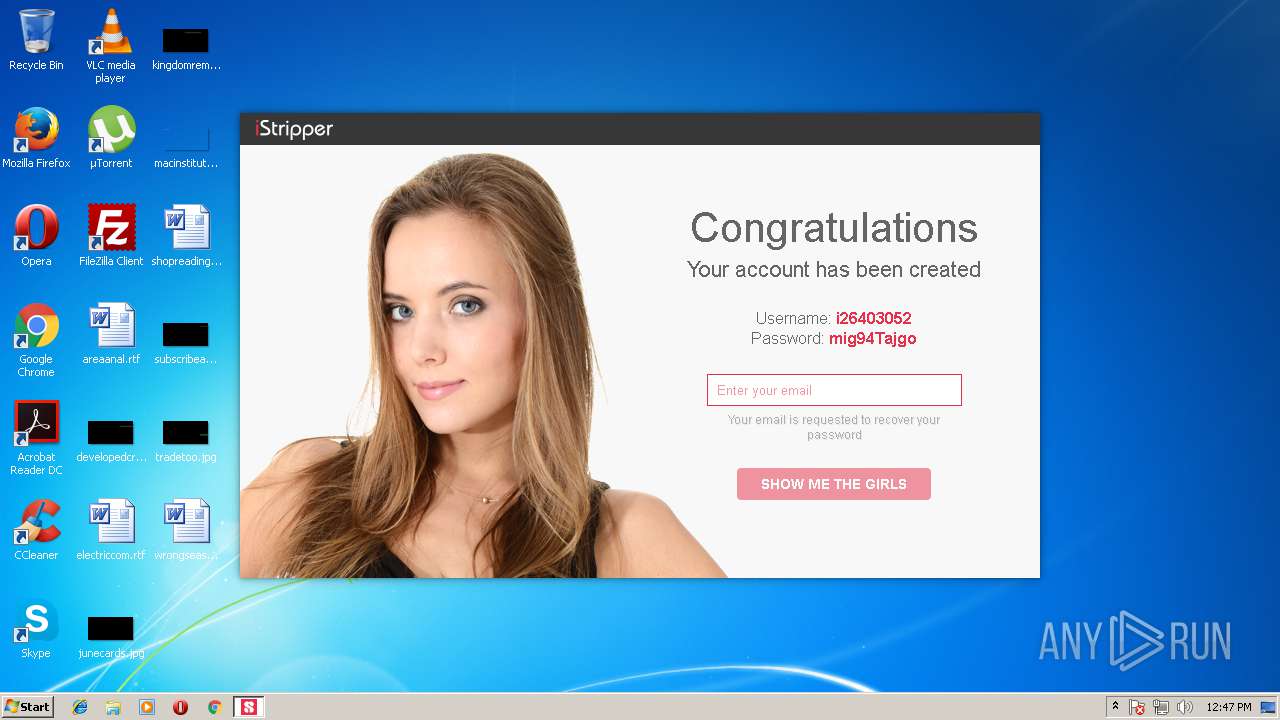
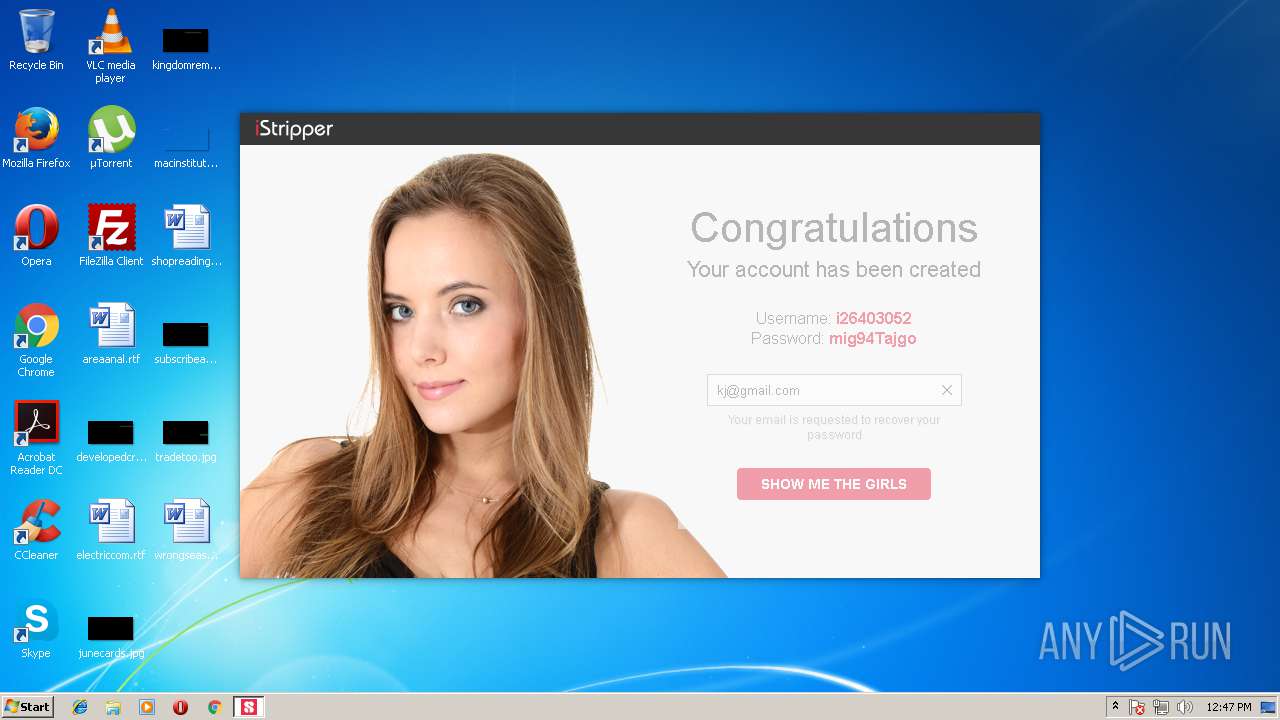
2580 | vghd.exe | GET | 200 | 130.185.144.4:80 | http://www.istripper.com/software/wishlist?add=&remove=&ui=i26403052&uk=FGFIKEFBBNHEKJBCFCKLMIKNBLIBOACJ&explicit=1&language=en | GB | text | 11 b | suspicious |
2580 | vghd.exe | POST | 200 | 130.185.144.4:80 | http://www.istripper.com/bof/bof.php | GB | binary | 26 b | suspicious |
2580 | vghd.exe | GET | 200 | 130.185.144.4:80 | http://www.istripper.com/bof/user4.php?user=U9T4B1generate&pass=&prid=28&ref=noid&mode=0&userkey=0002400900032349&mk1=8612091369&mk2=861441693&mk3=7811859561&mk4=5066523352&mk5=7381197774 | GB | text | 128 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1744 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1992 | iexplore.exe | 130.185.144.4:80 | www.istripper.com | iomart Cloud Services Limited. | GB | unknown |
1992 | iexplore.exe | 130.185.144.4:443 | www.istripper.com | iomart Cloud Services Limited. | GB | unknown |
1992 | iexplore.exe | 192.35.177.64:80 | apps.identrust.com | IdenTrust | US | malicious |
1992 | iexplore.exe | 2.16.186.81:80 | www.download.windowsupdate.com | Akamai International B.V. | — | whitelisted |
1992 | iexplore.exe | 23.111.10.137:443 | oss.maxcdn.com | netDNA | US | unknown |
1992 | iexplore.exe | 104.25.71.114:443 | webcdn.desktopware.com | Cloudflare Inc | US | shared |
1992 | iexplore.exe | 104.16.83.55:443 | v2.zopim.com | Cloudflare Inc | US | shared |
1992 | iexplore.exe | 216.58.215.238:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
1992 | iexplore.exe | 205.185.216.42:443 | static.hotjar.com | Highwinds Network Group, Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
www.istripper.com |
| suspicious |
apps.identrust.com |
| shared |
www.download.windowsupdate.com |
| whitelisted |
webcdn.desktopware.com |
| suspicious |
oss.maxcdn.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
v2.zopim.com |
| whitelisted |
static.hotjar.com |
| whitelisted |
stats.g.doubleclick.net |
| whitelisted |
Threats
Process | Message |
|---|---|
vghd.exe | Version: 1.2.2.02
|
vghd.exe | Qt version: 5.4.2
|
vghd.exe | WebSocketSession::instance Benchmarked: 162.64 ms
|
vghd.exe | CVgMain::CVgMain Benchmarked: 214.63 ms
|
vghd.exe | Models Directories: ("C:\Users\admin\AppData\Local\vghd\models")
|
vghd.exe | QLocale default: "en_US" , system: "en_US"
|
vghd.exe | Skin Directories changed: ("C:\Users\admin\AppData\Local\vghd\data\skins/iStripper/basic")
|
vghd.exe | CardImageCache::instance Benchmarked: 37.02 ms
|
vghd.exe | network: SSL version: "OpenSSL 1.0.1j 15 Oct 2014"
|
vghd.exe | NetworkAccessManager::instance Benchmarked: 68.70 ms
|