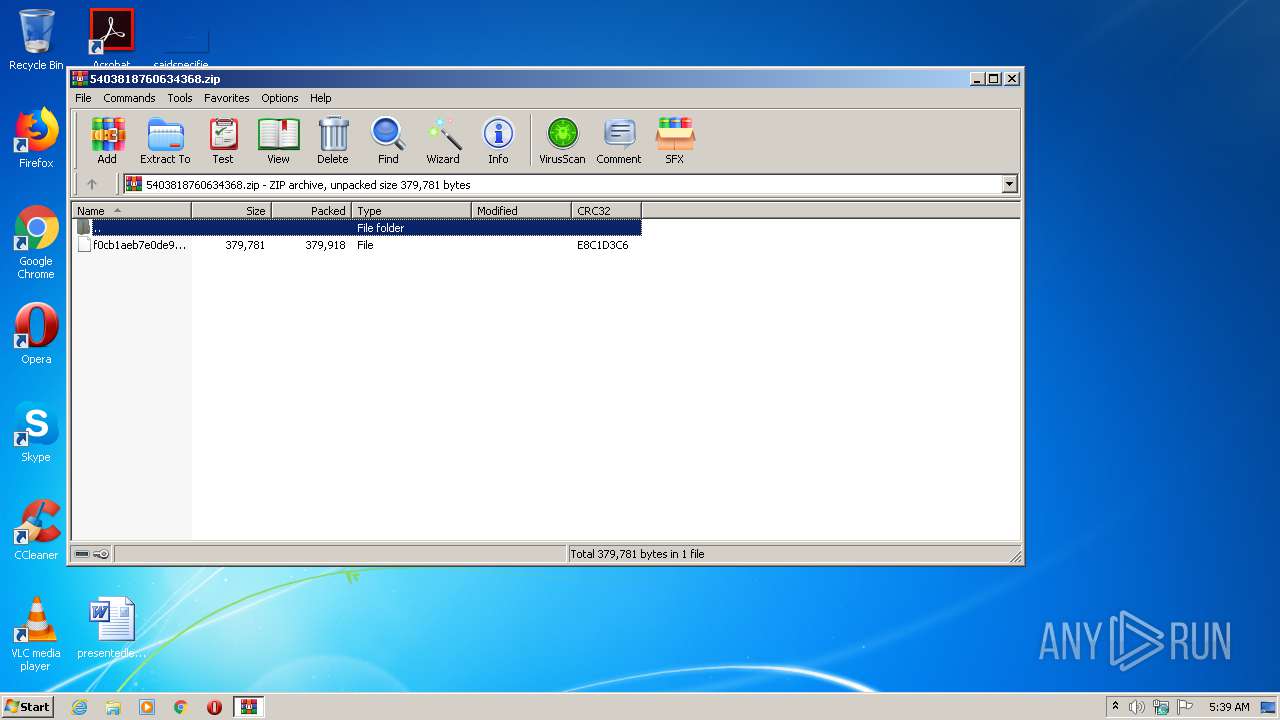
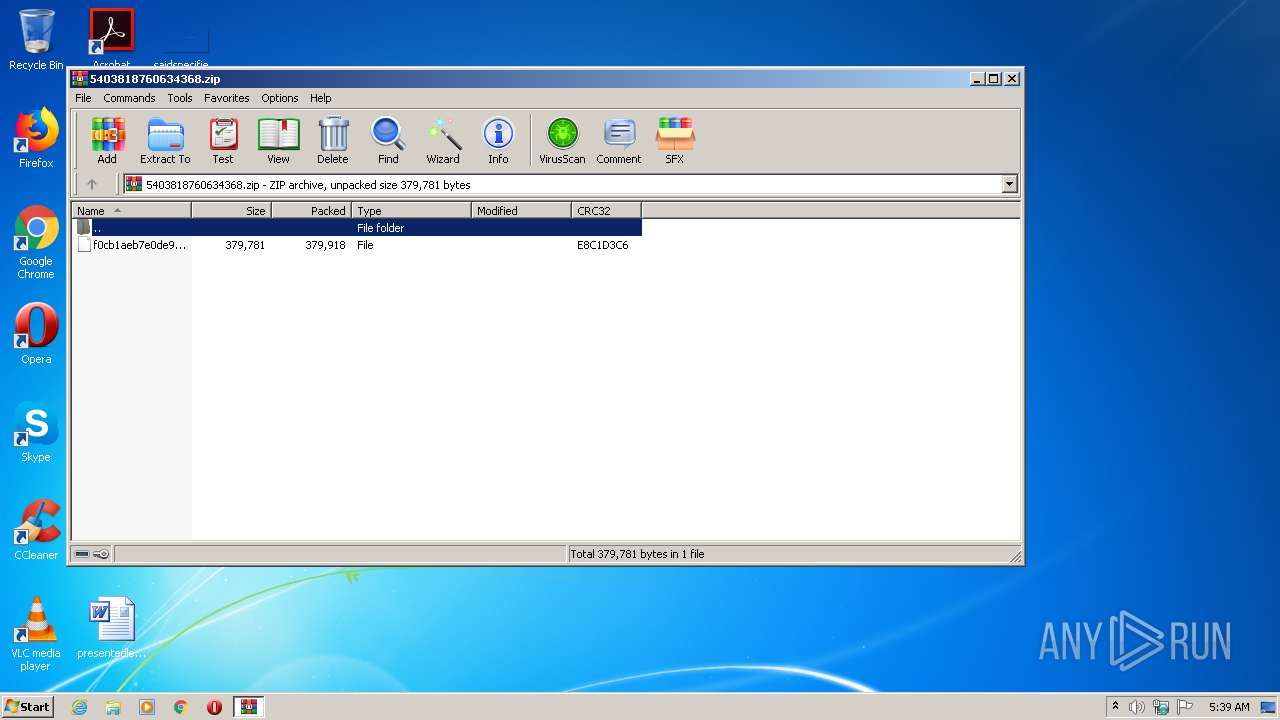
| File name: | 5403818760634368.zip |
| Full analysis: | https://app.any.run/tasks/822dd5f0-af4a-479f-addc-a07fdafcc3b0 |
| Verdict: | Malicious activity |
| Analysis date: | July 13, 2020, 04:39:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | B35EE8FBB7BC3090FC1A897329C2DD42 |
| SHA1: | E80F388CB64810435EE0C12D03FC4657563DDE27 |
| SHA256: | D21B1A065761715B5E3DCC2546C70D32CD340BAB6E3D2E6CC0E3BA090F3AFB1A |
| SSDEEP: | 6144:Bpo+GiHwnyYDxJJT5Dq7MudT6E5iEFhcgfh30x3k8zDGRfRHSf1epoWFZB+:lHwnyCXJT5Dwd5RFh7Jkx3WfY9eyWB+ |
MALICIOUS
Application was dropped or rewritten from another process
- ITIALIA SEPA PRODUCTZION REQQUEST FOR COV-19.exe (PID: 440)
- RegSvcs.exe (PID: 2688)
Changes the autorun value in the registry
- RegSvcs.exe (PID: 2688)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 284)
Uses Task Scheduler to run other applications
- ITIALIA SEPA PRODUCTZION REQQUEST FOR COV-19.exe (PID: 440)
Actions looks like stealing of personal data
- RegSvcs.exe (PID: 2688)
SUSPICIOUS
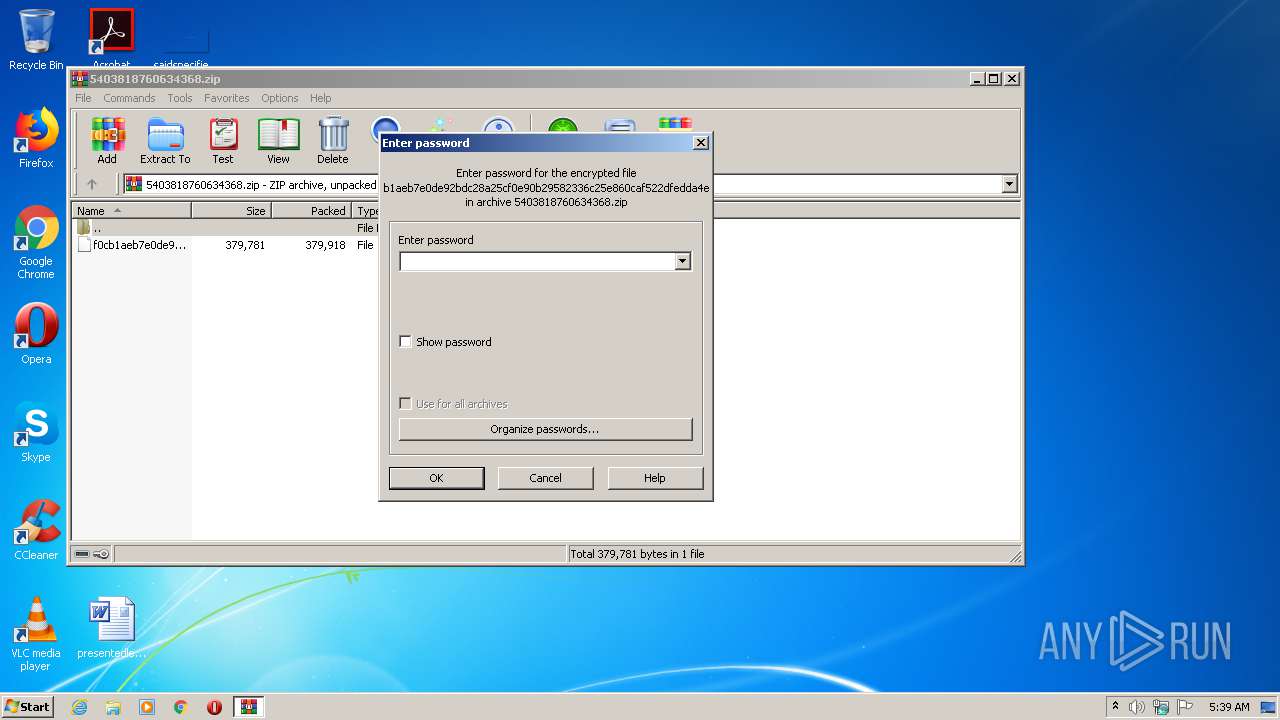
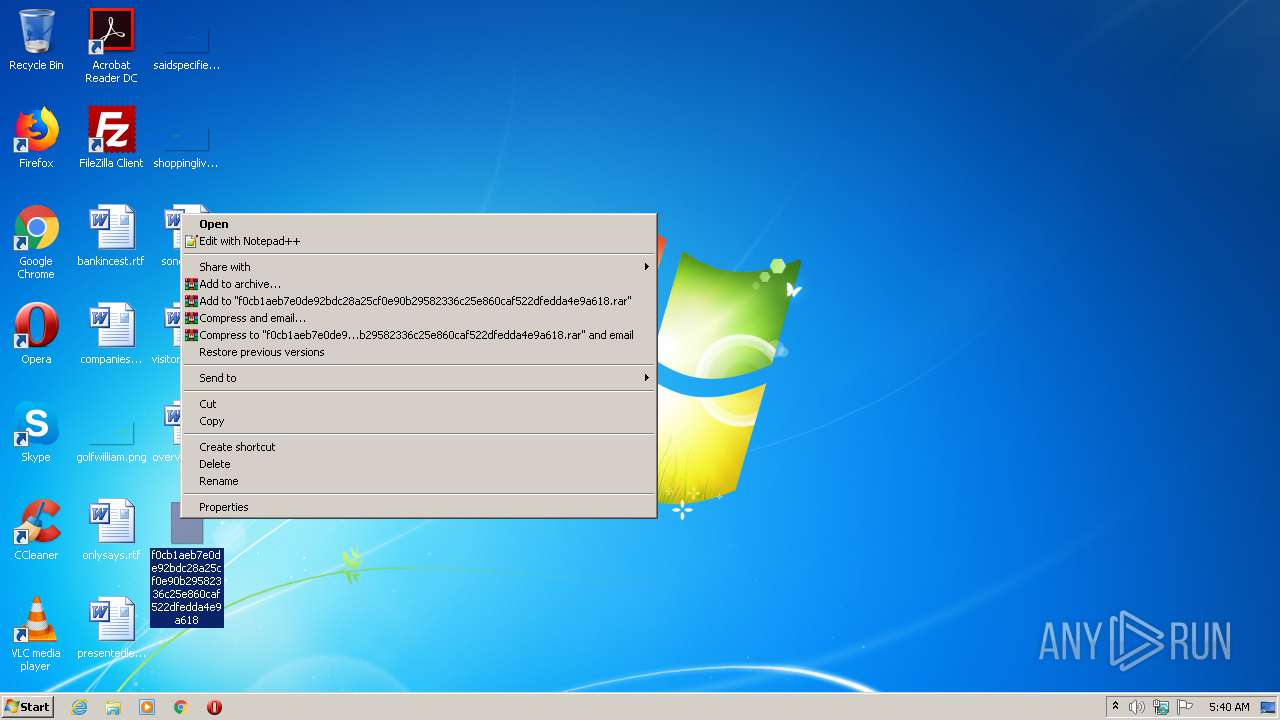
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2496)
- RegSvcs.exe (PID: 2688)
- ITIALIA SEPA PRODUCTZION REQQUEST FOR COV-19.exe (PID: 440)
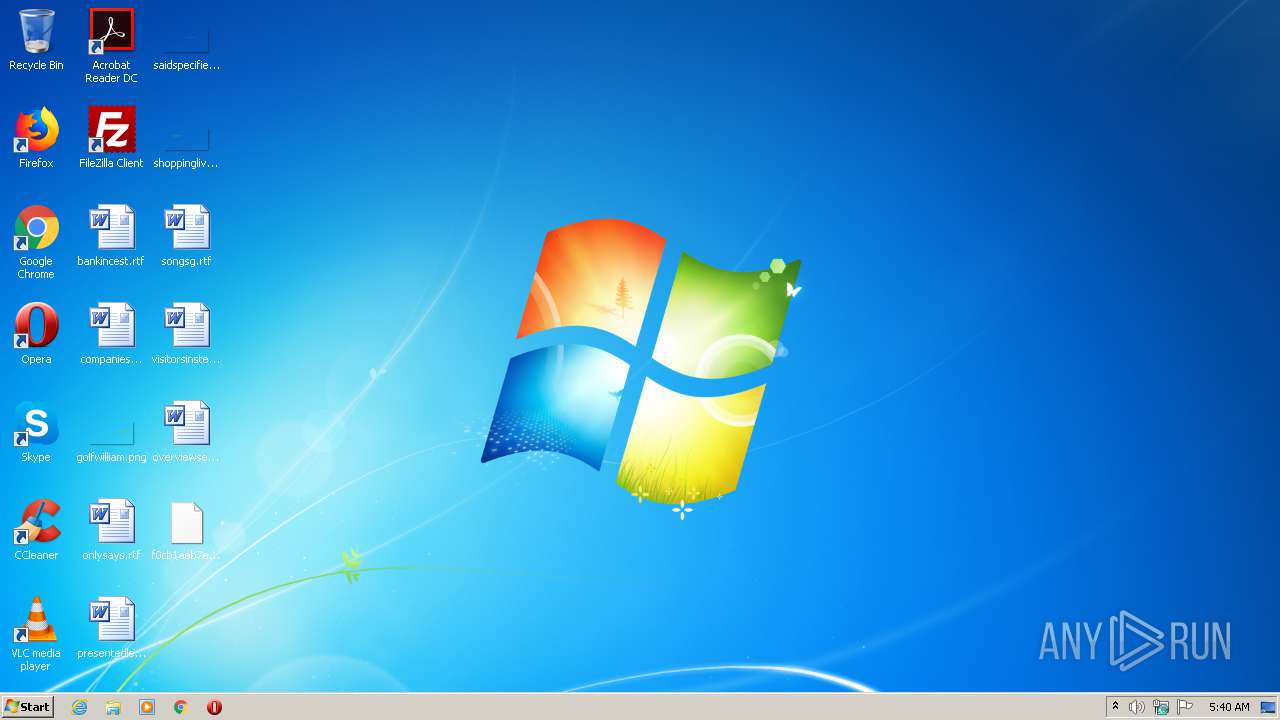
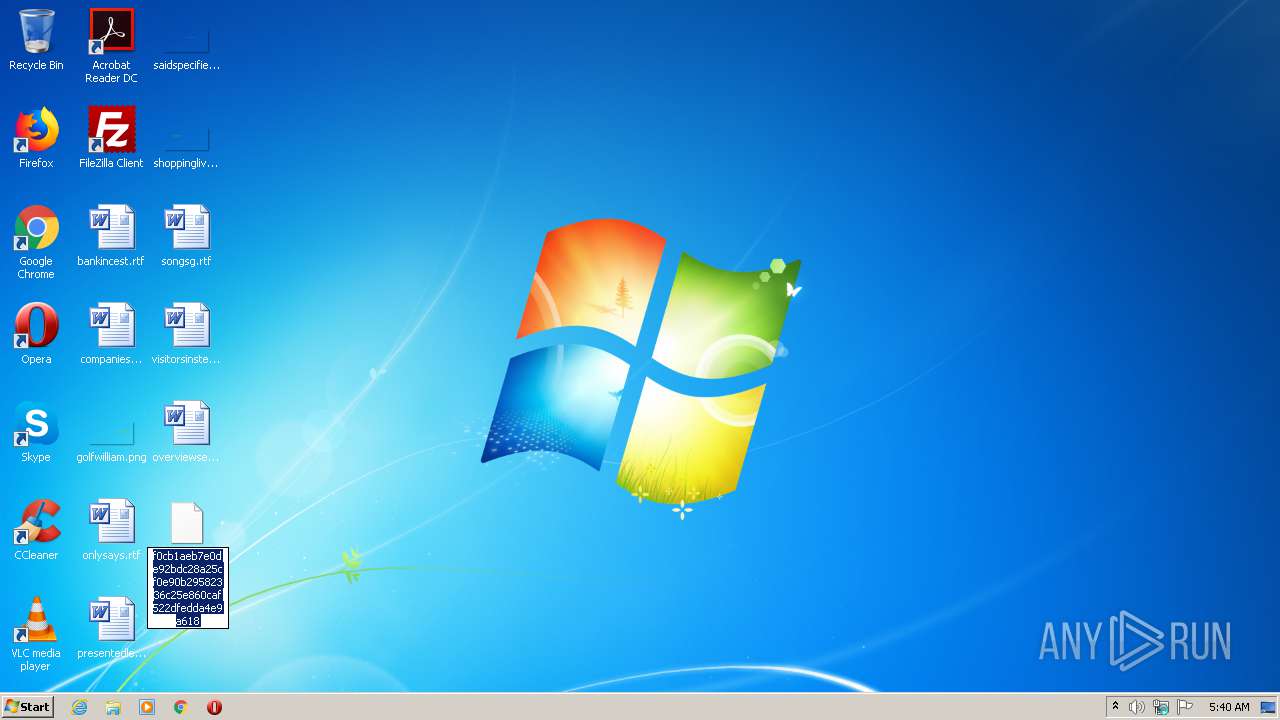
Creates files in the user directory
- RegSvcs.exe (PID: 2688)
- ITIALIA SEPA PRODUCTZION REQQUEST FOR COV-19.exe (PID: 440)
Reads the cookies of Google Chrome
- RegSvcs.exe (PID: 2688)
Reads the cookies of Mozilla Firefox
- RegSvcs.exe (PID: 2688)
INFO
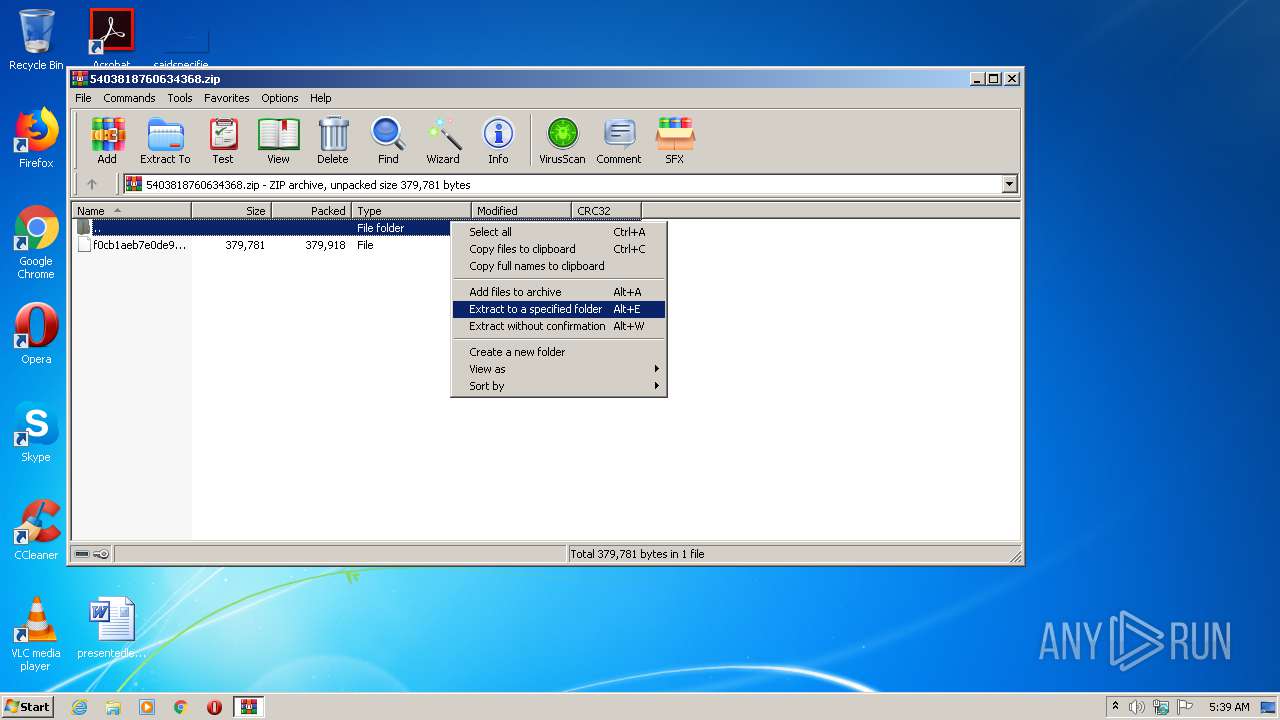
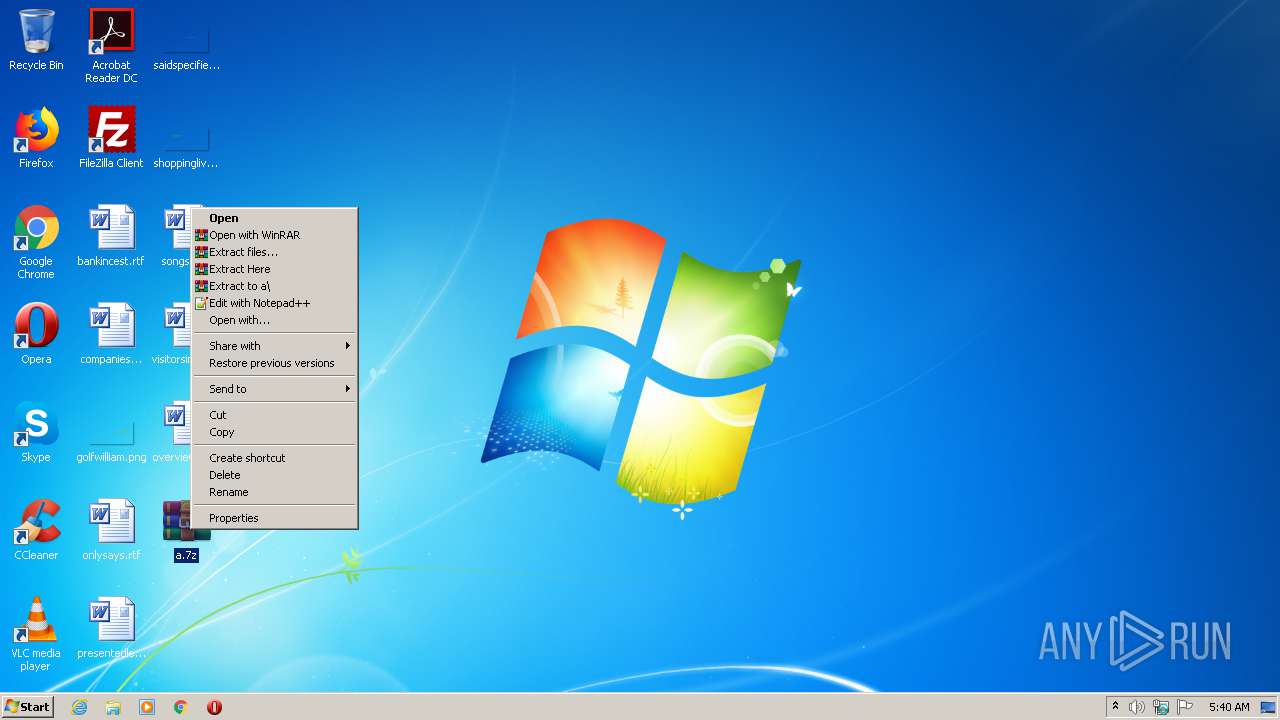
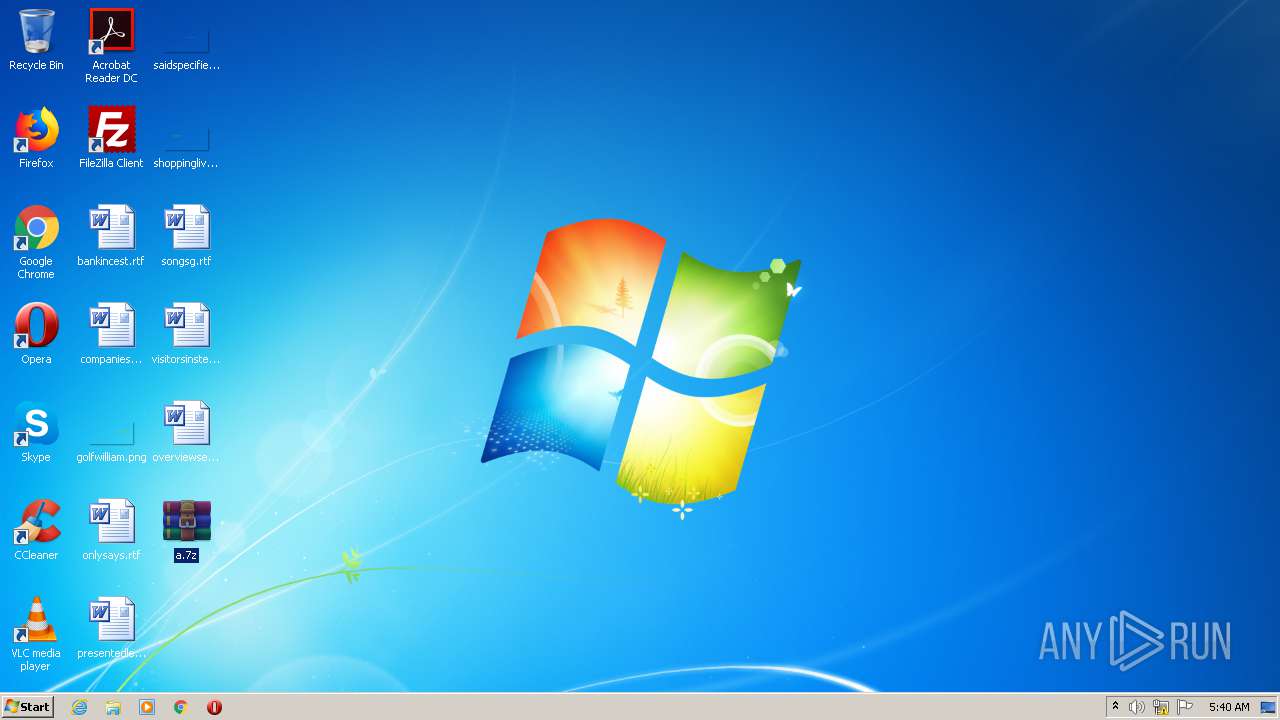
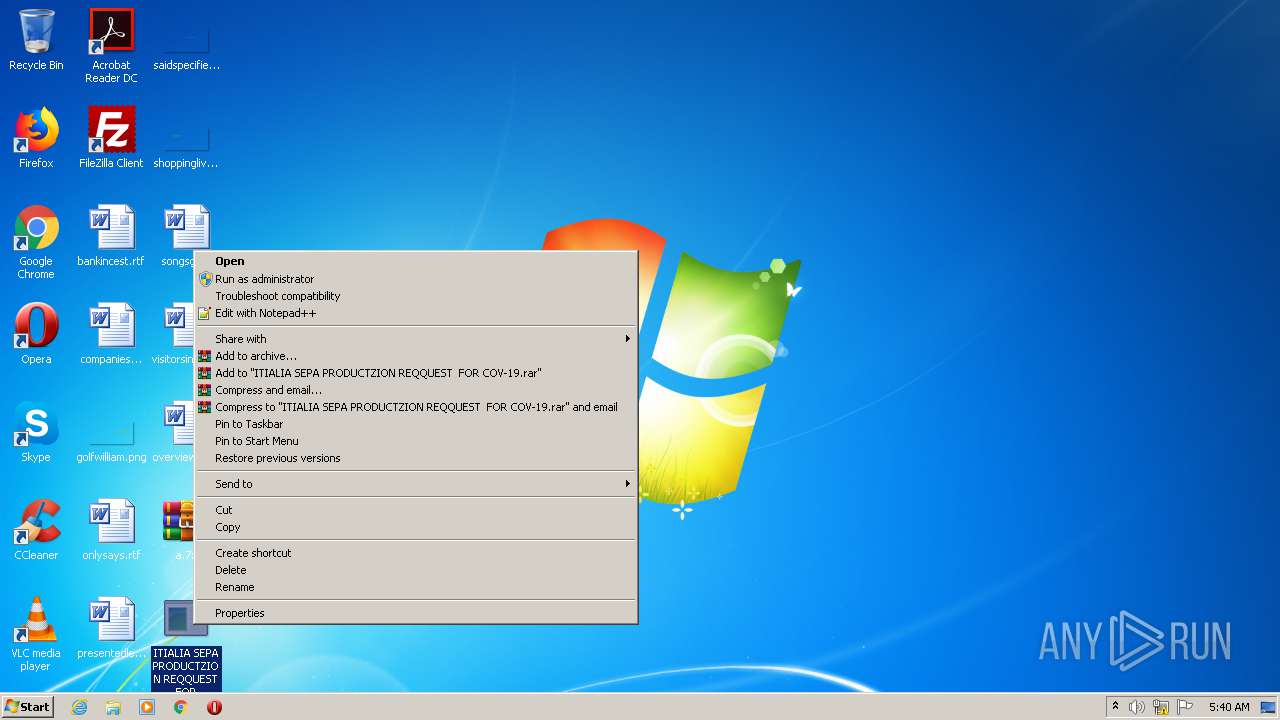
Manual execution by user
- WinRAR.exe (PID: 2496)
- ITIALIA SEPA PRODUCTZION REQQUEST FOR COV-19.exe (PID: 440)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:00:00 00:00:00 |
| ZipCRC: | 0xe8c1d3c6 |
| ZipCompressedSize: | 379918 |
| ZipUncompressedSize: | 379781 |
