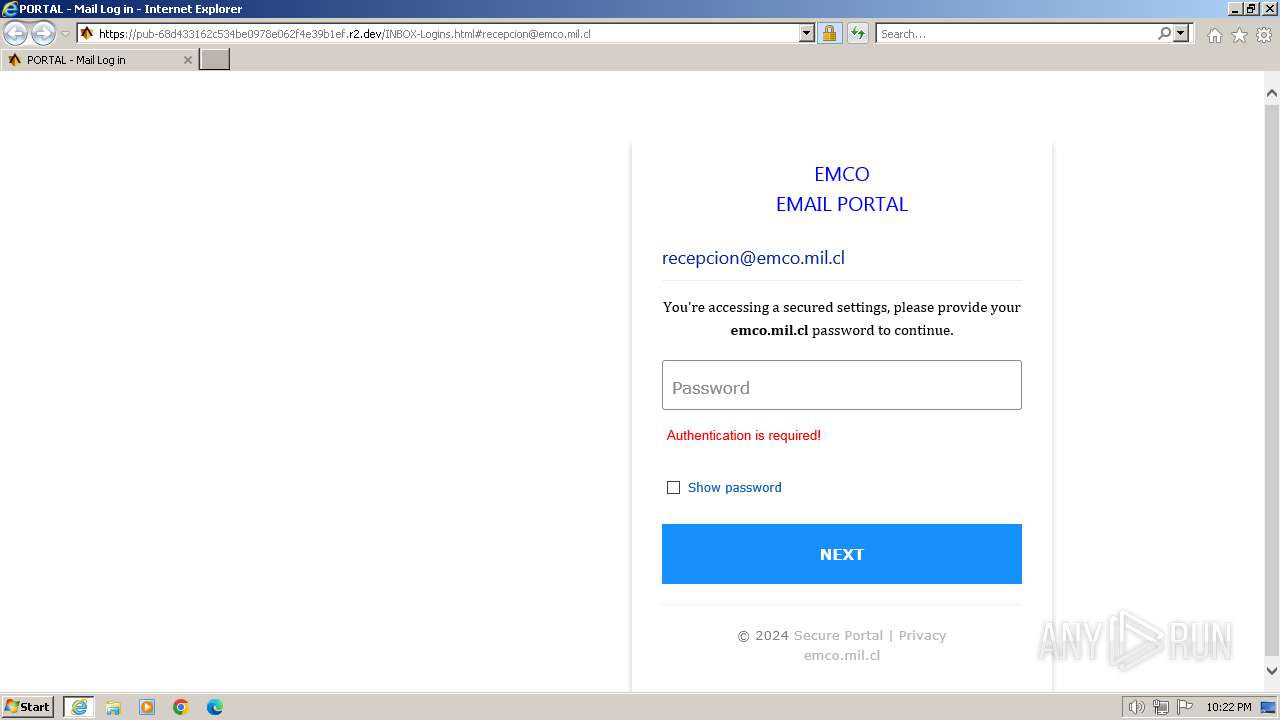
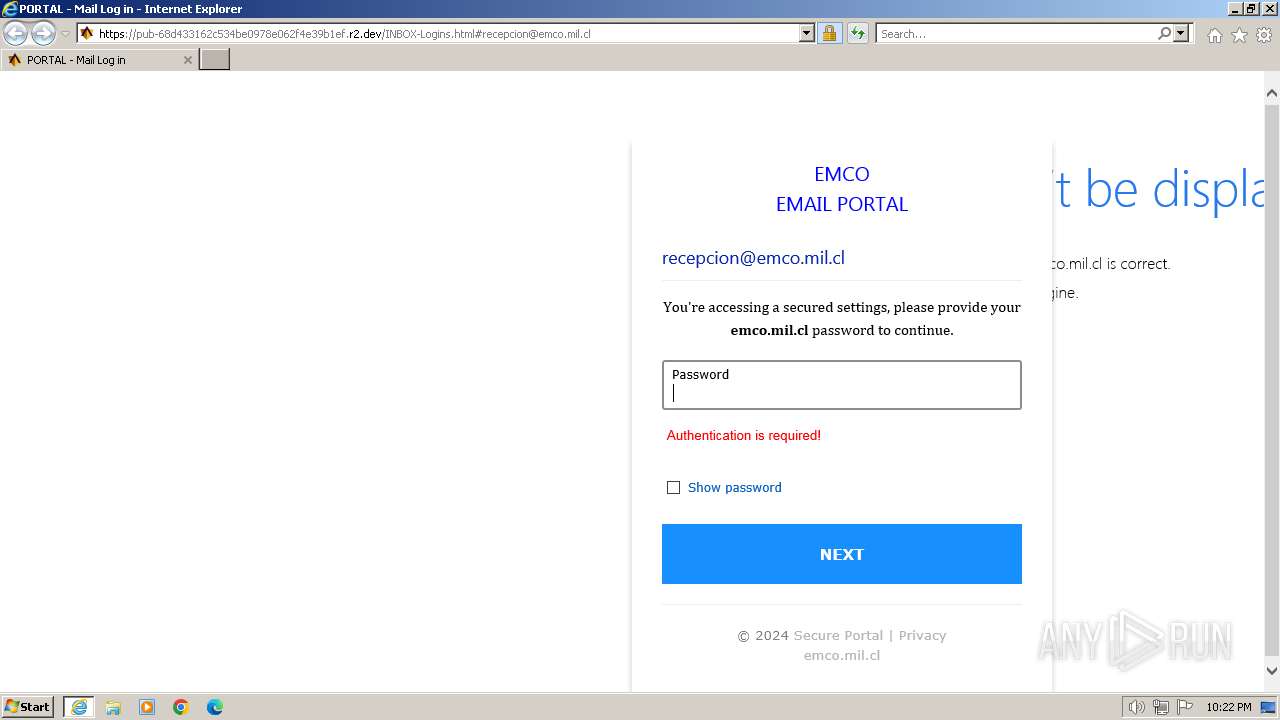
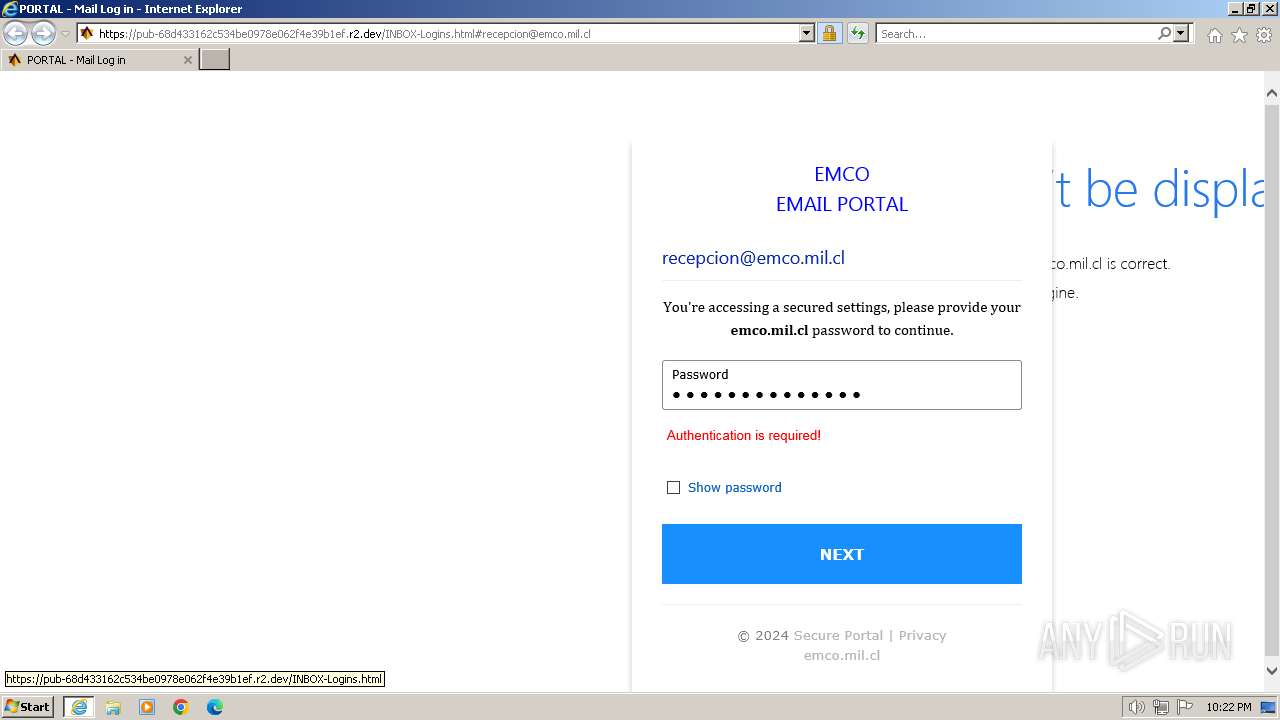
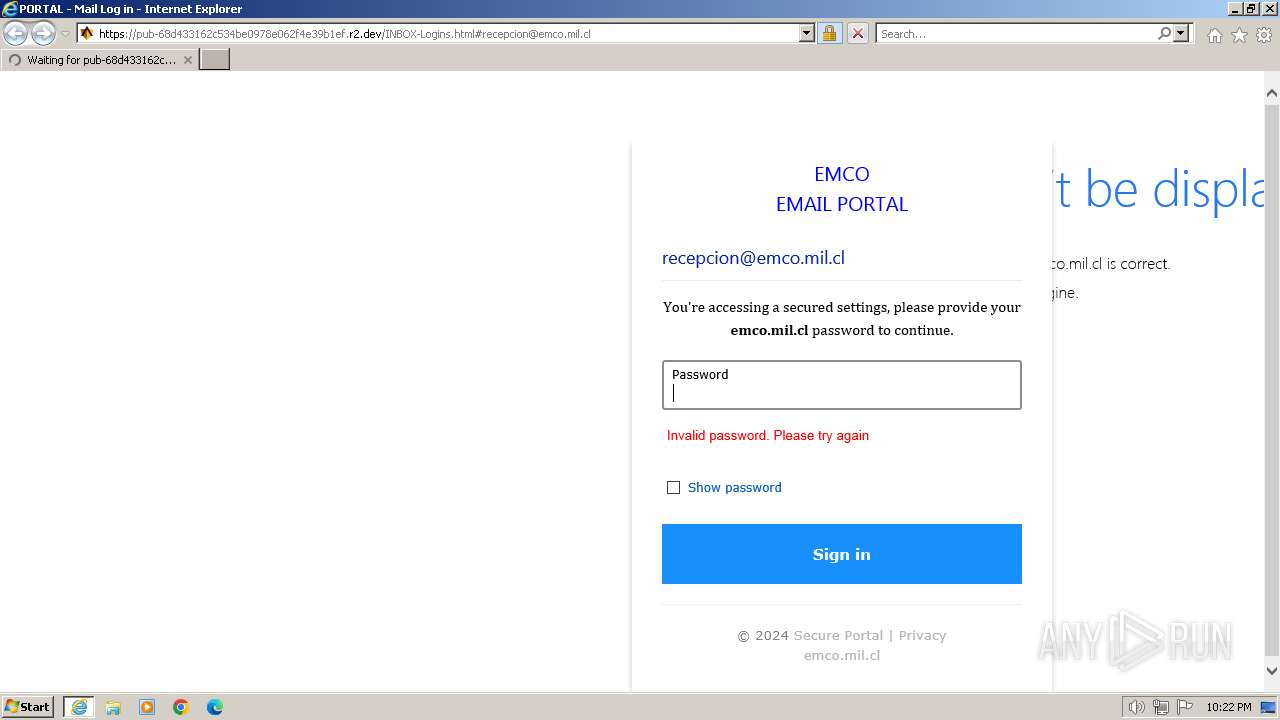
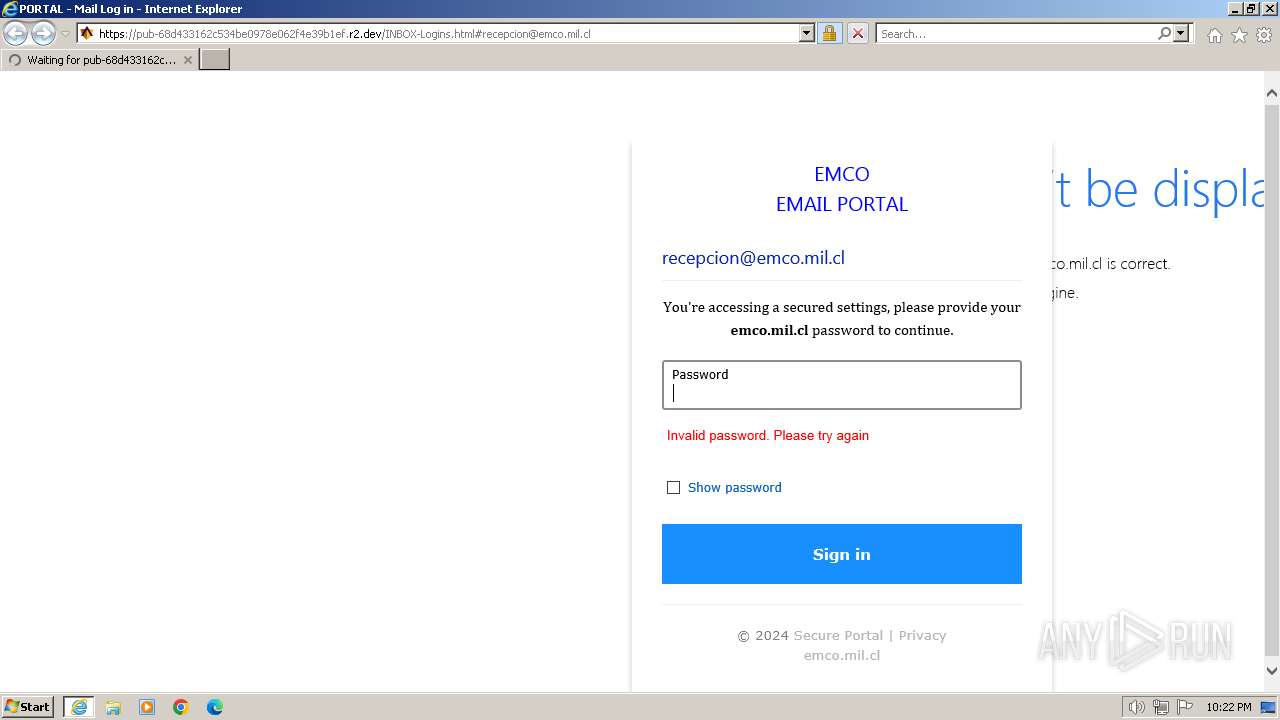
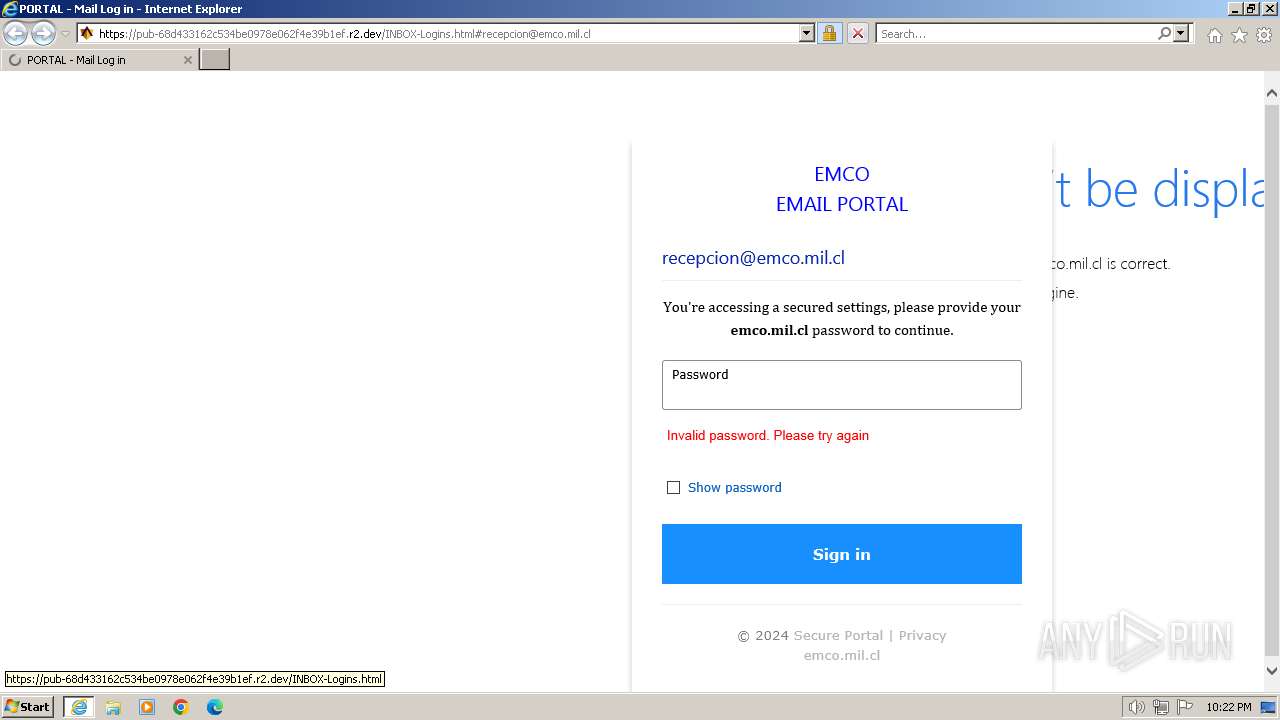
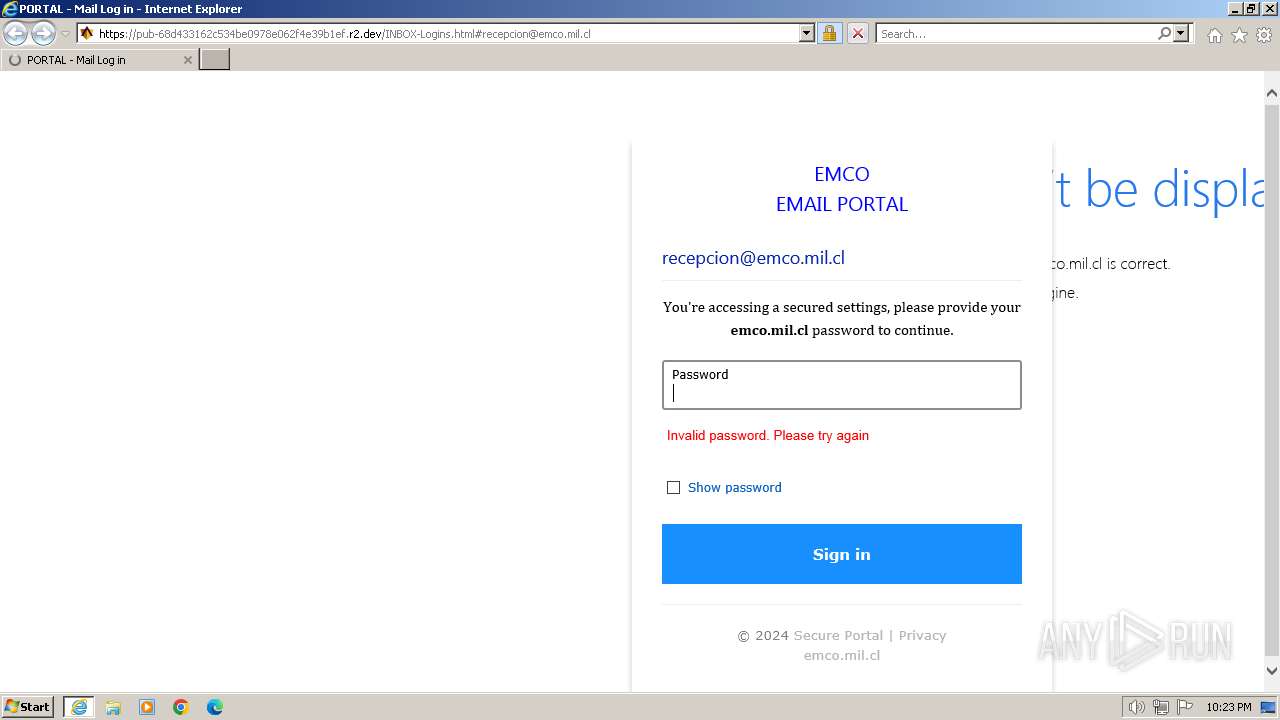
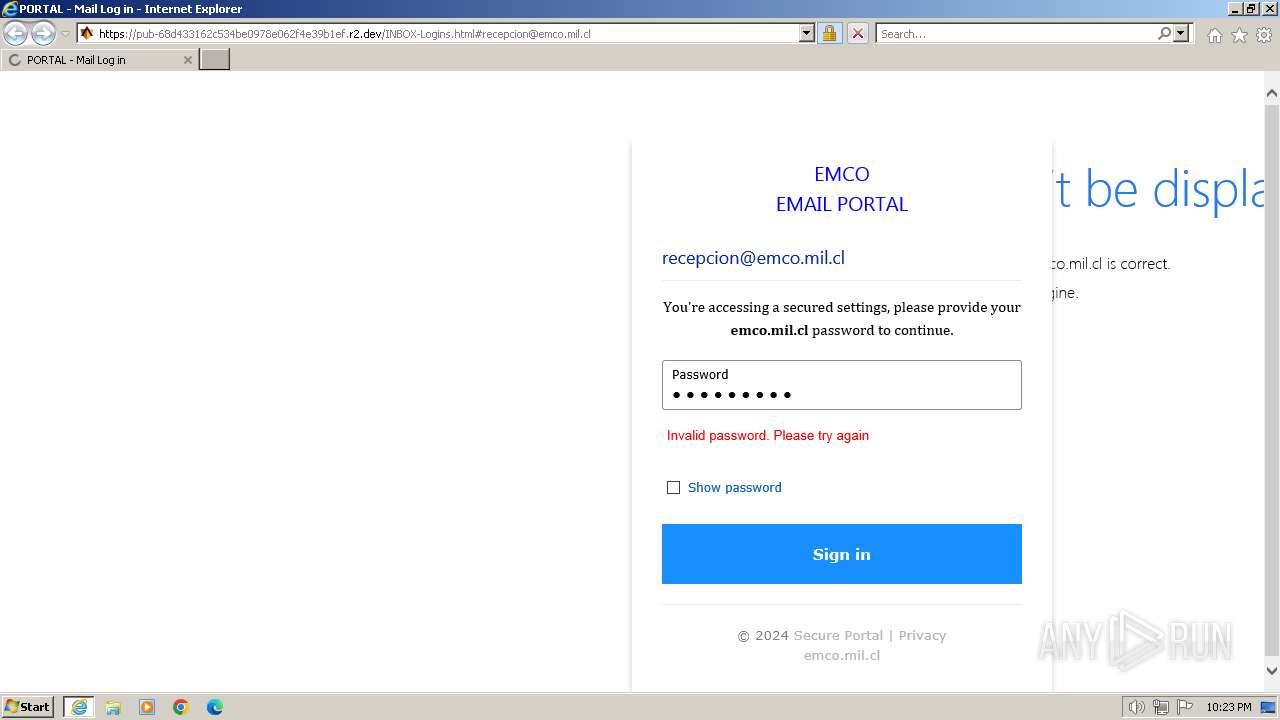
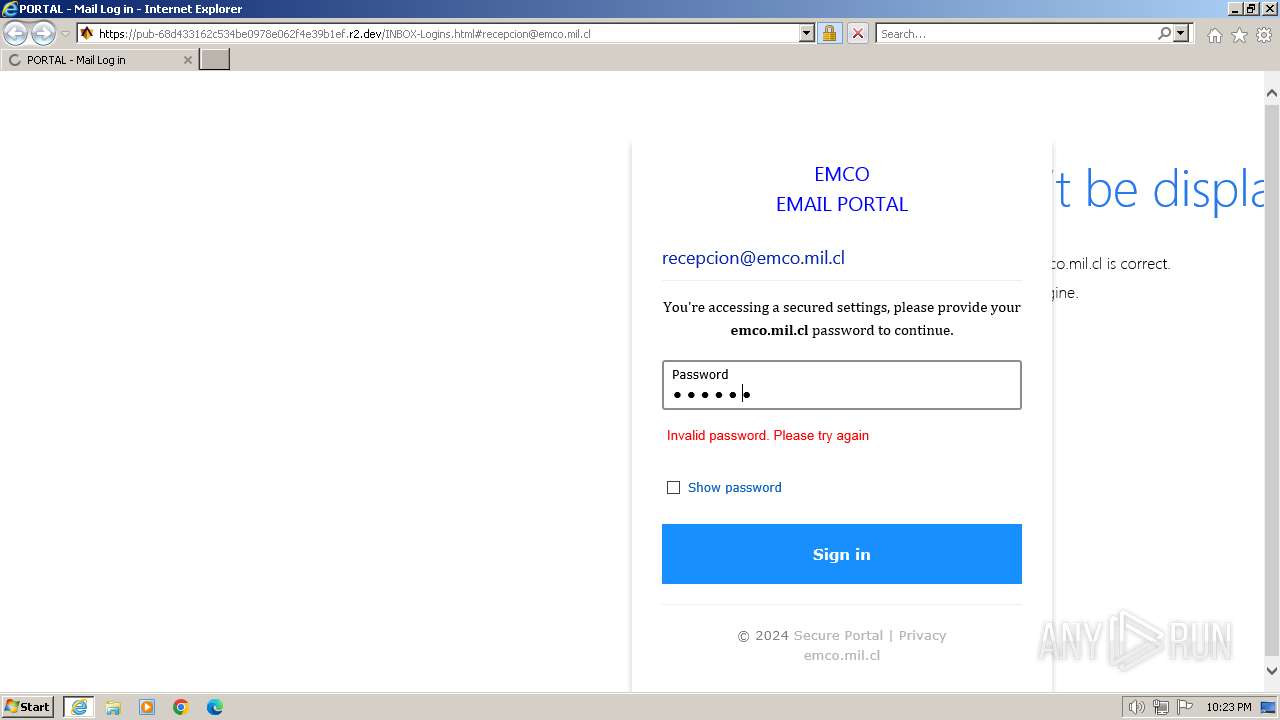
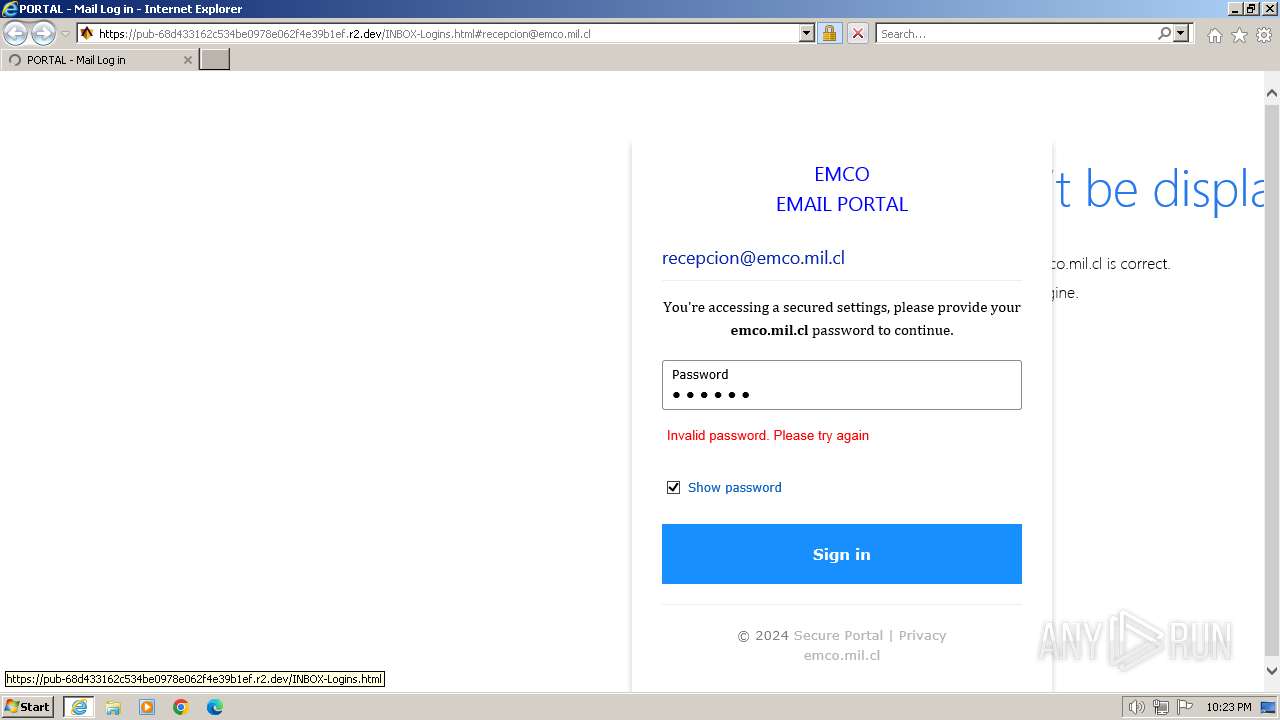
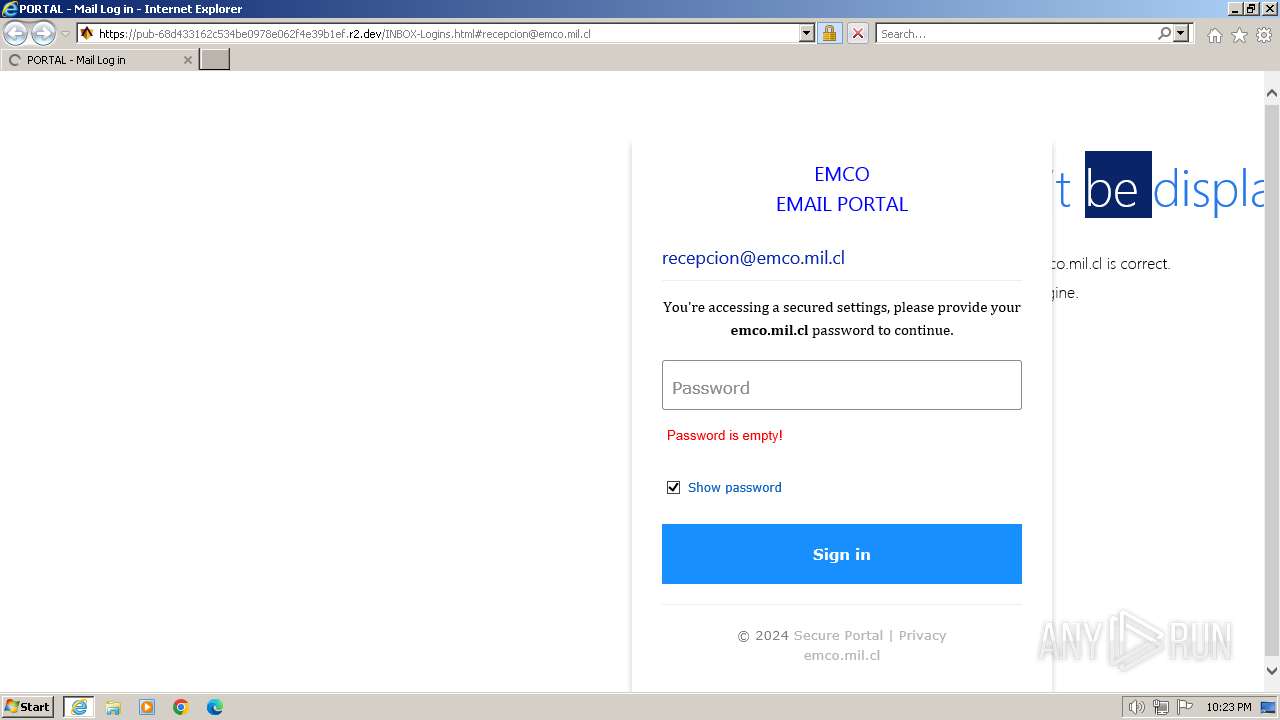
| URL: | https://pub-68d433162c534be0978e062f4e39b1ef.r2.dev/INBOX-Logins.html#recepcion@emco.mil.cl |
| Full analysis: | https://app.any.run/tasks/a55b8d64-d76e-4507-b99a-526617120312 |
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2024, 21:21:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E1440444F8C18F3761838CFFEAF23ADD |
| SHA1: | 6962CA0FF95D5D29C6932FFACF7625F407385F3B |
| SHA256: | D21502FC86C85807A283D907E959BD5FD019FDA1CE44A3372F1A659AB868880A |
| SSDEEP: | 3:N8UOEeRDbNy5nszGIXAGPRtGQxJan:2UO7TmnsaIQIRtGZ |
MALICIOUS
PHISHING has been detected (SURICATA)
- iexplore.exe (PID: 2296)
SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 1288)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1288 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://pub-68d433162c534be0978e062f4e39b1ef.r2.dev/INBOX-Logins.html#recepcion@emco.mil.cl" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2296 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1288 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
25 327
Read events
25 095
Write events
126
Delete events
106
Modification events
| (PID) Process: | (1288) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1288) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (1288) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31102404 | |||
| (PID) Process: | (1288) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (1288) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31102404 | |||
| (PID) Process: | (1288) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1288) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1288) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1288) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1288) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
39
Text files
26
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2296 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:29F65BA8E88C063813CC50A4EA544E93 | SHA256:1ED81FA8DFB6999A9FEDC6E779138FFD99568992E22D300ACD181A6D2C8DE184 | |||
| 2296 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarD975.tmp | cat | |
MD5:435A9AC180383F9FA094131B173A2F7B | SHA256:67DC37ED50B8E63272B49A254A6039EE225974F1D767BB83EB1FD80E759A7C34 | |||
| 2296 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarD987.tmp | cat | |
MD5:435A9AC180383F9FA094131B173A2F7B | SHA256:67DC37ED50B8E63272B49A254A6039EE225974F1D767BB83EB1FD80E759A7C34 | |||
| 2296 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:88E02173658DA1B28384047F7E788846 | SHA256:B6318633B9CAB24E8C4CA242B8FFD22E7B0C53D8B07A51F900D05A6CE3655274 | |||
| 2296 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabD974.tmp | compressed | |
MD5:29F65BA8E88C063813CC50A4EA544E93 | SHA256:1ED81FA8DFB6999A9FEDC6E779138FFD99568992E22D300ACD181A6D2C8DE184 | |||
| 2296 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | der | |
MD5:822467B728B7A66B081C91795373789A | SHA256:AF2343382B88335EEA72251AD84949E244FF54B6995063E24459A7216E9576B9 | |||
| 2296 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\popper.min[1].js | text | |
MD5:70D3FDA195602FE8B75E0097EED74DDE | SHA256:A52F7AA54D7BCAAFA056EE0A050262DFC5694AE28DEE8B4CAC3429AF37FF0D66 | |||
| 2296 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\1B1495DD322A24490E2BF2FAABAE1C61 | binary | |
MD5:AC98D646C489329A185F060C6A4E7D01 | SHA256:4BE4AC029A87B8035C27845D5E31B9A5F352DA5C864B0D394348D317E87DF139 | |||
| 2296 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:5BC5C02DEE940EF38177C6774C6D2312 | SHA256:ADC43CDE9E9F0DDAF60C24B0CCB9BED5724A4D1BA9CEE86B5B6A6D1531FF1F13 | |||
| 2296 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\1B1495DD322A24490E2BF2FAABAE1C61 | der | |
MD5:5AE8478AF8DD6EEC7AD4EDF162DD3DF1 | SHA256:FE42AC92EAE3B2850370B73C3691CCF394C23AB6133DE39F1697A6EBAC4BEDCA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
67
DNS requests
37
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2296 | iexplore.exe | GET | 200 | 92.123.133.34:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?5b4929cea90c89d8 | unknown | — | — | unknown |
2296 | iexplore.exe | GET | 304 | 92.123.133.34:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?e3969b55e300b10b | unknown | — | — | unknown |
2296 | iexplore.exe | GET | 304 | 92.123.133.34:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?378b9923119ef80e | unknown | — | — | unknown |
2296 | iexplore.exe | GET | 200 | 92.123.133.34:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?ec77a7b48dff2a8f | unknown | — | — | unknown |
2296 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | unknown | — | — | unknown |
2296 | iexplore.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | unknown | — | — | unknown |
2296 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | — | — | unknown |
2296 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | unknown | — | — | unknown |
2296 | iexplore.exe | GET | 200 | 184.27.137.75:80 | http://x1.c.lencr.org/ | unknown | — | — | unknown |
2296 | iexplore.exe | GET | 200 | 184.27.137.75:80 | http://x2.c.lencr.org/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
2296 | iexplore.exe | 104.18.2.35:443 | pub-68d433162c534be0978e062f4e39b1ef.r2.dev | CLOUDFLARENET | — | unknown |
2296 | iexplore.exe | 92.123.133.34:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
2296 | iexplore.exe | 184.27.137.75:80 | x1.c.lencr.org | AKAMAI-AS | US | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2296 | iexplore.exe | 104.17.25.14:443 | cdnjs.cloudflare.com | CLOUDFLARENET | — | unknown |
2296 | iexplore.exe | 192.229.133.221:443 | www.w3schools.com | EDGECAST | US | whitelisted |
2296 | iexplore.exe | 142.250.186.132:443 | t1.gstatic.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pub-68d433162c534be0978e062f4e39b1ef.r2.dev |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
x2.c.lencr.org |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
www.w3schools.com |
| whitelisted |
t1.gstatic.com |
| whitelisted |
code.jquery.com |
| whitelisted |
maxcdn.bootstrapcdn.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2296 | iexplore.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Possible Public R2.dev Bucket Abuse to Phishing in TLS (Greatness) |
2296 | iexplore.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code.jquery .com) |
1080 | svchost.exe | Misc activity | ET INFO Clearbit Logo Query in DNS Lookup |
2296 | iexplore.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Possible Fake Auth Page (Logo Request) |
2296 | iexplore.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Possible Fake Auth Page (Logo Request) |
2296 | iexplore.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Possible Fake Auth Page (Logo Request) |
2296 | iexplore.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Possible Fake Auth Page (Logo Request) |