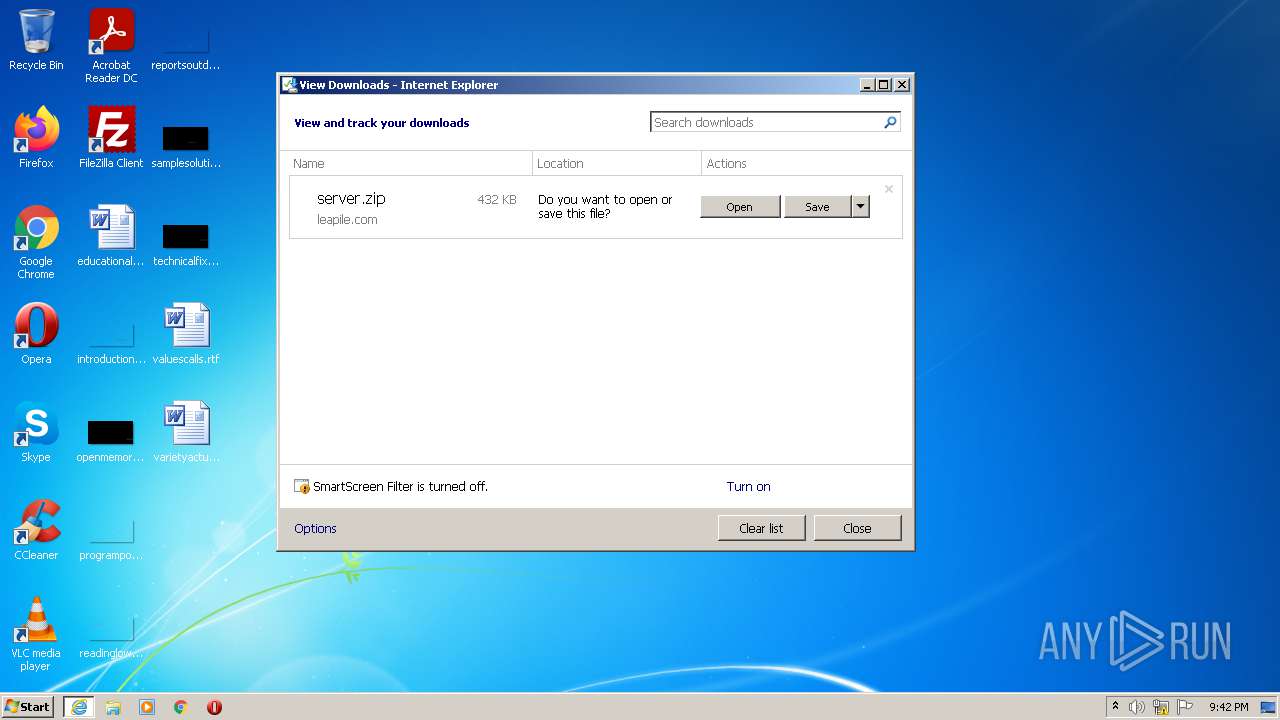
| URL: | http://bit.ly/2tjZjFZ |
| Full analysis: | https://app.any.run/tasks/821c69f1-e372-4a59-9e1a-b3ef1323daa4 |
| Verdict: | Malicious activity |
| Analysis date: | July 12, 2021, 20:42:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 8C68790730420429099C143BB7D1AF6B |
| SHA1: | E8B34542BE895ECFDCE47C73ACBE28F390A3B0FF |
| SHA256: | D21856934A160F5CE1872C380AF7FB02AD5873290596A54595363087D084F584 |
| SSDEEP: | 3:N1KcQ9TRPj:CcYRPj |
MALICIOUS
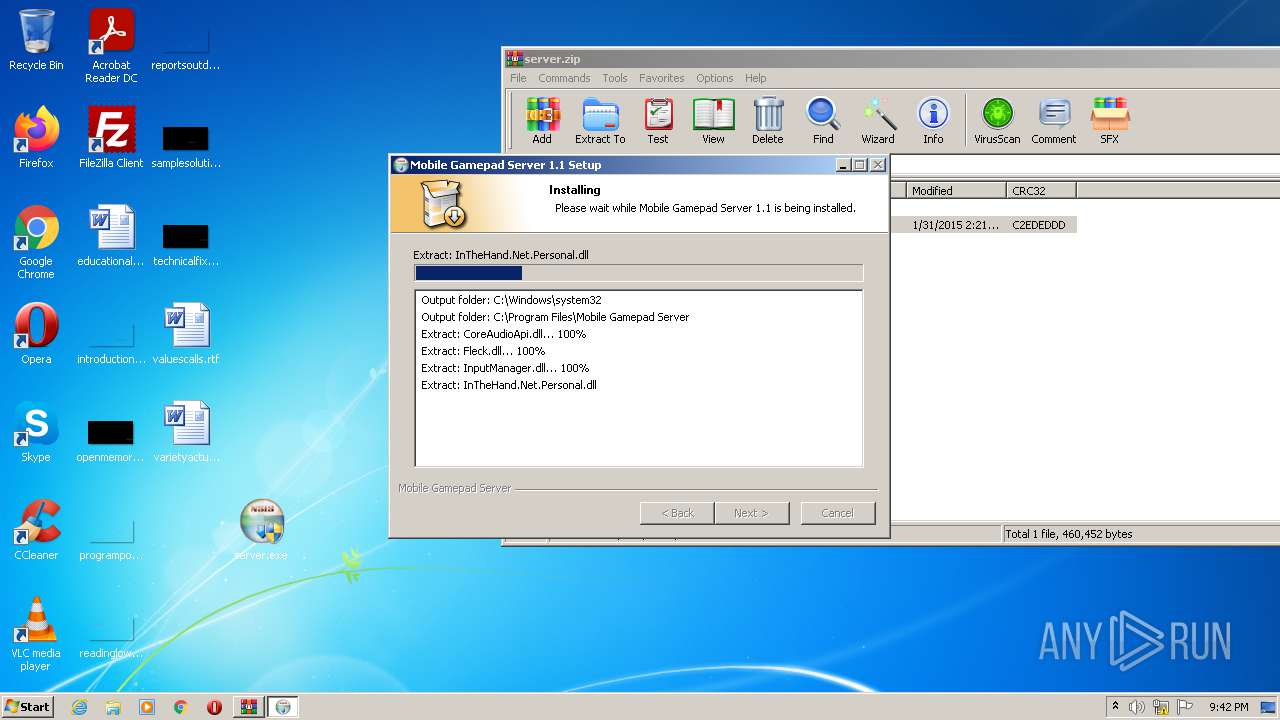
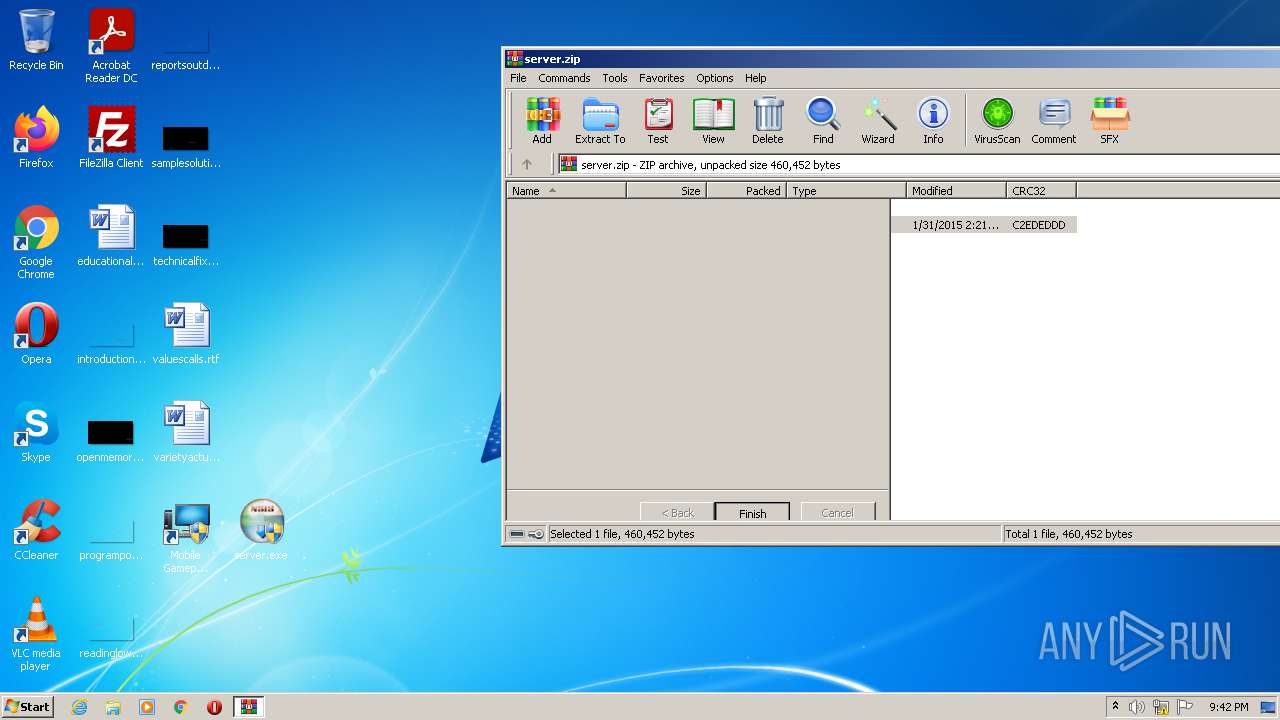
Application was dropped or rewritten from another process
- server.exe (PID: 3708)
- server.exe (PID: 2996)
- Mobile Gamepad.exe (PID: 2696)
Drops executable file immediately after starts
- server.exe (PID: 3708)
Loads dropped or rewritten executable
- server.exe (PID: 3708)
- Mobile Gamepad.exe (PID: 2696)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3792)
Reads the computer name
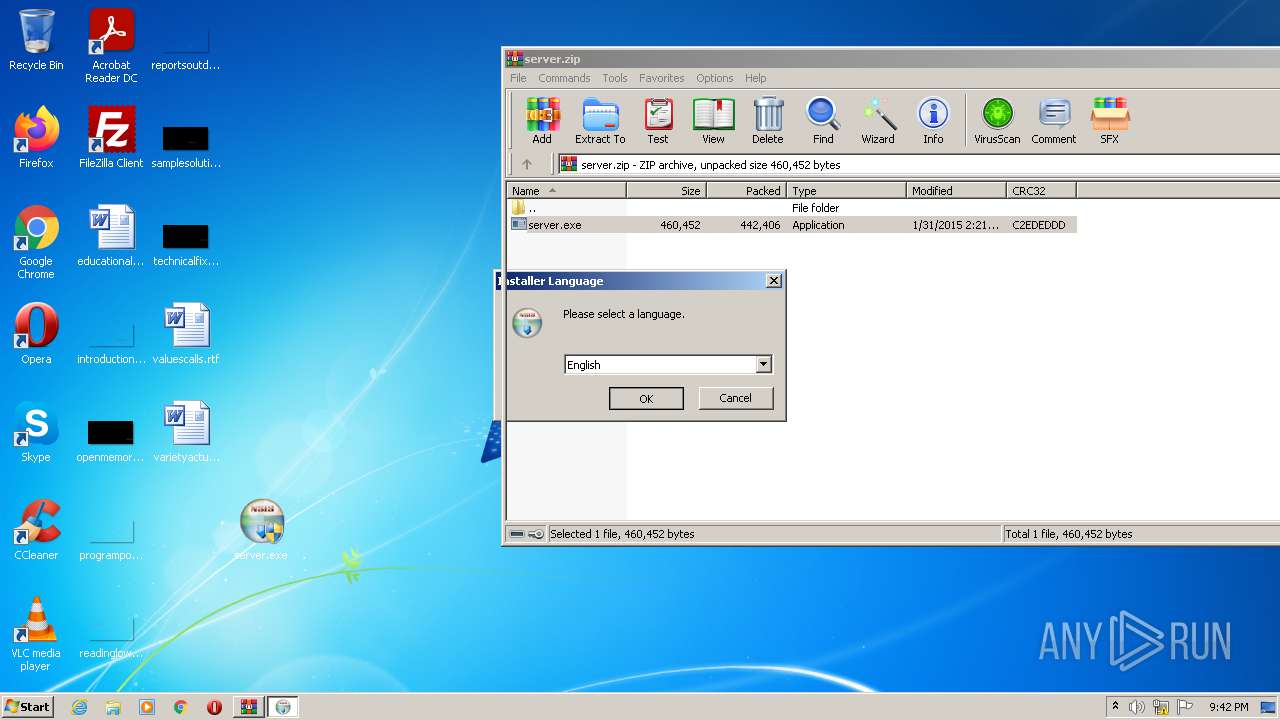
- WinRAR.exe (PID: 3228)
- Mobile Gamepad.exe (PID: 2696)
- server.exe (PID: 3708)
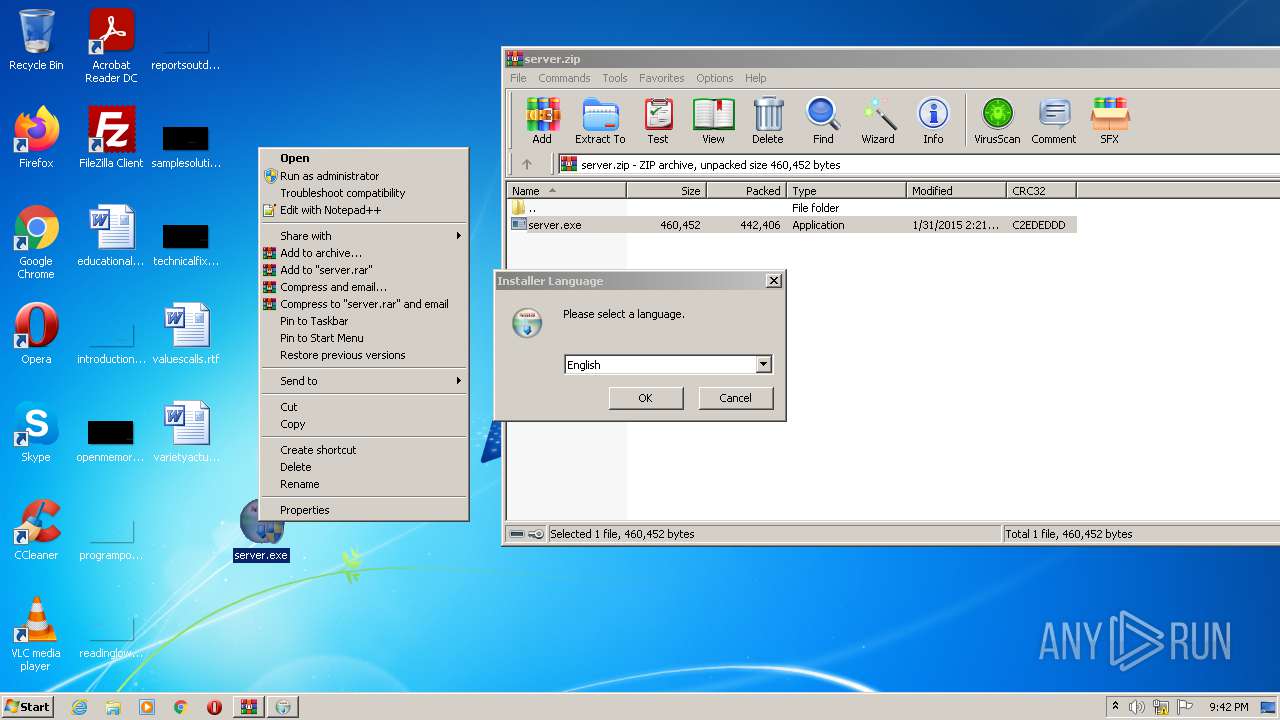
Checks supported languages
- WinRAR.exe (PID: 3228)
- Mobile Gamepad.exe (PID: 2696)
- server.exe (PID: 3708)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3228)
- server.exe (PID: 3708)
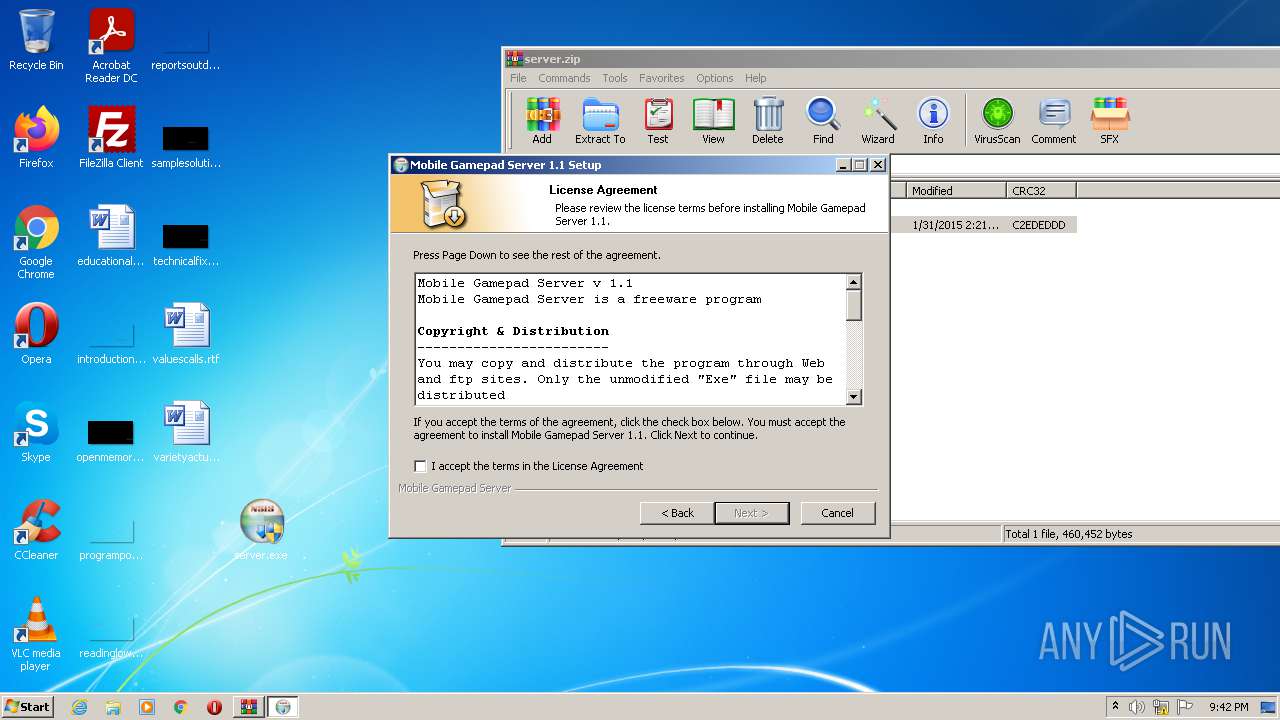
Drops a file with too old compile date
- WinRAR.exe (PID: 3228)
- server.exe (PID: 3708)
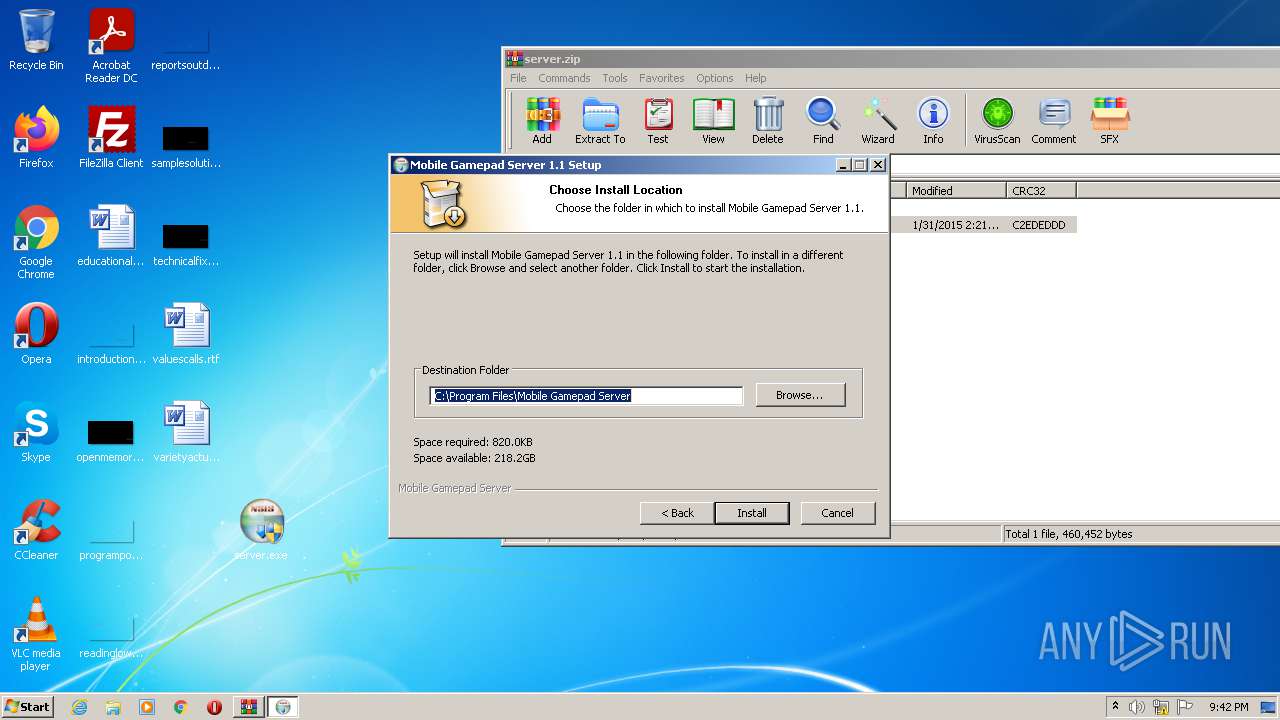
Creates files in the program directory
- server.exe (PID: 3708)
Creates a directory in Program Files
- server.exe (PID: 3708)
Creates a software uninstall entry
- server.exe (PID: 3708)
Drops a file that was compiled in debug mode
- server.exe (PID: 3708)
Creates files in the user directory
- Mobile Gamepad.exe (PID: 2696)
INFO
Reads the computer name
- iexplore.exe (PID: 340)
- iexplore.exe (PID: 3792)
Checks supported languages
- iexplore.exe (PID: 3792)
- iexplore.exe (PID: 340)
Application launched itself
- iexplore.exe (PID: 340)
Changes internet zones settings
- iexplore.exe (PID: 340)
Creates files in the user directory
- iexplore.exe (PID: 3792)
Checks Windows Trust Settings
- iexplore.exe (PID: 3792)
- iexplore.exe (PID: 340)
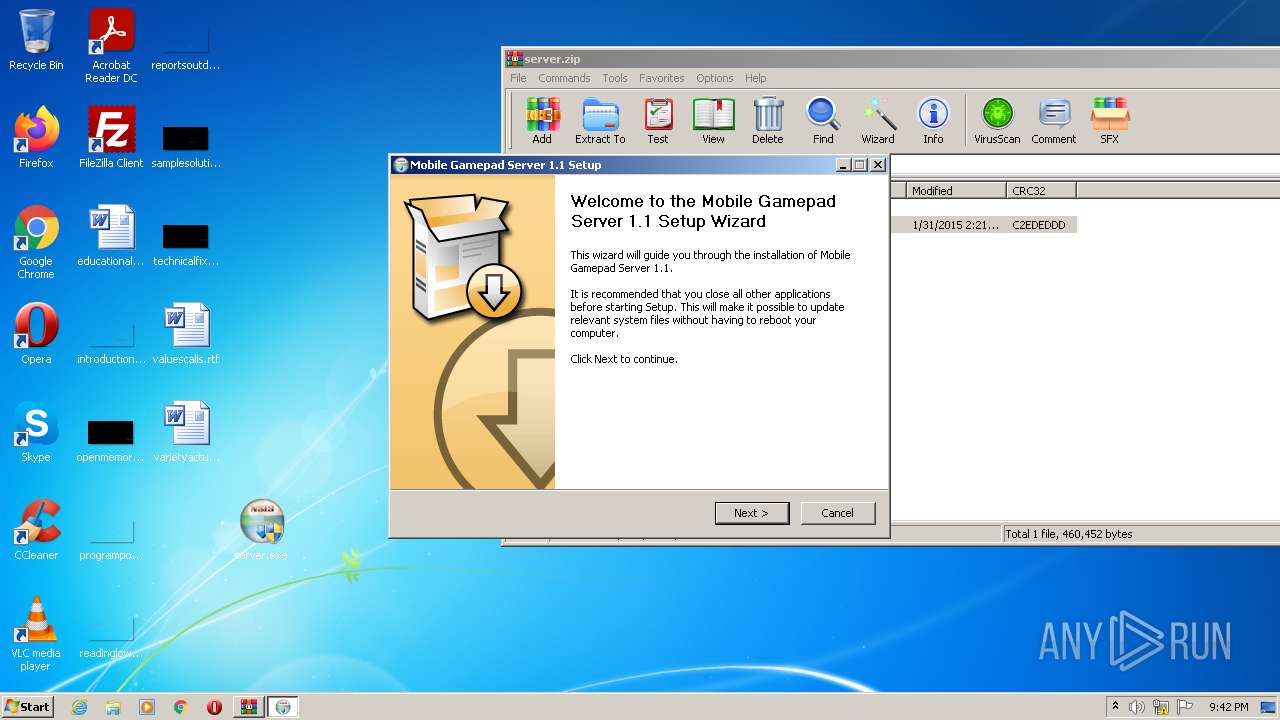
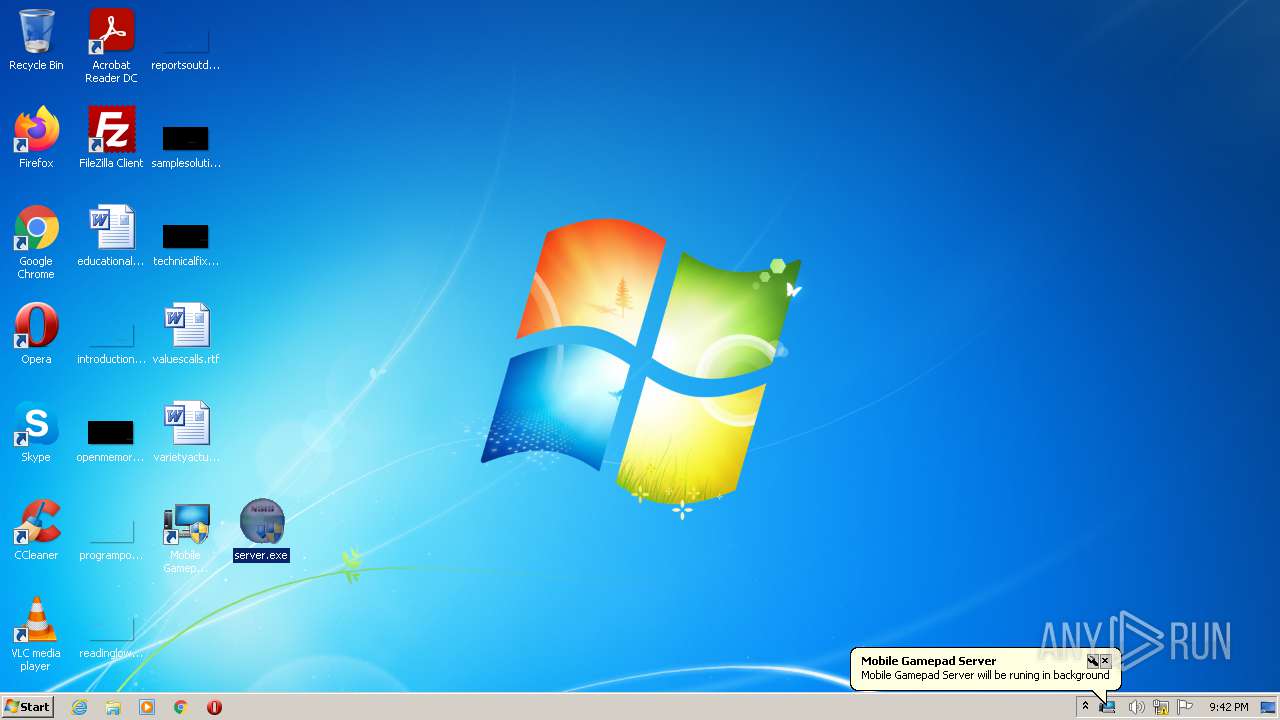
Manual execution by user
- server.exe (PID: 2996)
- server.exe (PID: 3708)
Reads settings of System Certificates
- iexplore.exe (PID: 3792)
- iexplore.exe (PID: 340)
Modifies the phishing filter of IE
- iexplore.exe (PID: 340)
Reads the date of Windows installation
- iexplore.exe (PID: 340)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
44
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 340 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://bit.ly/2tjZjFZ" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
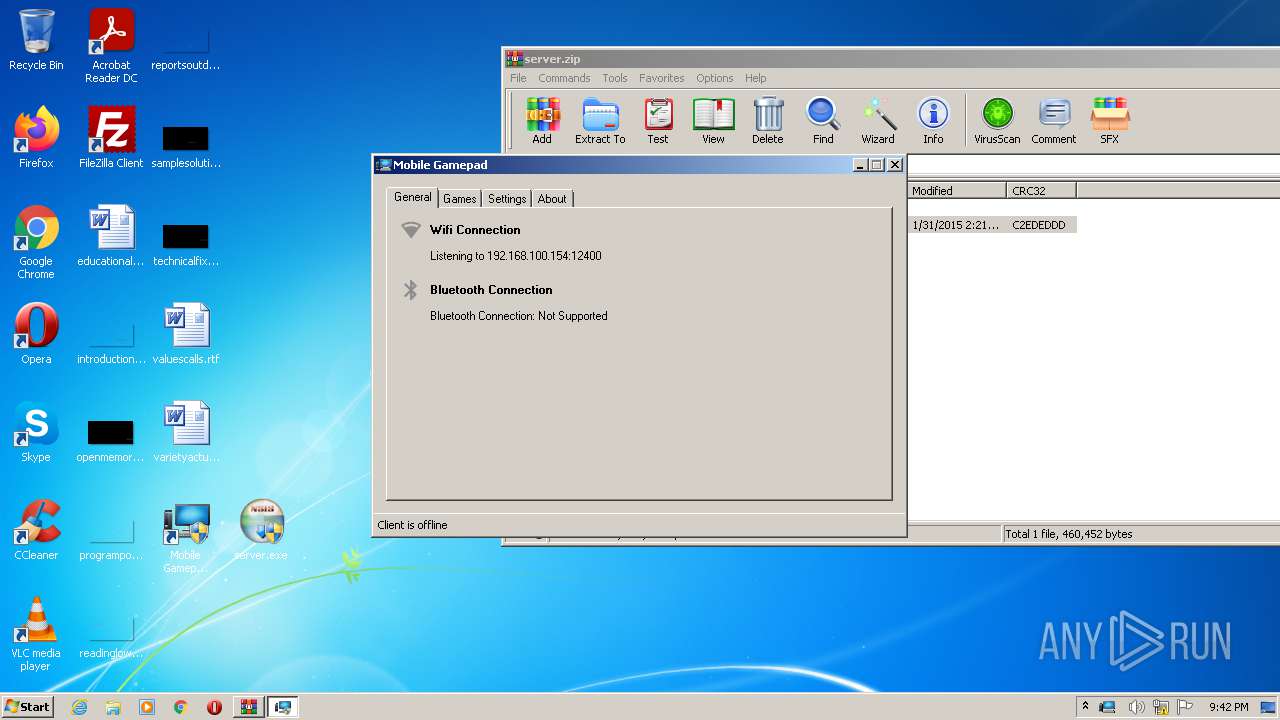
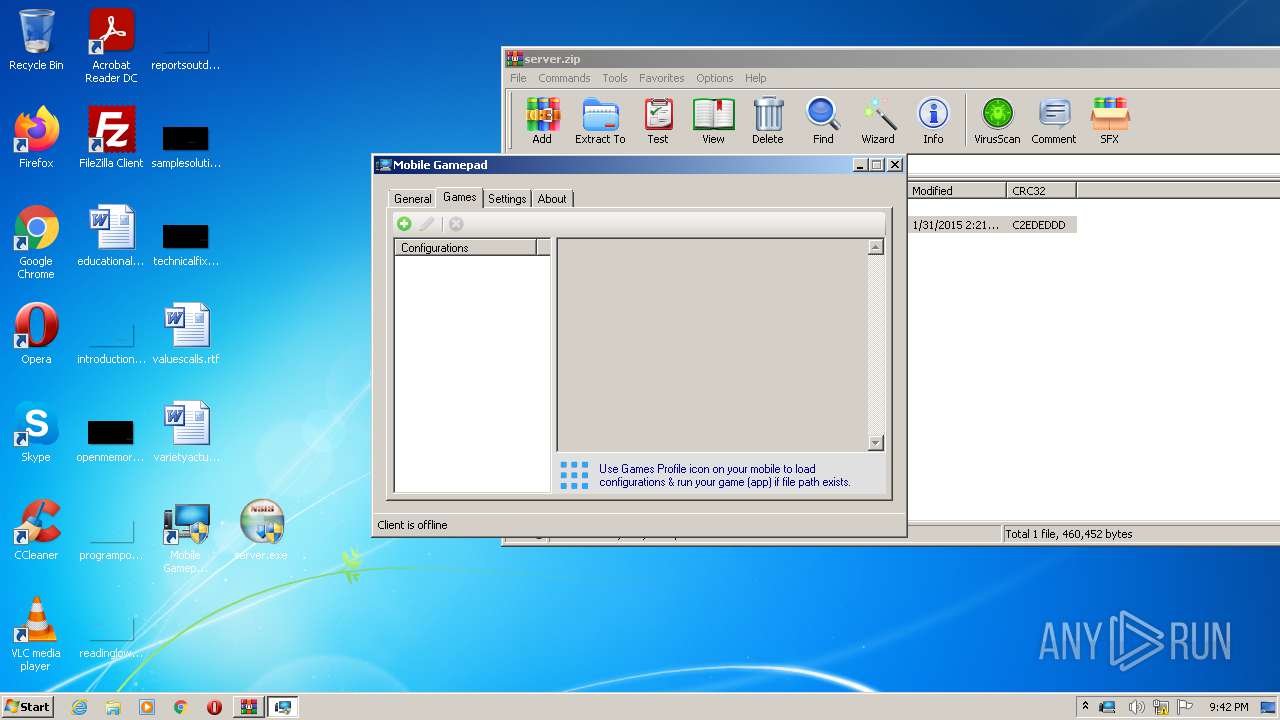
| 2696 | "C:\Program Files\Mobile Gamepad Server\Mobile Gamepad.exe" | C:\Program Files\Mobile Gamepad Server\Mobile Gamepad.exe | server.exe | ||||||||||||
User: admin Company: MMH Dev Integrity Level: HIGH Description: Mobile Gamepad Exit code: 0 Version: 1.1.0.0 Modules
| |||||||||||||||
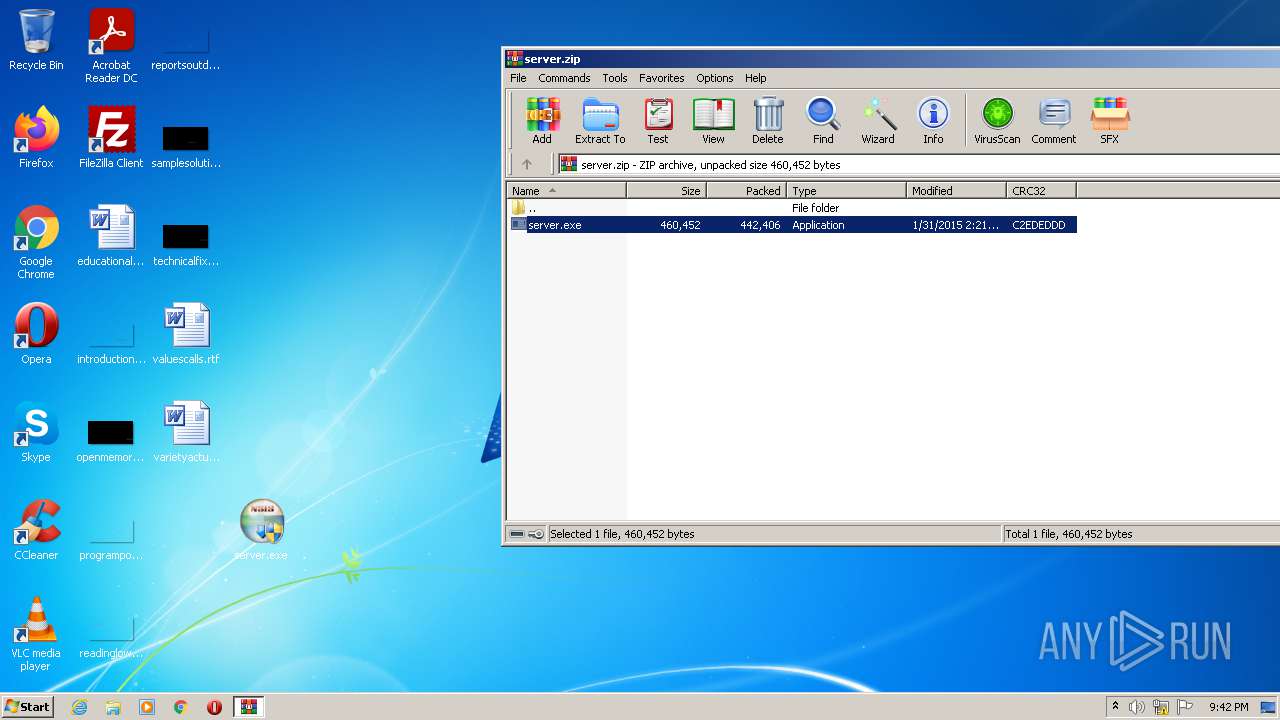
| 2996 | "C:\Users\admin\Desktop\server.exe" | C:\Users\admin\Desktop\server.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
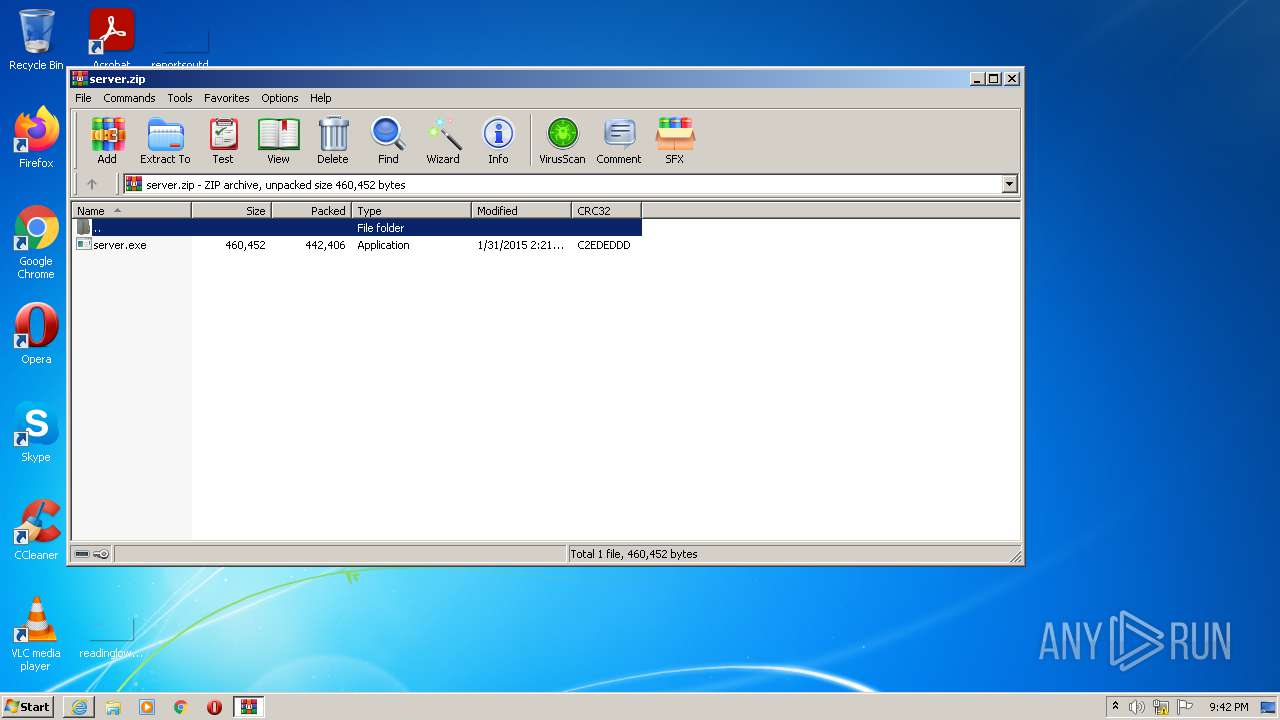
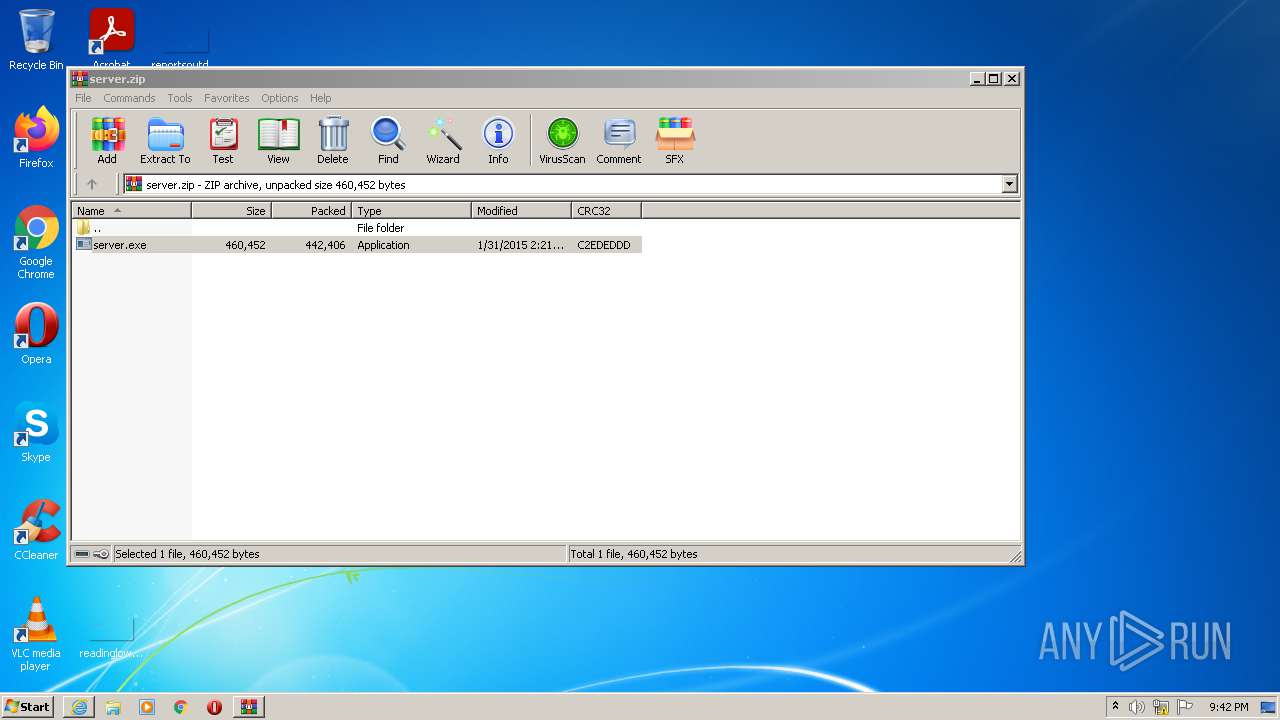
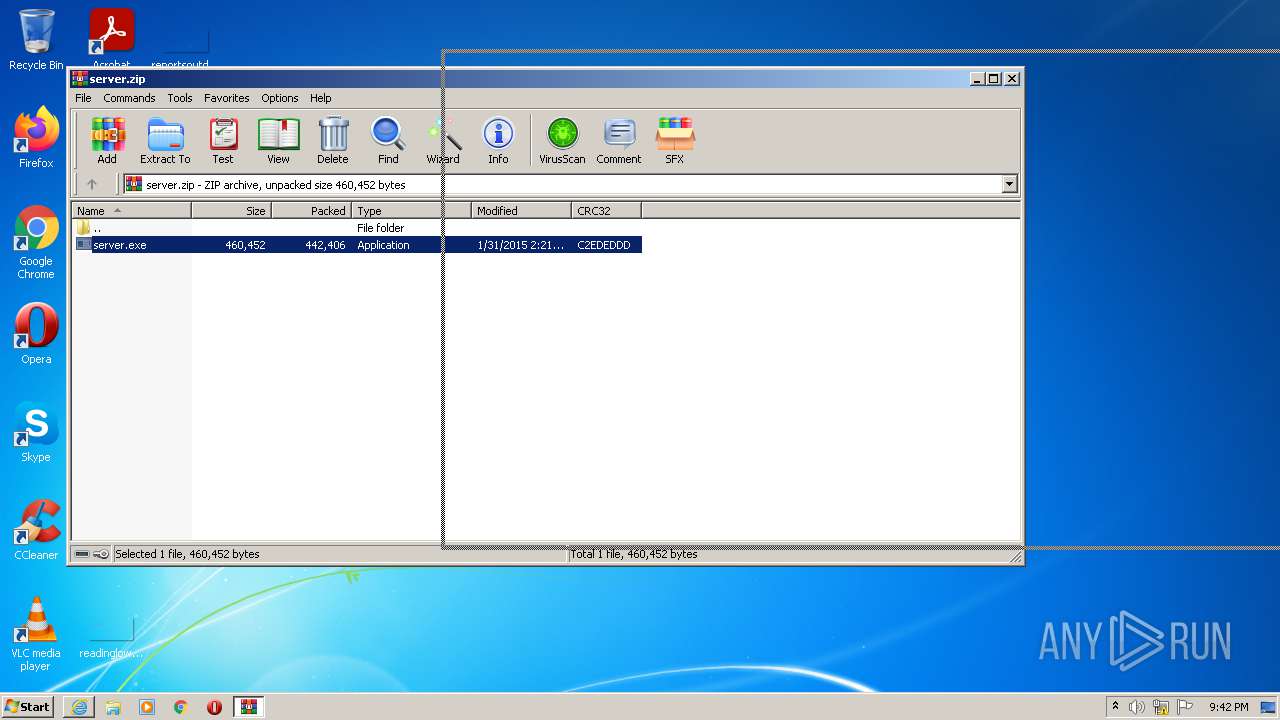
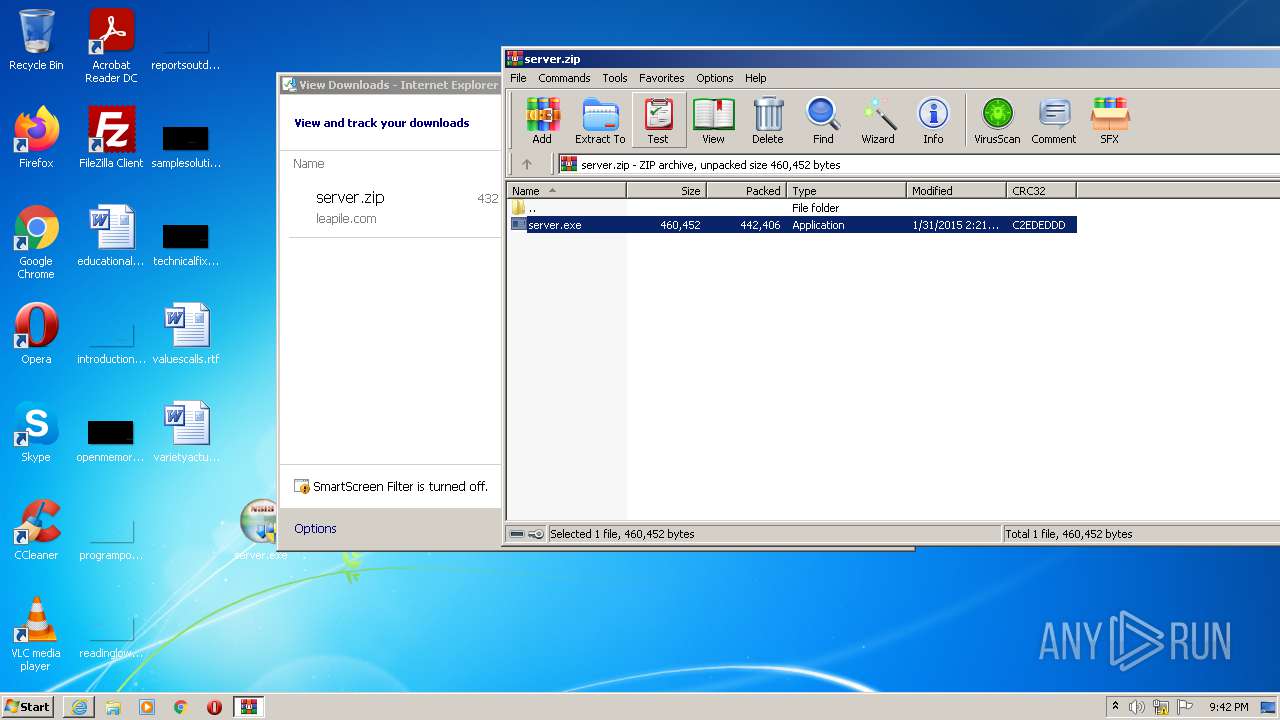
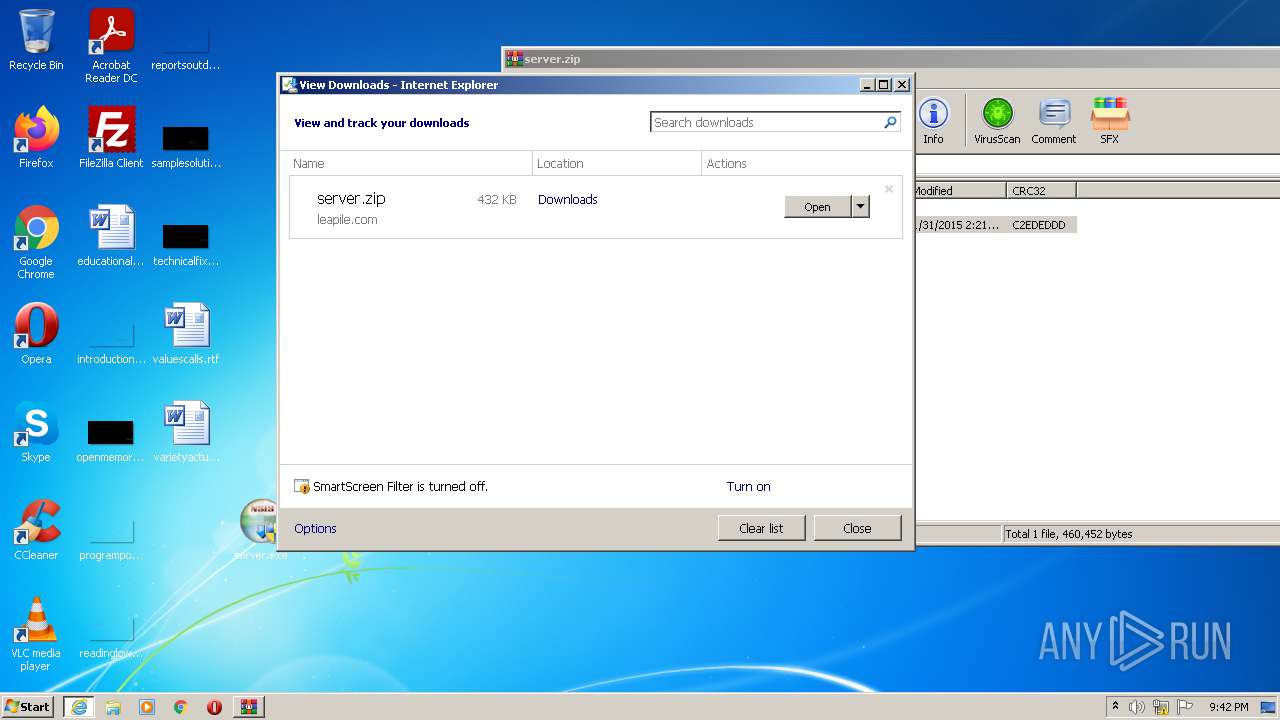
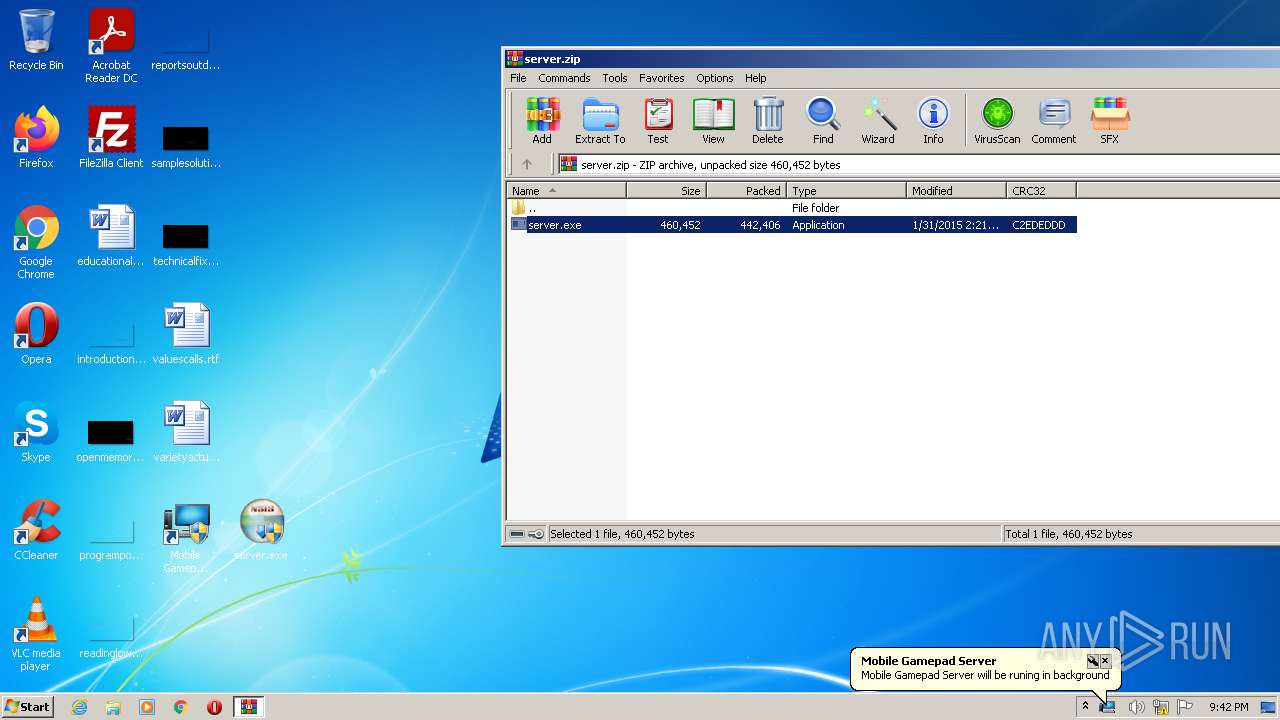
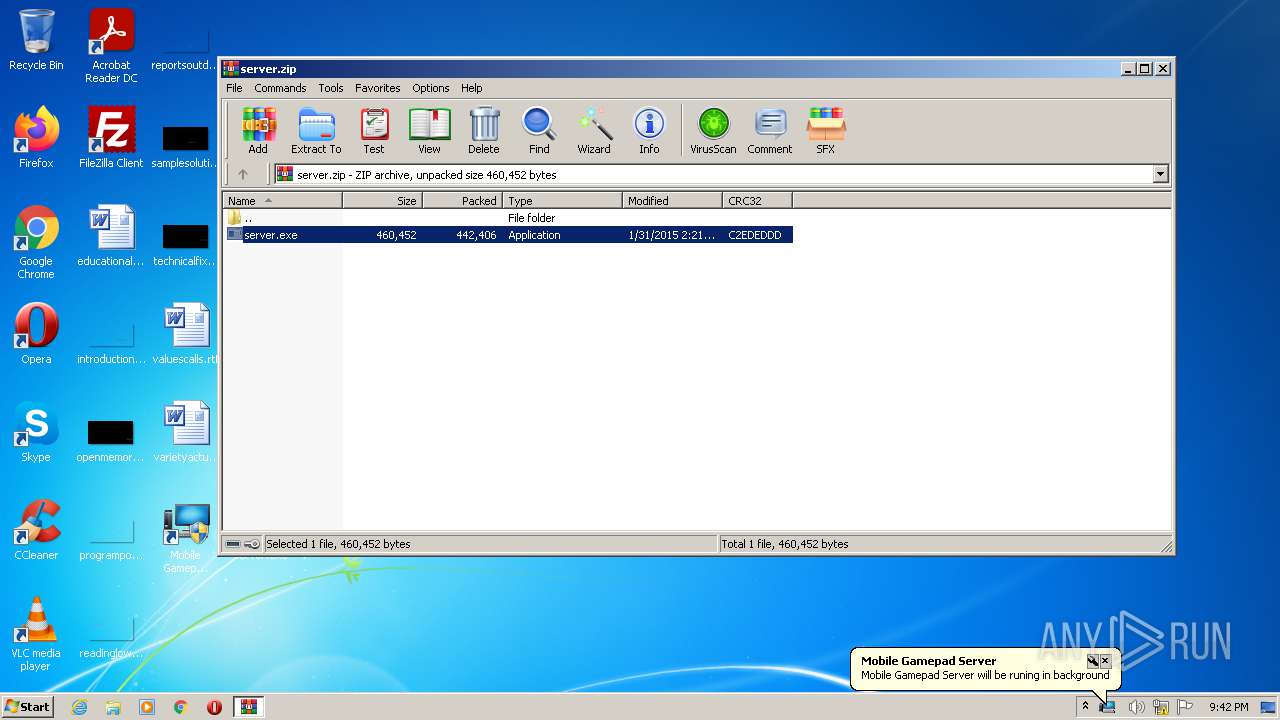
| 3228 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\server.zip" | C:\Program Files\WinRAR\WinRAR.exe | iexplore.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3708 | "C:\Users\admin\Desktop\server.exe" | C:\Users\admin\Desktop\server.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3792 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:340 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
18 424
Read events
18 297
Write events
126
Delete events
1
Modification events
| (PID) Process: | (340) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (340) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (340) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30898014 | |||
| (PID) Process: | (340) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (340) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30898014 | |||
| (PID) Process: | (340) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (340) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (340) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (340) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (340) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
9
Suspicious files
10
Text files
9
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3792 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\A32AFJ0Q.txt | text | |
MD5:— | SHA256:— | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:— | SHA256:— | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:— | SHA256:— | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\2tjZjFZ[1].htm | html | |
MD5:— | SHA256:— | |||
| 3792 | iexplore.exe | C:\Users\admin\Downloads\server.zip.j5av1nh.partial | compressed | |
MD5:— | SHA256:— | |||
| 340 | iexplore.exe | C:\Users\admin\Downloads\server.zip | compressed | |
MD5:— | SHA256:— | |||
| 3228 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3228.37642\server.exe | executable | |
MD5:— | SHA256:— | |||
| 3708 | server.exe | C:\Program Files\Mobile Gamepad Server\CoreAudioApi.dll | executable | |
MD5:— | SHA256:— | |||
| 340 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFAFB4D491AD52EC85.TMP | gmc | |
MD5:— | SHA256:— | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\server[1].zip | compressed | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
11
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
340 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3792 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
3792 | iexplore.exe | GET | 301 | 67.199.248.11:80 | http://bit.ly/2tjZjFZ | US | html | 131 b | shared |
3792 | iexplore.exe | GET | 200 | 13.107.4.50:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?79a1730873965623 | US | compressed | 4.70 Kb | whitelisted |
3792 | iexplore.exe | GET | 200 | 13.107.4.50:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?7013f233b39e31e7 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3792 | iexplore.exe | 67.199.248.11:80 | bit.ly | Bitly Inc | US | shared |
3792 | iexplore.exe | 172.67.157.219:443 | www.leapile.com | — | US | malicious |
3792 | iexplore.exe | 13.107.4.50:80 | ctldl.windowsupdate.com | Microsoft Corporation | US | whitelisted |
340 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3792 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
340 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bit.ly |
| shared |
www.leapile.com |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
Mobile Gamepad.exe | 32feet.NET: 'InTheHand.Net.Personal, Version=3.5.605.0, Culture=neutral, PublicKeyToken=ea38caa273134499'
versions: '3.5.605.0' and '3.5.0605.0'.
|
Mobile Gamepad.exe | IBtIf using WidcommStBtIf.
|
Mobile Gamepad.exe | Dependency DLL '32feetWidcomm' status: NotFound.
|
Mobile Gamepad.exe | System.PlatformNotSupportedException: Microsoft Bluetooth stack not supported (radio).
|
Mobile Gamepad.exe | System.Reflection.TargetInvocationException: Dependency DLL '32feetWidcomm' status: NotFound. ---> System.PlatformNotSupportedException: Dependency DLL '32feetWidcomm' status: NotFound. ---> System.DllNotFoundException: Unable to load DLL '32feetWidcomm': The specified module could not be found. (Exception from HRESULT: 0x8007007E)
|
Mobile Gamepad.exe | System.DllNotFoundException: Unable to load DLL 'BsSDK': The specified module could not be found. (Exception from HRESULT: 0x8007007E)
|