| File name: | hahaha.ps |
| Full analysis: | https://app.any.run/tasks/6283f32e-32e1-4b9e-b685-1e6b9b599d07 |
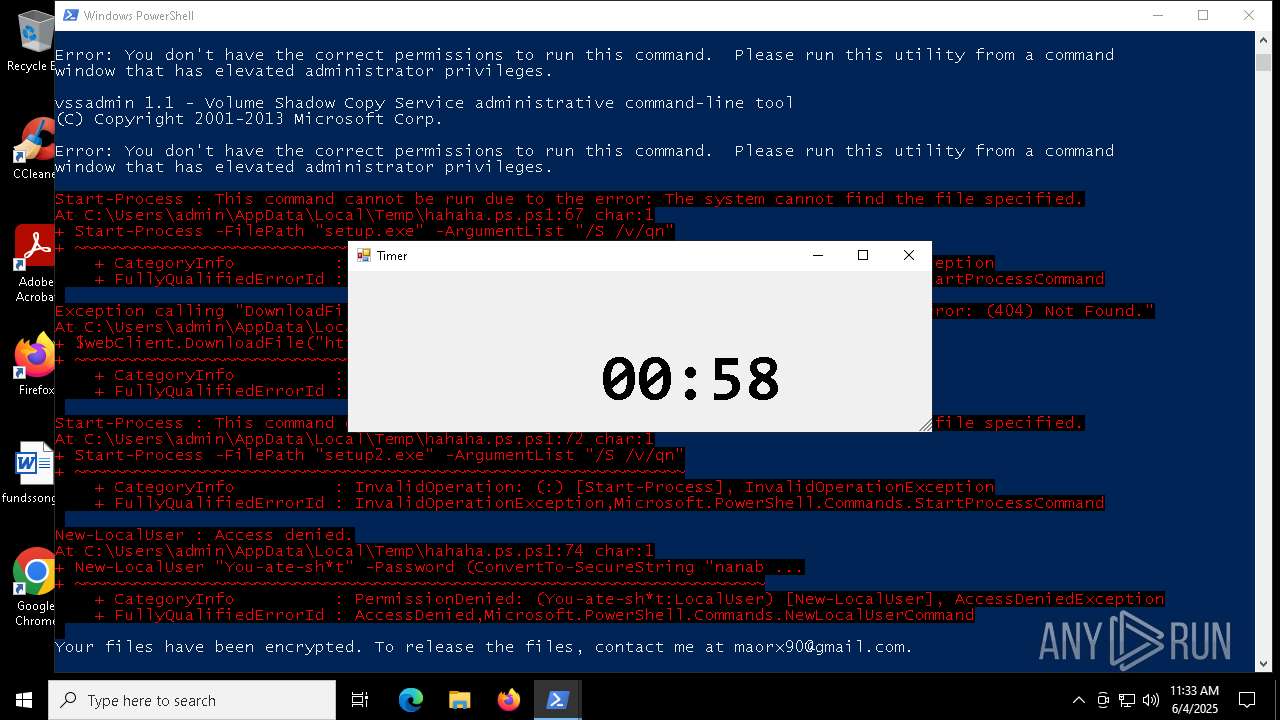
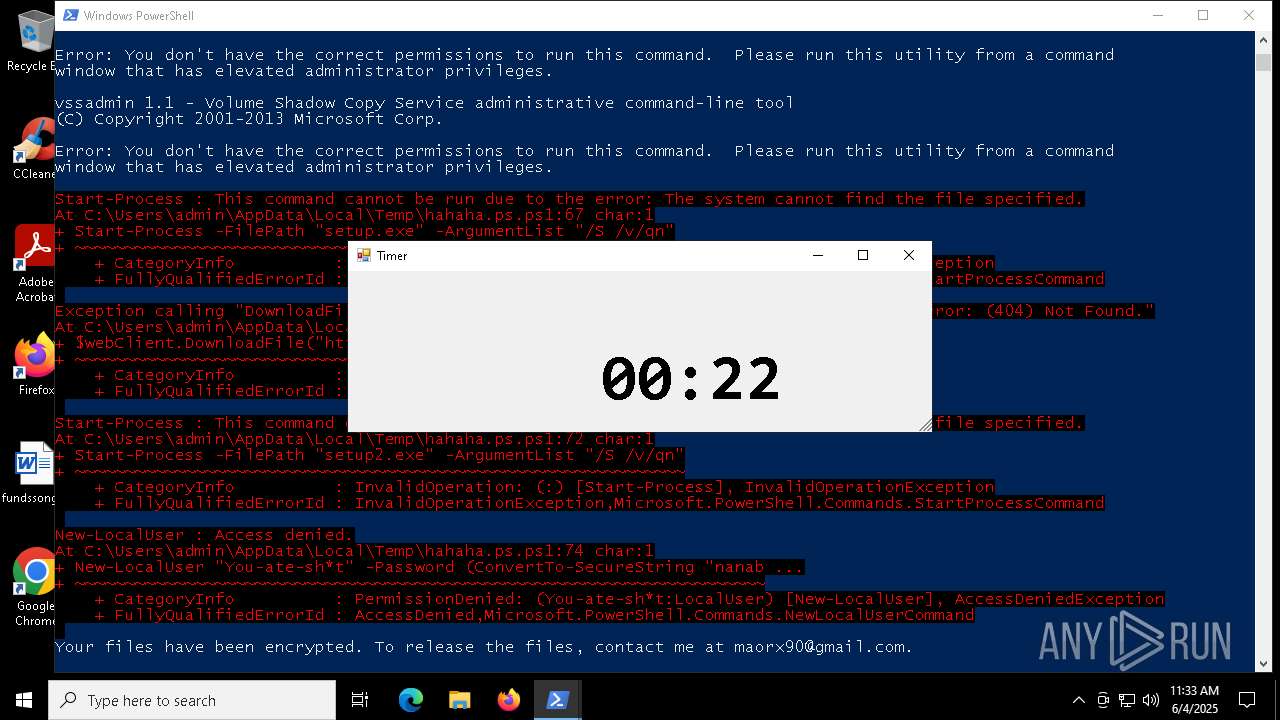
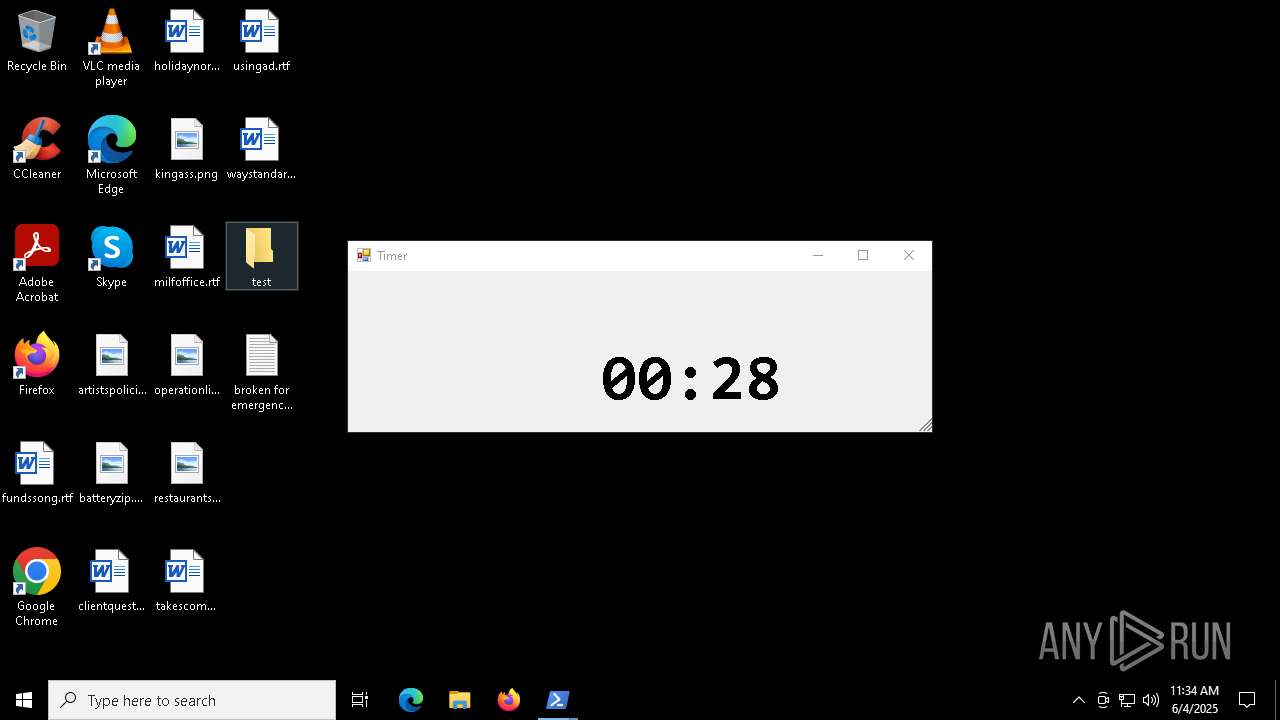
| Verdict: | Malicious activity |
| Analysis date: | June 04, 2025, 11:33:38 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | F612C804DCB85545F08D5FC1DA99719C |
| SHA1: | 9D3ABE7C5ECDDBE4F7793804468F877EDDB599C5 |
| SHA256: | D21C76B2CB5FEC09494499C6649DC44C7CEF3DC933F9D4FF333CAED9B54AA763 |
| SSDEEP: | 96:QkwjGU5IBJej0BatIMeS+FnpP1XFY52uIpEs5/s/sD:QkwGUuBJ4SMn+FnNYAvlD |
MALICIOUS
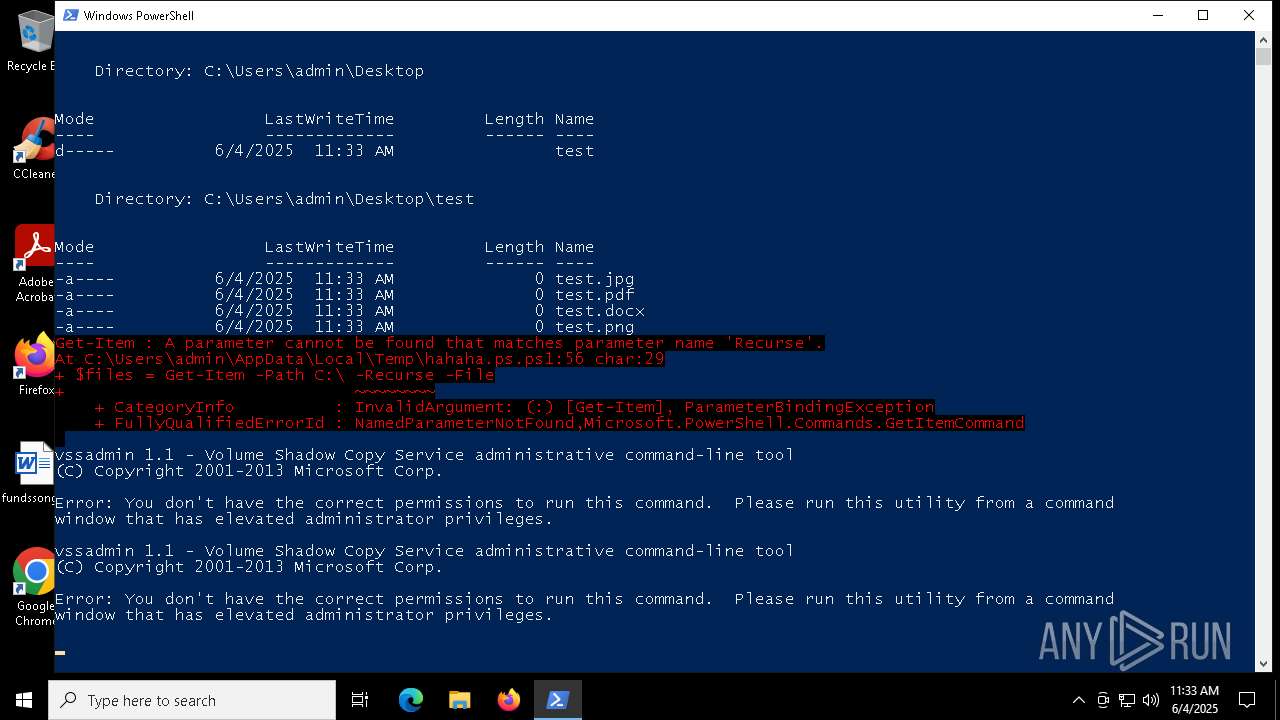
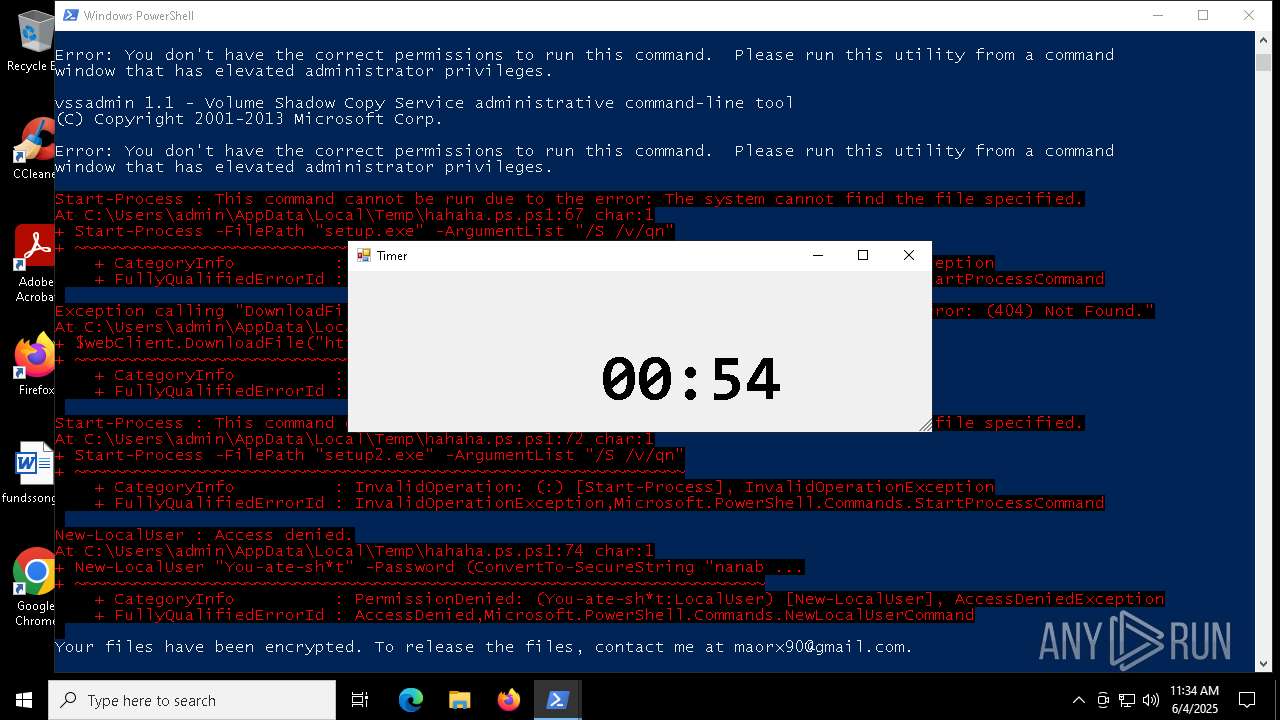
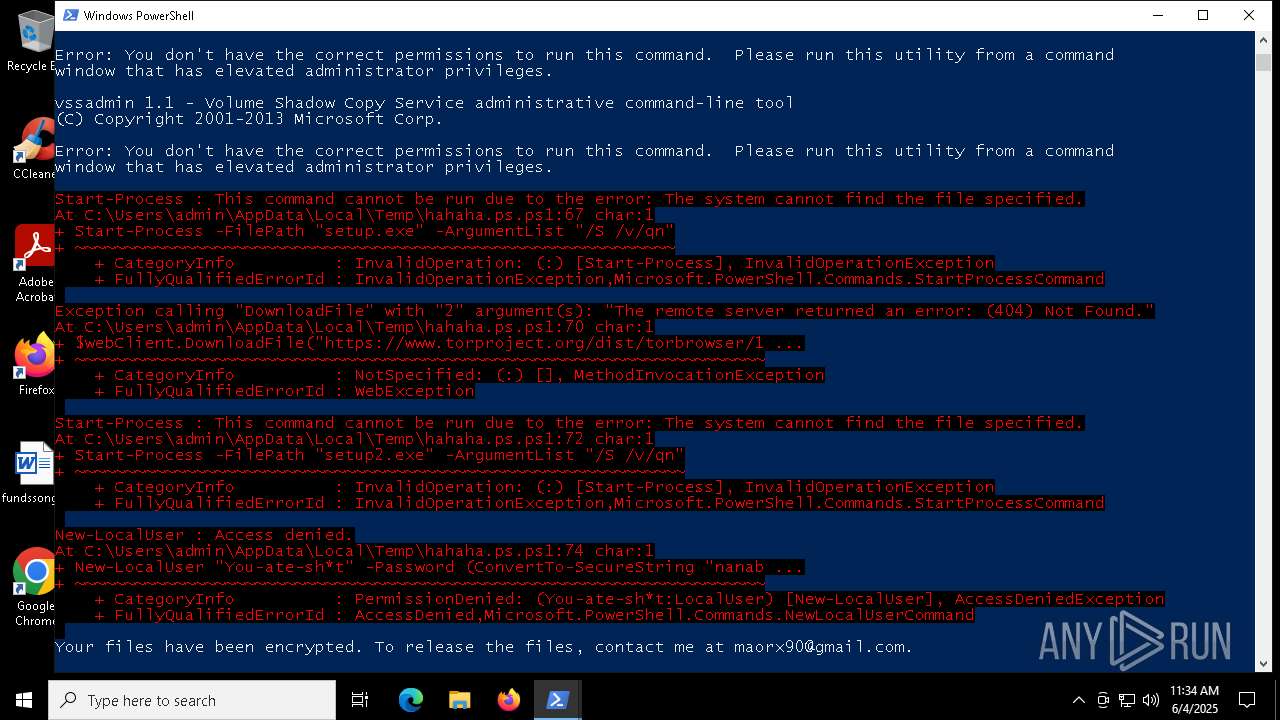
Bypass execution policy to execute commands
- powershell.exe (PID: 7800)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 7800)
Deletes shadow copies
- powershell.exe (PID: 7800)
SUSPICIOUS
Gets path to any of the special folders (POWERSHELL)
- powershell.exe (PID: 7800)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7800)
CSC.EXE is used to compile C# code
- csc.exe (PID: 3968)
Executable content was dropped or overwritten
- csc.exe (PID: 3968)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 7800)
INFO
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 7800)
Gets data length (POWERSHELL)
- powershell.exe (PID: 7800)
Disables trace logs
- powershell.exe (PID: 7800)
Gets or sets the time when the file was last written to (POWERSHELL)
- powershell.exe (PID: 7800)
Checks proxy server information
- powershell.exe (PID: 7800)
Checks supported languages
- csc.exe (PID: 3968)
- cvtres.exe (PID: 1696)
Reads the machine GUID from the registry
- csc.exe (PID: 3968)
Create files in a temporary directory
- csc.exe (PID: 3968)
- cvtres.exe (PID: 1696)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7800)
Remote server returned an error (POWERSHELL)
- powershell.exe (PID: 7800)
Reads the software policy settings
- slui.exe (PID: 7988)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
134
Monitored processes
10
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1696 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES14C8.tmp" "c:\Users\admin\AppData\Local\Temp\CSCB50D2948E074C7289B3138844361B7.TMP" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.32.31326.0 Modules
| |||||||||||||||
| 3968 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\gndlrtp3.cmdline" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 4224 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5048 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5540 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6476 | "C:\WINDOWS\system32\vssadmin.exe" delete shadows /all | C:\Windows\System32\vssadmin.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6980 | "C:\WINDOWS\system32\vssadmin.exe" list shadows | C:\Windows\System32\vssadmin.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7800 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass C:\Users\admin\AppData\Local\Temp\hahaha.ps.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7988 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8124 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
12 763
Read events
12 763
Write events
0
Delete events
0
Modification events
Executable files
1
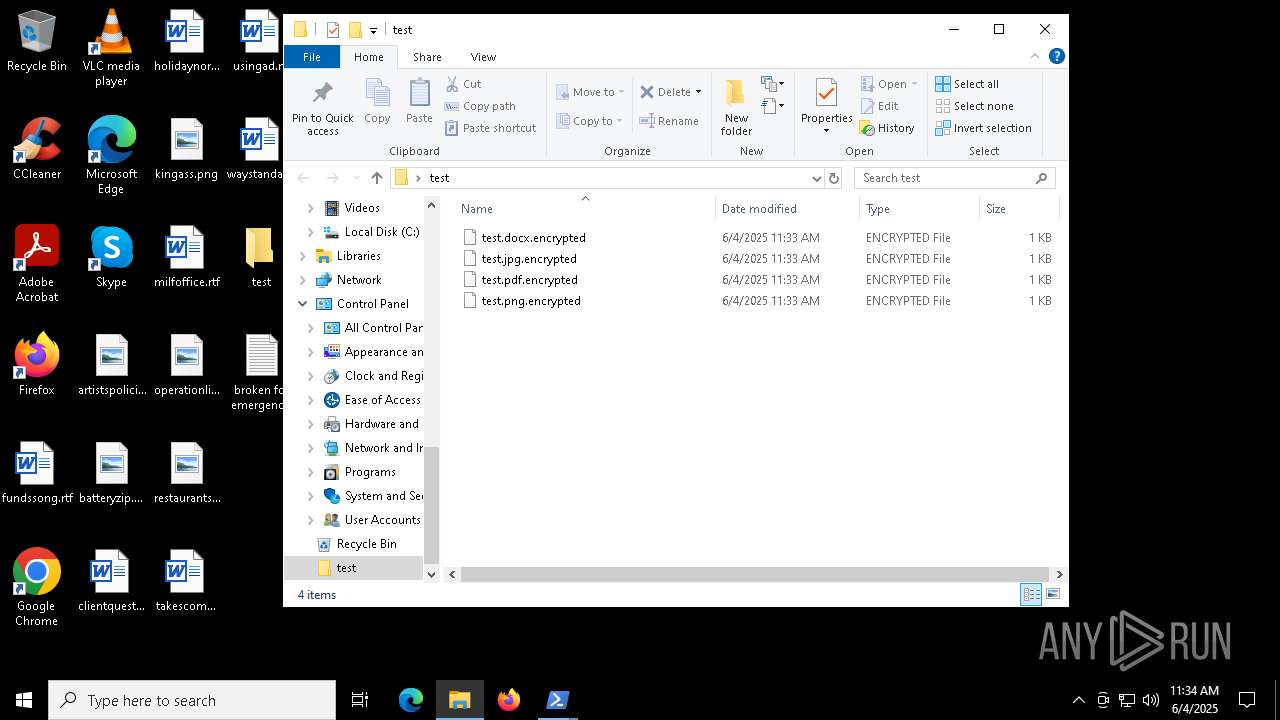
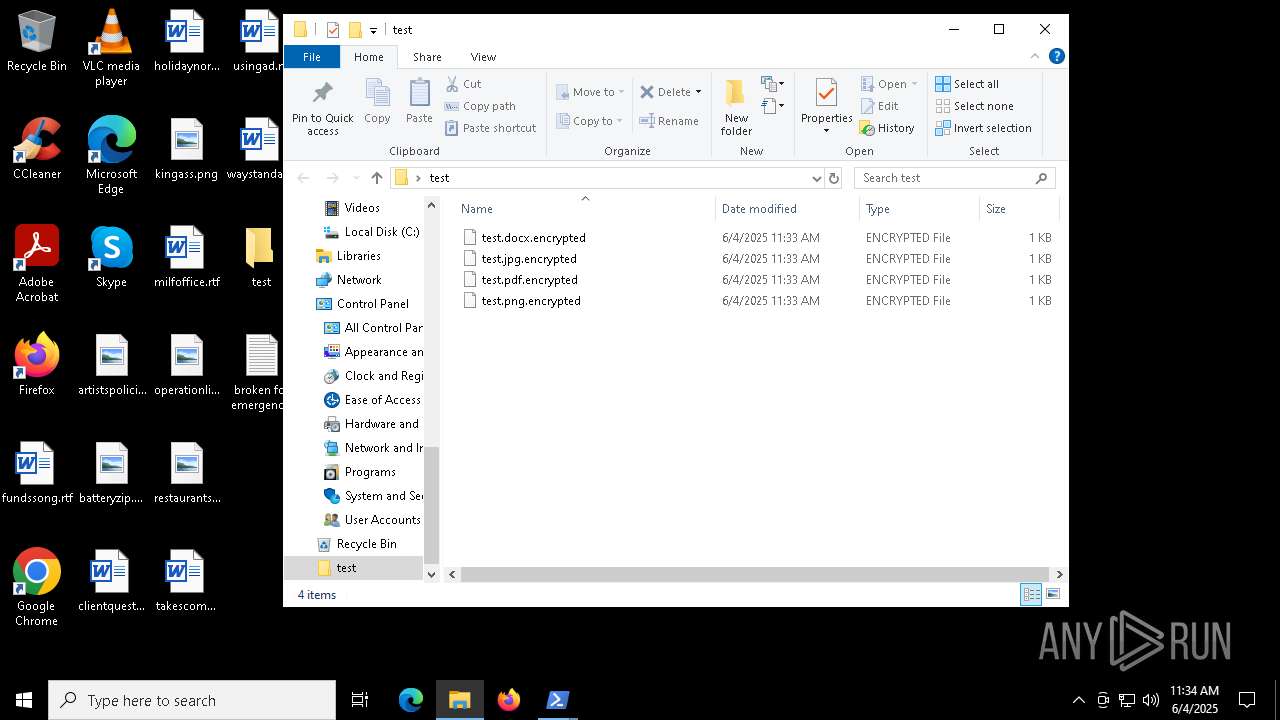
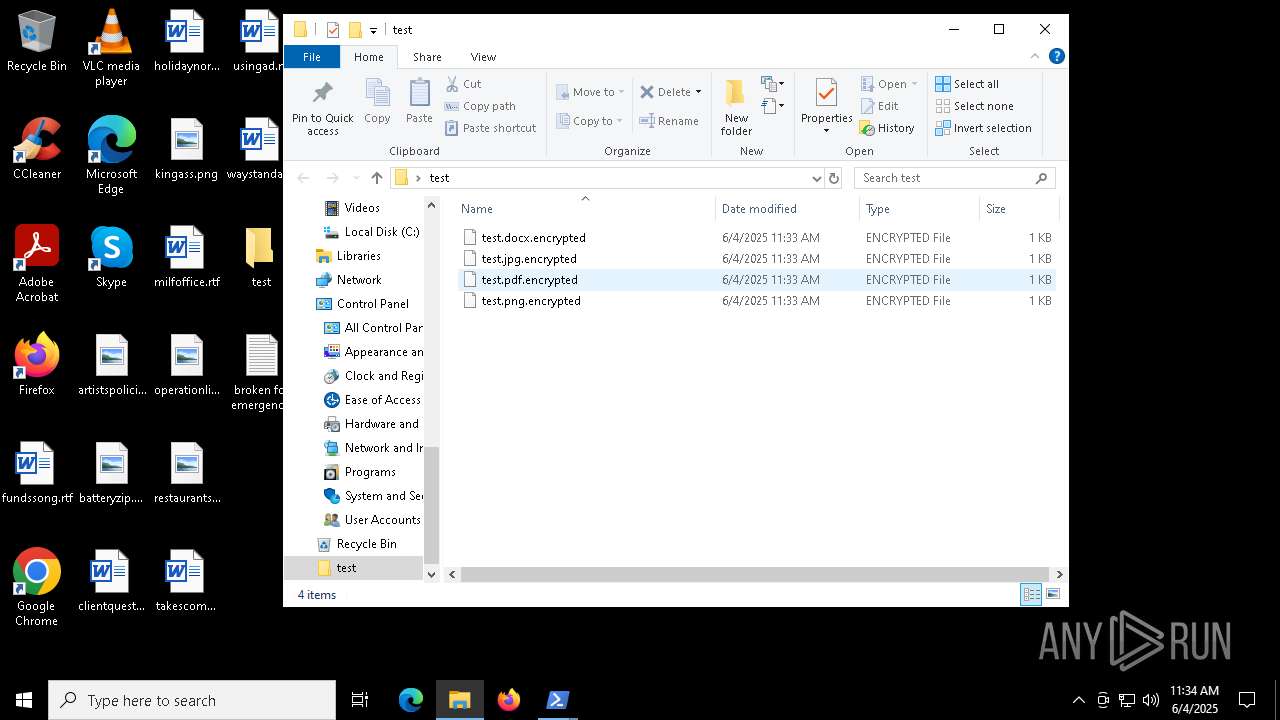
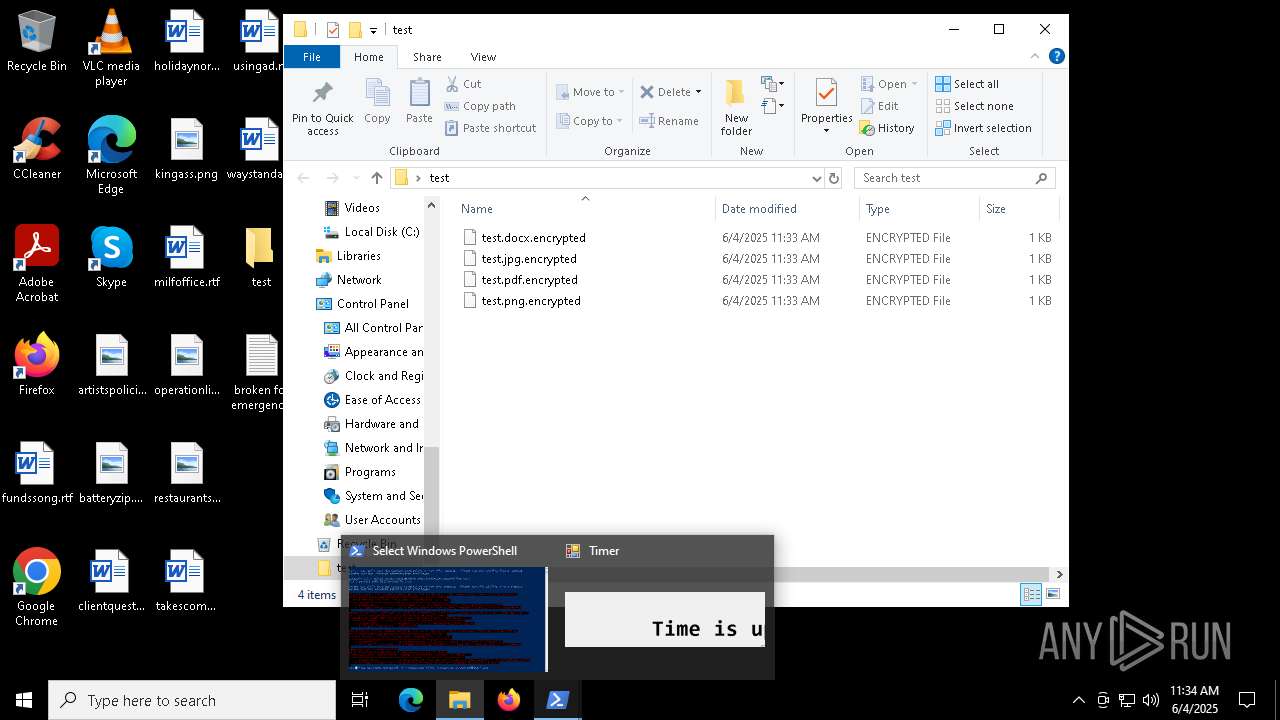
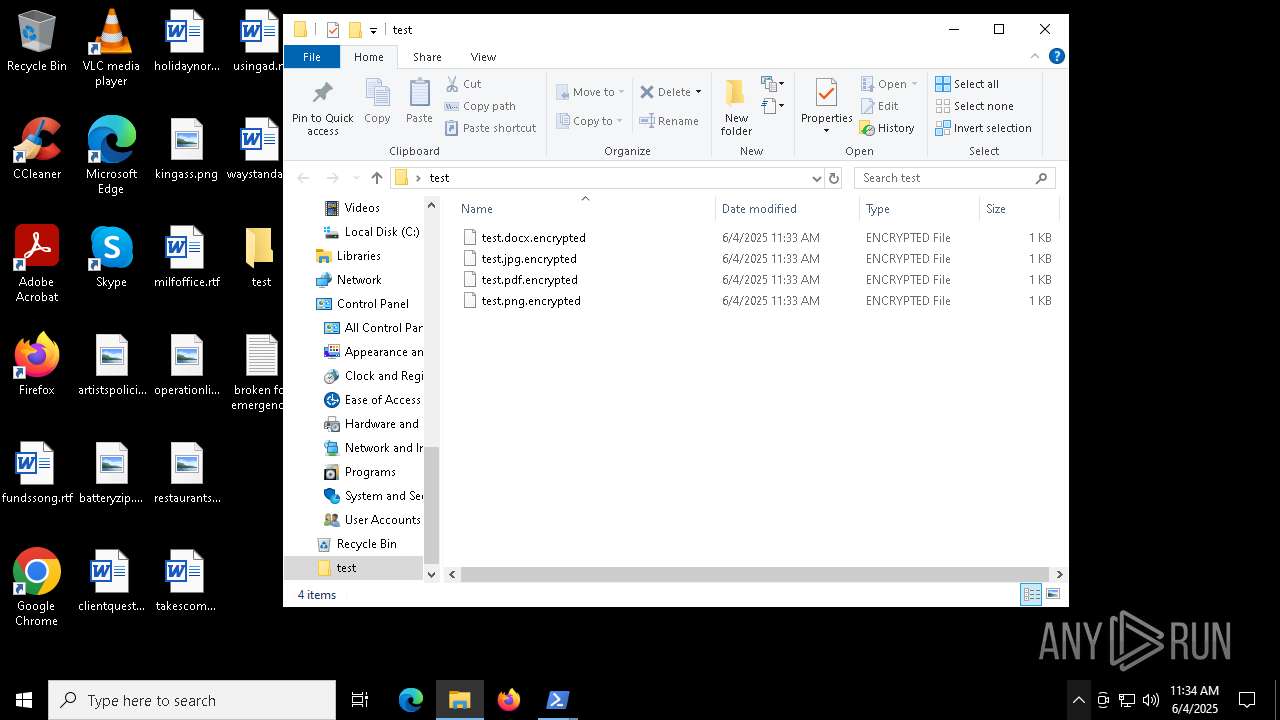
Suspicious files
4
Text files
13
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7800 | powershell.exe | C:\Users\admin\AppData\Local\Temp\setup.exe | — | |
MD5:— | SHA256:— | |||
| 7800 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\MJYZ3E9V2N64VZTBX8WO.temp | binary | |
MD5:9A00D2BEF0F9F6245D486B09CBA77621 | SHA256:AC1498E65608E6F9FFDCA7C6B8A70529F591E6D70FAB02E97C764FF71C00465F | |||
| 7800 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF11f876.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
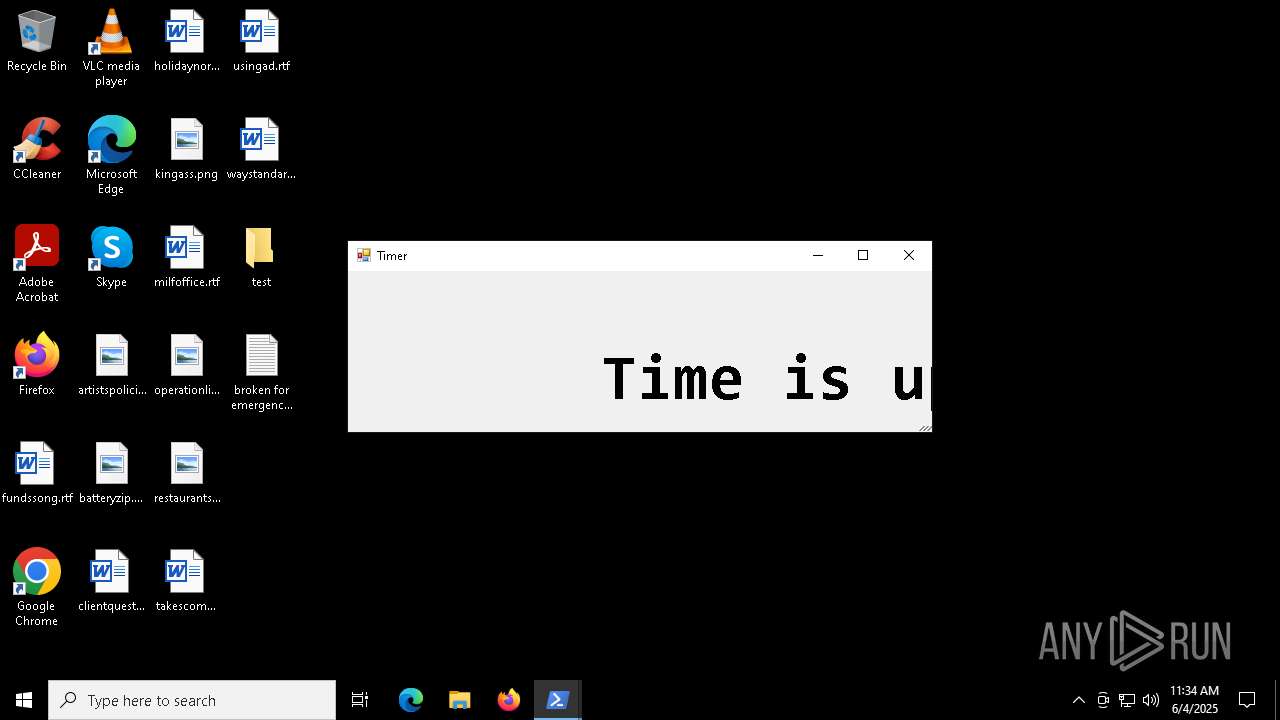
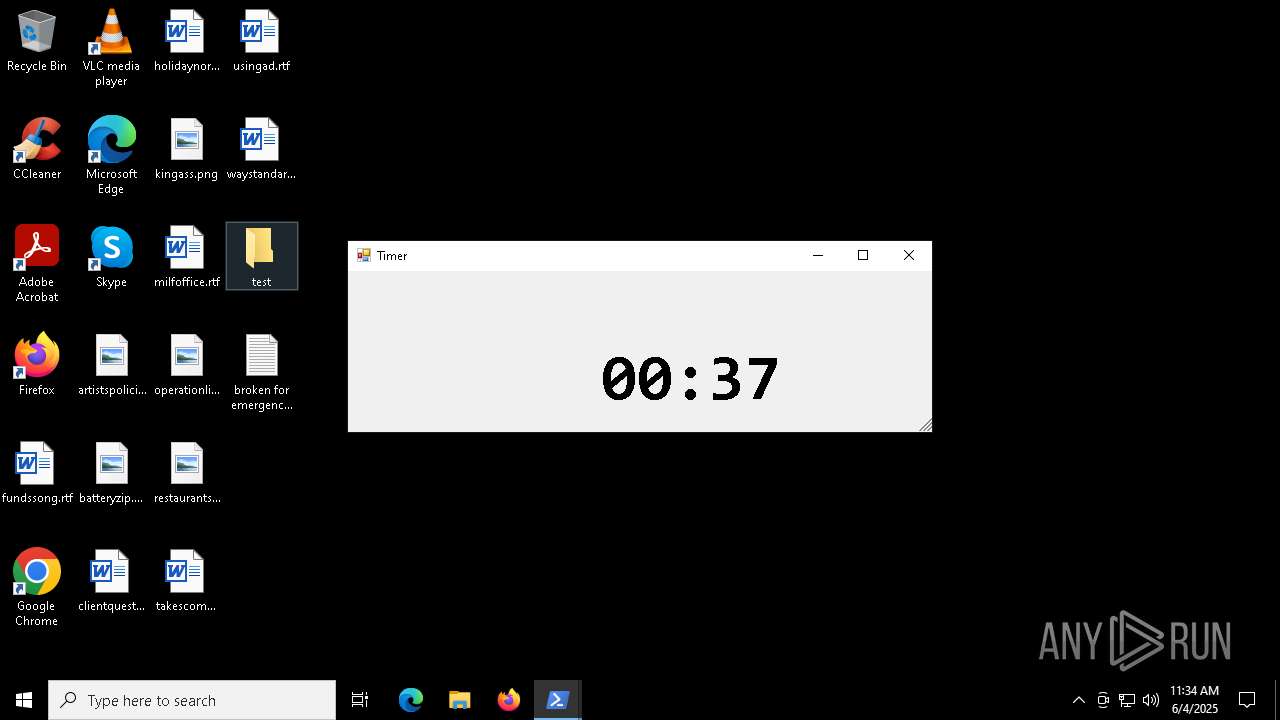
| 7800 | powershell.exe | C:\Users\admin\Desktop\test\test.pdf.encrypted | text | |
MD5:2597AB1E5FDF8CC3B91B716001E2663C | SHA256:4EAACF98CABE3BE51469261CC5E31FCE6DADEBA615A177C9B6DE5617426B8686 | |||
| 7800 | powershell.exe | C:\Users\admin\Desktop\broken for emergency.txt | text | |
MD5:DB210ADFBC1A99954CAB7239A3BF21AE | SHA256:6B3BA754127323FB390516192AC80FECBC921A7BC6CE6090A830BDD980E4C0F5 | |||
| 7800 | powershell.exe | C:\Users\admin\Desktop\test\test.jpg.encrypted | text | |
MD5:1A082AFFEA354808BBDB140B0A67DAED | SHA256:B51613B515BE75C7FC6C44F1FD0338A40629BFC38F1BE9F843C4359ABE0BE221 | |||
| 7800 | powershell.exe | C:\Users\admin\AppData\Local\Temp\gndlrtp3.0.cs | text | |
MD5:CBBDA5834A79677922770BEBAD078D29 | SHA256:844ED19F587B30771C79F21D4CBFC676AAEFC243F893842BC02406E3087CA7F6 | |||
| 7800 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:9A00D2BEF0F9F6245D486B09CBA77621 | SHA256:AC1498E65608E6F9FFDCA7C6B8A70529F591E6D70FAB02E97C764FF71C00465F | |||
| 7800 | powershell.exe | C:\Users\admin\AppData\Local\Temp\gndlrtp3.cmdline | text | |
MD5:0CBA31228983312D1B44308B411DE9AC | SHA256:20F29CD778A422A25F5A419BE816DB9519BEC9B80818A72DF7178CB2E8770E3F | |||
| 7800 | powershell.exe | C:\Users\admin\Desktop\test\test.png.encrypted | text | |
MD5:7541D49B113CC8A962EDF156A4418D4D | SHA256:62EA890551817199C45334CCF38C22BD9B61F1EB3963F289DCCE70031D3581F6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
25
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.32.238.34:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6368 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6368 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.32.238.34:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
864 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5056 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7800 | powershell.exe | 104.26.2.18:443 | www.sentinelone.com | CLOUDFLARENET | US | suspicious |
7800 | powershell.exe | 23.185.0.2:443 | de.sentinelone.com | FASTLY | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
www.sentinelone.com |
| unknown |
de.sentinelone.com |
| unknown |
download.electrum.org |
| whitelisted |
www.torproject.org |
| whitelisted |
dist.torproject.org |
| whitelisted |
login.live.com |
| whitelisted |