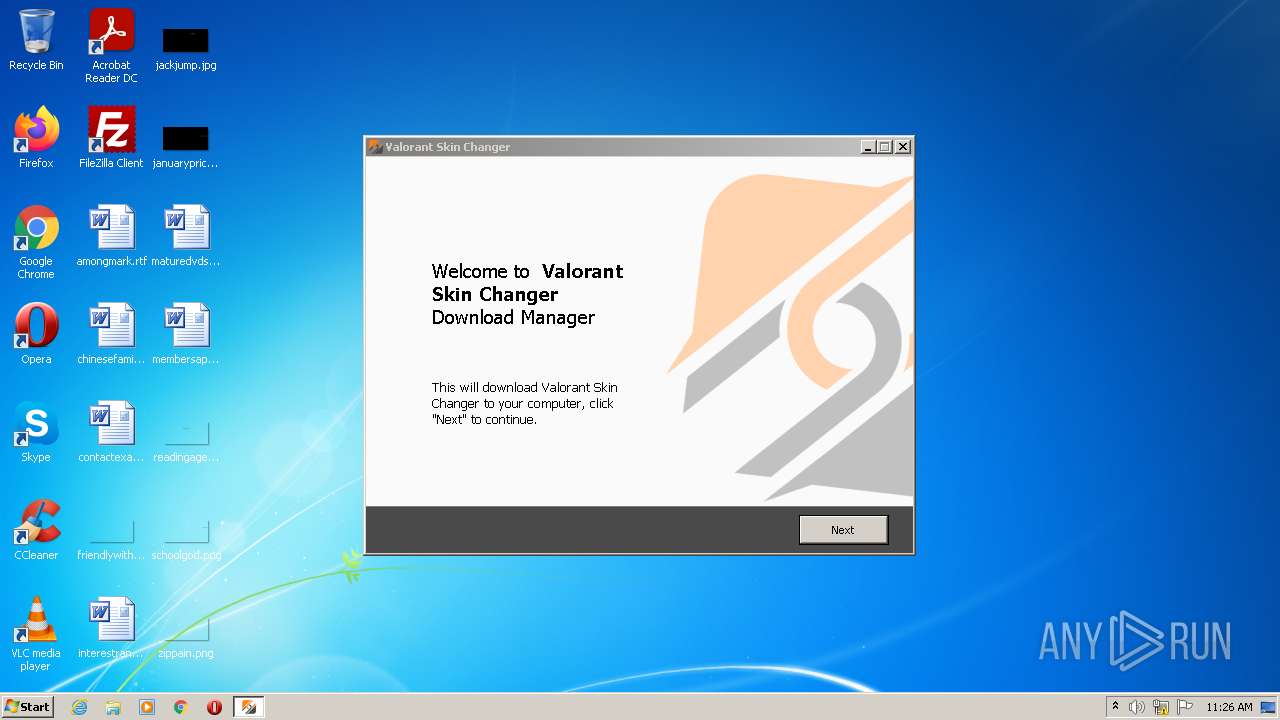
| File name: | Valorant Skin Changer - Linkvertise Downloader_n-Kh0R1.exe |
| Full analysis: | https://app.any.run/tasks/e9100e39-5ae0-45c8-9052-70822396d80d |
| Verdict: | Malicious activity |
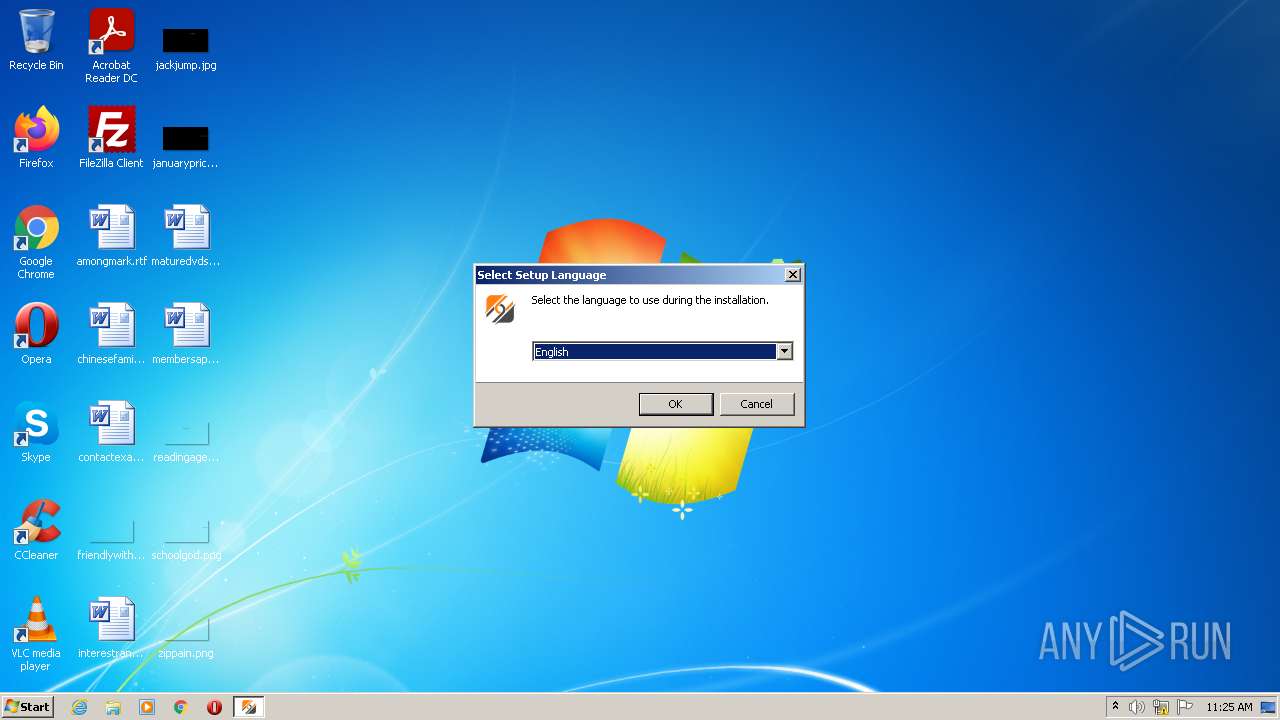
| Analysis date: | February 12, 2022, 11:25:48 |
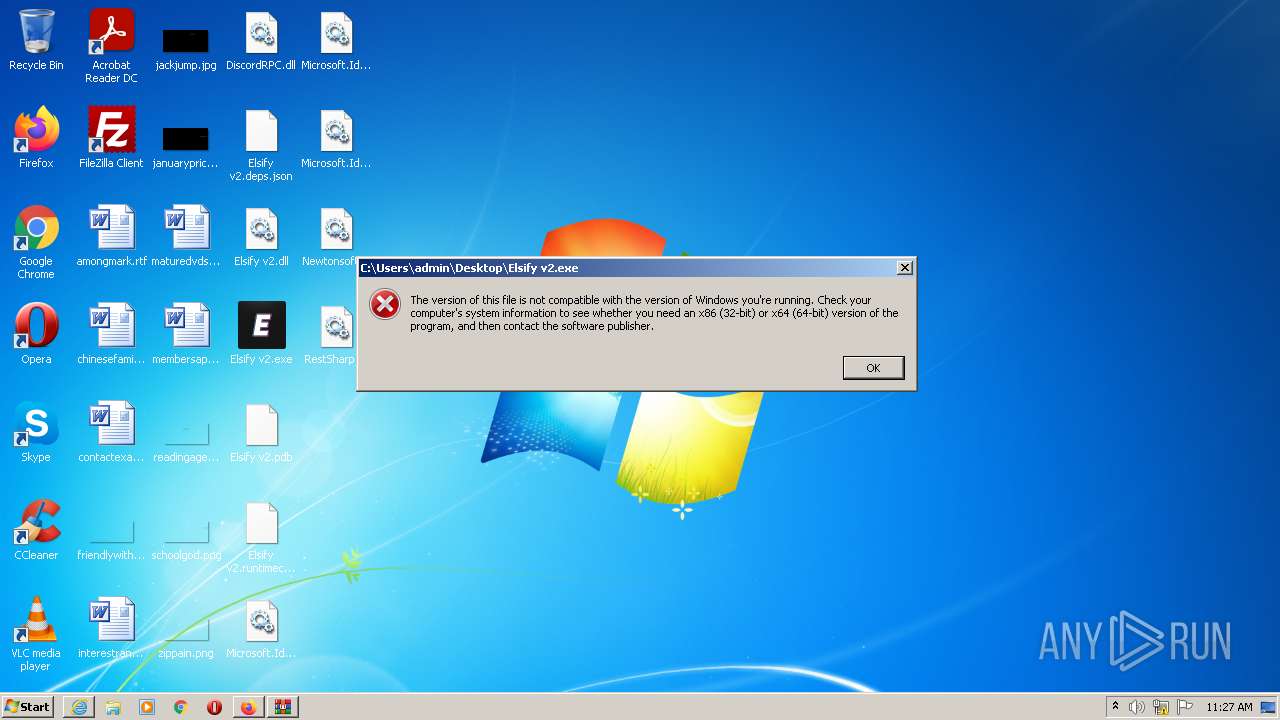
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 9D1287D3789E1BC6306A90CB12113240 |
| SHA1: | 6724BDD5C3A975B0879C5A268B19F17FF551BA63 |
| SHA256: | D22568B1989127178B13ABE5B726BF3886B5194203F6E97CCBB171D8F928D41E |
| SSDEEP: | 49152:6qe3f6a0zD7+H98AHaCfu6OWHCL+WuTmuKwEg:TSiBD7E9vBuTWHCK5NKXg |
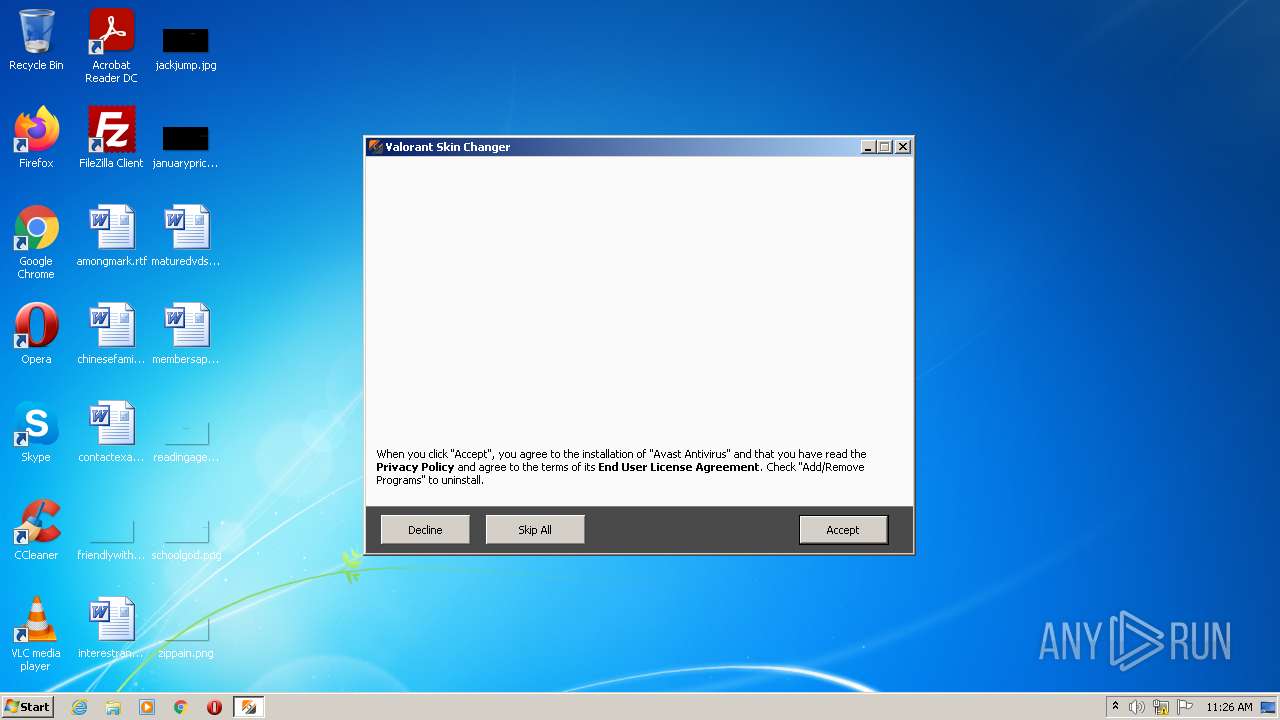
MALICIOUS
Drops executable file immediately after starts
- Valorant Skin Changer - Linkvertise Downloader_n-Kh0R1.exe (PID: 3436)
- Valorant Skin Changer - Linkvertise Downloader_n-Kh0R1.exe (PID: 2732)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 1256)
SUSPICIOUS
Checks supported languages
- Valorant Skin Changer - Linkvertise Downloader_n-Kh0R1.exe (PID: 3436)
- Valorant Skin Changer - Linkvertise Downloader_n-Kh0R1.tmp (PID: 3588)
- Valorant Skin Changer - Linkvertise Downloader_n-Kh0R1.exe (PID: 2732)
- Valorant Skin Changer - Linkvertise Downloader_n-Kh0R1.tmp (PID: 2456)
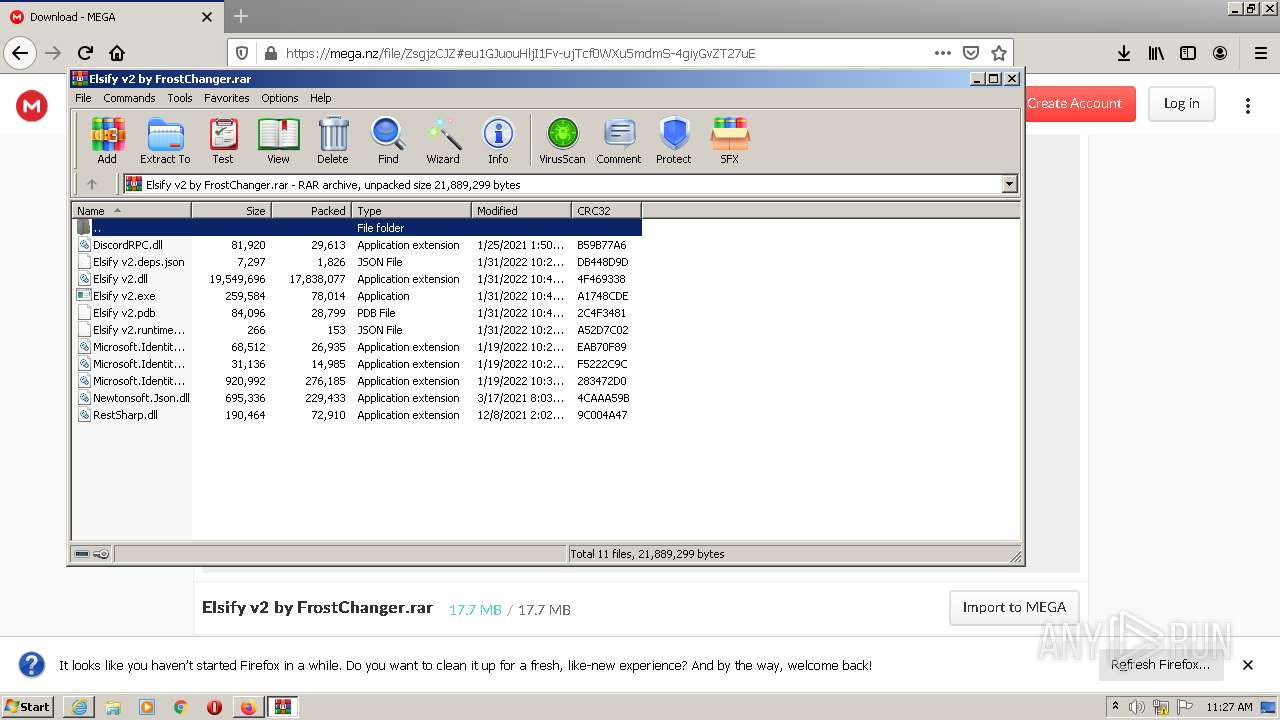
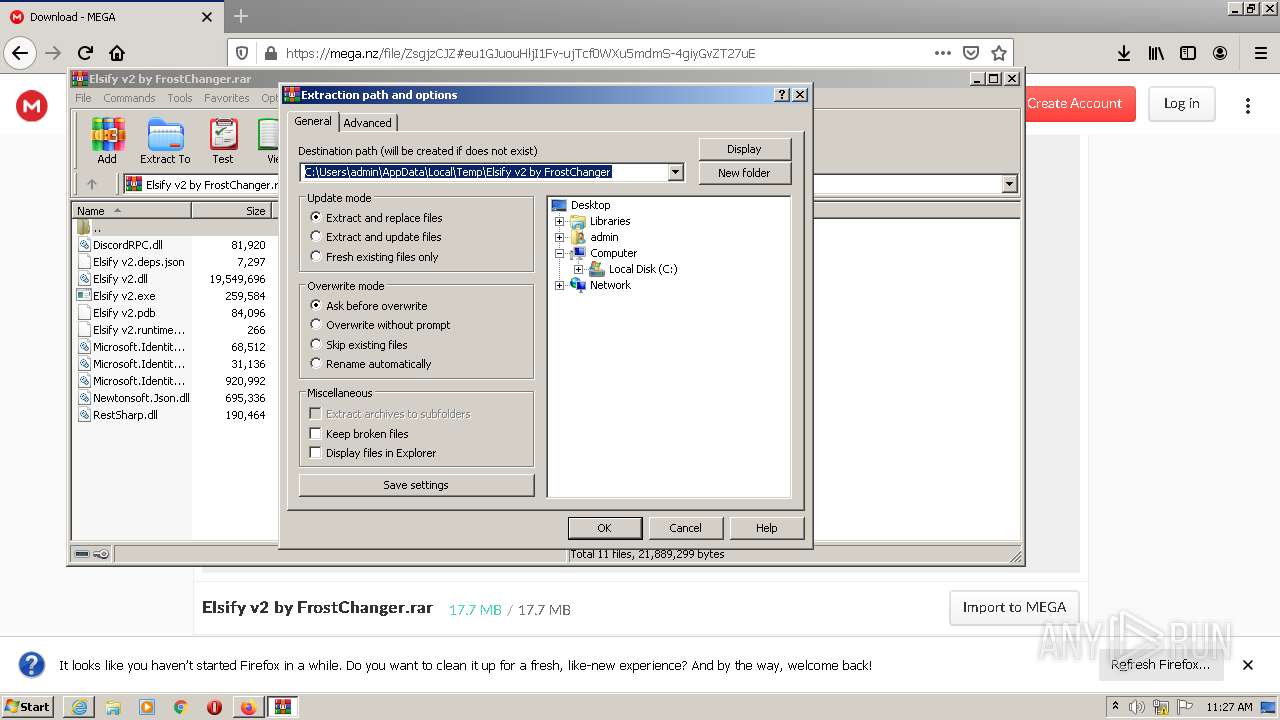
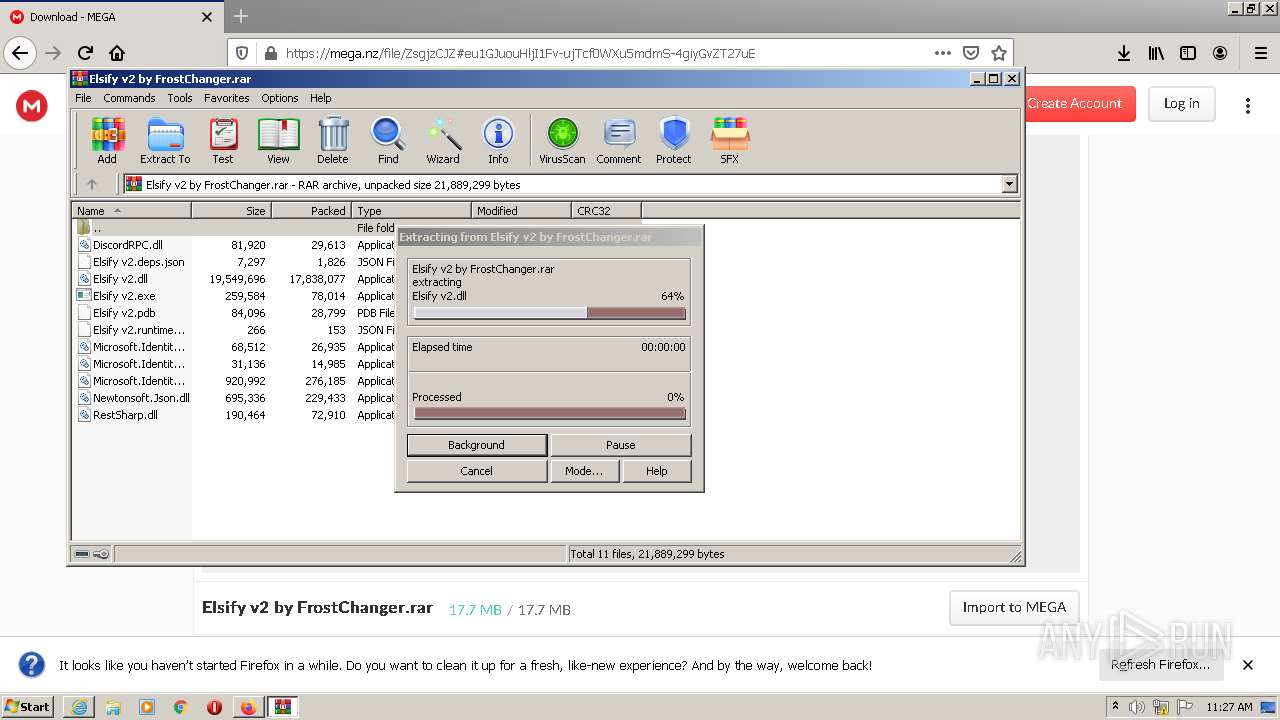
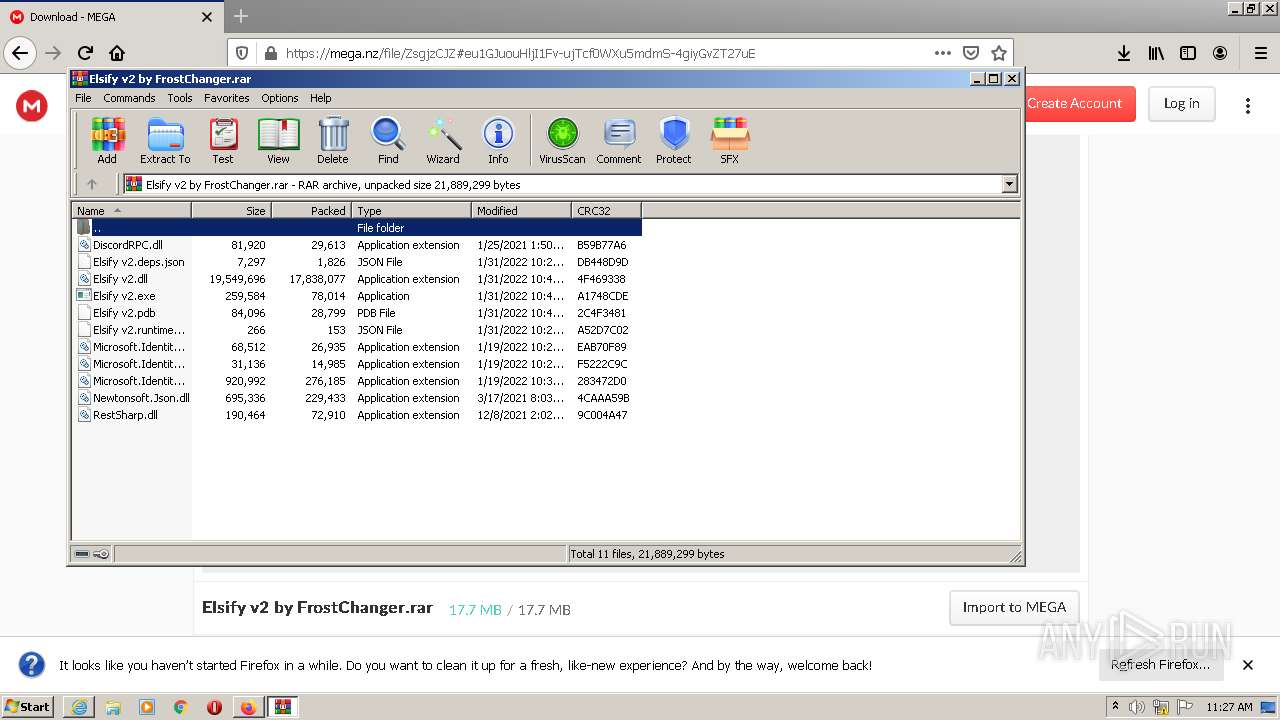
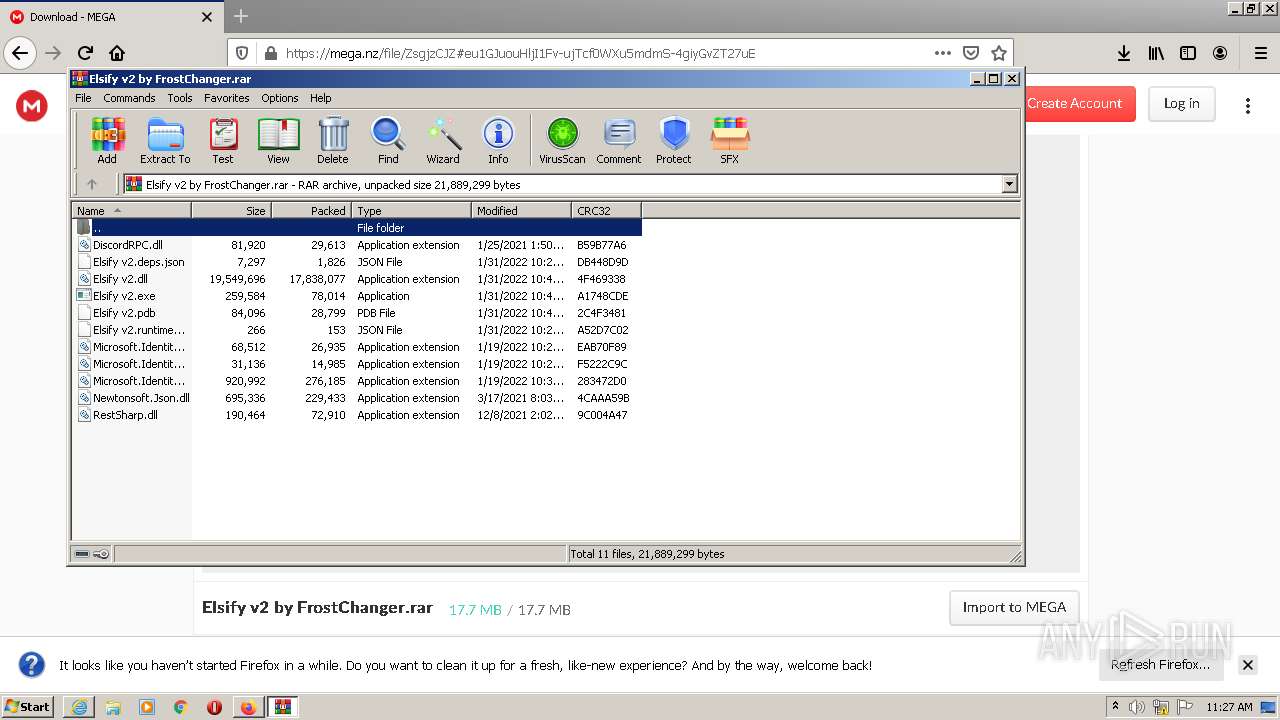
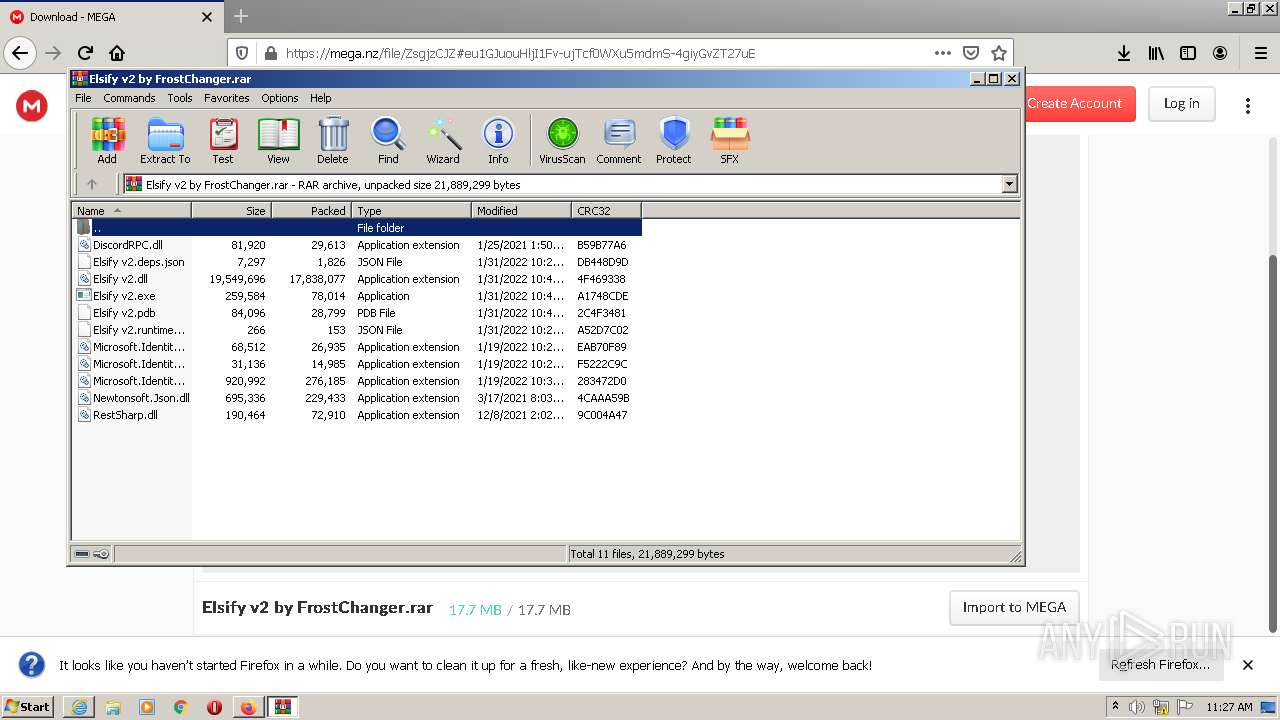
- WinRAR.exe (PID: 4016)
Executable content was dropped or overwritten
- Valorant Skin Changer - Linkvertise Downloader_n-Kh0R1.exe (PID: 3436)
- Valorant Skin Changer - Linkvertise Downloader_n-Kh0R1.exe (PID: 2732)
- Valorant Skin Changer - Linkvertise Downloader_n-Kh0R1.tmp (PID: 2456)
- WinRAR.exe (PID: 4016)
Reads the computer name
- Valorant Skin Changer - Linkvertise Downloader_n-Kh0R1.tmp (PID: 3588)
- Valorant Skin Changer - Linkvertise Downloader_n-Kh0R1.tmp (PID: 2456)
- WinRAR.exe (PID: 4016)
Reads Windows owner or organization settings
- Valorant Skin Changer - Linkvertise Downloader_n-Kh0R1.tmp (PID: 2456)
Reads the Windows organization settings
- Valorant Skin Changer - Linkvertise Downloader_n-Kh0R1.tmp (PID: 2456)
Drops a file with too old compile date
- Valorant Skin Changer - Linkvertise Downloader_n-Kh0R1.tmp (PID: 2456)
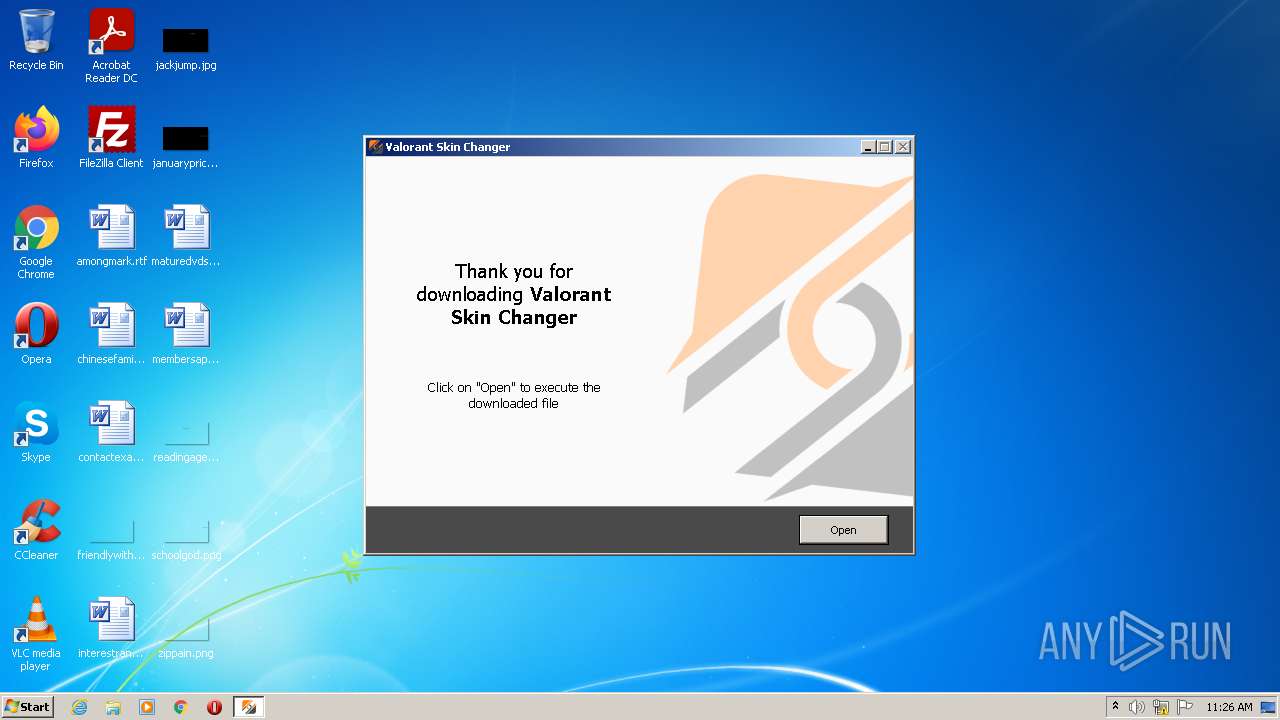
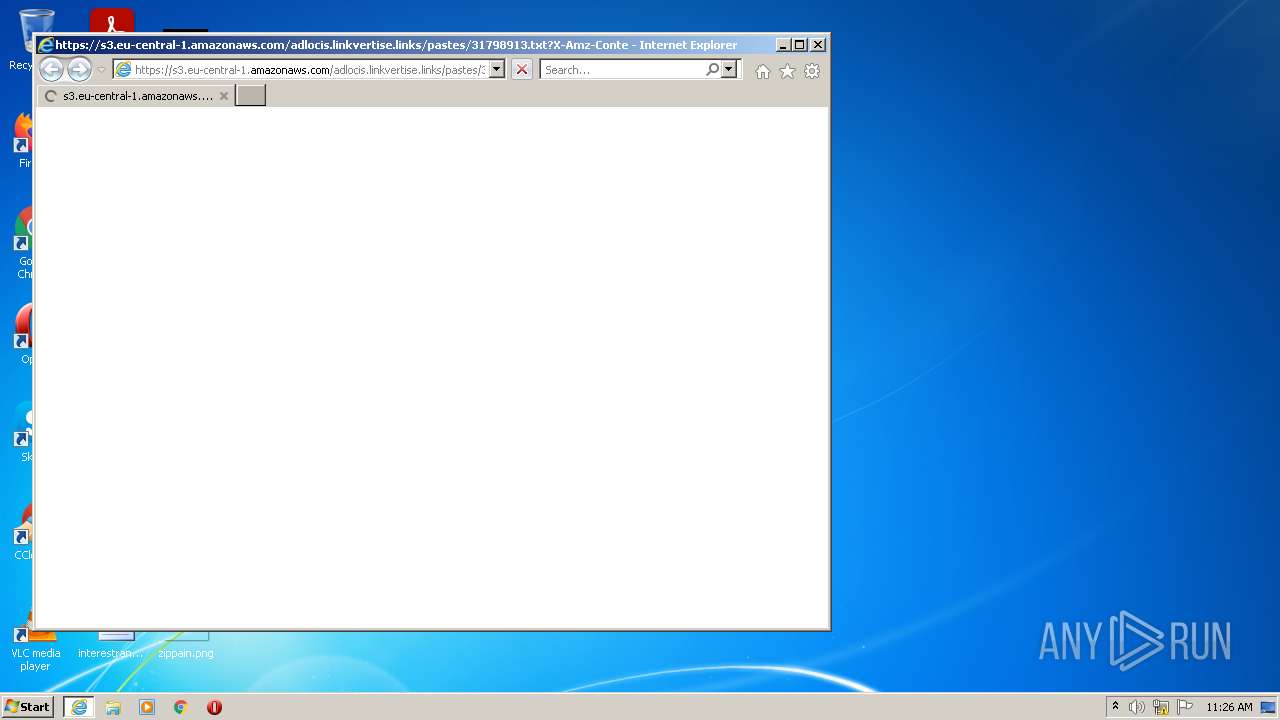
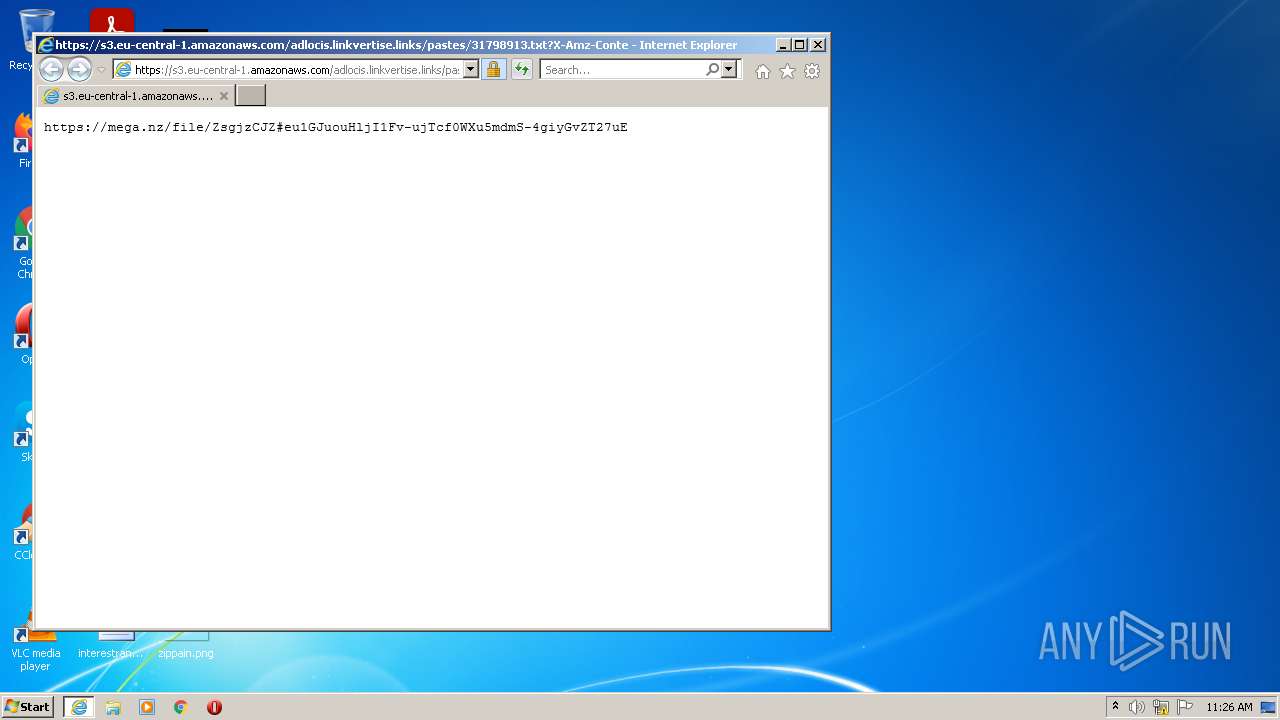
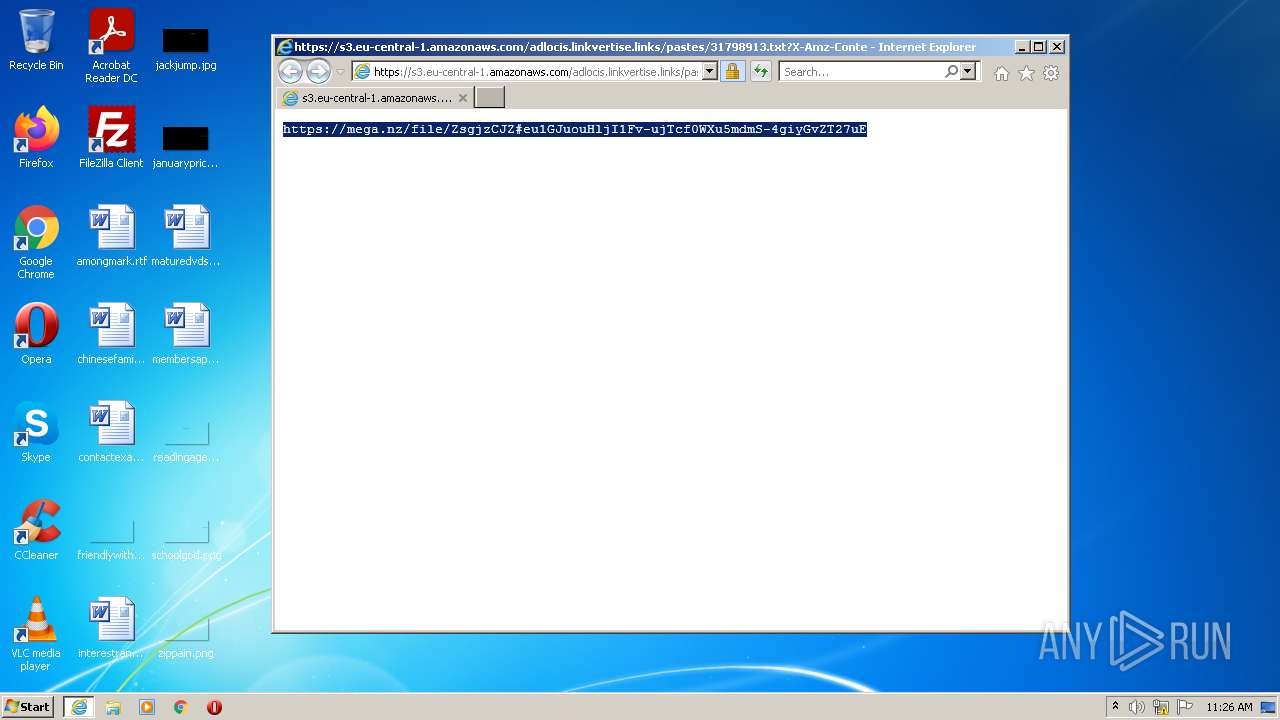
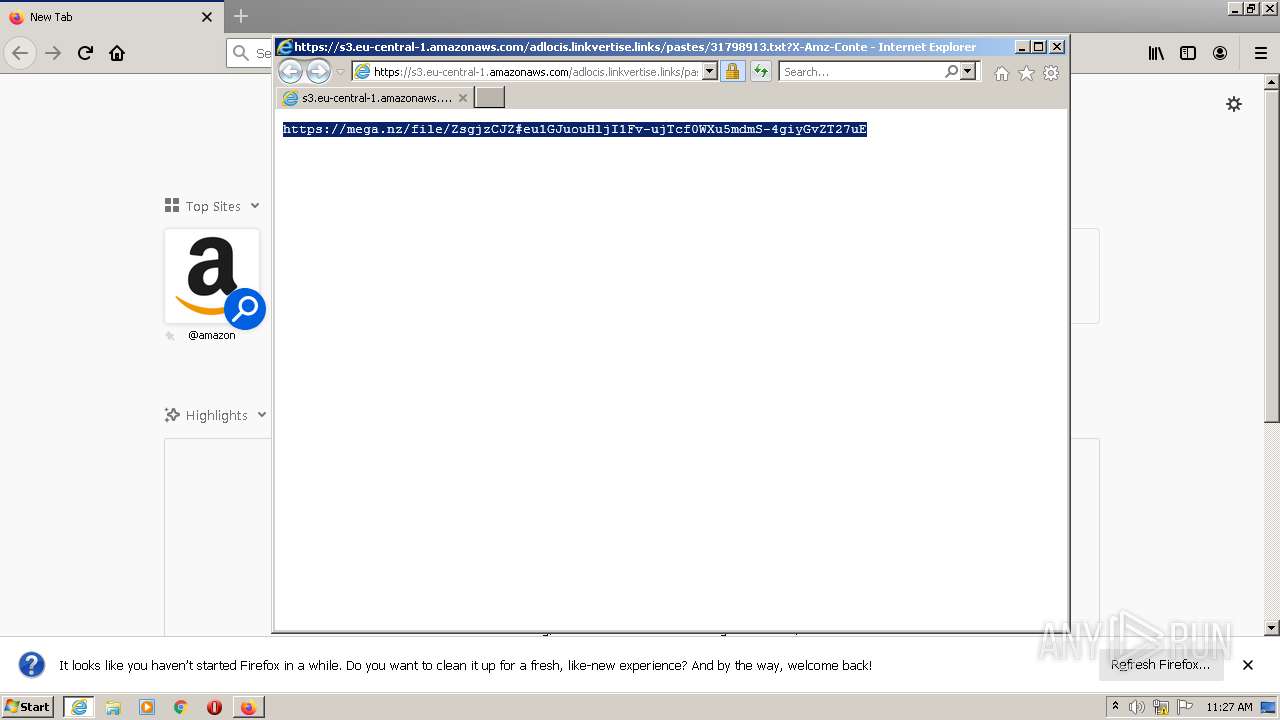
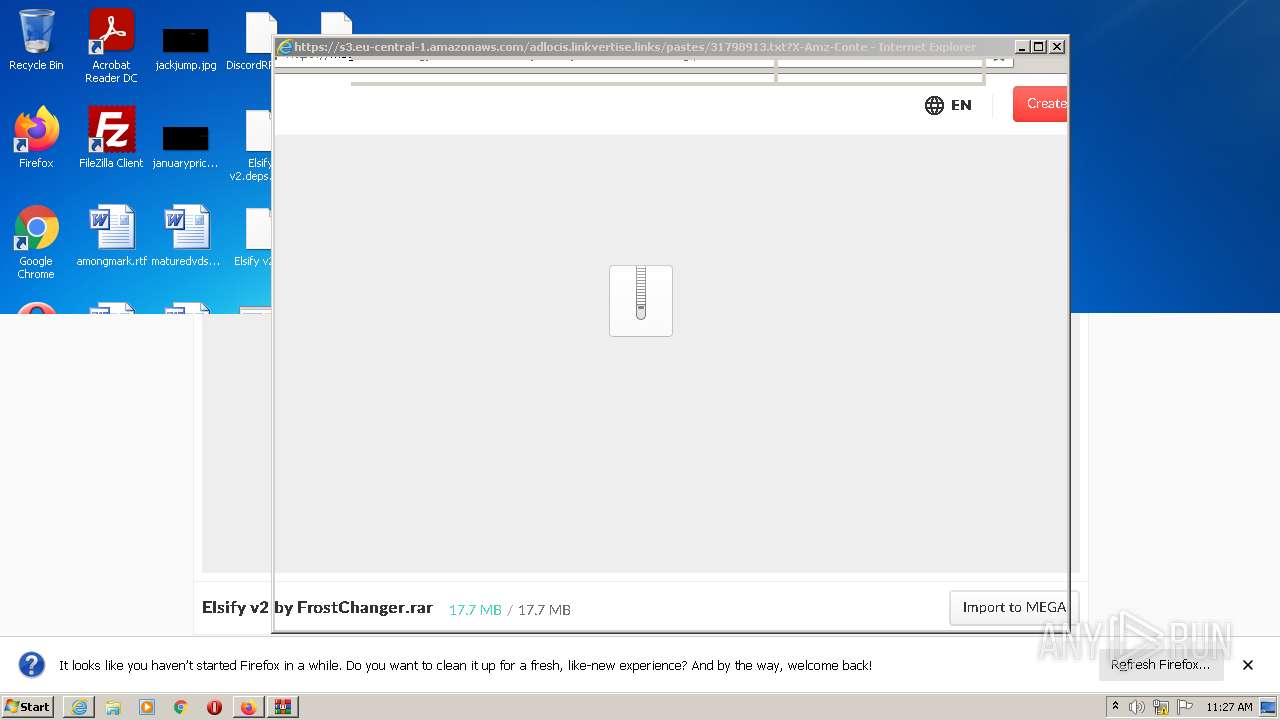
Starts Internet Explorer
- Valorant Skin Changer - Linkvertise Downloader_n-Kh0R1.tmp (PID: 2456)
Drops a file that was compiled in debug mode
- Valorant Skin Changer - Linkvertise Downloader_n-Kh0R1.tmp (PID: 2456)
- WinRAR.exe (PID: 4016)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2568)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 4016)
INFO
Application was dropped or rewritten from another process
- Valorant Skin Changer - Linkvertise Downloader_n-Kh0R1.tmp (PID: 2456)
- Valorant Skin Changer - Linkvertise Downloader_n-Kh0R1.tmp (PID: 3588)
Reads settings of System Certificates
- Valorant Skin Changer - Linkvertise Downloader_n-Kh0R1.tmp (PID: 2456)
- iexplore.exe (PID: 3876)
- iexplore.exe (PID: 2568)
Loads dropped or rewritten executable
- Valorant Skin Changer - Linkvertise Downloader_n-Kh0R1.tmp (PID: 2456)
Checks supported languages
- iexplore.exe (PID: 3876)
- iexplore.exe (PID: 2568)
- firefox.exe (PID: 2148)
- firefox.exe (PID: 3008)
- firefox.exe (PID: 412)
- firefox.exe (PID: 2428)
- firefox.exe (PID: 892)
- firefox.exe (PID: 3036)
- firefox.exe (PID: 3976)
- firefox.exe (PID: 720)
- SearchProtocolHost.exe (PID: 1256)
Application launched itself
- iexplore.exe (PID: 3876)
- firefox.exe (PID: 2148)
- firefox.exe (PID: 3008)
Reads the computer name
- iexplore.exe (PID: 2568)
- firefox.exe (PID: 3008)
- iexplore.exe (PID: 3876)
- firefox.exe (PID: 2428)
- firefox.exe (PID: 3976)
- firefox.exe (PID: 892)
- firefox.exe (PID: 3036)
- firefox.exe (PID: 412)
- firefox.exe (PID: 720)
- SearchProtocolHost.exe (PID: 1256)
Reads internet explorer settings
- iexplore.exe (PID: 2568)
Changes internet zones settings
- iexplore.exe (PID: 3876)
Checks Windows Trust Settings
- iexplore.exe (PID: 2568)
- iexplore.exe (PID: 3876)
- firefox.exe (PID: 3008)
Manual execution by user
- firefox.exe (PID: 2148)
- WinRAR.exe (PID: 4016)
Reads CPU info
- firefox.exe (PID: 3008)
Creates files in the program directory
- firefox.exe (PID: 3008)
Reads the date of Windows installation
- firefox.exe (PID: 3008)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3876)
Creates files in the user directory
- firefox.exe (PID: 3008)
- iexplore.exe (PID: 3876)
Changes settings of System certificates
- iexplore.exe (PID: 3876)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (67.7) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (25.6) |
| .exe | | | Win32 Executable (generic) (2.7) |
| .exe | | | Win16/32 Executable Delphi generic (1.2) |
| .exe | | | Generic Win/DOS Executable (1.2) |
EXIF
EXE
| ProductVersion: | 2.0.0.13 |
|---|---|
| ProductName: | Linkvertise GmbH & Co. KG |
| OriginalFileName: | |
| LegalCopyright: | |
| FileVersion: | 2.0.0.13 |
| FileDescription: | Linkvertise GmbH & Co. KG |
| CompanyName: | |
| Comments: | This installation was built with Inno Setup. |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 2.0.0.13 |
| FileVersionNumber: | 2.0.0.13 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6.1 |
| ImageVersion: | 6 |
| OSVersion: | 6.1 |
| EntryPoint: | 0xb5eec |
| UninitializedDataSize: | - |
| InitializedDataSize: | 157184 |
| CodeSize: | 741376 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 2020:11:15 10:48:30+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Nov-2020 09:48:30 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | - |
| FileDescription: | Linkvertise GmbH & Co. KG |
| FileVersion: | 2.0.0.13 |
| LegalCopyright: | - |
| OriginalFileName: | - |
| ProductName: | Linkvertise GmbH & Co. KG |
| ProductVersion: | 2.0.0.13 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 10 |
| Time date stamp: | 15-Nov-2020 09:48:30 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000B361C | 0x000B3800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.35606 |
.itext | 0x000B5000 | 0x00001688 | 0x00001800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.97275 |
.data | 0x000B7000 | 0x000037A4 | 0x00003800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.0444 |
.bss | 0x000BB000 | 0x00006DE8 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x000C2000 | 0x00000F36 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.8987 |
.didata | 0x000C3000 | 0x000001A4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.75636 |
.edata | 0x000C4000 | 0x0000009A | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.87222 |
.tls | 0x000C5000 | 0x00000018 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x000C6000 | 0x0000005D | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.38389 |
.rsrc | 0x000C7000 | 0x000216F0 | 0x00021800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.61597 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.18295 | 1830 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 2.80552 | 67624 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.40448 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.76613 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 4.12824 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 4.64443 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
4086 | 3.16547 | 864 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4087 | 3.40938 | 608 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4088 | 3.31153 | 1116 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4089 | 3.33977 | 1036 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
kernel32.dll (delay-loaded) |
netapi32.dll |
oleaut32.dll |
user32.dll |
version.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
dbkFCallWrapperAddr | 1 | 0x000BE63C |
__dbk_fcall_wrapper | 2 | 0x0000D0A0 |
TMethodImplementationIntercept | 3 | 0x00054060 |
Total processes
57
Monitored processes
16
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 412 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3008.0.778650327\1589067983" -parentBuildID 20201112153044 -prefsHandle 1136 -prefMapHandle 728 -prefsLen 1 -prefMapSize 238726 -appdir "C:\Program Files\Mozilla Firefox\browser" - 3008 "\\.\pipe\gecko-crash-server-pipe.3008" 1220 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe |
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 83.0 | ||||
| 720 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3008.34.8005415\985746720" -childID 5 -isForBrowser -prefsHandle 3468 -prefMapHandle 3384 -prefsLen 9449 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 3008 "\\.\pipe\gecko-crash-server-pipe.3008" 3564 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe |
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 | ||||
| 892 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3008.13.1787518703\1103028084" -childID 2 -isForBrowser -prefsHandle 3148 -prefMapHandle 3144 -prefsLen 6644 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 3008 "\\.\pipe\gecko-crash-server-pipe.3008" 3160 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe |
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 | ||||
| 1256 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe4_ Global\UsGthrCtrlFltPipeMssGthrPipe4 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe |
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) | ||||
| 2148 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | Explorer.EXE |
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 83.0 | ||||
| 2428 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3008.6.470641746\263432767" -childID 1 -isForBrowser -prefsHandle 2256 -prefMapHandle 2252 -prefsLen 181 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 3008 "\\.\pipe\gecko-crash-server-pipe.3008" 2268 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe |
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 | ||||
| 2456 | "C:\Users\admin\AppData\Local\Temp\is-O2L61.tmp\Valorant Skin Changer - Linkvertise Downloader_n-Kh0R1.tmp" /SL5="$2013E,1785071,899584,C:\Users\admin\AppData\Local\Temp\Valorant Skin Changer - Linkvertise Downloader_n-Kh0R1.exe" /SPAWNWND=$1013C /NOTIFYWND=$20138 | C:\Users\admin\AppData\Local\Temp\is-O2L61.tmp\Valorant Skin Changer - Linkvertise Downloader_n-Kh0R1.tmp | Valorant Skin Changer - Linkvertise Downloader_n-Kh0R1.exe | |
User: admin Company: Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 | ||||
| 2568 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3876 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) | ||||
| 2732 | "C:\Users\admin\AppData\Local\Temp\Valorant Skin Changer - Linkvertise Downloader_n-Kh0R1.exe" /SPAWNWND=$1013C /NOTIFYWND=$20138 | C:\Users\admin\AppData\Local\Temp\Valorant Skin Changer - Linkvertise Downloader_n-Kh0R1.exe | Valorant Skin Changer - Linkvertise Downloader_n-Kh0R1.tmp | |
User: admin Company: Integrity Level: HIGH Description: Linkvertise GmbH & Co. KG Exit code: 0 Version: 2.0.0.13 | ||||
| 3008 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | |
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 83.0 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
12
Suspicious files
137
Text files
59
Unknown types
34
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2456 | Valorant Skin Changer - Linkvertise Downloader_n-Kh0R1.tmp | C:\Users\admin\AppData\Local\Temp\is-BA8N0.tmp\WebAdvisor.png | image | |
MD5:— | SHA256:— | |||
| 2568 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B66240B0F6C84BD4857ABA60CF5CE4A0_5043E0F5DF723415C9EECC201C838A62 | der | |
MD5:— | SHA256:— | |||
| 2568 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\BAD725C80F9E10846F35D039A996E4A8_88B6AE015495C1ECC395D19C1DD02894 | der | |
MD5:— | SHA256:— | |||
| 2568 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\BAD725C80F9E10846F35D039A996E4A8_88B6AE015495C1ECC395D19C1DD02894 | binary | |
MD5:— | SHA256:— | |||
| 2568 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\75CA58072B9926F763A91F0CC2798706_93E4B2BA79A897B3100CCB27F2D3BF4F | binary | |
MD5:— | SHA256:— | |||
| 2568 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2568 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\75CA58072B9926F763A91F0CC2798706_93E4B2BA79A897B3100CCB27F2D3BF4F | der | |
MD5:— | SHA256:— | |||
| 2568 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B66240B0F6C84BD4857ABA60CF5CE4A0_5043E0F5DF723415C9EECC201C838A62 | binary | |
MD5:— | SHA256:— | |||
| 2456 | Valorant Skin Changer - Linkvertise Downloader_n-Kh0R1.tmp | C:\Users\admin\AppData\Local\Temp\is-BA8N0.tmp\is-DR0EU.tmp | image | |
MD5:— | SHA256:— | |||
| 2732 | Valorant Skin Changer - Linkvertise Downloader_n-Kh0R1.exe | C:\Users\admin\AppData\Local\Temp\is-O2L61.tmp\Valorant Skin Changer - Linkvertise Downloader_n-Kh0R1.tmp | executable | |
MD5:74FAD5C6CD2D3AF1FA257B5E9531993A | SHA256:8DC40627FA4C09F7FD6DF78E3AD03D7DB3767010E15418DBA24E63754DCBC59B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
57
DNS requests
112
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2568 | iexplore.exe | GET | 200 | 52.222.250.82:80 | http://ocsp.sca1b.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQz9arGHWbnBV0DFzpNHz4YcTiFDQQUWaRmBlKge5WSPKOUByeWdFv5PdACEAk2WFQSDTUgLjKxwffG58U%3D | US | der | 471 b | whitelisted |
3008 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3876 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3008 | firefox.exe | POST | 200 | 104.18.31.182:80 | http://ocsp.sectigo.com/ | US | der | 472 b | whitelisted |
3008 | firefox.exe | POST | 200 | 104.18.31.182:80 | http://ocsp.sectigo.com/ | US | der | 471 b | whitelisted |
2568 | iexplore.exe | GET | 200 | 18.66.92.70:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
3008 | firefox.exe | POST | 200 | 2.16.186.27:80 | http://r3.o.lencr.org/ | unknown | der | 503 b | shared |
3008 | firefox.exe | POST | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gts1c3 | US | der | 471 b | whitelisted |
3008 | firefox.exe | POST | 200 | 104.18.31.182:80 | http://ocsp.sectigo.com/ | US | der | 471 b | whitelisted |
2568 | iexplore.exe | GET | 200 | 52.222.206.202:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2568 | iexplore.exe | 52.219.170.29:443 | s3.eu-central-1.amazonaws.com | — | US | unknown |
2568 | iexplore.exe | 23.32.238.201:80 | ctldl.windowsupdate.com | XO Communications | US | suspicious |
2568 | iexplore.exe | 18.66.92.70:80 | o.ss2.us | Massachusetts Institute of Technology | US | unknown |
2456 | Valorant Skin Changer - Linkvertise Downloader_n-Kh0R1.tmp | 18.66.188.218:443 | d17kz3i6hbr7d3.cloudfront.net | Massachusetts Institute of Technology | US | unknown |
2568 | iexplore.exe | 52.222.250.82:80 | ocsp.sca1b.amazontrust.com | Amazon.com, Inc. | US | whitelisted |
3876 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2568 | iexplore.exe | 52.222.206.202:80 | ocsp.rootg2.amazontrust.com | Amazon.com, Inc. | US | whitelisted |
2568 | iexplore.exe | 52.222.206.67:80 | ocsp.rootg2.amazontrust.com | Amazon.com, Inc. | US | whitelisted |
3008 | firefox.exe | 52.89.43.233:443 | location.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3008 | firefox.exe | 52.222.214.105:443 | firefox.settings.services.mozilla.com | Amazon.com, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
d17kz3i6hbr7d3.cloudfront.net |
| whitelisted |
s3.eu-central-1.amazonaws.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| shared |
ocsp.sca1b.amazontrust.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3008 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
3008 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
3008 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
3008 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |