| File name: | Rahasia Administrador 01-05.exe |
| Full analysis: | https://app.any.run/tasks/d0cc5cbb-8e54-4ca4-b91e-6d476739ea2d |
| Verdict: | Malicious activity |
| Analysis date: | November 13, 2023, 06:13:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 6C08BD41F70D51662DF04EB4ECD2F9EE |
| SHA1: | 1E75F3F14DE56B34D503CB92426957999A310F4D |
| SHA256: | D24596A87B810ED934078EB7F474973FDE52DD4866C9114BE2E53E720C118750 |
| SSDEEP: | 768:wqP0kw7+1eOYN0QLycBu99AJtV7R0GrDybt:wq8kwY4N0Qex98tV7R0GSbt |
MALICIOUS
Changes the login/logoff helper path in the registry
- Rahasia Administrador 01-05.exe (PID: 3416)
Drops the executable file immediately after the start
- Rahasia Administrador 01-05.exe (PID: 3416)
Create files in the Startup directory
- Rahasia Administrador 01-05.exe (PID: 3416)
SUSPICIOUS
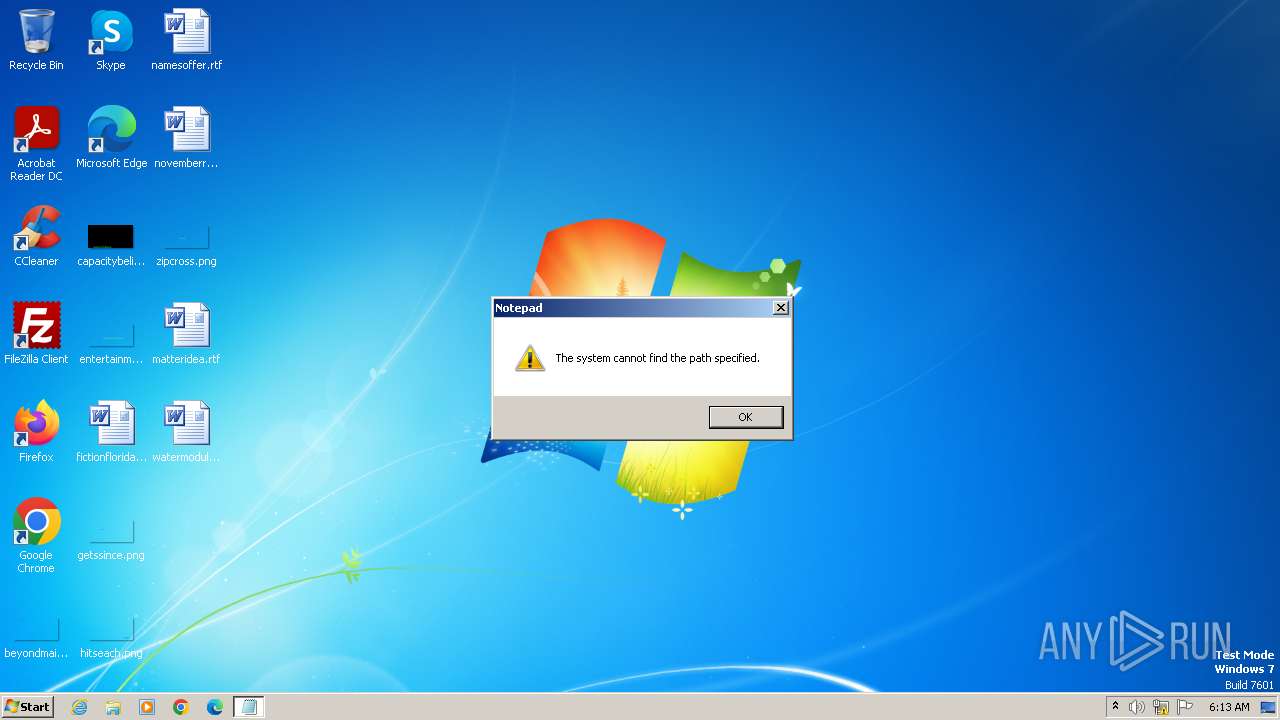
Start notepad (likely ransomware note)
- Rahasia Administrador 01-05.exe (PID: 3416)
INFO
Checks supported languages
- Rahasia Administrador 01-05.exe (PID: 3416)
Create files in a temporary directory
- Rahasia Administrador 01-05.exe (PID: 3416)
Creates files or folders in the user directory
- Rahasia Administrador 01-05.exe (PID: 3416)
Reads the machine GUID from the registry
- Rahasia Administrador 01-05.exe (PID: 3416)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Microsoft Visual Basic 6 (84.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (6.7) |
| .exe | | | Win32 Executable (generic) (4.6) |
| .exe | | | Generic Win/DOS Executable (2) |
| .exe | | | DOS Executable Generic (2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2006:06:11 12:07:15+02:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 45056 |
| InitializedDataSize: | 16384 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x183c |
| OSVersion: | 4 |
| ImageVersion: | 1.1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.1.0.1 |
| ProductVersionNumber: | 1.1.0.1 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | Take easy! I willn't harm your computer. FaTaLisTiCz_Fx #CyBeRz@Allnetwork.Org #CyBeRz@Dal.Net |
| CompanyName: | |
| FileDescription: | Microsoft Word Document |
| LegalCopyright: | © 2006 By FaTaLisTiCz_Fx |
| ProductName: | FeeLCoMz.By.FaTaLisTiCz_Fx |
| FileVersion: | 1.01.0001 |
| ProductVersion: | 1.01.0001 |
| InternalName: | FeeLCoMz_V1B |
| OriginalFileName: | FeeLCoMz_V1B.exe |
Total processes
36
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3128 | Notepad.exe C:\Windows\FeeLCoMz\Rahasia Administrador 01-05.txt | C:\Windows\System32\notepad.exe | — | Rahasia Administrador 01-05.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3416 | "C:\Users\admin\AppData\Local\Temp\Rahasia Administrador 01-05.exe" | C:\Users\admin\AppData\Local\Temp\Rahasia Administrador 01-05.exe | explorer.exe | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Microsoft Word Document Exit code: 0 Version: 1.01.0001 Modules
| |||||||||||||||
Total events
45
Read events
44
Write events
1
Delete events
0
Modification events
| (PID) Process: | (3416) Rahasia Administrador 01-05.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | Shell |
Value: explorer.exe | |||
Executable files
4
Suspicious files
1
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3416 | Rahasia Administrador 01-05.exe | C:\Users\admin\AppData\Local\Temp\~DFDCA741D97FB72DBF.TMP | binary | |
MD5:356E93CC8D29B7F0D9889A2C2C3F4D10 | SHA256:F8C63B0AAE58A22C95B8A924B555192AE0A81FAC5D3CA81ED01C9F9A39F49C0B | |||
| 3416 | Rahasia Administrador 01-05.exe | C:\Users\admin\AppData\Local\Temp\WPDNSE\Apa itu WPDNSE.exe | executable | |
MD5:6C08BD41F70D51662DF04EB4ECD2F9EE | SHA256:D24596A87B810ED934078EB7F474973FDE52DD4866C9114BE2E53E720C118750 | |||
| 3416 | Rahasia Administrador 01-05.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\Apa itu acrord32_sbx.exe | executable | |
MD5:6C08BD41F70D51662DF04EB4ECD2F9EE | SHA256:D24596A87B810ED934078EB7F474973FDE52DD4866C9114BE2E53E720C118750 | |||
| 3416 | Rahasia Administrador 01-05.exe | C:\Users\admin\AppData\Local\Temp\acrocef_low\Apa itu acrocef_low.exe | executable | |
MD5:6C08BD41F70D51662DF04EB4ECD2F9EE | SHA256:D24596A87B810ED934078EB7F474973FDE52DD4866C9114BE2E53E720C118750 | |||
| 3416 | Rahasia Administrador 01-05.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\Hardware Monitor.exe | executable | |
MD5:6C08BD41F70D51662DF04EB4ECD2F9EE | SHA256:D24596A87B810ED934078EB7F474973FDE52DD4866C9114BE2E53E720C118750 | |||
| 3416 | Rahasia Administrador 01-05.exe | C:\Users\admin\AppData\Local\VirtualStore\Windows\FeeLCoMz\Rahasia Administrador 01-05.txt | text | |
MD5:6056B1A076BBD0E814A9B570A5BEB25B | SHA256:B2B2FD042EE38BBBB47540073A4CE88E041CB838778618F90625CBC84CC2529F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |