| File name: | d2238bcff8d4ff94256c8df702a31182763fa55325040cd484bc9abae2e69c5a.exe |
| Full analysis: | https://app.any.run/tasks/113e9270-cc70-40f4-9e83-229901e9f576 |
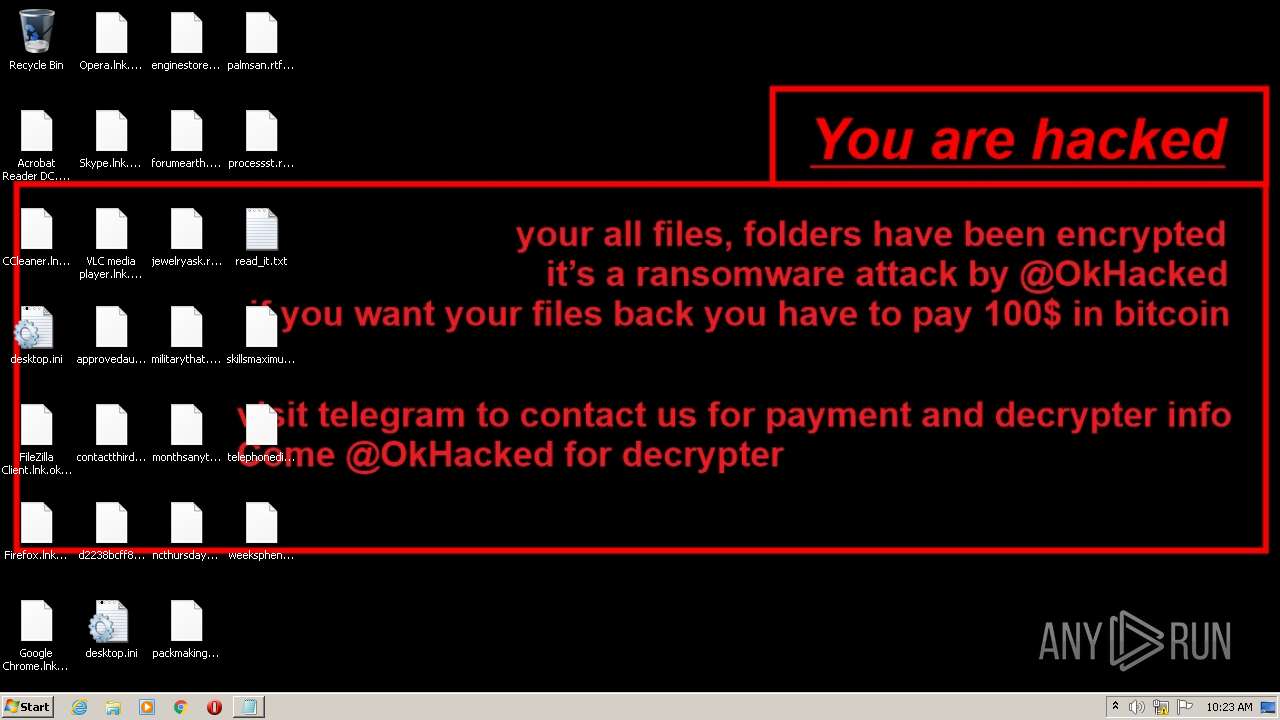
| Verdict: | Malicious activity |
| Analysis date: | September 27, 2022, 09:22:25 |
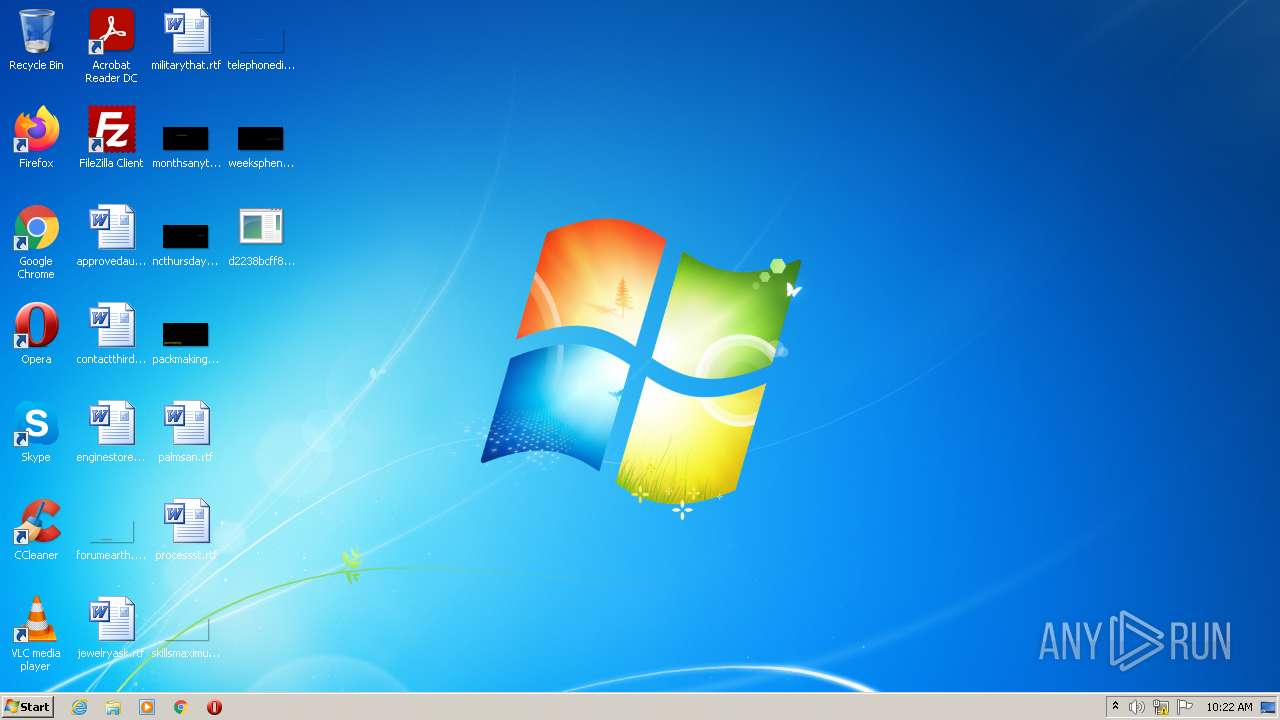
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 28A4C68D4AFF7E58D321065189FD68E3 |
| SHA1: | 884CCDE1C4732FEADC44ACF4C9289D97E3004D83 |
| SHA256: | D2238BCFF8D4FF94256C8DF702A31182763FA55325040CD484BC9ABAE2E69C5A |
| SSDEEP: | 12288:O4yERcXVFIXLfmSYgkkL+8h+afxQl9OUVfU:gI7rbp8 |
MALICIOUS
Drops executable file immediately after starts
- d2238bcff8d4ff94256c8df702a31182763fa55325040cd484bc9abae2e69c5a.exe (PID: 3148)
Changes the autorun value in the registry
- okhacked.exe (PID: 976)
Deletes shadow copies
- cmd.exe (PID: 832)
- cmd.exe (PID: 3460)
Starts BCDEDIT.EXE to disable recovery
- cmd.exe (PID: 3036)
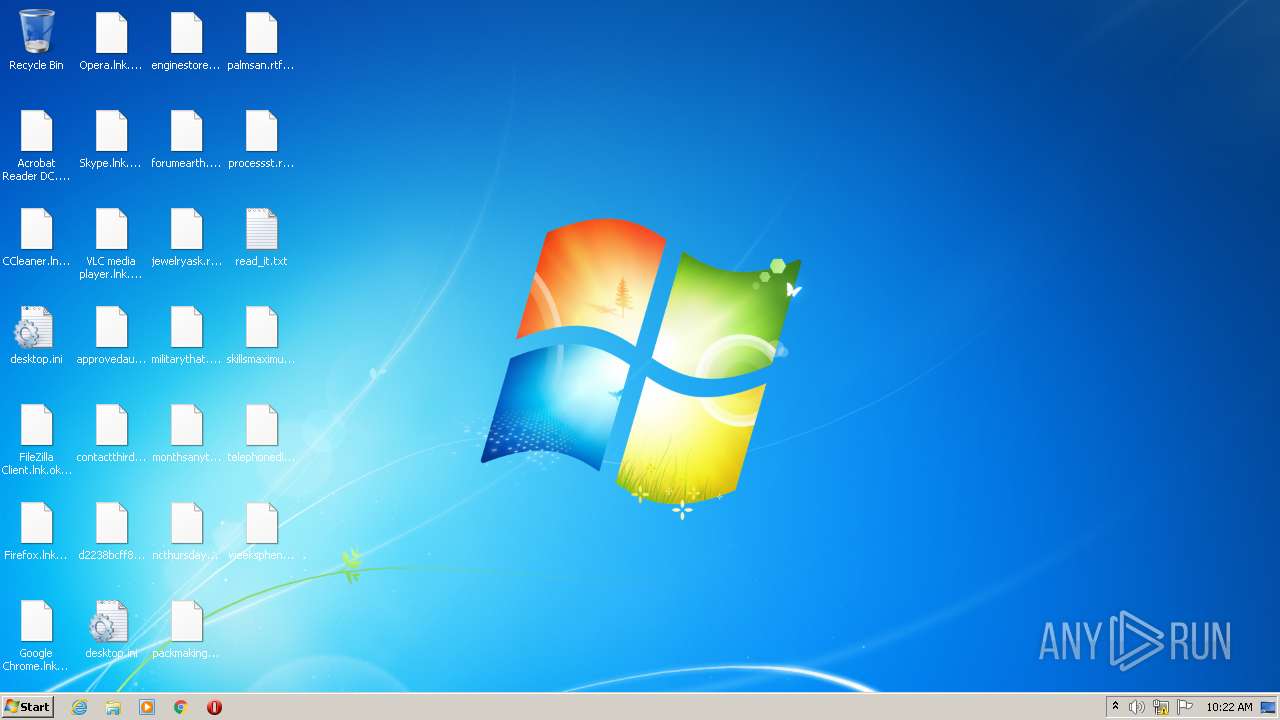
Writes to a start menu file
- okhacked.exe (PID: 976)
Steals credentials from Web Browsers
- okhacked.exe (PID: 976)
Loads the Task Scheduler COM API
- wbengine.exe (PID: 3776)
Task Manager has been disabled (taskmgr)
- okhacked.exe (PID: 976)
Modifies files in Chrome extension folder
- okhacked.exe (PID: 976)
Actions looks like stealing of personal data
- okhacked.exe (PID: 976)
SUSPICIOUS
Reads the computer name
- d2238bcff8d4ff94256c8df702a31182763fa55325040cd484bc9abae2e69c5a.exe (PID: 3148)
- okhacked.exe (PID: 976)
- WMIC.exe (PID: 1104)
Checks supported languages
- d2238bcff8d4ff94256c8df702a31182763fa55325040cd484bc9abae2e69c5a.exe (PID: 3148)
- okhacked.exe (PID: 976)
- cmd.exe (PID: 832)
- WMIC.exe (PID: 1104)
- cmd.exe (PID: 3036)
- cmd.exe (PID: 3460)
Executable content was dropped or overwritten
- d2238bcff8d4ff94256c8df702a31182763fa55325040cd484bc9abae2e69c5a.exe (PID: 3148)
Starts itself from another location
- d2238bcff8d4ff94256c8df702a31182763fa55325040cd484bc9abae2e69c5a.exe (PID: 3148)
Creates files in the user directory
- d2238bcff8d4ff94256c8df702a31182763fa55325040cd484bc9abae2e69c5a.exe (PID: 3148)
- okhacked.exe (PID: 976)
Drops a file with a compile date too recent
- d2238bcff8d4ff94256c8df702a31182763fa55325040cd484bc9abae2e69c5a.exe (PID: 3148)
Starts CMD.EXE for commands execution
- okhacked.exe (PID: 976)
Executed as Windows Service
- vssvc.exe (PID: 3136)
- wbengine.exe (PID: 3776)
- vds.exe (PID: 1372)
Executed via COM
- vdsldr.exe (PID: 448)
Creates files in the Windows directory
- wbadmin.exe (PID: 3400)
Creates files in the program directory
- okhacked.exe (PID: 976)
INFO
Checks supported languages
- vssadmin.exe (PID: 3664)
- vssvc.exe (PID: 3136)
- bcdedit.exe (PID: 3108)
- bcdedit.exe (PID: 272)
- vdsldr.exe (PID: 448)
- wbengine.exe (PID: 3776)
- vds.exe (PID: 1372)
- wbadmin.exe (PID: 3400)
- NOTEPAD.EXE (PID: 2108)
Reads the computer name
- vssadmin.exe (PID: 3664)
- vssvc.exe (PID: 3136)
- wbadmin.exe (PID: 3400)
- wbengine.exe (PID: 3776)
- vdsldr.exe (PID: 448)
- vds.exe (PID: 1372)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 2022-Sep-26 05:03:02 |
| FileDescription: | - |
| FileVersion: | 0.0.0.0 |
| InternalName: | OkHackedRansomware.exe |
| LegalCopyright: | - |
| OriginalFilename: | OkHackedRansomware.exe |
| ProductVersion: | 0.0.0.0 |
| Assembly Version: | 0.0.0.0 |
DOS Header
| e_magic: | MZ |
|---|---|
| e_cblp: | 144 |
| e_cp: | 3 |
| e_crlc: | - |
| e_cparhdr: | 4 |
| e_minalloc: | - |
| e_maxalloc: | 65535 |
| e_ss: | - |
| e_sp: | 184 |
| e_csum: | - |
| e_ip: | - |
| e_cs: | - |
| e_ovno: | - |
| e_oemid: | - |
| e_oeminfo: | - |
| e_lfanew: | 128 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| NumberofSections: | 3 |
| TimeDateStamp: | 2022-Sep-26 05:03:02 |
| PointerToSymbolTable: | - |
| NumberOfSymbols: | - |
| SizeOfOptionalHeader: | 224 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 8192 | 551636 | 551936 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 4.12665 |
.rsrc | 565248 | 1288 | 1536 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.8034 |
.reloc | 573440 | 12 | 512 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.20354 | 628 | UNKNOWN | UNKNOWN | RT_VERSION |
1 (#2) | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
58
Monitored processes
15
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | bcdedit /set {default} recoveryenabled no | C:\Windows\system32\bcdedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Boot Configuration Data Editor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 448 | C:\Windows\System32\vdsldr.exe -Embedding | C:\Windows\System32\vdsldr.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Virtual Disk Service Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 832 | "C:\Windows\System32\cmd.exe" /C vssadmin delete shadows /all /quiet & wmic shadowcopy delete | C:\Windows\System32\cmd.exe | — | okhacked.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 976 | "C:\Users\admin\AppData\Roaming\okhacked.exe" | C:\Users\admin\AppData\Roaming\okhacked.exe | d2238bcff8d4ff94256c8df702a31182763fa55325040cd484bc9abae2e69c5a.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 1104 | wmic shadowcopy delete | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1372 | C:\Windows\System32\vds.exe | C:\Windows\System32\vds.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Virtual Disk Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
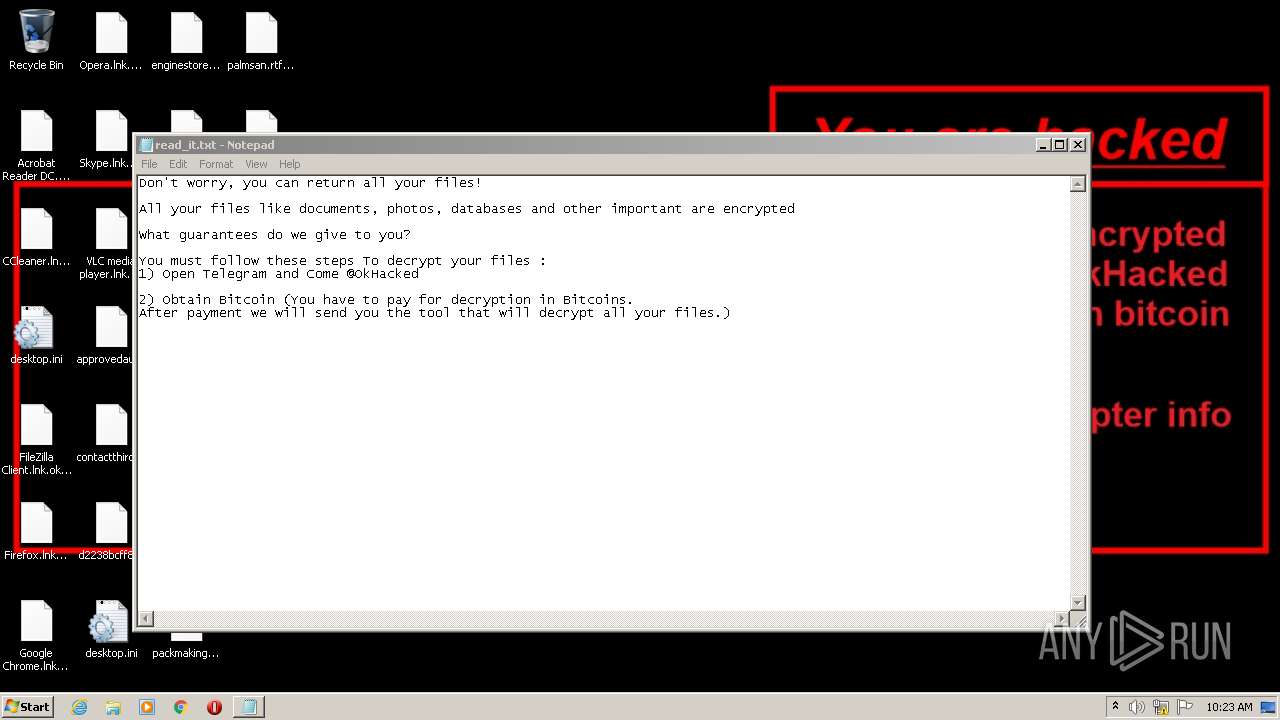
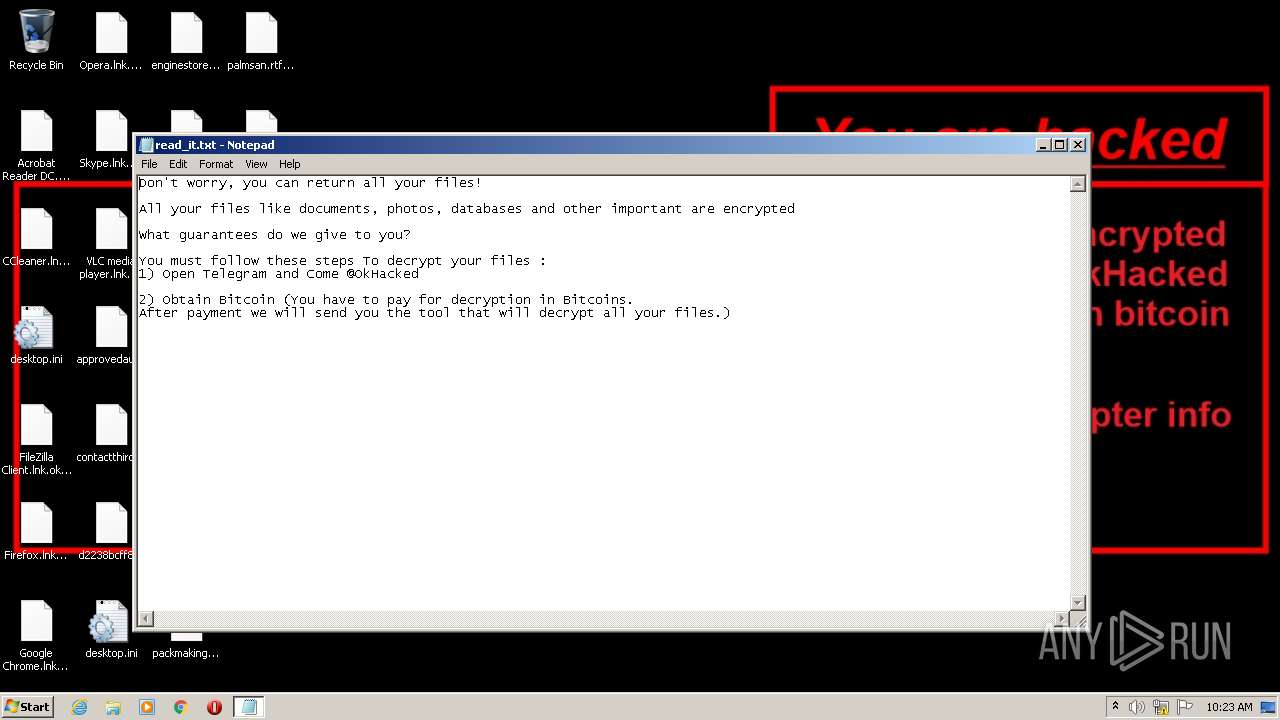
| 2108 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Roaming\read_it.txt | C:\Windows\system32\NOTEPAD.EXE | — | okhacked.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3036 | "C:\Windows\System32\cmd.exe" /C bcdedit /set {default} bootstatuspolicy ignoreallfailures & bcdedit /set {default} recoveryenabled no | C:\Windows\System32\cmd.exe | — | okhacked.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3108 | bcdedit /set {default} bootstatuspolicy ignoreallfailures | C:\Windows\system32\bcdedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Boot Configuration Data Editor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3136 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
5 051
Read events
5 031
Write events
20
Delete events
0
Modification events
| (PID) Process: | (3148) d2238bcff8d4ff94256c8df702a31182763fa55325040cd484bc9abae2e69c5a.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3148) d2238bcff8d4ff94256c8df702a31182763fa55325040cd484bc9abae2e69c5a.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3148) d2238bcff8d4ff94256c8df702a31182763fa55325040cd484bc9abae2e69c5a.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3148) d2238bcff8d4ff94256c8df702a31182763fa55325040cd484bc9abae2e69c5a.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (976) okhacked.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | UpdateTask |
Value: C:\Users\admin\AppData\Roaming\okhacked.exe | |||
| (PID) Process: | (976) okhacked.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (976) okhacked.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (976) okhacked.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (976) okhacked.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3108) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{345b46fd-a9f9-11e7-a83c-e8a4f72b1d33}\Elements\250000e0 |
| Operation: | write | Name: | Element |
Value: 0100000000000000 | |||
Executable files
1
Suspicious files
667
Text files
499
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 976 | okhacked.exe | C:\Users\Administrator\AppData\Local\read_it.txt | text | |
MD5:— | SHA256:— | |||
| 976 | okhacked.exe | C:\Users\admin\AppData\Local\read_it.txt | text | |
MD5:— | SHA256:— | |||
| 976 | okhacked.exe | C:\Users\Administrator\read_it.txt | text | |
MD5:— | SHA256:— | |||
| 976 | okhacked.exe | C:\ProgramData\Adobe\ARM\{291AA914-A987-4CE9-BD63-AC0A92D435E5}\read_it.txt | text | |
MD5:— | SHA256:— | |||
| 976 | okhacked.exe | C:\Users\read_it.txt | text | |
MD5:— | SHA256:— | |||
| 976 | okhacked.exe | C:\Users\Public\read_it.txt | text | |
MD5:— | SHA256:— | |||
| 976 | okhacked.exe | C:\Users\admin\read_it.txt | text | |
MD5:— | SHA256:— | |||
| 3148 | d2238bcff8d4ff94256c8df702a31182763fa55325040cd484bc9abae2e69c5a.exe | C:\Users\admin\AppData\Roaming\okhacked.exe | executable | |
MD5:— | SHA256:— | |||
| 976 | okhacked.exe | C:\Users\Default\read_it.txt | text | |
MD5:— | SHA256:— | |||
| 976 | okhacked.exe | C:\Users\Default\AppData\Roaming\Microsoft\Internet Explorer\Quick Launch\read_it.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report