| ZipFileName: | f0cb1aeb7e0de92bdc28a25cf0e90b29582336c25e860caf522dfedda4e9a618 |
Total processes
45
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | "C:\Windows\System32\schtasks.exe" /Create /TN "Updates\FhbBRqFVJ" /XML "C:\Users\admin\AppData\Local\Temp\tmpC987.tmp" | C:\Windows\System32\schtasks.exe | — | ITIALIA SEPA PRODUCTZION REQQUEST FOR COV-19.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 440 | "C:\Users\admin\Desktop\ITIALIA SEPA PRODUCTZION REQQUEST FOR COV-19.exe" | C:\Users\admin\Desktop\ITIALIA SEPA PRODUCTZION REQQUEST FOR COV-19.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: HIGH Description: DangNhap Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
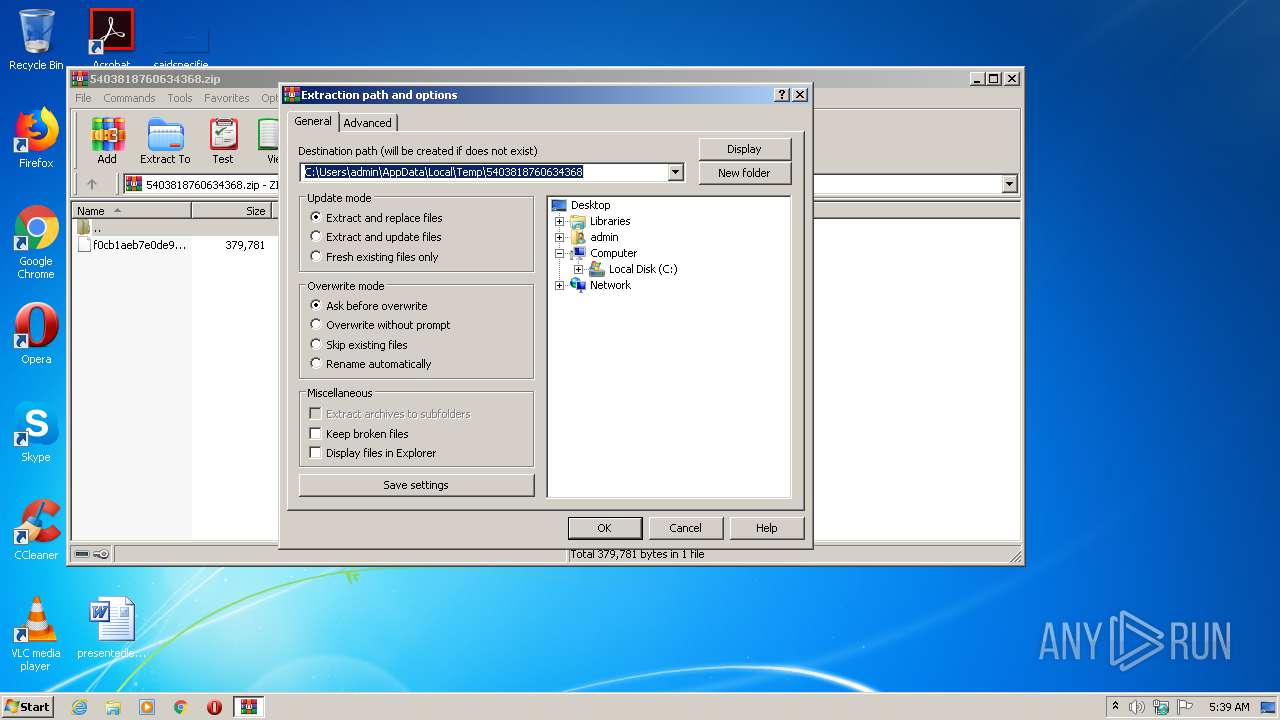
| 688 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\5403818760634368.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2496 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\a.7z" C:\Users\admin\Desktop\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2688 | "{path}" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegSvcs.exe | ITIALIA SEPA PRODUCTZION REQQUEST FOR COV-19.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Services Installation Utility Exit code: 0 Version: 2.0.50727.5420 (Win7SP1.050727-5400) Modules
| |||||||||||||||
Total events
616
Read events
570
Write events
46
Delete events
0
Modification events
| (PID) Process: | (688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (688) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (688) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\5403818760634368.zip | |||
| (PID) Process: | (688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
Executable files
3
Suspicious files
2
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2688 | RegSvcs.exe | C:\Users\admin\AppData\Roaming\sbclhapz.wwp\Chrome\Default\Cookies | — | |
MD5:— | SHA256:— | |||
| 2688 | RegSvcs.exe | C:\Users\admin\AppData\Roaming\sbclhapz.wwp\Firefox\Profiles\qldyz51w.default\cookies.sqlite | — | |
MD5:— | SHA256:— | |||
| 2688 | RegSvcs.exe | C:\Users\admin\AppData\Roaming\sbclhapz.wwp.zip | compressed | |
MD5:— | SHA256:— | |||
| 688 | WinRAR.exe | C:\Users\admin\Desktop\f0cb1aeb7e0de92bdc28a25cf0e90b29582336c25e860caf522dfedda4e9a618 | compressed | |
MD5:— | SHA256:— | |||
| 2688 | RegSvcs.exe | C:\Users\admin\AppData\Roaming\VWTxoTc\ERZmR.exe | executable | |
MD5:— | SHA256:— | |||
| 440 | ITIALIA SEPA PRODUCTZION REQQUEST FOR COV-19.exe | C:\Users\admin\AppData\Roaming\FhbBRqFVJ.exe | executable | |
MD5:6F9604CC2089A0C40731CB83274BA2DC | SHA256:6DA72872F9D948174753C156B916DCE48B56107B2C7759C04BE6667595CAD852 | |||
| 2496 | WinRAR.exe | C:\Users\admin\Desktop\ITIALIA SEPA PRODUCTZION REQQUEST FOR COV-19.exe | executable | |
MD5:6F9604CC2089A0C40731CB83274BA2DC | SHA256:6DA72872F9D948174753C156B916DCE48B56107B2C7759C04BE6667595CAD852 | |||
| 440 | ITIALIA SEPA PRODUCTZION REQQUEST FOR COV-19.exe | C:\Users\admin\AppData\Local\Temp\tmpC987.tmp | xml | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
1
Threats
2
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2688 | RegSvcs.exe | 207.191.38.36:21 | ftp.fox8live.com | Level 3 Communications, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ftp.fox8live.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2688 | RegSvcs.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2688 | RegSvcs.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |