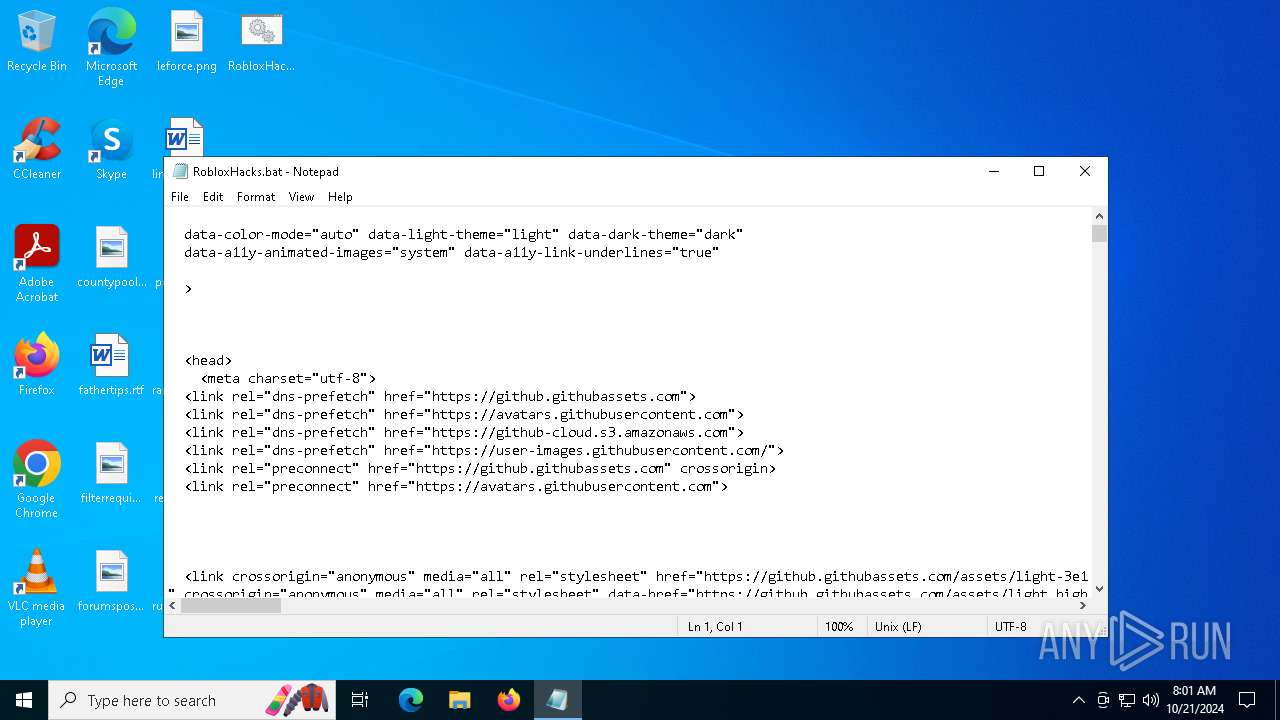
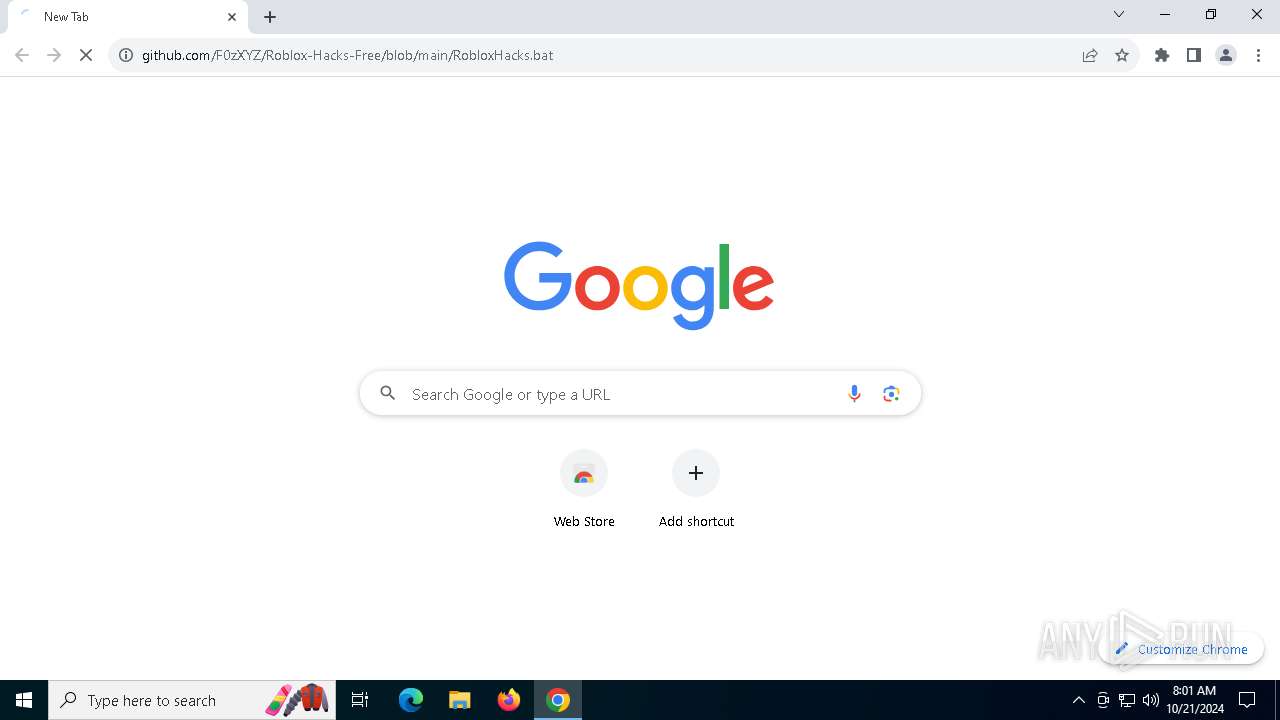
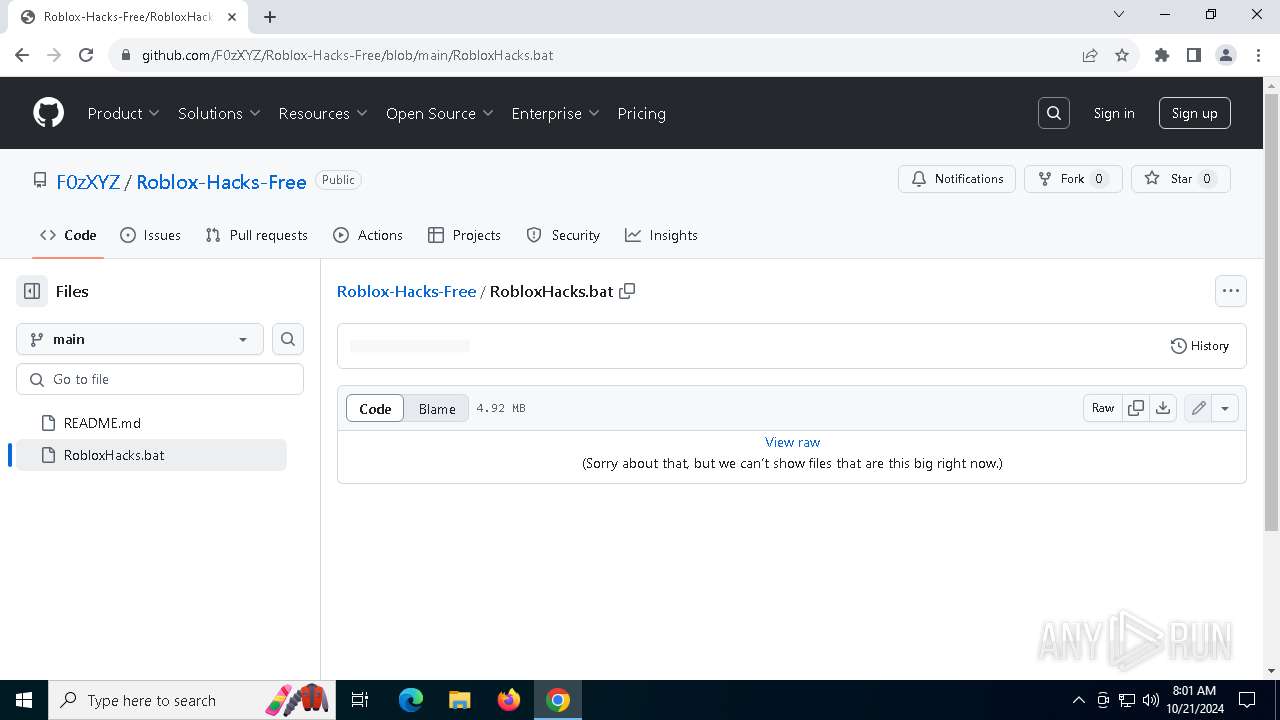
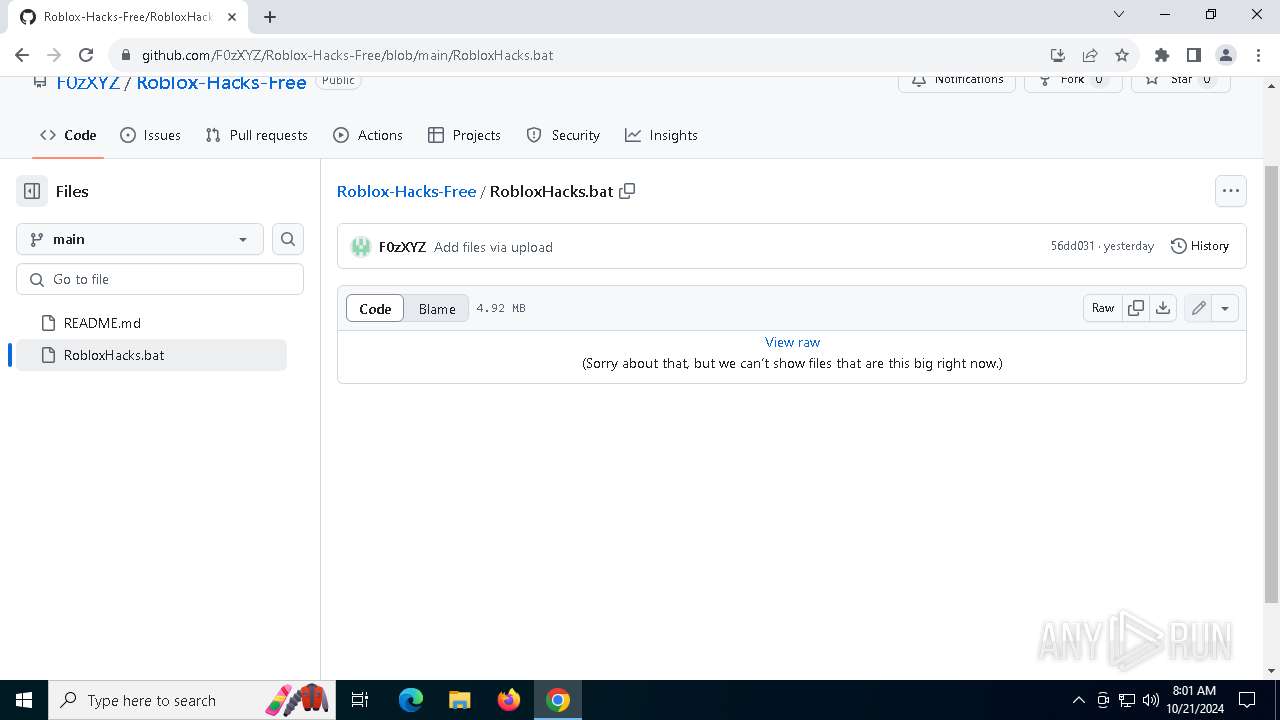
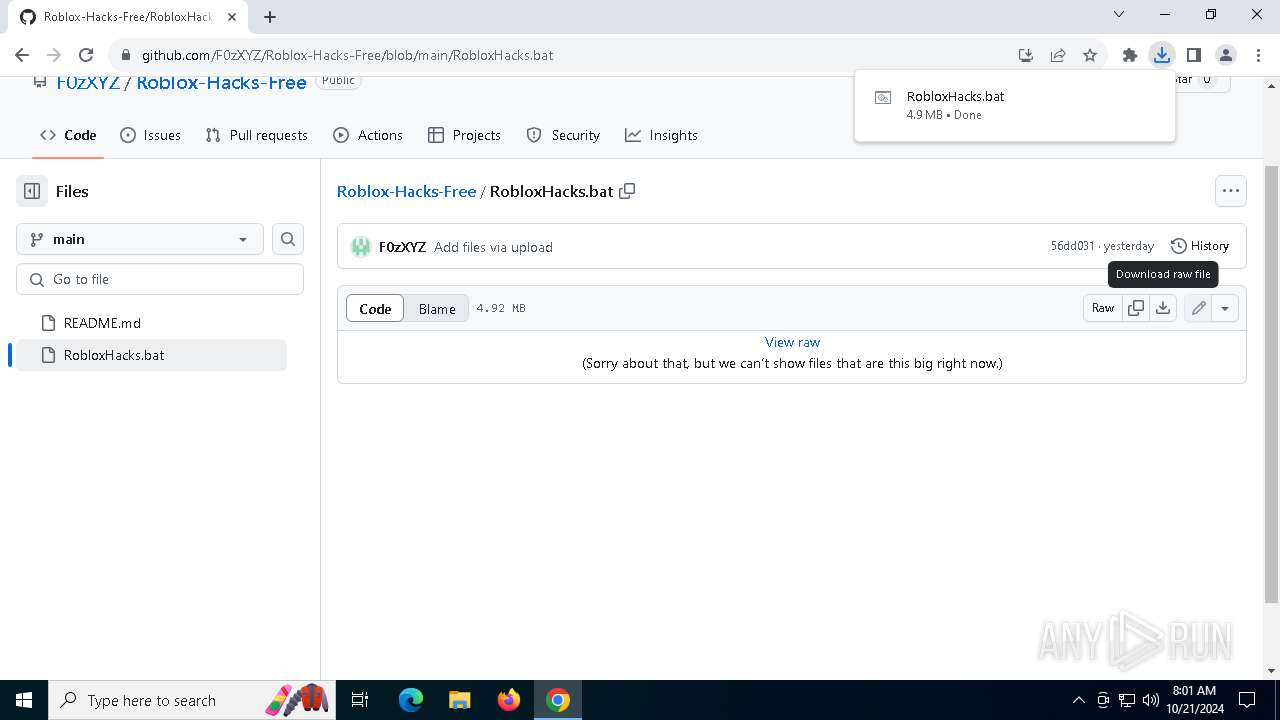
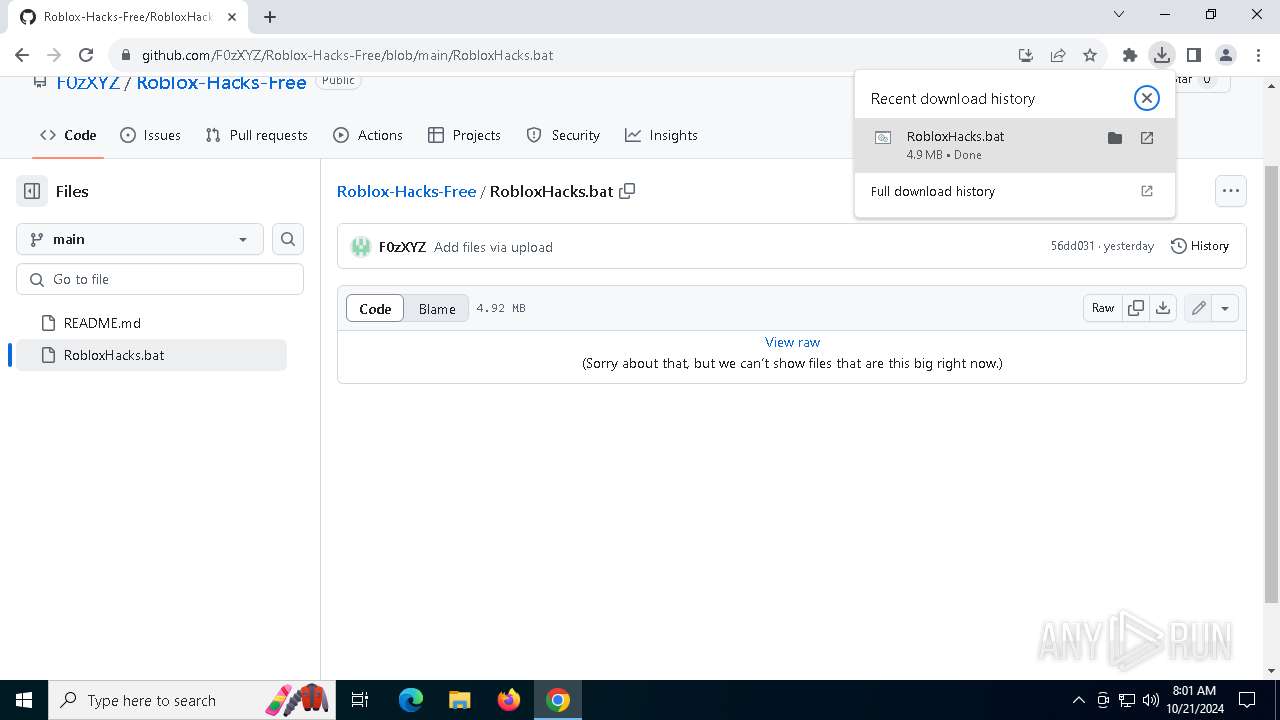
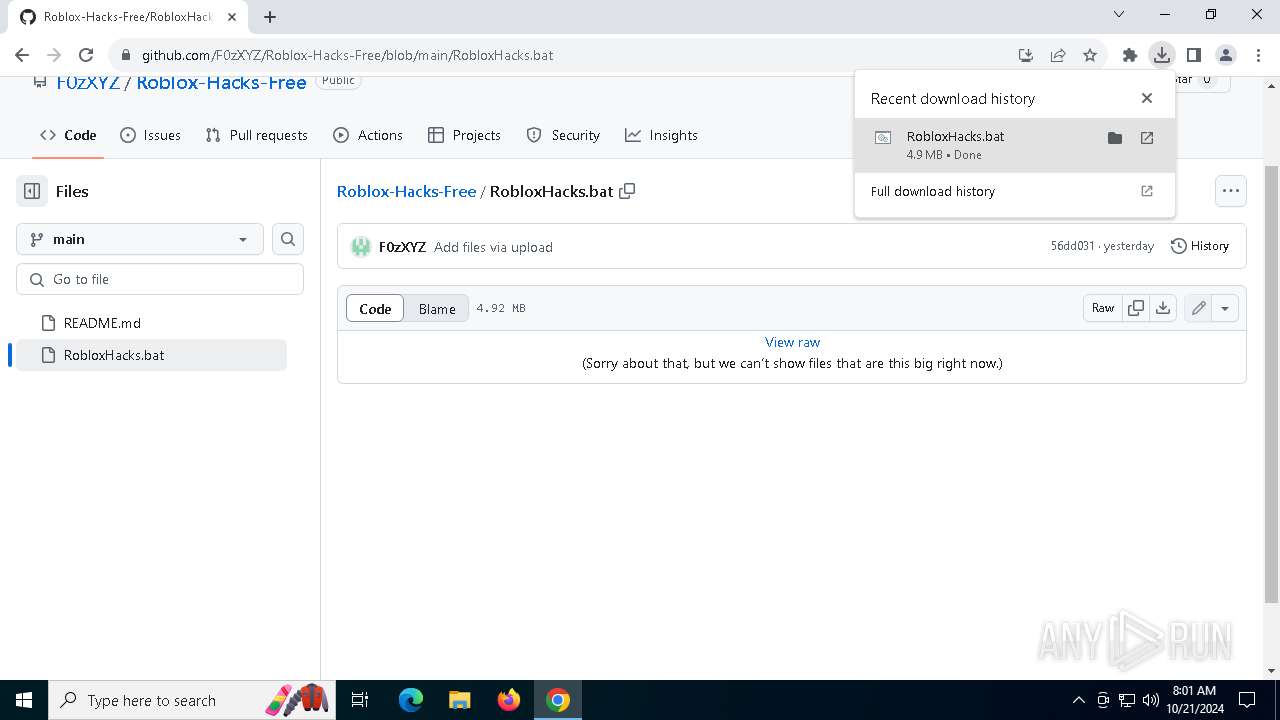
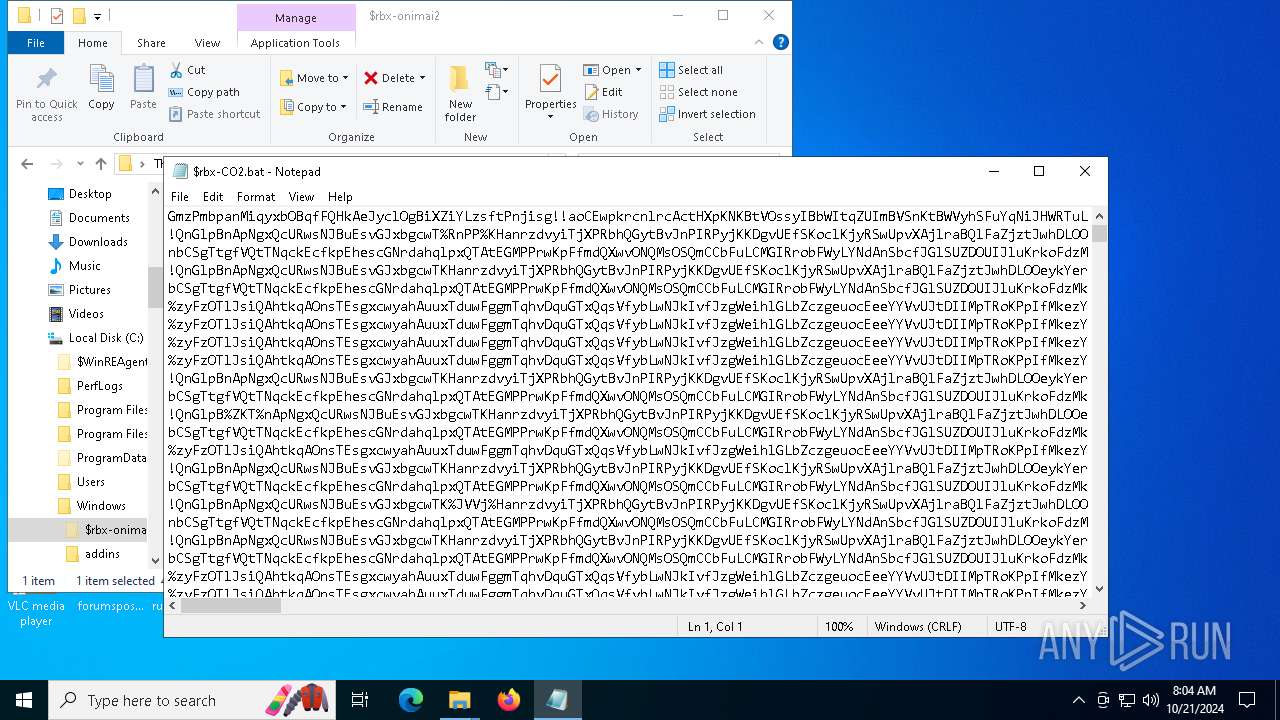
| download: | /F0zXYZ/Roblox-Hacks-Free/blob/main/RobloxHacks.bat |
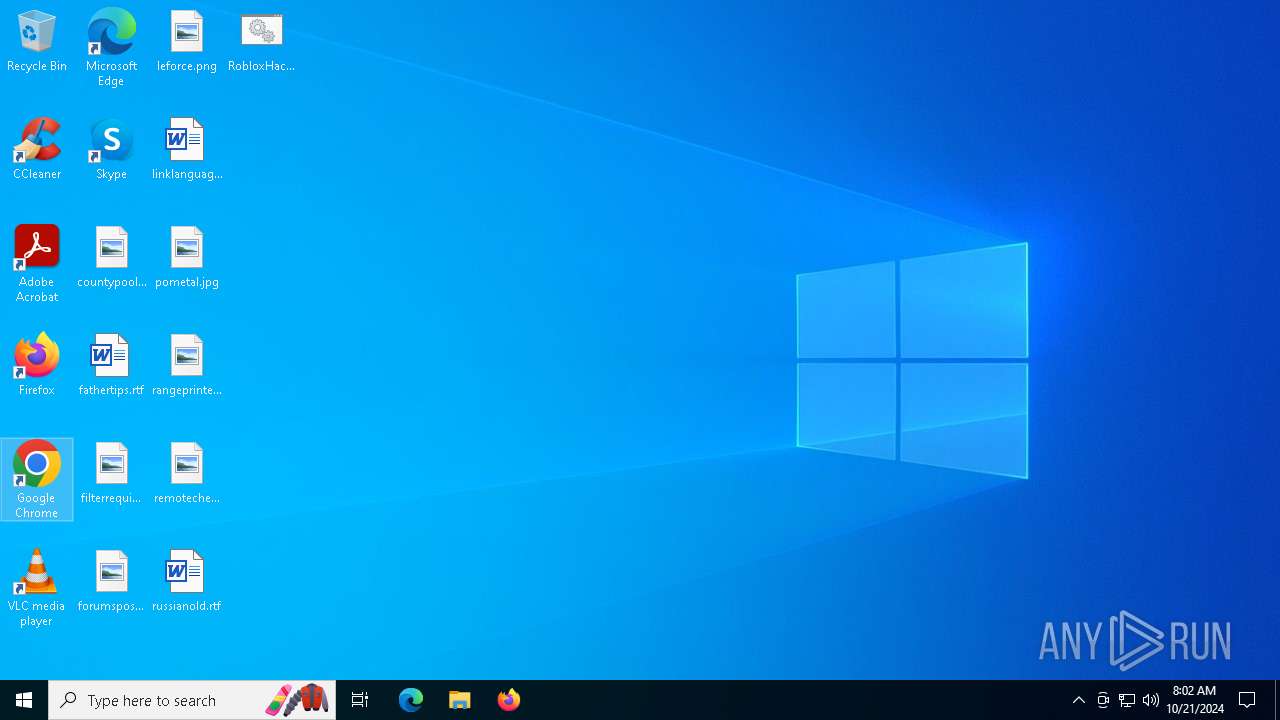
| Full analysis: | https://app.any.run/tasks/caeb286b-a0d8-416c-af02-c460632df67e |
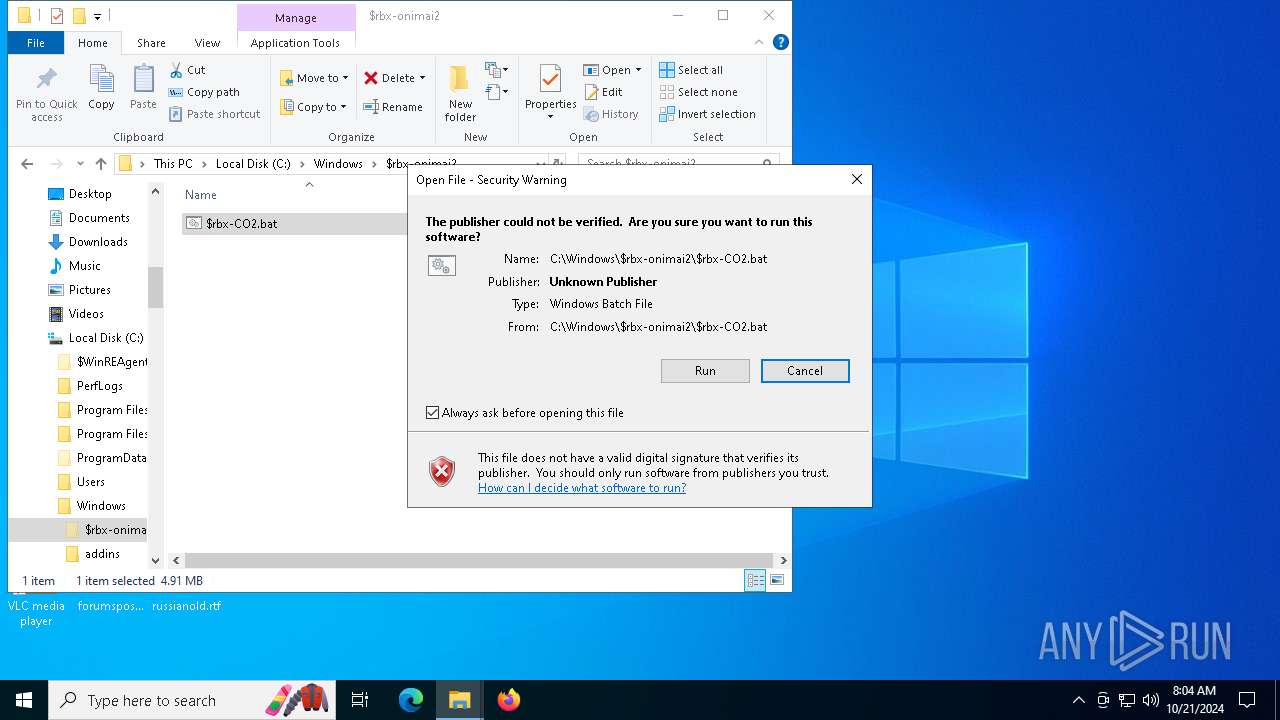
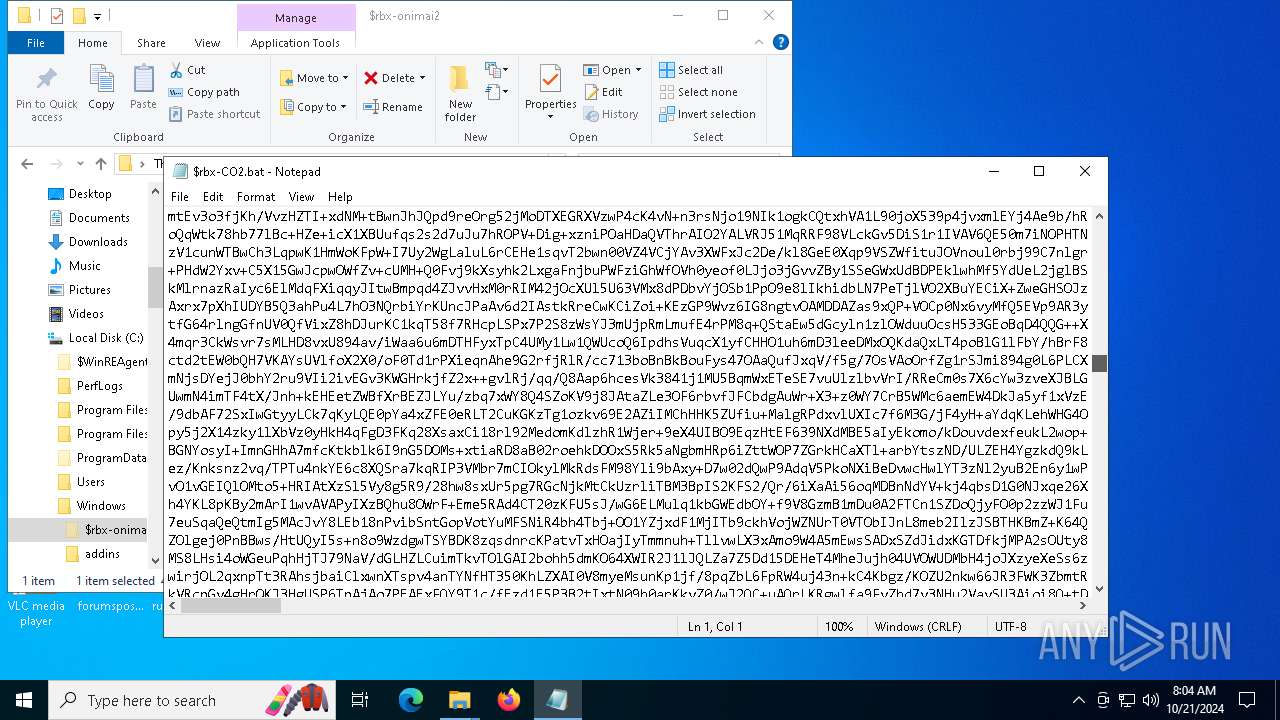
| Verdict: | Malicious activity |
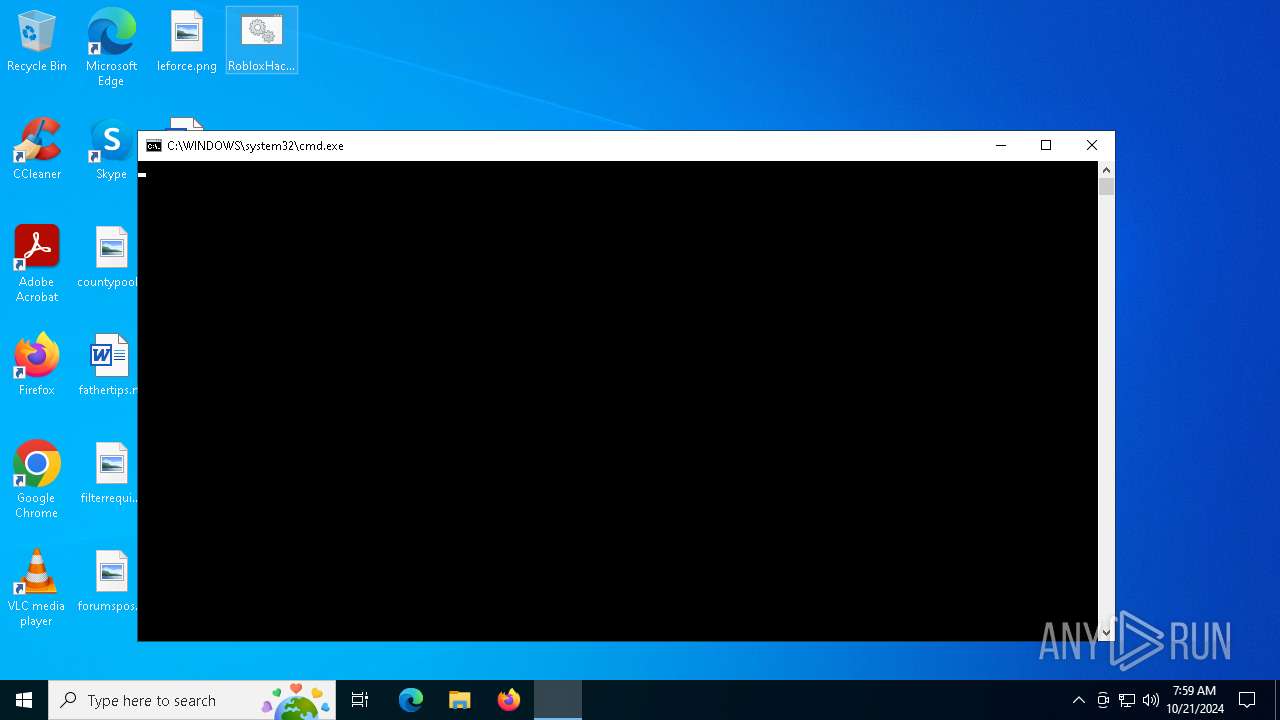
| Analysis date: | October 21, 2024, 07:59:45 |
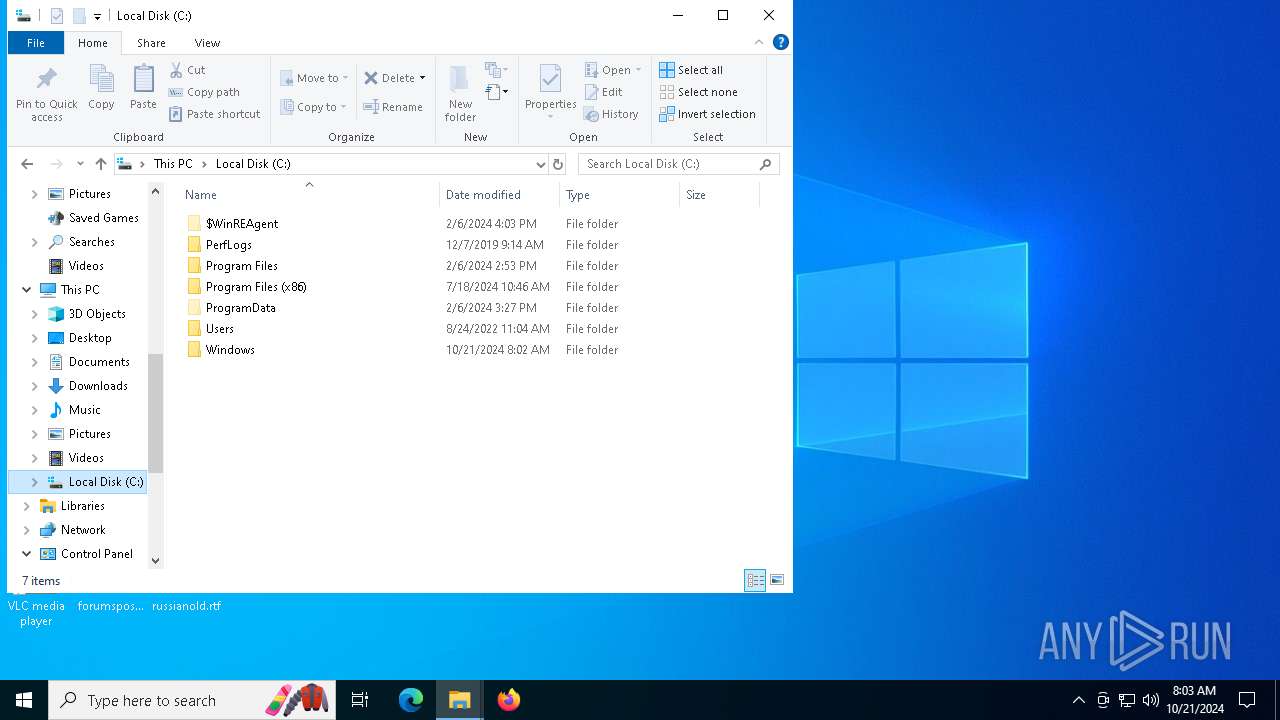
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
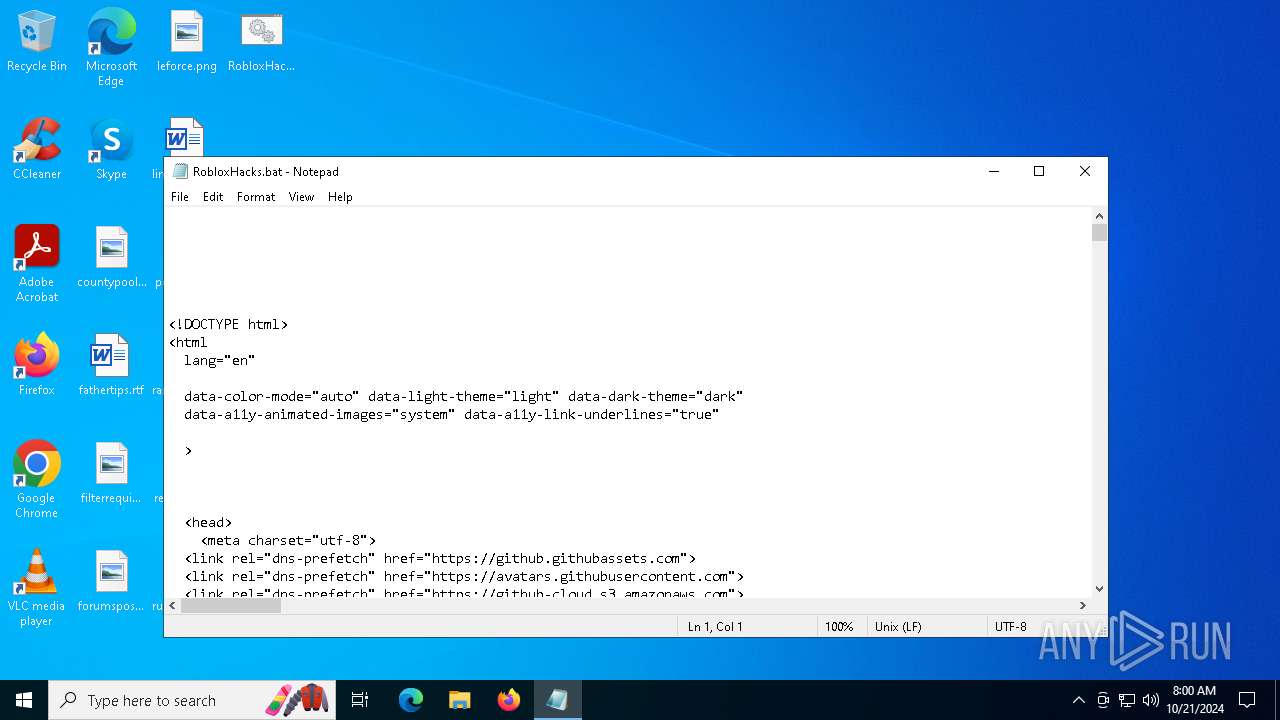
| MIME: | text/html |
| File info: | HTML document, Unicode text, UTF-8 text, with very long lines (1616) |
| MD5: | 1CC4D6D36E0AA502E02C92388E89375A |
| SHA1: | 564D5CB3873BD04CC37B9EAD8CC65ABA596817C0 |
| SHA256: | D23646314F54F14E3B32A4FEF0E89192F3359E06871DF56C05691BAF3518DFFE |
| SSDEEP: | 6144:SEoRXpOL/saqkPV9FemLtcsDSsmwF9pvZJT3CqbMrhryf65NRPaCieMjAkvCJv1V:VoRXpOL/saqkPV9FemLtcsDSsmwF9pvs |
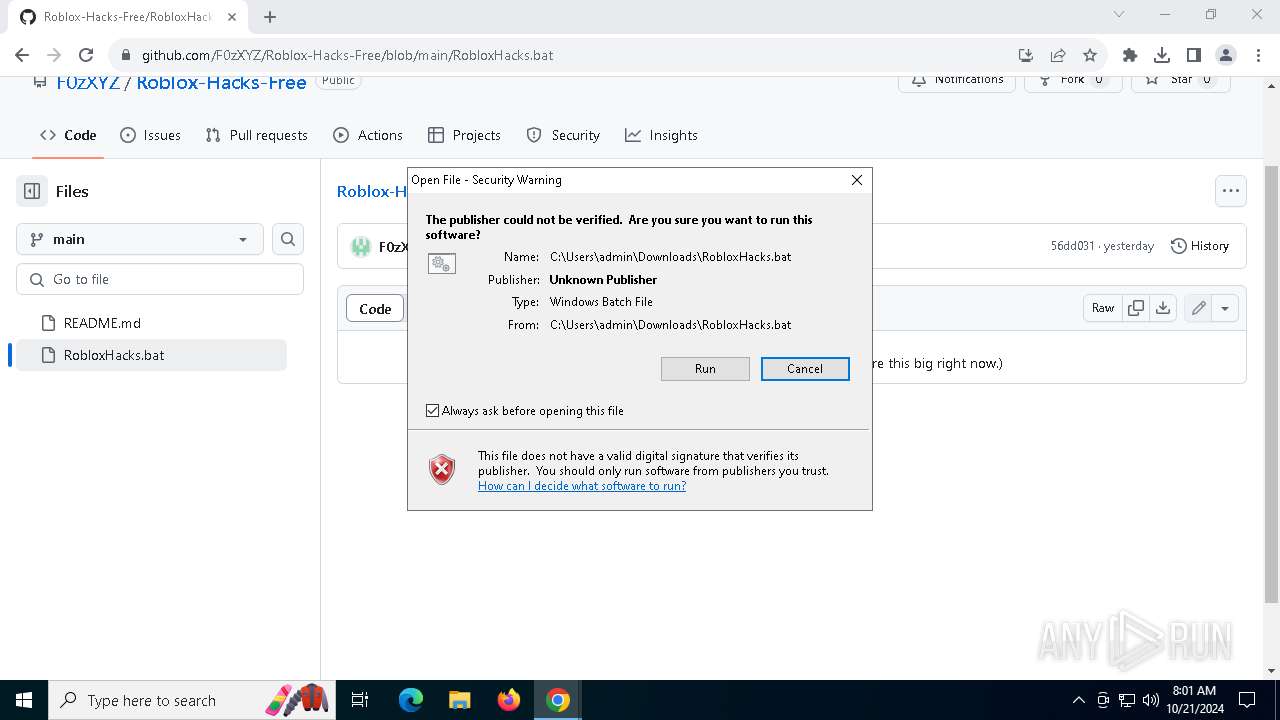
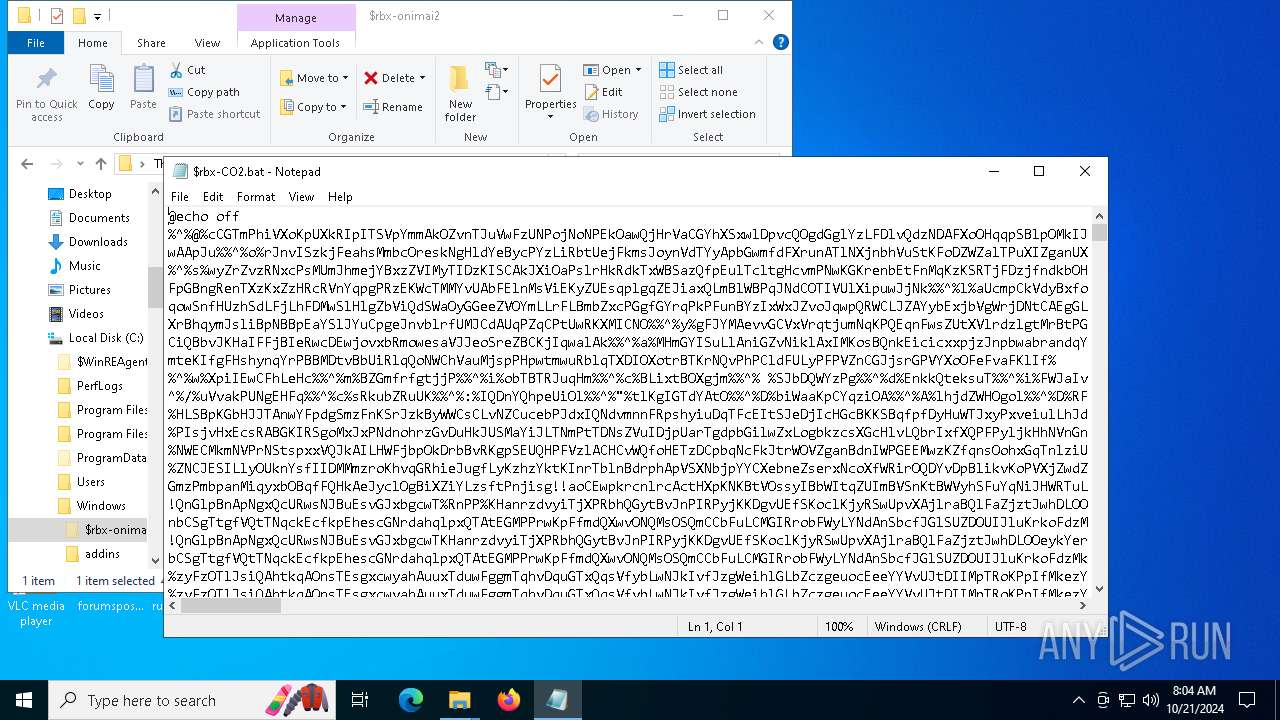
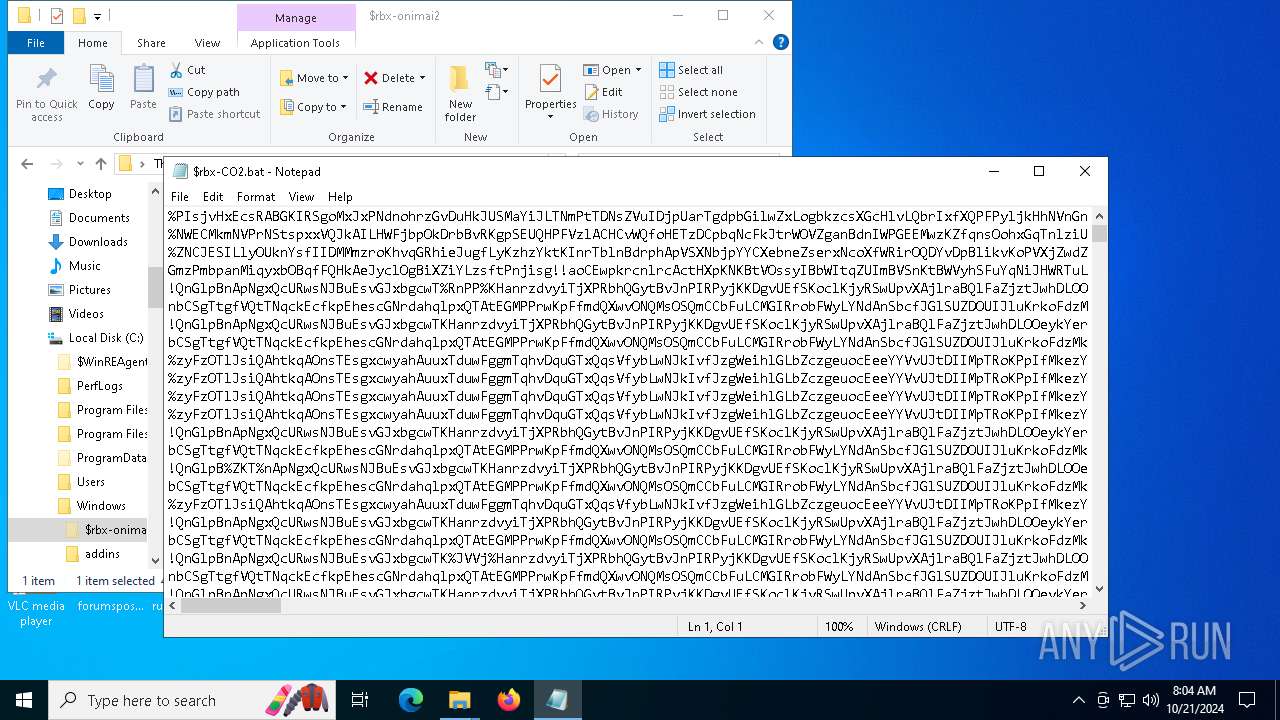
MALICIOUS
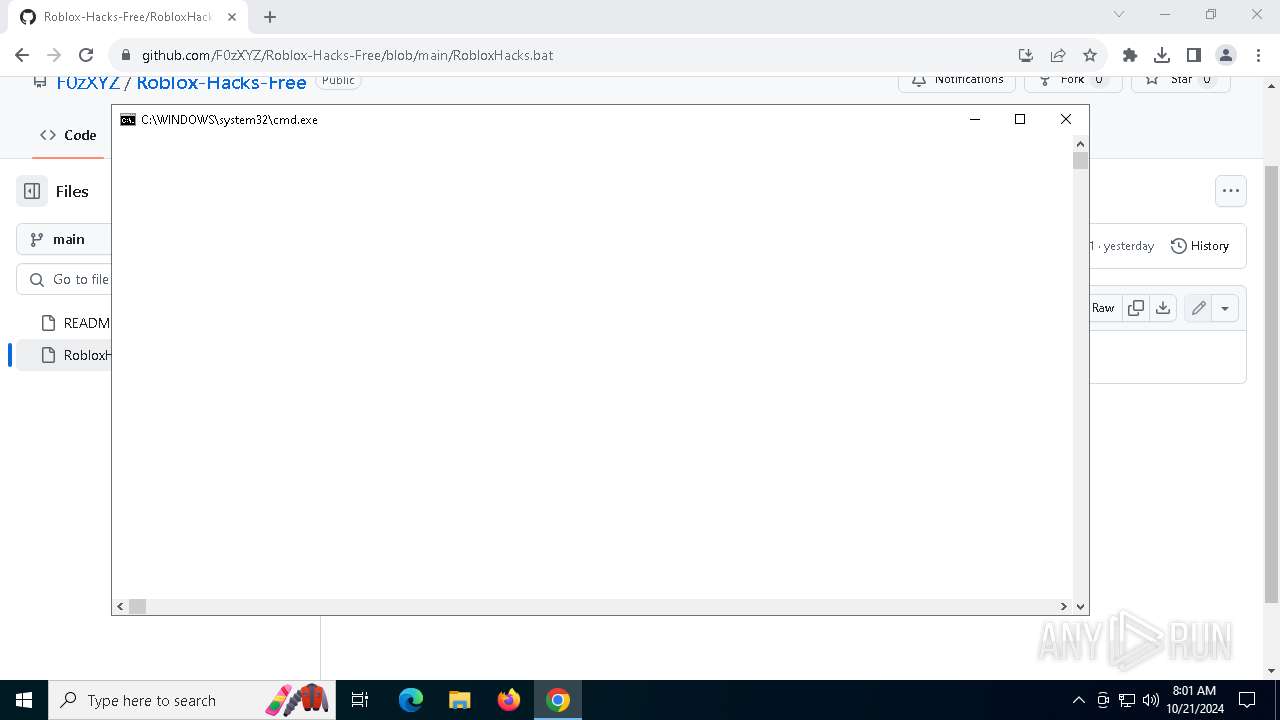
Starts CMD.EXE for commands execution
- chrome.exe (PID: 6112)
Run PowerShell with an invisible window
- powershell.exe (PID: 7112)
- powershell.exe (PID: 1068)
- powershell.exe (PID: 1712)
- powershell.exe (PID: 6136)
Known privilege escalation attack
- dllhost.exe (PID: 3728)
SUSPICIOUS
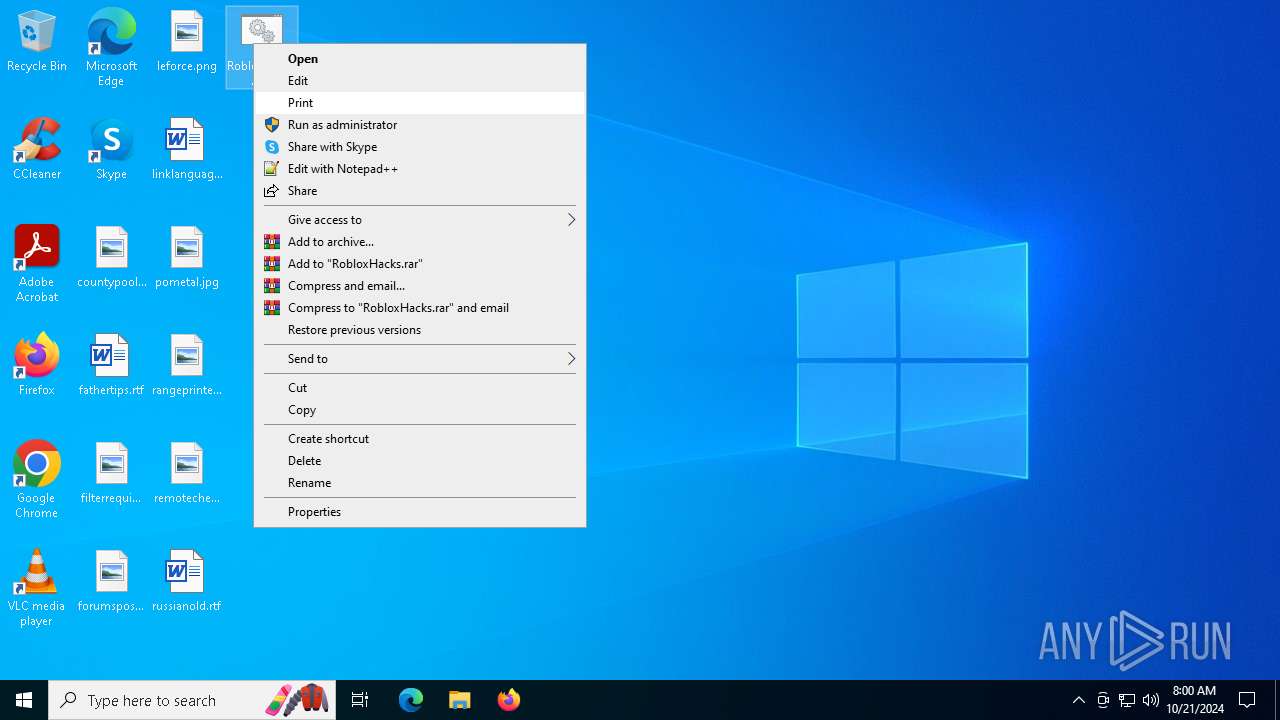
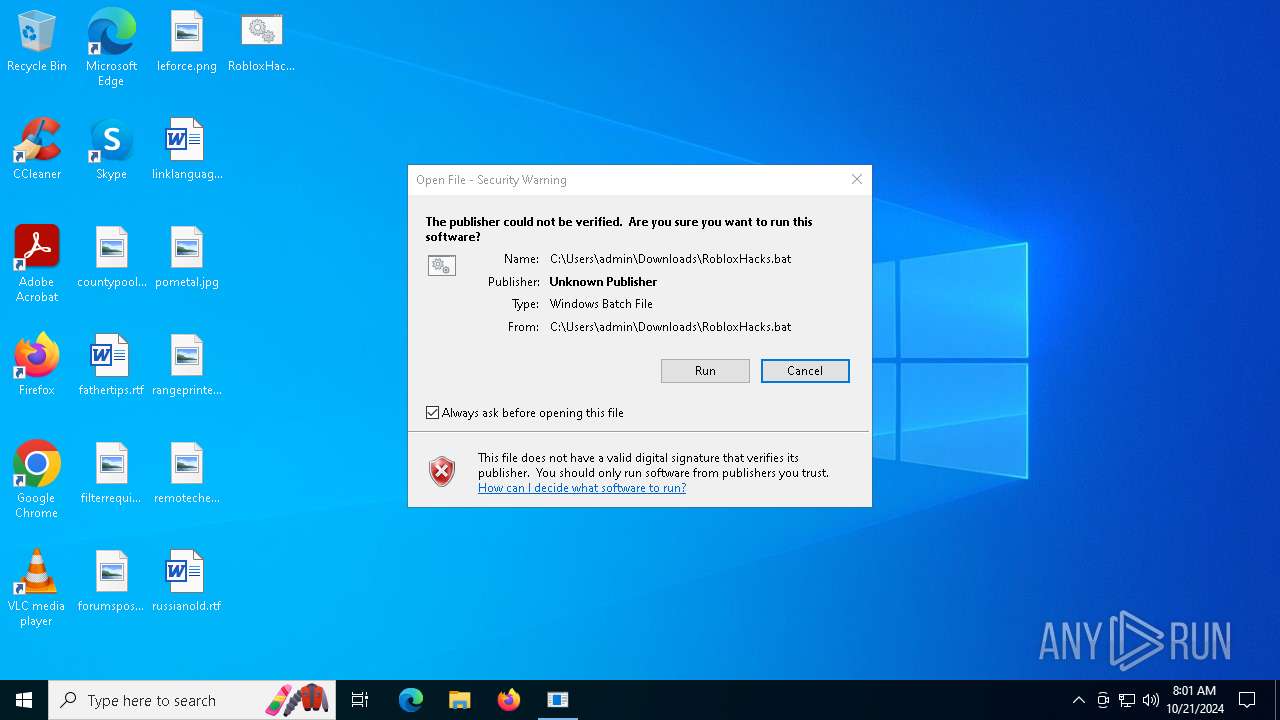
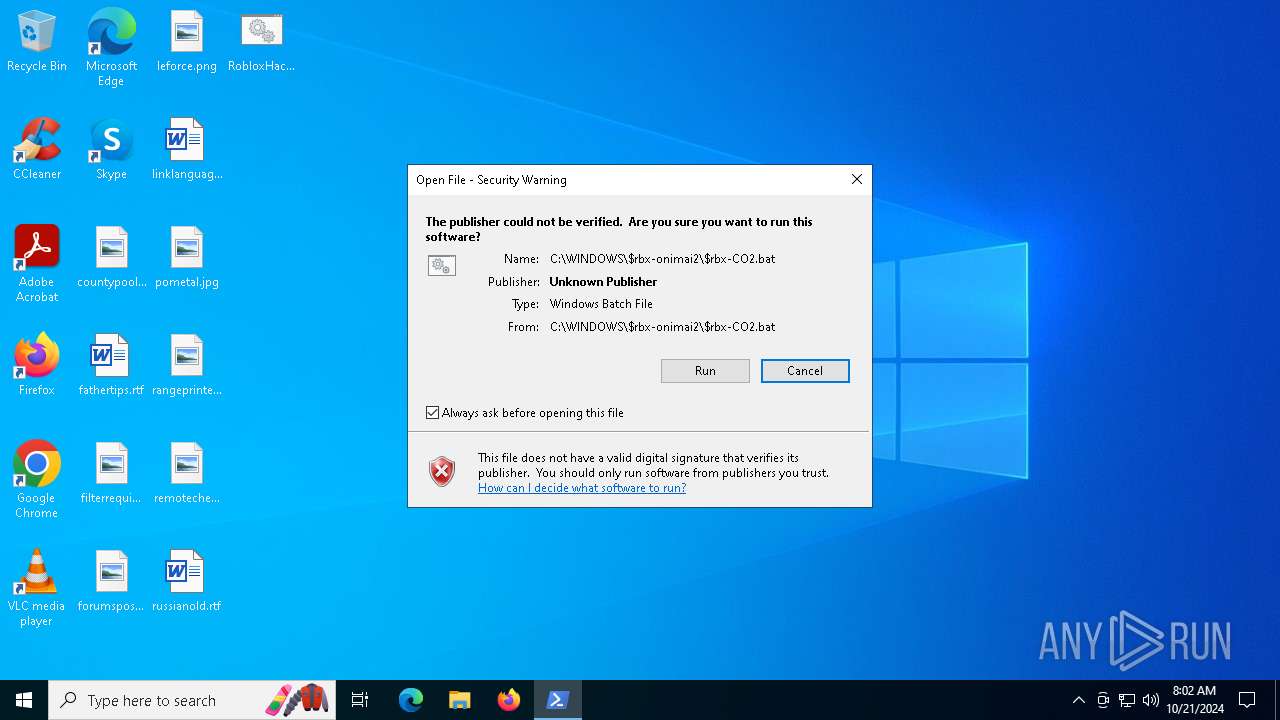
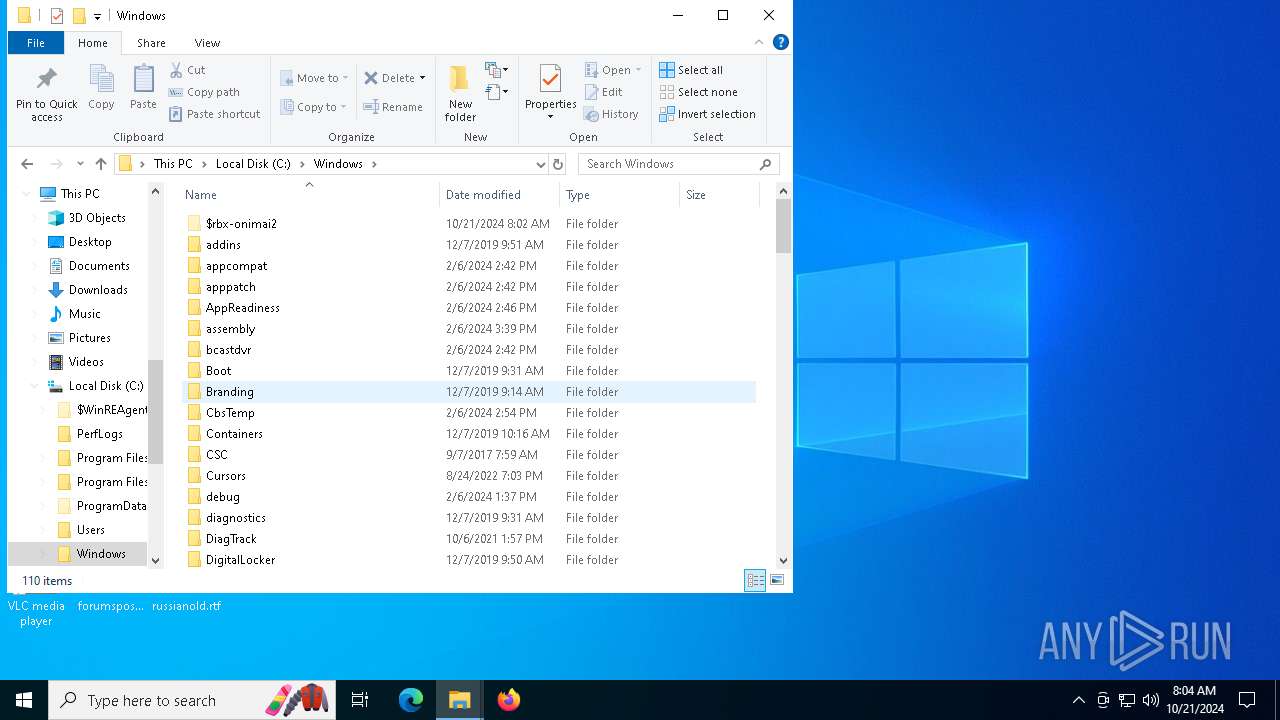
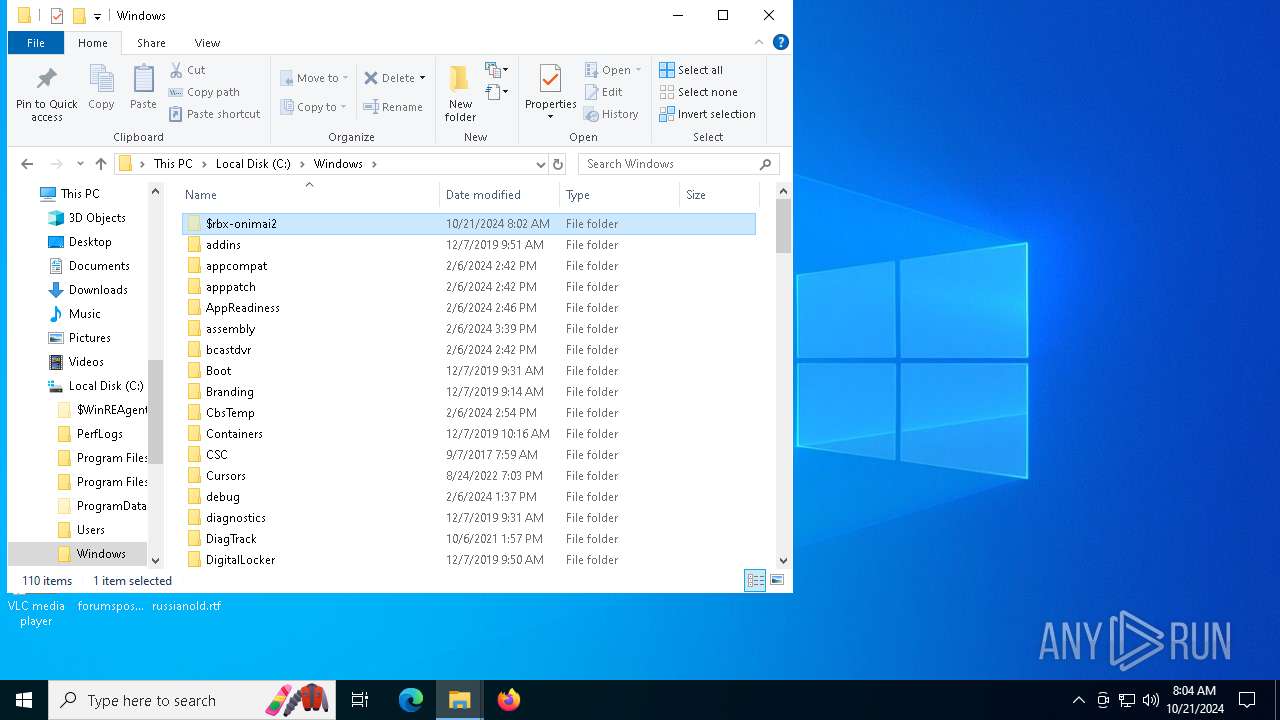
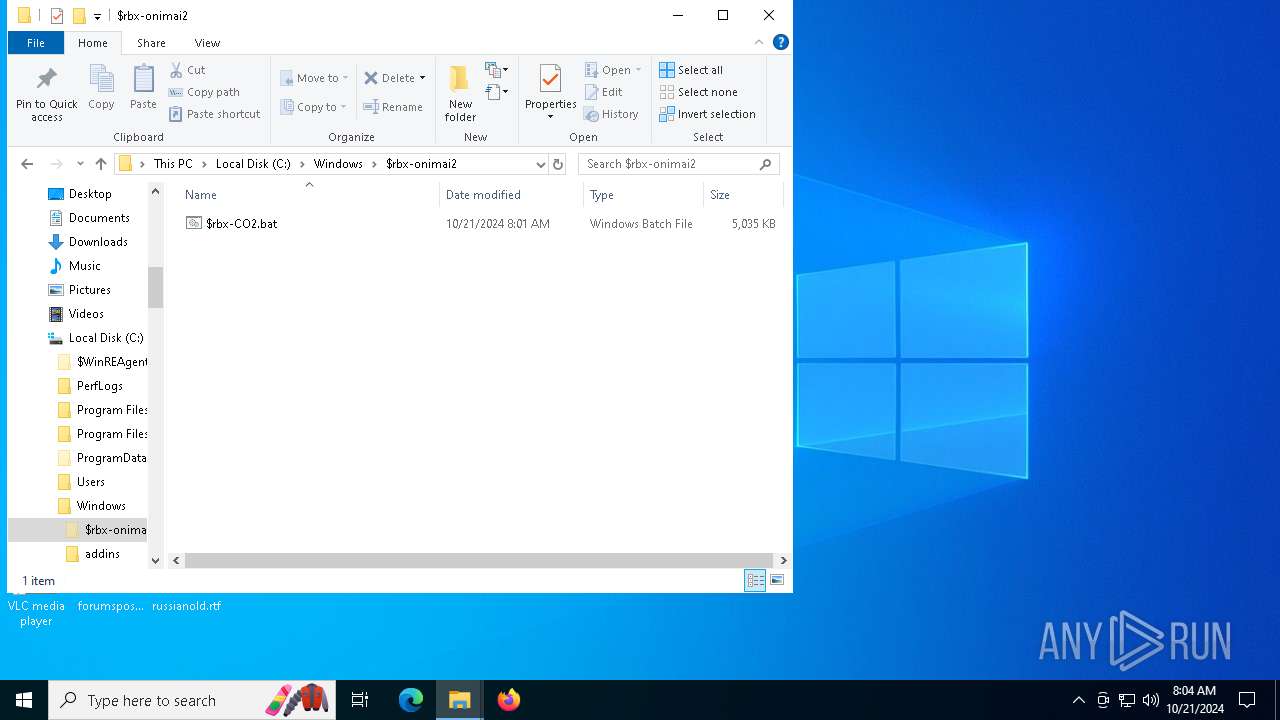
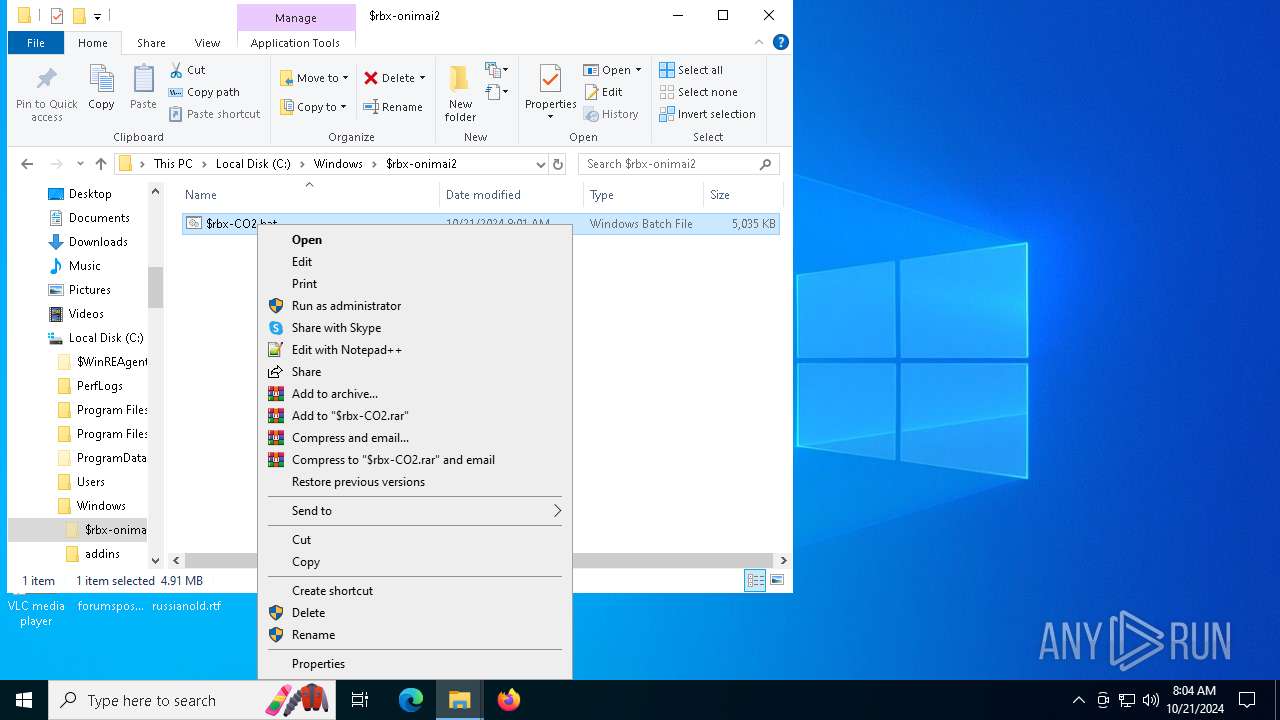
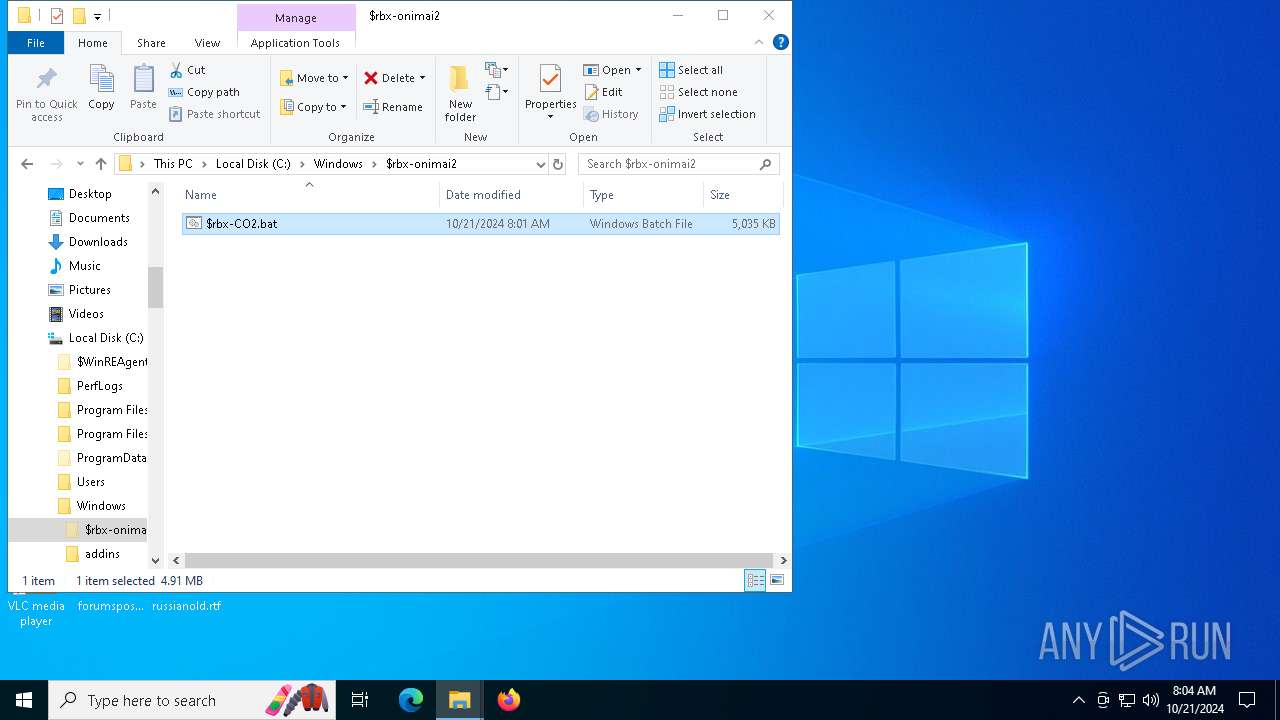
Executing commands from a ".bat" file
- chrome.exe (PID: 6112)
- cmd.exe (PID: 2484)
- dllhost.exe (PID: 3728)
- powershell.exe (PID: 1068)
- cmd.exe (PID: 5640)
- cmd.exe (PID: 6132)
- powershell.exe (PID: 1712)
- cmd.exe (PID: 6236)
Uses WMIC.EXE to obtain physical disk drive information
- cmd.exe (PID: 2484)
- cmd.exe (PID: 5640)
- cmd.exe (PID: 6236)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 2484)
- cmd.exe (PID: 5640)
- cmd.exe (PID: 6236)
Application launched itself
- cmd.exe (PID: 2484)
- cmd.exe (PID: 5640)
- cmd.exe (PID: 6132)
- cmd.exe (PID: 6236)
- powershell.exe (PID: 5184)
- powershell.exe (PID: 6240)
- powershell.exe (PID: 6424)
- powershell.exe (PID: 3732)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2484)
- dllhost.exe (PID: 3728)
- cmd.exe (PID: 5640)
- powershell.exe (PID: 1712)
- powershell.exe (PID: 1068)
- cmd.exe (PID: 6132)
- cmd.exe (PID: 6236)
Cryptography encrypted command line is found
- cmd.exe (PID: 4080)
- cmd.exe (PID: 6448)
- cmd.exe (PID: 1752)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2484)
- cmd.exe (PID: 5640)
- cmd.exe (PID: 6132)
- cmd.exe (PID: 6236)
- powershell.exe (PID: 6136)
- powershell.exe (PID: 6240)
- powershell.exe (PID: 5184)
- powershell.exe (PID: 6424)
- powershell.exe (PID: 3732)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 5756)
Connects to unusual port
- powershell.exe (PID: 6136)
INFO
Manual execution by a user
- cmd.exe (PID: 1428)
- chrome.exe (PID: 6112)
- cmd.exe (PID: 6436)
- notepad.exe (PID: 5564)
- cmd.exe (PID: 5792)
- notepad.exe (PID: 3832)
Application launched itself
- chrome.exe (PID: 6112)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
EXIF
HTML
| Title: | Roblox-Hacks-Free/RobloxHacks.bat at main · F0zXYZ/Roblox-Hacks-Free · GitHub |
|---|---|
| RoutePattern: | /:user_id/:repository/blob/*name(/*path) |
| RouteController: | blob |
| RouteAction: | show |
| CurrentCatalogServiceHash: | f3abb0cc802f3d7b95fc8762b94bdcb13bf39634c40c357301c4aa1d67a256fb |
| RequestId: | FAD2:BC3C9:294821F:2A57898:671609F1 |
| HtmlSafeNonce: | 4e602f29dedd96705329737145596c923ccf383541fb4110855b5a15b8279f24 |
| VisitorPayload: | eyJyZWZlcnJlciI6IiIsInJlcXVlc3RfaWQiOiJGQUQyOkJDM0M5OjI5NDgyMUY6MkE1Nzg5ODo2NzE2MDlGMSIsInZpc2l0b3JfaWQiOiIyMDA2MjQ0NzE1MzUyNDI2OTkzIiwicmVnaW9uX2VkZ2UiOiJmcmEiLCJyZWdpb25fcmVuZGVyIjoiZnJhIn0= |
| VisitorHmac: | 54fe330e8bb4d4321c9b94918d2a09dda190f51c54e56cac4583338295281df3 |
| HovercardSubjectTag: | repository:875549369 |
| GithubKeyboardShortcuts: | repository,source-code,file-tree,copilot |
| GoogleSiteVerification: | Apib7-x98H0j5cPqHWwSMm6dNU4GmODRoqxLiDzdx9I |
| OctolyticsUrl: | https://collector.github.com/github/collect |
| AnalyticsLocation: | /<user-name>/<repo-name>/blob/show |
| UserLogin: | - |
| Viewport: | width=device-width |
| Description: | Free Roblox Haxxx. Contribute to F0zXYZ/Roblox-Hacks-Free development by creating an account on GitHub. |
| AppleItunesApp: | app-id=1477376905, app-argument=https://github.com/F0zXYZ/Roblox-Hacks-Free/blob/main/RobloxHacks.bat |
| TwitterImage: | https://opengraph.githubassets.com/9004769dcad31d0473729631bc20986e6182db842384acabaca9c6fb80887919/F0zXYZ/Roblox-Hacks-Free |
| TwitterSite: | @github |
| TwitterCard: | summary_large_image |
| TwitterTitle: | Roblox-Hacks-Free/RobloxHacks.bat at main · F0zXYZ/Roblox-Hacks-Free |
| TwitterDescription: | Free Roblox Haxxx. Contribute to F0zXYZ/Roblox-Hacks-Free development by creating an account on GitHub. |
| Hostname: | github.com |
| ExpectedHostname: | github.com |
| HTTPEquivXPjaxVersion: | bcf905d69f19d2a72d57a75e002a94caaec7c0f8693d085b82661ecf5efa8949 |
| HTTPEquivXPjaxCspVersion: | ace39c3b6632770952207593607e6e0be0db363435a8b877b1f96abe6430f345 |
| HTTPEquivXPjaxCssVersion: | 6799ca7c5d90d335a555cb049e18e95092201b013b9dc658bb3fa3b68c57bc90 |
| HTTPEquivXPjaxJsVersion: | 7119cbe4d8959626c984206cf852626b527098d38e1a72a9493b7299e225b1b7 |
| TurboCacheControl: | no-cache |
| GoImport: | github.com/F0zXYZ/Roblox-Hacks-Free git https://github.com/F0zXYZ/Roblox-Hacks-Free.git |
| OctolyticsDimensionUser_id: | 185640068 |
| OctolyticsDimensionUser_login: | F0zXYZ |
| OctolyticsDimensionRepository_id: | 875549369 |
| OctolyticsDimensionRepository_nwo: | F0zXYZ/Roblox-Hacks-Free |
| OctolyticsDimensionRepository_public: | |
| OctolyticsDimensionRepository_is_fork: | - |
| OctolyticsDimensionRepository_network_root_id: | 875549369 |
| OctolyticsDimensionRepository_network_root_nwo: | F0zXYZ/Roblox-Hacks-Free |
| TurboBodyClasses: | logged-out env-production page-responsive |
| BrowserStatsUrl: | https://api.github.com/_private/browser/stats |
| BrowserErrorsUrl: | https://api.github.com/_private/browser/errors |
| ThemeColor: | #1e2327 |
| ColorScheme: | light dark |
Total processes
211
Monitored processes
77
Malicious processes
10
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 916 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\RobloxHacks.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 255 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1068 | powershell.exe -WindowStyle Hidden | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 4294967295 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1084 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5860 --field-trial-handle=1952,i,184719081787906486,4340828762377885096,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1112 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1248 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1428 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\RobloxHacks.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1568 | findstr /i /c:"QEMU HARDDISK" /c:"DADY HARDDISK" /c:"WDS100T2B0A" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1580 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1712 | powershell.exe -WindowStyle Hidden | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4768 --field-trial-handle=1952,i,184719081787906486,4340828762377885096,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
27 016
Read events
26 997
Write events
17
Delete events
2
Modification events
| (PID) Process: | (6112) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6112) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6112) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6112) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6112) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6112) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1F |
Value: 1 | |||
| (PID) Process: | (2196) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000EEA7546E8F23DB01 | |||
| (PID) Process: | (6112) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (6112) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\PreferenceMACs\Default\extensions.settings |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6112) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | GoogleChromeAutoLaunch_A822CA3D40D4B8944864CFEA751D8D57 |
Value: | |||
Executable files
0
Suspicious files
163
Text files
38
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6112 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RFa0713.TMP | — | |
MD5:— | SHA256:— | |||
| 6112 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6112 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RFa0713.TMP | — | |
MD5:— | SHA256:— | |||
| 6112 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6112 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RFa0713.TMP | — | |
MD5:— | SHA256:— | |||
| 6112 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6112 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RFa0713.TMP | — | |
MD5:— | SHA256:— | |||
| 6112 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RFa0723.TMP | — | |
MD5:— | SHA256:— | |||
| 6112 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6112 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
105
DNS requests
61
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 973 b | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 973 b | whitelisted |
5784 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 312 b | whitelisted |
3740 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
4208 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | NL | binary | 419 b | whitelisted |
4208 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | NL | binary | 408 b | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | US | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.23.209.160:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5488 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4432 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
4432 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |